Packet capture and protocol analysis 1 Content TCPIP
- Slides: 56
Packet capture and protocol analysis 1
Content • TCP/IP Networking Review • Packet Capture • Protocol Analysis 2
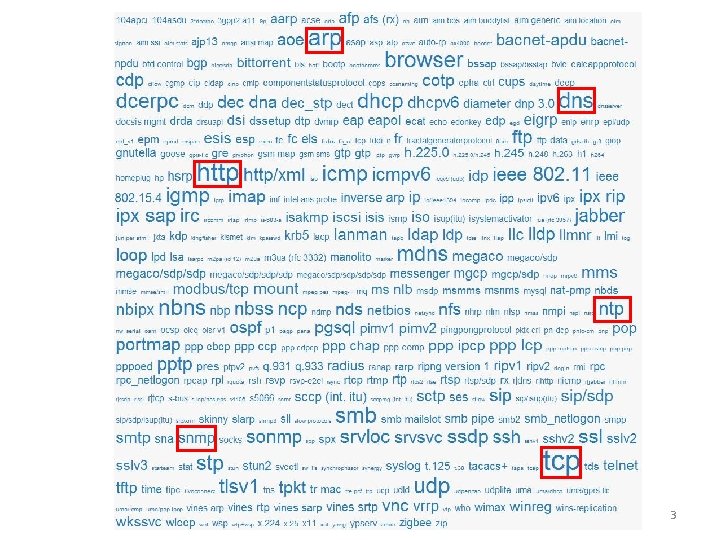
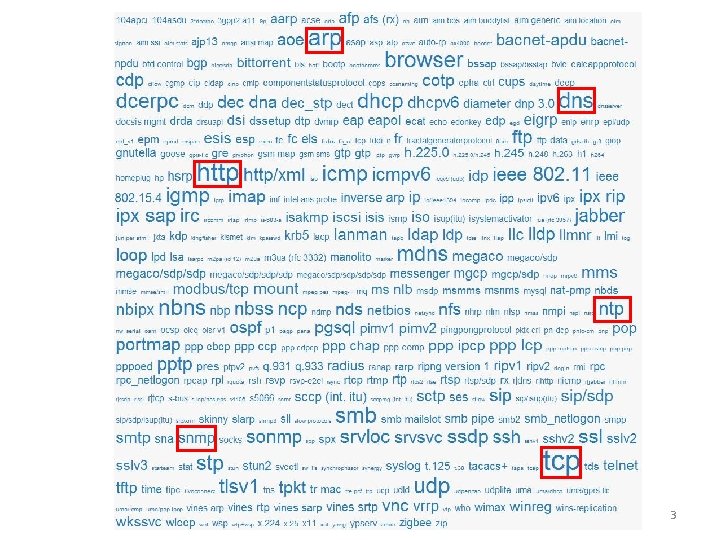
3
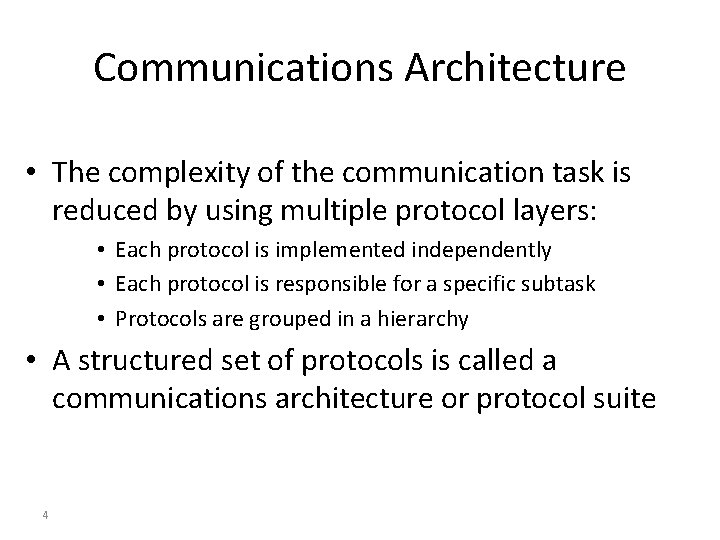
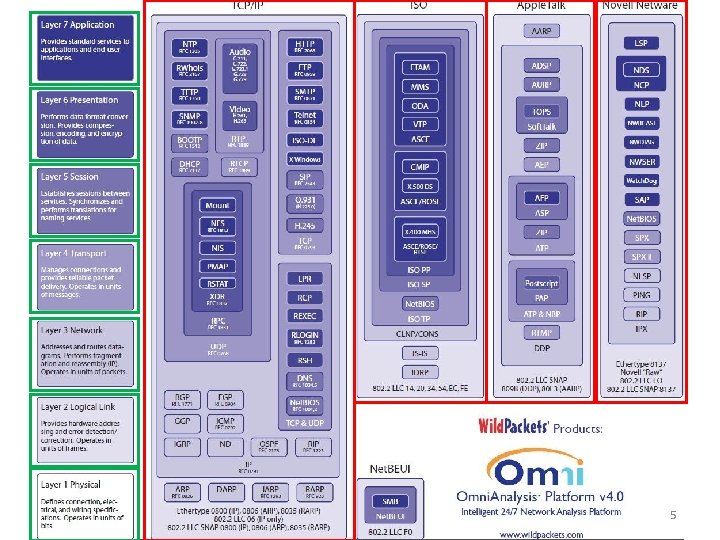
Communications Architecture • The complexity of the communication task is reduced by using multiple protocol layers: • Each protocol is implemented independently • Each protocol is responsible for a specific subtask • Protocols are grouped in a hierarchy • A structured set of protocols is called a communications architecture or protocol suite 4
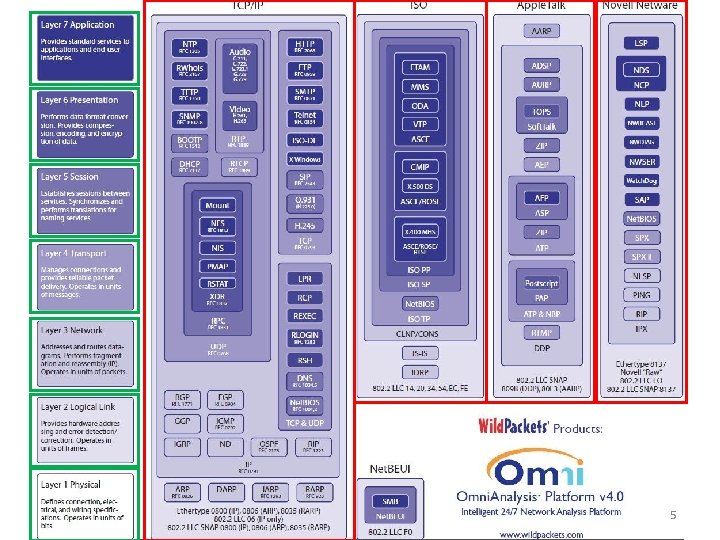
5
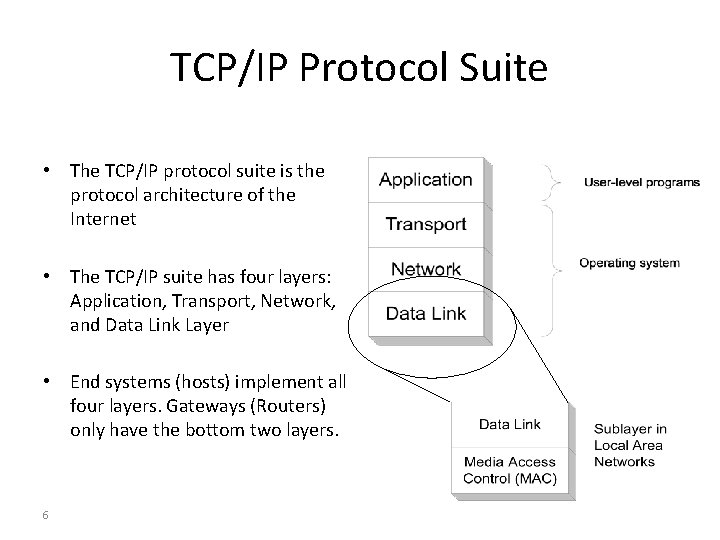
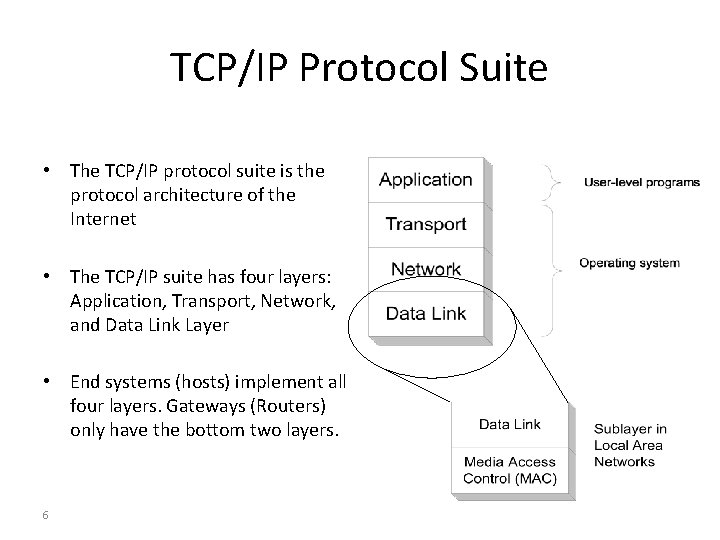
TCP/IP Protocol Suite • The TCP/IP protocol suite is the protocol architecture of the Internet • The TCP/IP suite has four layers: Application, Transport, Network, and Data Link Layer • End systems (hosts) implement all four layers. Gateways (Routers) only have the bottom two layers. 6
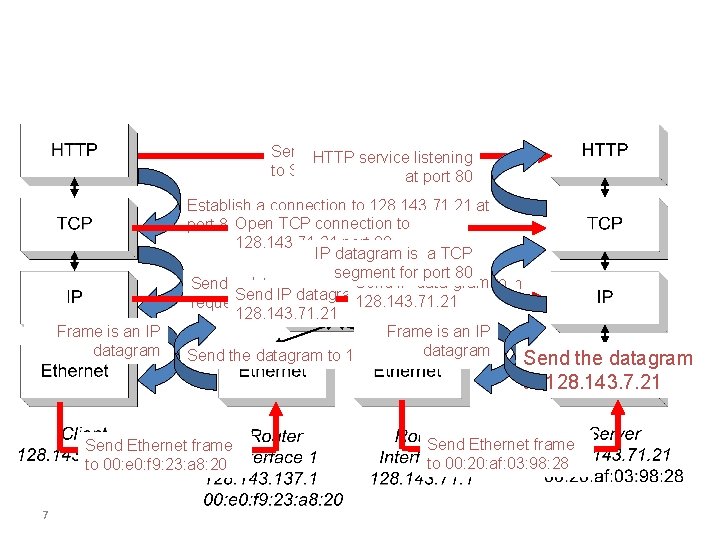
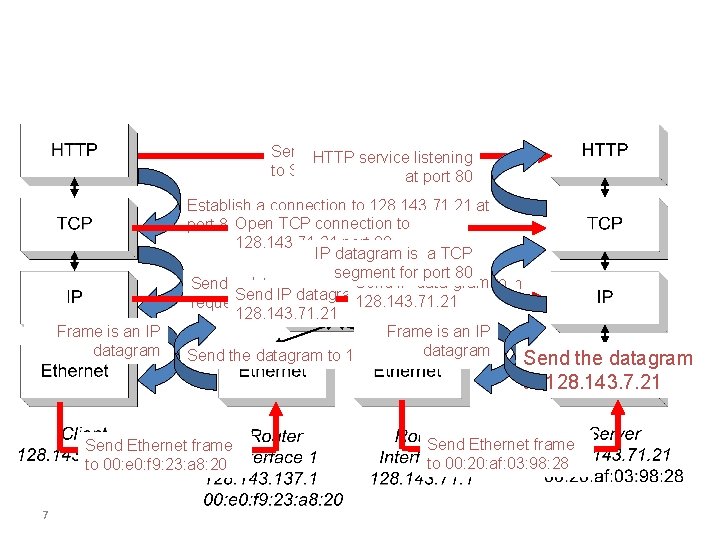
Send HTTP service Requestlistening to Server at port 80 Frame is an IP datagram Establish a connection to 128. 143. 71. 21 at port 80 Open TCP connection to 128. 143. 71. 21 port 80 IP datagram is a TCP segment for port 80 Send IP data-gram to Send a datagram (which contains a connection Send IP datagram to 128. 143. 71. 21 request) to 128. 143. 71. 21 Frame is an IP datagram Send the datagram to 128. 143. 137. 1 Send Ethernet frame to 00: e 0: f 9: 23: a 8: 20 7 the datagram to 128. 143. 7. 21 Send Ethernet frame to 00: 20: af: 03: 98: 28
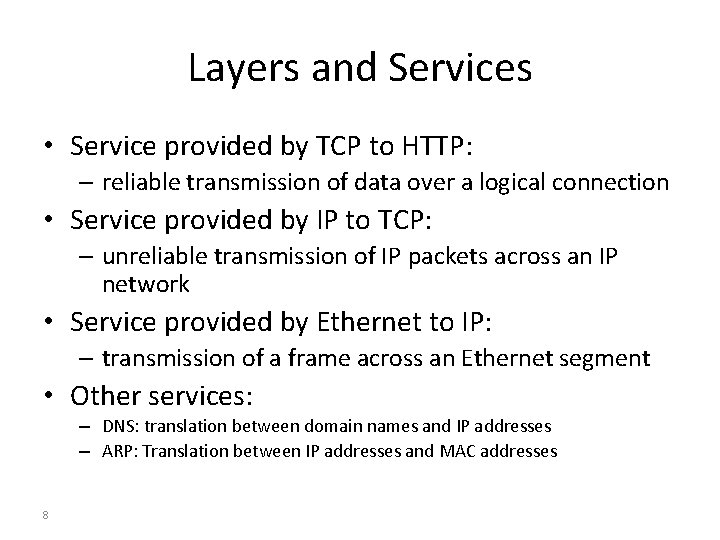
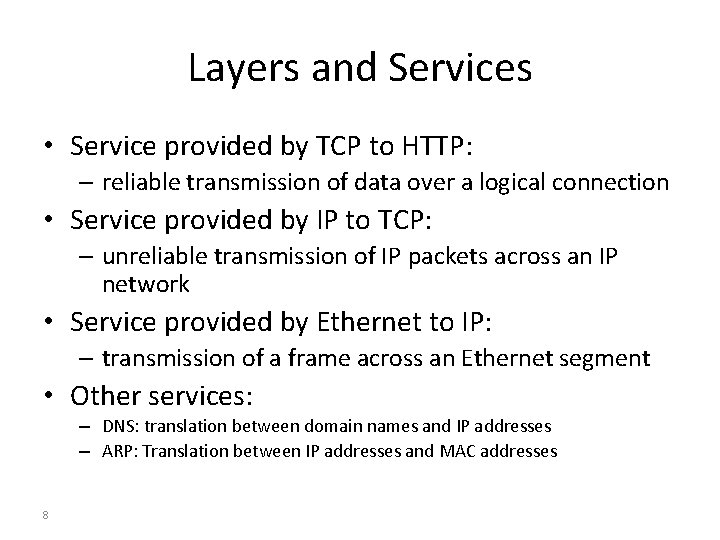
Layers and Services • Service provided by TCP to HTTP: – reliable transmission of data over a logical connection • Service provided by IP to TCP: – unreliable transmission of IP packets across an IP network • Service provided by Ethernet to IP: – transmission of a frame across an Ethernet segment • Other services: – DNS: translation between domain names and IP addresses – ARP: Translation between IP addresses and MAC addresses 8
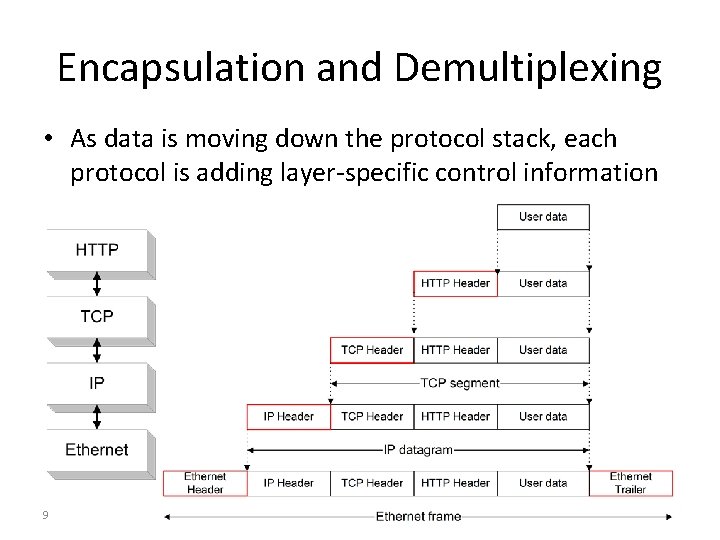
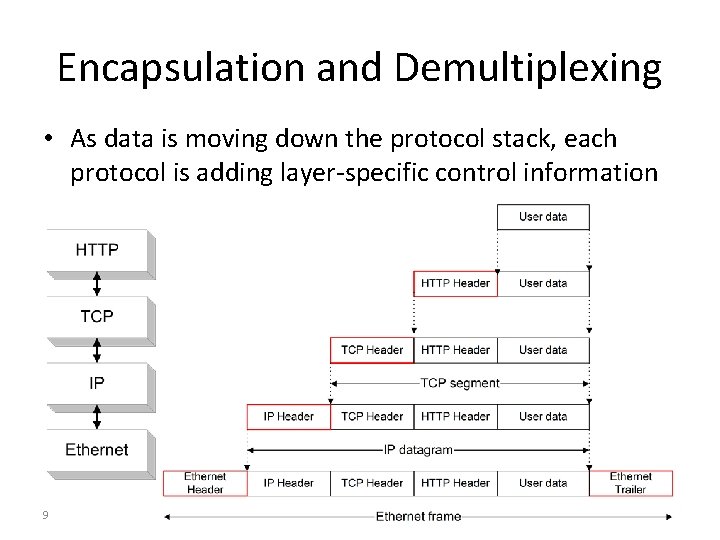
Encapsulation and Demultiplexing • As data is moving down the protocol stack, each protocol is adding layer-specific control information 9
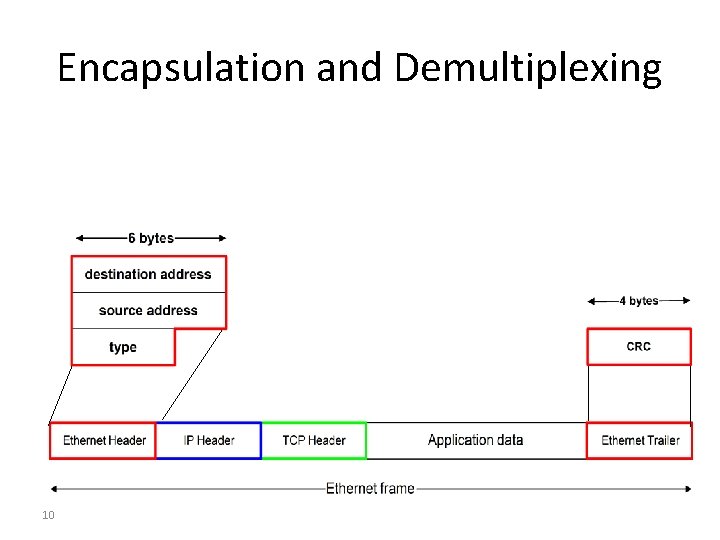
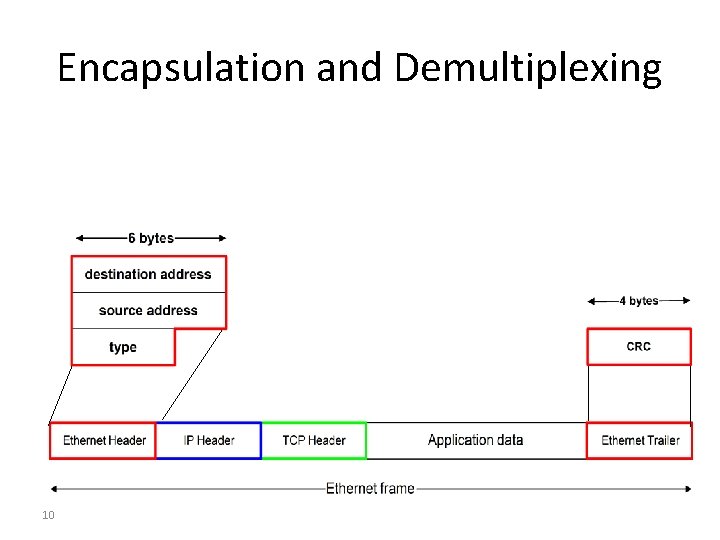
Encapsulation and Demultiplexing 10
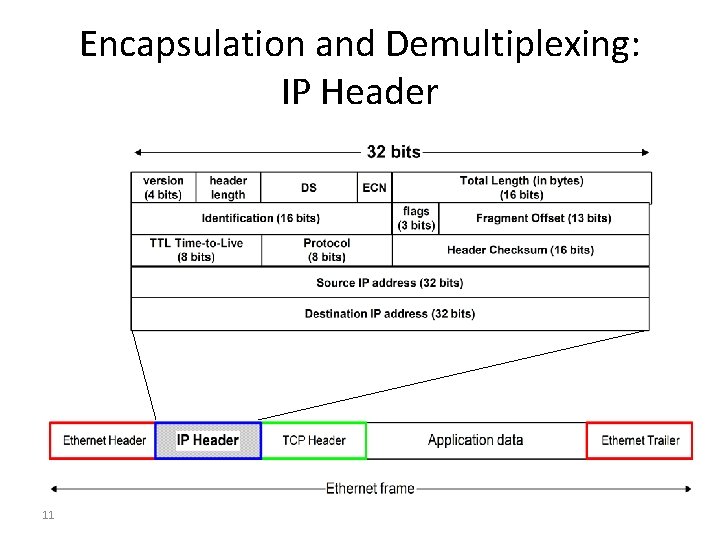
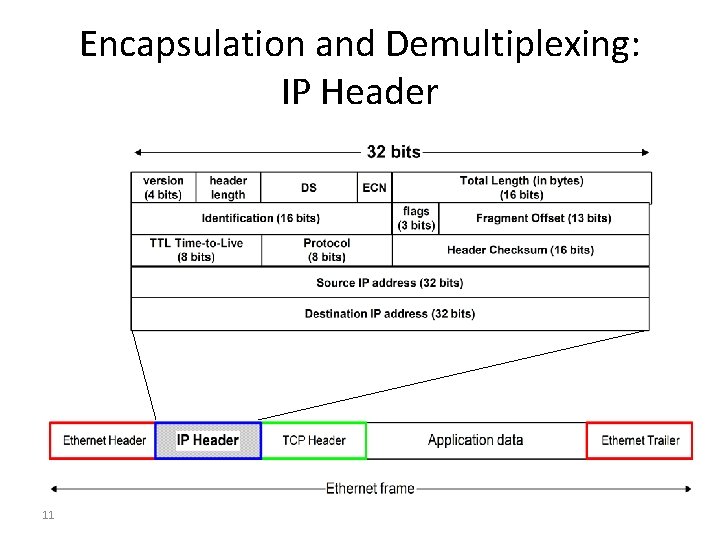
Encapsulation and Demultiplexing: IP Header 11
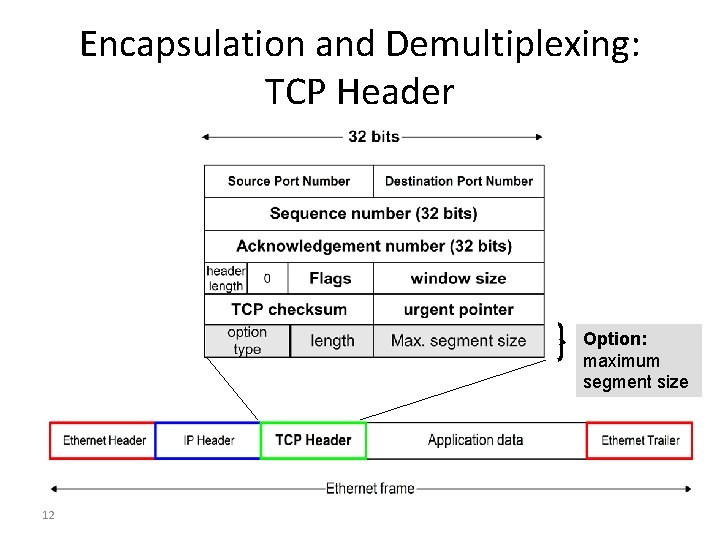
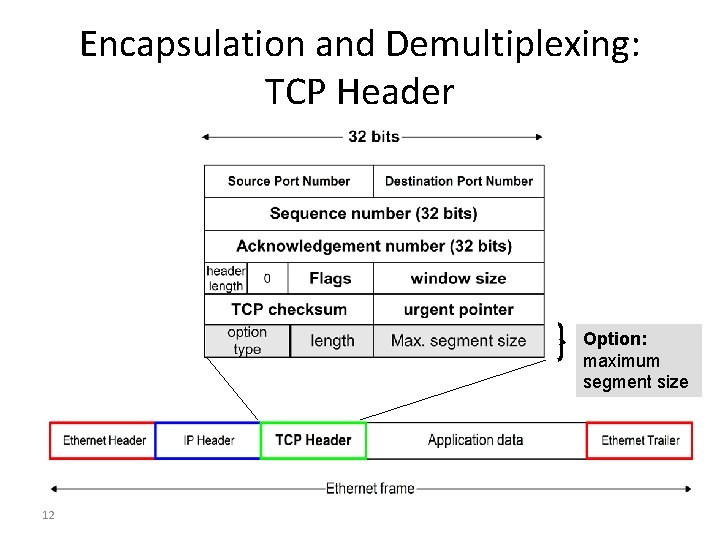
Encapsulation and Demultiplexing: TCP Header Option: maximum segment size 12
Content • TCP/IP Networking Review • Packet Capture • Protocol Analysis 13
Packet capture/Sniffering • Why do we need to capture packets? – troubleshoot network problems – examine security problems – debug protocol implementations – learn network protocol internals 14
Packet capture tools/Sniffers • Classic tools – Wire. Shark (http: //www. wireshark. org/) – TCPDump (http: //www. tcpdump. org/) • Other tools – Ettercap – Dsniff – Ntop – KISMET – Win. Dump – Tshark –… 15
What is Wireshark? An open source packet analyzer Decodes 1115 protocols (V 1. 4) Supports command-line and GUI interfaces Run on many platforms including Windows, OS X, Linux, and UNIX • Many online resources • Wireshark User's Guide (http: //www. wireshark. org/download/docs/u ser-guide-a 4. pdf) • • 16
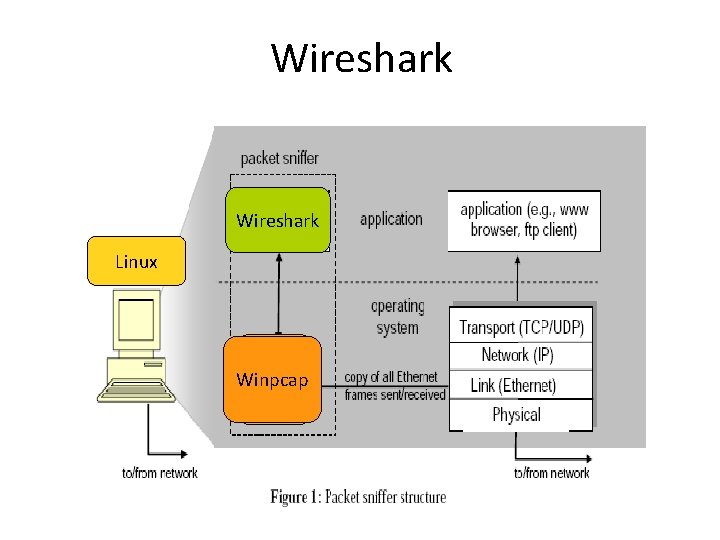
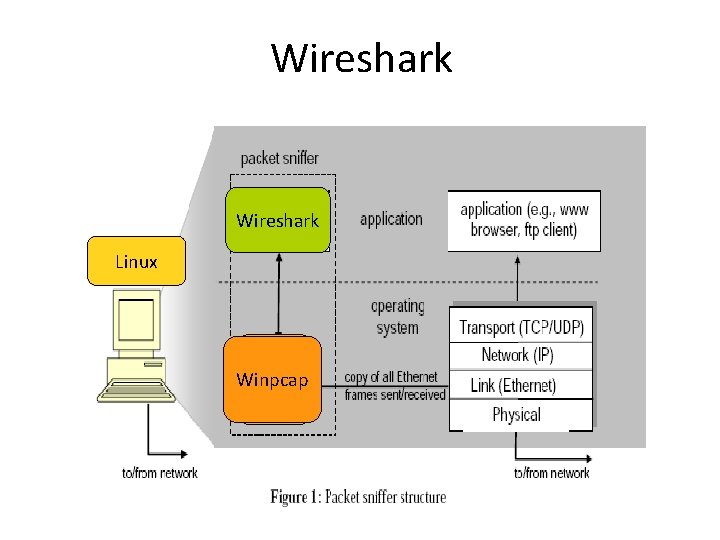
Wireshark Windows Linux Winpcap libpcap
Wireshark • • • Y: Win 32Wireshark. Portable Select interface tcp visit www. polyu. edu. hk HTTP traffic 18
TCPDump/Win. Dump/Tshark • Tcpdump – Unix-based command-line tool used to analyze packets • Including filtering to just capture the packets of interest – Capture packets from interface specified using -i option – Read packets from an existing trace file specified using -r option – Save captured packets using -w option • Win. Dump – The Windows version of tcpdump • Tshark – Tcpdump-like capture program that comes with Wireshark – Very similar behavior & flags to tcpdump 19
Commonly Used Tcpdump Options • -n Don’t convert host addresses to names. Avoids DNS lookups. It can save you time. • -w <filename> Write the raw packets to the specified file instead of parsing and printing them out. Useful for saving a packet capture session and running multiple filters against it later • -r <filename> Read packets from the specified file instead of live capture. The file should have been created with –w option • -q Quiet output. Prints less information per output line 20
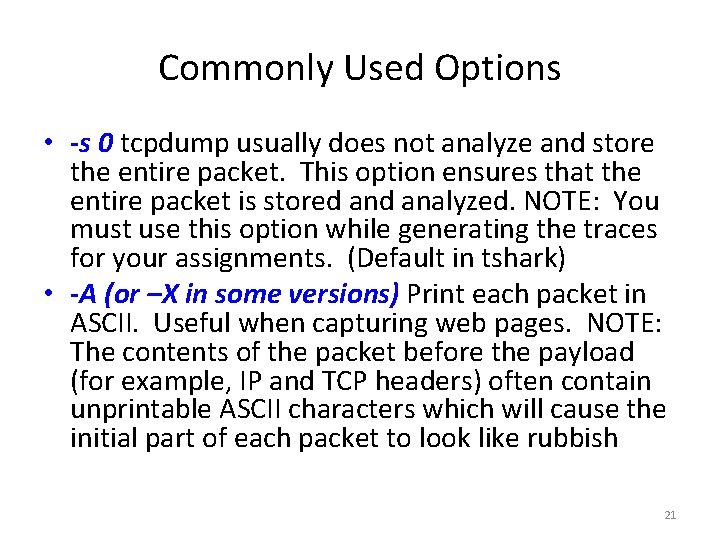
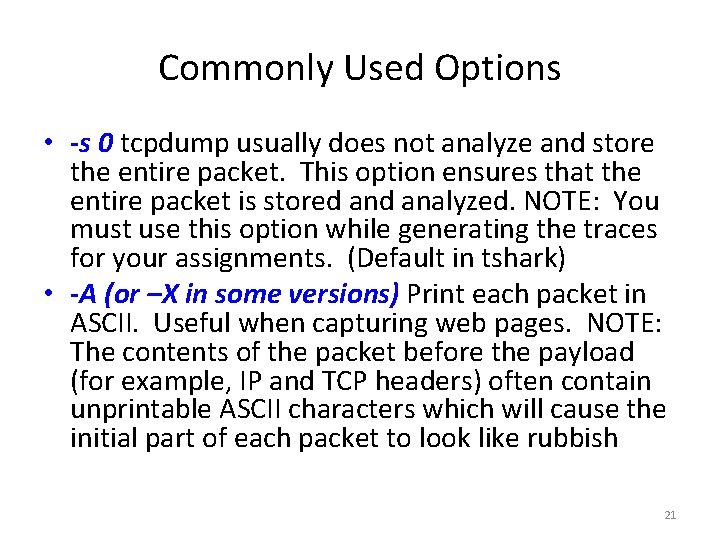
Commonly Used Options • -s 0 tcpdump usually does not analyze and store the entire packet. This option ensures that the entire packet is stored analyzed. NOTE: You must use this option while generating the traces for your assignments. (Default in tshark) • -A (or –X in some versions) Print each packet in ASCII. Useful when capturing web pages. NOTE: The contents of the packet before the payload (for example, IP and TCP headers) often contain unprintable ASCII characters which will cause the initial part of each packet to look like rubbish 21
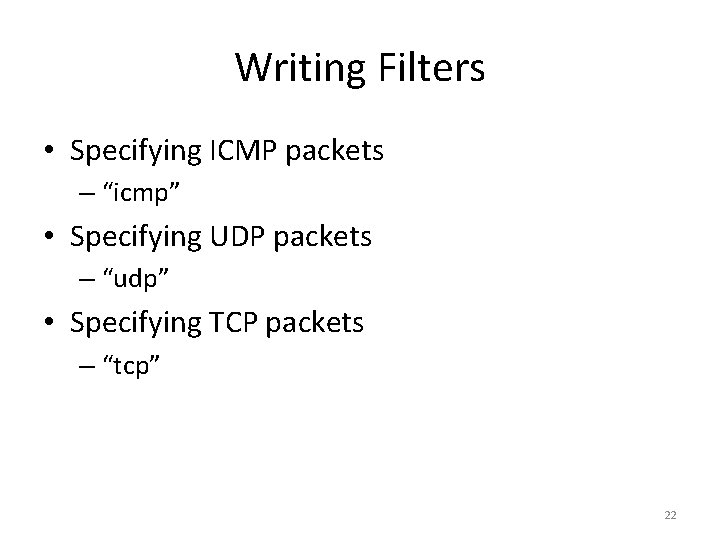
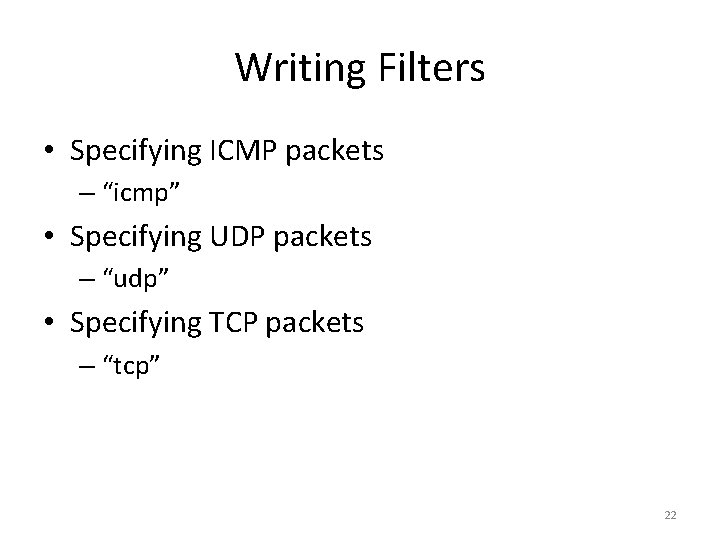
Writing Filters • Specifying ICMP packets – “icmp” • Specifying UDP packets – “udp” • Specifying TCP packets – “tcp” 22
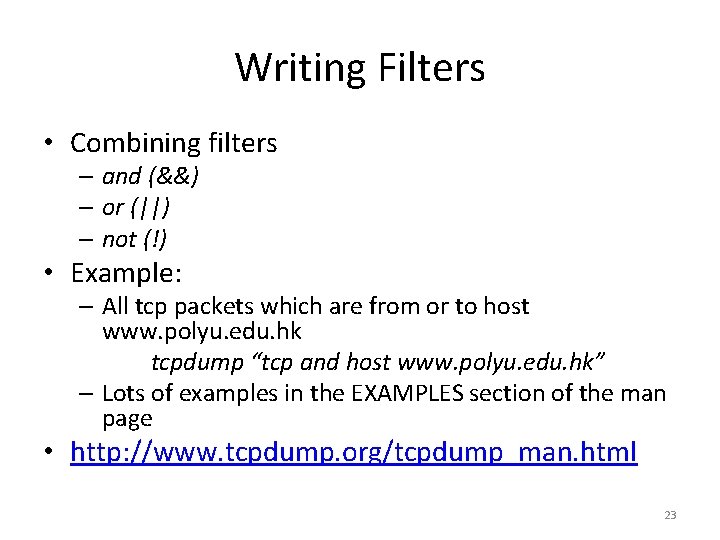
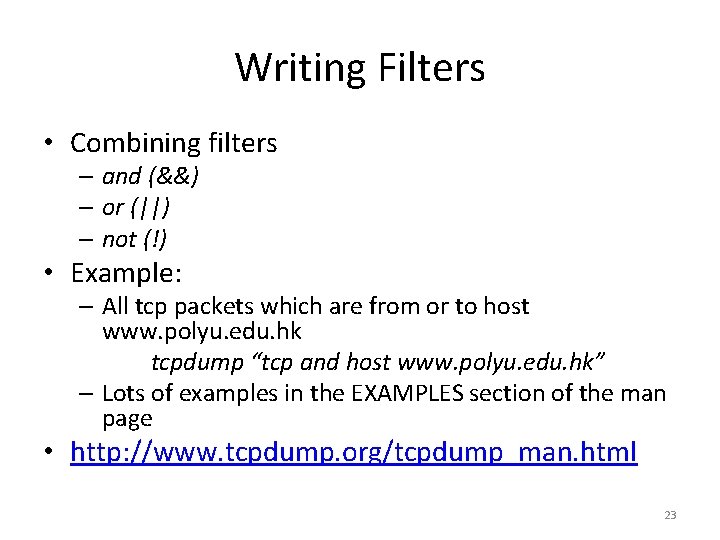
Writing Filters • Combining filters – and (&&) – or (||) – not (!) • Example: – All tcp packets which are from or to host www. polyu. edu. hk tcpdump “tcp and host www. polyu. edu. hk” – Lots of examples in the EXAMPLES section of the man page • http: //www. tcpdump. org/tcpdump_man. html 23
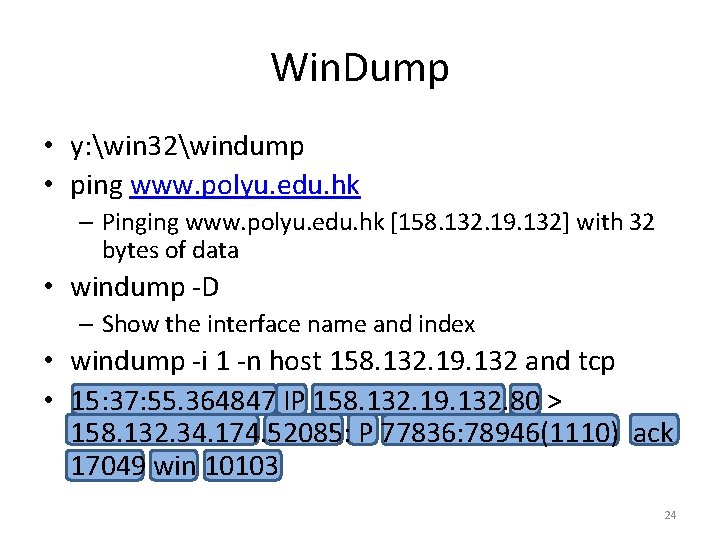
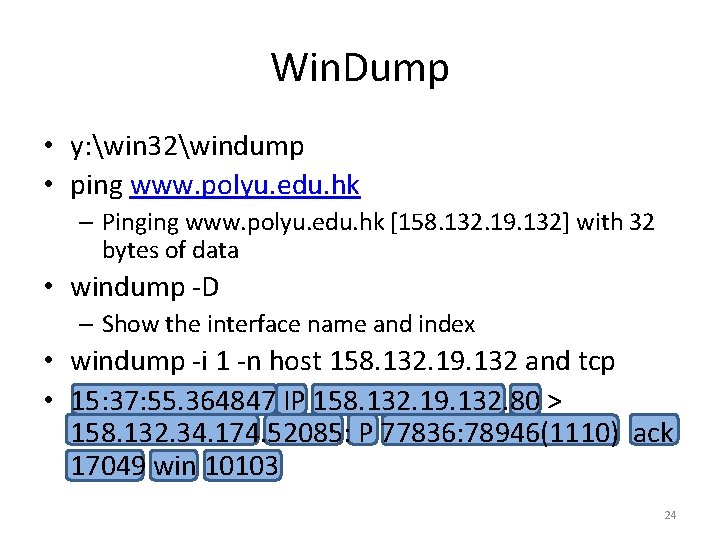
Win. Dump • y: win 32windump • ping www. polyu. edu. hk – Pinging www. polyu. edu. hk [158. 132. 19. 132] with 32 bytes of data • windump -D – Show the interface name and index • windump -i 1 -n host 158. 132. 19. 132 and tcp • 15: 37: 55. 364847 IP 158. 132. 19. 132. 80 > 158. 132. 34. 174. 52085: P 77836: 78946(1110) ack 17049 win 10103 24
Content • TCP/IP Networking Review • Packet Capture • Protocol Analysis 25
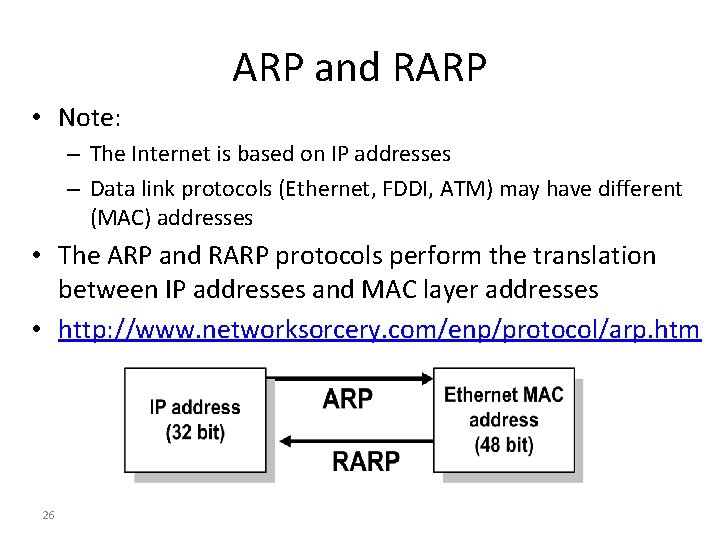
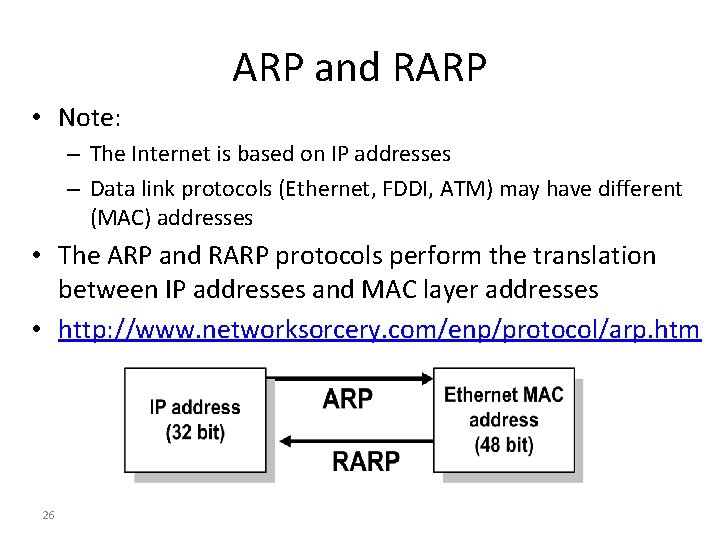
ARP and RARP • Note: – The Internet is based on IP addresses – Data link protocols (Ethernet, FDDI, ATM) may have different (MAC) addresses • The ARP and RARP protocols perform the translation between IP addresses and MAC layer addresses • http: //www. networksorcery. com/enp/protocol/arp. htm 26
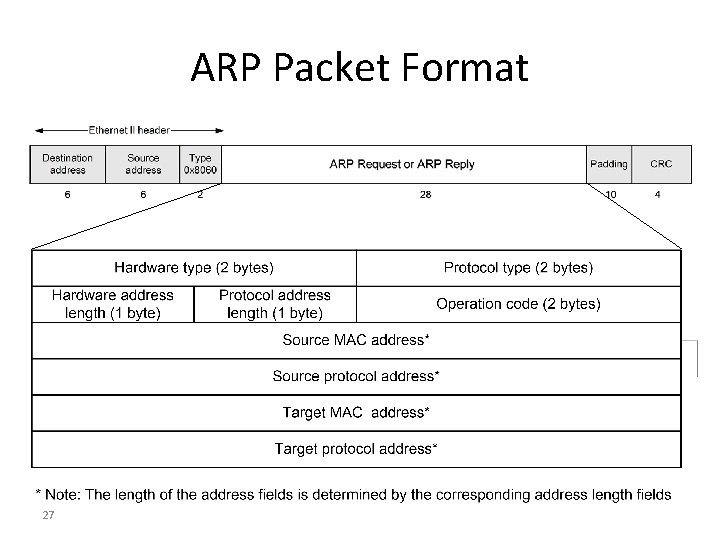
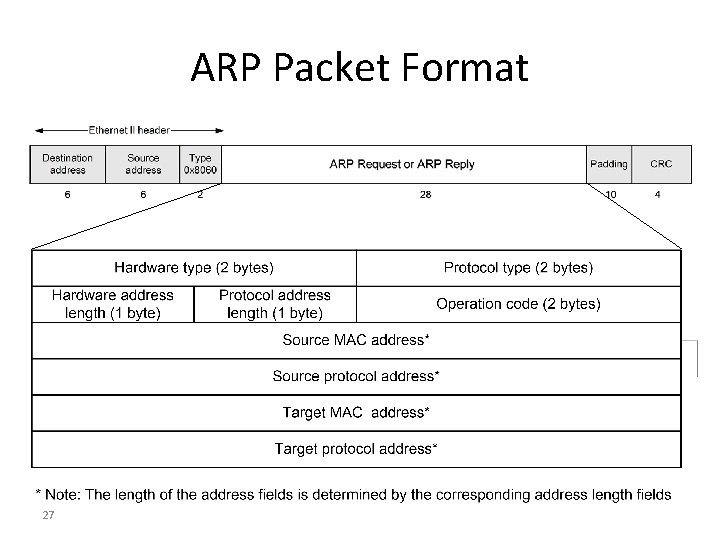
ARP Packet Format 27
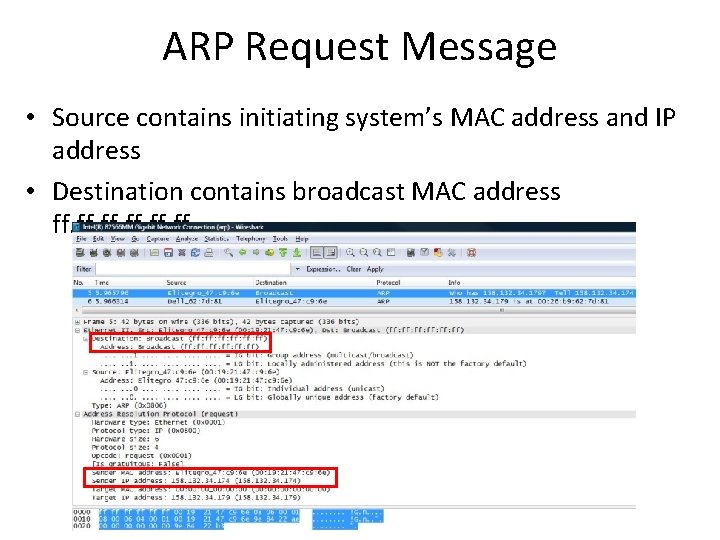
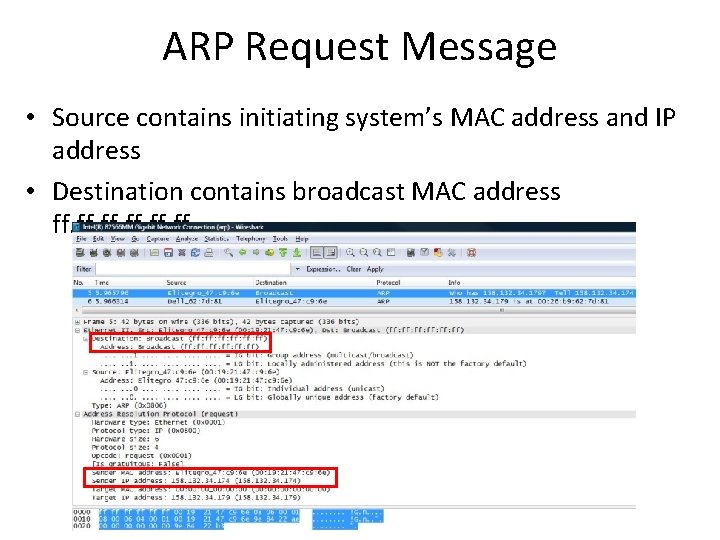
ARP Request Message • Source contains initiating system’s MAC address and IP address • Destination contains broadcast MAC address ff. ff
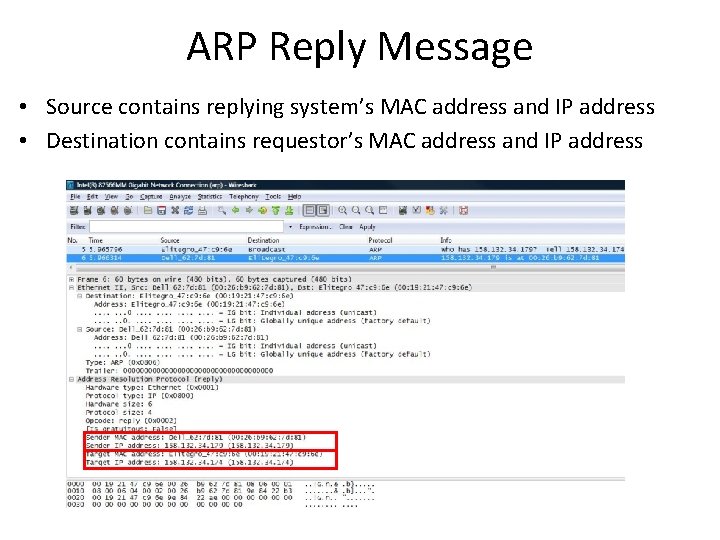
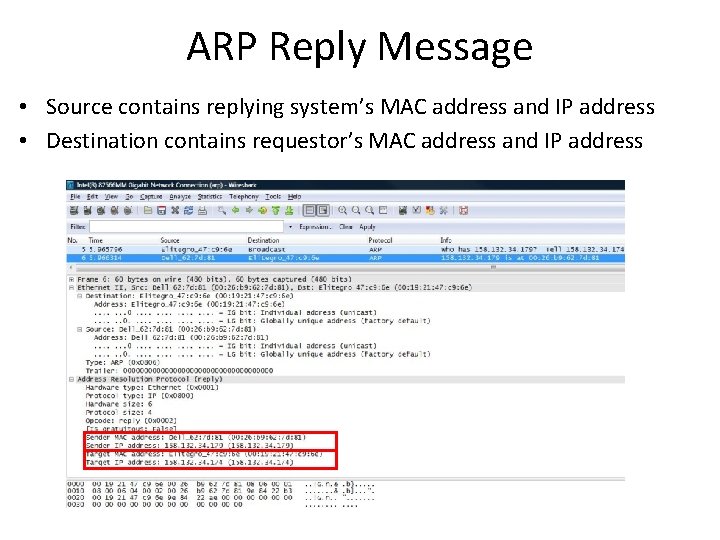
ARP Reply Message • Source contains replying system’s MAC address and IP address • Destination contains requestor’s MAC address and IP address
Domain names and IP addresses • People prefer to use easy-to-remember names instead of IP addresses • Domain names are alphanumeric names for IP addresses e. g. , www. polyu. edu. hk, www. google. com, ietf. org • The domain name system (DNS) is an Internetwide distributed database that translates between domain names and IP addresses
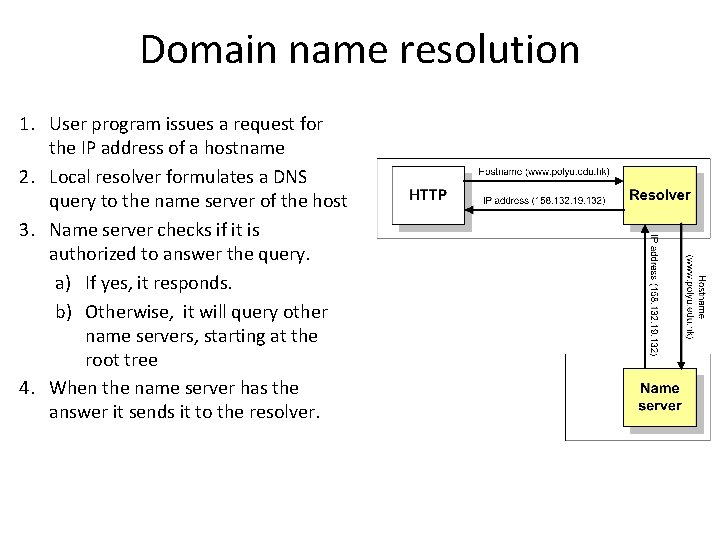
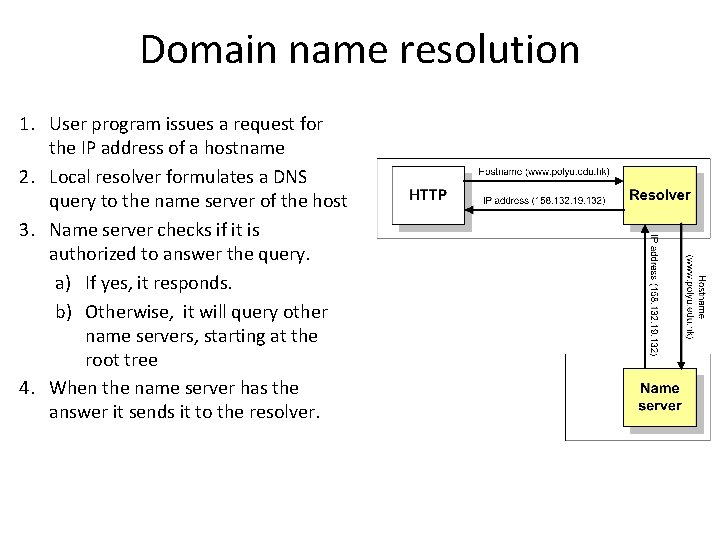
Domain name resolution 1. User program issues a request for the IP address of a hostname 2. Local resolver formulates a DNS query to the name server of the host 3. Name server checks if it is authorized to answer the query. a) If yes, it responds. b) Otherwise, it will query other name servers, starting at the root tree 4. When the name server has the answer it sends it to the resolver.
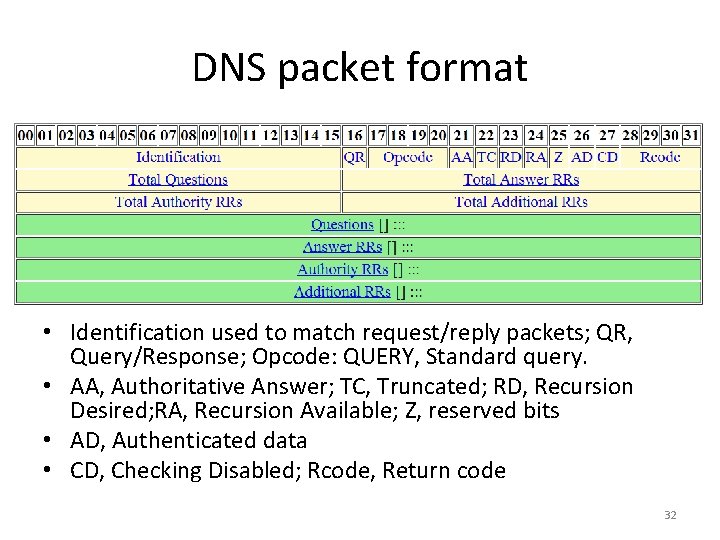
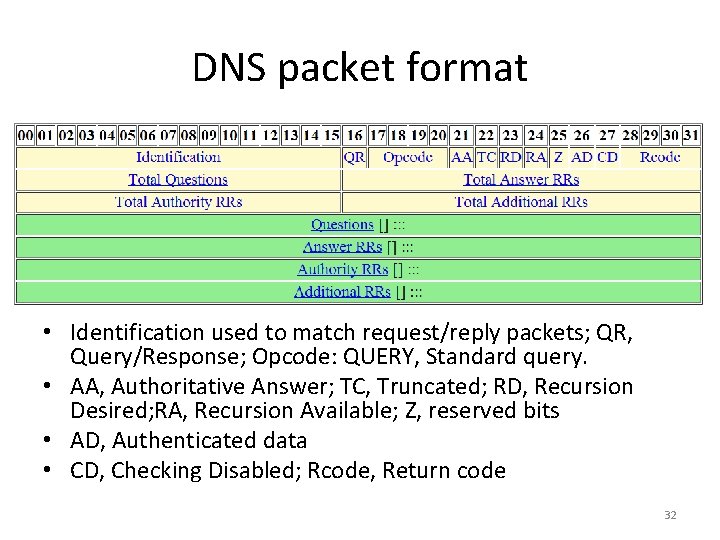
DNS packet format • Identification used to match request/reply packets; QR, Query/Response; Opcode: QUERY, Standard query. • AA, Authoritative Answer; TC, Truncated; RD, Recursion Desired; RA, Recursion Available; Z, reserved bits • AD, Authenticated data • CD, Checking Disabled; Rcode, Return code 32
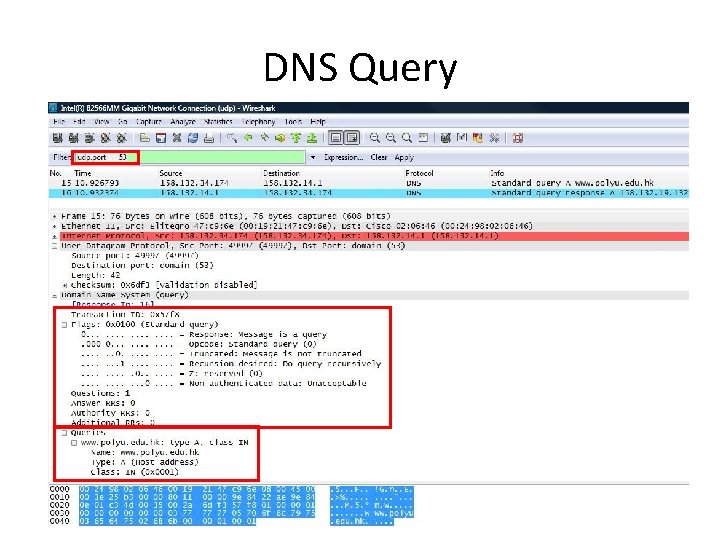
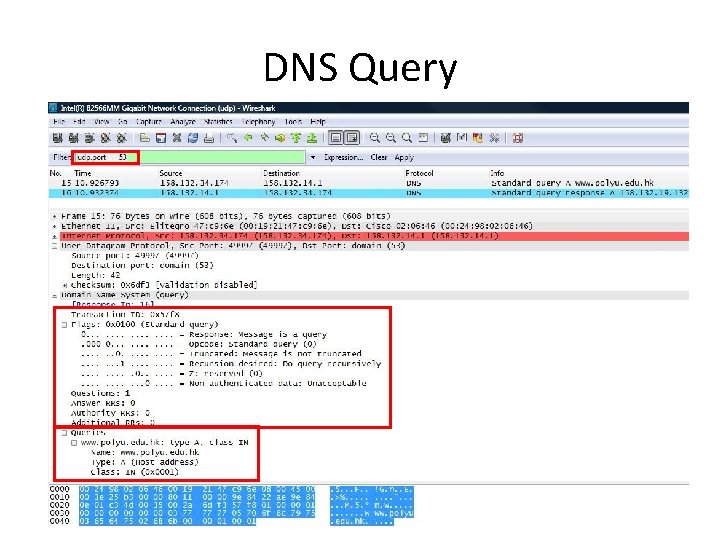
DNS Query 33
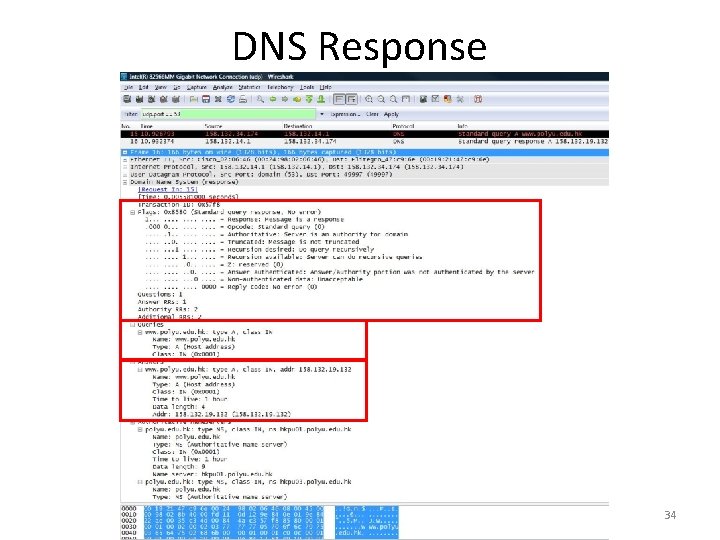
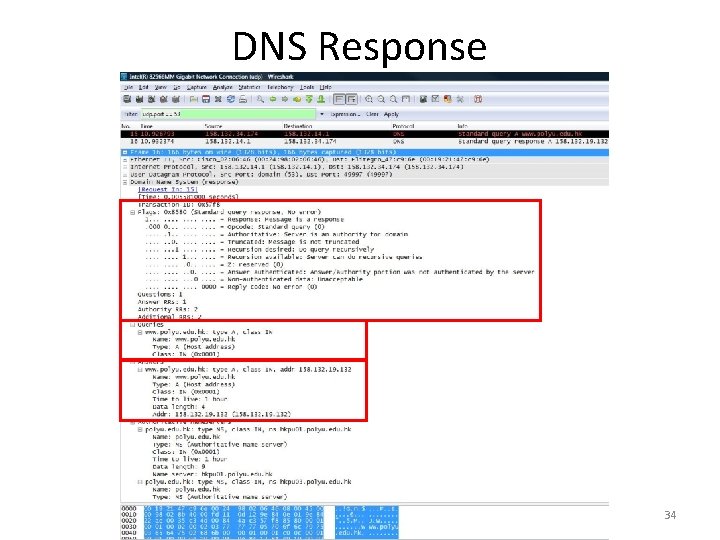
DNS Response 34
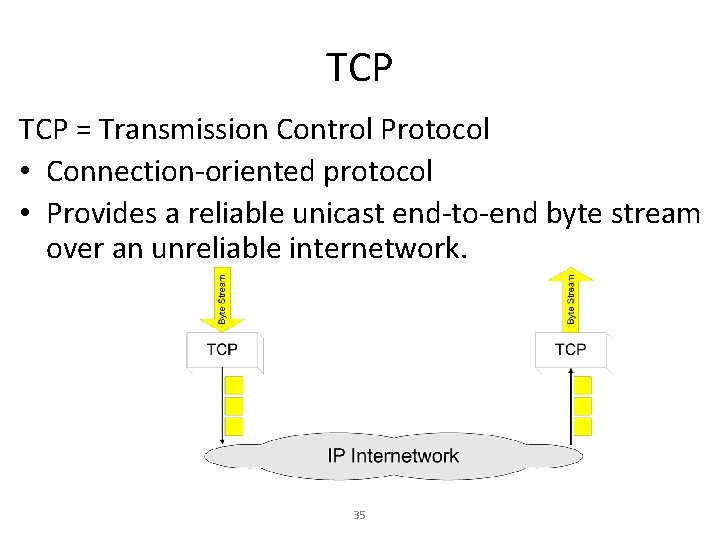
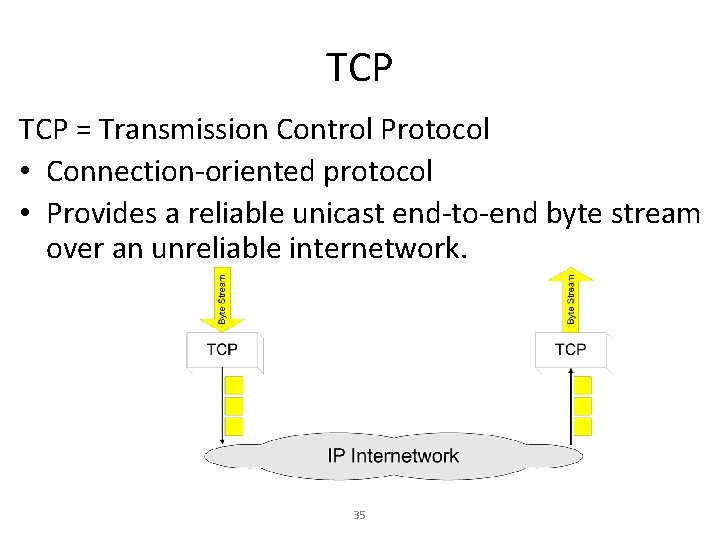
TCP = Transmission Control Protocol • Connection-oriented protocol • Provides a reliable unicast end-to-end byte stream over an unreliable internetwork. 35
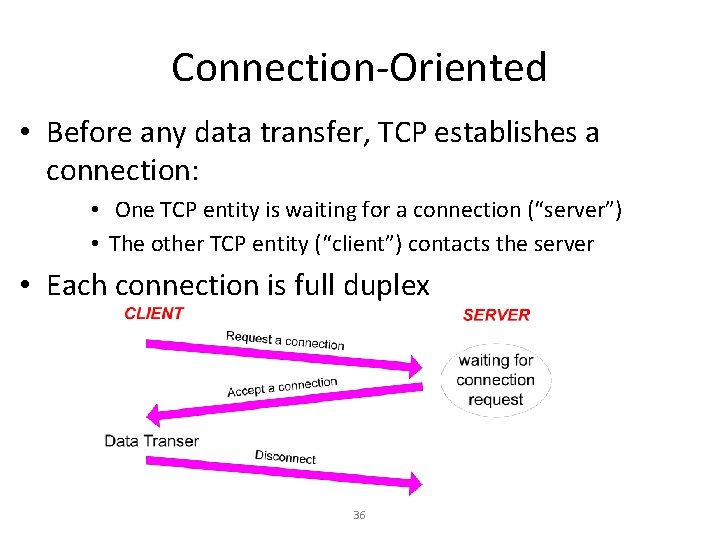
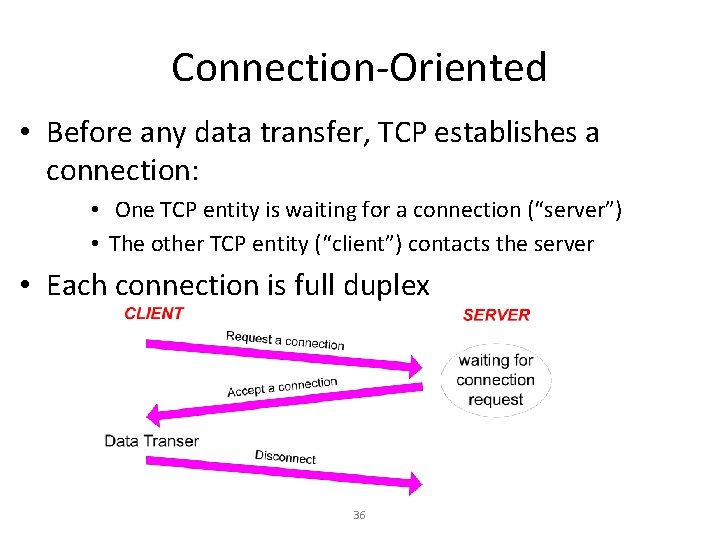
Connection-Oriented • Before any data transfer, TCP establishes a connection: • One TCP entity is waiting for a connection (“server”) • The other TCP entity (“client”) contacts the server • Each connection is full duplex 36
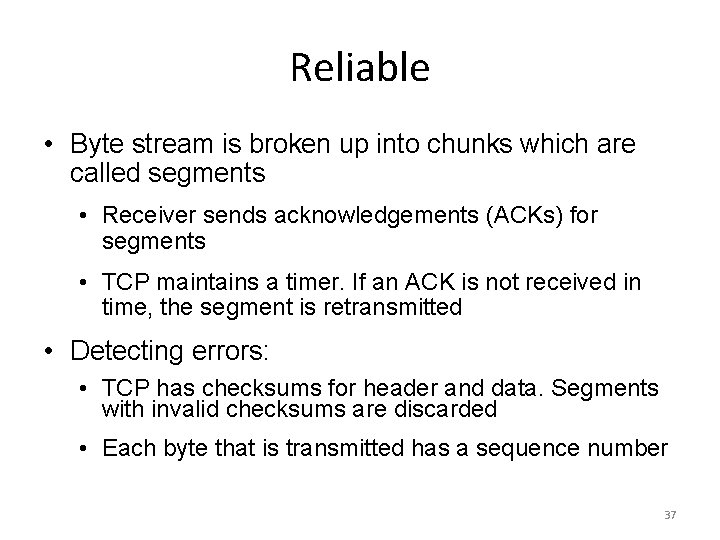
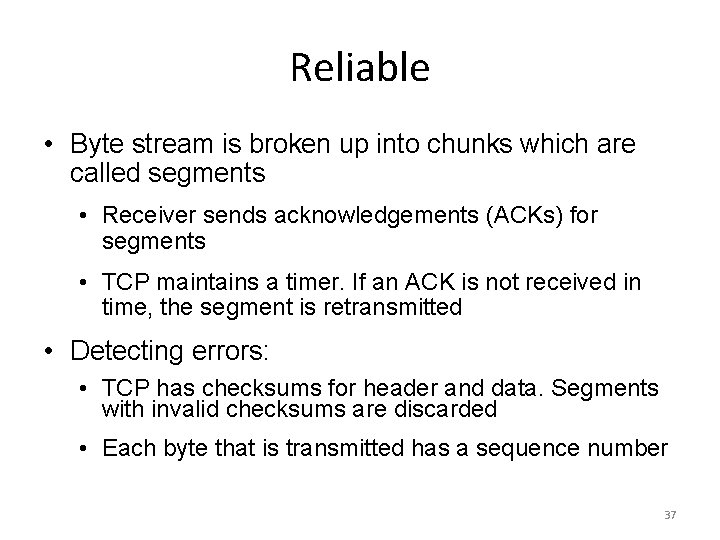
Reliable • Byte stream is broken up into chunks which are called segments • Receiver sends acknowledgements (ACKs) for segments • TCP maintains a timer. If an ACK is not received in time, the segment is retransmitted • Detecting errors: • TCP has checksums for header and data. Segments with invalid checksums are discarded • Each byte that is transmitted has a sequence number 37
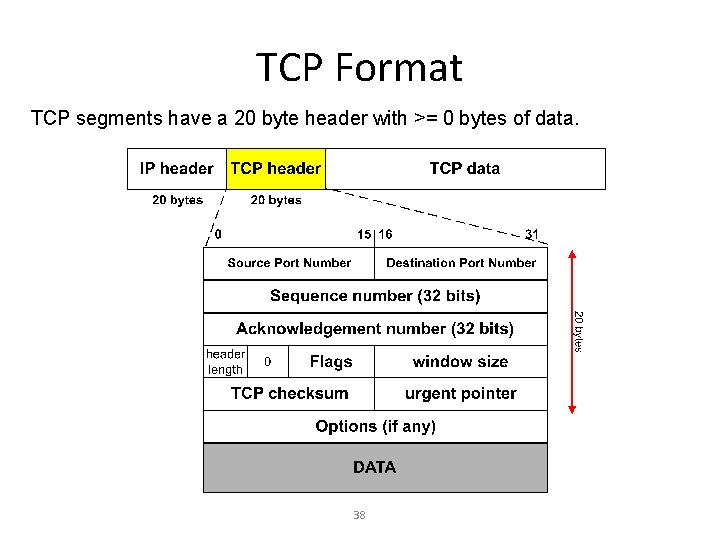
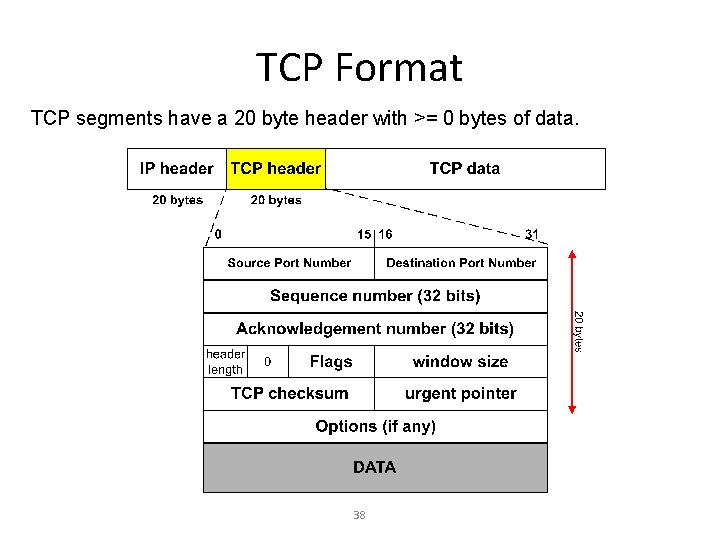
TCP Format TCP segments have a 20 byte header with >= 0 bytes of data. 38
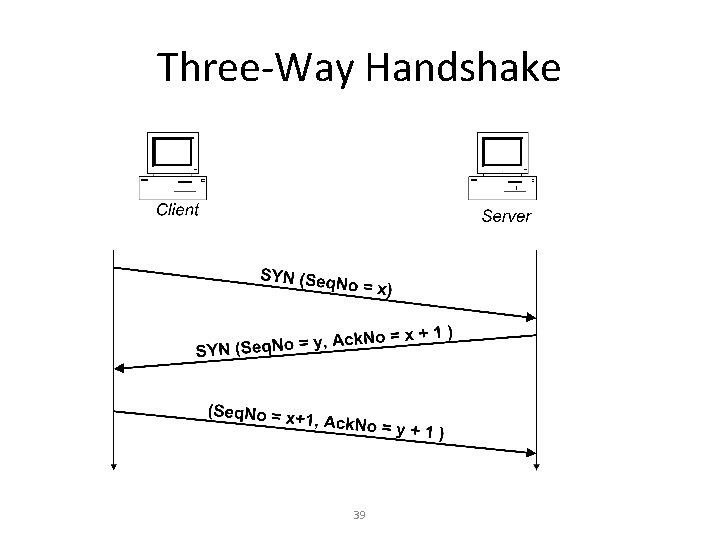
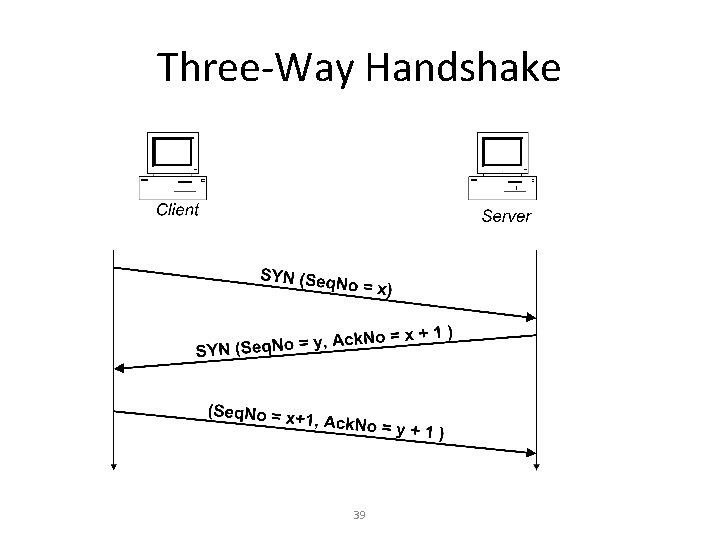
Three-Way Handshake 39
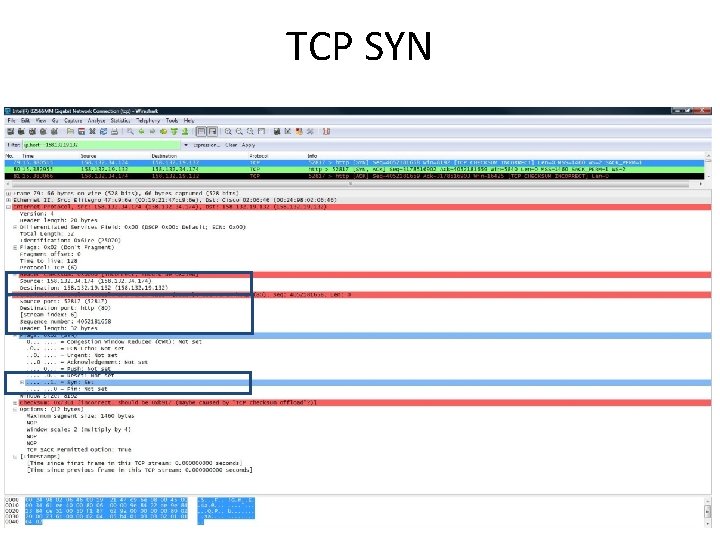
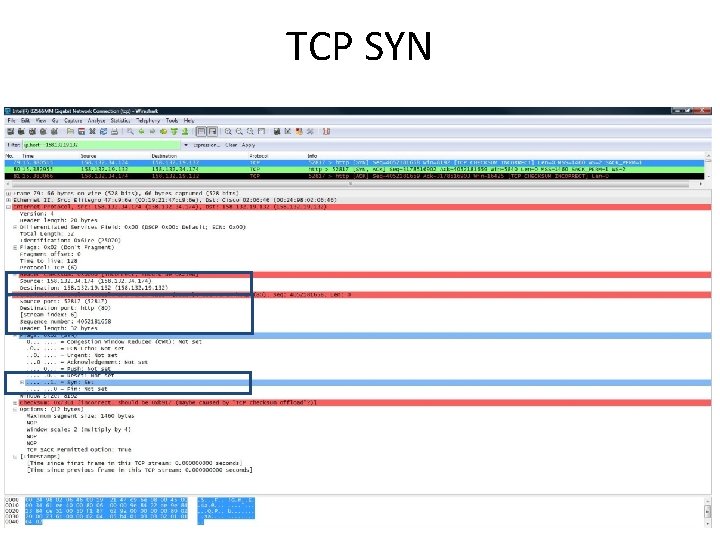
TCP SYN 40
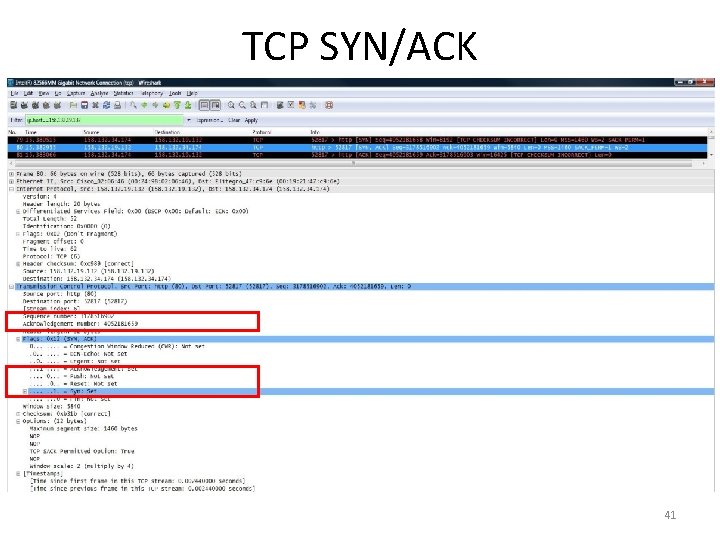
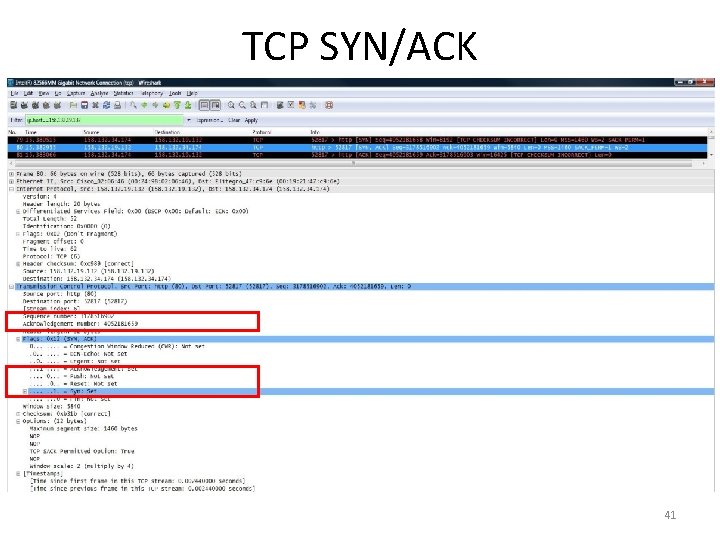
TCP SYN/ACK 41
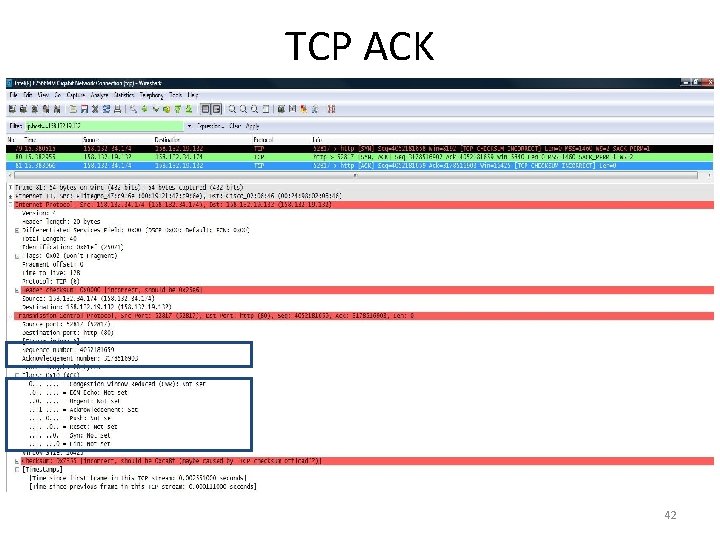
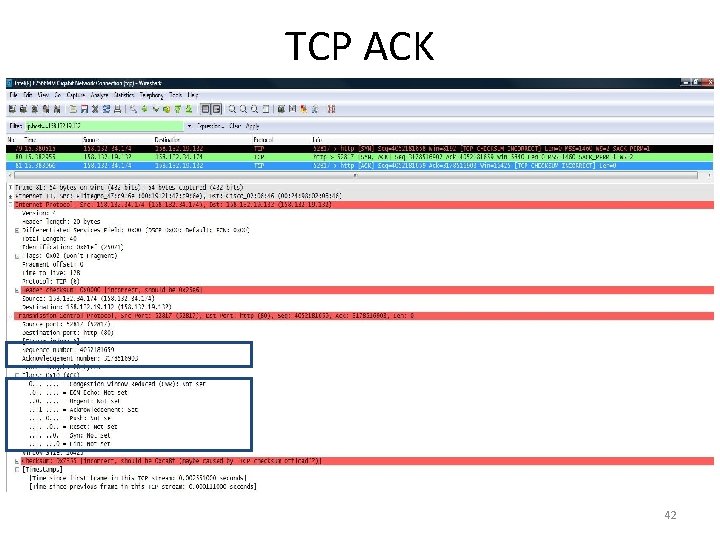
TCP ACK 42
HTTP Hypertext Transfer Protocol is a network protocol used to deliver virtually all files and other data (collectively called resources) on the World Wide Web. This is a request and retrieve function of the server. This includes: Text files, graphic images, sound, video, and other multi-media files. 43
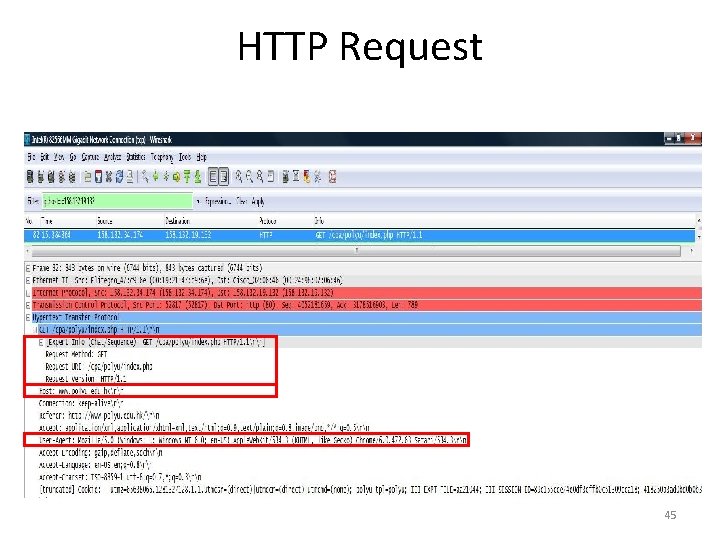
HTTP Request Methods There are 3 open-ended methods that are frequently used to request information: • GET – used to ask for specific document and is the simplest form of requesting information (URL access will not change the state of database) • HEAD – used to ask for information about a document (very fast because less data is required) • POST – used when the service associated with the processing of the form has side effects (URL access will cause change in database). Example: Ebay, Amazon 44
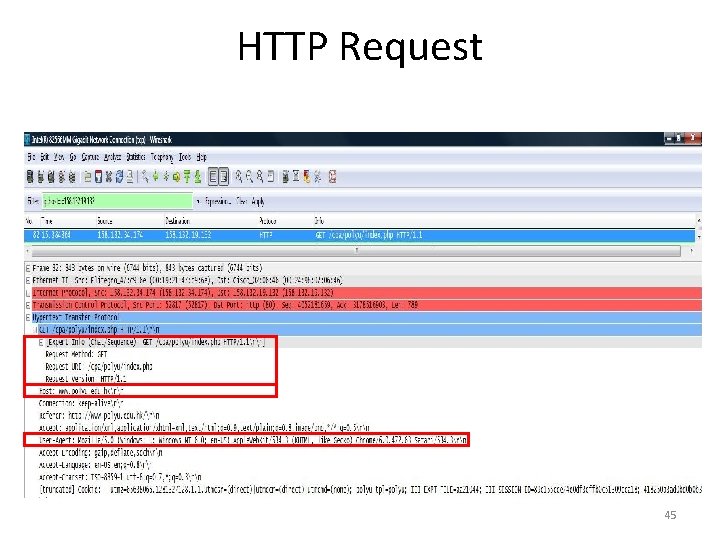
HTTP Request 45
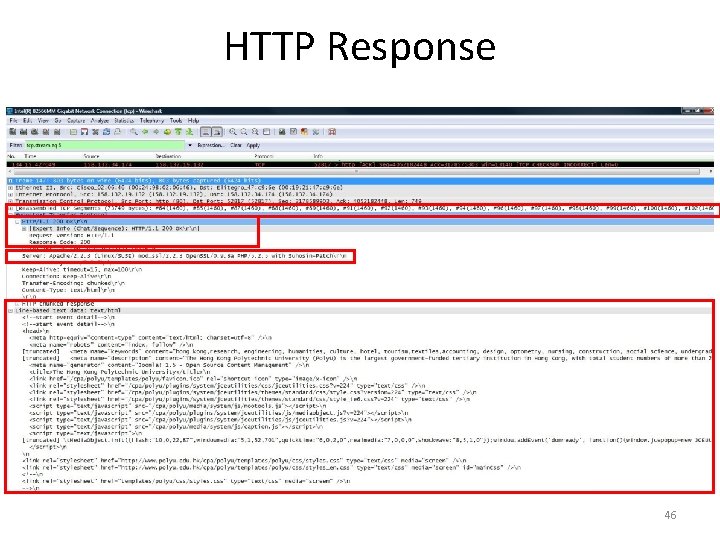
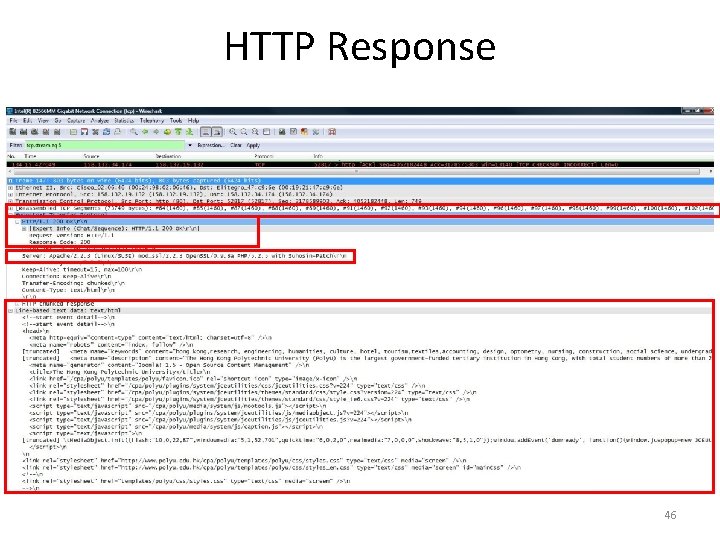
HTTP Response 46
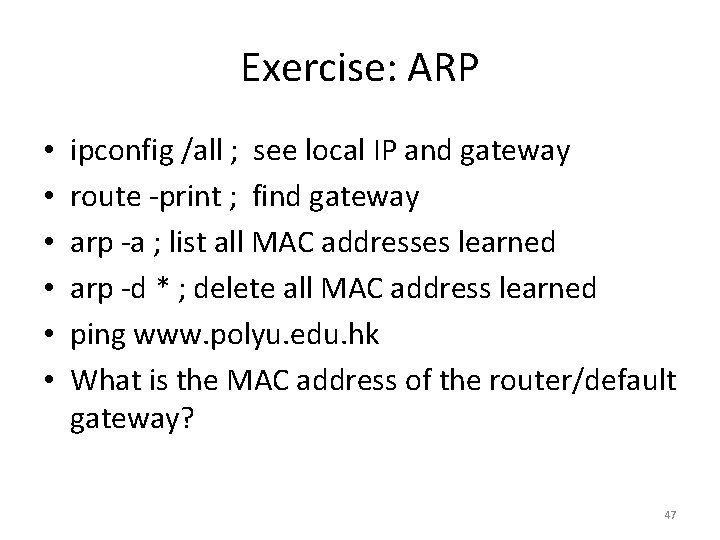
Exercise: ARP • • • ipconfig /all ; see local IP and gateway route -print ; find gateway arp -a ; list all MAC addresses learned arp -d * ; delete all MAC address learned ping www. polyu. edu. hk What is the MAC address of the router/default gateway? 47
Hints • If the default gateway/router’s MAC address is not in the cache, the host will send ARP to ask for it. • The default gateway’s IP address is preconfigured or learnt through the DHCP protocol. 48
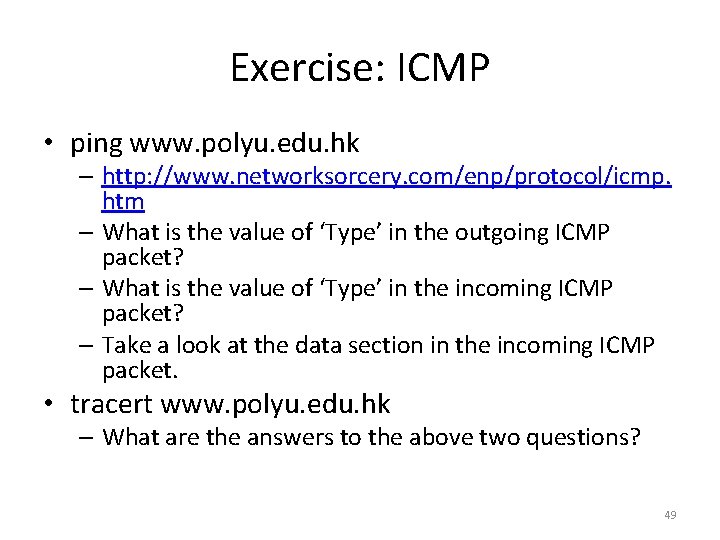
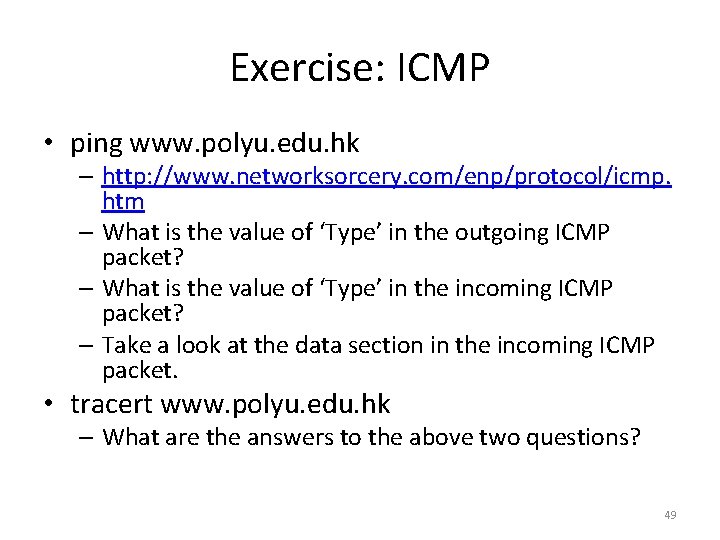
Exercise: ICMP • ping www. polyu. edu. hk – http: //www. networksorcery. com/enp/protocol/icmp. htm – What is the value of ‘Type’ in the outgoing ICMP packet? – What is the value of ‘Type’ in the incoming ICMP packet? – Take a look at the data section in the incoming ICMP packet. • tracert www. polyu. edu. hk – What are the answers to the above two questions? 49
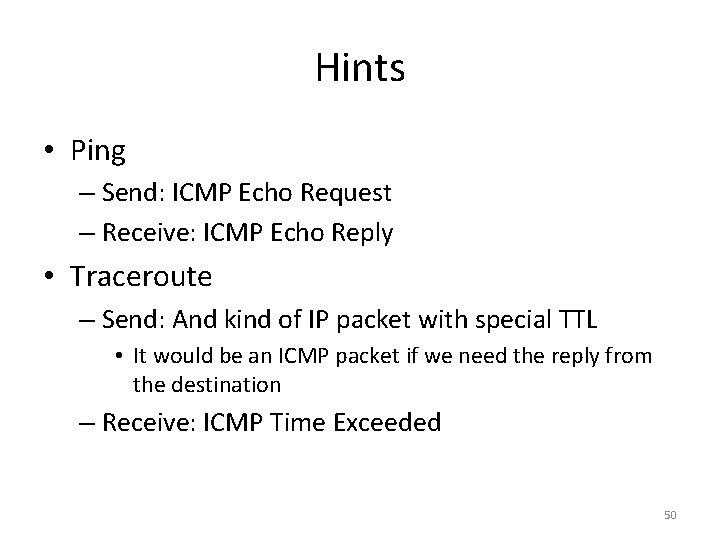
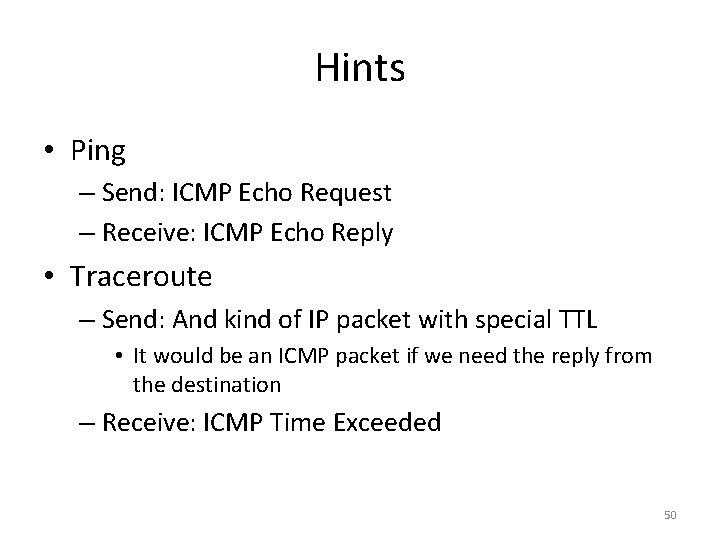
Hints • Ping – Send: ICMP Echo Request – Receive: ICMP Echo Reply • Traceroute – Send: And kind of IP packet with special TTL • It would be an ICMP packet if we need the reply from the destination – Receive: ICMP Time Exceeded 50
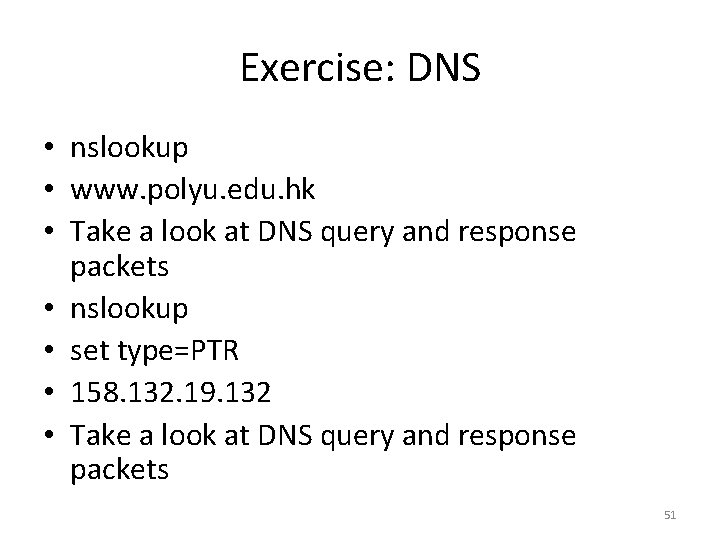
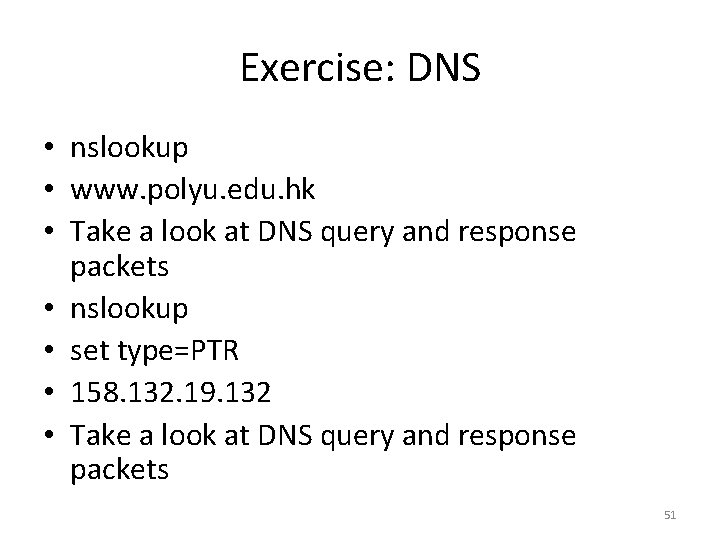
Exercise: DNS • nslookup • www. polyu. edu. hk • Take a look at DNS query and response packets • nslookup • set type=PTR • 158. 132. 19. 132 • Take a look at DNS query and response packets 51
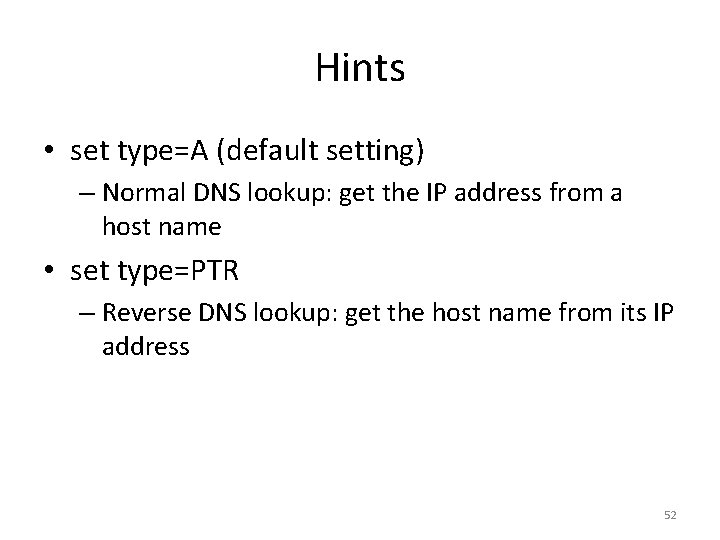
Hints • set type=A (default setting) – Normal DNS lookup: get the IP address from a host name • set type=PTR – Reverse DNS lookup: get the host name from its IP address 52
Exercise: HTTP/TCP • Use browser to visit www. polyu. edu. hk • Take a look at – TCP’s three-way handshake – sequence numbers in packets from the server and the acknowledgement number in packets from the client – HTTP header in the packets from the server 53
Exercise: Trace analysis • Real trace from a Vo. IP hacking demo – https: //honeynet. org/files/Forensic_challenge_4_0. pcap • Analyze the trace using Wireshark and answer the following questions – Which 4 protocols are involved in the pcap? – Which codec does the RTP stream use? – How did the attacker gain access to the server? – Where is the hacked server? • Tips: look into the payload 54
Hints • 4 Protocols: HTTP, RTCP, SIP • RTP uses G. 7111 PCMU coding • Default user name/password – Authorization: Basic b. WFpbn. Q 6 c. GFzc 3 dvcm. Q= • The city is DISTRITO FEDERAL MEXICO – Hear it • Telephony -> RTP -> Stream analysis – Public IP: 132. 248. 255. 82 in an HTTP response • Follow HTTP connections • Look into the HTTP responses • Use Geolocation websites to locate the city 55
Reference* • http: //www. cs. virginia. edu/~cs 458/ • http: //www. eecs. berkeley. edu/~jortiz/courses/ee 122/presentations/W ireshark. ppt • http: //www. cis. udel. edu/~amer/856/wireshark. 08 f. ppt • http: //www. blackhat. com/presentations/bh-usa-01/Mike. Beekey/bhusa-01 -Mike-Beekey. ppt • http: //classes. bus. oregonstate. edu/winter-06/ba 471/marshall/Special. Topics/http. ppt • http: //www. wildpackets. com/elements/misc/WP_encapsulation_chart. pdf • http: //sectools. org/sniffers. html • Computer Networking: A Top-down Approach Featuring the Internet • https: //honeynet. org/challenges/2010_4_voip_traditional_cn • * Some slides were taken from the above sources and the pcap file was from Forensic Challenge 2010 - Vo. IP 56