OWASP University Challenge OWASP App SecUSA OWASP September
OWASP University. Challenge OWASP App. Sec-USA OWASP September 2011 Copyright © The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the OWASP License. The OWASP Foundation http: //www. owasp. org
The OWASP University Challenge Attack Defence OWASP
The OWASP University Challenge 3 Teams: • Dakota State University • University of North Carolina at Charlotte • St. Cloud State University OWASP
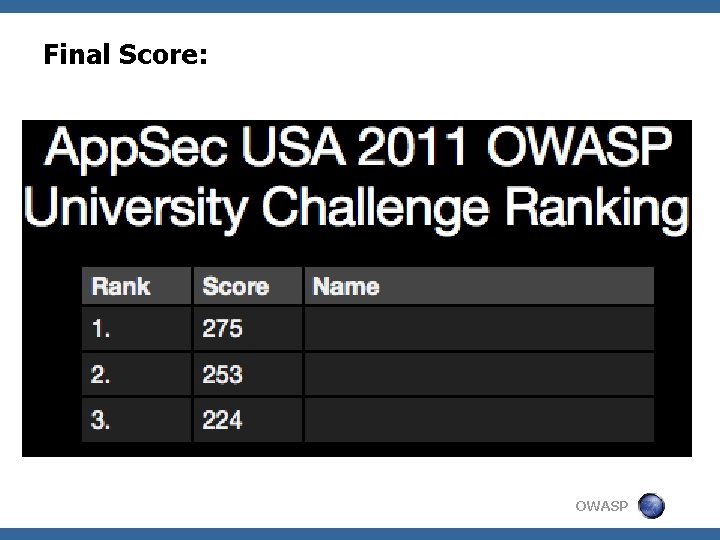
Final Score: OWASP
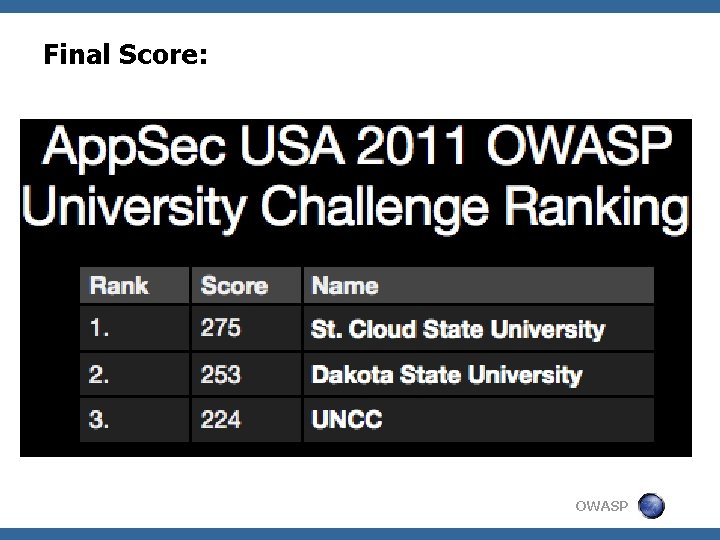
Final Score: OWASP
Winner of the Attack part: St. Cloud State University Joshua Platz Jake Soenneker OWASP
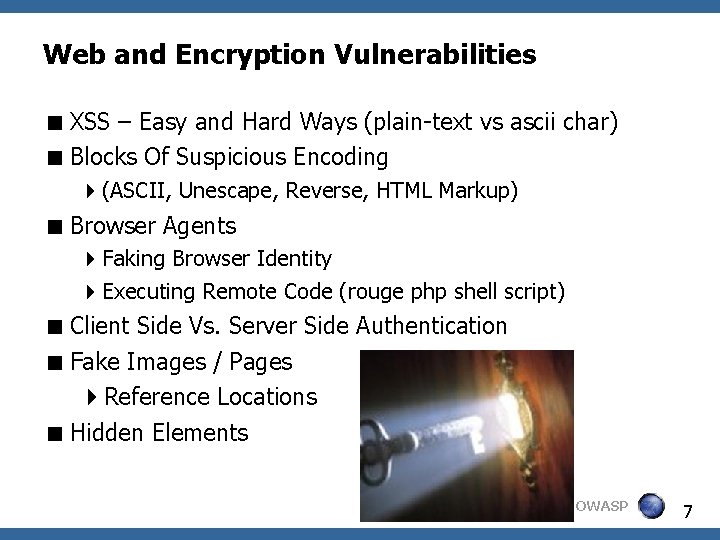
Web and Encryption Vulnerabilities XSS – Easy and Hard Ways (plain-text vs ascii char) Blocks Of Suspicious Encoding (ASCII, Unescape, Reverse, HTML Markup) Browser Agents Faking Browser Identity Executing Remote Code (rouge php shell script) Client Side Vs. Server Side Authentication Fake Images / Pages Reference Locations Hidden Elements OWASP 7
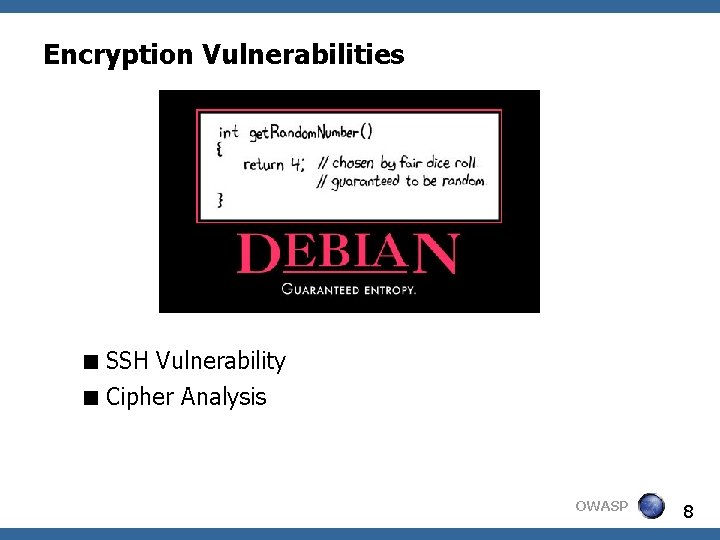
Encryption Vulnerabilities SSH Vulnerability Cipher Analysis OWASP 8
Winner of the Defence part: University of North Carolina at Charlotte Joshua Schroeder Joel Kerr Chris Burke OWASP
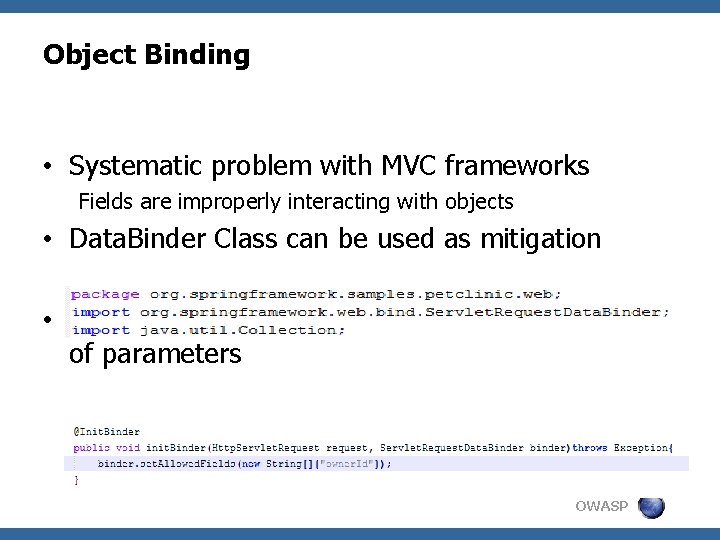
Object Binding • Systematic problem with MVC frameworks Fields are improperly interacting with objects • Data. Binder Class can be used as mitigation • set. Allowed. Fields Property allows whitelisting of parameters UNC Charlotte OWASP
Web Application Firewall • Mod_JK • Linking Apache to Tomcat • Mod Security • Identifies and denies XSS and SQL injection attacks UNC Charlotte OWASP 1 1
Input Validation • Identified problems with ASIDE • Static Analysis Tool • Provides mitigation suggestions • Defense against XSS UNC Charlotte OWASP 1 2
- Slides: 12