OWASP Education Computer based training The OWASP Foundation
OWASP Education Computer based training The OWASP Foundation http: //www. owasp. org 2011 CWE/SANS Top 25 with OWASP Top 10 and PCI DSS V 2 Mapping Nishi Kumar Keith Turpin IT Architect Specialist Chair, Software Security Forum at FIS OWASP CBT Project Lead OWASP Global Projects Committee The Boeing Company Application Security Assessments Lead OWASP Secure Coding Practices Lead OWASP Global Projects Committee Nishi. Kumar@owasp. org keith. turpin@owasp. org
Objectives Provide an overview of the 2011 CWE/SANS Top 25 Discuss mapping relationships between CWE/SANS Top 25, OWASP Top 10 for 2010 and PCI DSS V 2 Understand the CWE/SANS Top 25 weaknesses and how to remediate them 2
Organizations MITRE - http: //www. mitre. org/ The MITRE Corporation is a not-for-profit organization that manages several Federally Funded Research and Development Centers. Mitre currently runs various IT security projects including the Common Weakness Enumeration (CWE) and it is the official source for the CWE/SANS Top 25 Most Dangerous Software Errors. CWE Database - http: //cwe. mitre. org/ SANS - http: //www. sans. org The Sys. Admin, Audit, Network, Security (SANS) Institute operates as a commercial research and education company. SANS is well known for its Internet Storm Center, its comprehensive list of computing security training programs and its work with Mitre on the CWE/SANS Top 25 Most Dangerous Software Errors. 3
Selection and Ranking Builds on the original 2009 and 2010 versions Methodology - Qualitative rather than quantitative Factors in ranking: Prevalence Importance Likelihood of exploit Initially started with 41 candidate weaknesses 4
![2011 CWE/SANS Top 25 Rank ID Name [1] CWE-89 Improper Neutralization of Special Elements 2011 CWE/SANS Top 25 Rank ID Name [1] CWE-89 Improper Neutralization of Special Elements](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-5.jpg)
2011 CWE/SANS Top 25 Rank ID Name [1] CWE-89 Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') [2] CWE-78 Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') [3] CWE-120 Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') CWE-79 Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') CWE-306 Missing Authentication for Critical Function CWE-862 Missing Authorization CWE-798 Use of Hard-coded Credentials CWE-311 Missing Encryption of Sensitive Data CWE-434 Unrestricted Upload of File with Dangerous Type CWE-807 Reliance on Untrusted Inputs in a Security Decision CWE-250 Execution with Unnecessary Privileges CWE-352 Cross-Site Request Forgery ('CSRF') [4] [5] [6] [7] [8] [9] [10] [11] [12] 5
![2011 CWE/SANS Top 25 Rank ID Name [13] CWE-22 [14] [15] [16] [17] [18] 2011 CWE/SANS Top 25 Rank ID Name [13] CWE-22 [14] [15] [16] [17] [18]](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-6.jpg)
2011 CWE/SANS Top 25 Rank ID Name [13] CWE-22 [14] [15] [16] [17] [18] [19] [20] [21] CWE-494 CWE-863 CWE-829 CWE-732 CWE-676 CWE-327 CWE-131 CWE-307 Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') Download of Code Without Integrity Check Incorrect Authorization Inclusion of Functionality from Untrusted Control Sphere Incorrect Permission Assignment for Critical Resource Use of Potentially Dangerous Function Use of a Broken or Risky Cryptographic Algorithm Incorrect Calculation of Buffer Size Improper Restriction of Excessive Authentication Attempts [22] [23] [24] [25] CWE-601 CWE-134 CWE-190 CWE-759 URL Redirection to Untrusted Site ('Open Redirect') Uncontrolled Format String Integer Overflow or Wraparound Use of a One-Way Hash without a Salt 6
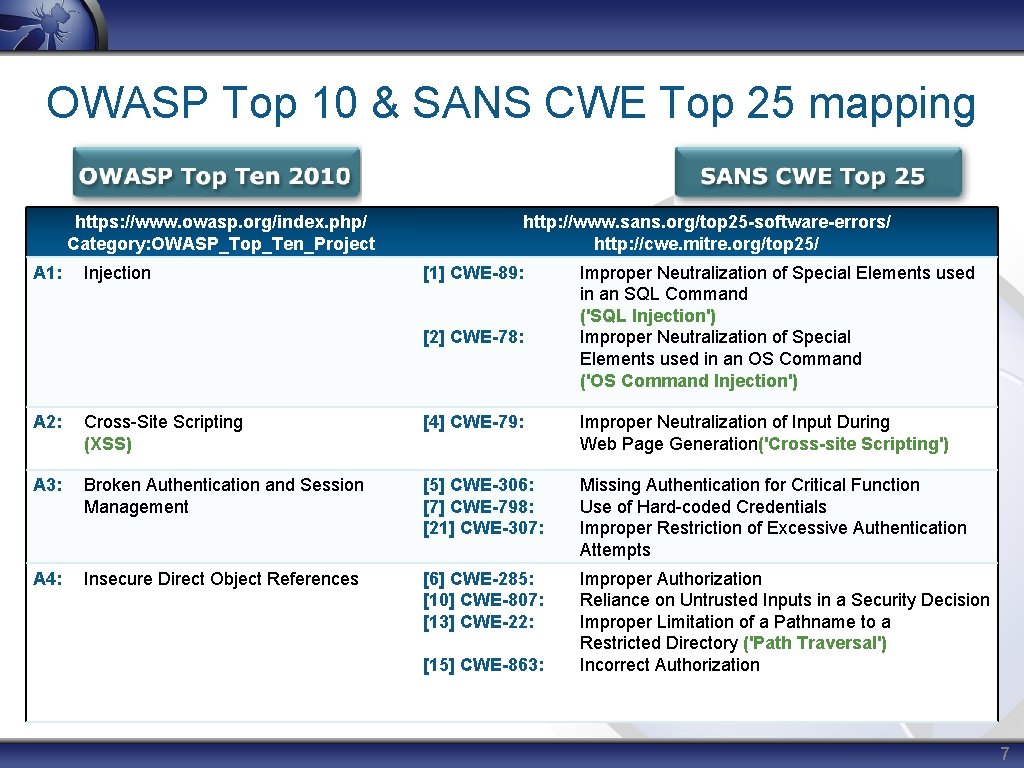
OWASP Top 10 & SANS CWE Top 25 mapping https: //www. owasp. org/index. php/ Category: OWASP_Top_Ten_Project A 1: Injection http: //www. sans. org/top 25 -software-errors/ http: //cwe. mitre. org/top 25/ [1] CWE-89: [2] CWE-78: Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') A 2: Cross-Site Scripting (XSS) [4] CWE-79: Improper Neutralization of Input During Web Page Generation('Cross-site Scripting') A 3: Broken Authentication and Session Management [5] CWE-306: [7] CWE-798: [21] CWE-307: Missing Authentication for Critical Function Use of Hard-coded Credentials Improper Restriction of Excessive Authentication Attempts A 4: Insecure Direct Object References [6] CWE-285: [10] CWE-807: [13] CWE-22: Improper Authorization Reliance on Untrusted Inputs in a Security Decision Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') Incorrect Authorization [15] CWE-863: 7
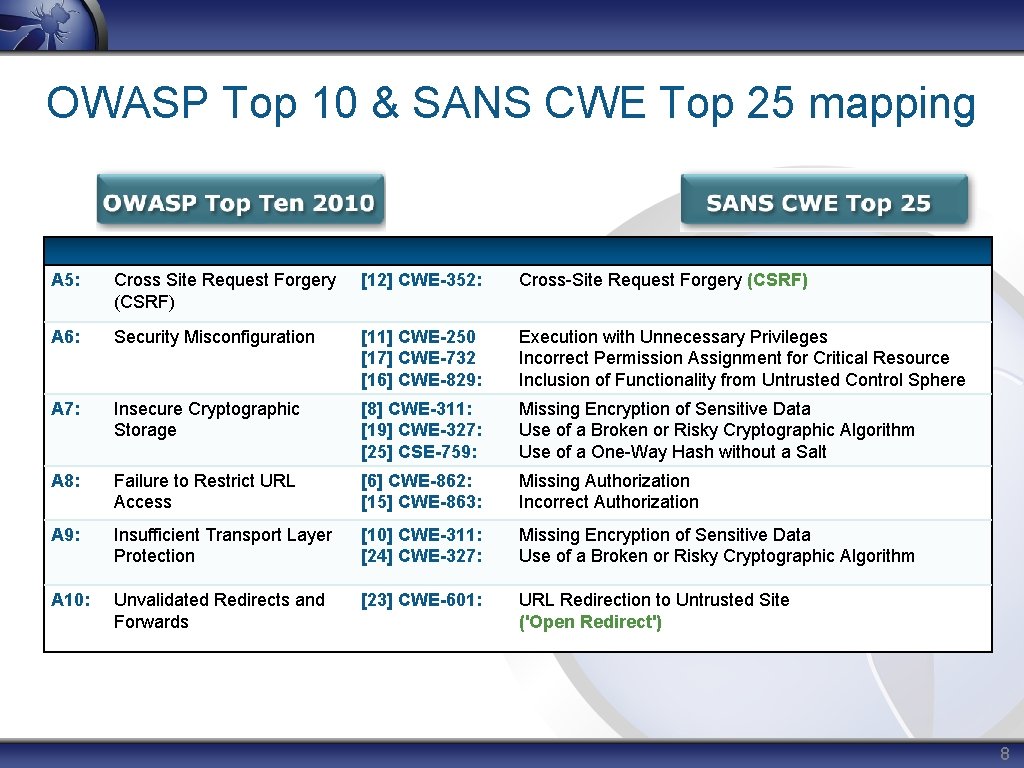
OWASP Top 10 & SANS CWE Top 25 mapping A 5: Cross Site Request Forgery (CSRF) [12] CWE-352: Cross-Site Request Forgery (CSRF) A 6: Security Misconfiguration [11] CWE-250 [17] CWE-732 [16] CWE-829: Execution with Unnecessary Privileges Incorrect Permission Assignment for Critical Resource Inclusion of Functionality from Untrusted Control Sphere A 7: Insecure Cryptographic Storage [8] CWE-311: [19] CWE-327: [25] CSE-759: Missing Encryption of Sensitive Data Use of a Broken or Risky Cryptographic Algorithm Use of a One-Way Hash without a Salt A 8: Failure to Restrict URL Access [6] CWE-862: [15] CWE-863: Missing Authorization Incorrect Authorization A 9: Insufficient Transport Layer Protection [10] CWE-311: [24] CWE-327: Missing Encryption of Sensitive Data Use of a Broken or Risky Cryptographic Algorithm A 10: Unvalidated Redirects and Forwards [23] CWE-601: URL Redirection to Untrusted Site ('Open Redirect') 8
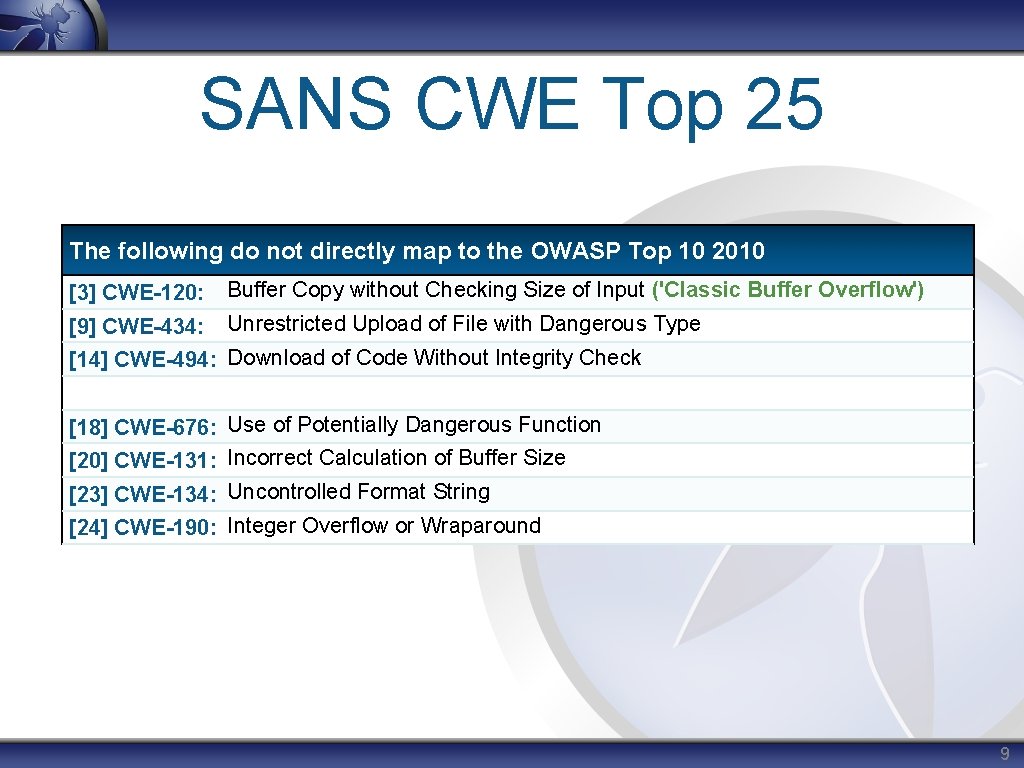
SANS CWE Top 25 The following do not directly map to the OWASP Top 10 2010 [3] CWE-120: Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') [9] CWE-434: Unrestricted Upload of File with Dangerous Type [14] CWE-494: Download of Code Without Integrity Check [18] CWE-676: Use of Potentially Dangerous Function [20] CWE-131: Incorrect Calculation of Buffer Size [23] CWE-134: Uncontrolled Format String [24] CWE-190: Integer Overflow or Wraparound 9
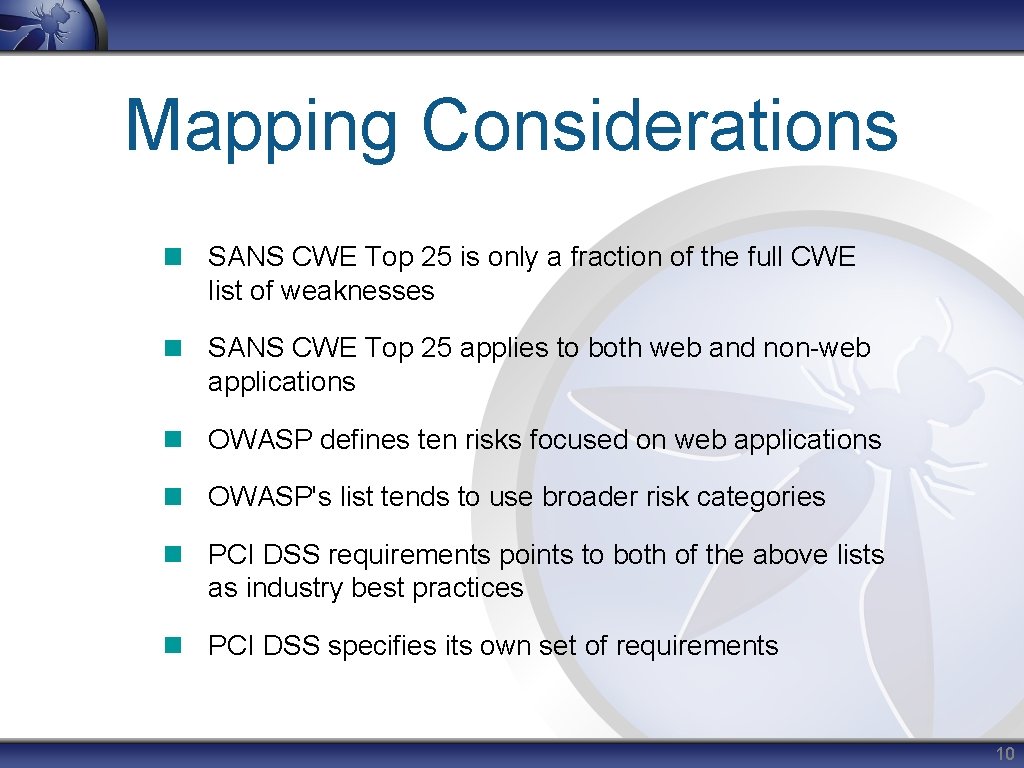
Mapping Considerations SANS CWE Top 25 is only a fraction of the full CWE list of weaknesses SANS CWE Top 25 applies to both web and non-web applications OWASP defines ten risks focused on web applications OWASP's list tends to use broader risk categories PCI DSS requirements points to both of the above lists as industry best practices PCI DSS specifies its own set of requirements 10
![[1] CWE-89 Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') [1] CWE-89 Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection')](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-11.jpg)
[1] CWE-89 Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') OWASP Top 10 and PCI Mapping • OWASP 2010: • PCI-DSS V 2: A 1 Injection 6. 5. 1 Injection flaws, particularly SQL injection. General Description • The software constructs a dynamic SQL statement using input that has not been properly neutralized • Example of dynamic query modification: • String query = "SELECT * FROM accounts WHERE cust. ID='" + request. get. Parameter("id") +"'"; • The attacker modifies the ‘id’ parameter in their browser to send: ' or '1'='1 • This changes the meaning of the query, because 1=1 is always true, to return all the records from the accounts database, instead of only the intended customer’s • http: //example. com/app/account. View? id=' or '1'='1 11
![[1] CWE-89 Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') [1] CWE-89 Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection')](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-12.jpg)
[1] CWE-89 Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') Potential Impacts • Unauthorized access to data, authentication bypass, compromise of the host OS, use of database utilities to breach a perimeter (when the DB is deployed along network boundaries) Common Mitigations • Use a safe API to avoid using the interpreter entirely or to provide parameterized interface • Use strongly typed parameterized queries String sql. String = "select * from db_user where username=? … Prepared. Statement stmt = connection. prepare. Statement(sql. String); stmt. set. String (1, username); … • Input validation-Validate and Filter user input to remove special characters ' " ` ; * % _ =&|*? ~<>^()[]{}$nr • If the use of a dynamic query is required, then address special characters by removal, replacement, encoding or escaping • Turn off all unnecessary database functionality 12
![[2] CWE-78 Improper Neutralization of Special Elements used in an OS Command ('OS Command [2] CWE-78 Improper Neutralization of Special Elements used in an OS Command ('OS Command](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-13.jpg)
[2] CWE-78 Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') OWASP Top 10 and PCI Mapping • OWASP 2010: A 1 Injection • PCI-DSS V 2: 6. 5. 1 Injection flaws General Description • The software constructs all or part of an OS command using input that has not been properly neutralized • Variants include: • The software intends to execute a single, fixed program that is under its own control using externally-supplied inputs as arguments to that program. However, if the program does not remove command separators from input, separators in the argument allow for the execution of additional programs • The software accepts an input that it uses to fully select which program to run, as well as which commands to use. The application redirects this entire command to the operating system 13
![[2] CWE-78 Improper Neutralization of Special Elements used in an OS Command ('OS Command [2] CWE-78 Improper Neutralization of Special Elements used in an OS Command ('OS Command](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-14.jpg)
[2] CWE-78 Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') Potential Impacts • Execution of arbitrary code, authentication bypass, compromise of the host OS Common Mitigations • Utilize task specific built-in APIs to conduct operating system tasks • Run code in a "jail" or similar sandbox environment that enforces strict boundaries between the process and the operating system • Properly neutralize all input from the client, especially command separators and special characters which can effect intended execution • Conduct all data validation and encoding on a trusted system (e. g. , The server) 14
![[3] CWE-120 Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') OWASP Top [3] CWE-120 Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') OWASP Top](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-15.jpg)
[3] CWE-120 Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') OWASP Top 10 and PCI Mapping • OWASP 2010: N/A • PCI-DSS V 2: 6. 5. 2 Buffer overflow General Description • The software copies an input buffer to an output buffer without verifying that the size of the input buffer is less than the size of the output buffer • Effects: C, C++ and Assembly Example: C char last_name[20]; . . Declare array with 20 character limit printf ("Enter your last name: "); scanf ("%s", last_name); . . . . Get input (no limit) and store in array The software does not limit the size of the name entered by the user, so an entry of more than 20 characters will cause a buffer overflow, since the "last_name" array can only hold 20 characters 15
![[3] CWE-120 Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') Potential Impacts [3] CWE-120 Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') Potential Impacts](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-16.jpg)
[3] CWE-120 Buffer Copy without Checking Size of Input ('Classic Buffer Overflow') Potential Impacts • Allow for the execution of arbitrary code, which is usually outside the scope of a program's implicit security policy Common Mitigations • Use a language that does not allow this weakness to occur (e. g. , Java) • Use a vetted library or framework that helps prevent this weakness (e. g. , Strsafe. h library from Microsoft) • Use a compiler with features or extensions that provide a protection mechanism against buffer overflows • Ensure the destination buffer size is equal to or larger than the source buffer size • Utilize input validation to enforce length limits 16
![[4] CWE-79 Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') OWASP Top [4] CWE-79 Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') OWASP Top](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-17.jpg)
[4] CWE-79 Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') OWASP Top 10 and PCI Mapping • OWASP 2010: A 2 Cross-Site Scripting (XSS) • PCI-DSS V 2: 6. 5. 7 Cross-site scripting (XSS) General Description • The software does not properly neutralize user-controllable input before using it in a web page. Variants include: • Reflected: The software reads data directly from the HTTP request and reflects it back in the HTTP response • Stored: The software stores data in a database or other trusted data store and includes that data as part of a future web page • DOM: Client supplied input is inserted into an HTML response page by a client side script that processed Document Object Model (DOM) data (e. g. , document. location, document. URL, etc) Try this in your browser's address bar: javascript: alert(document. cookie) 17
![[4] CWE-79 Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') Potential Impacts [4] CWE-79 Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') Potential Impacts](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-18.jpg)
[4] CWE-79 Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') Potential Impacts • Theft of session credentials, networks scans, key stroke loggers, XSS Proxy (allowing full control and viewing of exploited browser) Common Mitigations • Properly neutralize all input from the client. Be sure to address all content, used by the software, that originated in an HTTP Request • Conduct all data validation and encoding on a trusted system (e. g. , The server) • Establish and enforce appropriate data type, range and length controls for all content • Use a vetted library or framework to make it easier to generate properly encoded output including Microsoft's Anti-XSS library, the OWASP ESAPI Encoding module, and Apache Wicket E. g. output encoding with HTML entity encoding: The < character becomes: < The " character becomes: " This tag <script> becomes: < script> 18
![[5] CWE-306 Missing Authentication for Critical Function OWASP Top 10 and PCI Mapping • [5] CWE-306 Missing Authentication for Critical Function OWASP Top 10 and PCI Mapping •](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-19.jpg)
[5] CWE-306 Missing Authentication for Critical Function OWASP Top 10 and PCI Mapping • OWASP 2010: A 3 Broken Authentication and Session Management • PCI-DSS V 2: 8. 5 Ensure proper user identification and authentication management General Description • The software does not perform any authentication for functionality that requires a provable user identity or consumes a significant amount of resources 19
![[5] CWE-306 Missing Authentication for Critical Function Potential Impacts • Unauthorized access to read [5] CWE-306 Missing Authentication for Critical Function Potential Impacts • Unauthorized access to read](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-20.jpg)
[5] CWE-306 Missing Authentication for Critical Function Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Utilize authentication for all information, resources and functionality, except those specifically intended to be public • Ensure all authentication controls operate on a trusted system • Use a standardized, centralized, and tested implementation for all authentication controls • Authentication services should utilize a centralized authentication store • All authentication controls need to fail securely • Map roles and use role-based access control (RBAC) to enforce the roles at the appropriate boundaries 20
![[6] CWE-862 Missing Authorization OWASP Top 10 and PCI Mapping • OWASP 2010: A [6] CWE-862 Missing Authorization OWASP Top 10 and PCI Mapping • OWASP 2010: A](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-21.jpg)
[6] CWE-862 Missing Authorization OWASP Top 10 and PCI Mapping • OWASP 2010: A 4 Insecure Direct Object References • A 8 Failure to Restrict URL Access • PCI-DSS V 2: 6. 5. 8 Improper Access Control General Description • The software does not perform an authorization check when an actor attempts to access a resource or perform an action 21
![[6] CWE-862 Missing Authorization Potential Impacts • Unauthorized access to read or modify data [6] CWE-862 Missing Authorization Potential Impacts • Unauthorized access to read or modify data](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-22.jpg)
[6] CWE-862 Missing Authorization Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Enforce authorization controls on every request • Map roles and use role-based access control (RBAC) to enforce the roles at the appropriate boundaries • Enforce application logic flows to comply with business rules • Restrict access to files, URLs, protected functions, services, application data, user and data attributes and security-relevant configuration information to only authorized users 22
![[7] CWE-798 Use of Hard-coded Credentials OWASP Top 10 and PCI Mapping • OWASP [7] CWE-798 Use of Hard-coded Credentials OWASP Top 10 and PCI Mapping • OWASP](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-23.jpg)
[7] CWE-798 Use of Hard-coded Credentials OWASP Top 10 and PCI Mapping • OWASP 2010: Management A 3 Broken Authentication and Session • PCI-DSS V 2: 8. 5 Ensure proper user identification and authentication management General Description • The software contains hard-coded credentials, such as a password or cryptographic key, which it uses for its own inbound authentication, outbound communication to external components, or encryption of internal data • Variants include: • Inbound: The software contains an authentication mechanism that checks the input credentials against a hard-coded set of credentials • Outbound: The software connects to another system or component, and it contains hard-coded credentials for connecting to that component 23
![[7] CWE-798 Use of Hard-coded Credentials Potential Impacts • Unauthorized access to read or [7] CWE-798 Use of Hard-coded Credentials Potential Impacts • Unauthorized access to read or](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-24.jpg)
[7] CWE-798 Use of Hard-coded Credentials Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Outbound Authentication: Store passwords, keys, and other credentials outside of the code in a strongly-protected, encrypted configuration file or database that is protected from access by all outsiders, including other local users on the same system • Inbound Authentication: Rather than hard-code a default username and password, key, or other authentication credentials for first time logins, utilize a "first login" mode that requires the user to enter a unique strong password or key • If the software must contain hard-coded credentials or they cannot be removed, perform access control checks and limit which entities can access the feature that requires the hard-coded credentials 24
![[8] CWE-311 Missing Encryption of Sensitive Data OWASP Top 10 and PCI Mapping • [8] CWE-311 Missing Encryption of Sensitive Data OWASP Top 10 and PCI Mapping •](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-25.jpg)
[8] CWE-311 Missing Encryption of Sensitive Data OWASP Top 10 and PCI Mapping • OWASP 2010: A 7 Insecure Cryptographic Storage • A 9: Insufficient Transport Layer Protection • PCI-DSS V 2: 6. 5. 3 Insecure cryptographic storage • 6. 5. 4 Insecure communications • Additionally: 2. 3, 3. 4, 3. 5, 3. 6, 4. 1, 4. 2, 8. 4 General Description • The software does not encrypt sensitive or critical information before storage or transmission • Unencrypted network traffic may be intercepted, monitored or in some cases altered • Sensitive information stored in plain text may be accessed without authorization, if the data store is reached 25
![[8] CWE-311 Missing Encryption of Sensitive Data Potential Impacts • Unauthorized access to read [8] CWE-311 Missing Encryption of Sensitive Data Potential Impacts • Unauthorized access to read](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-26.jpg)
[8] CWE-311 Missing Encryption of Sensitive Data Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Implement encryption for the transmission of all sensitive information and for conducting critical operations (e. g. , TLS, SSH and SFTP) • Prevent unauthorized access by encrypting sensitive data, even on trusted systems • Select a well-vetted algorithm that is currently considered to be strong (e. g. , FIPS 140 -2 or an equivalent standard). Periodically ensure that the cryptography used by the software has not become obsolete • If the software relies on wireless communications, implement strong encryption for authentication and transmission 26
![[9] CWE-434 Unrestricted Upload of File with Dangerous Type OWASP Top 10 and PCI [9] CWE-434 Unrestricted Upload of File with Dangerous Type OWASP Top 10 and PCI](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-27.jpg)
[9] CWE-434 Unrestricted Upload of File with Dangerous Type OWASP Top 10 and PCI Mapping • OWASP 2010: • PCI-DSS V 2: N/A General Description • The software allows for the uploading or transfer files of dangerous types that can be automatically processed within the product's environment • If proper validation of the file type is not done, a user may be able to upload a malicious file and then access that file to gain unauthorized privileges. Example: This PHP file provides access to the host OS <? php system($_GET['cmd']); ? > http: //server. example. com/upload_dir/malicious. php? cmd=ls%20 -l 27
![[9] CWE-434 Unrestricted Upload of File with Dangerous Type Potential Impacts • Unauthorized access [9] CWE-434 Unrestricted Upload of File with Dangerous Type Potential Impacts • Unauthorized access](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-28.jpg)
[9] CWE-434 Unrestricted Upload of File with Dangerous Type Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • The software should generate its own filename for an uploaded file instead of the user-supplied filename • Validate uploaded files are the expected type by checking file headers • Prevent or restrict the uploading of any file that may be interpreted by the web server • Turn off execution privileges on file upload directories • Do not save files in the same web context as the application 28
![[10] CWE-807 Reliance on Untrusted Inputs in a Security Decision OWASP Top 10 and [10] CWE-807 Reliance on Untrusted Inputs in a Security Decision OWASP Top 10 and](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-29.jpg)
[10] CWE-807 Reliance on Untrusted Inputs in a Security Decision OWASP Top 10 and PCI Mapping • OWASP 2010: A 4 Insecure Direct Object References • PCI-DSS V 2: 6. 5. 8 Improper Access Control General Description • The software does not perform or incorrectly performs an authorization check when an attempt is made to access a resource or perform an action • The software bases access decisions on client accessible data or parameters. https: //example. com/account. Info? acct=Bob) Bob makes request for his own acct https: //example. com/account. Info? acct=Tom) Bob makes request for Tom’s acct • Any item in an HTTP request, that is used in addition to the session identifier to make access decisions, is at risk of attacker tampering 29
![[10] CWE-807 Reliance on Untrusted Inputs in a Security Decision Potential Impacts • Unauthorized [10] CWE-807 Reliance on Untrusted Inputs in a Security Decision Potential Impacts • Unauthorized](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-30.jpg)
[10] CWE-807 Reliance on Untrusted Inputs in a Security Decision Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Enforce authorization controls on every request • Store data used to make authorization decisions only on a trusted system (e. g. the server) • If this data must be exposed to the client, use integrity checking on the server side to prevent tampering. (e. g. , ASP. NET View State) • Enforce application logic flows to comply with business rules 30
![[11] CWE-250 Execution with Unnecessary Privileges OWASP Top 10 and PCI Mapping • OWASP [11] CWE-250 Execution with Unnecessary Privileges OWASP Top 10 and PCI Mapping • OWASP](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-31.jpg)
[11] CWE-250 Execution with Unnecessary Privileges OWASP Top 10 and PCI Mapping • OWASP 2010: A 6 Security Misconfiguration • PCI-DSS V 2: 6. 5. 8 Improper Access Control General Description • The software performs an operation at a privilege level that is higher than the minimum level required • Running with extra privileges, such as root or Administrator, can disable the normal security checks being performed by the operating system or surrounding environment • Other pre-existing weaknesses can turn into security vulnerabilities if they occur while operating at raised privileges • An example might be an application connecting to a database as the schema/database owner 31
![[11] CWE-250 Execution with Unnecessary Privileges Potential Impacts • Unauthorized access to read or [11] CWE-250 Execution with Unnecessary Privileges Potential Impacts • Unauthorized access to read or](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-32.jpg)
[11] CWE-250 Execution with Unnecessary Privileges Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Run your code using the lowest privileges that are required to accomplish the necessary tasks • Raise your privileges as late as possible, and drop them as soon as possible • If possible, create isolated accounts with limited privileges that are only used for a single task • Ensure privilege management functions account for the fact that spawned processes run at the privilege of the owning process, so if a process is running as root when a sub-process is executed, the sub-process will operate with root privileges 32
![[12] CWE-352 Cross-Site Request Forgery (CSRF) OWASP Top 10 and PCI Mapping • OWASP [12] CWE-352 Cross-Site Request Forgery (CSRF) OWASP Top 10 and PCI Mapping • OWASP](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-33.jpg)
[12] CWE-352 Cross-Site Request Forgery (CSRF) OWASP Top 10 and PCI Mapping • OWASP 2010: A 5 Cross-Site Request Forgery (CSRF) • PCI-DSS V 2: 6. 5. 9 Cross-site request forgery (CSRF) General Description • If the software does not sufficiently verify that the user "intentionally" submitted a request, a user with an active session may be tricked into executing an unintended action on the software. The URL and required parameters must be known to the attacker Example of a legitimate request: http: //example. com/app/transfer. Funds? amount=1500&destination. Account=4673243243 Example or a forged request using a hidden image tag: <img src=http: //example. com/app/transfer. Funds? amount=1500&destination. Account= attackers. Acct# width="0" height="0" /> 33
![[12] CWE-352 Cross-Site Request Forgery (CSRF) Potential Impacts • Attackers can cause the victim [12] CWE-352 Cross-Site Request Forgery (CSRF) Potential Impacts • Attackers can cause the victim](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-34.jpg)
[12] CWE-352 Cross-Site Request Forgery (CSRF) Potential Impacts • Attackers can cause the victim to execute any action the victim is authorized to perform Common Mitigations • Use a vetted library to prevent this weakness (e. g. , OWASP CSRFGuard, OWASP ESAPI Session Management control) • Include an unpredictable token in each form and verify the token upon receipt of the form • Utilize the HTTP POST method to avoid exposing the token in the URL • Re-authenticate users prior to performing critical operations 34
![[13] CWE-22 Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') OWASP [13] CWE-22 Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') OWASP](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-35.jpg)
[13] CWE-22 Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') OWASP Top 10 and PCI Mapping • OWASP 2010: A 4 Insecure Direct Object References • PCI-DSS V 2: 6. 5. 8 Improper Access Control General Description • The software constructs dynamic directory or file path statements based on user supplied input that is not properly neutralized for special elements that can alter the path • The “dot-slash (. . / or. . )” sequences can be used to move up the directory structure and then navigate to a new location Expected Request: http: //app/page. jsp? include=file. txt Malicious Request: http: //app/page. jsp? include=/. . /etc/passwd • Adding a null byte (i. e. %00, or 0 x 00 in hex) may allow an attacker to bypass extension based file type restrictions by dropping everything after the null. Expected Request: http: //app/page. jsp? file=graphic. gif Malicious Request: http: //app/page. jsp? file=serverlogs. txt%00. gif 35
![[13] CWE-22 Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') Potential [13] CWE-22 Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') Potential](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-36.jpg)
[13] CWE-22 Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') Potential Impacts • Unauthorized access to read, create or overwrite critical files Common Mitigations • Replace direct object references by using place holder values and mapping them to the actual file names or paths Direct object reference: http: //app? file=Report 123. xls Mapped value reference: http: //app? file=1 (In sever side code: 1 = Report 123. xls) • Properly neutralize all input from the client, especially path characters (. , /, ) and null bytes (%00) • Conduct all data validation and encoding on a trusted system (e. g. , The server) • Enforce authorization controls on every request 36
![[14] CWE-494 Download of Code Without Integrity Check OWASP Top 10 and PCI Mapping [14] CWE-494 Download of Code Without Integrity Check OWASP Top 10 and PCI Mapping](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-37.jpg)
[14] CWE-494 Download of Code Without Integrity Check OWASP Top 10 and PCI Mapping • OWASP 2010: N/A • PCI-DSS V 2: N/A General Description • The product downloads source code or an executable from a remote location and executes the code without sufficiently verifying the origin and integrity of the code Example: Java URL[] class. URLs= new URL[]{ new URL("file: subdir/") }; URLClass. Loader loader = new URLClass. Loader(class. URLs); Class loaded. Class = Class. for. Name("load. Me", true, loader); This code does not ensure that the class loaded is the intended one, for example by verifying the class's checksum. An attacker may be able to modify the class file to execute malicious code. 37
![[14] CWE-494 Download of Code Without Integrity Check Potential Impacts • Unauthorized access to [14] CWE-494 Download of Code Without Integrity Check Potential Impacts • Unauthorized access to](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-38.jpg)
[14] CWE-494 Download of Code Without Integrity Check Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software or hosting environment's security controls Common Mitigations • Perform proper forward and reverse DNS lookups to detect DNS spoofing • Encrypt the code with a reliable encryption scheme before transmitting • Perform integrity checking on the transmitted code • Use code signing technologies such as Authenticode 38
![[15] CWE-863 Incorrect Authorization OWASP Top 10 and PCI Mapping • OWASP 2010: A [15] CWE-863 Incorrect Authorization OWASP Top 10 and PCI Mapping • OWASP 2010: A](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-39.jpg)
[15] CWE-863 Incorrect Authorization OWASP Top 10 and PCI Mapping • OWASP 2010: A 8 Failure to Restrict URL Access • A 4 Insecure Direct Object References • PCI-DSS V 2: 6. 5. 8 Improper Access Control General Description • The software does not perform or incorrectly performs an authorization check when an attempt is made to access a resource or perform an action • Example: The Software uses presentation layer access control. (URLs are treated like secrets. They are displayed on screen, appear in browser histories and log files, may be shared by users and are known to previously privileged users whose role has changed) Attacker notices the URL indicates his role /user/get. Accounts He modifies it to another directory (role) /admin/get. Accounts Attacker views more accounts than just their own 39
![[15] CWE-863 Incorrect Authorization Potential Impacts • Unauthorized access to read or modify data [15] CWE-863 Incorrect Authorization Potential Impacts • Unauthorized access to read or modify data](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-40.jpg)
[15] CWE-863 Incorrect Authorization Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Enforce authorization controls on every request • Access control decisions must not depend on untrusted data • Map roles and use Role-Based Access Control (RBAC) to enforce the roles at the appropriate boundaries • Enforce application logic flows to comply with business rules • Restrict access to files, URLs, protected functions, services, application data, user and data attributes and security-relevant configuration information to only authorized users • Ensure access control is enforced correctly on a trusted system 40
![[16] CWE-829 Inclusion of Functionality from Untrusted Control Sphere OWASP Top 10 and PCI [16] CWE-829 Inclusion of Functionality from Untrusted Control Sphere OWASP Top 10 and PCI](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-41.jpg)
[16] CWE-829 Inclusion of Functionality from Untrusted Control Sphere OWASP Top 10 and PCI Mapping • OWASP 2010: A 6 Security Misconfiguration • PCI-DSS V 2: N/A General Description • The software imports, requires, or includes executable functionality from an untrusted source • An example might be a web application including a weather widget from an external source <div id="Weather. Widget"> <script type="text/javascript" src="external. Domain. example. com/weatherwidget. js"></script> </div> 41
![[16] CWE-829 Inclusion of Functionality from Untrusted Control Sphere Potential Impacts • The functionality [16] CWE-829 Inclusion of Functionality from Untrusted Control Sphere Potential Impacts • The functionality](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-42.jpg)
[16] CWE-829 Inclusion of Functionality from Untrusted Control Sphere Potential Impacts • The functionality could be malicious in nature if the source becomes compromised or if the content is modified in transit • The functionality may also have vulnerabilities that become inherited by the including application Common Mitigations • • Evaluate the security of untrusted functionality before using it Use a local version of the code whenever possible Run your code in a "jail" or similar sandbox environment Use anti-malware to monitor the execution of untrusted code 42
![[17] CWE-732 Incorrect Permission Assignment for Critical Resource OWASP Top 10 and PCI Mapping [17] CWE-732 Incorrect Permission Assignment for Critical Resource OWASP Top 10 and PCI Mapping](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-43.jpg)
[17] CWE-732 Incorrect Permission Assignment for Critical Resource OWASP Top 10 and PCI Mapping • OWASP 2010: A 8 Failure to Restrict URL Access • PCI-DSS V 2: 6. 5. 8 Improper Access Control General Description • The software specifies permissions for a security-critical resource in a way that allows that resource to be read or modified by unintended actors • Changes to the operating environment, data sensitivity or user groups might result in inappropriate permissions • Loose permissions are set to minimize problems during installation and configuration. This may require the administrator to proactively lock them down before moving to production, which does not always happen 43
![[17] CWE-732 Incorrect Permission Assignment for Critical Resource Potential Impacts • Unauthorized access to [17] CWE-732 Incorrect Permission Assignment for Critical Resource Potential Impacts • Unauthorized access to](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-44.jpg)
[17] CWE-732 Incorrect Permission Assignment for Critical Resource Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • When using a critical resource verify that it has secure permissions • During program startup, explicitly set the default permissions to the most restrictive setting possible • For all configuration files, executables, and libraries, make sure that they are only readable and writable by the software's administrator • Do not assume that the system administrator will manually change the configuration to the settings that you recommend in the manual • Map roles and use role-based access control (RBAC) to enforce the roles at the appropriate boundaries 44
![[18] CWE-676 Use of Potentially Dangerous Function OWASP Top 10 and PCI Mapping • [18] CWE-676 Use of Potentially Dangerous Function OWASP Top 10 and PCI Mapping •](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-45.jpg)
[18] CWE-676 Use of Potentially Dangerous Function OWASP Top 10 and PCI Mapping • OWASP 2010: N/A • PCI-DSS V 2: N/A General Description • The program invokes a potentially dangerous function that could introduce a vulnerability if it is used incorrectly • Most commonly identified in C and C++ application using functions like strcpy() 45
![[18] CWE-676 Use of Potentially Dangerous Function Potential Impacts • System crash • Allow [18] CWE-676 Use of Potentially Dangerous Function Potential Impacts • System crash • Allow](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-46.jpg)
[18] CWE-676 Use of Potentially Dangerous Function Potential Impacts • System crash • Allow for the execution of arbitrary code • Unauthorized access to read or modify data Common Mitigations • Identify a list of prohibited API functions and prohibit the use of these functions, providing safer alternatives • Refer to the Microsoft Security Development Lifecycle (SDL) Banned Function Calls • http: //msdn. microsoft. com/en-us/library/bb 288454. aspx 46
![[19] CWE-327 Use of a Broken or Risky Cryptographic Algorithm OWASP Top 10 and [19] CWE-327 Use of a Broken or Risky Cryptographic Algorithm OWASP Top 10 and](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-47.jpg)
[19] CWE-327 Use of a Broken or Risky Cryptographic Algorithm OWASP Top 10 and PCI Mapping • OWASP 2010: A 7: Insecure Cryptographic Storage • A 9: Insufficient Transport Layer Protection • PCI-DSS V 2: 4. 1 Use strong cryptography and security protocols • 6. 5. 3 Insecure cryptographic storage General Description • The software uses a broken or risky cryptographic algorithm. The algorithm may be dangerous because it is non-standard or because it is known to be weak • The Data Encryption Standard (DES) was once considered a strong algorithm, however it is now regarded as insufficient for many applications and has been replaced by Advanced Encryption Standard (AES) 47
![[19] CWE-327 Use of a Broken or Risky Cryptographic Algorithm Potential Impacts • Unauthorized [19] CWE-327 Use of a Broken or Risky Cryptographic Algorithm Potential Impacts • Unauthorized](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-48.jpg)
[19] CWE-327 Use of a Broken or Risky Cryptographic Algorithm Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Select a well-vetted algorithm that is currently considered to be strong (e. g. , FIPS 140 -2 (i. e. Triple-DES, AES, RSA) or an equivalent standard) • Periodically ensure that the cryptography used by the software has not become obsolete • Design your software so that you can replace one cryptographic algorithm with another • All cryptographic functions used to protect secrets from the application user must be implemented on a trusted system (e. g. , The server) • Protect master secrets from unauthorized access 48
![[20] CWE-131 Incorrect Calculation of Buffer Size OWASP Top 10 and PCI Mapping • [20] CWE-131 Incorrect Calculation of Buffer Size OWASP Top 10 and PCI Mapping •](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-49.jpg)
[20] CWE-131 Incorrect Calculation of Buffer Size OWASP Top 10 and PCI Mapping • OWASP 2010: N/A • PCI-DSS V 2: 6. 5. 2 Buffer overflow General Description • The software does not correctly calculate the size to be used when allocating a buffer, which could lead to a buffer overflow Example: C int *id_sequence; id_sequence = (int*) malloc(3); if (id_sequence == NULL) exit(1); id_sequence[0] = 13579; id_sequence[1] = 24680; id_sequence[2] = 97531; The size parameter used during the malloc() call is set to '3' which results in a buffer of 3 bytes. The intent was to create a buffer that holds three ints, and in C, each int requires 4 bytes, so an array of 12 bytes is needed. Executing the above code could result in a buffer overflow as 12 bytes of data is being saved into 3 bytes worth of allocated space 49
![[20] CWE-131 Incorrect Calculation of Buffer Size Potential Impacts • System crash • Allow [20] CWE-131 Incorrect Calculation of Buffer Size Potential Impacts • System crash • Allow](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-50.jpg)
[20] CWE-131 Incorrect Calculation of Buffer Size Potential Impacts • System crash • Allow for the execution of arbitrary code • Unauthorized access to read or modify data Common Mitigations • If you allocate a buffer for the purpose of transforming, converting, or encoding an input, make sure that you allocate enough memory to handle the largest possible encoding • Understand your programming language's underlying representation and how it interacts with numeric calculation • Utilize input validation to enforce length and range limits • Conduct all data validation and encoding on a trusted system (e. g. , The server) 50
![[21] CWE-307 Improper Restriction of Excessive Authentication Attempts OWASP Top 10 and PCI Mapping [21] CWE-307 Improper Restriction of Excessive Authentication Attempts OWASP Top 10 and PCI Mapping](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-51.jpg)
[21] CWE-307 Improper Restriction of Excessive Authentication Attempts OWASP Top 10 and PCI Mapping • OWASP 2010: A 3 Broken Authentication and Session Management • PCI-DSS V 2: 8. 5 Ensure proper user identification and authentication management for non-consumer users and administrators on all system components General Description • The software does not implement sufficient measures to prevent multiple failed authentication attempts within in a short time frame, making it more susceptible to brute force attacks 51
![[21] CWE-307 Improper Restriction of Excessive Authentication Attempts Potential Impacts • Attackers may be [21] CWE-307 Improper Restriction of Excessive Authentication Attempts Potential Impacts • Attackers may be](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-52.jpg)
[21] CWE-307 Improper Restriction of Excessive Authentication Attempts Potential Impacts • Attackers may be able gain access by conducting attacks utilizing automated brute force or dictionary based attacks Common Mitigations • Enforce account locking, disabling or time outs after an established number of invalid login attempts (e. g. , five attempts is common) • Lockout messages should not indicate which data caused the lockout condition • Controls need to be implemented on the logon page and also any other places where this type of attack might be used, such as password changing and recovery areas • Combine with sophisticated challenge questions • Use Multi-Factor Authentication for highly sensitive or high value transactional accounts 52
![[22] CWE-601 URL Redirection to Untrusted Site ('Open Redirect') OWASP Top 10 and PCI [22] CWE-601 URL Redirection to Untrusted Site ('Open Redirect') OWASP Top 10 and PCI](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-53.jpg)
[22] CWE-601 URL Redirection to Untrusted Site ('Open Redirect') OWASP Top 10 and PCI Mapping • OWASP 2010: A 10 Unvalidated Redirects and Forwards • PCI-DSS V 2: N/A General Description • A web application accepts a user-controlled input that specifies a link to an external site, and uses that link in a Redirect Example: PHP $redirect_url = $_GET['url']; header("Location: ". $redirect_url); This page could be used as part of a phishing scam by starting on a trusted domain, but redirecting users to a malicious site. An attacker could supply a user with the following link: http: //example. com/example. php? url=http: //malicious. example. com This is the same URL only obfuscated with URL encoding to mask the off site redirect: http: //example. com/example. php? url=%68%74%74%70%3 a%2 f%2 f%6 d%61%6 c%69%63%6 9%6 f%75%73%2 e%65%78%61%6 d%70%6 c%65%2 e%63%6 f%6 d 53
![[22] CWE-601 URL Redirection to Untrusted Site ('Open Redirect') Potential Impacts • Compromise of [22] CWE-601 URL Redirection to Untrusted Site ('Open Redirect') Potential Impacts • Compromise of](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-54.jpg)
[22] CWE-601 URL Redirection to Untrusted Site ('Open Redirect') Potential Impacts • Compromise of the client machine through malware exposure • Client credential or sensitive information exposure through spoofing content that implies the user is still on the trusted web site Common Mitigations • When the set of acceptable URLs is limited or known, create a mapping from a set of fixed input values (such as numeric IDs) to the actual filenames or URLs, and reject all other inputs • Do not pass user supplied data into a dynamic redirect. If this must be allowed, then the redirect should accept only validated, relative path URLs • If absolute paths are used, either have the page add the domain component or strictly validate the domain • Use an intermediate disclaimer page that provides the user with a clear warning that they are leaving your site 54
![[23] CWE-134 Uncontrolled Format String OWASP Top 10 and PCI Mapping • OWASP 2010: [23] CWE-134 Uncontrolled Format String OWASP Top 10 and PCI Mapping • OWASP 2010:](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-55.jpg)
[23] CWE-134 Uncontrolled Format String OWASP Top 10 and PCI Mapping • OWASP 2010: N/A • PCI-DSS V 2: 6. 5. 2 Buffer overflow General Description • The software uses externally-controlled format strings in printf style functions, which can lead to buffer overflows or data representation problems Example C: int main(int argc, char **argv){ char buf[128]; . . . snprintf(buf, 128, argv[1]); } This code allows an attacker to view the contents of the stack and write to the stack using a command line argument containing a sequence of formatting directives. 55
![[23] CWE-134 Uncontrolled Format String Potential Impacts • System crash • Allow for the [23] CWE-134 Uncontrolled Format String Potential Impacts • System crash • Allow for the](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-56.jpg)
[23] CWE-134 Uncontrolled Format String Potential Impacts • System crash • Allow for the execution of arbitrary code • Data Corruption Common Mitigations • Ensure that all format string functions are passed a static string which cannot be controlled by the user and that the proper number of arguments are always sent to that function as well. If at all possible, use functions that do not support the %n operator in format strings • Utilize input validation to enforce length and range limits • Conduct all data validation and encoding on a trusted system (e. g. , The server) 56
![[24] CWE-190 Integer Overflow or Wraparound OWASP Top 10 and PCI Mapping • OWASP [24] CWE-190 Integer Overflow or Wraparound OWASP Top 10 and PCI Mapping • OWASP](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-57.jpg)
[24] CWE-190 Integer Overflow or Wraparound OWASP Top 10 and PCI Mapping • OWASP 2010: N/A • PCI-DSS V 2: 6. 5. 2 Buffer overflow General Description • The software performs a calculation that can produce an integer overflow or wraparound, when the logic assumes that the resulting value will always be larger than the original value Example: C nresp = packet_get_int(); if (nresp > 0) { response = xmalloc(nresp*sizeof(char*)); for (i = 0; i > nresp; i++) response[i] = packet_get_string(NULL); } If nresp has the value 1073741824 and sizeof(char*) has its typical value of 4, then the result of the operation nresp*sizeof(char*) overflows, and the argument to xmalloc() will be 0, causing the subsequent loop iterations to overflow the heap buffer response 57
![[24] CWE-190 Integer Overflow or Wraparound Potential Impacts • System crash • Allow for [24] CWE-190 Integer Overflow or Wraparound Potential Impacts • System crash • Allow for](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-58.jpg)
[24] CWE-190 Integer Overflow or Wraparound Potential Impacts • System crash • Allow for the execution of arbitrary code • Data Corruption Common Mitigations • Ensure that all protocols are strictly defined, such that all out-of-bounds behavior can be identified simply, and require strict conformance to the protocol • Use libraries or frameworks that make it easier to handle numbers without unexpected consequences. (e. g. , Safe. Int (C++) or Integer. Lib (C or C++) • Utilize input validation to enforce length and range limits • Conduct all data validation and encoding on a trusted system (e. g. , The server) 58
![[25] CWE-759 Use of a One-Way Hash without a Salt OWASP Top 10 and [25] CWE-759 Use of a One-Way Hash without a Salt OWASP Top 10 and](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-59.jpg)
[25] CWE-759 Use of a One-Way Hash without a Salt OWASP Top 10 and PCI Mapping • OWASP 2010: A 7 Insecure Cryptographic Storage • PCI-DSS V 2: 6. 5. 3 Insecure cryptographic storage General Description • The software uses a one-way cryptographic hash against an input that should not be reversible, such as a password, but the software does not also use a salt as part of the input • This makes it easier for attackers to pre-compute the hash value using dictionary attack techniques such as rainbow tables 59
![[25] CWE-759 Use of a One-Way Hash without a Salt Potential Impacts • Unauthorized [25] CWE-759 Use of a One-Way Hash without a Salt Potential Impacts • Unauthorized](http://slidetodoc.com/presentation_image_h/b4eced9b799d865cd6d631ee281b9370/image-60.jpg)
[25] CWE-759 Use of a One-Way Hash without a Salt Potential Impacts • Unauthorized access to read or modify data • Ability to gain additional privileges that could lead to a complete compromise of the software's security controls Common Mitigations • Generate a random salt each time you process a new data that requires hashing • Add the salt to the plaintext data before hashing it • When you store the hash, also store the salt. Do not use the same salt for every piece of data that you process 60
61
- Slides: 61