OWASP Broken Web Applications OWASP BWA Beyond 1
OWASP Broken Web Applications (OWASP BWA): Beyond 1. 0
Agenda • • • Introductions Project Background Current Status Future Q&A 2
About Me • Sr. Technical Director at Mandiant in DC • Application Security, Penetration Testing, Source Code Analysis, Forensics, Incident Response, Research and Development • Leader of OWASP Broken Web Applications project • chuck. willis@mandiant. com • @chuckatsf 3
Project Background
Problem • Looking for web applications with vulnerabilities where I could: – Test web application scanners – Test manual attack techniques – Test source code analysis tools – Look at the code that implements the vulnerabilities – Modify code to fix vulnerabilities – Test web application firewalls – Examine evidence left by attacks 5
OWASP Web. Goat • It is a great learning tool, but… • It is a training environment, not a real application • Same held for many other “training” applications 6
Proprietary “Free” Apps • Realistic applications with vulnerabilities • Often closed source, which prevents some uses • Can conflict with one another • Can be difficult to install • Licensing restrictions 7
OWASP BWA Solution • Free, Linux-based Virtual Machine • Contains a variety of web applications – Some intentionally broken – Some old versions of open source applications • Pre-configured and ready to use / test • All applications are open source – Allows for source code analysis – Allows users to modify the source to fix vulnerabilities (or add new ones) 8
OWASP BWA History • Initial 0. 9 release at App. Sec DC 2009 • 1. 0 release in July 2012 • Current version is 1. 1. 1 – Released in September 2013 – Download links off www. owaspbwa. org – Some known issues 9
OWASP BWA Details
Virtual Machine • Available in VMware and OVA formats • Compatible with – VMware Products • No-cost and commercial • OWASP BWA intentionally uses older VM format – Oracle Virtual. Box – Parallels Desktop 11
Base Operating System • OS is Ubuntu Linux Server 10. 04 LTS – No X-Windows / Graphical User Interface • Managed via – Console – Open. SSH – Samba – php. My. Admin 12
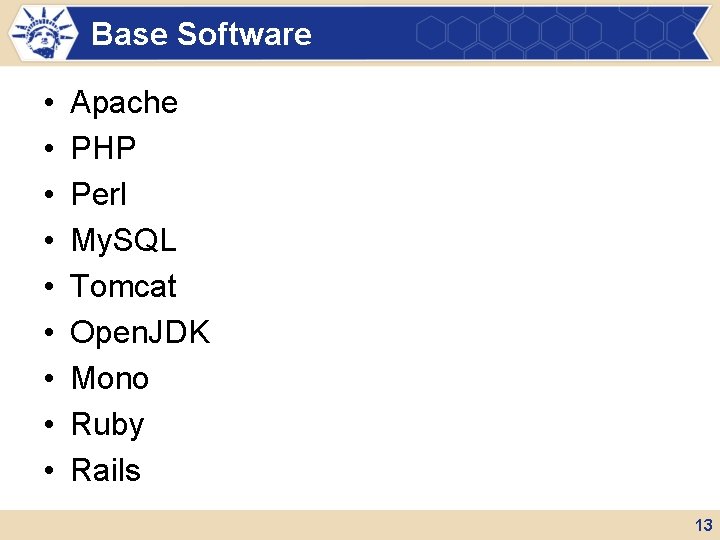
Base Software • • • Apache PHP Perl My. SQL Tomcat Open. JDK Mono Ruby Rails 13
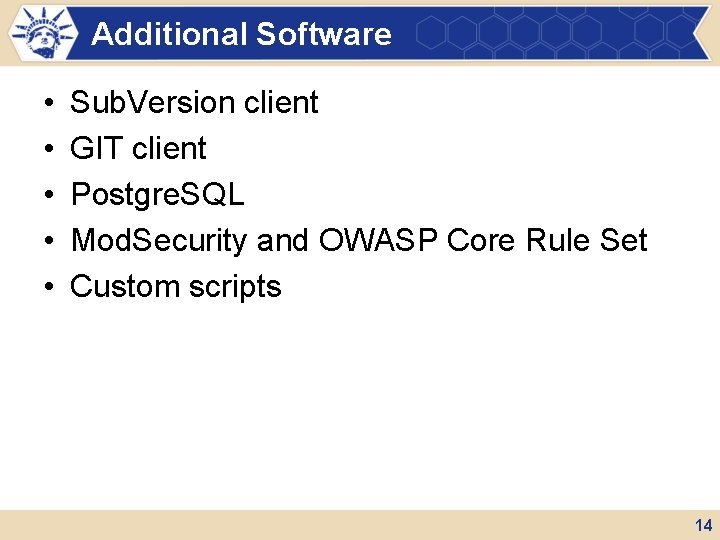
Additional Software • • • Sub. Version client GIT client Postgre. SQL Mod. Security and OWASP Core Rule Set Custom scripts 14
Applications
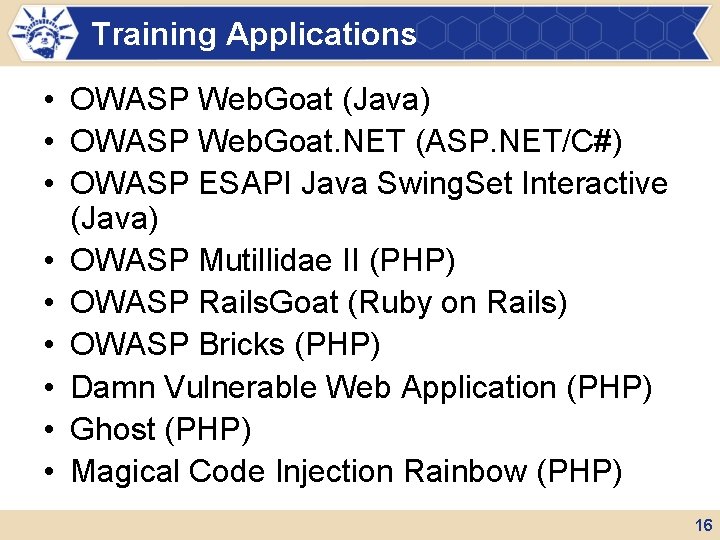
Training Applications • OWASP Web. Goat (Java) • OWASP Web. Goat. NET (ASP. NET/C#) • OWASP ESAPI Java Swing. Set Interactive (Java) • OWASP Mutillidae II (PHP) • OWASP Rails. Goat (Ruby on Rails) • OWASP Bricks (PHP) • Damn Vulnerable Web Application (PHP) • Ghost (PHP) • Magical Code Injection Rainbow (PHP) 16
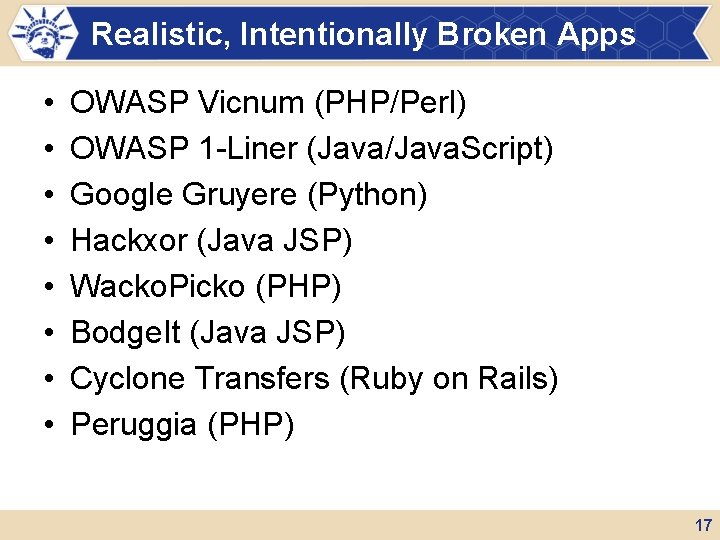
Realistic, Intentionally Broken Apps • • OWASP Vicnum (PHP/Perl) OWASP 1 -Liner (Java/Java. Script) Google Gruyere (Python) Hackxor (Java JSP) Wacko. Picko (PHP) Bodge. It (Java JSP) Cyclone Transfers (Ruby on Rails) Peruggia (PHP) 17
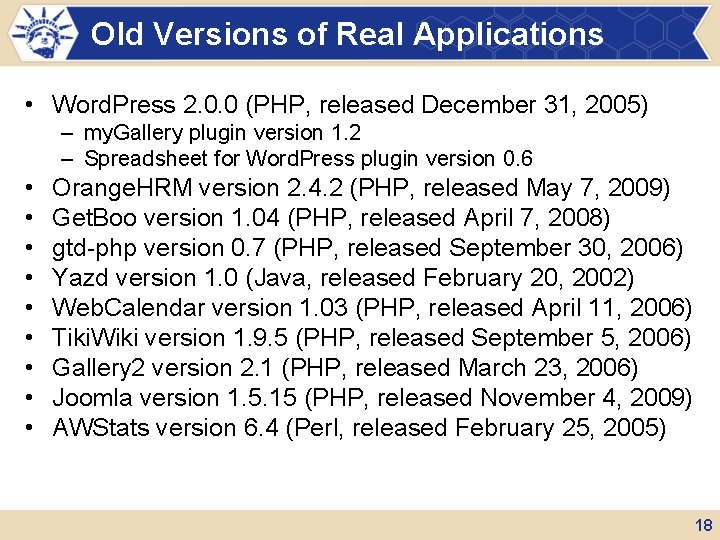
Old Versions of Real Applications • Word. Press 2. 0. 0 (PHP, released December 31, 2005) – my. Gallery plugin version 1. 2 – Spreadsheet for Word. Press plugin version 0. 6 • • • Orange. HRM version 2. 4. 2 (PHP, released May 7, 2009) Get. Boo version 1. 04 (PHP, released April 7, 2008) gtd-php version 0. 7 (PHP, released September 30, 2006) Yazd version 1. 0 (Java, released February 20, 2002) Web. Calendar version 1. 03 (PHP, released April 11, 2006) Tiki. Wiki version 1. 9. 5 (PHP, released September 5, 2006) Gallery 2 version 2. 1 (PHP, released March 23, 2006) Joomla version 1. 5. 15 (PHP, released November 4, 2009) AWStats version 6. 4 (Perl, released February 25, 2005) 18
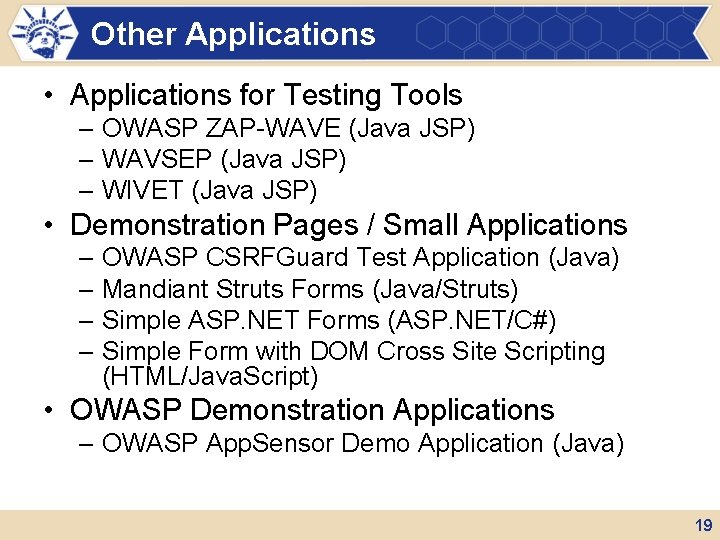
Other Applications • Applications for Testing Tools – OWASP ZAP-WAVE (Java JSP) – WAVSEP (Java JSP) – WIVET (Java JSP) • Demonstration Pages / Small Applications – OWASP CSRFGuard Test Application (Java) – Mandiant Struts Forms (Java/Struts) – Simple ASP. NET Forms (ASP. NET/C#) – Simple Form with DOM Cross Site Scripting (HTML/Java. Script) • OWASP Demonstration Applications – OWASP App. Sensor Demo Application (Java) 19
Other Features
Editing Applications • Application code can be edited via SMB shares, SSH, or the console • Updates to PHP, JSP, etc. application files will take place immediately • Scripts provided to rebuild and redeploy applications that require it: – Web. Goat – Yazd – CSRFGuard Test Apps – Swing. Set Apps 21
Updating VM • Scripts are provided to update VM from source code repositories – OWASP BWA specific files from Google Code SVN repository – Application files from their SVN or GIT repositories • Can break applications due to changes in database schemas or dependencies • Can allow for using updated versions of applications without waiting for a new version of OWASP BWA 22
OWASP Mod. Security Core Rule Set • Web server on OWASP BWA is running mod_security • By default, no rules are enabled • Scripts are provided to: – Enable logging using CRS: • owaspbwa-modsecurity-crs-log. sh – Enable blocking using CRS: • owaspbwa-modsecurity-crs-block. sh – Disable all rules: • owaspbwa-modsecurity-crs-off. sh • Rules can be easily edited via SMB shares 23
Log Files • Logging for the web and application servers are left in their default configuration – What you will most likely see when responding to an incident • Logs are available via SMB share • Logging settings can be easily edited • Logs are cleared when VM is packaged 24
User Guide • User Guide available on Google Code Wiki https: //code. google. com/p/owaspbwa/wiki/User. Guide • Welcome any volunteers to contribute – Author – Review – Edit – Comment 25
Vulnerabilities
Where are the vulnerabilities? • Don’t have a master list of vulnerabilities (yet) • Looking for the community to contribute • Using “Trac” issue tracker at Source. Forge: http: //sourceforge. net/apps/trac/owaspbwa/report/1 • Not intended to duplicate content within applications or application documentation 27
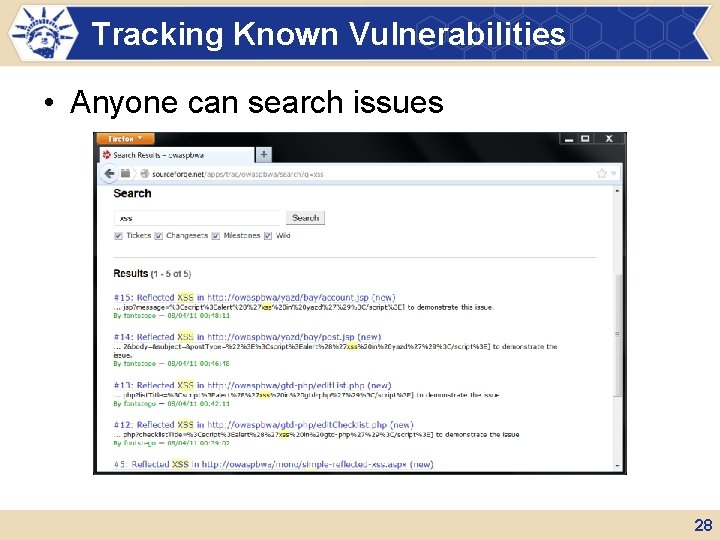
Tracking Known Vulnerabilities • Anyone can search issues 28
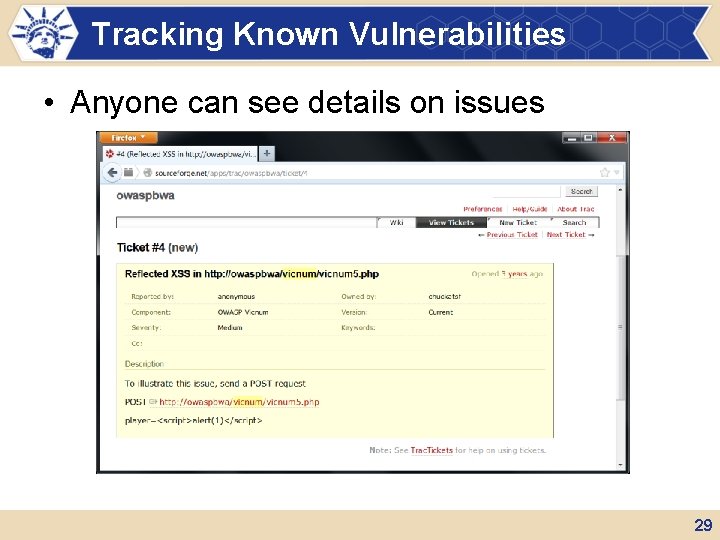
Tracking Known Vulnerabilities • Anyone can see details on issues 29
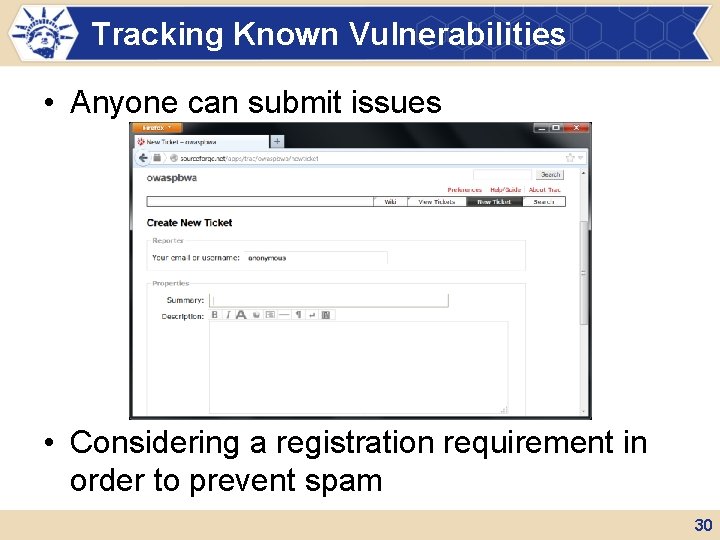
Tracking Known Vulnerabilities • Anyone can submit issues • Considering a registration requirement in order to prevent spam 30
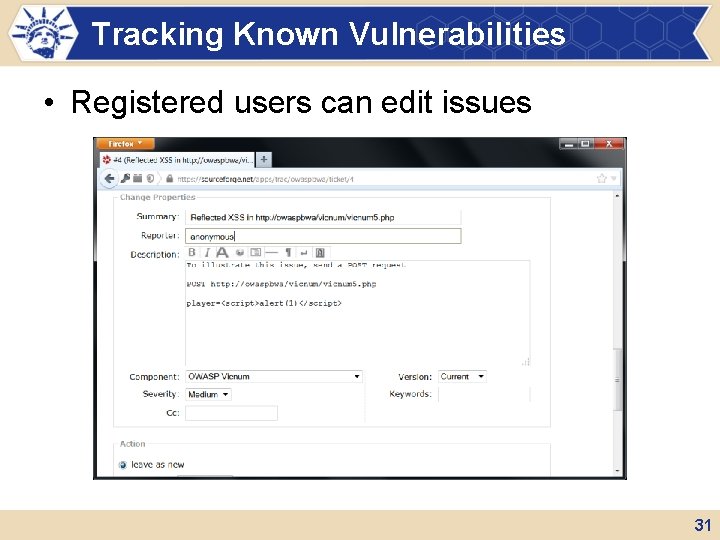
Tracking Known Vulnerabilities • Registered users can edit issues 31
The Future
Near Term • Version 1. 2 planned before the end of 2013 – Bug fixes – Add b. WAPP application – Update applications – Add ability to more easily update OWASP Mutillidae 33
Other Near Term Items • Documentation can use some work • Catalog of vulnerabilities can be expanded 34
Longer Term • Will get increasingly difficult to support modern and old applications – Due to library and other dependency issues • May move to multiple VMs • Would like to improve set of applications… 35
Wish List • More applications in more languages – Compiled Java – ASP. NET – Python – Node. js • Common frameworks and libraries • Looking for feedback from people who use VM for developer training 36
Wish List • More modern UIs – Rich Java. Script – HTML 5 – Mobile optimized sites – Adobe Flash 37
Wish List • More database backends – Postgre. SQL – SQLite – No. SQL • Opportunity for someone – Create a small data driven application with SQL injection – Make variants connected to different database backends 38
Wish List • Improved set of real applications with security issues – More applications – More modern applications 39
Wish List • More web services – Mobile apps – Rich web UIs – Desktop thick clients 40
Wish List • Updated home page on VM – More intuitive layout – Refreshed appearance – Perhaps indicate applications based on • Application’s scope • Application’s level of activity / updates • User’s role / level • Looking for feedback from users 41
What do you want to see in OWASP BWA?
We welcome any help, feedback, or broken apps you can provide!
More Information and Getting Involved • More information on the project can be found at http: //www. owaspbwa. org/ • Join our Google Group: owaspbwa • Follow us on Twitter @owaspbwa • Submit bugs and security issues to the trackers 44
- Slides: 44