OWAMP and BWCTL Installation and Configuration Jeff Boote
OWAMP and BWCTL: Installation and Configuration Jeff Boote (boote@internet 2. edu) Network Performance Workshop 10 -Jun-2005
Overview • Intro • Installation • Policy • Partitioning Resources • Classifying Connections • OWAMP configuration • owampd general configuration • owampd policy configuration • Testing and troubleshooting • BWCTL configuration • bwctld general configuration • bwctld policy configuration • Testing and troubleshooting Policies and Procedures 2005 -Mar-22 2
Review Website • Most of the information from this talk is on the web sites: http: //e 2 epi. internet 2. edu/owamp/ http: //e 2 epi. internet 2. edu/bwctl/ Policies and Procedures 2005 -Mar-22 3
Overview • Intro • Installation • Policy • Partitioning Resources • Classifying Connections • OWAMP configuration • owampd general configuration • owampd policy configuration • Testing and troubleshooting • BWCTL configuration • bwctld general configuration • bwctld policy configuration • Testing and troubleshooting Policies and Procedures 2005 -Mar-22 4
Download • http: //e 2 epi. internet 2. edu/owamp/download. html • http: //e 2 epi. internet 2. edu/bwctl/download. html Policies and Procedures 2005 -Mar-22 5
Unpack/Build/Install %gzip -cd owamp-$VERS. tar. gz | tar xf %cd owamp-$VERS %. /configure --prefix=/ami #--prefix is only needed if you don't like the default #(/usr/local on most systems) %make install Does not install configuration files (Same process for BWCTL - do it now) Policies and Procedures 2005 -Mar-22 6
Overview • Intro • Installation • Policy • Partitioning Resources • Classifying Connections • OWAMP configuration • owampd general configuration • owampd policy configuration • Testing and troubleshooting • BWCTL configuration • bwctld general configuration • bwctld policy configuration • Testing and troubleshooting Policies and Procedures 2005 -Mar-22 7
General Security Considerations (review) • Do no harm • Don’t want machines to be a source of denial of service attacks • On the other hand, would like them to be as available as possible, so as useful as possible for debugging • Avoid being an attractive nuisance • Again, obscurity lessens usefulness • But do harden machines themselves Policies and Procedures 2005 -Mar-22 8
OWAMP Security Considerations • Limit the bandwidth that can be consumed • Limit the memory/disk that can be consumed on the test host Policies and Procedures 2005 -Mar-22 9
• BWCTL Security considerations • Limit the bandwidth that can be consumed • Including protocol type (UDP/TCP) Policies and Procedures 2005 -Mar-22 10
• Partitioning Resources • Decide upon complete amount of resources it is acceptable for the test host to consume • Decide how to allocate those resources among users • How much disk space can be dedicated? Per group? • How much bandwidth total? Per group? • Keep system load in mind as well as network. The data accuracy will suffer if the system is too loaded. Policies and Procedures 2005 -Mar-22 11
Resources Allocated Using Hierarchical Limitclasses • Users are grouped into hierarchical limitclasses • One parent-less class allowed, it defines the total amount of resources available • When limitclasses are defined, limits of the one and only parent are inherited • When consumable resources are requested, the limits of the limitclass and all parent limitclasses must be satisfied (memory/bandwidth/timeslots) Policies and Procedures 2005 -Mar-22 12
Example organization of limitclasses • Classifications of users into limitclasses • Root: Complete set of resources available • Hostile: Used to “jail” hostile users • NOC: Super-user limits • Peer: Extended limits for peer tests • Normal: Reasonable limits for end-users • Open == Conservative limits for *anyone* Policies and Procedures 2005 -Mar-22 13
Example Allocation for bandwidth (BWCTL) • Available per limitclass • Root: Complete set of resources available • Hostile: No tests allowed • NOC: Inherit Root limits • Peer: Limit UDP to 500 m • Could make children limitclasses for each individual peer if lower limits should be applied to some • Normal: UDP not needed for most end users • Open: No tests allowed Policies and Procedures 2005 -Mar-22 14
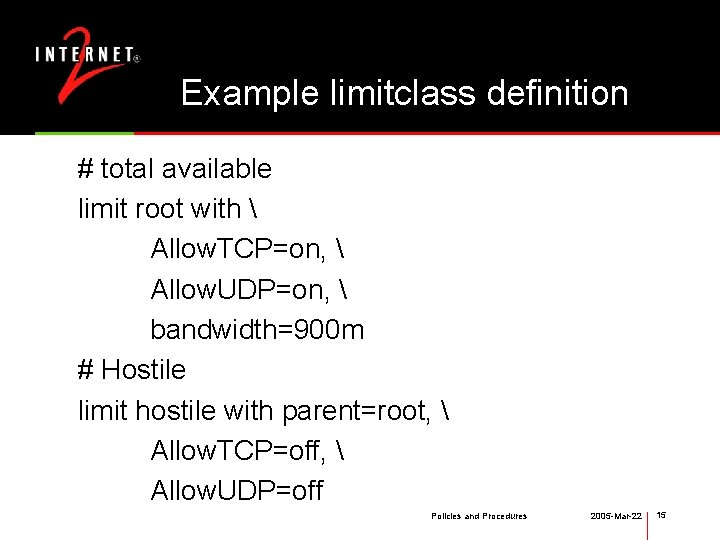
Example limitclass definition # total available limit root with Allow. TCP=on, Allow. UDP=on, bandwidth=900 m # Hostile limit hostile with parent=root, Allow. TCP=off, Allow. UDP=off Policies and Procedures 2005 -Mar-22 15
Classifying Connections • IP/netmask • The IP address of the client is matched against a list of IP netmask specified subnets and assigned to a limitclass based on the address of the client • Username and AES key • Client specifies a username, the server must already know the associated AES key • AES key is used as a symmetric session key – Client and Server use the key as a shared secret Policies and Procedures 2005 -Mar-22 16
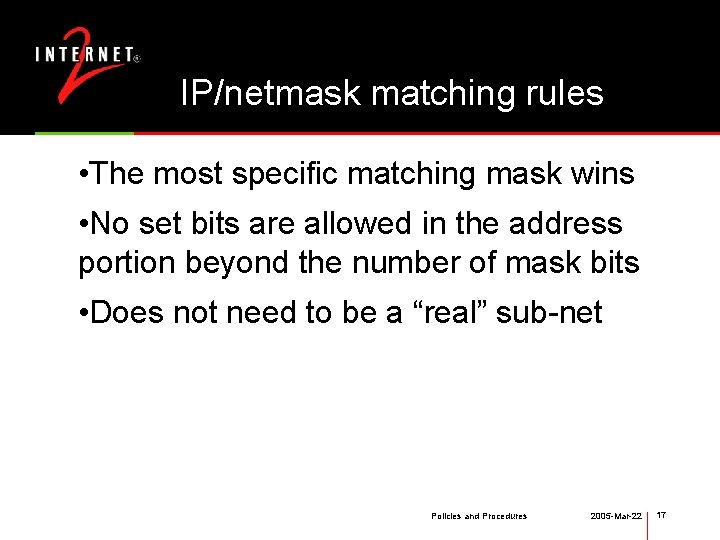
IP/netmask matching rules • The most specific matching mask wins • No set bits are allowed in the address portion beyond the number of mask bits • Does not need to be a “real” sub-net Policies and Procedures 2005 -Mar-22 17
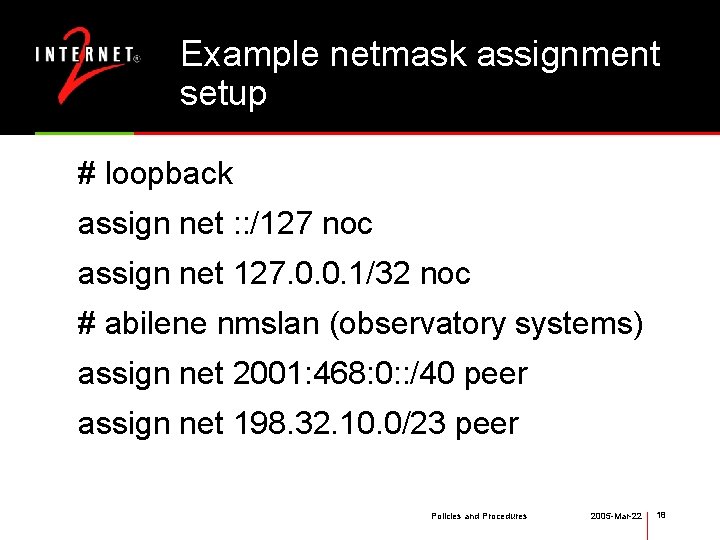
Example netmask assignment setup # loopback assign net : : /127 noc assign net 127. 0. 0. 1/32 noc # abilene nmslan (observatory systems) assign net 2001: 468: 0: : /40 peer assign net 198. 32. 10. 0/23 peer Policies and Procedures 2005 -Mar-22 18
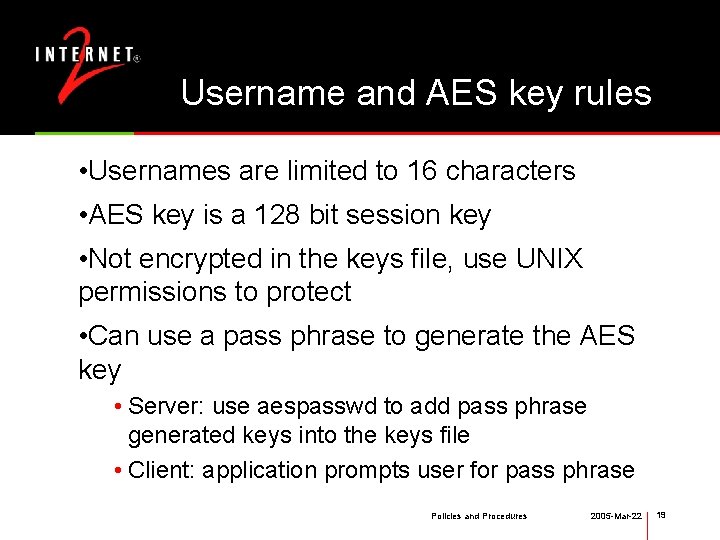
Username and AES key rules • Usernames are limited to 16 characters • AES key is a 128 bit session key • Not encrypted in the keys file, use UNIX permissions to protect • Can use a pass phrase to generate the AES key • Server: use aespasswd to add pass phrase generated keys into the keys file • Client: application prompts user for pass phrase Policies and Procedures 2005 -Mar-22 19
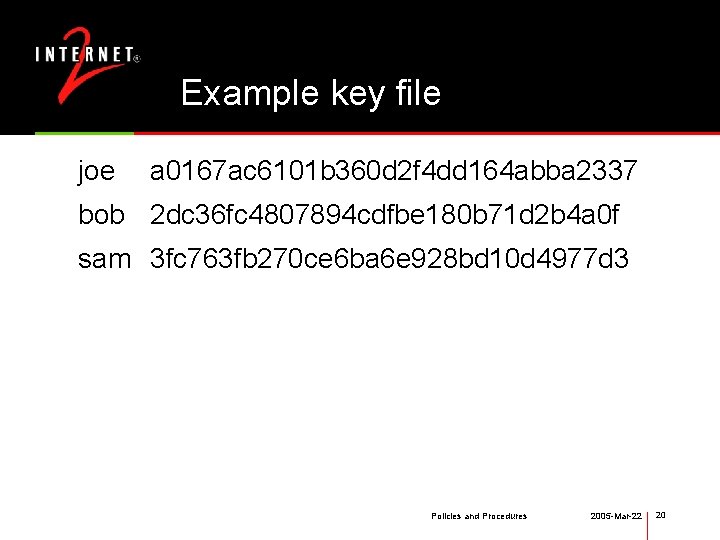
Example key file joe a 0167 ac 6101 b 360 d 2 f 4 dd 164 abba 2337 bob 2 dc 36 fc 4807894 cdfbe 180 b 71 d 2 b 4 a 0 f sam 3 fc 763 fb 270 ce 6 ba 6 e 928 bd 10 d 4977 d 3 Policies and Procedures 2005 -Mar-22 20
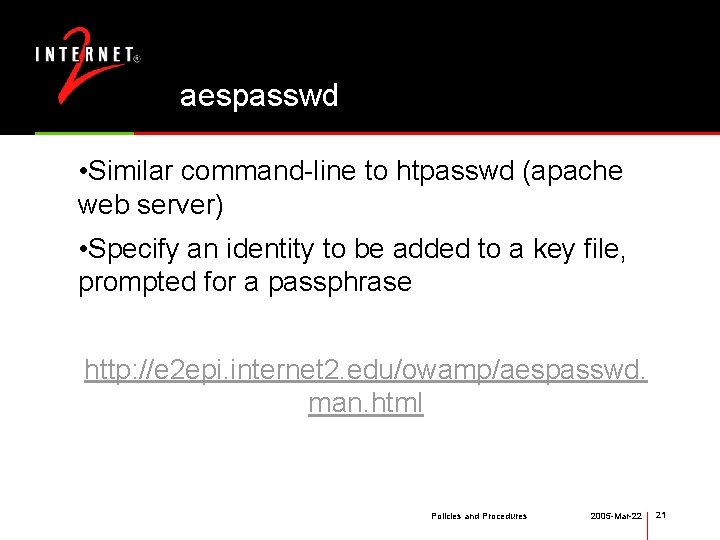
aespasswd • Similar command-line to htpasswd (apache web server) • Specify an identity to be added to a key file, prompted for a passphrase http: //e 2 epi. internet 2. edu/owamp/aespasswd. man. html Policies and Procedures 2005 -Mar-22 21
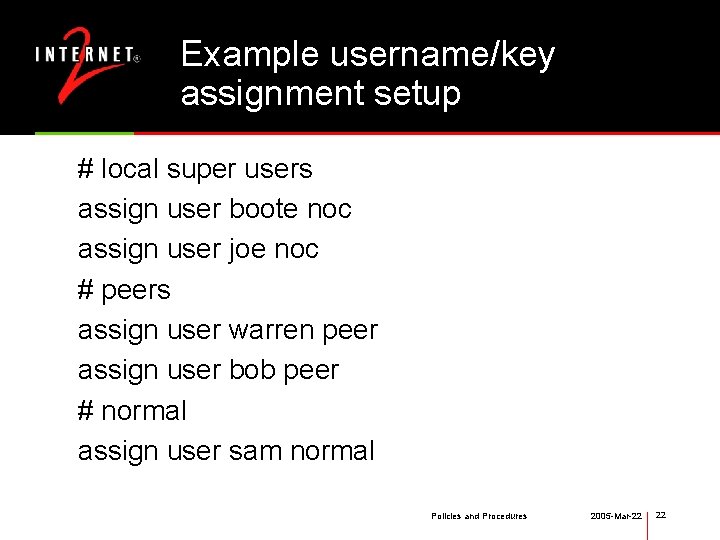
Example username/key assignment setup # local super users assign user boote noc assign user joe noc # peers assign user warren peer assign user bob peer # normal assign user sam normal Policies and Procedures 2005 -Mar-22 22
Overview • Intro • Installation • Policy • Partitioning Resources • Classifying Connections • OWAMP configuration • owampd general configuration • owampd policy configuration • Testing and troubleshooting • BWCTL configuration • bwctld general configuration • bwctld policy configuration • Testing and troubleshooting Policies and Procedures 2005 -Mar-22 23
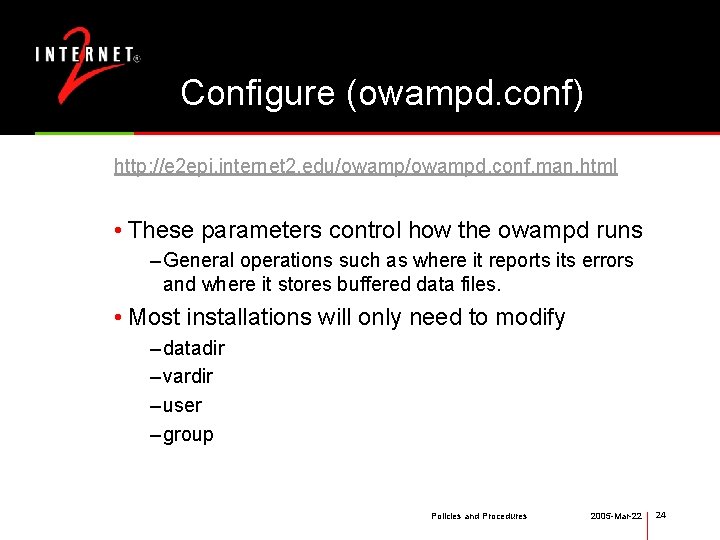
Configure (owampd. conf) http: //e 2 epi. internet 2. edu/owampd. conf. man. html • These parameters control how the owampd runs – General operations such as where it reports its errors and where it stores buffered data files. • Most installations will only need to modify – datadir – vardir – user – group Policies and Procedures 2005 -Mar-22 24
Configure (owampd. limits) http: //e 2 epi. internet 2. edu/owampd. limits. man. html Two parts: 1. Authentication Who is making the request? 2. Authorization What is that identity allowed to do? Policies and Procedures 2005 -Mar-22 25
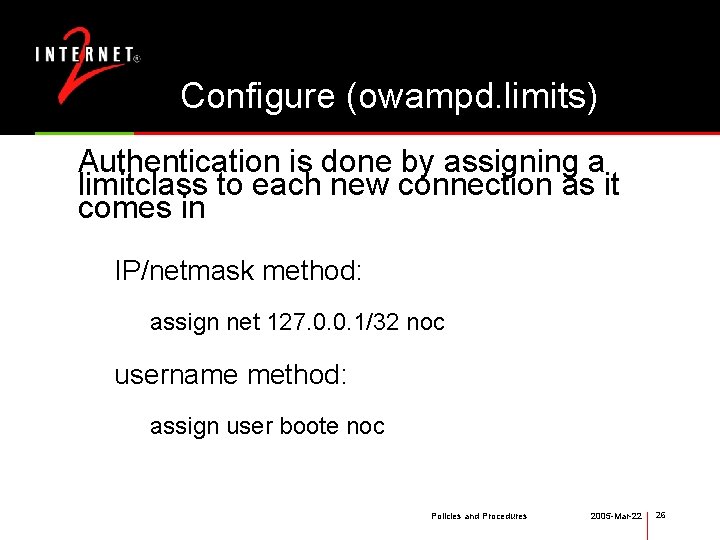
Configure (owampd. limits) Authentication is done by assigning a limitclass to each new connection as it comes in IP/netmask method: assign net 127. 0. 0. 1/32 noc username method: assign user boote noc Policies and Procedures 2005 -Mar-22 26
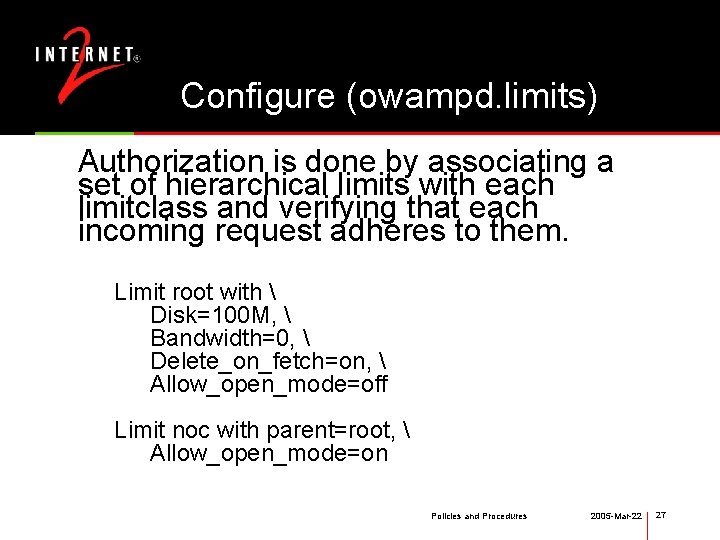
Configure (owampd. limits) Authorization is done by associating a set of hierarchical limits with each limitclass and verifying that each incoming request adheres to them. Limit root with Disk=100 M, Bandwidth=0, Delete_on_fetch=on, Allow_open_mode=off Limit noc with parent=root, Allow_open_mode=on Policies and Procedures 2005 -Mar-22 27
Configure (owampd. keys) http: //e 2 epi. internet 2. edu/owampd. keys. man. html http: //e 2 epi. internet 2. edu/owamp/aespasswd. man. html • Used to hold the username/AESKey pairing information for the daemon. • Use the aespasswd program to generate a key if you want a passphrase associated with it Policies and Procedures 2005 -Mar-22 28
Starting owampd http: //e 2 epi. internet 2. edu/owampd. man. html • start in foreground during testing • /usr/local/bin/owampd -c /usr/local/etc -Z Policies and Procedures 2005 -Mar-22 29
Testing (owping) http: //e 2 epi. internet 2. edu/owamp/owping. man. html Simple localhost test: • /ami/bin/owping localhost Test to Internet 2 test host: • /ami/bin/owping nmsy-aami. abilene. ucaid. edu Others: • /usr/local/bin/owping otherhost Policies and Procedures 2005 -Mar-22 30
Troubleshooting • No control connection • Control connection denied • 100% packet loss in test streams • Clock offset (ntpq, loss timeout) • Firewall Policies and Procedures 2005 -Mar-22 31
Overview • Intro • Installation • Policy • Partitioning Resources • Classifying Connections • OWAMP configuration • owampd general configuration • owampd policy configuration • Testing and troubleshooting • BWCTL configuration • bwctld general configuration • bwctld policy configuration • Testing and troubleshooting Policies and Procedures 2005 -Mar-22 32
Configure (bwctld. conf) http: //e 2 epi. internet 2. edu/bwctld. conf. man. html • These parameters control how the bwctld runs • General operations such as where it reports its errors and other daemon wide configuration options • Most installations will only need to modify • vardir • user • group Policies and Procedures 2005 -Mar-22 33
Configure (bwctld. limits) http: //e 2 epi. internet 2. edu/bwctld. limits. man. html Two parts: 1. Authentication Who is making the request? 2. Authorization What is that identity allowed to do? Policies and Procedures 2005 -Mar-22 34
Configure (bwctld. limits) Authentication is done by assigning a limitclass to each new connection as it comes in IP/netmask method: assign net 127. 0. 0. 1/32 noc username method: assign user boote noc Policies and Procedures 2005 -Mar-22 35
Configure (bwctld. limits) Authorization is done by associating a set of hierarchical limits with each limitclass and verifying that each incoming request adheres to them. Limit root with bandwidth=900 m, duration=0, allow_tcp=on, allow_udp=on, allow_open_mode=off Limit noc with parent=root, Allow_open_mode=on Policies and Procedures 2005 -Mar-22 36
Configure (bwctld. keys) http: //e 2 epi. internet 2. edu/bwctl/owampd. keys. man. html http: //e 2 epi. internet 2. edu/bwctl/aespasswd. man. html • Used to hold the username/AESKey pairing information for the daemon. • Use the aespasswd program to generate a key if you want a passphrase associated with it Policies and Procedures 2005 -Mar-22 37
Testing bwctl http: //e 2 epi. internet 2. edu/bwctl. man. html Try to create a test from the Internet 2 test host: % /ami/bin/bwctl -s nmsx-aami. abilene. ucaid. edu A AESKEY jimbob Try to create a test toward the Internet 2 test host: % /ami/bin/bwctl -c nmsx-aami. abilene. ucaid. edu A AESKEY jimbob Policies and Procedures 2005 -Mar-22 38
Starting bwctld http: //e 2 epi. internet 2. edu/bwctld. man. html • start in foreground during testing • /usr/local/bin/bwctld -c /usr/local/etc -Z Policies and Procedures 2005 -Mar-22 39
Testing bwctl (With Your Daemon) If there is a local daemon running, the bwctl client will automatically connect to it to schedule the local resources instead of running the test directly. (The same command-lines are used from above to test this. ) Try to create a test from the Internet 2 test host: % /ami/bin/bwctl -s nmsx-aami. abilene. ucaid. edu A AESKEY jimbob Try to create a test toward the Internet 2 test host: % /ami/bin/bwctl -c nmsx-aami. abilene. ucaid. edu A AESKEY jimbob Policies and Procedures 2005 -Mar-22 40
Testing bwctl (3 -Party) The bwctl client can be used to request a test between 2 other hosts If you have the same identity on the two hosts: % /ami/bin/bwctl -s sendhost -c recvhost -A A AESKEY jimbob If you have different identities, you must append the auth args after the host: % /ami/bin/bwctl -s sendhost A AESKEY jim -c recvhost A AESKEY bob Policies and Procedures 2005 -Mar-22 41
Troubleshooting • No control connection • Control connection denied • Initial control connection works - peer connection fails • Scheduling problems • Iperf connections fail • Iperf results are bad Policies and Procedures 2005 -Mar-22 42
Questions? /Review? • Intro • Installation • Policy • Partitioning Resources • Classifying Connections • OWAMP configuration • owampd general configuration • owampd policy configuration • Testing and troubleshooting • BWCTL configuration • bwctld general configuration • bwctld policy configuration • Testing and troubleshooting Policies and Procedures 2005 -Mar-22 43

www. internet 2. edu 2005 -Mar-22 44
- Slides: 44