Operating Systems and Virtual Machines Security Eng Hector
![Linux / Unix Access Control Lists • [d[efault]: ] [u[ser]: ]uid [: perms] – Linux / Unix Access Control Lists • [d[efault]: ] [u[ser]: ]uid [: perms] –](https://slidetodoc.com/presentation_image_h/8deec0fe026f3c866fb7233c22eefa79/image-24.jpg)
- Slides: 46
Operating Systems and Virtual Machines Security Eng. Hector M Lugo-Cordero, MS CIS 4361 Secure OS Admin
Problem • Client / Server infrastructure very common among most organizations – Clients provide access to system – Servers run the systems • Software vulnerabilities (e. g. buffer overflow) and malware need to be considered • Follow a framework detailed by NIST (National Institute of Standards and Technology) to provide a secure environment, even when we know it is not there
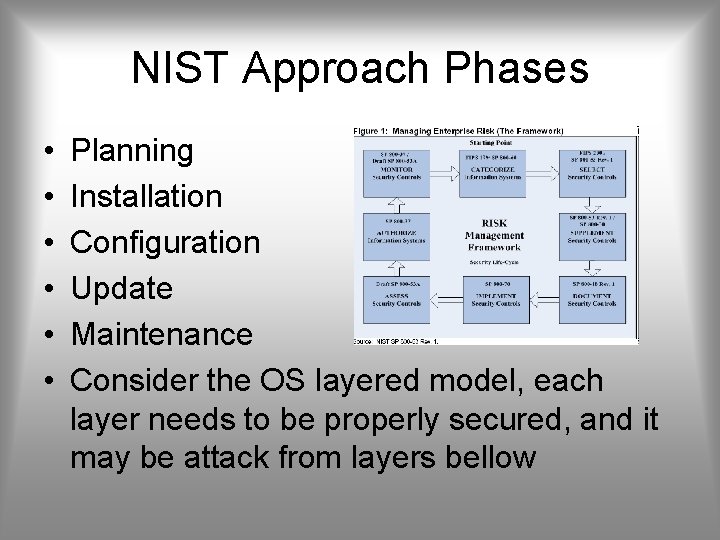
NIST Approach Phases • • • Planning Installation Configuration Update Maintenance Consider the OS layered model, each layer needs to be properly secured, and it may be attack from layers bellow
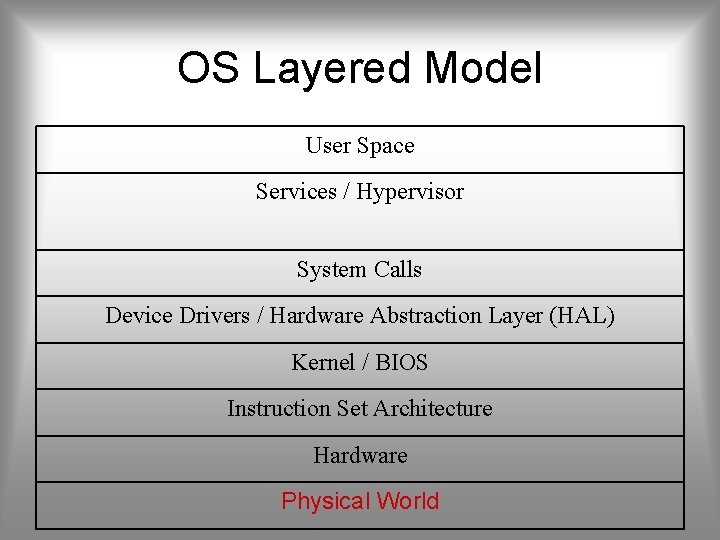
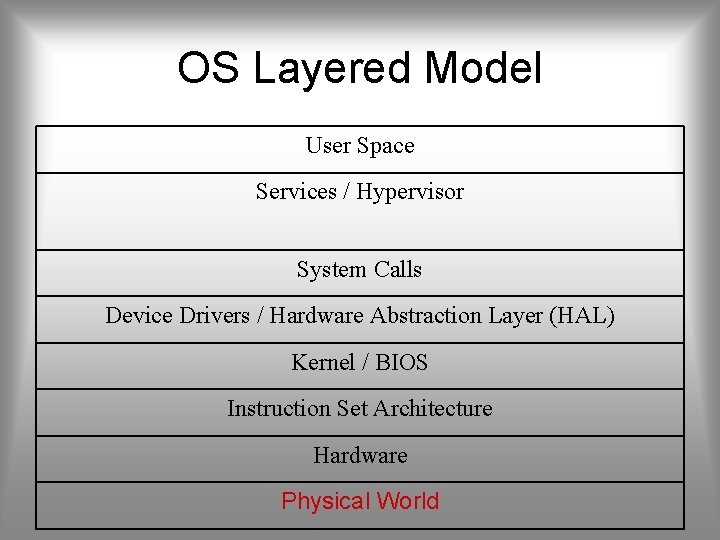
OS Layered Model User Space Services / Hypervisor System Calls Device Drivers / Hardware Abstraction Layer (HAL) Kernel / BIOS Instruction Set Architecture Hardware Physical World
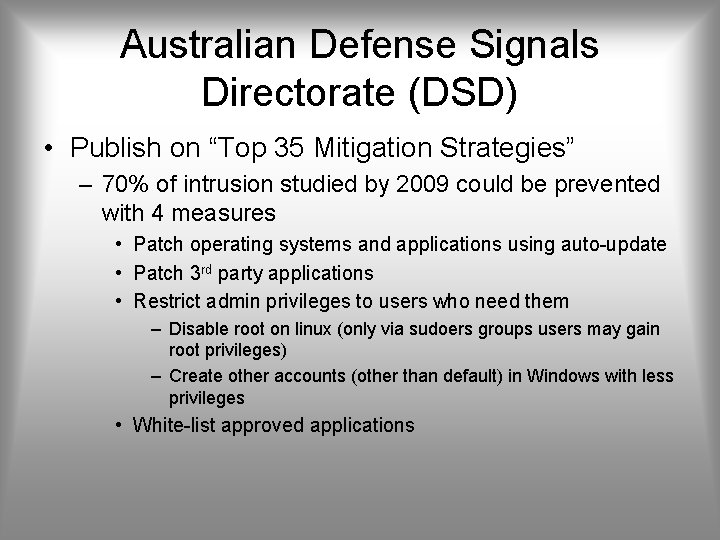
Australian Defense Signals Directorate (DSD) • Publish on “Top 35 Mitigation Strategies” – 70% of intrusion studied by 2009 could be prevented with 4 measures • Patch operating systems and applications using auto-update • Patch 3 rd party applications • Restrict admin privileges to users who need them – Disable root on linux (only via sudoers groups users may gain root privileges) – Create other accounts (other than default) in Windows with less privileges • White-list approved applications
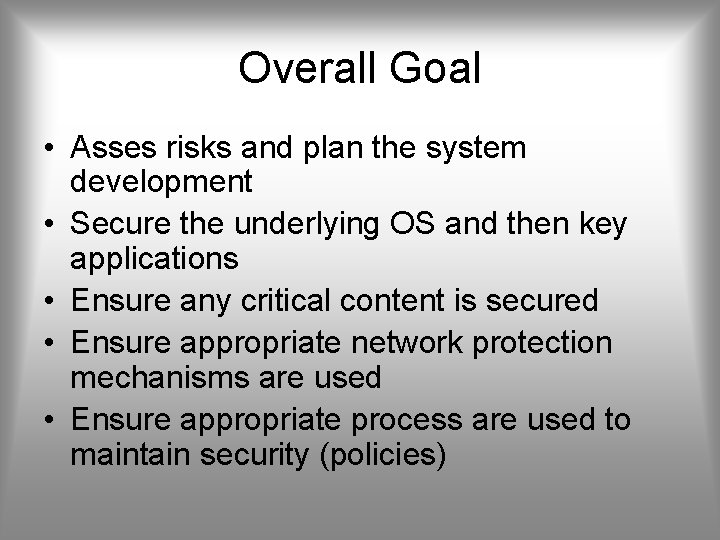
Overall Goal • Asses risks and plan the system development • Secure the underlying OS and then key applications • Ensure any critical content is secured • Ensure appropriate network protection mechanisms are used • Ensure appropriate process are used to maintain security (policies)
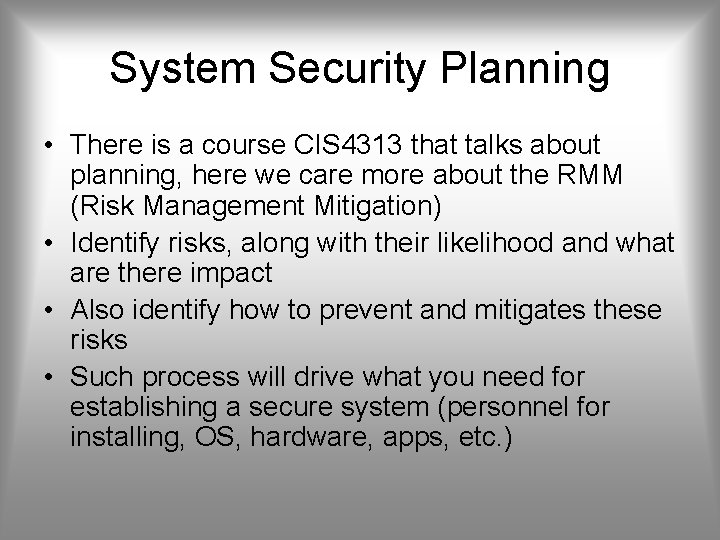
System Security Planning • There is a course CIS 4313 that talks about planning, here we care more about the RMM (Risk Management Mitigation) • Identify risks, along with their likelihood and what are there impact • Also identify how to prevent and mitigates these risks • Such process will drive what you need for establishing a secure system (personnel for installing, OS, hardware, apps, etc. )
Things to keep in mind • Purpose of the system, type of information stored, applications and services provided • Users of the system and their privileges • How are users authenticated • How information on system is managed • What other hosts / DBs are accessed by system • Who will manage system and how (remote or local) • Additional measures such as: firewall, anti-virus, logging
Hardening the OS • Default OS configurations are for ease of use • Measures have to be done at all stages – Installing and patching – Configuring • Remove unnecessary applications, services and protocols • Users, groups, controls and privileges – Install additional software (anti-virus, firewall, intrusion detection system, etc. ) – Test Security
Installing and Patching • Installation – Machines should not connect to network until secured • However removable media may be infected as well – Limited network (firewall) is acceptable, ideally: • No inbound connections • Only out to certain key sites – Install only required services and drivers (from trusted sources) – Set up automatic updates (only if update time is not an issue) • Booting – Protect BIOS changes with password – Disable some bootable media – Cryptographic hard drives? Pros and Cons
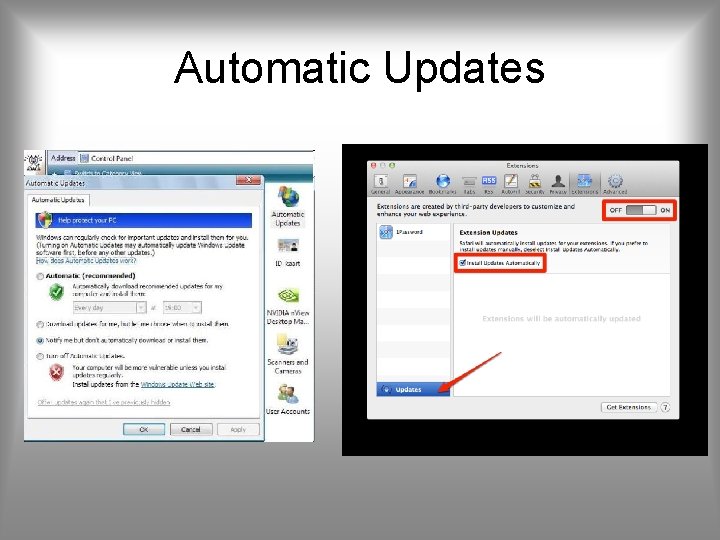
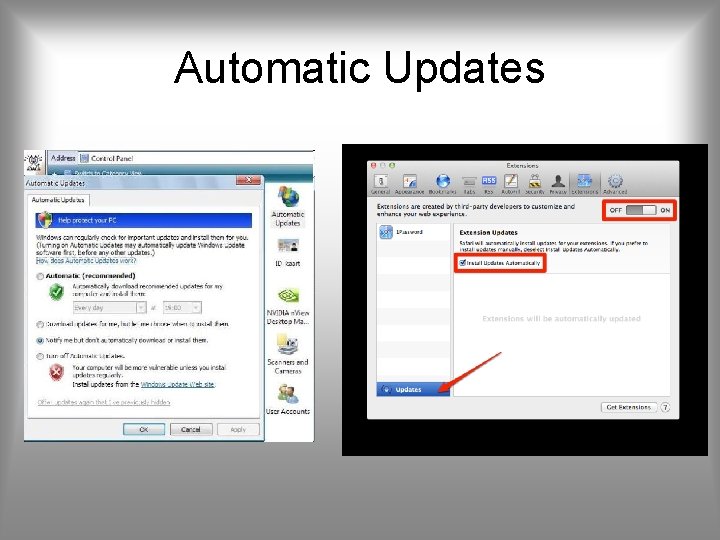
Automatic Updates
Remove Unnecessary Support • Software have vulnerabilities, hence more software = more vulnerabilities • Better to not install it at all – Uninstallers sometimes fail to clean all dependency – Disabled software may be enabled by an attacker upon control acquisition • Disabling can be done via msconfig command (Windows), yast or equivalent (Linux) or Control Panel (Windows / Linux)
Configure U/G Authentication • Define user types and privileges – Admin (ideally only temporary) – Normal – Limited • Authentication – Force default password change – Password definition – Password lifespan • Remove or disable old accounts • Allow for remote connections?
Additional Security and Testing • Anti-virus • Firewalls, IDS, IPS • White list – If attackers manage to install a program what will happen? • Run some test cases which attempt to break security (stress testing), good hackers make a lot of money here
Security Testing
Application Security • Configure applications properly • Use encryption when possible as seen earlier – For storing – For transmit (SSH connections) • Limit privileges as with users – Remember what we have said about security in Android, Blackberry, and i. Phone • Applications may provide backdoors if not configured properly
Maintenance • Now that system is set, keep it secure • This involves – Monitoring and analyzing logging information – Performing regular backups – Recovering from security compromises – Regular testing of security – Patch, update, and revise critical software
Logging • Keep a record of important events in the computer • Problems – Need to make sure to have enough space – Manual analysis is hard, so these logs should contain a format such that a program (e. g. in Perl) can parse messages
Data Backup • Backup is the act of creating copies of information such that it may be recovered • Archive is to keep these backups for a long period of time in order to meet some legal aspects • Should the backup be kept online or offline? – Online makes easier access, faster recover – Offline is more secure, harder to recover – Why not both? : Users should keep their own offline backups, in case online backup gets removed • Data may be lost accidentally (hardware failures, human mistake) or intentionally
Backups
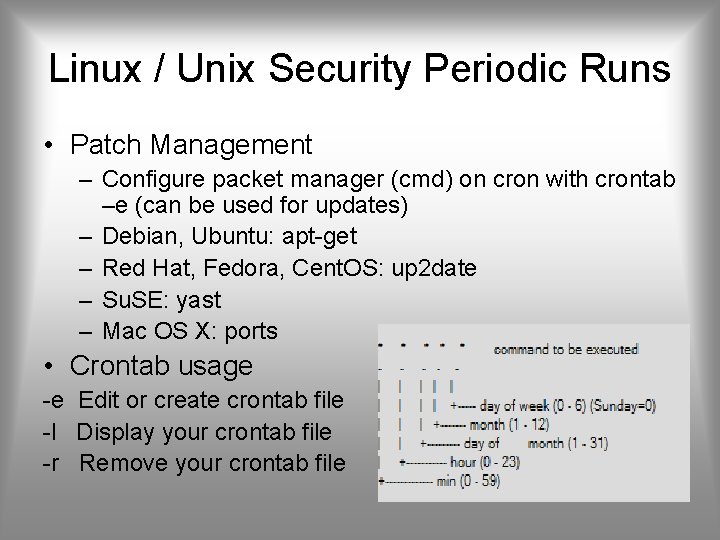
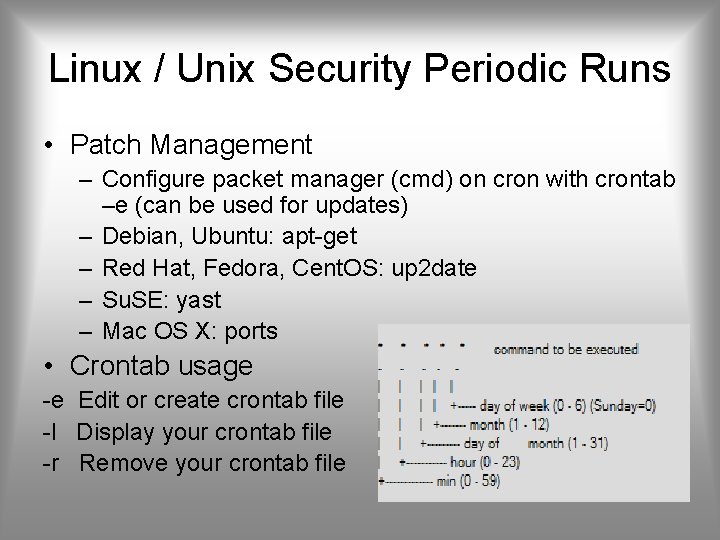
Linux / Unix Security Periodic Runs • Patch Management – Configure packet manager (cmd) on cron with crontab –e (can be used for updates) – Debian, Ubuntu: apt-get – Red Hat, Fedora, Cent. OS: up 2 date – Su. SE: yast – Mac OS X: ports • Crontab usage -e Edit or create crontab file -l Display your crontab file -r Remove your crontab file
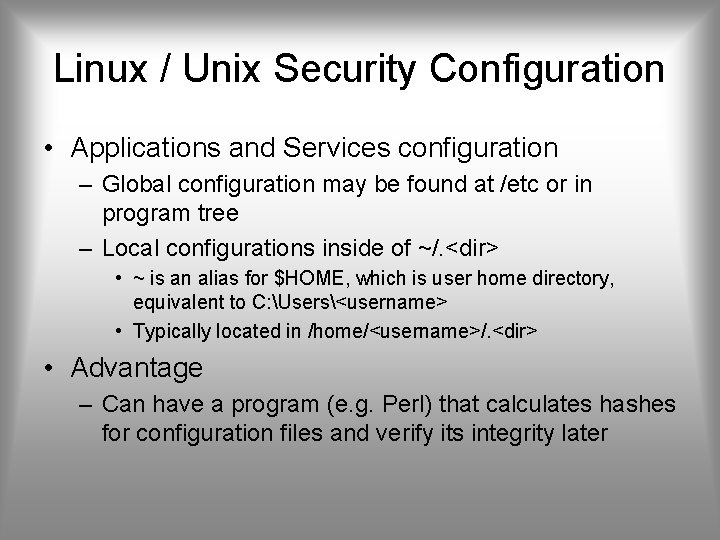
Linux / Unix Security Configuration • Applications and Services configuration – Global configuration may be found at /etc or in program tree – Local configurations inside of ~/. <dir> • ~ is an alias for $HOME, which is user home directory, equivalent to C: Users<username> • Typically located in /home/<username>/. <dir> • Advantage – Can have a program (e. g. Perl) that calculates hashes for configuration files and verify its integrity later
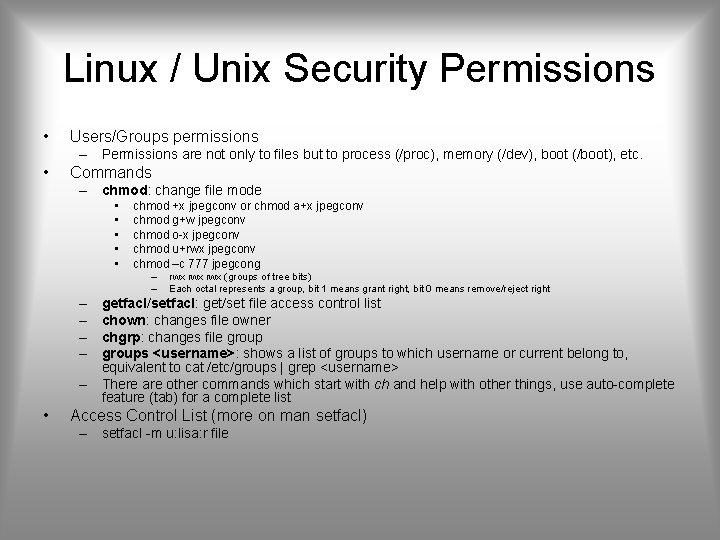
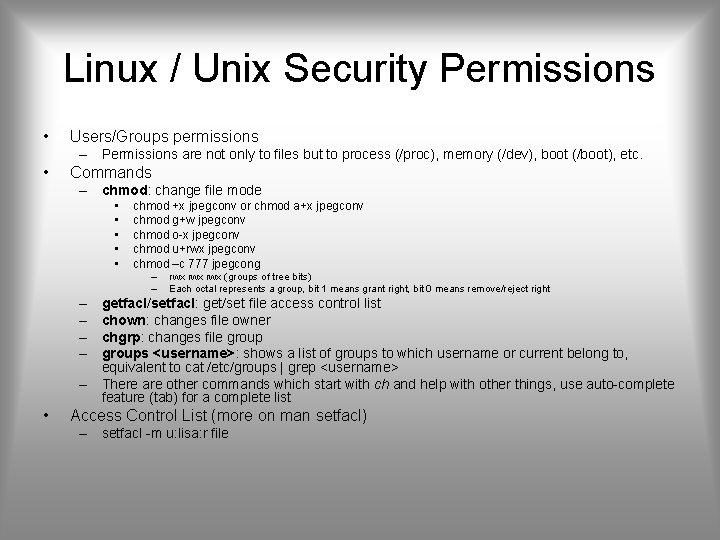
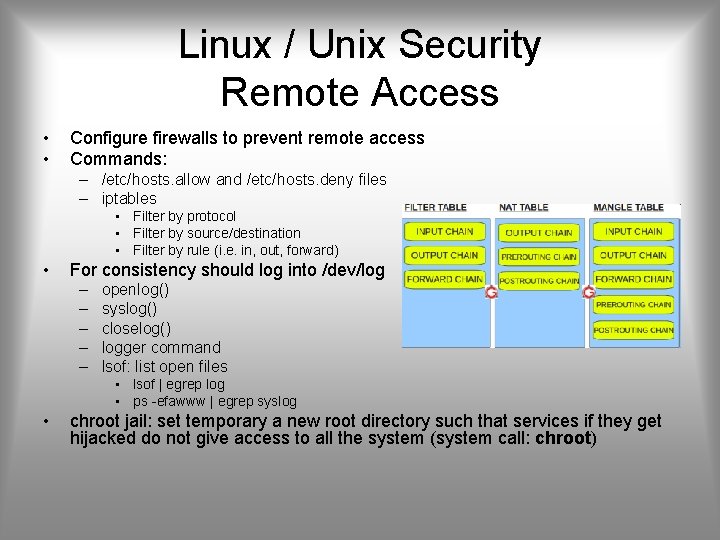
Linux / Unix Security Permissions • Users/Groups permissions – Permissions are not only to files but to process (/proc), memory (/dev), boot (/boot), etc. • Commands – chmod: change file mode • • • chmod +x jpegconv or chmod a+x jpegconv chmod g+w jpegconv chmod o-x jpegconv chmod u+rwx jpegconv chmod –c 777 jpegcong – – – – • rwx rwx (groups of tree bits) Each octal represents a group, bit 1 means grant right, bit 0 means remove/reject right getfacl/setfacl: get/set file access control list chown: changes file owner chgrp: changes file groups <username>: shows a list of groups to which username or current belong to, equivalent to cat /etc/groups | grep <username> There are other commands which start with ch and help with other things, use auto-complete feature (tab) for a complete list Access Control List (more on man setfacl) – setfacl -m u: lisa: r file
![Linux Unix Access Control Lists default user uid perms Linux / Unix Access Control Lists • [d[efault]: ] [u[ser]: ]uid [: perms] –](https://slidetodoc.com/presentation_image_h/8deec0fe026f3c866fb7233c22eefa79/image-24.jpg)
Linux / Unix Access Control Lists • [d[efault]: ] [u[ser]: ]uid [: perms] – Permissions of a named user. Permissions of the file owner if uid is empty. • [d[efault]: ] g[roup]: gid [: perms] – Permissions of a named group. Permissions of the owning group if gid is empty. • [d[efault]: ] m[ask][: ] [: perms] – Effective rights mask • [d[efault]: ] o[ther][: ] [: perms] – Permissions of others.
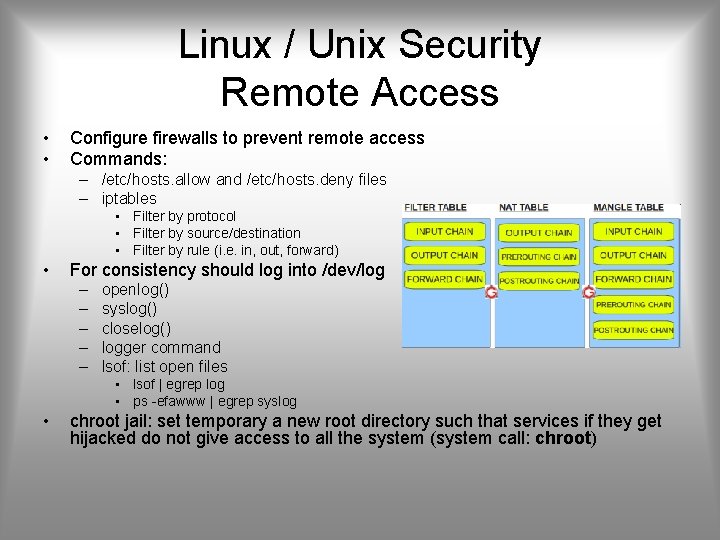
Linux / Unix Security Remote Access • • Configure firewalls to prevent remote access Commands: – /etc/hosts. allow and /etc/hosts. deny files – iptables • Filter by protocol • Filter by source/destination • Filter by rule (i. e. in, out, forward) • For consistency should log into /dev/log – – – openlog() syslog() closelog() logger command lsof: list open files • lsof | egrep log • ps -efawww | egrep syslog • chroot jail: set temporary a new root directory such that services if they get hijacked do not give access to all the system (system call: chroot)
Linux / Unix Security Testing • Nessus: security scanning and vulnerability testing (like a fuzzer) • Tripwire: builds and check integrity of files (md 5 compares) • Nmap: can check for surrounding network services
Windows Security • Use automatic updates specially for – Windows – Adobe Acrobat Reader and Flash Plugin – Java • Users are defined with a Security ID (SID) and information such as passwords may be stored at Security Account Manager (SAM) • System restore • User Account Control to treat users with admin only as admin when required, otherwise as normal (Vista and later)
Windows Registry • Hard to maintain • Easy to access • May use a specific application hiding complex information from administrator • May use regedit to see everything – Useful to have an application that queues and monitors registry changes, such that they need to get approved before proceeding
Other Windows Security • • Anti-virus Anti-spyware Personal firewall Encrypting File Systems – Local Security Policy • Bit. Locker: full disk encryption with AES • More on Control Panel System Security • Microsoft Baseline Security Analyzer – Checks for minimal recommended requirements in a system – Its free – Shavlik Net. Chk Limited for legacy
Virtualization • Virtualization: defines an isomorphism that maps a virtual guest system to a physical host • Adds another degree of freedom by enabling multiple resource managers and controlled sharing. – Adds a level of indirection • Can virtualize a single resource (DRAM, Disks) or an entire system (machine). – may create one or more virtual objects. • Virtual Machine: Add virtualization layer which transforms the physical machine into the desired virtual architecture.
Virtualization (Some Terms) • Hypervisor/Virtual Machine Monitor: manages physical resource allocation among VMs • Application Virtualization: allow an application written for one environment, to run at others – Java –. NET • Full Virtualization: allows to run a full OS on a machine – Native Virtualization: runs without a host OS – Hosted Virtualization: requires to have an OS running below it
Some Virtual Machines • • • Oracle Virtual. Box Microsoft Virtual PC (formerly Virtual PC) VMware Xen Hypervisor Parallel Desktop (popular on MAC)
History of Virtualization • 1960’s – 1964 - Birth of virtualization with the IBM CP series which was a test bed for the IBM S/360 system. Provided full hardware virtualization with the ability to run 14 OS instances. – 1965 – IBM begins shipping S/360 systems, the first mass production multi-purpose mainframe. First machine to use virtual memory for ‘infinite’ storage capacity.
History of Virtualization • 1970’s – IBM S/370, more of the same • 1980’s – 1987 - Merge/386 becomes available allowing emulation of Intel 8086 instructions on Intel 80286 & 80386 CPUs. Could run any 8086 coded OS but was typical found running Microsoft MS-DOS.
History of Virtualization • 1990’s – 1997 – Virtual PC released for Macintosh – 1998 – VMware released for Windows – 1999 – Citrix Presentation Server released for Windows • 2001 – Virtual PC released for Windows – VMware Server released (first x 86 server VM)
History of Virtualization • 2003 – Xen Hypervisor released (Open Source x 86) – MS buys Virtual PC & releases MS Virtual PC 2004 • 2005 – MS releases Virtual Server 2005 (guest machines limited to 32 bit, 4 GB of RAM, & 1 CPU) – Intel’s VT and AMD’s AMD-V hardware virtualization added to Server and Desktop CPUs
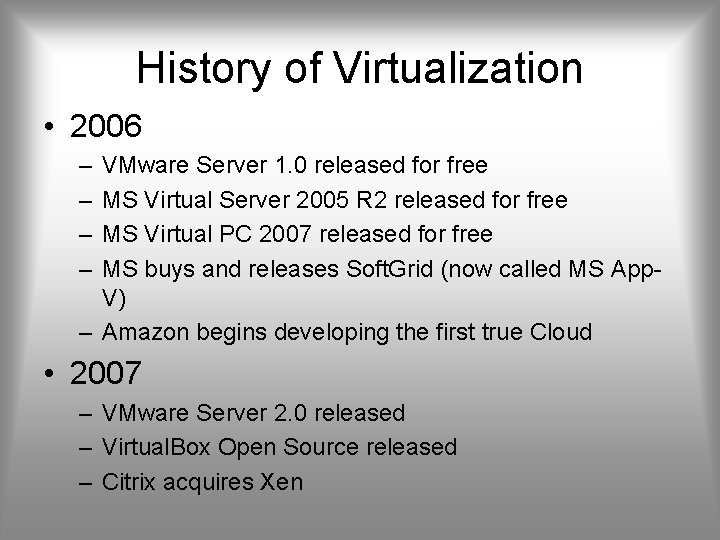
History of Virtualization • 2006 – – VMware Server 1. 0 released for free MS Virtual Server 2005 R 2 released for free MS Virtual PC 2007 released for free MS buys and releases Soft. Grid (now called MS App. V) – Amazon begins developing the first true Cloud • 2007 – VMware Server 2. 0 released – Virtual. Box Open Source released – Citrix acquires Xen
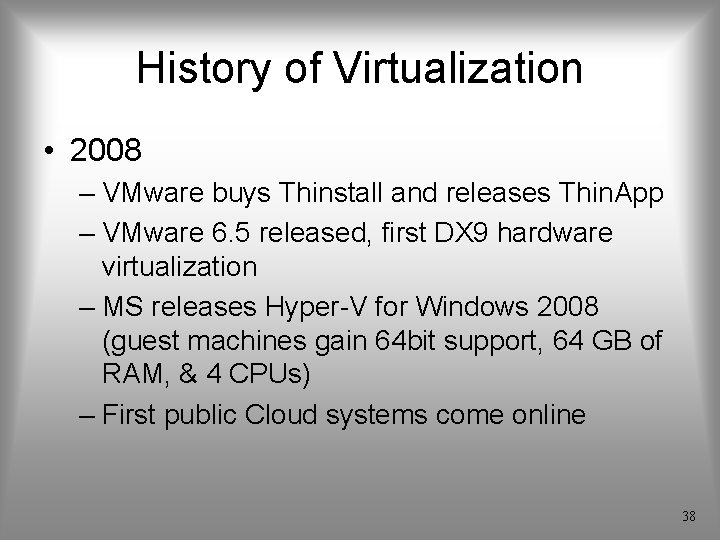
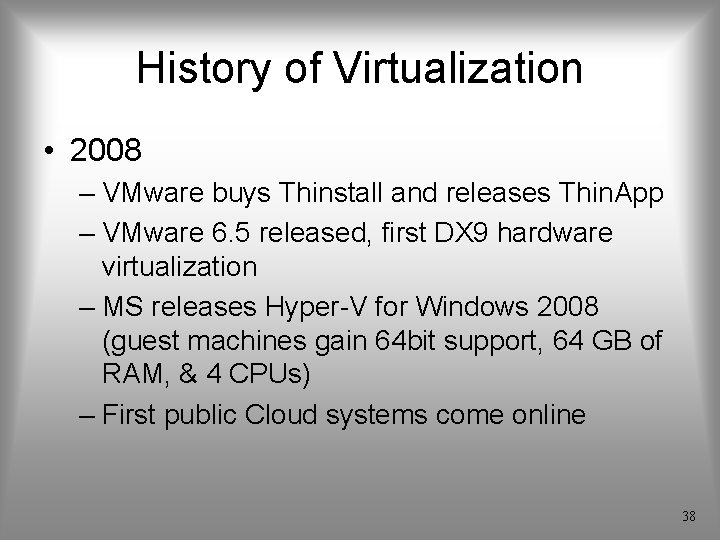
History of Virtualization • 2008 – VMware buys Thinstall and releases Thin. App – VMware 6. 5 released, first DX 9 hardware virtualization – MS releases Hyper-V for Windows 2008 (guest machines gain 64 bit support, 64 GB of RAM, & 4 CPUs) – First public Cloud systems come online 38
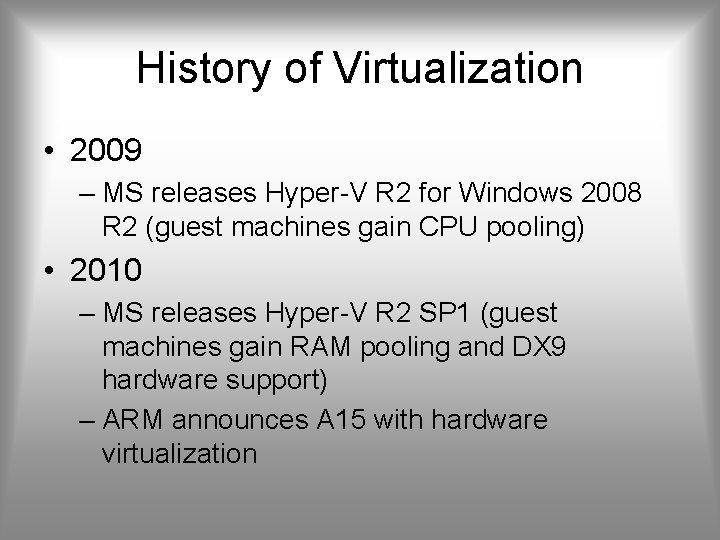
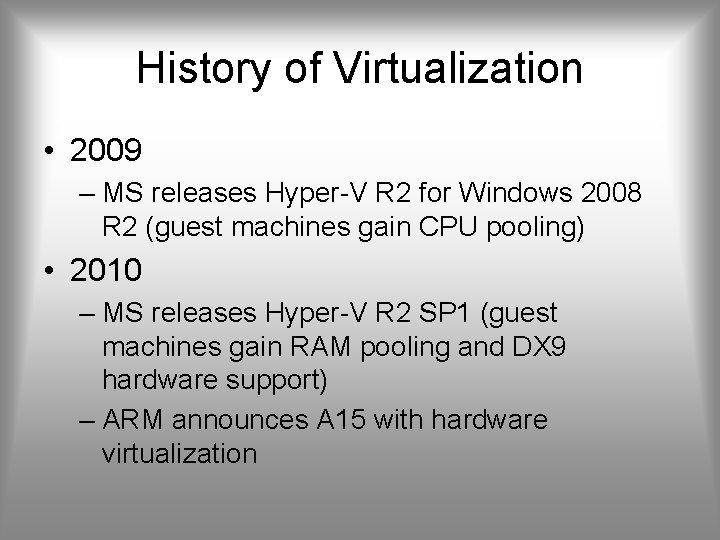
History of Virtualization • 2009 – MS releases Hyper-V R 2 for Windows 2008 R 2 (guest machines gain CPU pooling) • 2010 – MS releases Hyper-V R 2 SP 1 (guest machines gain RAM pooling and DX 9 hardware support) – ARM announces A 15 with hardware virtualization
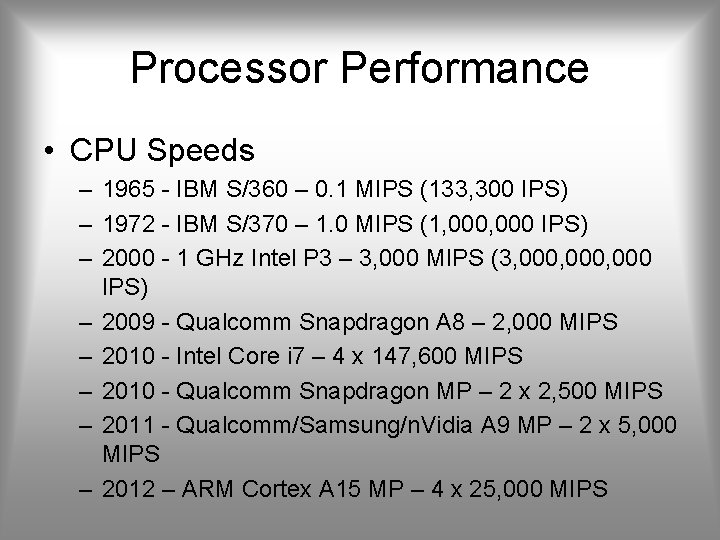
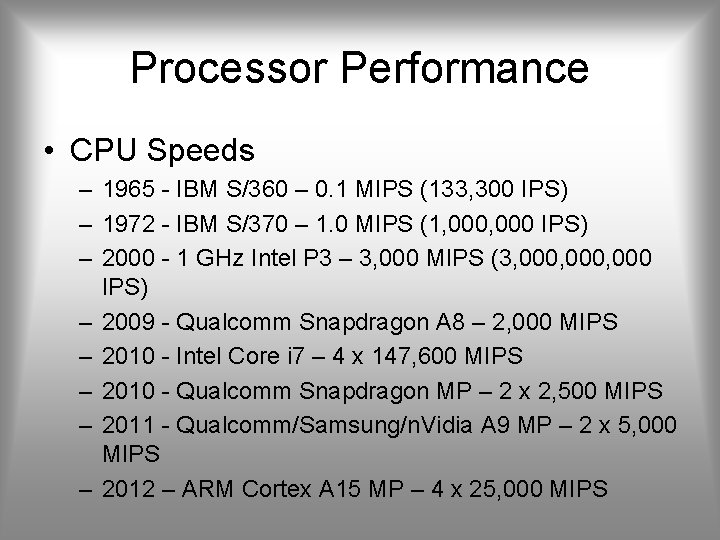
Processor Performance • CPU Speeds – 1965 - IBM S/360 – 0. 1 MIPS (133, 300 IPS) – 1972 - IBM S/370 – 1. 0 MIPS (1, 000 IPS) – 2000 - 1 GHz Intel P 3 – 3, 000 MIPS (3, 000, 000 IPS) – 2009 - Qualcomm Snapdragon A 8 – 2, 000 MIPS – 2010 - Intel Core i 7 – 4 x 147, 600 MIPS – 2010 - Qualcomm Snapdragon MP – 2 x 2, 500 MIPS – 2011 - Qualcomm/Samsung/n. Vidia A 9 MP – 2 x 5, 000 MIPS – 2012 – ARM Cortex A 15 MP – 4 x 25, 000 MIPS
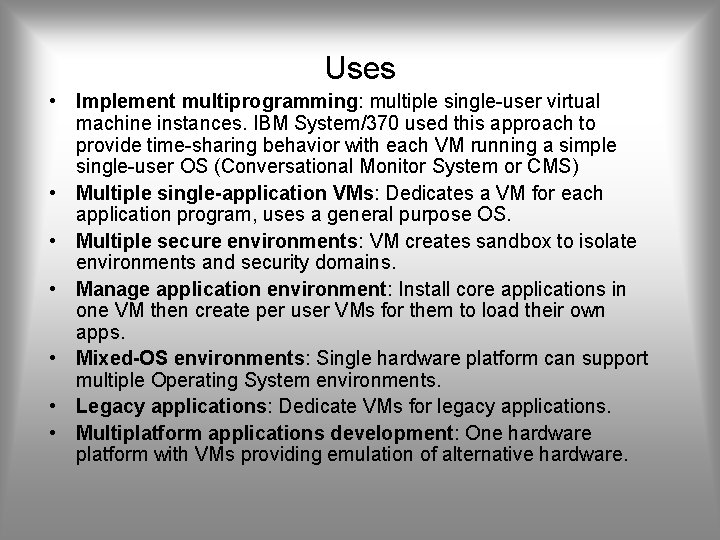
Uses • Implement multiprogramming: multiple single-user virtual machine instances. IBM System/370 used this approach to provide time-sharing behavior with each VM running a simple single-user OS (Conversational Monitor System or CMS) • Multiple single-application VMs: Dedicates a VM for each application program, uses a general purpose OS. • Multiple secure environments: VM creates sandbox to isolate environments and security domains. • Manage application environment: Install core applications in one VM then create per user VMs for them to load their own apps. • Mixed-OS environments: Single hardware platform can support multiple Operating System environments. • Legacy applications: Dedicate VMs for legacy applications. • Multiplatform applications development: One hardware platform with VMs providing emulation of alternative hardware.
Uses • New system transition: Staged or gradual migration (opposite of legacy support). • System software development: For testing or developing new system software in a protected environment. • Operating system training: Run OS instance in a VM so parameter or configuration adjustments do not affect rest of system • Help desk support: Use VM to replicate user environment • Operating system instrumentation: Can monitor hardware access or low level software abstractions • Event monitoring: execution traces, machine state dumps and replaying of traces • System encapsulation: Check pointing system state and restarting on same or different machine.
Virtualization Security Issues • Guest OS isolation: to have no connection among running OS and the Hypervisor • Keep the integrity of the hypervisor • Adds layers to the OS security
Virtualization Security Guidelines • Plan the security • Secure all elements of full virtualization – OS – Hypervisor – Virtualized infrastructure • Restrict and protect administrator access
Hypervisor Security • Like OS security – Install from private network, or clean media – Configure for automatic updates – Disable unused services and hardware – Restrict access to hypervisor – If there is remote access do it on a separate network (e. g. VLAN, VPN, etc. )
Virtualized Infrastructure Security • Consider monitoring hardware activity • Search for VMM which allow to allocate hardware properly, such these activities on the guess OS may be monitored