Open BIDS An Open Flowenabled Network Intrusion Detection
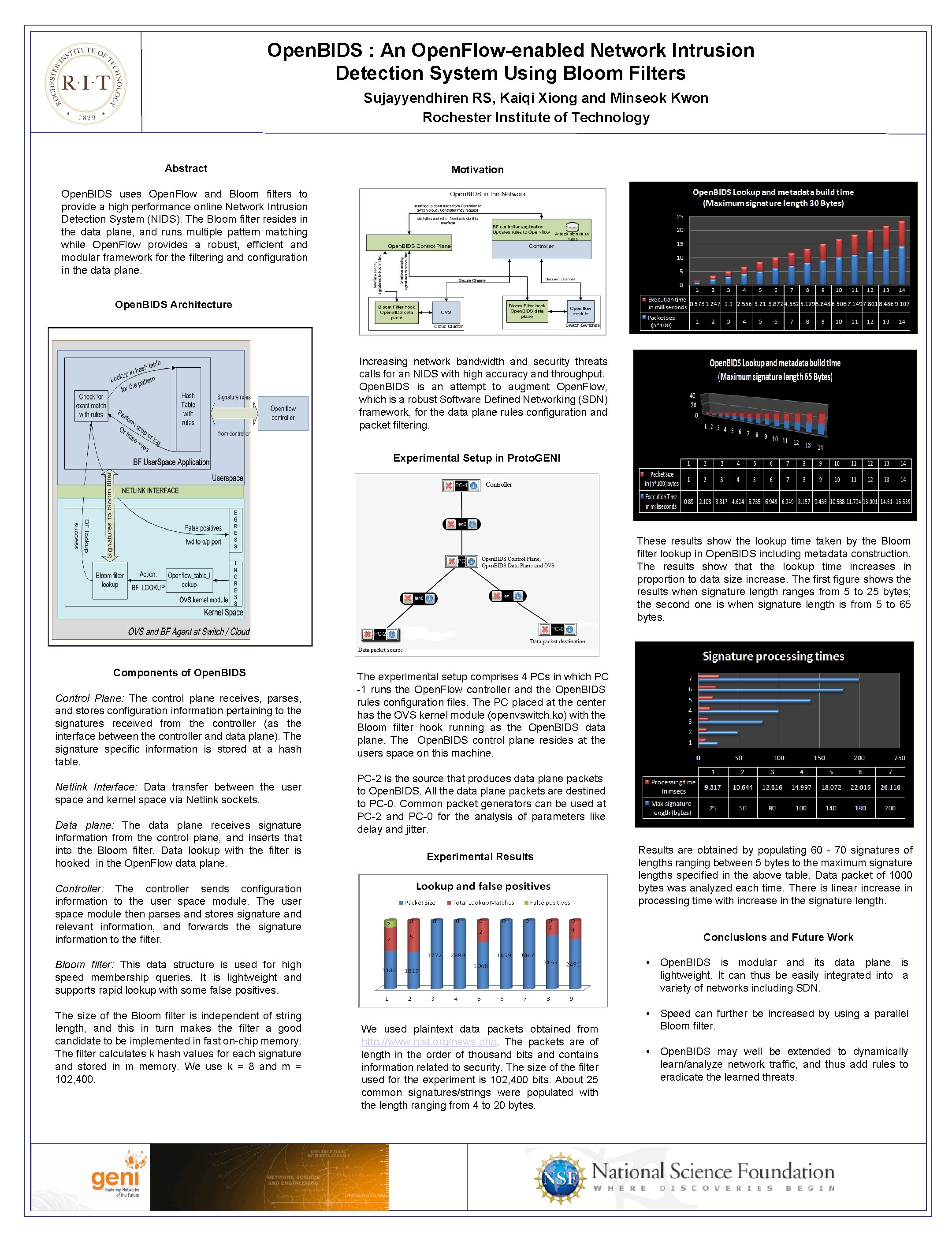
Open. BIDS : An Open. Flow-enabled Network Intrusion Detection System Using Bloom Filters Sujayyendhiren RS, Kaiqi Xiong and Minseok Kwon Rochester Institute of Technology Abstract Motivation Open. BIDS uses Open. Flow and Bloom filters to provide a high performance online Network Intrusion Detection System (NIDS). The Bloom filter resides in the data plane, and runs multiple pattern matching while Open. Flow provides a robust, efficient and modular framework for the filtering and configuration in the data plane. Open. BIDS Architecture Increasing network bandwidth and security threats calls for an NIDS with high accuracy and throughput. Open. BIDS is an attempt to augment Open. Flow, which is a robust Software Defined Networking (SDN) framework, for the data plane rules configuration and packet filtering. Experimental Setup in Proto. GENI These results show the lookup time taken by the Bloom filter lookup in Open. BIDS including metadata construction. The results show that the lookup time increases in proportion to data size increase. The first figure shows the results when signature length ranges from 5 to 25 bytes; the second one is when signature length is from 5 to 65 bytes. Components of Open. BIDS Control Plane: The control plane receives, parses, and stores configuration information pertaining to the signatures received from the controller (as the interface between the controller and data plane). The signature specific information is stored at a hash table. Netlink Interface: Data transfer between the user space and kernel space via Netlink sockets. Data plane: The data plane receives signature information from the control plane, and inserts that into the Bloom filter. Data lookup with the filter is hooked in the Open. Flow data plane. The experimental setup comprises 4 PCs in which PC -1 runs the Open. Flow controller and the Open. BIDS rules configuration files. The PC placed at the center has the OVS kernel module (openvswitch. ko) with the Bloom filter hook running as the Open. BIDS data plane. The Open. BIDS control plane resides at the users space on this machine. PC-2 is the source that produces data plane packets to Open. BIDS. All the data plane packets are destined to PC-0. Common packet generators can be used at PC-2 and PC-0 for the analysis of parameters like delay and jitter. Experimental Results Controller: The controller sends configuration information to the user space module. The user space module then parses and stores signature and relevant information, and forwards the signature information to the filter. Results are obtained by populating 60 - 70 signatures of lengths ranging between 5 bytes to the maximum signature lengths specified in the above table. Data packet of 1000 bytes was analyzed each time. There is linear increase in processing time with increase in the signature length. Conclusions and Future Work Bloom filter: This data structure is used for high speed membership queries. It is lightweight and supports rapid lookup with some false positives. • Open. BIDS is modular and its data plane is lightweight. It can thus be easily integrated into a variety of networks including SDN. The size of the Bloom filter is independent of string length, and this in turn makes the filter a good candidate to be implemented in fast on-chip memory. The filter calculates k hash values for each signature and stored in m memory. We use k = 8 and m = 102, 400. • Speed can further be increased by using a parallel Bloom filter. We used plaintext data packets obtained from http: //www. nist. org/news. php. The packets are of length in the order of thousand bits and contains information related to security. The size of the filter used for the experiment is 102, 400 bits. About 25 common signatures/strings were populated with the length ranging from 4 to 20 bytes. • Open. BIDS may well be extended to dynamically learn/analyze network traffic, and thus add rules to eradicate the learned threats.
- Slides: 1