Online Cryptography Course Dan Boneh Block ciphers The
Online Cryptography Course Dan Boneh Block ciphers The data encryption standard (DES) Dan Boneh
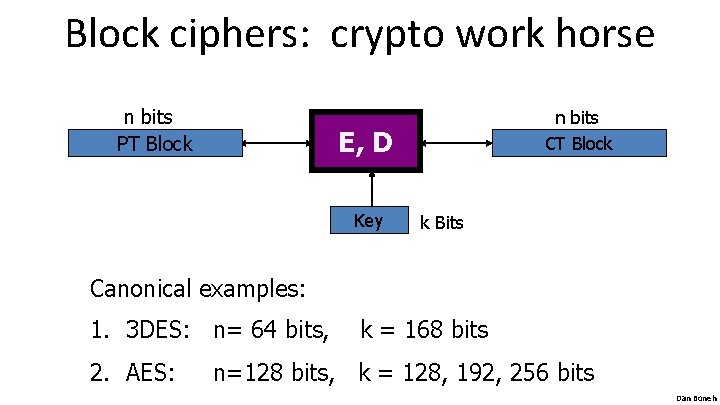
Block ciphers: crypto work horse n bits PT Block n bits CT Block E, D Key k Bits Canonical examples: 1. 3 DES: n= 64 bits, 2. AES: k = 168 bits n=128 bits, k = 128, 192, 256 bits Dan Boneh
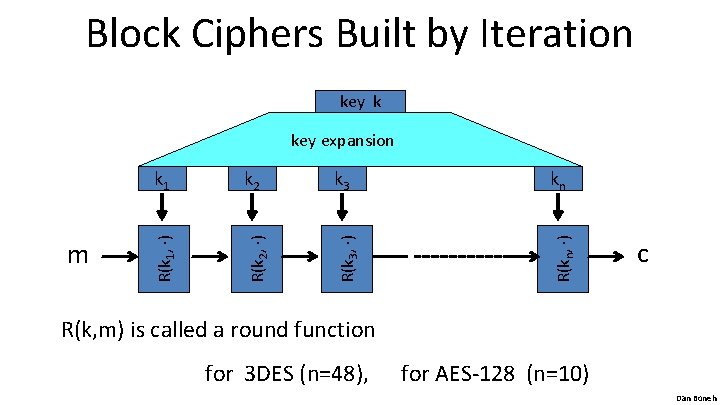
Block Ciphers Built by Iteration key k k 2 k 3 kn R(k 2, ) R(k 3, ) R(kn, ) m k 1 R(k 1, ) key expansion c R(k, m) is called a round function for 3 DES (n=48), for AES-128 (n=10) Dan Boneh
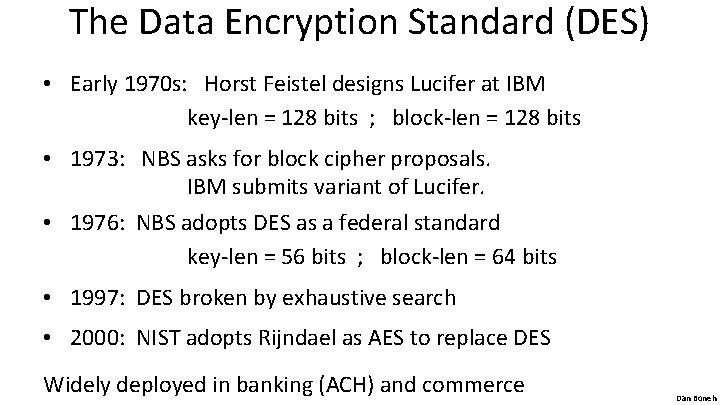
The Data Encryption Standard (DES) • Early 1970 s: Horst Feistel designs Lucifer at IBM key-len = 128 bits ; block-len = 128 bits • 1973: NBS asks for block cipher proposals. IBM submits variant of Lucifer. • 1976: NBS adopts DES as a federal standard key-len = 56 bits ; block-len = 64 bits • 1997: DES broken by exhaustive search • 2000: NIST adopts Rijndael as AES to replace DES Widely deployed in banking (ACH) and commerce Dan Boneh
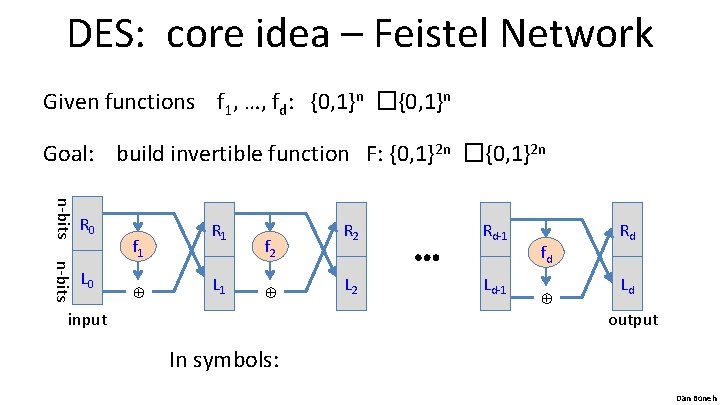
DES: core idea – Feistel Network Given functions f 1, …, fd: {0, 1}n �{0, 1}n Goal: build invertible function F: {0, 1}2 n �{0, 1}2 n L 1 f 2 ⊕ ⊕ n-bits L 0 f 1 R 1 input R 2 L 2 ⋯ Rd-1 Ld-1 fd ⊕ n-bits R 0 Rd Ld output In symbols: Dan Boneh
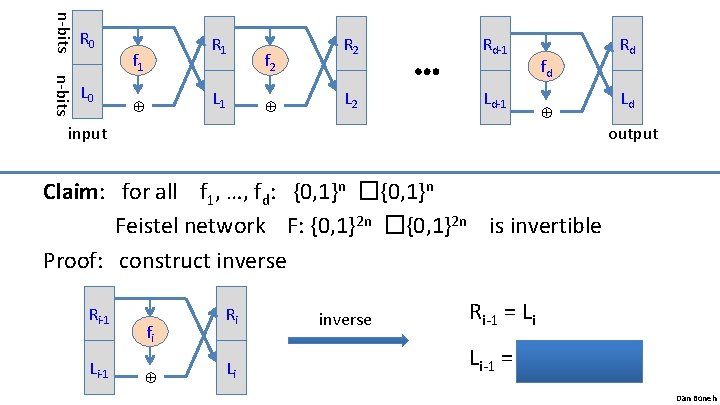
f 1 L 1 f 2 ⊕ ⊕ n-bits L 0 R 1 R 2 L 2 ⋯ Rd-1 Ld-1 input fd ⊕ n-bits R 0 Rd Ld output Claim: for all f 1, …, fd: {0, 1}n �{0, 1}n Feistel network F: {0, 1}2 n �{0, 1}2 n is invertible Proof: construct inverse Li-1 fi ⊕ Ri-1 Ri Li inverse Ri-1 = Li Li-1 = fi(Li) �Ri Dan Boneh
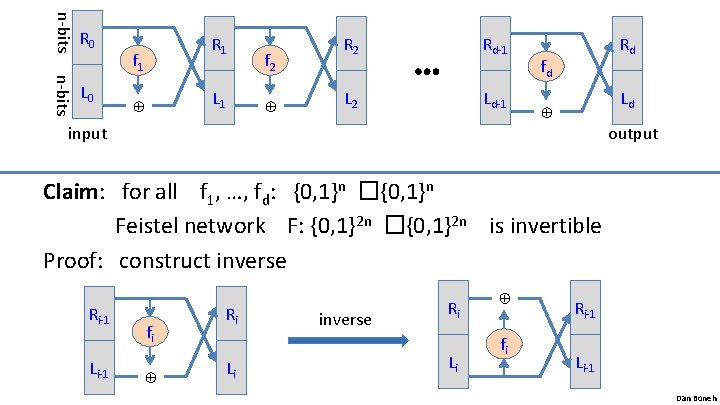
f 1 L 1 f 2 ⊕ ⊕ n-bits L 0 R 1 R 2 L 2 Rd-1 ⋯ Ld-1 input Rd fd Ld ⊕ n-bits R 0 output Claim: for all f 1, …, fd: {0, 1}n �{0, 1}n Feistel network F: {0, 1}2 n �{0, 1}2 n is invertible Proof: construct inverse Li-1 fi ⊕ Ri-1 Ri Li inverse Ri Li ⊕ fi Ri-1 Li-1 Dan Boneh
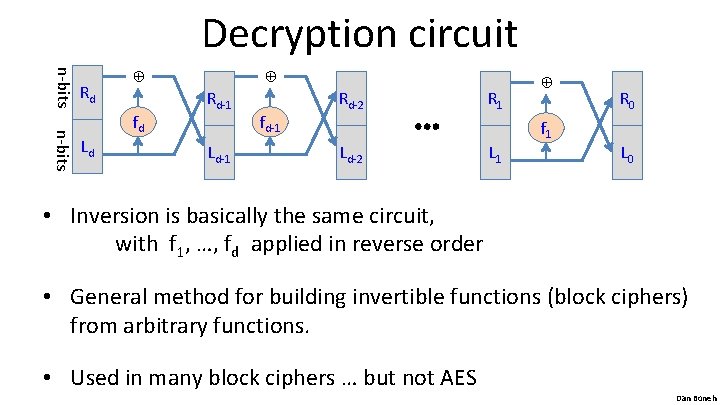
Decryption circuit n-bits Rd n-bits Ld ⊕ fd Rd-1 Ld-1 ⊕ fd-1 Rd-2 Ld-2 ⋯ R 1 L 1 ⊕ f 1 R 0 L 0 • Inversion is basically the same circuit, with f 1, …, fd applied in reverse order • General method for building invertible functions (block ciphers) from arbitrary functions. • Used in many block ciphers … but not AES Dan Boneh
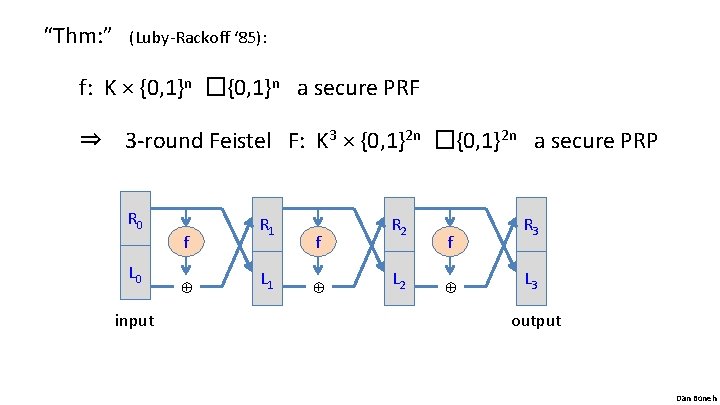
“Thm: ” (Luby-Rackoff ‘ 85): f: K × {0, 1}n �{0, 1}n a secure PRF ⇒ 3 -round Feistel F: K 3 × {0, 1}2 n �{0, 1}2 n a secure PRP ⊕ input L 1 f ⊕ L 0 f R 1 R 2 L 2 f ⊕ R 0 R 3 L 3 output Dan Boneh
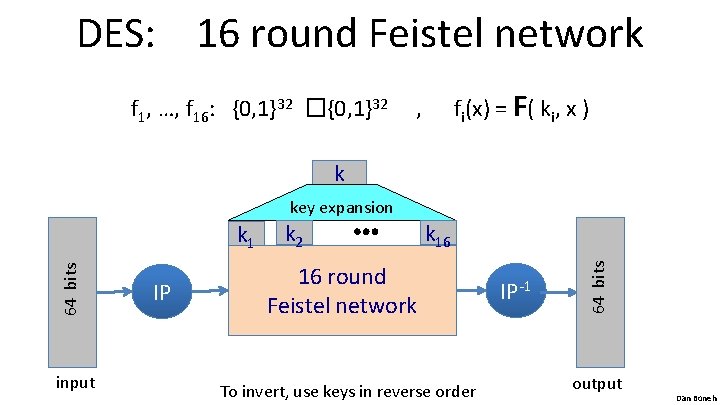
DES: 16 round Feistel network f 1, …, f 16: {0, 1}32 �{0, 1}32 fi(x) = F( ki, x ) , k key expansion input IP k 2 ⋯ k 16 16 round Feistel network To invert, use keys in reverse order IP-1 64 bits k 1 output Dan Boneh
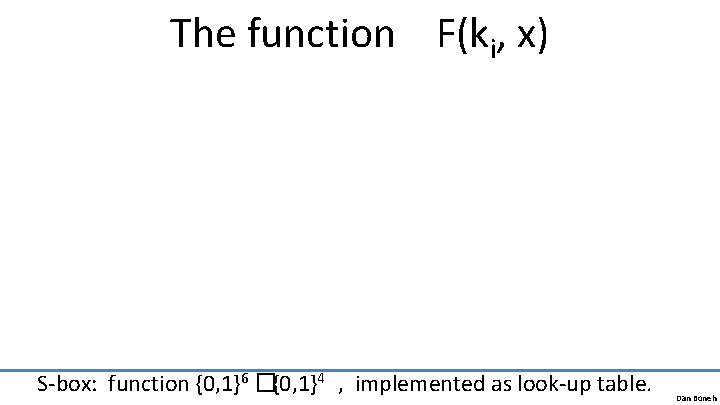
The function F(ki, x) S-box: function {0, 1}6 �{0, 1}4 , implemented as look-up table. Dan Boneh
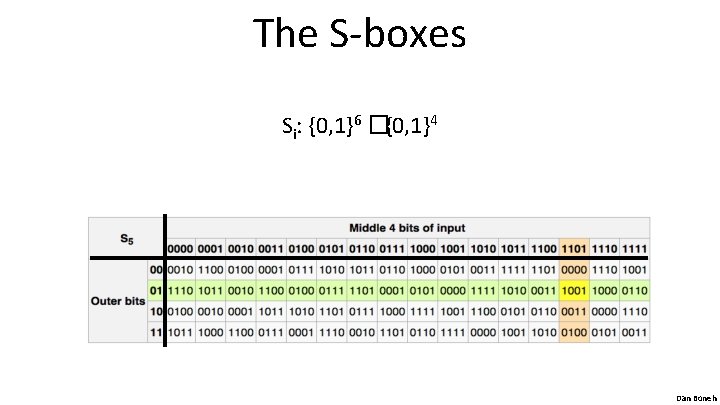
The S-boxes Si: {0, 1}6 �{0, 1}4 Dan Boneh
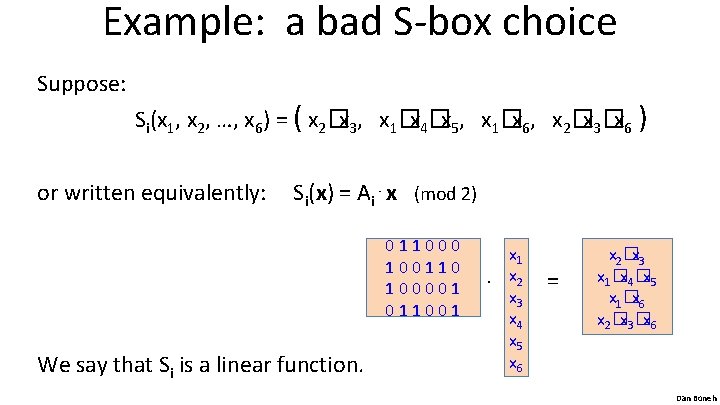
Example: a bad S-box choice Suppose: Si(x 1, x 2, …, x 6) = ( x 2�x 3, x 1�x 4�x 5, x 1�x 6, x 2�x 3�x 6 ) or written equivalently: Si(x) = Ai⋅x (mod 2) 011000 100110 100001 011001 We say that Si is a linear function. x 1. x 2 x 3 x 4 x 5 x 6 = x 2�x 3 x 1�x 4�x 5 x 1�x 6 x 2�x 3�x 6 Dan Boneh
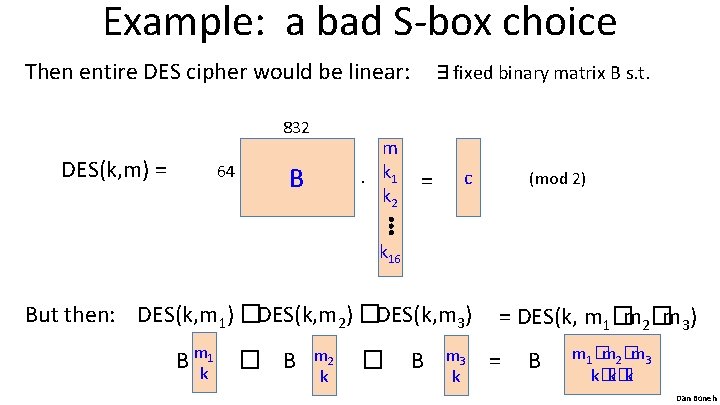
Example: a bad S-box choice Then entire DES cipher would be linear: ∃fixed binary matrix B s. t. 832 DES(k, m) = 64 m. k 1 k 2 B = c (mod 2) ⋮ k 16 But then: DES(k, m 1) �DES(k, m 2) �DES(k, m 3) B mk 1 � B m 2 k � B m 3 k = DES(k, m 1�m 2�m 3) = B m 1�m 2�m 3 k�k�k Dan Boneh
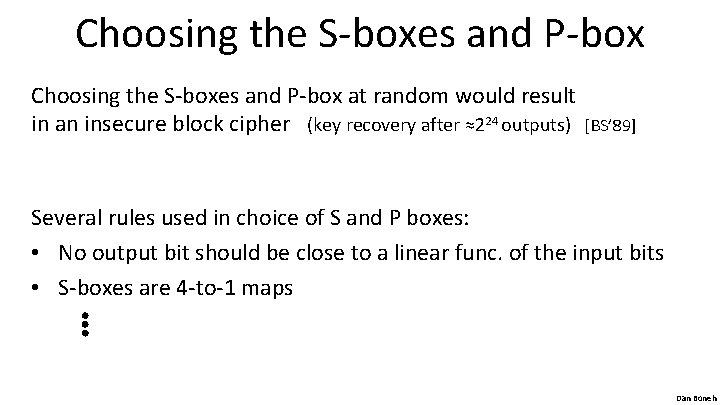
Choosing the S-boxes and P-box at random would result in an insecure block cipher (key recovery after ≈224 outputs) [BS’ 89] Several rules used in choice of S and P boxes: • No output bit should be close to a linear func. of the input bits • S-boxes are 4 -to-1 maps ⋮ Dan Boneh
End of Segment Dan Boneh
- Slides: 16