Once Again Our sincere thanks to Bri Vineetha
Once Again Our sincere thanks to. . . Bri. Vineetha & Our own Friends
The ---------- ** * * ---------- WEB Cops Returns…
Scanning for Viruses
Instructions. . . s e s iru S r. V o f g n canni . s n o i e t l s b e i s u s Q po 0 t 1 o y n l n m is a r n g o i o t Ø O r p lec r e e s w e s l an n ultip i ts M e n i c i o o Ø p e ch v i r – u s o a ty r c e e d l i e s on c Ø S s i ng i t i r w ver O Ø Start Scann…
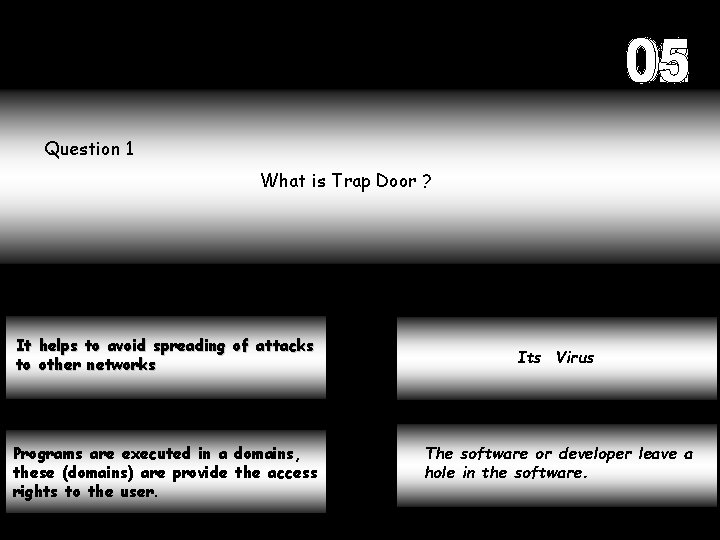
Question 1 What is Trap Door ? It helps to avoid spreading of attacks to other networks Programs are executed in a domains, these (domains) are provide the access rights to the user. Its Virus The software or developer leave a hole in the software.
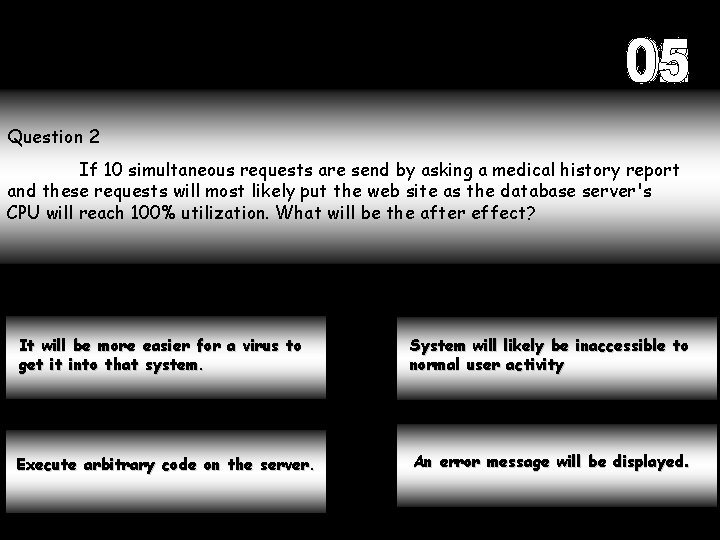
Question 2 If 10 simultaneous requests are send by asking a medical history report and these requests will most likely put the web site as the database server's CPU will reach 100% utilization. What will be the after effect? It will be more easier for a virus to get it into that system. System will likely be inaccessible to normal user activity Execute arbitrary code on the server. An error message will be displayed.
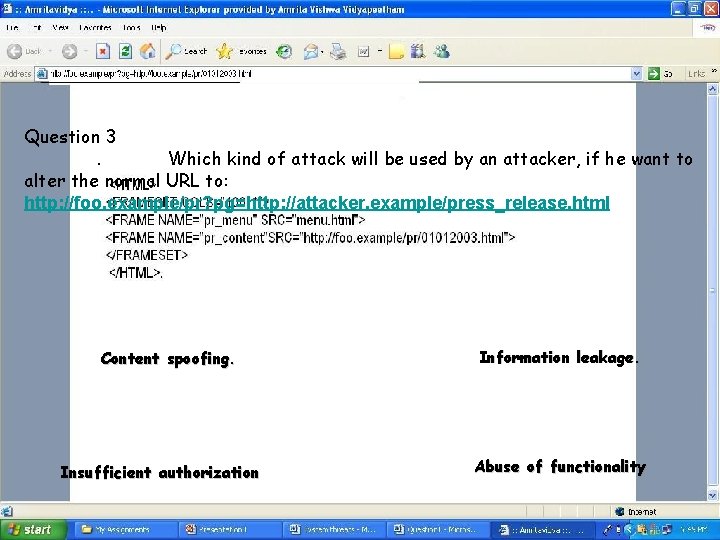
Question 33. . If. Which a user kind would ofvisit attack a link willsuch be used as by an attacker, if he want to alter the normal URL to: (http: //foo. example/pr? pg=http: //foo. example/pr/01012003. html) The resulting webpage HTML would be : http: //foo. example/pr? pg=http: //attacker. example/press_release. html Content spoofing. Insufficient authorization Information leakage. Abuse of functionality
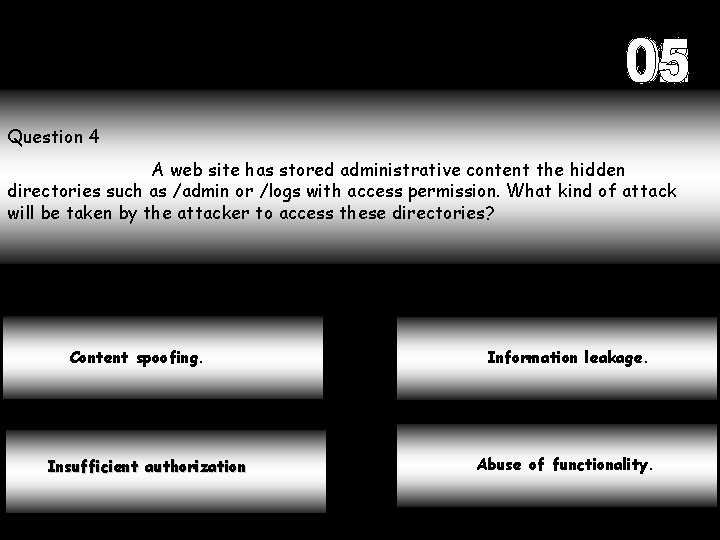
Question 4 A web site has stored administrative content the hidden directories such as /admin or /logs with access permission. What kind of attack will be taken by the attacker to access these directories? Content spoofing. Insufficient authorization Information leakage. Abuse of functionality.
Question 5 Performing a Do. S by flooding a web-login system with good usernames and bad passwords to lock out legitimate users when the allowed login retry-limit is exceeded. Given is an example for: Content spoofing. Denial of service. Information leakage. Abuse of functionality.
Question 6 A Trojan is a______ ? Malware attack that disguises itself as threat Virus that attacks boot sector. Malware that disguises itself as something innocent. Glean data electronically from compromised network.
Question 7 A programmer hides a piece of code under a condition that the files start deleting, when the number of files exceeds 10, 000. Identify the threat? Trojan horse. Time bomb. Worm. Logic bomb.
Question 8 Ur system is hacked by an hacker who browses your private database, alter and corrupts confidential information. U can avoid the risk of being attacked in future by using a. . . . . Firewall Remote Login Hub All of the above
Question 9 Which property in Windows Firewall allows user to select the required program or port to be unblocked by the firewall Exception General Advanced Sorry …!
Question 10 ………… can cache previously visited sites to avoid excessive use of ……………? Switch, Firewall, Bandwidth Router, Firewall Sorry …!
Scanning is Complete …. . …… Please wait …. ! We scan your results …. . |||||||||||||||||||||||||||||| |

The Results

d n E . . u. T k n ha u o y
- Slides: 17