ON THE INTERNET NOBODY KNOWS YOU ARE A
ON THE INTERNET, NOBODY KNOWS YOU ARE A DOG
FIRST PART THREE SUBPARTS (1) What is Cyber Laws (2) What are violations of Cyber Laws (3) What is Cyber Crime (4) Cyber Crime - Remedies and Punishment
CYBER LAWS VIOLATIONS: IPR (a) Copyright, Trademark infringement – Internet (b) Illegal Copying, Distribution – Software (c) Trade Secret, Reverse Engineering, Patents - Software
VIOLATIONS OTHERS THAN IPR Computer/ Communication Device (i) Object/ Target (ii) Instrument to Commit – Offence (iii) Other Violations under the IT Act Civil - Chapters IX & X Offences - Chapter XI
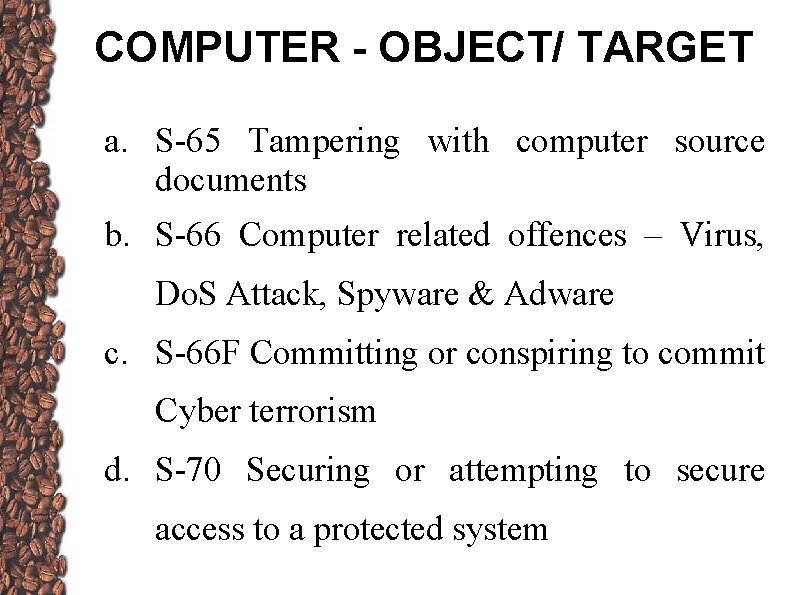
COMPUTER - OBJECT/ TARGET a. S-65 Tampering with computer source documents b. S-66 Computer related offences – Virus, Do. S Attack, Spyware & Adware c. S-66 F Committing or conspiring to commit Cyber terrorism d. S-70 Securing or attempting to secure access to a protected system
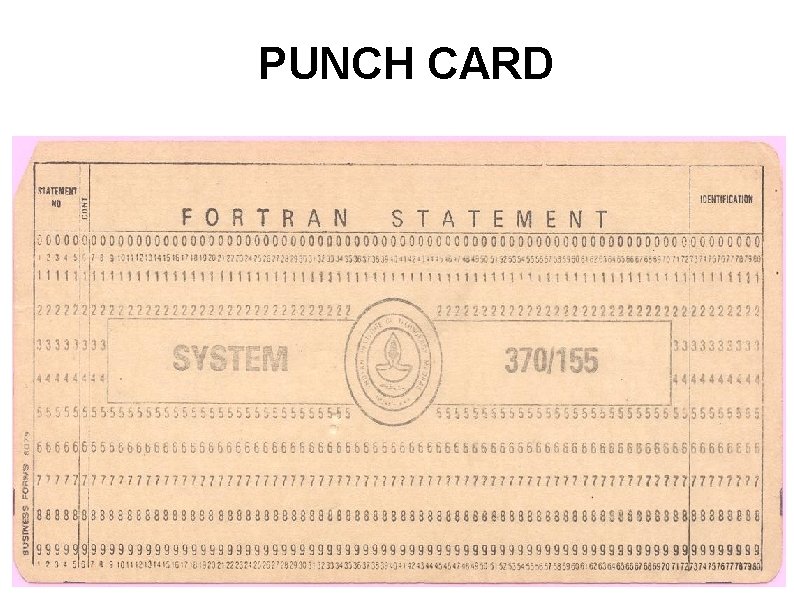
PUNCH CARD
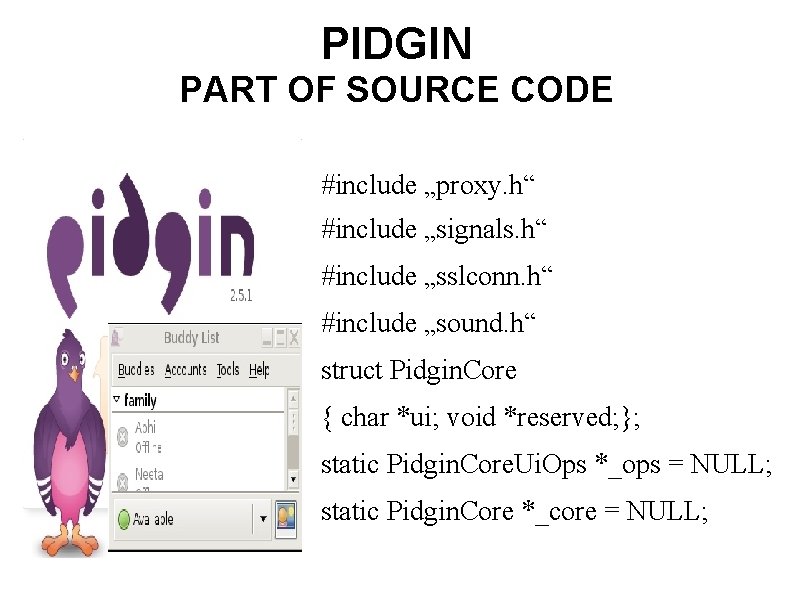
PIDGIN PART OF SOURCE CODE #include „proxy. h“ #include „signals. h“ #include „sslconn. h“ #include „sound. h“ struct Pidgin. Core { char *ui; void *reserved; }; static Pidgin. Core. Ui. Ops *_ops = NULL; static Pidgin. Core *_core = NULL;
COMPUTER - OBJECT/ TARGET b. S-66 Computer related offences – Virus, Do. S Attack, Spyware & Adware c. S-66 F Committing or conspiring to commit Cyber terrorism d. S-70 Securing or attempting to secure access a protected system
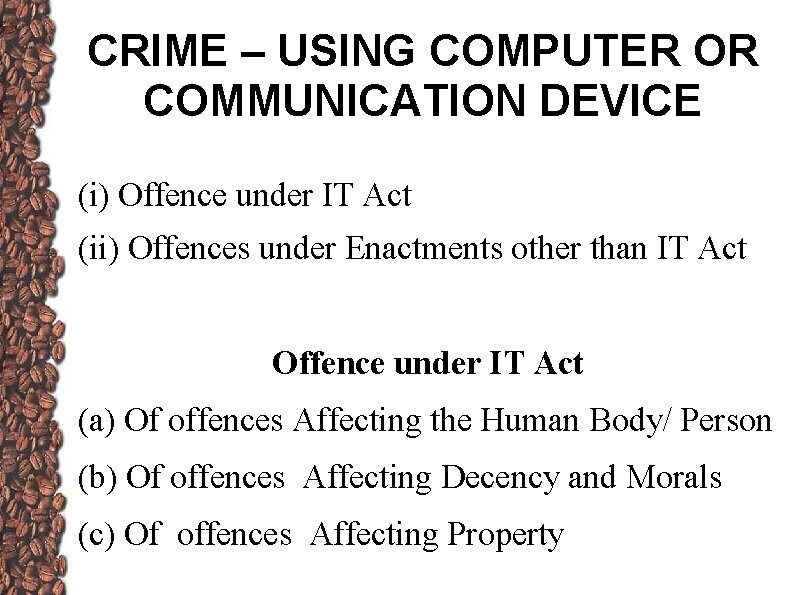
CRIME – USING COMPUTER OR COMMUNICATION DEVICE (i) Offence under IT Act (ii) Offences under Enactments other than IT Act Offence under IT Act (a) Of offences Affecting the Human Body/ Person (b) Of offences Affecting Decency and Morals (c) Of offences Affecting Property
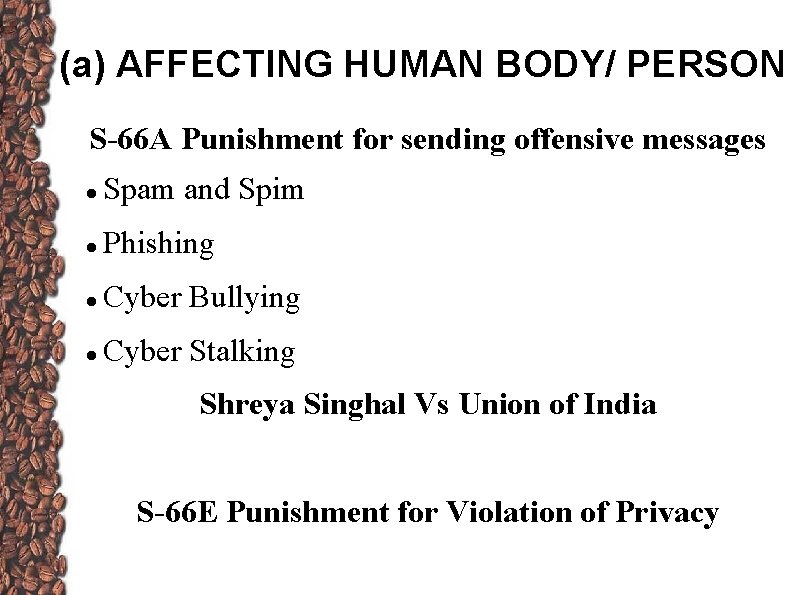
(a) AFFECTING HUMAN BODY/ PERSON S-66 A Punishment for sending offensive messages Spam and Spim Phishing Cyber Bullying Cyber Stalking Shreya Singhal Vs Union of India S-66 E Punishment for Violation of Privacy
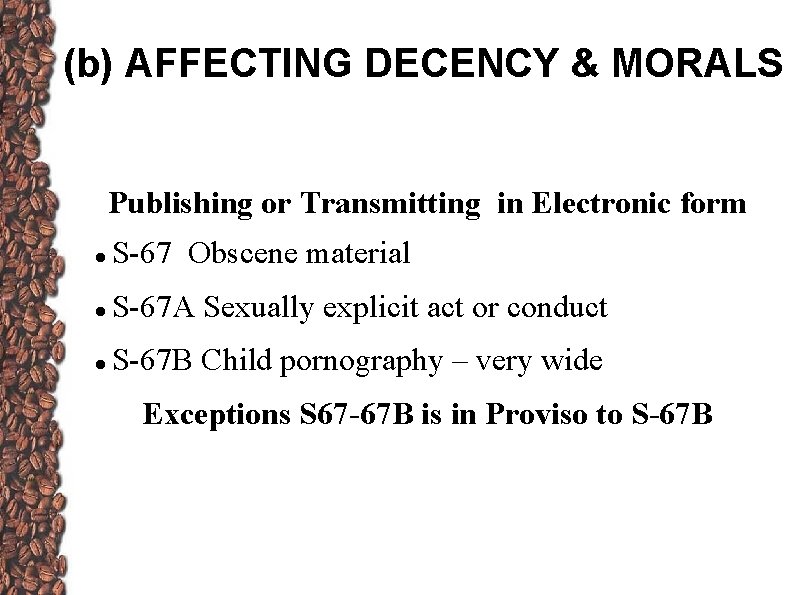
(b) AFFECTING DECENCY & MORALS Publishing or Transmitting in Electronic form S-67 Obscene material S-67 A Sexually explicit act or conduct S-67 B Child pornography – very wide Exceptions S 67 -67 B is in Proviso to S-67 B
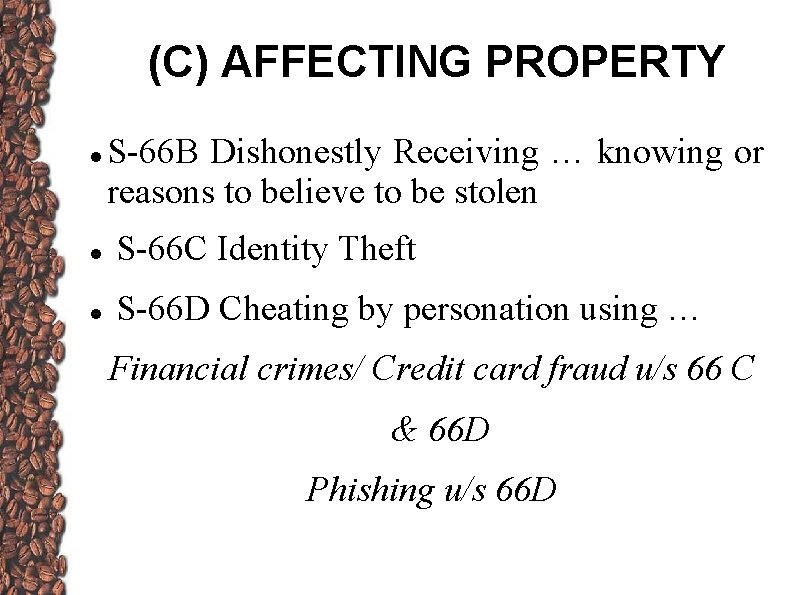
(C) AFFECTING PROPERTY S-66 B Dishonestly Receiving … knowing or reasons to believe to be stolen S-66 C Identity Theft S-66 D Cheating by personation using … Financial crimes/ Credit card fraud u/s 66 C & 66 D Phishing u/s 66 D
OFFENCES OTHER THAN IT ACT HATE CRIMES - IPC S-124 A Sedition S-153 A Promoting enmity between. . . groups … S-153 B Imputations … prejudicial to national interest S-295 A … to outrage religious feelings … C-XXI Defamation C-XXII Criminal Intimidation Insult & Annoyance
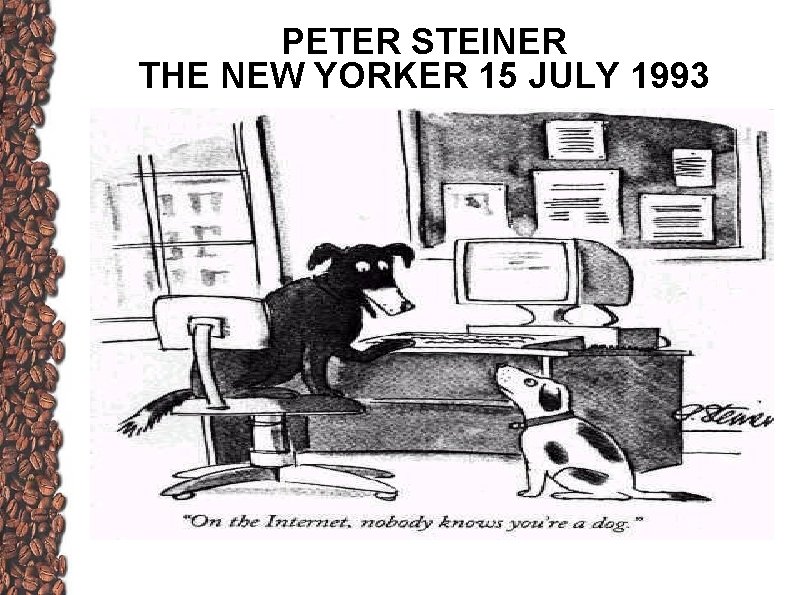
PETER STEINER THE NEW YORKER 15 JULY 1993
- Slides: 14