On the Incoherencies in Web Browser Access Control
On the Incoherencies in Web Browser Access Control Policies Authors: Kapil Singh, et al Presented by Yi Yang
Outline ü Introduction ü Analysis of browser access control incoherencies ü Web. Analyzer Measurement Framework ü Experimental Results ü Related work & Discussion & Limitations ü Conclusions
Major Access Control Flaws ü Inconsistent principal labeling ü Inappropriate handling of principal label changes ü Disregard of the user principal
What is a Principal ü In the Web environment, principal=domain? ü Principal and domain are interchangeable. H. Wang, et. al (SOSP’ 07) ü Different labeling for resources. ü for the DOM (memory) resource, a principal is labeled by <protocol, domain, port>; ü for the cookie resource, a principal is labeled by <domain, path>.
document. domain ü Gets/sets the domain of the current document. ü Eg. a script in the document at x. a. com/index. html executes document. domain = “a. com”. After that statement executes, the page would pass the origin check with a. com/index. html . ü However, a. com cannot set document. domain to b. com
Review of Access Control Flaws ü Inconsistent principal labeling ü Inappropriate handling of principal label changes: ü Disregard the “effective” principle IDs set by document. domain. ü Disregard of the user principal ü eg. clipboard, geolocation, user actions, etc
Contributions ü Principal-driven analysis of access control incoherencies in today’s browsers. ü User principal concept for the browser setting. ü Compatibility measurement framework----Web. Analyzer. ü Measurements on the compatibility cost of coherent access control policies.
II. Analysis of Browser Access Control Incoherencies ü Methodology ü Browser Resources ü The Interplay of the Resources ü Effective Principal ID ü The User Principal
Methodology ü Each shared browser resource should have a principal definition and have an access control policy. ü For each non-shared browser resource, the resource should have an owner principal with a specific label or be globally accessible. ü When two resources interplay, both resources should have the same principal definition. ü All access control policies must consider the runtime label of the principals, namely, the “effective” principal ID. ü The user principal’s resources should not be accessible by web applications.
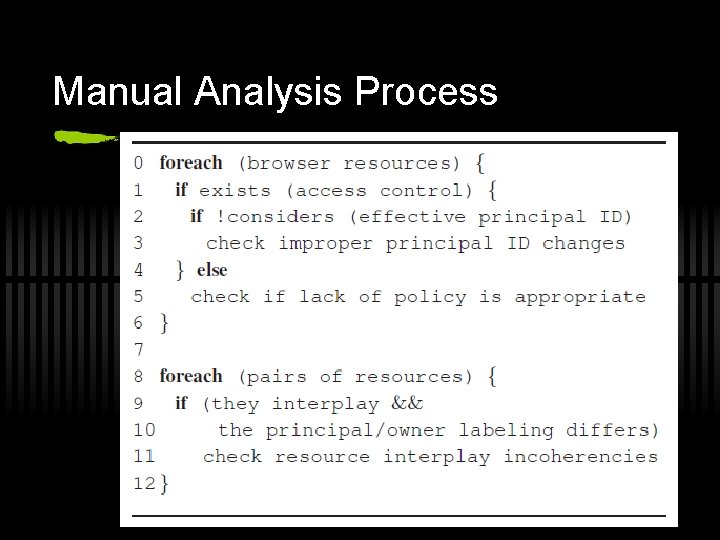
Manual Analysis Process
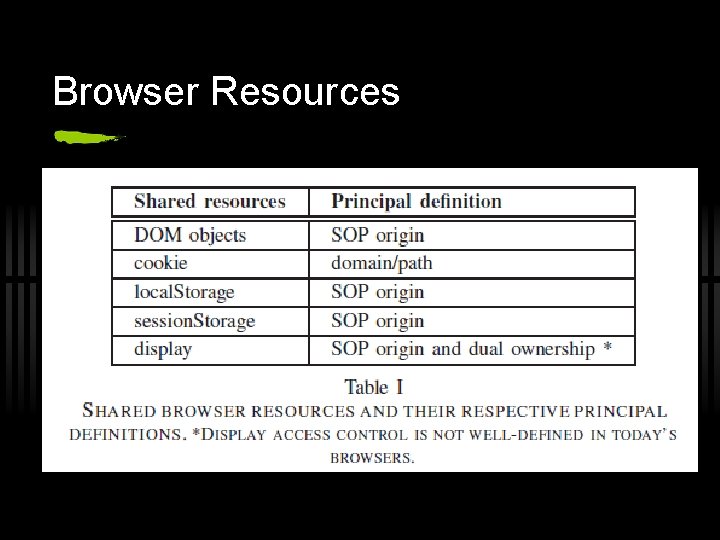
Browser Resources
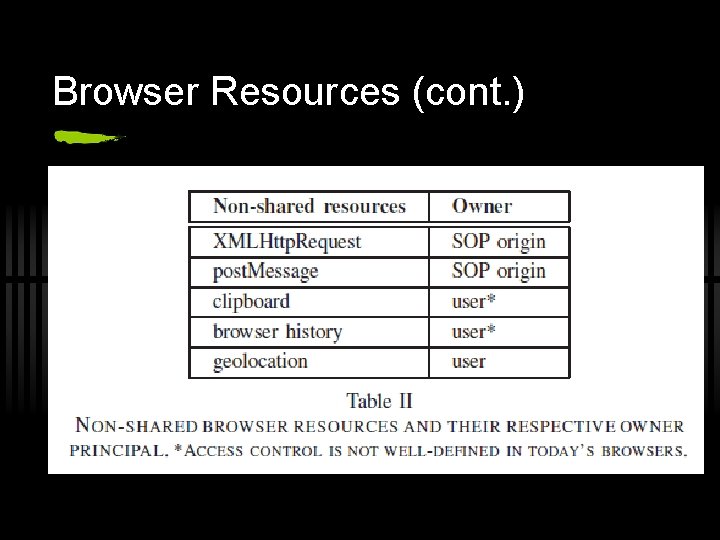
Browser Resources (cont. )
Interplay of the Resources ü DOM and Cookies ü Cookies and XMLHttp. Request ü DOM and Display
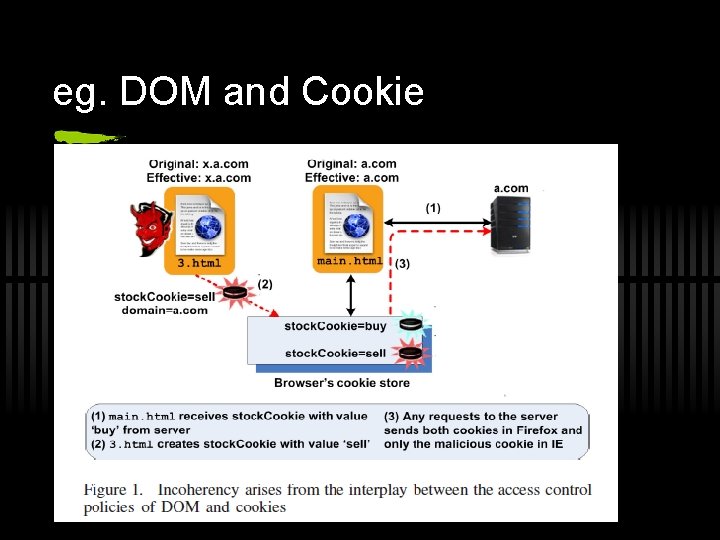
eg. DOM and Cookie
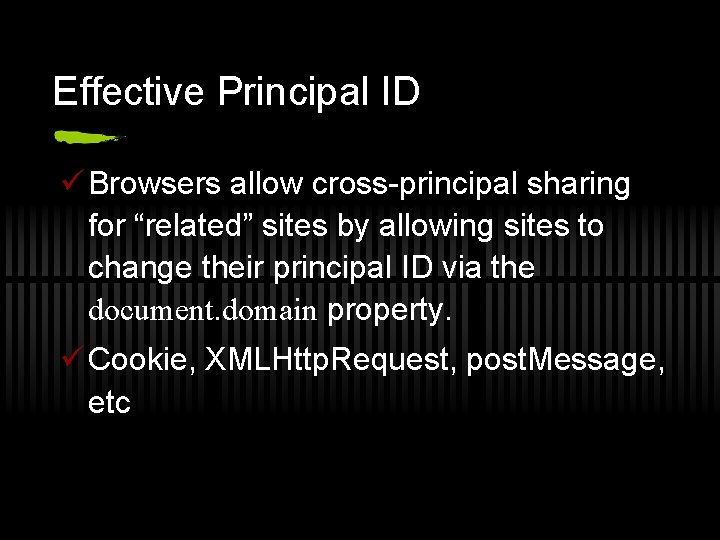
Effective Principal ID ü Browsers allow cross-principal sharing for “related” sites by allowing sites to change their principal ID via the document. domain property. ü Cookie, XMLHttp. Request, post. Message, etc
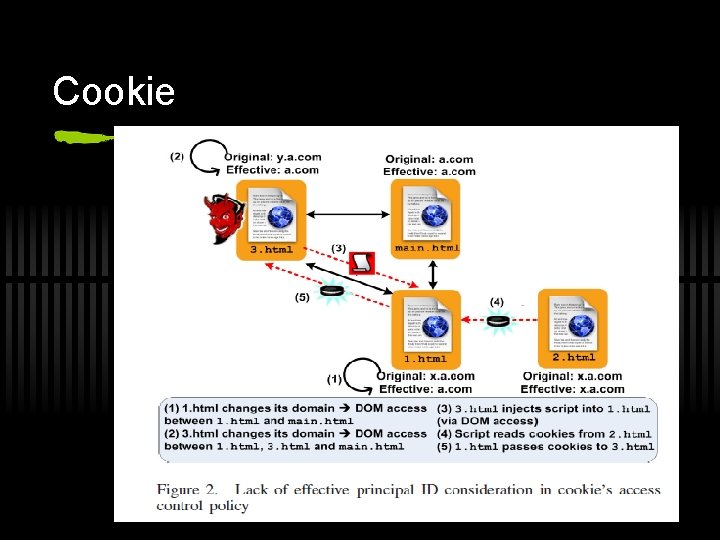
Cookie
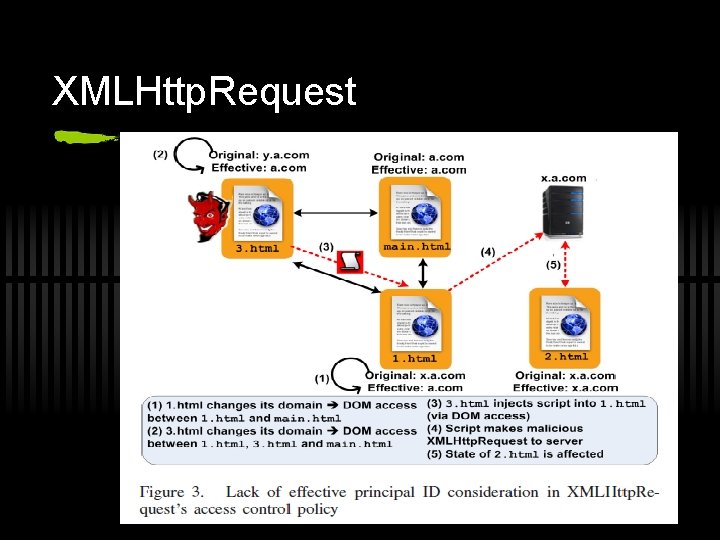
XMLHttp. Request
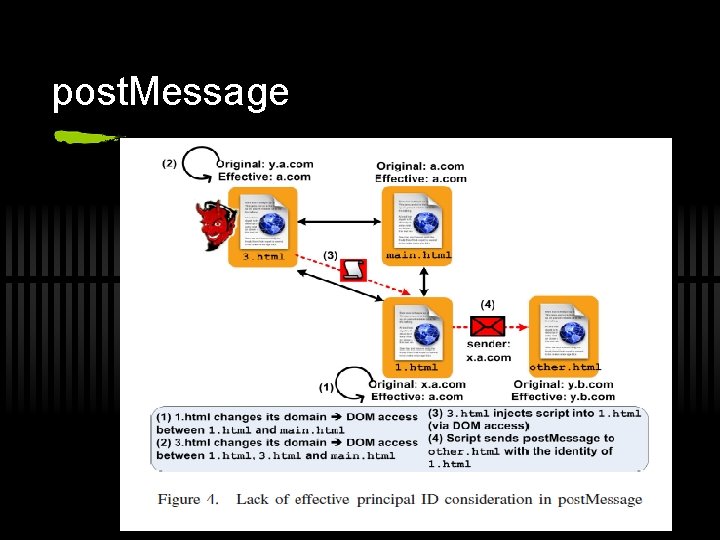
post. Message
The User Principal ü User actions ü back(), forward(), history ü Browser UI ü move. To(), resize. To(), etc ü User-private State ü Geolocation is one of the latest browser features. ü Geolocation dialog is active for only one origin at a time. DOS attack
Web. Analyzer Measurement Framework ü Crawl the web to look for prevalence of unsafe browser features on existing web pages. ü IEWA , a specially instrumented version of IE, provides dynamic mediation for all browser resources, and detects when a resource invocation matches one of preset policy rules.
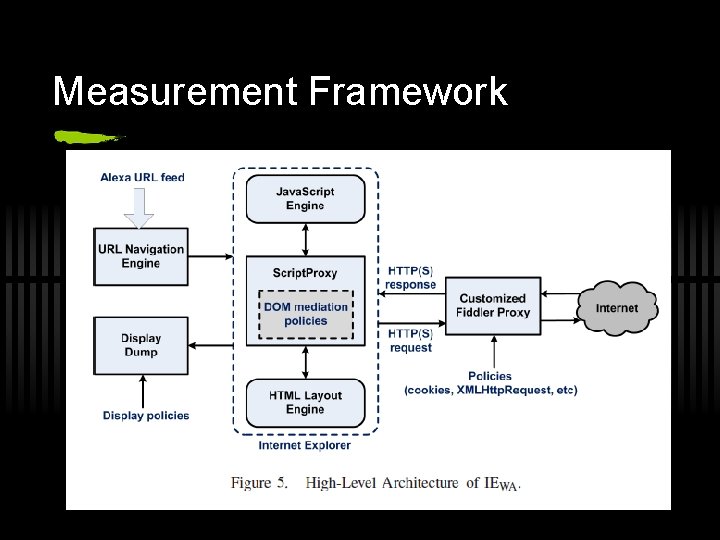
Measurement Framework
heuristics-driven automated crawling ü It’s hard to fully study all possible website features. ü Simple heuristics to simulate user interaction. ü find and click at most 5 random links; ü produce 5 random navigation events; ü check search form, fill it and submit it.
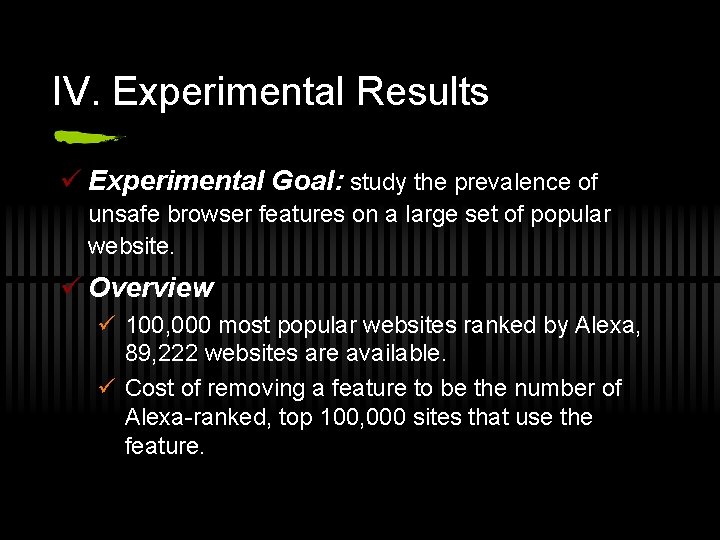
IV. Experimental Results ü Experimental Goal: study the prevalence of unsafe browser features on a large set of popular website. ü Overview ü 100, 000 most popular websites ranked by Alexa, 89, 222 websites are available. ü Cost of removing a feature to be the number of Alexa-ranked, top 100, 000 sites that use the feature.
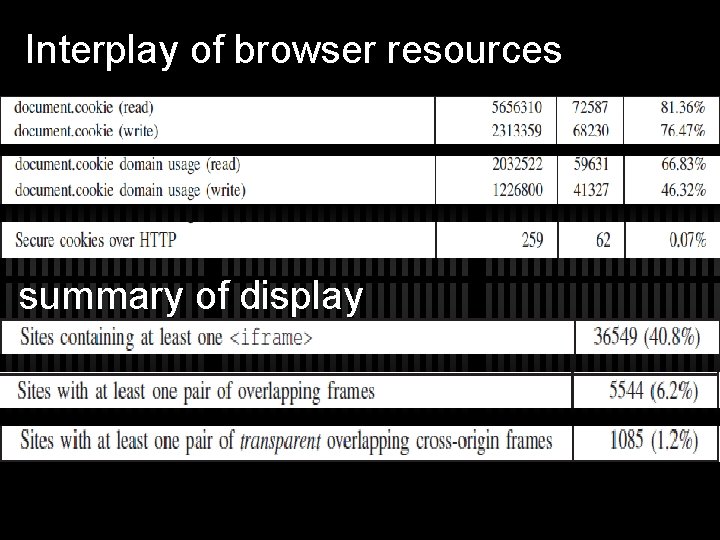
Interplay of browser resources summary of display
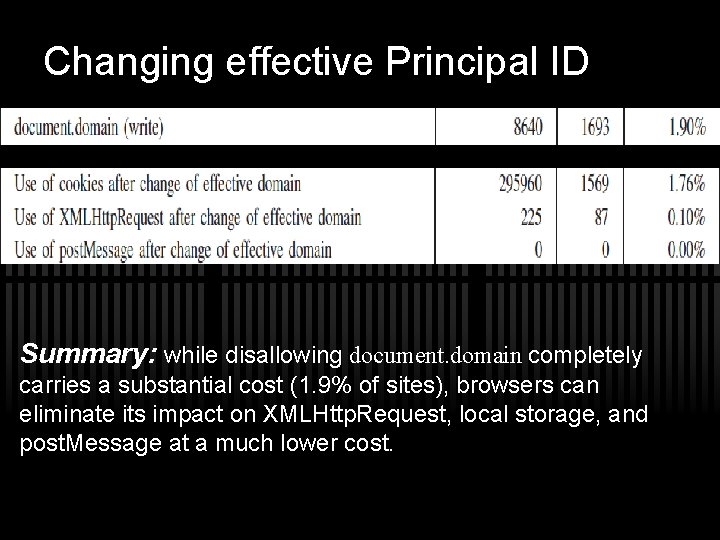
Changing effective Principal ID Summary: while disallowing document. domain completely carries a substantial cost (1. 9% of sites), browsers can eliminate its impact on XMLHttp. Request, local storage, and post. Message at a much lower cost.
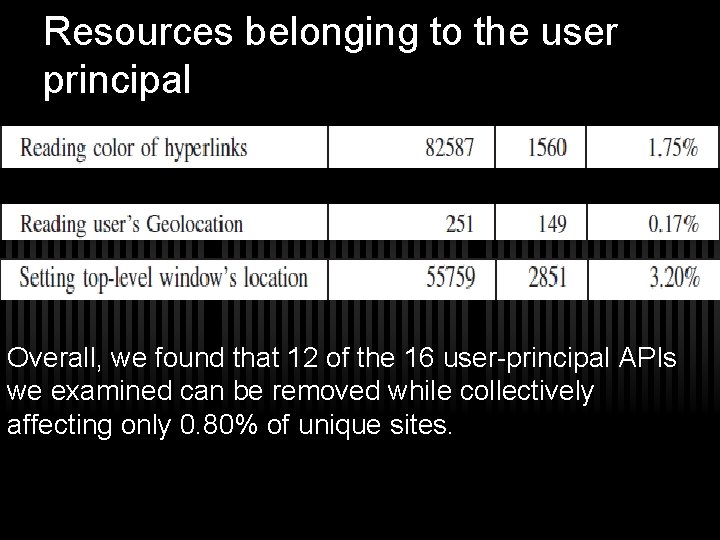
Resources belonging to the user principal Overall, we found that 12 of the 16 user-principal APIs we examined can be removed while collectively affecting only 0. 80% of unique sites.
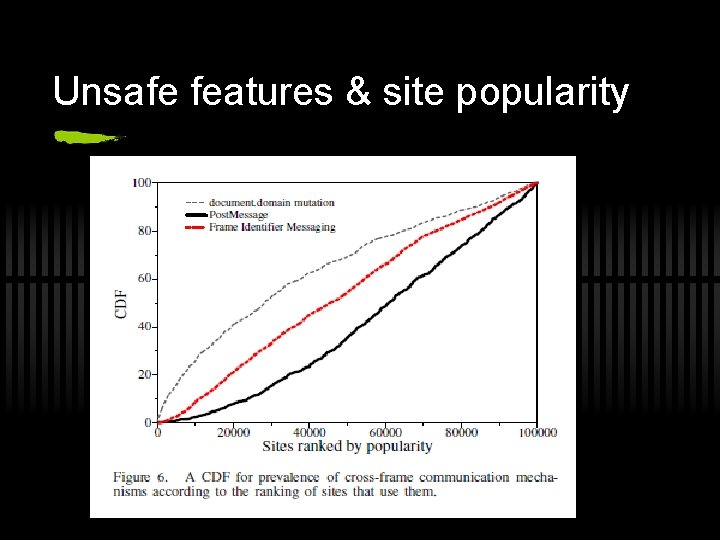
Unsafe features & site popularity
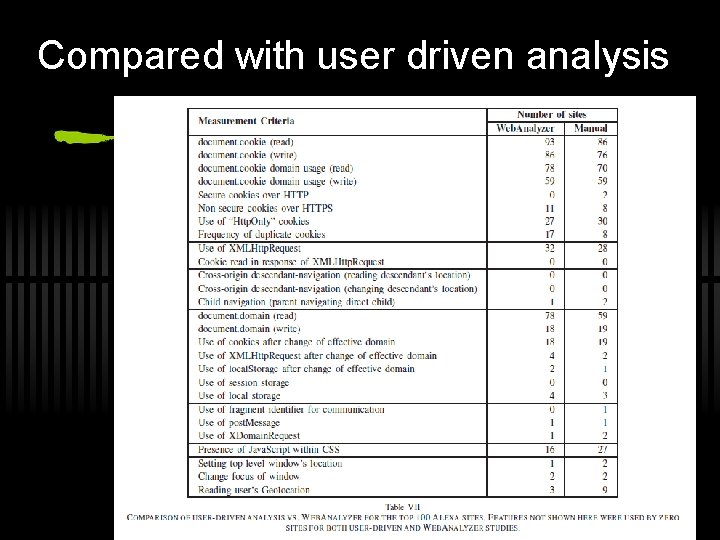
Compared with user driven analysis
V. Discussion & Limitations ü Benefits of heuristics-driven automated crawling. ü Limits of automated crawler-based measurements. ü Picking the right browser. ü Studying other web segments.
VI. Related Work ü Previous work has looked at weaknesses in cross-frame communication mechanisms, client-side browser state, cookie path protection, display protection, and other issues. ü DOM access checker is a tool designed to automatically validate numerous aspects of domain security policy enforcement to detect common security attacks or information disclosure vectors. ü Browserscope is a community-driven project for tracking browser functionality. Its security test suite checks whether new browser security features are implemented by a browser.
VII. Conclusions ü incoherencies in access control policies ü user principal ü measured the cost of removing unsafe policies

Thanks
- Slides: 32