On Proxy Server based Multipath Connections PSMC Ph
On Proxy Server based Multipath Connections (PSMC) Ph. D Proposal Yu Cai 12/2003 University of Colorado at Colorado Springs

Outline n 1. Introduction n 2. Related work n 3. PSMC algorithms n 4. PSMC protocols n 5. PSMC applications n 6. PSMC security n 7. Conclusion
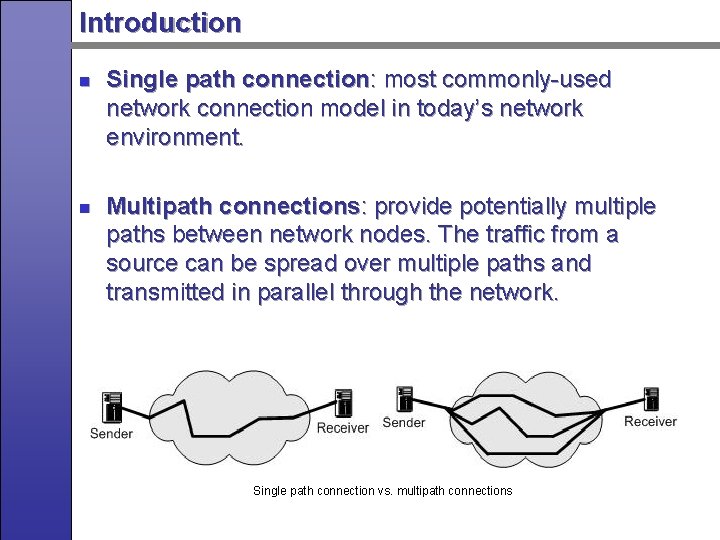
Introduction n n Single path connection: most commonly-used network connection model in today’s network environment. Multipath connections: provide potentially multiple paths between network nodes. The traffic from a source can be spread over multiple paths and transmitted in parallel through the network. Single path connection vs. multipath connections
Why Multipath Connections n Improve the network security by providing alternate paths n Improve the network reliability, stability and availability n Improve the network performance by increasing the aggregate bandwidth between network nodes n Utilize the network resources more efficiently n Cope well with network congestion, link breakage, burst traffic and potential attacks n Provide better quality-of-service
Related Works on Multipath Connections n Multipath connections have been studied since 70 s. n n n The IBM Systems Network Architecture (SNA) in 1974 Nicholas F. Maxemchuk in 1975, the dispersity routing Classification of multipath connections based on OSI 7 -layer model. n n Physical layer: Multipath Interference; Antenna Array. Data link layer: Link Aggregation, defined in IEEE 802. 3 ad. (requires additional hardware support)
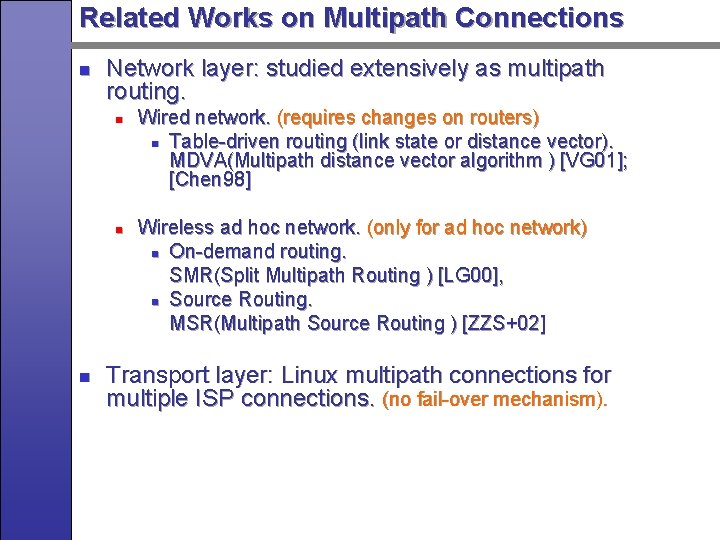
Related Works on Multipath Connections n Network layer: studied extensively as multipath routing. n n n Wired network. (requires changes on routers) n Table-driven routing (link state or distance vector). MDVA(Multipath distance vector algorithm ) [VG 01]; [Chen 98] Wireless ad hoc network. (only for ad hoc network) n On-demand routing. SMR(Split Multipath Routing ) [LG 00], n Source Routing. MSR(Multipath Source Routing ) [ZZS+02] Transport layer: Linux multipath connections for multiple ISP connections. (no fail-over mechanism).
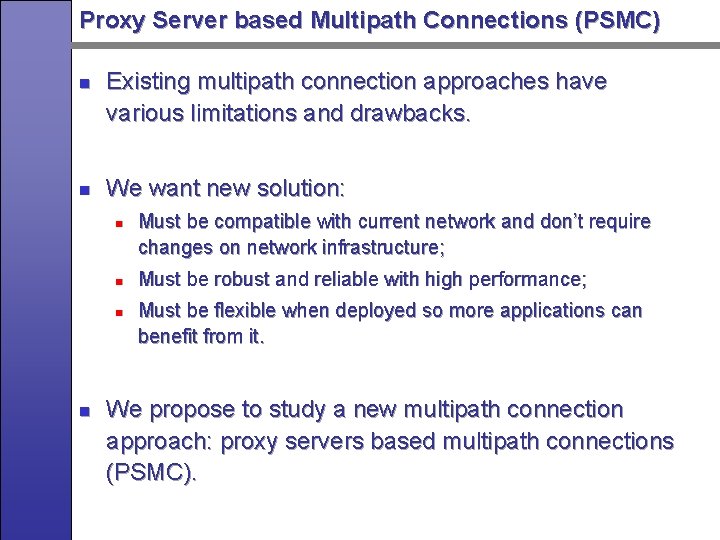
Proxy Server based Multipath Connections (PSMC) n n Existing multipath connection approaches have various limitations and drawbacks. We want new solution: n n Must be compatible with current network and don’t require changes on network infrastructure; Must be robust and reliable with high performance; Must be flexible when deployed so more applications can benefit from it. We propose to study a new multipath connection approach: proxy servers based multipath connections (PSMC).
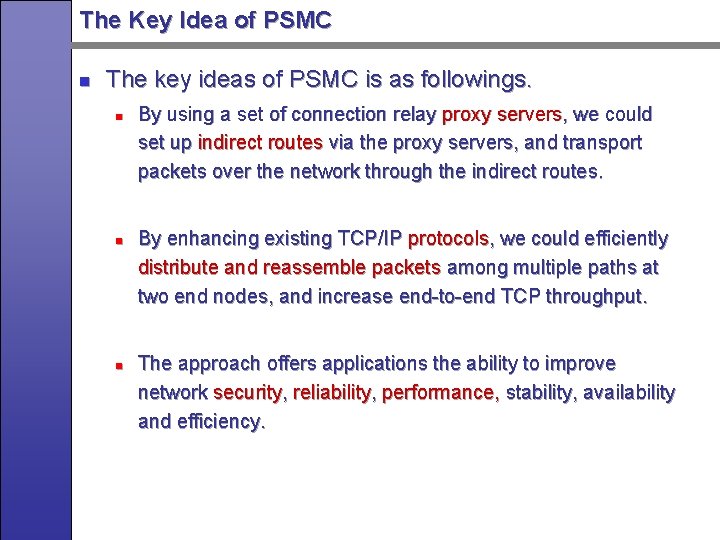
The Key Idea of PSMC n The key ideas of PSMC is as followings. n n n By using a set of connection relay proxy servers, we could set up indirect routes via the proxy servers, and transport packets over the network through the indirect routes. By enhancing existing TCP/IP protocols, we could efficiently distribute and reassemble packets among multiple paths at two end nodes, and increase end-to-end TCP throughput. The approach offers applications the ability to improve network security, reliability, performance, stability, availability and efficiency.
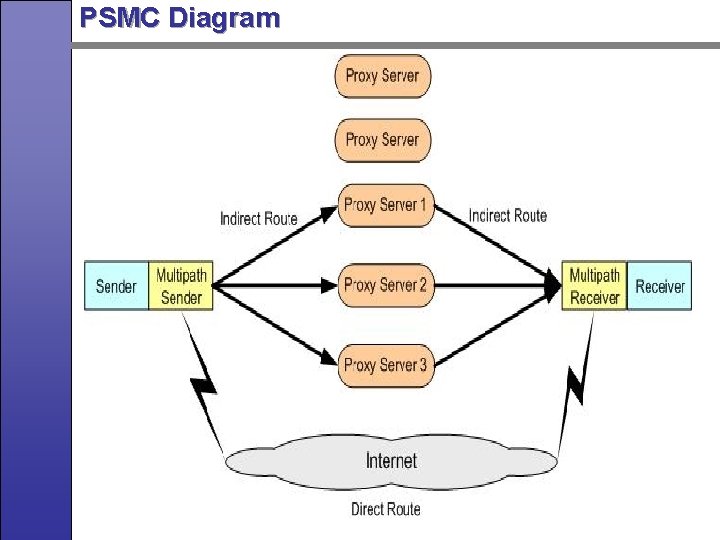
PSMC Diagram
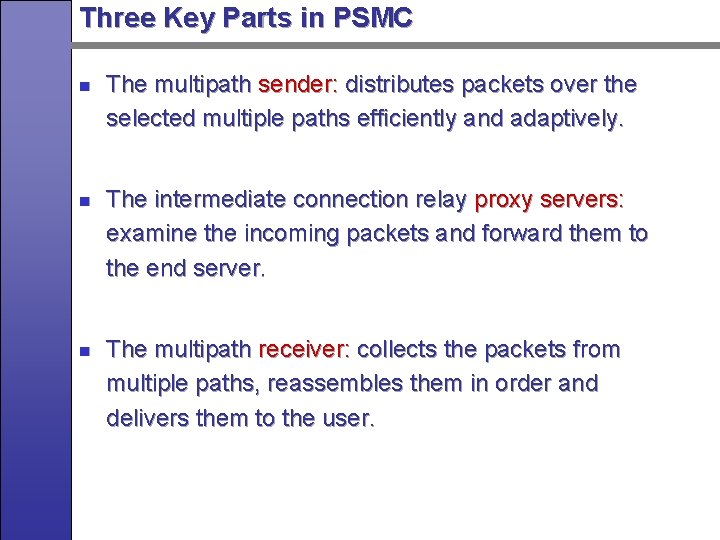
Three Key Parts in PSMC n n n The multipath sender: distributes packets over the selected multiple paths efficiently and adaptively. The intermediate connection relay proxy servers: examine the incoming packets and forward them to the end server. The multipath receiver: collects the packets from multiple paths, reassembles them in order and delivers them to the user.
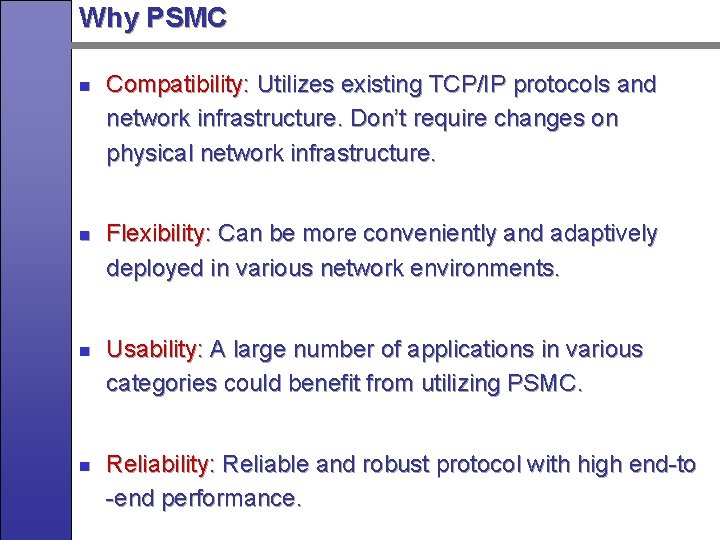
Why PSMC n n Compatibility: Utilizes existing TCP/IP protocols and network infrastructure. Don’t require changes on physical network infrastructure. Flexibility: Can be more conveniently and adaptively deployed in various network environments. Usability: A large number of applications in various categories could benefit from utilizing PSMC. Reliability: Reliable and robust protocol with high end-to -end performance.
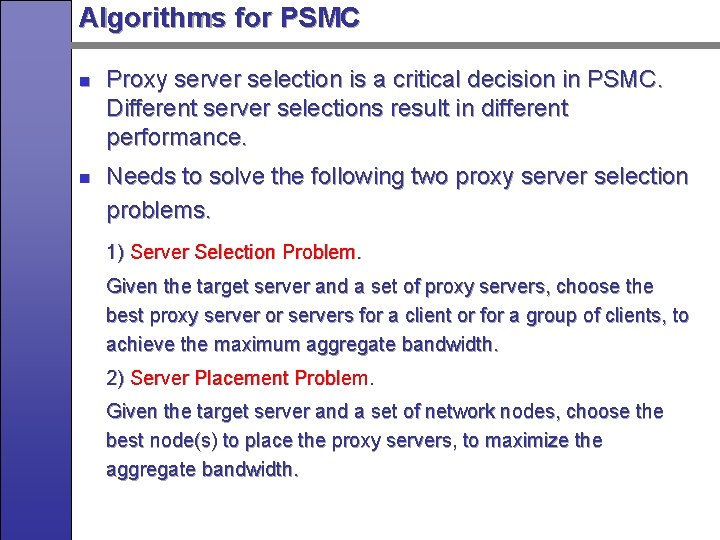
Algorithms for PSMC n n Proxy server selection is a critical decision in PSMC. Different server selections result in different performance. Needs to solve the following two proxy server selection problems. 1) Server Selection Problem. Given the target server and a set of proxy servers, choose the best proxy server or servers for a client or for a group of clients, to achieve the maximum aggregate bandwidth. 2) Server Placement Problem. Given the target server and a set of network nodes, choose the best node(s) to place the proxy servers, to maximize the aggregate bandwidth.
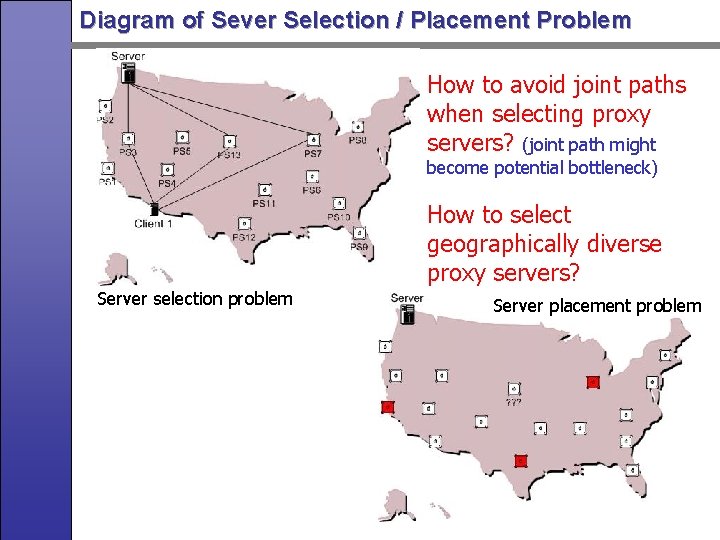
Diagram of Sever Selection / Placement Problem How to avoid joint paths when selecting proxy servers? (joint path might become potential bottleneck) How to select geographically diverse proxy servers? Server selection problem Server placement problem
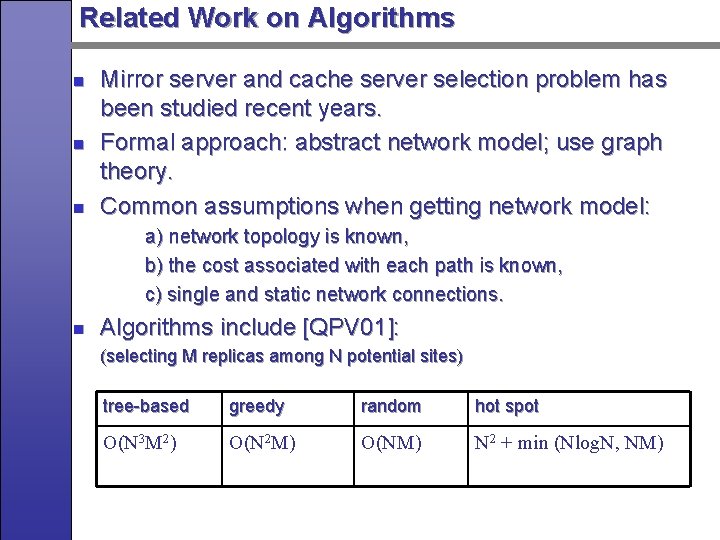
Related Work on Algorithms n n n Mirror server and cache server selection problem has been studied recent years. Formal approach: abstract network model; use graph theory. Common assumptions when getting network model: a) network topology is known, b) the cost associated with each path is known, c) single and static network connections. n Algorithms include [QPV 01]: (selecting M replicas among N potential sites) tree-based greedy random hot spot O(N 3 M 2) O(N 2 M) O(NM) N 2 + min (Nlog. N, NM)
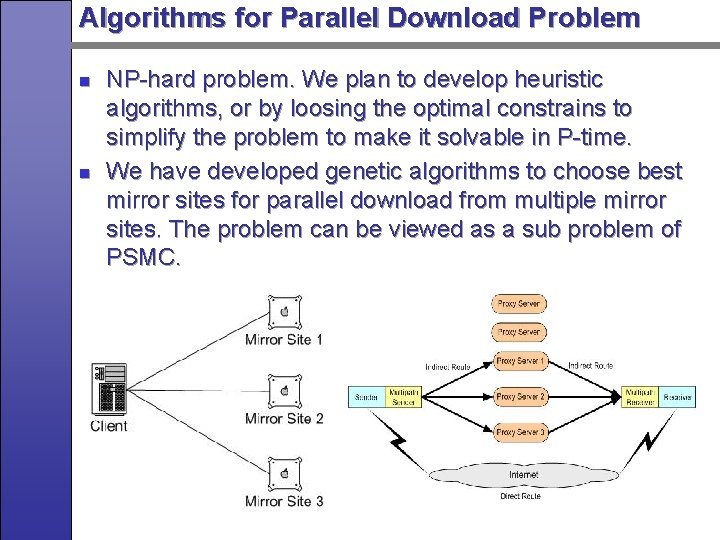
Algorithms for Parallel Download Problem n n NP-hard problem. We plan to develop heuristic algorithms, or by loosing the optimal constrains to simplify the problem to make it solvable in P-time. We have developed genetic algorithms to choose best mirror sites for parallel download from multiple mirror sites. The problem can be viewed as a sub problem of PSMC.
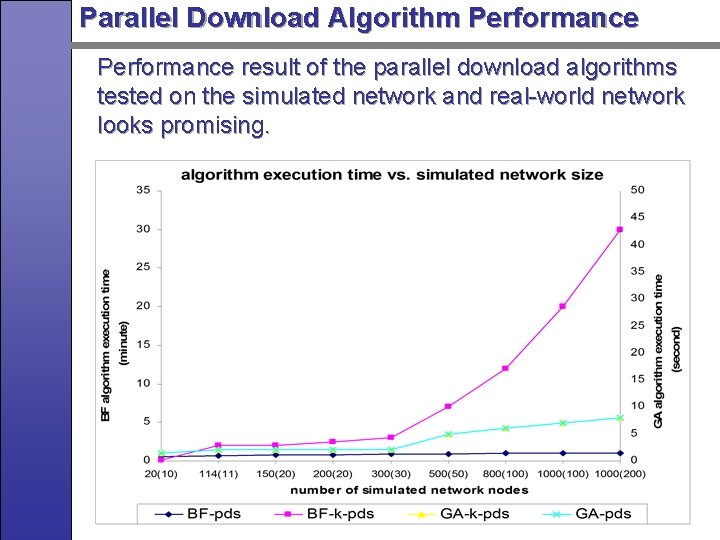
Parallel Download Algorithm Performance result of the parallel download algorithms tested on the simulated network and real-world network looks promising.
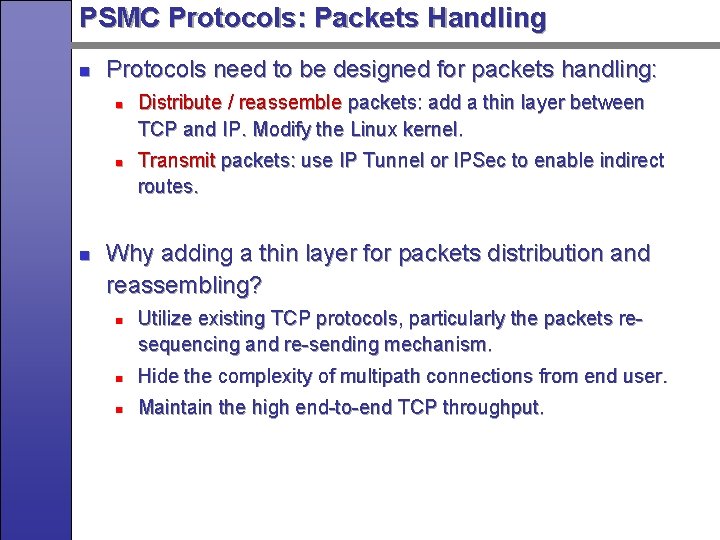
PSMC Protocols: Packets Handling n Protocols need to be designed for packets handling: n n n Distribute / reassemble packets: add a thin layer between TCP and IP. Modify the Linux kernel. Transmit packets: use IP Tunnel or IPSec to enable indirect routes. Why adding a thin layer for packets distribution and reassembling? n Utilize existing TCP protocols, particularly the packets resequencing and re-sending mechanism. n Hide the complexity of multipath connections from end user. n Maintain the high end-to-end TCP throughput.
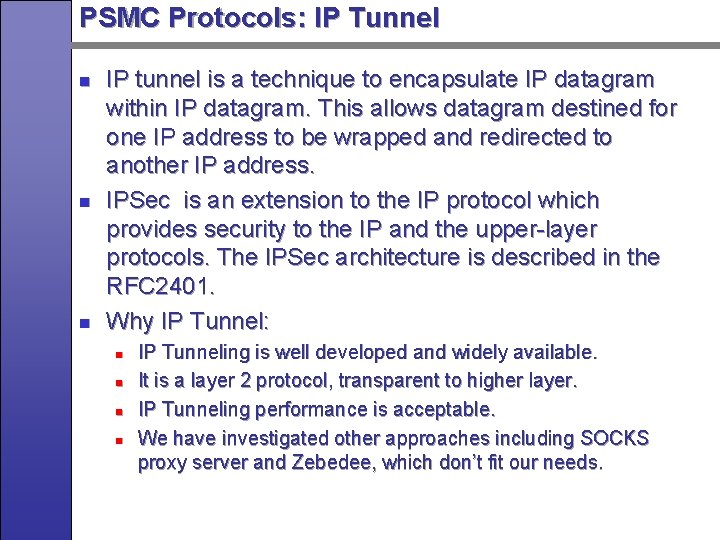
PSMC Protocols: IP Tunnel n n n IP tunnel is a technique to encapsulate IP datagram within IP datagram. This allows datagram destined for one IP address to be wrapped and redirected to another IP address. IPSec is an extension to the IP protocol which provides security to the IP and the upper-layer protocols. The IPSec architecture is described in the RFC 2401. Why IP Tunnel: n n IP Tunneling is well developed and widely available. It is a layer 2 protocol, transparent to higher layer. IP Tunneling performance is acceptable. We have investigated other approaches including SOCKS proxy server and Zebedee, which don’t fit our needs.
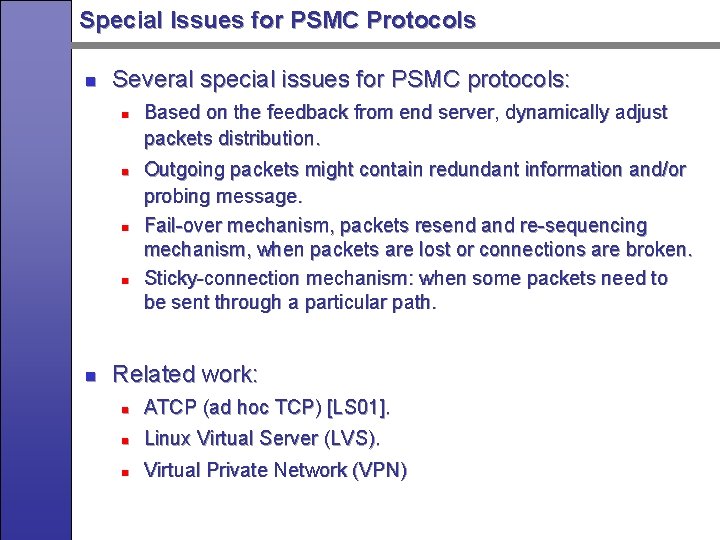
Special Issues for PSMC Protocols n Several special issues for PSMC protocols: n n n Based on the feedback from end server, dynamically adjust packets distribution. Outgoing packets might contain redundant information and/or probing message. Fail-over mechanism, packets resend and re-sequencing mechanism, when packets are lost or connections are broken. Sticky-connection mechanism: when some packets need to be sent through a particular path. Related work: n ATCP (ad hoc TCP) [LS 01]. n Linux Virtual Server (LVS). n Virtual Private Network (VPN)
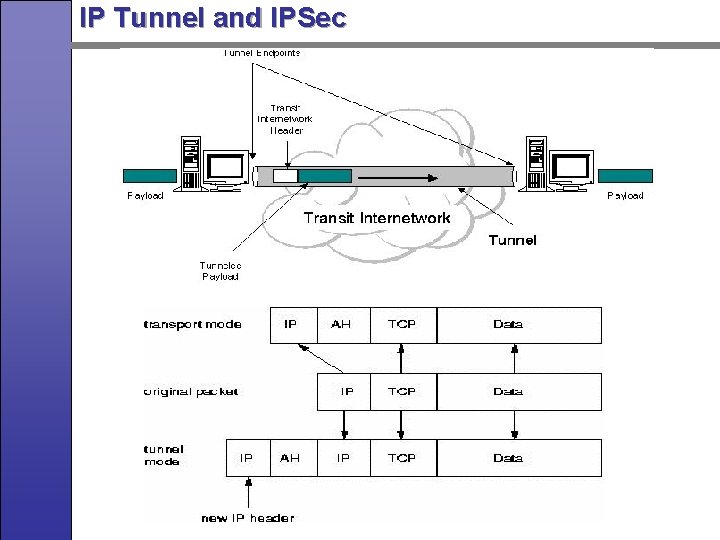
IP Tunnel and IPSec
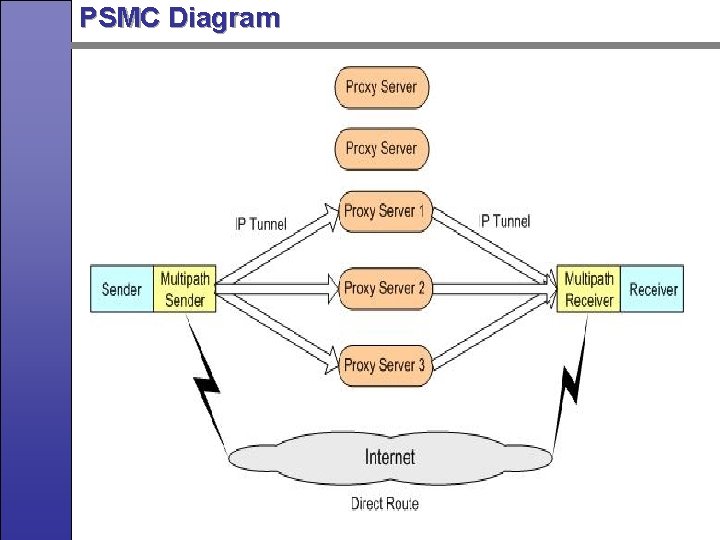
PSMC Diagram
PSMC Applications n Secure Collective Defense (SCOLD) network n PSMC in wireless ad hoc network. n Indirect route / additional bandwidth upon operational requests. n Qo. S for video streaming. n Parallel download from multiple mirror sites.
Secure Collective Defense (SCOLD) network n n SCOLD tolerates the DDo. S attacks through indirect routes via proxy servers, and improves network performance by spreading packets through multiple indirect routes. SCOLD will incorporate various cyber security techniques, like secure DNS update, Autonomous Anti-DDo. S network, IDIP(Intrusion Detection and Isolation Protocol) protocols. The prototype of SCOLD system version 1. 0 is finished with secure DNS update and indirect route. We plan to enhance SCOLD for better scalability, reliability, performance and security.
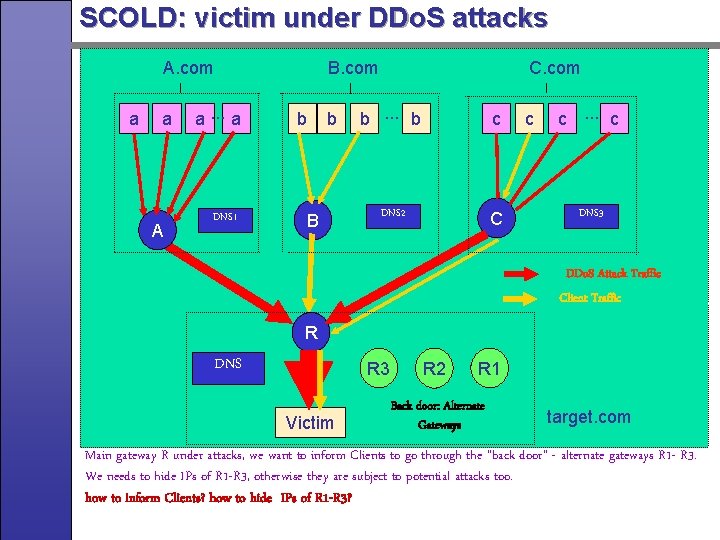
SCOLD: victim under DDo. S attacks A. com a a A a. . . a DNS 1 B. com b b B C. com b. . . b c DNS 2 C c c. . . c DNS 3 DDo. S Attack Traffic Client Traffic R DNS R 3 Victim R 2 R 1 Back door: Alternate Gateways target. com Main gateway R under attacks, we want to inform Clients to go through the “back door” - alternate gateways R 1 - R 3. We needs to hide IPs of R 1 -R 3, otherwise they are subject to potential attacks too. how to inform Clients? how to hide IPs of R 1 -R 3?
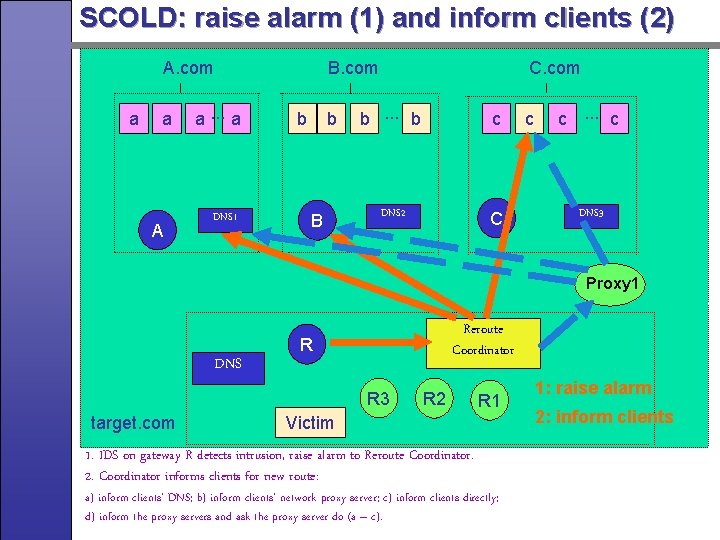
SCOLD: raise alarm (1) and inform clients (2) A. com a a A a. . . a DNS 1 B. com b b B C. com b. . . b c DNS 2 C c c. . . c DNS 3 Proxy 1 DNS Reroute Coordinator R R 3 target. com R 2 R 1 Victim 1. IDS on gateway R detects intrusion, raise alarm to Reroute Coordinator. 2. Coordinator informs clients for new route: a) inform clients’ DNS; b) inform clients’ network proxy server; c) inform clients directly; d) inform the proxy servers and ask the proxy server do (a – c). 1: raise alarm 2: inform clients
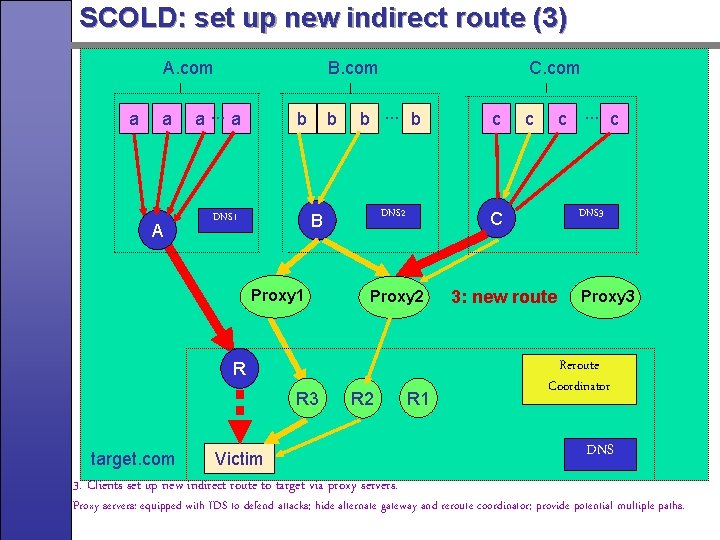
SCOLD: set up new indirect route (3) A. com a a A B. com a. . . a b b b. . . b c DNS 2 C B DNS 1 Proxy 1 C. com Proxy 2 R R 3 R 2 target. com Victim 3. Clients set up new indirect route to target via proxy servers. R 1 c. . . c c DNS 3 3: new route Proxy 3 Reroute Coordinator DNS Proxy servers: equipped with IDS to defend attacks; hide alternate gateway and reroute coordinator; provide potential multiple paths.
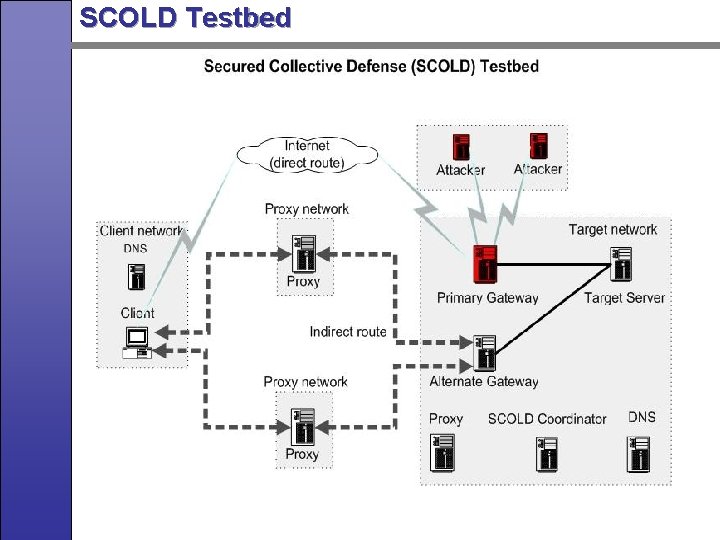
SCOLD Testbed
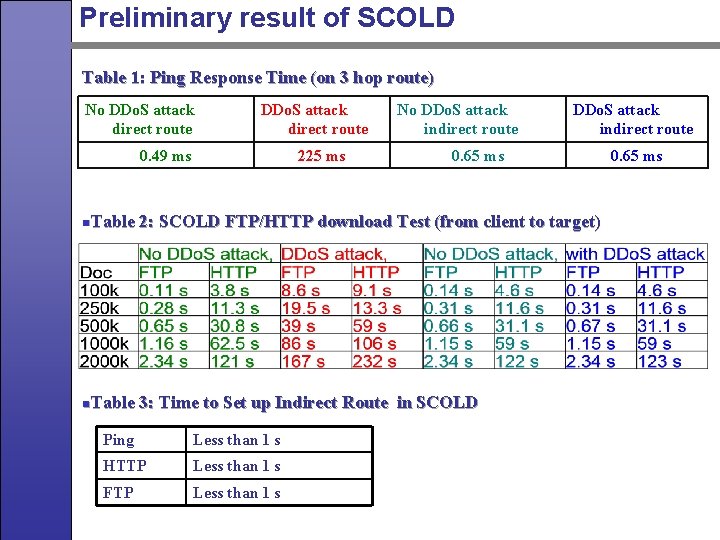
Preliminary result of SCOLD Table 1: Ping Response Time (on 3 hop route) No DDo. S attack direct route 0. 49 ms 225 ms No DDo. S attack indirect route 0. 65 ms n. Table 2: SCOLD FTP/HTTP download Test (from client to target) n. Table 3: Time to Set up Indirect Route in SCOLD Ping Less than 1 s HTTP Less than 1 s FTP Less than 1 s 0. 65 ms
PSMC Applications Evaluation n The performance and overhead of multipath connections will be evaluated. PSMC will be compared with other multipath connection approaches, like source routing, and Linux multipath connections. Extensive simulation study on PSMC applications in virtual network, real network, small scale network and large scale network will be conducted.
Security Issues Related to PSMC n n Potential security issues raised by misusing of PSMC: how to control aggressive clients? Potential attacks against PSMC: Tunneling to death? (similar to ping to death). How to detect and deal with comprised nodes in PSMC network? Study the collective defend mechanism to tie different organizations with better cooperation and collaboration.
Research Plan n Will systematically study PSMC in the following areas: n Algorithms for server selections n Protocols for packet handling n Applications n Security issues
Thank you!
- Slides: 32