On NonBlackBox Proofs of Security Boaz Barak Princeton
On Non-Black-Box Proofs of Security Boaz Barak Princeton
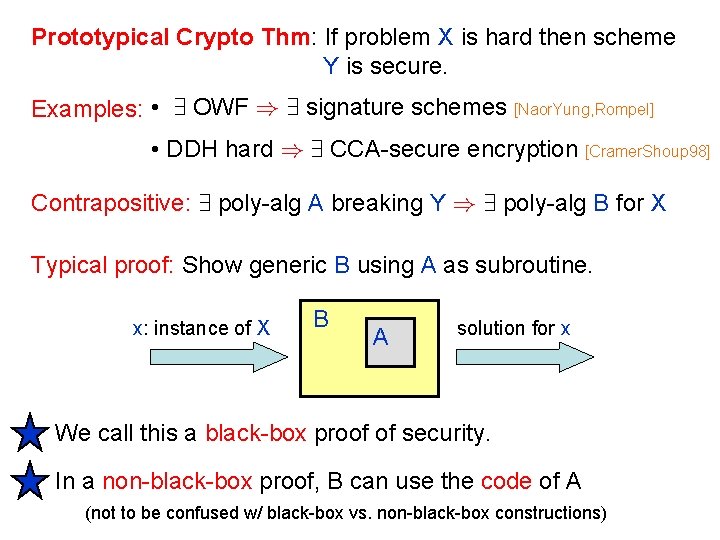
Prototypical Crypto Thm: If problem X is hard then scheme Y is secure. Examples: • 9 OWF ) 9 signature schemes [Naor. Yung, Rompel] • DDH hard ) 9 CCA-secure encryption [Cramer. Shoup 98] Contrapositive: 9 poly-alg A breaking Y ) 9 poly-alg B for X Typical proof: Show generic B using A as subroutine. x: instance of X B A solution for x We call this a black-box proof of security. In a non-black-box proof, B can use the code of A (not to be confused w/ black-box vs. non-black-box constructions)
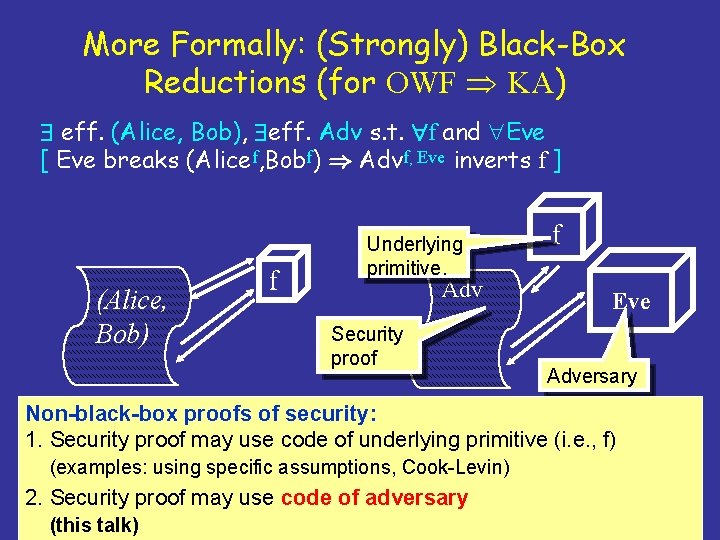
More Formally: (Strongly) Black-Box Reductions (for OWF KA) eff. (Alice, Bob), eff. Adv s. t. f and Eve [ Eve breaks (Alicef, Bobf) ) Advf, Eve inverts f ] (Alice, Bob) f Underlying primitive. Adv Security proof f Eve Adversary Non-black-box proofs of security: 1. Security proof may use code of underlying primitive (i. e. , f) (examples: using specific assumptions, Cook-Levin) 2. Security proof may use code of adversary (this talk)
Non-Black-Box Security Proofs Advantages: • More general proof technique, can prove more thms. • Bypass proven limitations of black-box proofs. (Somewhat surprisingly, without “real” understanding of computation. ) Disadvantages: • Less robust proofs, more dependence on model. • E. g. : Uniform TMs vs. circuits, quantum algorithms. • Seem to come at steep cost in efficiency.
![Applications of Non-BB Proofs: Composable protocols: • O(1)-round bounded concurrent zero-knowledge (ZK) [B. 01] Applications of Non-BB Proofs: Composable protocols: • O(1)-round bounded concurrent zero-knowledge (ZK) [B. 01]](http://slidetodoc.com/presentation_image/19e9dbc0cb8683005591fb47954b0673/image-5.jpg)
Applications of Non-BB Proofs: Composable protocols: • O(1)-round bounded concurrent zero-knowledge (ZK) [B. 01] • O(1)-round concurrent, non-malleable commitments [B. 02], [Pass. Rosen 05 a], [Pass. Rosen 05 b] • Concurrent, non-malleable general computation [Lindell 03], [Pass. Rosen 03], [Pass 04], [B. Sahai 05] Strong Forms of Zero Knowledge: • Resettable ZK proof of knowledge [B. Goldwasser. Goldreich. Lindell 01] • Resettably-sound ZK • ZK with strict poly-time simulation & extraction [B. Lindell 02] O(1)-round general multiparty computation [Katz. Ostrovsky. Smith 03], [Pass 04]
![Plan I Basic Non-BB ZK Protocol [B. 01] II Making it bounded-concurrent [B. 01] Plan I Basic Non-BB ZK Protocol [B. 01] II Making it bounded-concurrent [B. 01]](http://slidetodoc.com/presentation_image/19e9dbc0cb8683005591fb47954b0673/image-6.jpg)
Plan I Basic Non-BB ZK Protocol [B. 01] II Making it bounded-concurrent [B. 01] III Making it bounded non-malleable. [Pass. 04] IV Unbounded concurrency and non-malleability using super-polynomial simulation. [B. Sahai. 04] V Limitations and open questions.
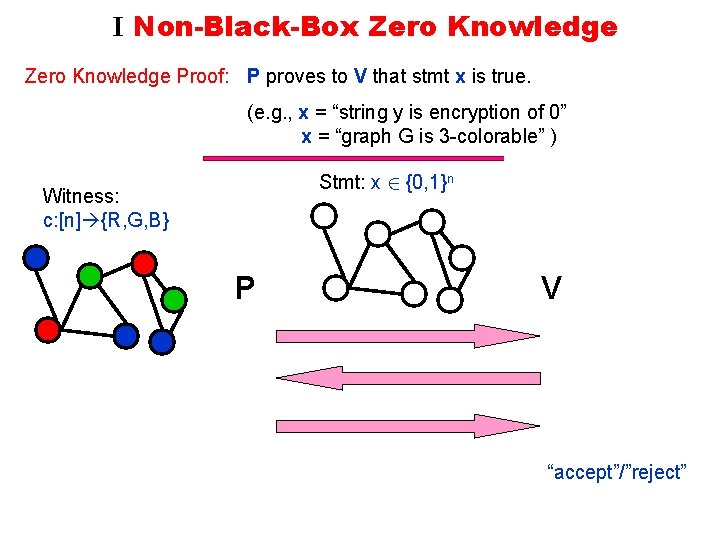
I Non-Black-Box Zero Knowledge Proof: P proves to V that stmt x is true. (e. g. , x = “string y is encryption of 0” x = “graph G is 3 -colorable” ) Stmt: x 2 {0, 1}n Witness: c: [n] {R, G, B} P V “accept”/”reject”
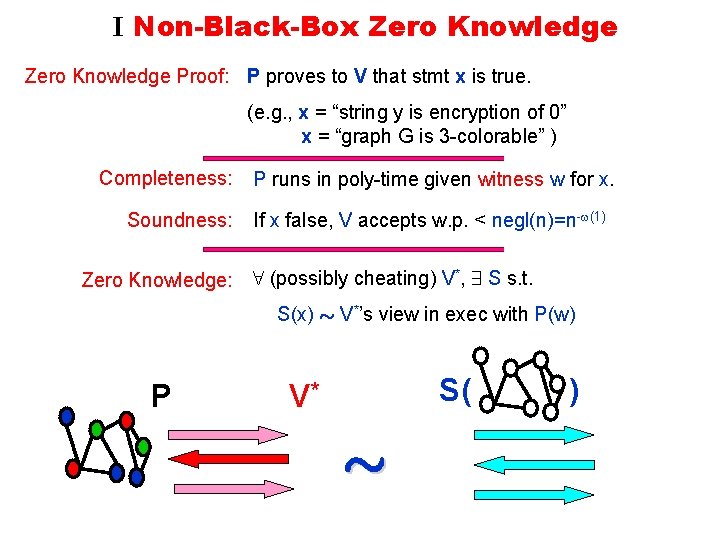
I Non-Black-Box Zero Knowledge Proof: P proves to V that stmt x is true. (e. g. , x = “string y is encryption of 0” x = “graph G is 3 -colorable” ) Completeness: Soundness: Zero Knowledge: P runs in poly-time given witness w for x. If x false, V accepts w. p. < negl(n)=n- (1) 8 (possibly cheating) V*, 9 S s. t. S(x) » V*’s view in exec with P(w) P S( V* » )
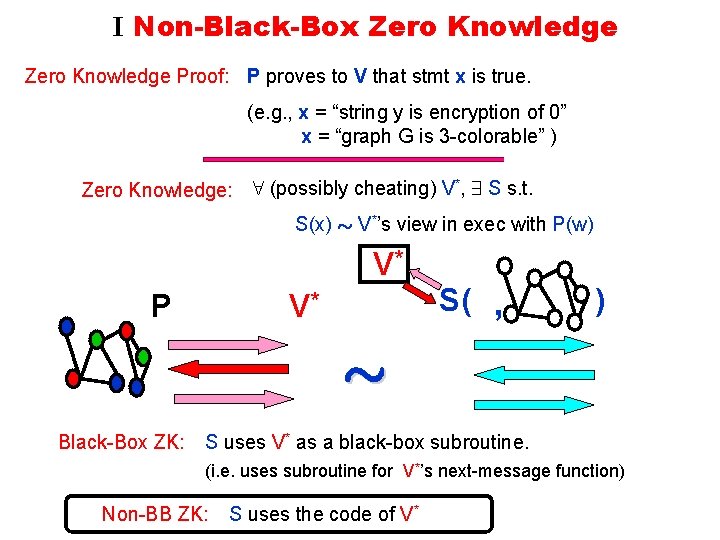
I Non-Black-Box Zero Knowledge Proof: P proves to V that stmt x is true. (e. g. , x = “string y is encryption of 0” x = “graph G is 3 -colorable” ) Zero Knowledge: 8 (possibly cheating) V*, 9 S s. t. S(x) » V*’s view in exec with P(w) V* P S( , V* ) » Black-Box ZK: S uses V* as a black-box subroutine. (i. e. uses subroutine for V*’s next-message function) Non-BB ZK: S uses the code of V*
![Some Tools Commitments: [Blum 84], [Naor 91] Efficient func Com: {0, 1}k£{0, 1}n {0, Some Tools Commitments: [Blum 84], [Naor 91] Efficient func Com: {0, 1}k£{0, 1}n {0,](http://slidetodoc.com/presentation_image/19e9dbc0cb8683005591fb47954b0673/image-10.jpg)
Some Tools Commitments: [Blum 84], [Naor 91] Efficient func Com: {0, 1}k£{0, 1}n {0, 1}m Hiding: 8 x, x’ Com(x, Un) » Com(x’, Un) Binding: x x’ Com(x, {0, 1}n), Com(x’, {0, 1}n) disjoint x Collision Resistant Hash (CRH): (Notation: Com(x) = Com(x, Un) ) Collection H of efficient functions {0, 1}* {0, 1}n s. t. for random h 2 H hard to find x x’ w/ h(x)=h(x’) (implies CRH from {0, 1}2 n to {0, 1}n) [Goldwasser. Micali. Rivest 84], SHA 1, AES, … When proving x 1Çx 2, verifier can’t tell witness used. Witness Indistinguishable • Implied by zero knowledge. Proofs (WI): • Closed under concurrent composition. [Feige. Shamir 90]
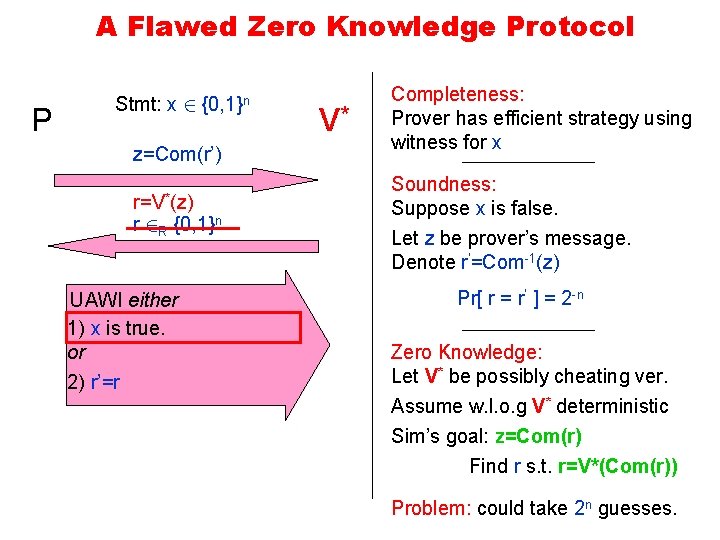
A Flawed Zero Knowledge Protocol P Stmt: x 2 {0, 1}n z=Com(r’) r=V*(z) r 2 R {0, 1}n UAWI either 1) x is true. or 2) r’=r V* Completeness: Prover has efficient strategy using witness for x Soundness: Suppose x is false. Let z be prover’s message. Denote r’=Com-1(z) Pr[ r = r’ ] = 2 -n Zero Knowledge: Let V* be possibly cheating ver. Assume w. l. o. g V* deterministic Sim’s goal: z=Com(r) Find r s. t. r=V*(Com(r)) Problem: could take 2 n guesses.
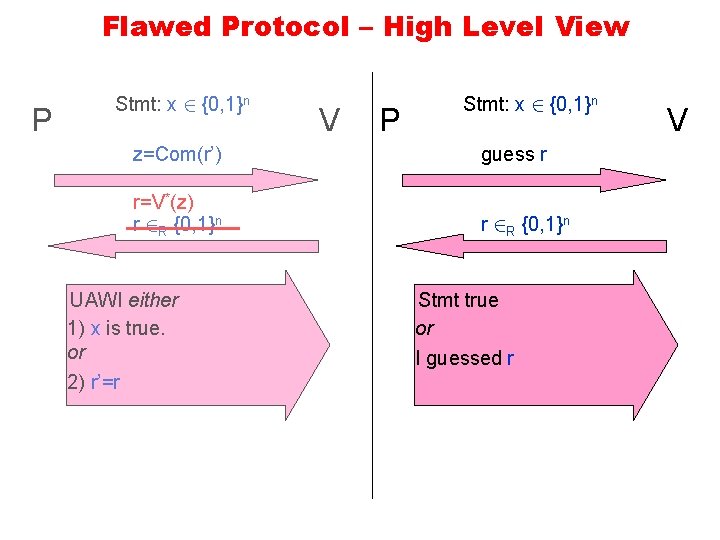
Flawed Protocol – High Level View P Stmt: x 2 {0, 1}n P z=Com(r’) guess r r=V*(z) r 2 R {0, 1}n UAWI either 1) x is true. or 2) r’=r V Stmt: x 2 {0, 1}n Stmt true or I guessed r V
![Main Tool – Universal Arguments Interactive proof system for super-polynomial languages. [Kilian 92], [Micali Main Tool – Universal Arguments Interactive proof system for super-polynomial languages. [Kilian 92], [Micali](http://slidetodoc.com/presentation_image/19e9dbc0cb8683005591fb47954b0673/image-13.jpg)
Main Tool – Universal Arguments Interactive proof system for super-polynomial languages. [Kilian 92], [Micali 94], [B. Goldreich 02] Based on following variant of PCP thm: [Babai. Fortnow. Levin. Szegedy 91] Every statement verifiable in T time deterministically, can be proven in polylog(T) time in “prob. proof in sky” (PCP) model. n bits description M x TO(1) long proof T running time Statement: “M(x)=1” (M can be deterministic/non-det) c queries Verifier 2 - (c) error c¢polylog(T) time
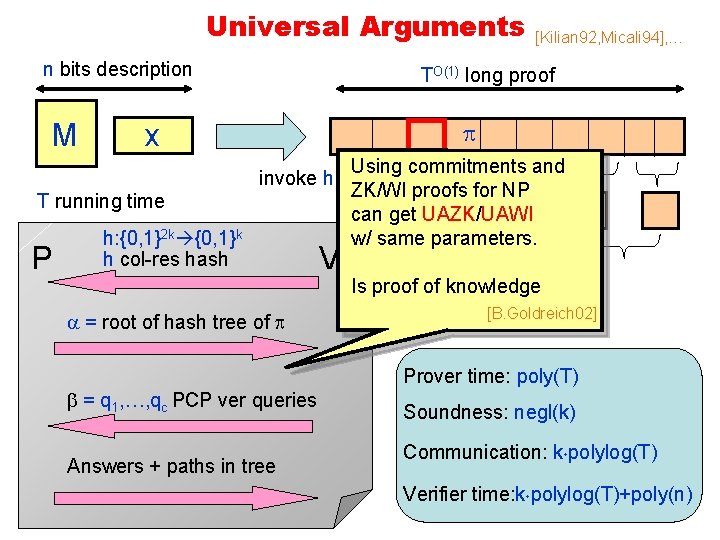
Universal Arguments n bits description M TO(1) long proof x invoke h T running time P [Kilian 92, Micali 94], … h: {0, 1}2 k {0, 1}k h col-res hash = root of hash tree of = q 1, …, qc PCP ver queries Answers + paths in tree V Using commitments and ZK/WI proofs for NP can get UAZK/UAWI w/ same parameters. … Is proof of knowledge [Merkle] root [B. Goldreich 02] Prover time: poly(T) Soundness: negl(k) Communication: k¢polylog(T) Verifier time: k¢polylog(T)+poly(n)
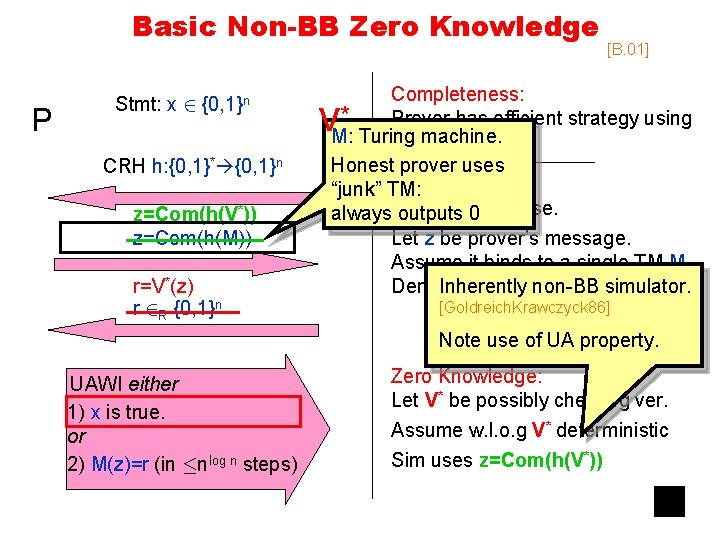
Basic Non-BB Zero Knowledge P Stmt: x 2 {0, 1}n CRH h: {0, 1}* {0, 1}n z=Com(h(V*)) z=Com(h(M)) r=V*(z) r 2 R {0, 1}n UAWI either 1) x is true. or 2) M(z)=r (in ·nlog n steps) [B. 01] Completeness: * Prover has efficient strategy using M: Turing machine. witness for x Honest prover uses Soundness: “junk” TM: always. Suppose outputs 0 x is false. Let z be prover’s message. Assume it binds to a single TM M. Inherently Denote r’=M(z) non-BB simulator. V [Goldreich. Krawczyck 86] Pr[ r = r’ ] = 2 -n Note use of UA property. Zero Knowledge: Let V* be possibly cheating ver. Assume w. l. o. g V* deterministic Sim uses z=Com(h(V*))
![High Level View: Basic Non-BB ZK [B. 01] P Stmt: x 2 {0, 1}n High Level View: Basic Non-BB ZK [B. 01] P Stmt: x 2 {0, 1}n](http://slidetodoc.com/presentation_image/19e9dbc0cb8683005591fb47954b0673/image-16.jpg)
High Level View: Basic Non-BB ZK [B. 01] P Stmt: x 2 {0, 1}n V P Stmt: x 2 {0, 1}n CRH h: {0, 1}* {0, 1}n z=Com(h(M)) r 2 R {0, 1}n UAWI either 1) x is true. or 2) M(z)=r (in ·nlog n steps) implicitly guess r r 2 R {0, 1}n Stmt true or I guessed r V
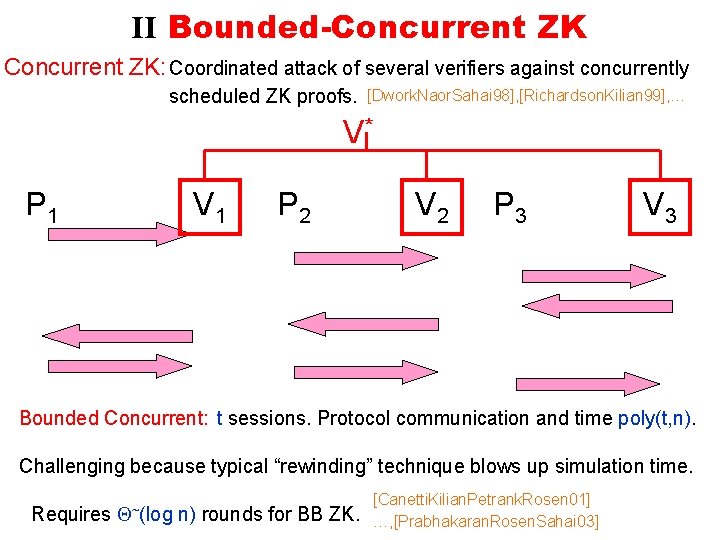
II Bounded-Concurrent ZK: Coordinated attack of several verifiers against concurrently scheduled ZK proofs. [Dwork. Naor. Sahai 98], [Richardson. Kilian 99], … V* P 1 V 1 P 2 V 2 P 3 V 3 Bounded Concurrent: t sessions. Protocol communication and time poly(t, n). Challenging because typical “rewinding” technique blows up simulation time. Requires ~(log n) rounds for BB ZK. [Canetti. Kilian. Petrank. Rosen 01] …, [Prabhakaran. Rosen. Sahai 03]
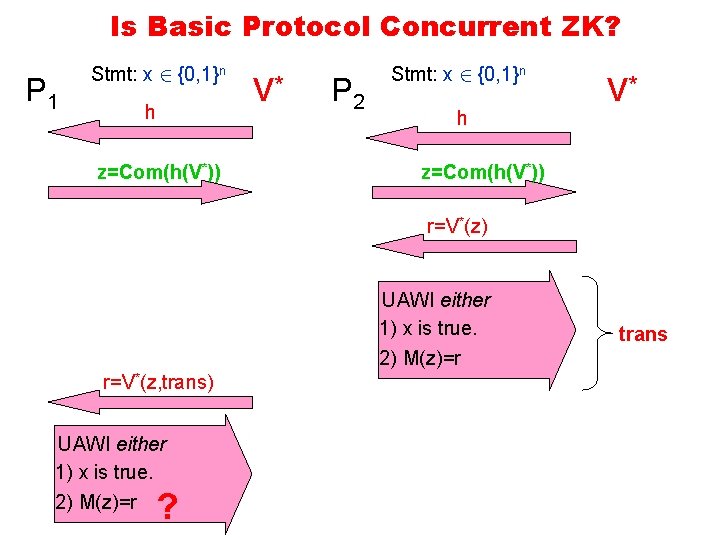
Is Basic Protocol Concurrent ZK? P 1 Stmt: x 2 {0, 1}n h z=Com(h(V*)) V* P 2 Stmt: x 2 {0, 1}n h V* z=Com(h(V*)) r=V*(z) UAWI either 1) x is true. 2) M(z)=r r=V*(z, trans) UAWI either 1) x is true. 2) M(z)=r ? trans
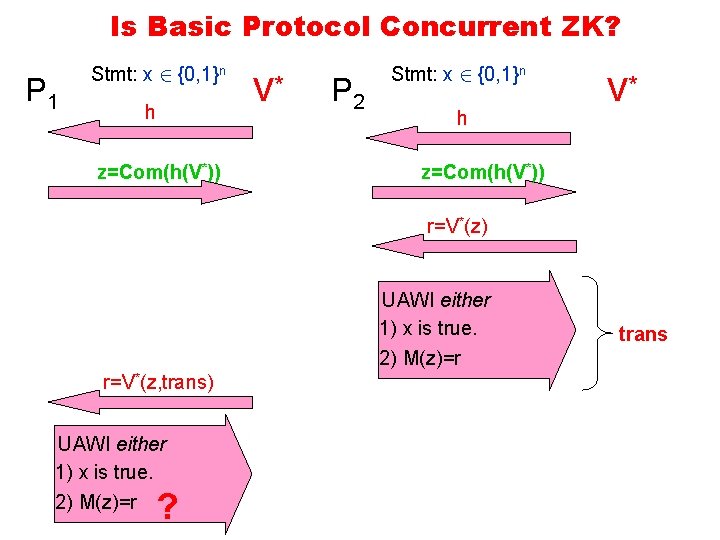
Is Basic Protocol Concurrent ZK? P 1 Stmt: x 2 {0, 1}n h z=Com(h(V*)) V* P 2 Stmt: x 2 {0, 1}n h V* z=Com(h(V*)) r=V*(z) UAWI either 1) x is true. 2) M(z)=r r=V*(z, trans) UAWI either 1) x is true. 2) M(z)=r ? trans
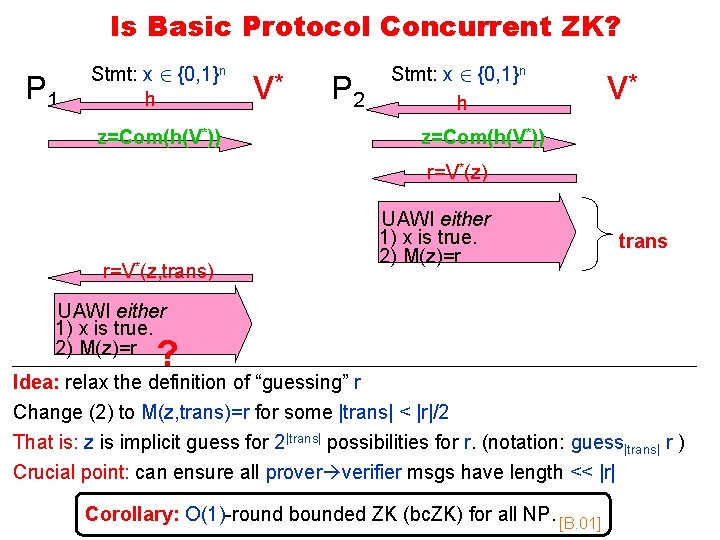
Is Basic Protocol Concurrent ZK? P 1 Stmt: x 2 {0, 1}n h z=Com(h(V*)) V* P 2 Stmt: x 2 {0, 1}n h V* z=Com(h(V*)) r=V*(z, trans) UAWI either 1) x is true. 2) M(z)=r trans UAWI either 1) x is true. 2) M(z)=r ? Idea: relax the definition of “guessing” r Change (2) to M(z, trans)=r for some |trans| < |r|/2 That is: z is implicit guess for 2|trans| possibilities for r. (notation: guess|trans| r ) Crucial point: can ensure all prover verifier msgs have length << |r| Corollary: O(1)-round bounded ZK (bc. ZK) for all NP. [B. 01]
![III Non-Malleable ZK Adversary is “man-in-middle” between prover & verifier. [Dwork. Dolev. Naor 90] III Non-Malleable ZK Adversary is “man-in-middle” between prover & verifier. [Dwork. Dolev. Naor 90]](http://slidetodoc.com/presentation_image/19e9dbc0cb8683005591fb47954b0673/image-21.jpg)
III Non-Malleable ZK Adversary is “man-in-middle” between prover & verifier. [Dwork. Dolev. Naor 90] Security goal: Ensure proof to honest verifiers is sound even when simulating honest prover – simulation soundness. [Sahai 00] V* P V 1 P 2 • 2 sessions with unique id. • Arbitrary scheduling. V (synchronized is hardest) [DDN]: O(logn)-rounds [B. 02]: O(1)-rounds A bit different non-BB technique. [Pass 04]: O(1)-rounds bounded non-mal (simpler, weaker assump) [Pass. Rosen 05 a]: make [Pass 04] unbounded NM Bounded non-malleability: id’s come from set of size t, protocol communication and time poly(t, n)
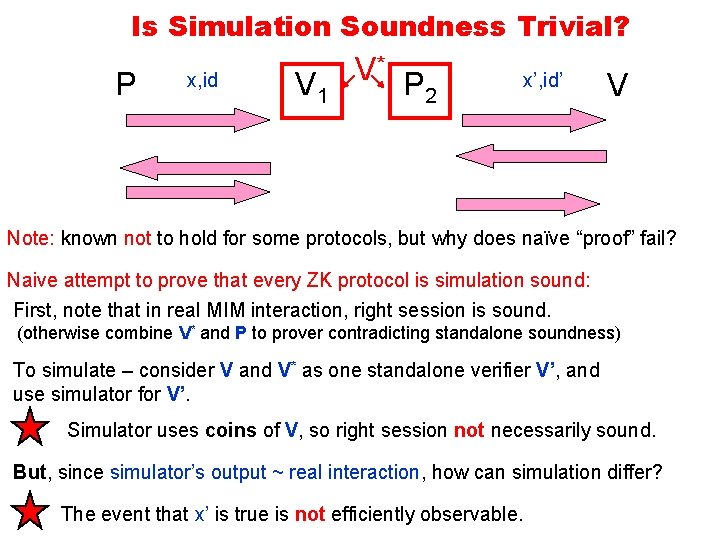
Is Simulation Soundness Trivial? P x, id V 1 V* P 2 x’, id’ V Note: known not to hold for some protocols, but why does naïve “proof” fail? Naive attempt to prove that every ZK protocol is simulation sound: First, note that in real MIM interaction, right session is sound. (otherwise combine V* and P to prover contradicting standalone soundness) To simulate – consider V and V* as one standalone verifier V’, and use simulator for V’. Simulator uses coins of V, so right session not necessarily sound. But, since simulator’s output ~ real interaction, how can simulation differ? The event that x’ is true is not efficiently observable.
![Pass’s Bounded-NMZK Protocol [Pass 04] Crucial observation: use bc. ZK to get one-directional simulation Pass’s Bounded-NMZK Protocol [Pass 04] Crucial observation: use bc. ZK to get one-directional simulation](http://slidetodoc.com/presentation_image/19e9dbc0cb8683005591fb47954b0673/image-23.jpg)
Pass’s Bounded-NMZK Protocol [Pass 04] Crucial observation: use bc. ZK to get one-directional simulation soundness. P imp. guess r 1 V 1 P 2 r 12 R{0, 1}m 1 Stmt true or guessedm 1 r 1 imp. guess r 22 R{0, 1}m 2 Stmt true or guessedm 2 r 2 If m 1 >> |right session| then can simulate left w/o right verifier’s coins! Pass’s Protocol: 1. Use |r| = id*B (B bound on all other comm in all sessions, note id’s bounded) 2. Run another iteration w/ id = max{id} - id 3. Prove in WI that at least one of the iterations succeeded. V
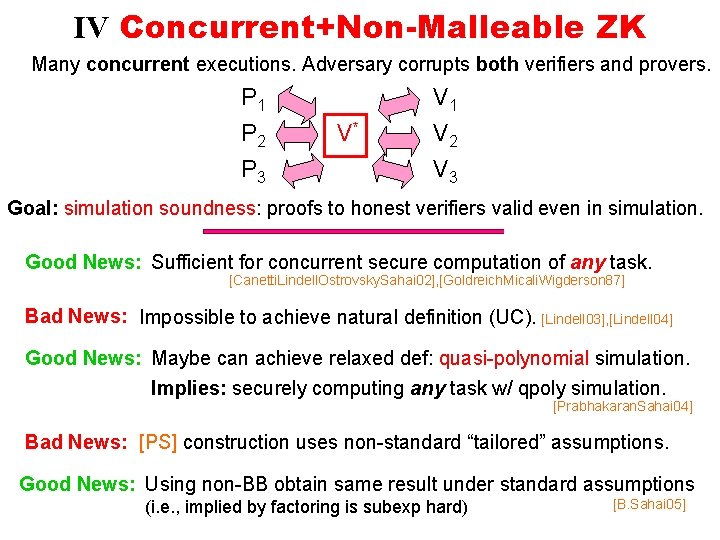
IV Concurrent+Non-Malleable ZK Many concurrent executions. Adversary corrupts both verifiers and provers. P 1 P 2 P 3 V* V 1 V 2 V 3 Goal: simulation soundness: proofs to honest verifiers valid even in simulation. Good News: Sufficient for concurrent secure computation of any task. [Canetti. Lindell. Ostrovsky. Sahai 02], [Goldreich. Micali. Wigderson 87] Bad News: Impossible to achieve natural definition (UC). [Lindell 03], [Lindell 04] Good News: Maybe can achieve relaxed def: quasi-polynomial simulation. Implies: securely computing any task w/ qpoly simulation. [Prabhakaran. Sahai 04] Bad News: [PS] construction uses non-standard “tailored” assumptions. Good News: Using non-BB obtain same result under standard assumptions (i. e. , implied by factoring is subexp hard) [B. Sahai 05]
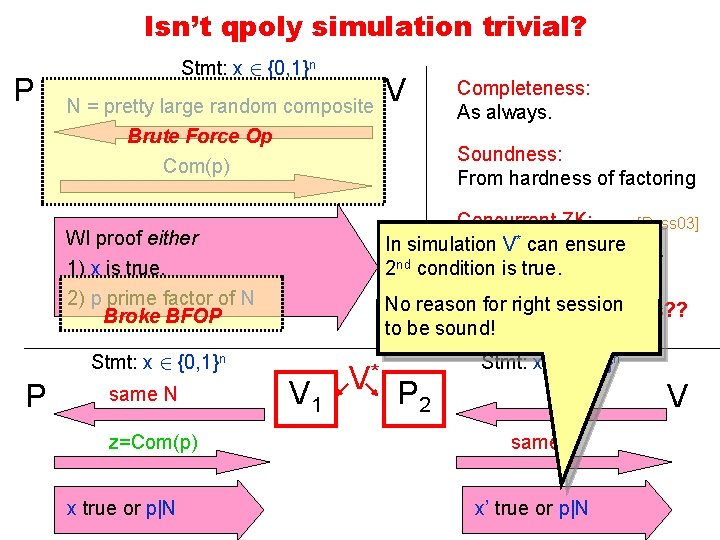
Isn’t qpoly simulation trivial? P Stmt: x 2 {0, 1}n N = pretty large random composite Brute Force Op V Soundness: From hardness of factoring Com(p) Concurrent ZK: [Pass 03] In simulation V* can ensure Straight-line simulation. nd 2 condition is true. WI proof either 1) x is true. 2) p prime factor of N Broke BFOP Stmt: x 2 {0, 1}n P same N z=Com(p) x true or p|N Completeness: As always. No reason for right session Simulation soundness? ? to be sound! V 1 V* P 2 Stmt: x’ 2 {0, 1}n N same z x’ true or p|N V
![Concurrent Non-Mal q. ZK Protocol [B. Sahai 05] Starting point: Pass’s protocol for bounded-NM Concurrent Non-Mal q. ZK Protocol [B. Sahai 05] Starting point: Pass’s protocol for bounded-NM](http://slidetodoc.com/presentation_image/19e9dbc0cb8683005591fb47954b0673/image-26.jpg)
Concurrent Non-Mal q. ZK Protocol [B. Sahai 05] Starting point: Pass’s protocol for bounded-NM zero knowledge 1 st Step: Change it to handle #id’s to t=nlog n Problem: In Pass’s protocol communication>t Solution: “Compress” the long messages. Com(h(r 1)) r 12 R{0, 1} m 1 If proof succssesful, have qpoly-time knowledge extractor can obtain r 1 by rewinding Is it (stand-alone) sound? Is it (stand-alone) zero knowledge? Implicitly send r 1 UAZK Know r 12 R{0, 1} r 1=0 n m 1
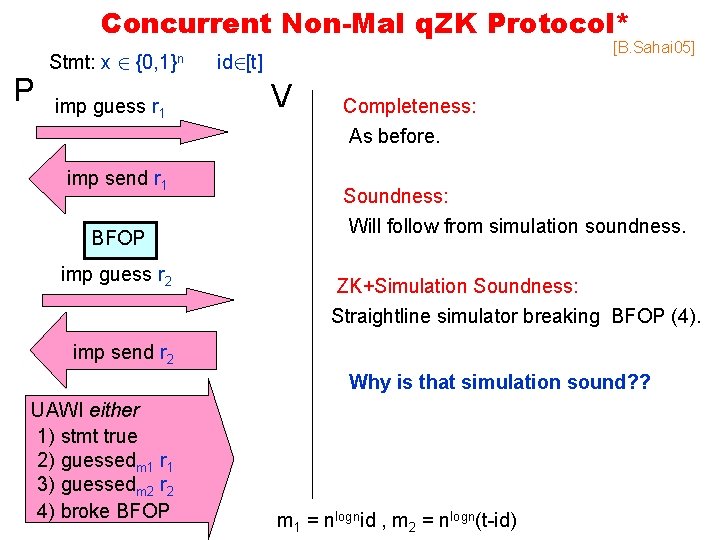
Concurrent Non-Mal q. ZK Protocol* P Stmt: x 2 {0, 1}n imp guess r 1 imp send r 1 BFOP imp guess r 2 [B. Sahai 05] id 2[t] V Completeness: As before. Soundness: Will follow from simulation soundness. ZK+Simulation Soundness: Straightline simulator breaking BFOP (4). imp send r 2 Why is that simulation sound? ? UAWI either 1) stmt true 2) guessedm 1 r 1 3) guessedm 2 r 2 4) broke BFOP m 1 = nlognid , m 2 = nlogn(t-id)
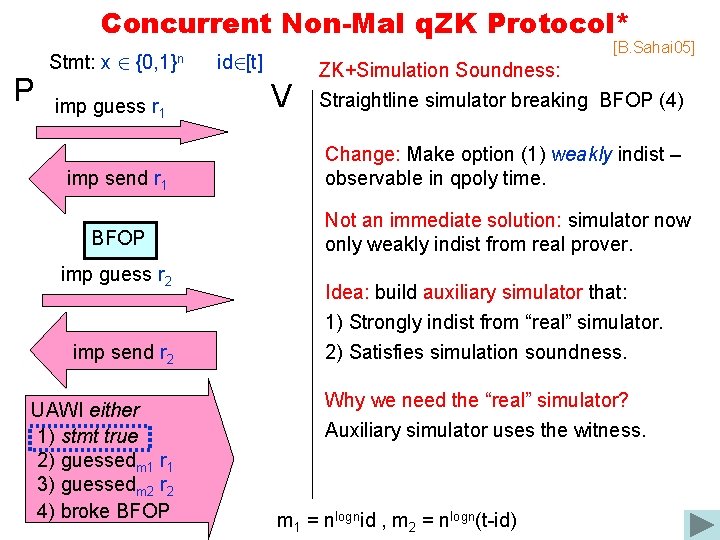
Concurrent Non-Mal q. ZK Protocol* P Stmt: x 2 {0, 1}n imp guess r 1 [B. Sahai 05] id 2[t] V ZK+Simulation Soundness: Straightline simulator breaking BFOP (4) imp send r 1 Change: Make option (1) weakly indist – observable in qpoly time. BFOP Not an immediate solution: simulator now only weakly indist from real prover. imp guess r 2 imp send r 2 UAWI either 1) stmt true 2) guessedm 1 r 1 3) guessedm 2 r 2 4) broke BFOP Idea: build auxiliary simulator that: 1) Strongly indist from “real” simulator. 2) Satisfies simulation soundness. Why we need the “real” simulator? Auxiliary simulator uses the witness. m 1 = nlognid , m 2 = nlogn(t-id)
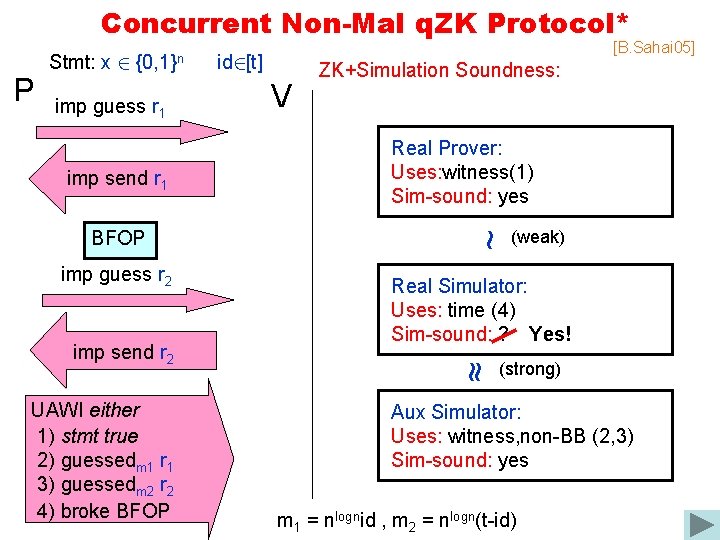
Concurrent Non-Mal q. ZK Protocol* P Stmt: x 2 {0, 1}n imp guess r 1 imp send r 1 imp guess r 2 UAWI either 1) stmt true 2) guessedm 1 r 1 3) guessedm 2 r 2 4) broke BFOP V ZK+Simulation Soundness: Real Prover: Uses: witness(1) Sim-sound: yes (weak) Real Simulator: Uses: time (4) Sim-sound: ? Yes! ~ imp send r 2 id 2[t] ~ BFOP [B. Sahai 05] (strong) Aux Simulator: Uses: witness, non-BB (2, 3) Sim-sound: yes m 1 = nlognid , m 2 = nlogn(t-id)
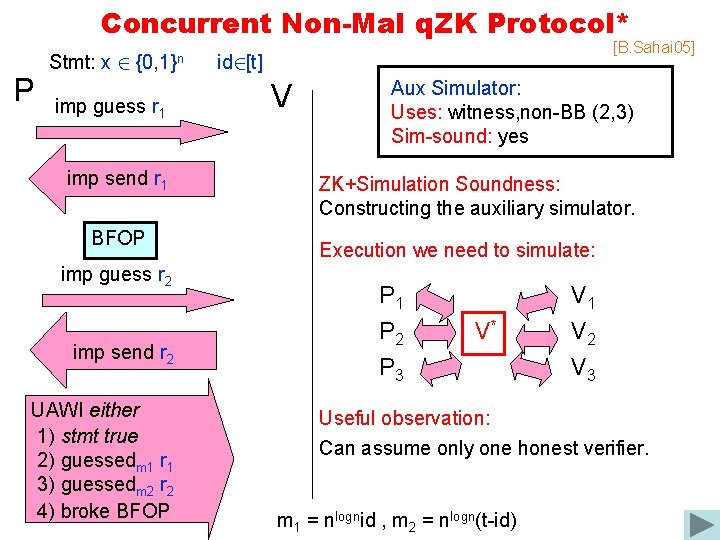
Concurrent Non-Mal q. ZK Protocol* P Stmt: x 2 {0, 1}n imp guess r 1 imp send r 1 BFOP imp guess r 2 imp send r 2 UAWI either 1) stmt true 2) guessedm 1 r 1 3) guessedm 2 r 2 4) broke BFOP [B. Sahai 05] id 2[t] V Aux Simulator: Uses: witness, non-BB (2, 3) Sim-sound: yes ZK+Simulation Soundness: Constructing the auxiliary simulator. Execution we need to simulate: P 1 P 2 P 3 V* V 1 V 2 V 3 Useful observation: Can assume only one honest verifier. m 1 = nlognid , m 2 = nlogn(t-id)
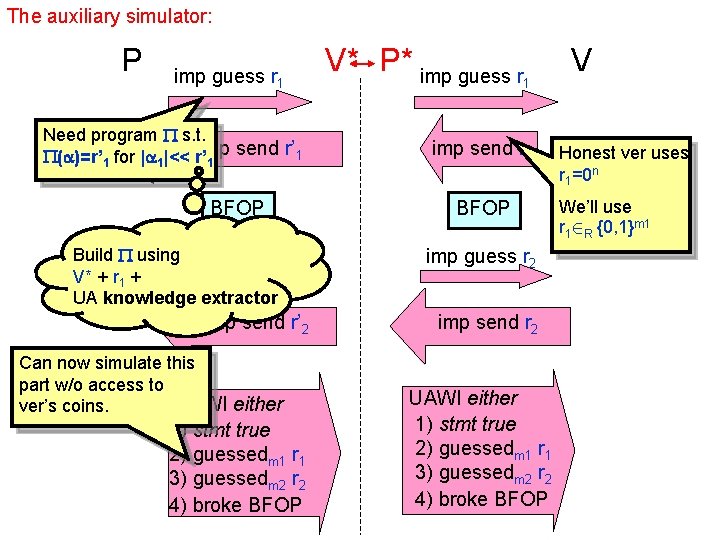
The auxiliary simulator: P imp guess r 1 Need program s. t. send r’ 1 ( )=r’ 1 for | 1|<< r’imp 1 BFOP Build using imp guess r’ 2 V* + r 1 + UA knowledge extractor imp send r’ 2 Can now simulate this part w/o access to UAWI either ver’s coins. 1) stmt true 2) guessedm 1 r 1 3) guessedm 2 r 2 4) broke BFOP V* P* imp guess r 1 imp send r 1 BFOP imp guess r 2 imp send r 2 UAWI either 1) stmt true 2) guessedm 1 r 1 3) guessedm 2 r 2 4) broke BFOP V Honest ver uses r 1=0 n We’ll use r 12 R {0, 1}m 1
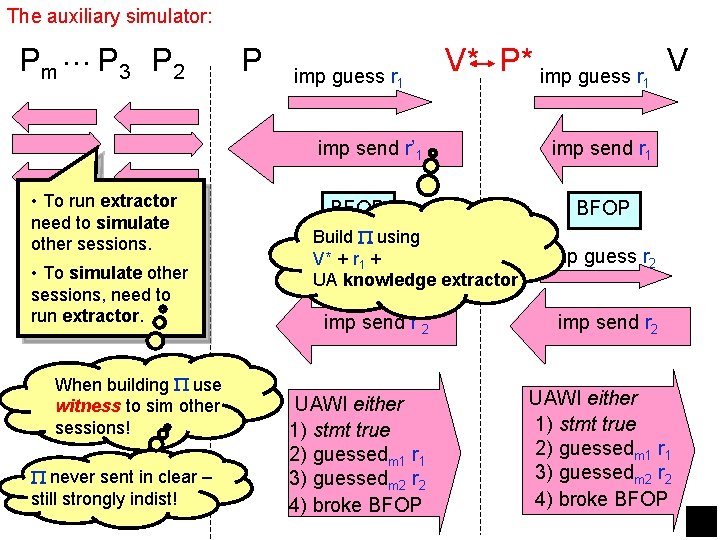
The auxiliary simulator: Pm … P 3 P 2 P imp guess r 1 V* P* imp guess r V imp send r’ 1 • To run extractor need to simulate other sessions. • To simulate other sessions, need to run extractor. When building use witness to sim other sessions! never sent in clear – still strongly indist! BFOP Build using imp V* +guess r 1 + r’ 2 UA knowledge extractor imp send r’ 2 UAWI either 1) stmt true 2) guessedm 1 r 1 3) guessedm 2 r 2 4) broke BFOP 1 imp send r 1 BFOP imp guess r 2 imp send r 2 UAWI either 1) stmt true 2) guessedm 1 r 1 3) guessedm 2 r 2 4) broke BFOP
Questions: • Random oracle model also used to achieve non-malleability and concurrent security. Can we justify this? (so far mostly negative results [Canetti. Goldreich. Halevi 98], [Goldwasser. Ta 03] ) • All these universal args. Are there different non-BB techniques? • Is there ZK system w/ O(1)-rounds and public coin verifier? Related to both these questions. • Are these non-BB techniques inherently unpractical? Two problematic components: general ZK and PCP theorem. On other hand: PCP get simpler, more efficient [Ben. Sasson. Sudan 05], [Dinur 05] Maybe can push complexity to simulation? [B. Sahai 05] • Handling quantum adversaries?
P 1 P 2 V* Use random r 1 of length k 1 Stmt: x 2 {0, 1}n id 2[t] h z 1=Com(h(M 1)) UACom(r 1) Use M 1 = V* program + r 1 + extractor for UA BFOP To rewind, M 1 uses witness! z 2=Com(h(M 1)) UACom(r 2) Rules of engagement: Simulate execution s. t. : 1) Never use option #1 in UAWI 2) No use of time between dotted lines. UAWI either 1) x is true. 2) 9 |t 1|<k 1 -n s. t. M 1(z 1, t 1)=r 1 3) 9 |t 2|<k 2 -n s. t. M 2(z 2, t 2)=r 2 4) Broke BFOP. 2) No use of ver. coins after green line. k 1 = nlognid , k 2 = nlogn(t-id) V
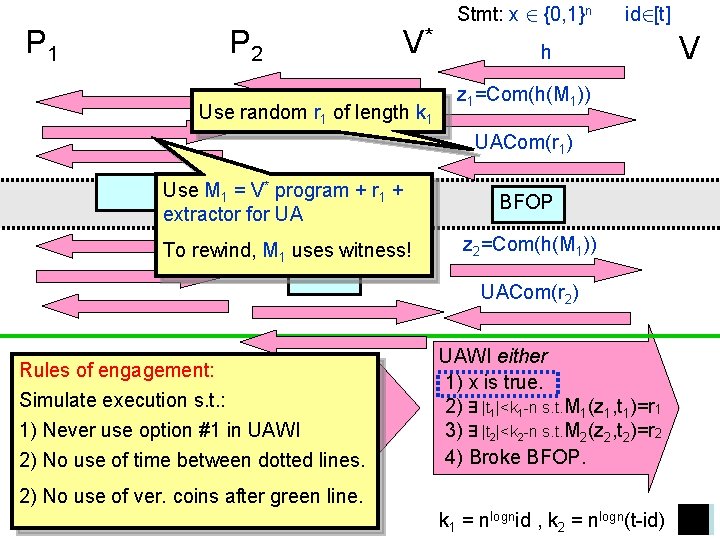
P 1 P 2 V* Use random r 1 of length k 1 Stmt: x 2 {0, 1}n id 2[t] h z 1=Com(h(M 1)) UACom(r 1) Use M 1 = V* program + r 1 + extractor for UA BFOP To rewind, M 1 uses witness! z 2=Com(h(M 1)) UACom(r 2) Rules of engagement: Simulate execution s. t. : 1) Never use option #1 in UAWI 2) No use of time between dotted lines. UAWI either 1) x is true. 2) 9 |t 1|<k 1 -n s. t. M 1(z 1, t 1)=r 1 3) 9 |t 2|<k 2 -n s. t. M 2(z 2, t 2)=r 2 4) Broke BFOP. 2) No use of ver. coins after green line. k 1 = nlognid , k 2 = nlogn(t-id) V
- Slides: 35