Offensive IW Open Sources Reading List Open Source

- Slides: 34
Offensive IW Open Sources
Reading List – Open Source Intelligence: Private Sector Capabilities to Support Do. D Policy, Acquisitions, and Operations , http: //www. fas. org/irp/eprint/oss 980501. htm l Interesting Read – INTellingence: Open Source Intelligence, CIA, https: //www. cia. gov/news-information/featured-storyarchive/2010 -featured-story-archive/open-sourceintelligence. html – Project Grey Goose Report on Critical Infrastructure, 2010, http: //dataclonelabs. com/security_talkworkshop/papers/255 50091 -Proj-Grey-Goose-report-on-Critical-Infrastructure. Attacks-Actors-and-Emerging-Threats. pdf CSCE 727 - Farkas 2
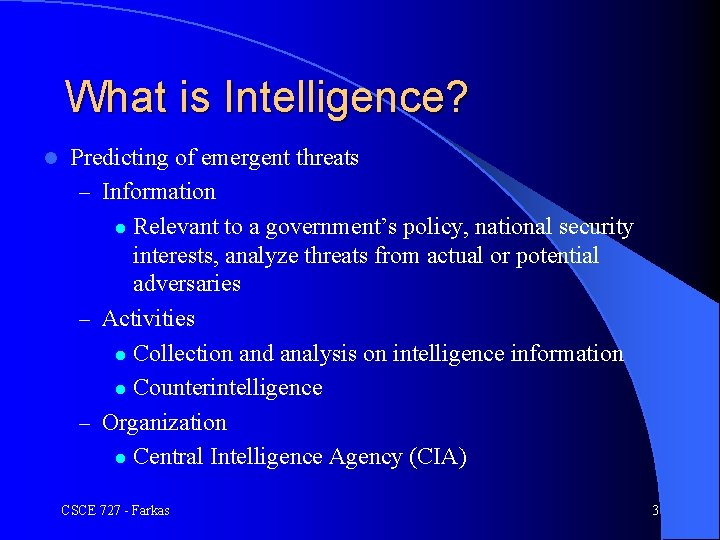
What is Intelligence? l Predicting of emergent threats – Information l Relevant to a government’s policy, national security interests, analyze threats from actual or potential adversaries – Activities l Collection and analysis on intelligence information l Counterintelligence – Organization l Central Intelligence Agency (CIA) CSCE 727 - Farkas 3
Modern Intelligence? James Bond Cyber Intelligence Mata Hari CSCE 727 - Farkas 4
Source of Threats l Physical attacks – Use of IT technology to predict traditional threats – OSINT l Cyber attacks – Use of IT technology to predict cyber threats – Need: understanding of these threats and their consequences on national security CSCE 727 - Farkas 5
Information “…relevant to a government’s formulation and implementation of policy to further its national security interests and to deal with threats from actual or potential adversaries. ” (A. Shulsky and G. Schmitt, Silent Warfare) l Examples: – Military matters of foreign nations – Diplomatic activities and intentions of foreign nations – Intelligence activities of foreign nations l Other party may or may not want to keep it secret l Raw data and analyses and assessments based on raw data l CSCE 727 - Farkas 6
Technical Intelligence Interesting read: Office of Scientific Intelligence: The Original Wizards of Langley, http: //www. foia. cia. gov/collection/original-wizardslangley l Office of Scientific Intelligence – Track technical challenges – Originates back to 1954 -1962 – Aim: create and apply innovative technologies to meet intelligence needs l CSCE 727 - Farkas 7
Open Source l Unclassified information in the public domain or available from commercial services l Example sources: – Traditional: newspapers, magazines, scientific publications, television and radio broadcasting, etc. – Emerging: Internet, geospatial data, images CSCE 727 - Farkas 8
Birth of Open Source Intelligence l 1946: Central Intelligence Group (CIG) established – Track scientific development abroad and estimate its importance – Consequences of foreign scientific development on US national security – Issues: Soviet nuclear weapons, ballistic missile, space exploration, air defense, chemical and biological weapons, etc. CSCE 727 - Farkas 9
Open Source Concerns l Acquisition of information – Open source intelligence – Privacy l Legal and ethical issues – Piracy – Infringement on intellectual property rights – Fraud CSCE 727 - Farkas 10
What kind of information resources do YOU use? How do YOU evaluate the accuracy of the data? How do YOU analyze the collected data? CSCE 727 - Farkas 11
Advances in IT l Increased: data and analysts l Raw data sharing – Intelligence community – Government offices – Interest groups CSCE 727 - Farkas 12
Activity Obtaining or denying information l Activities: l – Collection and analysis on intelligence information – Counterintelligence, deception Collection: wide range (e. g. , wiretapping, broadcasts, newspapers, research publications, aerial photography, espionage, etc. ) l Analysis: quality of data, correctness of analysis, timeliness, etc. l CSCE 727 - Farkas 13
What are the OSI Challenges? l Collection? – Data accuracy (correctness, timeliness, etc. ) – Data integration (heterogeneous data, duplicate, inconsistent data) – Volume of data (processing capability) l Analysis? – Statistical data analysis – Accuracy of results, application of results – Efficiency CSCE 727 - Farkas 14
Counterintelligence l Covert action l Protect a nation against the actions of hostile intelligence services – National Security – Nature of regime – Law CSCE 727 - Farkas 15
Counterintelligence l Passive measures – Blocking access to the information – Information classification: l l l Top Secret: “exceptionally grave damage” Secret: “serious damage” Confidential: “damage” l Counter espionage – Surveillance, intelligence collections – Defectors and double agents – Deception CSCE 727 - Farkas 16
Counterintelligence l Foreign intelligence guidelines: classified – Investigation of: Illegal activities: detecting and preventing foreign espionage and terrorist activities l Legal activities: foreign legal political activities like fund-raising, organizational work, etc. l l Domestic intelligence guidelines (“Levi Guidelines”): public – Investigation of groups that hostile to government policies and fundamental principles l seeks to deprive some class of people l has violent approach to political change l CSCE 727 - Farkas 17
Scope of Intelligence l Government -- national security – Range from peace time to war time intelligence – Type of government l l l Domestic Intelligence -- depends on nature of regime Business corporations – competitive advantage Economics and Intelligence – Government-run economy – Economic well-being of nation (post-Cold War era) l Non-traditions Intelligence – Environmental issues CSCE 727 - Farkas 18
Intelligence and Law Enforcement l Transnational threats: – – Do not originate primarily from a foreign government Serious threats for nation’s well-being Fall within law enforcement rather than intelligence Examples: narcotics trafficking, international terrorism Law enforcement: waiting until a crime has been committed l Intelligence: collection of convincing evidence l Criminal investigation vs. criminal intelligence investigation l – Punishment of a given criminal act vs. struggle with an organization engaged in criminal activity CSCE 727 - Farkas 19
Intelligence and Information Age l l l Advent of information age Change the mode of operations for business corporations and government Technology: communicating and processing information Behavioral and institutional change: information as the key of organizational activities Intelligent Services vs. competing organizations CSCE 727 - Farkas 20
Military Affairs l Enhanced usefulness of information – Weapon systems l Enhanced ability to collect, process and disseminate information in a timely manner CSCE 727 - Farkas 21
Government Operations l Circulation and use of information for policy making and implementation – Competitiveness of non-government organizations – How to exploit information – How to integrate information from heterogeneous sources CSCE 727 - Farkas 22
Intelligence and Information Age (cont. ) l Globalization: increased flow of information across borders – International trade – Division of labor – Increased travel – Increased penetration by news media CSCE 727 - Farkas 23
Open Source Information Collection l l l Goal oriented Publications and broadcast Additional information available from nonintelligence sources Special sources (e. g. , speeches of political leaders, legal documents, demographic data, etc. ) Large amount of openly available data Need processing power CSCE 727 - Farkas 24
Problem of Increased Availability l How to locate sources? l How to evaluate source reliability? l How timely the data is? l How to analyze information and integrate with other intelligence information? l How to protect confidentiality of policy maker’s interest? CSCE 727 - Farkas 25

Information Specialist l Policy maker l Staff of policy maker l Intelligence analysts CSCE 727 - Farkas 26
IW and Open Source Intelligence Generally legal (uses readily available information) l Attacker gains access to protected information, e. g. , l – Business trade secrets – Military strategy – Personal information l Protected information: readily available in public domain, can be inferred from public data, or deduced from aggregated public data CSCE 727 - Farkas 27
Open Source Intelligence l l l Widely used (e. g. , Department of Defense) Cheap, fast, or timely Most often legal Advantages: no risk for collector, provides context, mode of information acquisition, cover for data discovery by secret operations Disadvantages: may not discover important information, assurance of discovery(? ) CSCE 727 - Farkas 28
Online Open Source Intelligence l Large amount of public data online – Web pages, online databases, digital collections, organizations on line, government offices, etc. l Freedom and Information Act (FOIA): industry data l U. S. Patent Office: copies of U. S. patents l Trade shows, public records, etc. CSCE 727 - Farkas 29
Privacy l Use open source to find out confidential data about people l Find confidential data about people while they browse through open source (e. g. , Web searches) CSCE 727 - Farkas 30
Who is Selling Your Personal Data? Online investigative industry l Cash strapped government – Maryland DMV: 1996 – driver’s license info and vehicle registration data – Virginia: voter registration data – Washington State: 1997 WATCH (criminal history data) l Accidental: – Experian Inc. 08/13/1997, software error in web application released other customers’ credit standing, http: //www. highbeam. com/doc/1 P 2 -738117. html l CSCE 727 - Farkas 31
Privacy Violations l Snooping via Open Sources l Online activities – Questionnaires – Customers’ data – Web site data collection (Cookies, IP address, operating system, browser, requested page, time of request, etc. ) – without user’s permission CSCE 727 - Farkas 32
Legislations Privacy Act of 1974, U. S. Department of Justice (http: //www. justice. gov/opcl/1974 privacyact-overview. htm ) l Family Educational Rights and Privacy Act (FERPA), U. S. Department of Education, (http: //www. ed. gov/policy/gen/guid/fpco/ferpa/index. html ) l Health Information Privacy, Health Insurance Portability and Accountability Act of 1996 (HIPAA), (http: //www. hhs. gov/ocr/privacy/index. html ) l CSCE 727 - Farkas 33
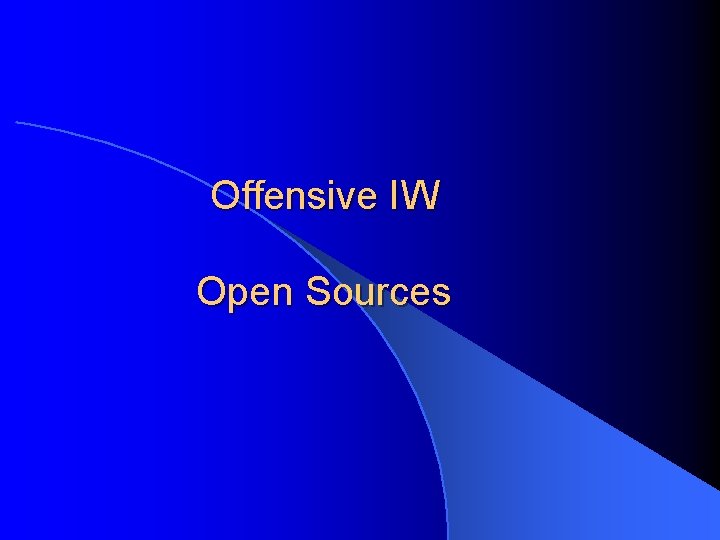
Other Open Source Attacks Piracy – Available in open source, but still protected by copyright, patent, trademark, etc. l Copyright Infringement – Acquisition of protected work without the owner’s permission and sold for a fee – Human perception: not serious crime – Significant loss for marketing/manufacturing/owner l Trademark Infringement l CSCE 727 - Farkas 34