ObjectOriented Enterprise Application Development Introduction to the Internet
Object-Oriented Enterprise Application Development Introduction to the Internet
Topics During this class we will examine: A Brief History of the Internet N-Tier Architectures HTTP Protocol and the Request-Response Model Required Technology for the Course
An Introduction to the Internet (1 of 12) Like all other technology the Internet has evolved over time. The following slides show an abbreviated timeline of the Internet's evolution.
An Introduction to the Internet (2 of 12) 1957 The USSR launches Sputnik. The US response is to form Advanced Research Projects Agency (ARPA) within the Department of Defense (Do. D). 1961 Leonard Kleinrock of MIT produces the first paper on packet switching theory.
An Introduction to the Internet (3 of 12) 1964 Paul Baran of RAND produces paper on packet switching networks. 1969 ARPANET commissioned by the Do. D. 1971 Ray Tomlinson develops the first email program.
An Introduction to the Internet (4 of 12) 1972 Ray Tomlinson modifies the email program for ARPANET. RFC 318 for Telnet. 1973 Bob Metcalfe proposes Ethernet. RFC 454 for FTP. ARPA study shows that email is 75% of the traffic over ARPANET.
An Introduction to the Internet (5 of 12) 1975 First ARPANET mailing list created by Steve Walker. 1977 RFC 733 for mail. 1978 TCP split into TCP and IP.
An Introduction to the Internet (6 of 12) 1979 USENET established. Kevin Mac. Kenzie proposes the use of smileys. 1977 RFC 733 for mail. 1980 First virus infects ARPANET. It was accidental.
An Introduction to the Internet (7 of 12) 1983 University of Wisconsin produces the first name server. 1984 DNS is introduced. Number of hosts breaks 1, 000. Moderated USENET groups introduced.
An Introduction to the Internet (8 of 12) 1985 Symbolics. com becomes the first registered domain. 100 years to the day of the last spike being driven on the cross-Canada railroad, the last Canadian university is connected to Net. North in a one-year effort to have coastto-coast connectivity.
An Introduction to the Internet (9 of 12) 1986 Number of hosts breaks 10, 000. 1987 Internet worm released. CERT formed. Do. D adopts the OSI model. Internet Relay Chat (IRC) developed by Jarkko Oikarinen
An Introduction to the Internet (10 of 12) 1989 Number of hosts breaks 100, 000. 1990 ARPANET ceases to exist. World. std. com becomes the first provider of dial-up Internet access.
An Introduction to the Internet (11 of 12) 1991 WWW released by CERN (Tim Berners-Lee). PGP released by Phillip Zimmerman. 1993 INTERNIC formed. Mosaic introduced.
An Introduction to the Internet (12 of 12) 1994 First on-line shopping malls and banks appear. 1995 Sun launches Java. Netscape goes public. 1998 ICANN (Internet Corporation for Assigned Names and Numbers) formed.
Architectures
N-Tier Architectures Technical architectures have evolved to handle the increasingly complex requirements of the applications that they support. These architectures are loosely described in terms of tier. The degree of tier governs the overall structure of the architecture as well as its inherent properties and limitations.
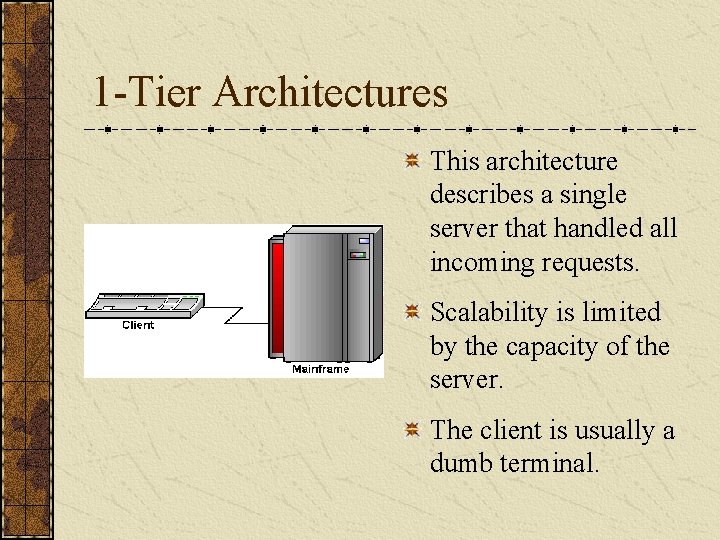
1 -Tier Architectures This architecture describes a single server that handled all incoming requests. Scalability is limited by the capacity of the server. The client is usually a dumb terminal.
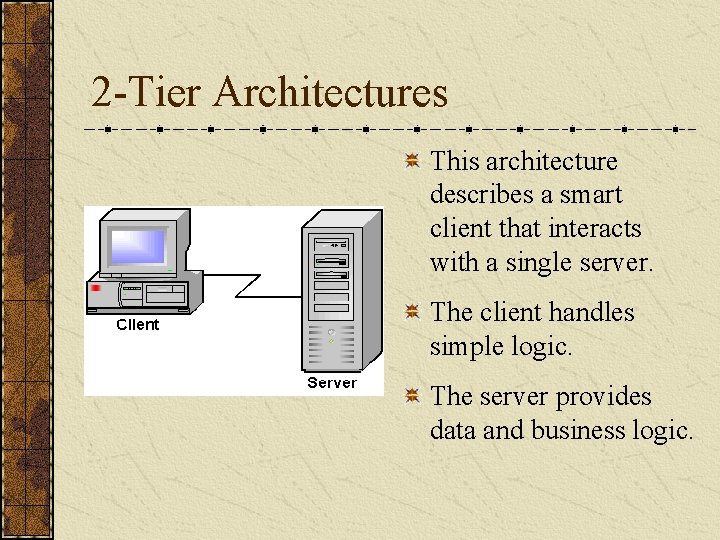
2 -Tier Architectures This architecture describes a smart client that interacts with a single server. The client handles simple logic. The server provides data and business logic.
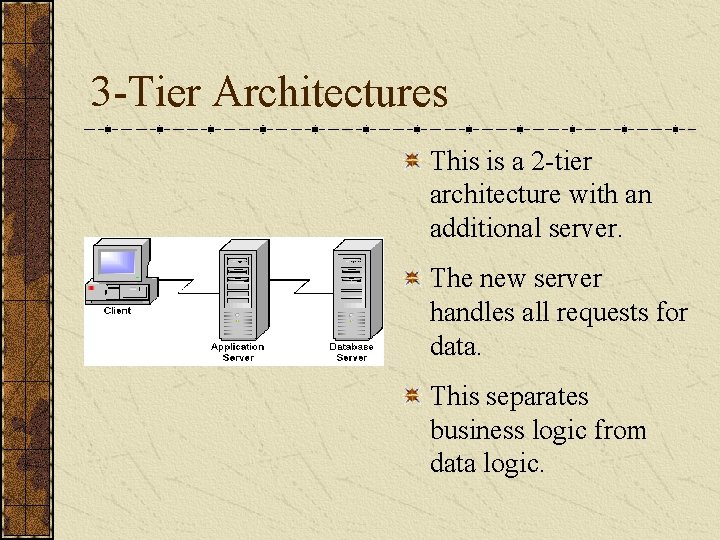
3 -Tier Architectures This is a 2 -tier architecture with an additional server. The new server handles all requests for data. This separates business logic from data logic.
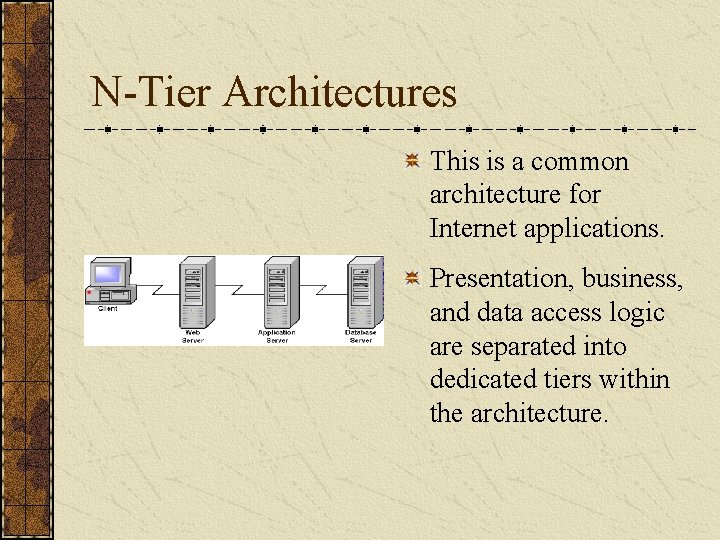
N-Tier Architectures This is a common architecture for Internet applications. Presentation, business, and data access logic are separated into dedicated tiers within the architecture.
Standard Hardware & Software Configurations
Standard Hardware & Software Modern e-commerce applications involve a staggering array of specialized hardware and software. For this course we'll only be concerned with three (3) specific technologies: Web Servers Application Servers Database Servers
Web Servers Web servers deliver presentation content to a client. As a general rule, the web server is the only part of an e-commerce application with which a client interacts. Its fundamental role is to act as the application's server-side presentation layer.
Application Servers Application servers are used to hold an application's business logic. Clients rarely communicate with an application server directly; the client communicates with a web server which sends the request to the application server.
Database Servers Database servers hold an application's data logic. It is usually only the application server that communicates with the database server. This maintains the separation between the application's business and data logic.
Architecture Capabilities
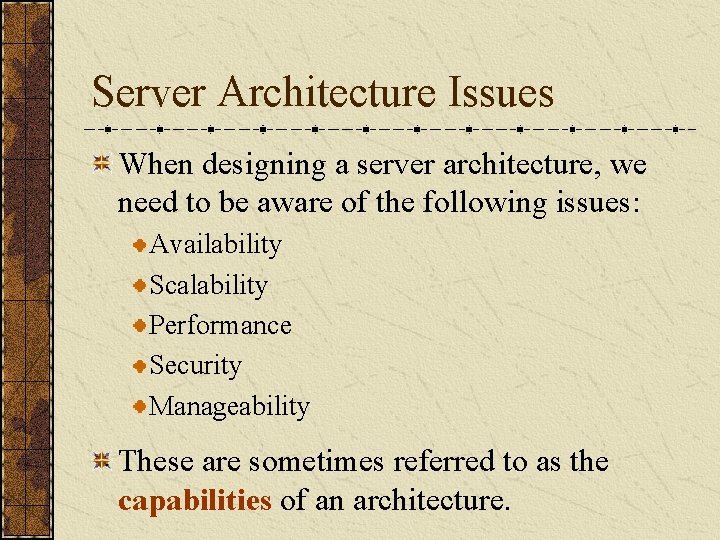
Server Architecture Issues When designing a server architecture, we need to be aware of the following issues: Availability Scalability Performance Security Manageability These are sometimes referred to as the capabilities of an architecture.
Availability is concerned with keeping a system operational despite hardware or software problems. This is sometimes called fault tolerance. One key approach to ensure availability is redundancy.
Scalability is a measure of how easily an architecture can handle increased loads or be installed on higher-capacity hardware. We generally want our architectures to be upwardly scalable.
Performance can have many metrics depending on the aspects of the architecture that we deem to be important. Some critical measures include: Response time Throughput These performance metrics often require us to split servers across physical devices.
Security The goal of security is to ensure that the only information that a user sees is the information that they are supposed to see. This is common for e-commerce sites involving the exchange of sensitive information such as credit card numbers or personal data.
Manageability is concerned with the effort required to make changes to the architecture such as installations or configuration alterations. Once we get into multi-tiered architectures, this capability can quickly become a significant burden on an application support group.
Cost is the strongest force in the ecommerce realm. All of our architectural decisions must be put through a reasonable cost-benefit analysis. We must be able to convince management that the cost of an architectural feature will be justified by the benefits of that feature.
HTTP
Hyper. Text Transfer Protocol Many modern N-tier architectures are designed as Internet applications. The underlying network protocol of the Internet is TCP/IP. Internet applications make use of the Hyper. Text Transfer Protocol, or HTTP, to provide communications between clients and servers.
HTTP Versions In 1997 most servers and browsers communicated using HTTP 1. 0 The current version is HTTP 1. 1. The HTTP specification is administered by the World Wide Web Consortium (W 3 C). http: //www. w 3. org/Protocols/
Request-Response Model When working with HTTP, a requestresponse model is used: The client opens a connection to a server, The client requests some resource from the server. The server sends a response containing the requested resource back to the client. The client and server close their connections.
HTTP Request Conceptually a request is just that: a request for a specified resource from a target server on a given port. An HTTP request has the following format: Request-method URI and HTTP version Optional request headers A blank line Optional data (POST method only)
HTTP Request - Sample Suppose I issue a request for the following URL: http: //www. depaul. edu/~cjones/ index. html The HTTP request would appear as: GET /~cjones/index. html HTTP/1. 0
HTTP Request Methods There are three (3) key request methods: GET: Data sent to the server goes on the URI as arguments. POST: The same as GET but data sent to the server goes on a separate line. This provides basic security. HEAD: As GET but the server only provides the response headers and not the actual content.
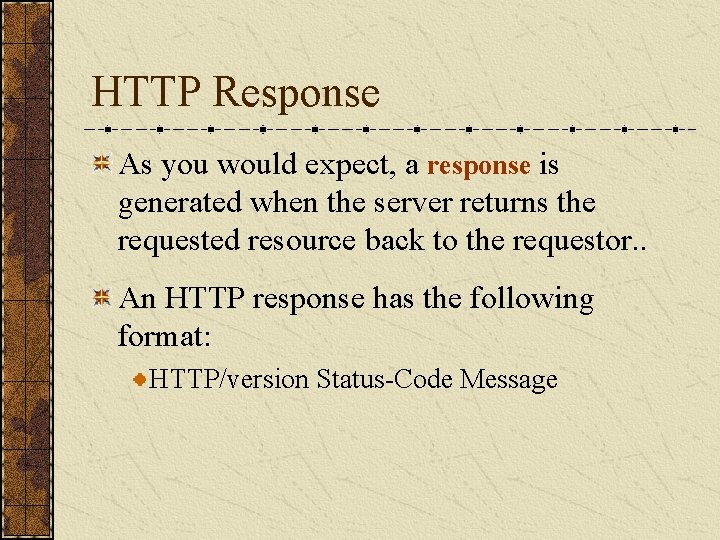
HTTP Response As you would expect, a response is generated when the server returns the requested resource back to the requestor. . An HTTP response has the following format: HTTP/version Status-Code Message
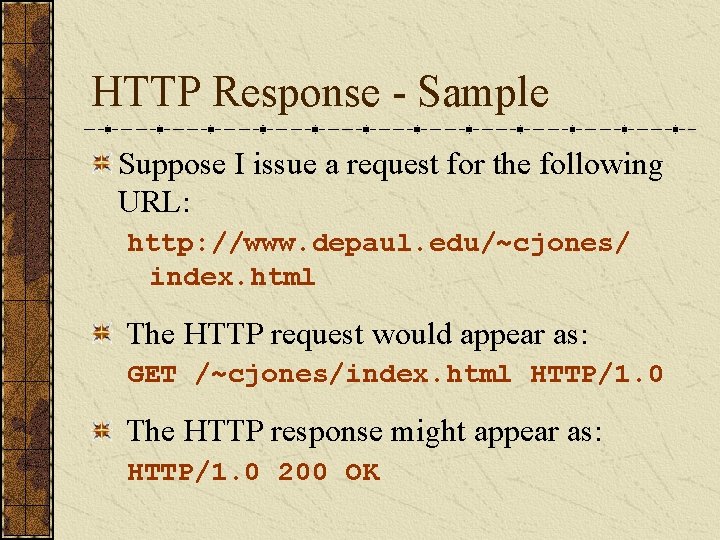
HTTP Response - Sample Suppose I issue a request for the following URL: http: //www. depaul. edu/~cjones/ index. html The HTTP request would appear as: GET /~cjones/index. html HTTP/1. 0 The HTTP response might appear as: HTTP/1. 0 200 OK
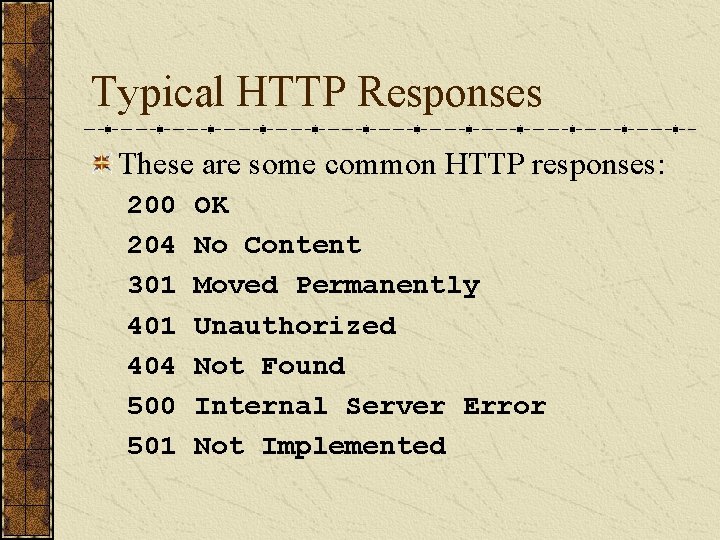
Typical HTTP Responses These are some common HTTP responses: 200 204 301 404 500 501 OK No Content Moved Permanently Unauthorized Not Found Internal Server Error Not Implemented
Consequences The request-response model results in sideeffects that change how we write software to function layered on top of HTTP. Because each request is independent from every other request, HTTP is considered a stateless protocol. We'll address this issue later in the course.
Required Technology
Hardware In order for this course to function, you'll need a computer. It can be a laptop or desktop. You should be able to install software on it. You're better off using your own hardware if possible. I'll try to have some university machines configured with the software if necessary.
Hardware Configuration I don't care what platform you use but it needs to be compatible with: Intel Pentium Processor Microsoft Windows NT 4. 0 or Windows 2 K I don't provide hardware support. If you need this kind of support, start cracking open the manuals.
Software This class requires the following software components: Relational database Web server Application server Web browser
Software Configuration I'm standardizing the software configuration: Microsoft Access or Cloudscape 3. 6 (database) Tomcat 3. 2 (web & application server) MSIE or Netscape (web browser)
Java This class requires extensive use of Java. Based on your operating system you have two (2) choices: Windows 95/98: Install Java 1. 3 Standard Edition and then install the JSDK (Java Servlet Development Kit) on top of it. Windows NT/2 K: Install Java 1. 2. 2 Enterprise Edition. You can also use the Windows 95/98 installation instructions.
Review During this class we've discussed: A Brief History of the Internet N-Tier Architectures HTTP Protocol and the Request-Response Model Required Technology for the Course
Resources Hobbes' Internet Timeline Robert H. Zakon, 1993 -2000. Core Web Programming Hall, M. Core Books. 1998, Upper Saddle River, NJ: Prentice-Hall, Inc. 1279. ISBN: 0 -13 -625666 -X
Coming Attractions Next week we will begin using the JDBC API. We'll look at the mechanics around setting up and accessing a JDBC compliant database. We'll discuss transaction control and the proper closing and de-allocation of JDBC resources. Please read chapter 18 in your text.
Coming Attractions Next week we will begin using the JDBC API. We'll look at the mechanics around setting up and accessing a JDBC compliant database. We'll demonstrate how to manipulate the database using JDBC. We'll discuss transaction control and the proper closing and de-allocation of JDBC resources.
- Slides: 54