NWC 604 COM Ubiquitous Computing Week 2 Assignment
NWC 604 COM Ubiquitous Computing Week 2 – Assignment 1 Task 1 Theory
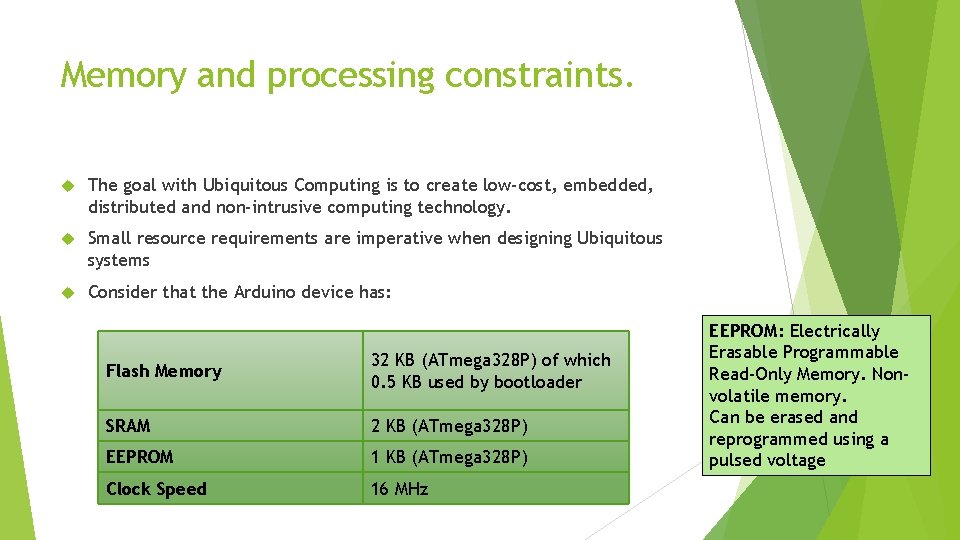
Memory and processing constraints. The goal with Ubiquitous Computing is to create low-cost, embedded, distributed and non-intrusive computing technology. Small resource requirements are imperative when designing Ubiquitous systems Consider that the Arduino device has: Flash Memory 32 KB (ATmega 328 P) of which 0. 5 KB used by bootloader SRAM 2 KB (ATmega 328 P) EEPROM 1 KB (ATmega 328 P) Clock Speed 16 MHz EEPROM: Electrically Erasable Programmable Read-Only Memory. Nonvolatile memory. Can be erased and reprogrammed using a pulsed voltage
Other constraints Range and bandwidth: Mobile Internet access is generally slower than direct cable connections. Technologies include: GPRS and EDGE, HSDPA, HSUPA, 3 G and 4 G networks and upcoming 5 G network. Available within range of commercial mobile phone towers. High speed network wireless LANs are inexpensive but have very limited range. Security standards: When working mobile, you become dependent on public networks, requiring careful use of VPN for sensitive data. Security is a major concern with mobile computing standards. Attacks could take place throughto the VPN through a huge number of networks interconnected through the line. Power consumption: When no power outlet or portable generator is available, mobile computing rely entirely on battery power. With the compact size of many mobile devices, this means expensive batteries must be used to obtain the needed battery life.
Other constraints Transmission interferences: Weather, terrain, and the range from the nearest signal point can all interfere with signal reception. Reception in tunnels, some buildings, and rural areas is often poor. Potential health hazards: People who use mobile devices while driving are often distracted from driving and are thus assumed more likely to be involved in traffic accidents. Mobile phones may interfere with sensitive medical devices. Questions concerning mobile phone radiation and health have been raised. Human interface with device: Screens and keyboards tend to be small, which may make them hard to use. Alternate input methods such as speech or handwriting recognition require training.
Mobile computing applications. What are the applications of portable mobile computing devices: Could include compact, lightweight units including a full character set keyboard and primarily intended as hosts for software that may be parameterized, such as laptops/desktops, smartphones/tablets, etc. Smart cards that can run multiple applications but typically payment, travel and secure area access. Mobile phone devices which can call from a distance through cellular networking technology. Wearable computers, mostly limited to functional keys and primarily intended as incorporation of software agents, such as bracelets, keyless implants, etc. And many, many more.
Mobility and persistence. Always available, always on. Maintains user data. Should be transparent to application developer Data is stored on persistent storage(Non-volatile) before de-activation and loaded up on activation from persistent storage. Persistent storage can be: File systems Relational Database Object-Database Flash-RAM
Overview of ad-hoc wireless networking. A network that is composed of individual devices communicating with each other directly. A spontaneous or impromptu construction because these networks often bypass the gatekeeping hardware or central access point such as a router. For file and printer sharing, all users need to be in the same workgroup, or if one computer is joined to a domain, the other users have to have accounts on that computer in order to access shared items. Other limitations of ad hoc wireless networking include the lack of security and a slow data rate. Ad hoc mode offers minimal security. If an attacker comes within range of your ad hoc network, he won't have any trouble connecting.
Locationing Wi-Fi positioning system (WPS) or Wi. PS/WFPS is used where GPS are inadequate due to various causes including multipath and signal blockage indoors. Such systems include indoor positioning systems. The most common and widespread localisation technique used for positioning with wireless access points is based on measuring the intensity of the received signal known as received signal strength indication( RSSI. Typical parameters useful to geolocate the Wi-Fi hotspot or wireless access point include the SSID and the MAC address of the access point. Accuracy depends on the number of positions that have been entered into the database. The Wi-Fi hotspot database gets filled by correlating mobile device GPS location data with Wi-Fi hotspot MAC addresses. The possible signal fluctuations that may occur can increase errors and inaccuracies in the path of the user. To minimize fluctuations in the received signal, there are certain techniques that can be applied to filter the noise.
Routing is the process of selecting a path for traffic in a network, or between or across multiple networks. In packet switching networks, routing is the higher-level decision making that directs network packets from their source toward their destination through intermediate network nodes by specific packet forwarding mechanisms. Packet forwarding is the transit of logically addressed network packets from one network interface to another. Intermediate nodes are typically network hardware devices such as routers, bridges, gateways, firewalls, or switches. Routing has become the dominant form of addressing on the Internet.
Network Organisation. Set-up an Io. T gateway – Manage Io. T devices and sensors that come on to the network. Translate each “thing’s” protocols, and forward each unique piece of Io. T data to its most appropriate destination. Ensure network capacity and adequate bandwidth Get the network ready to analyse big data - Servers ready with the processing power and capacity necessary for data analysis, and make sure servers are fit for the environments where Io. T lives. Get the network ready to store big data Upgrade to IPv 6 to support the many new devices – IPv 6 provides greater numbers of IP Addresses Secure the network appropriately for Io. T - Risk analyses, device and protocol audits, as well as Io. T policies and policy enforcement. Set-up network monitoring in support of Io. T - Plan ahead for adaptable, scalable network monitoring that encompasses the variables you must account for with Io. T.
Other elements of Assignment 1 Task 1 Current and future applications for interactive pervasive devices and systems and some case studies. Research and discuss your findings. Software environments for mobile and ubiquitous systems development. Such as: Arduino IDE Raspian Open. SCADA Platform. IO Eclipse Io. T Project (Kura)
- Slides: 11