November 2006 doc IEEE 802 11 061867 r
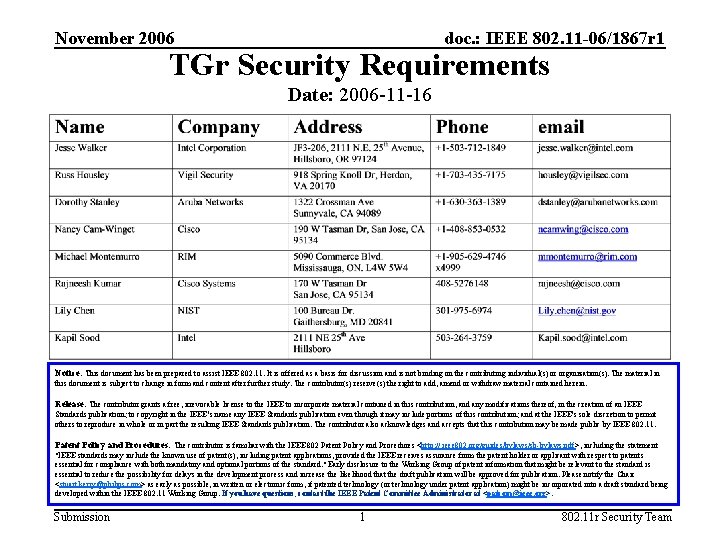
November 2006 doc. : IEEE 802. 11 -06/1867 r 1 TGr Security Requirements Date: 2006 -11 -16 Notice: This document has been prepared to assist IEEE 802. 11. It is offered as a basis for discussion and is not binding on the contributing individual(s) or organization(s). The material in this document is subject to change in form and content after further study. The contributor(s) reserve(s) the right to add, amend or withdraw material contained herein. Release: The contributor grants a free, irrevocable license to the IEEE to incorporate material contained in this contribution, and any modifications thereof, in the creation of an IEEE Standards publication; to copyright in the IEEE’s name any IEEE Standards publication even though it may include portions of this contribution; and at the IEEE’s sole discretion to permit others to reproduce in whole or in part the resulting IEEE Standards publication. The contributor also acknowledges and accepts that this contribution may be made public by IEEE 802. 11. Patent Policy and Procedures: The contributor is familiar with the IEEE 802 Patent Policy and Procedures <http: // ieee 802. org/guides/bylaws/sb-bylaws. pdf>, including the statement "IEEE standards may include the known use of patent(s), including patent applications, provided the IEEE receives assurance from the patent holder or applicant with respect to patents essential for compliance with both mandatory and optional portions of the standard. " Early disclosure to the Working Group of patent information that might be relevant to the standard is essential to reduce the possibility for delays in the development process and increase the likelihood that the draft publication will be approved for publication. Please notify the Chair <stuart. kerry@philips. com> as early as possible, in written or electronic form, if patented technology (or technology under patent application) might be incorporated into a draft standard being developed within the IEEE 802. 11 Working Group. If you have questions, contact the IEEE Patent Committee Administrator at <patcom@ieee. org>. Submission 1 802. 11 r Security Team
November 2006 doc. : IEEE 802. 11 -06/1867 r 1 Abstract This submission summarizes security requirements for TGr. Please consider these requirements during the upcoming letter ballot. Submission 2 802. 11 r Security Team
November 2006 doc. : IEEE 802. 11 -06/1867 r 1 R 0 and R 1 Keys • R 0 Key – Known only to AAA Server, STA, and R 0 KH – Each party knows what other parties have R 0 Key – AAA Server and STA must have a common understanding of the R 0 KH identity • R 1 Key – Known only to R 0 KH, STA, and appropriate R 1 KH – Each party knows what other parties have R 1 Key – Accept that AAA Server can compute R 1 Key if it learns the public information that is used to derive the R 1 Key – that is, we have to trust the AAA Server – Trust the R 0 KH to distribute the R 1 Key to the appropriate R 1 KH, and no other party • The STA and the R 0 KH must have a common understanding of each R 1 KH identity – Accept that the solution may be outside TGr, but the requirements ought to be specified by TGr Submission 3 802. 11 r Security Team
November 2006 doc. : IEEE 802. 11 -06/1867 r 1 PMK-R 1 Derivation • STA can distinguish – Correct PMK sharing among thin APs managed by the same controller, and – Sharing a PMK among compromised fat APs Submission 4 802. 11 r Security Team
November 2006 doc. : IEEE 802. 11 -06/1867 r 1 R 0 Key Transition • Initial Association creates a different R 0 Key, perhaps at different R 0 KHs – Can each R 0 Key (and the hierarchy under it) be distinguished? – Do all parties know when the key hierarchy can be discarded? Submission 5 802. 11 r Security Team
November 2006 doc. : IEEE 802. 11 -06/1867 r 1 Security Services in Key Management Protocols Key management provides • Confidentiality • Integrity • Replay protection • Key binding to the appropriate context and scope • Authentication of parties that communicate with each other • Authorization – AAA Server authorizes STA and R 0 KH for the mobility domain security association – R 0 KH authorizes the R 1 KH for their associations with the mobility domain Submission 6 802. 11 r Security Team
- Slides: 6