November 2005 doc IEEE 802 22 050105 r
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 A Cognitive PHY/MAC Proposal for IEEE 802. 22 WRAN Systems Authors: IEEE P 802. 22 Wireless RANs Date: 2005 -11 -07 Notice: This document has been prepared to assist IEEE 802. 22. It is offered as a basis for discussion and is not binding on the contributing individual(s) or organization(s). The material in this document is subject to change in form and content after further study. The contributor(s) reserve(s) the right to add, amend or withdraw material contained herein. Release: The contributor grants a free, irrevocable license to the IEEE to incorporate material contained in this contribution, and any modifications thereof, in the creation of an IEEE Standards publication; to copyright in the IEEE’s name any IEEE Standards publication even though it may include portions of this contribution; and at the IEEE’s sole discretion to permit others to reproduce in whole or in part the resulting IEEE Standards publication. The contributor also acknowledges and accepts that this contribution may be made public by IEEE 802. 22. Patent Policy and Procedures: The contributor is familiar with the IEEE 802 Patent Policy and Procedures http: //standards. ieee. org/guides/bylaws/sb-bylaws. pdf including the statement "IEEE standards may include the known use of patent(s), including patent applications, provided the IEEE receives assurance from the patent holder or applicant with respect to patents essential for compliance with both mandatory and optional portions of the standard. " Early disclosure to the Working Group of patent information that might be relevant to the standard is essential to reduce the possibility for delays in the development process and increase the likelihood that the draft publication will be approved for publication. Please notify the Chair Carl R. Stevenson as early as possible, in written or electronic form, if patented technology (or technology under patent application) might be incorporated into a draft standard being developed within the IEEE 802. 22 Working Group. If you have questions, contact the IEEE Patent Committee Administrator at patcom@iee. org. Submission 1 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 PHY Abstract Digital modulation systems presently make use of two basic modulation technologies: single carrier and multi-carrier. Their features are well-known since they have been deployed for several years around the world for broadcasting applications. Wireless access applications differ from broadcasting since they require : flexibility on the downstream link : variable number of user, variable throughput per user, variable level of protection, etc; multiple access on the upstream link. Single carrier modulation can tackle these objectives through time multiplexing techniques. Multi-carrier modulation is however more flexible since it enables to control the signal in both time and frequency domains. This gives the opportunity to define two dimensional (time and frequency) slots and to map the services to be transmitted in both directions onto a subset of these slots. Two types of multi-carrier modulation has been retained in IEEE 802. 16 (Wi. MAX) standard: OFDM in the fixed MAN version and OFDMA in the mobile version. In the continuity of IEEE 802. 16, it is proposed here to consider OFDMA modulation for downstream and upstream links with two technological improvements: • Spreading; • OQAM waveforming. To meet the tight link budget requirements of WRAN, duo binary turbo code is proposed for service ranges up to 100 Km Submission 2 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 MAC Abstract We propose the Cognitive MAC (CMAC) layer to be used as the basis for the future IEEE 802. 22 WRAN standard operating in the TV bands. The proposed CMAC is in some respects inspired by the IEEE 802. 16 standard, but it provides major extensions, improvements and also simplifications in order to meet the 802. 22 functional requirements. CMAC is based on a superframe architecture which is general enough to allow multiple wireless systems to coexist in addition to support the flexibility to group multiple vacant TV channels and hence achieve greater capacity. To coexist with incumbent services, CMAC is able to efficiently manage distributed incumbent measurement, control, and recovery procedures, while also providing the necessary spectrum management features. To coexist amongst 802. 22 systems, CMAC is the first of its kind to implement a novel coexistence beacon protocol (CBP) that allows BSs with overlapping coverage areas to coordinate and efficiently share the radio spectrum, hence minimizing interference. The efficiency of CBP is further improved by a new scheme that dynamically synchronizes overlapping BSs. Additional characteristics of CMAC include the support of various traffic types with different Qo. S requirements, flexible bandwidth management, and a combination of access mechanisms. Submission 3 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction – A Glimpse of IEEE 802. 22 • The Cognitive PHY Proposal • The Cognitive MAC Proposal • Conclusions Submission 4 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction – A Glimpse of IEEE 802. 22 • The Cognitive PHY Proposal • The Cognitive MAC Proposal • Conclusions Submission 5 Carlos Cordeiro, Philips
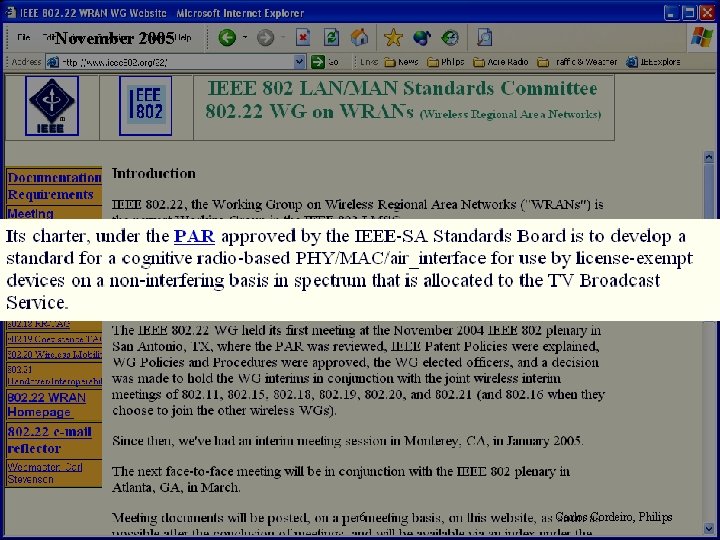
November 2005 Submission doc. : IEEE 802. 22 -05/0105 r 0 6 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 The IEEE 802. 22 • From 18 Mbps to 24 Mbps • Propagation delays in excess of 300 µs • Operates in TV bands – 54 to 862 MHz – 6 MHz, 7 MHz and 8 MHz channel bandwidth Submission 7 Carlos Cordeiro, Philips
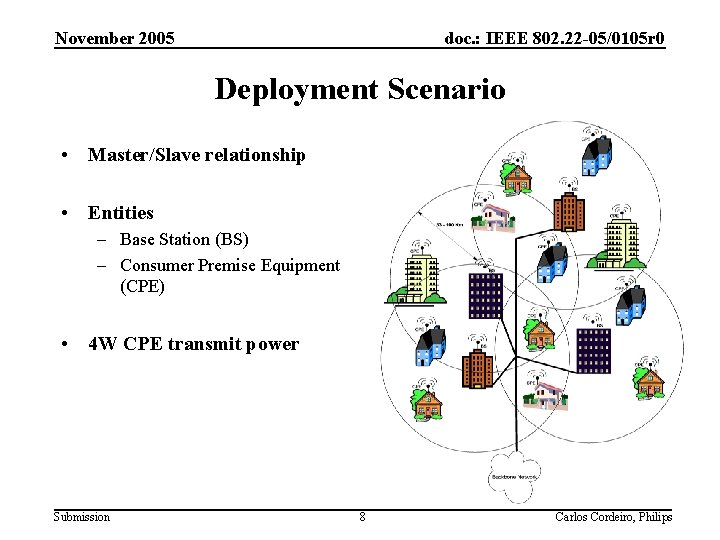
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Deployment Scenario • Master/Slave relationship • Entities – Base Station (BS) – Consumer Premise Equipment (CPE) • 4 W CPE transmit power Submission 8 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction – A Glimpse of IEEE 802. 22 • The Cognitive PHY Proposal • The Cognitive MAC Proposal • Conclusions Submission 9 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 PHY Presentation Outline • • Background Top-level description of modulation/coding Channel bonding Modulation Parameters Spreading OFDMA Sensing techniques OQAM/OFDMA Duo-binary CTC Submission 10 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 802. 22 requirements consideration • • • Regional Area Network (up to 30 Km) 4 watt transmission power Large delay spread and roundtrip time Data rate: from 1. 5 Mbps DS and ~300 Kbps US -70 d. B OOB emission Should not cause harmful interference to other devices (incumbents) Submission 11 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 802. 22 requirements consideration (cont. ) • Flexibility – – Bandwidth Access and services Data protection Power • Maximise Bit-rate/Hertz x Watt Submission 12 Carlos Cordeiro, Philips
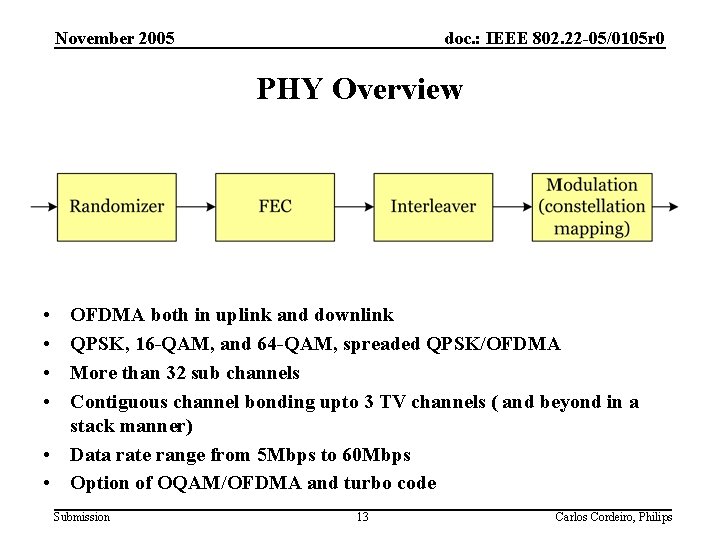
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 PHY Overview • • OFDMA both in uplink and downlink QPSK, 16 -QAM, and 64 -QAM, spreaded QPSK/OFDMA More than 32 sub channels Contiguous channel bonding upto 3 TV channels ( and beyond in a stack manner) • Data rate range from 5 Mbps to 60 Mbps • Option of OQAM/OFDMA and turbo code Submission 13 Carlos Cordeiro, Philips
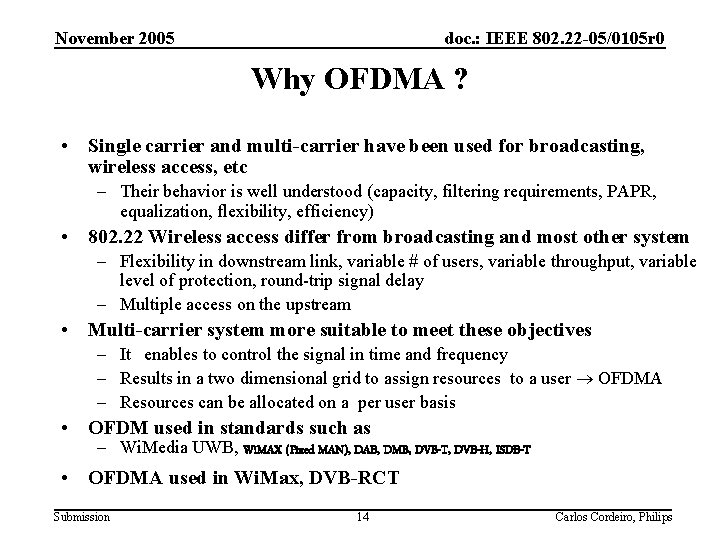
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Why OFDMA ? • Single carrier and multi-carrier have been used for broadcasting, wireless access, etc – Their behavior is well understood (capacity, filtering requirements, PAPR, equalization, flexibility, efficiency) • 802. 22 Wireless access differ from broadcasting and most other system – Flexibility in downstream link, variable # of users, variable throughput, variable level of protection, round-trip signal delay – Multiple access on the upstream • Multi-carrier system more suitable to meet these objectives – It enables to control the signal in time and frequency – Results in a two dimensional grid to assign resources to a user OFDMA – Resources can be allocated on a per user basis • OFDM used in standards such as – Wi. Media UWB, Wi. MAX (Fixed MAN), DAB, DMB, DVB-T, DVB-H, ISDB-T • OFDMA used in Wi. Max, DVB-RCT Submission 14 Carlos Cordeiro, Philips
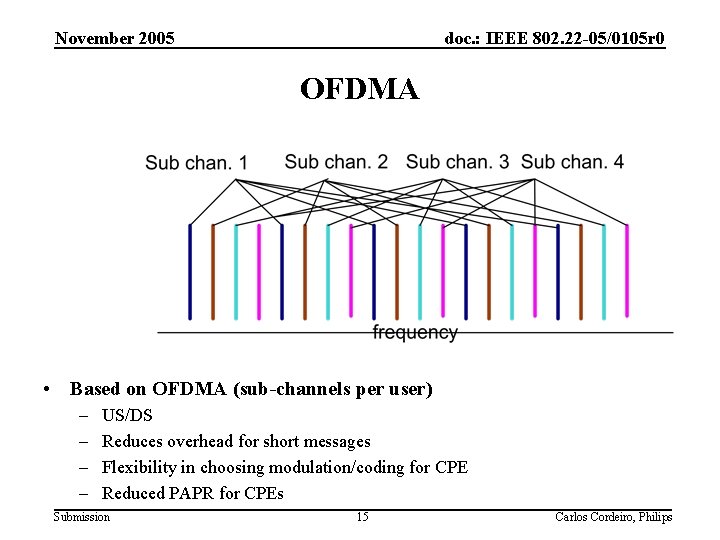
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 OFDMA • Based on OFDMA (sub-channels per user) – – US/DS Reduces overhead for short messages Flexibility in choosing modulation/coding for CPE Reduced PAPR for CPEs Submission 15 Carlos Cordeiro, Philips
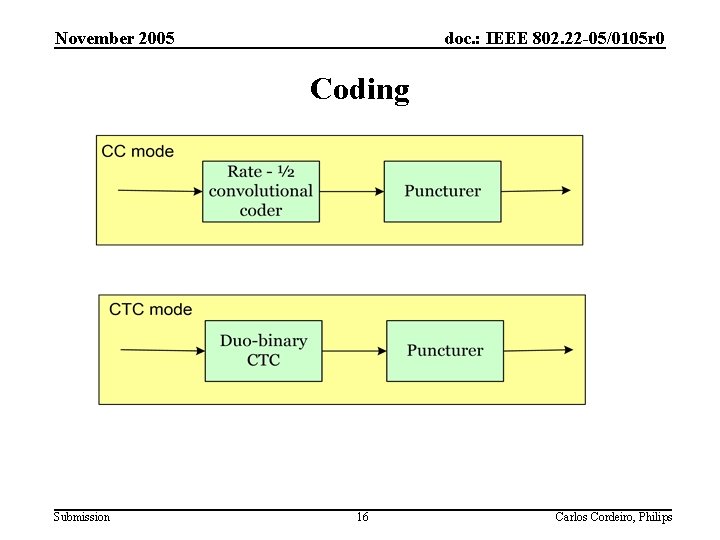
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Coding Submission 16 Carlos Cordeiro, Philips
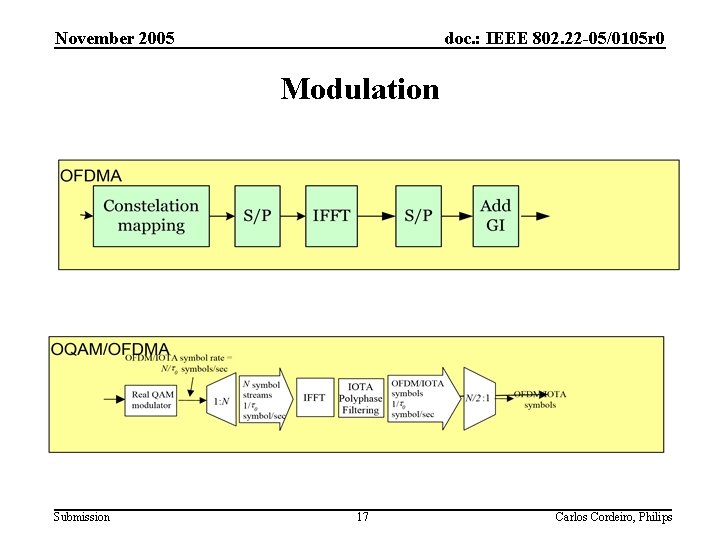
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Modulation Submission 17 Carlos Cordeiro, Philips
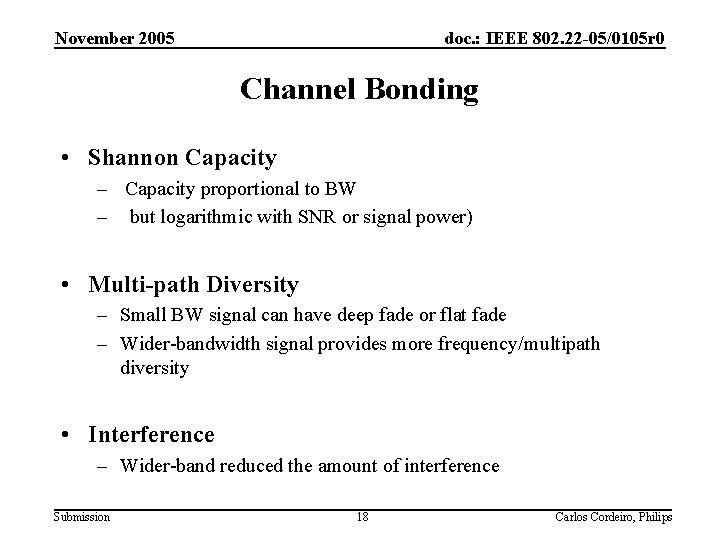
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Channel Bonding • Shannon Capacity – Capacity proportional to BW – but logarithmic with SNR or signal power) • Multi-path Diversity – Small BW signal can have deep fade or flat fade – Wider-bandwidth signal provides more frequency/multipath diversity • Interference – Wider-band reduced the amount of interference Submission 18 Carlos Cordeiro, Philips
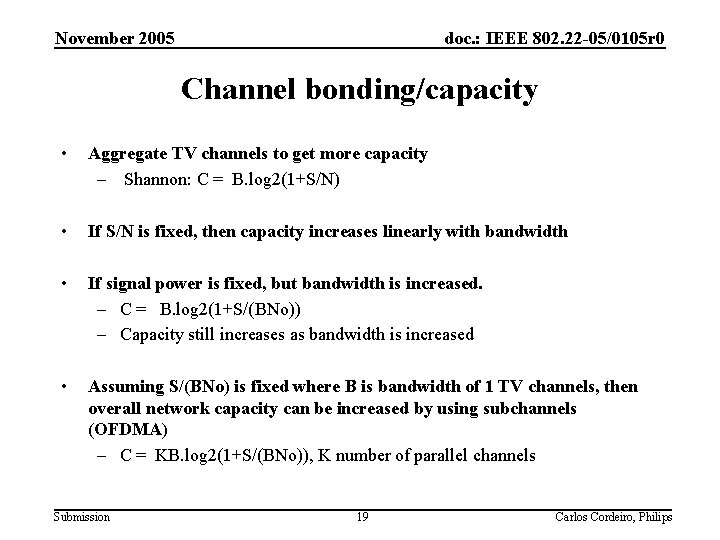
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Channel bonding/capacity • Aggregate TV channels to get more capacity – Shannon: C = B. log 2(1+S/N) • If S/N is fixed, then capacity increases linearly with bandwidth • If signal power is fixed, but bandwidth is increased. – C = B. log 2(1+S/(BNo)) – Capacity still increases as bandwidth is increased • Assuming S/(BNo) is fixed where B is bandwidth of 1 TV channels, then overall network capacity can be increased by using subchannels (OFDMA) – C = KB. log 2(1+S/(BNo)), K number of parallel channels Submission 19 Carlos Cordeiro, Philips
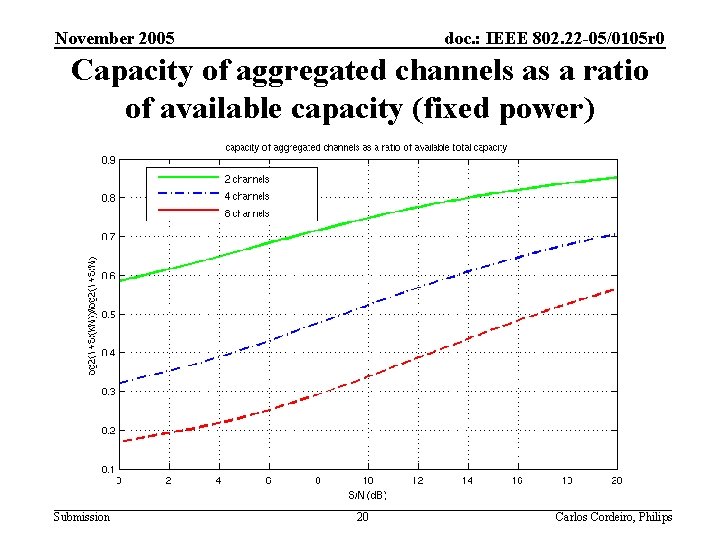
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Capacity of aggregated channels as a ratio of available capacity (fixed power) Submission 20 Carlos Cordeiro, Philips
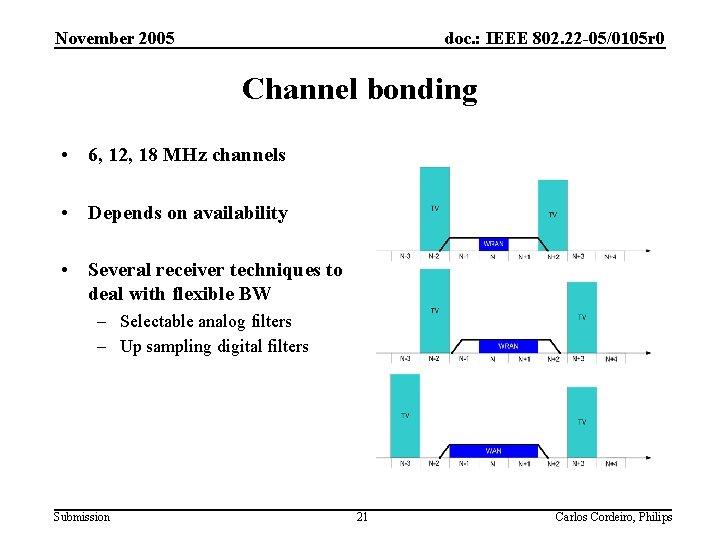
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Channel bonding • 6, 12, 18 MHz channels • Depends on availability • Several receiver techniques to deal with flexible BW – Selectable analog filters – Up sampling digital filters Submission 21 Carlos Cordeiro, Philips
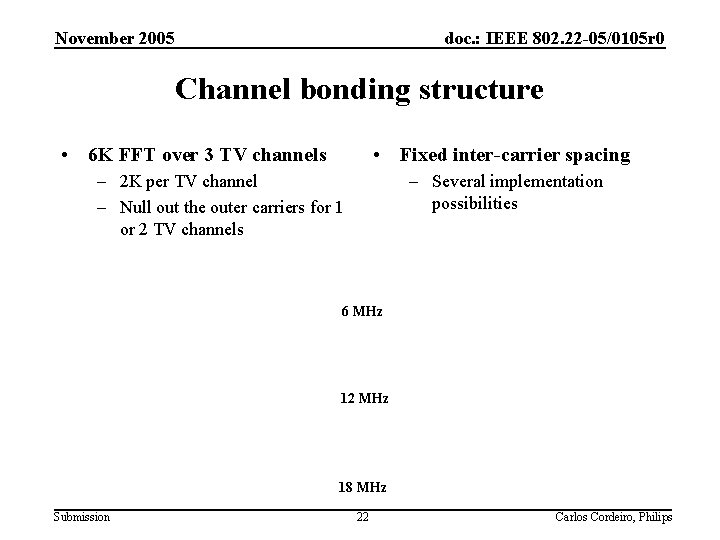
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Channel bonding structure • 6 K FFT over 3 TV channels • Fixed inter-carrier spacing – 2 K per TV channel – Null out the outer carriers for 1 or 2 TV channels – Several implementation possibilities 6 MHz 12 MHz 18 MHz Submission 22 Carlos Cordeiro, Philips
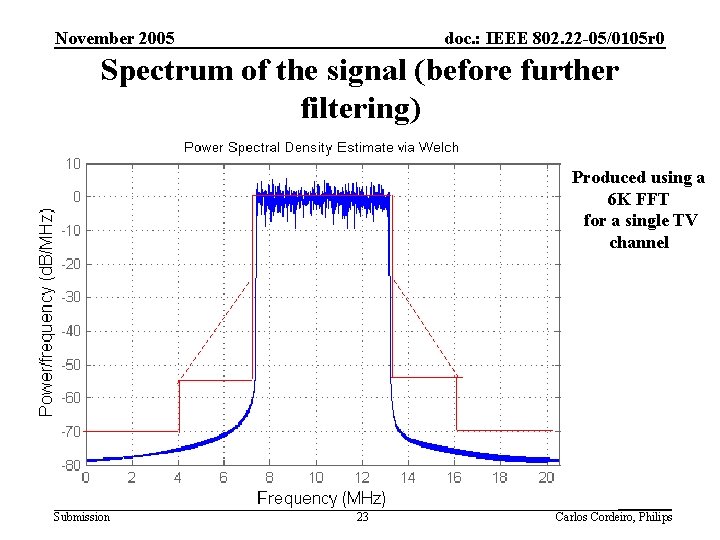
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Spectrum of the signal (before further filtering) Produced using a 6 K FFT for a single TV channel Submission 23 Carlos Cordeiro, Philips
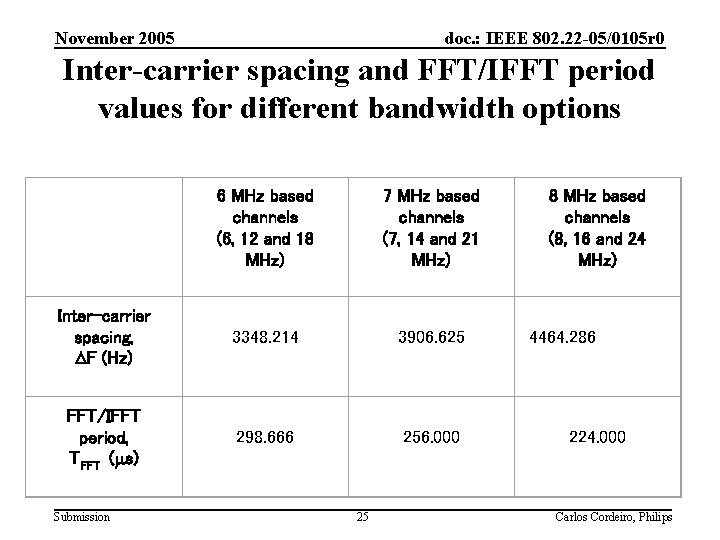
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Inter-carrier spacing and FFT/IFFT period values for different bandwidth options 6 MHz based channels (6, 12 and 18 MHz) 7 MHz based channels (7, 14 and 21 MHz) Inter-carrier spacing, DF (Hz) 3348. 214 3906. 625 FFT/IFFT period, TFFT (ms) 298. 666 256. 000 Submission 25 8 MHz based channels (8, 16 and 24 MHz) 4464. 286 224. 000 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 OFDMA parameters Submission 26 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Modulation/coding modes and corresponding rates Submission 27 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Frame structure: Superframe Submission 28 Carlos Cordeiro, Philips
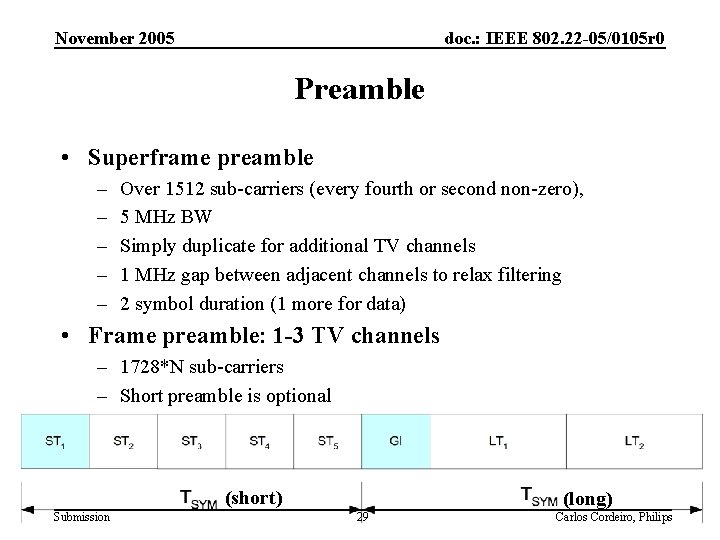
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Preamble • Superframe preamble – – – Over 1512 sub-carriers (every fourth or second non-zero), 5 MHz BW Simply duplicate for additional TV channels 1 MHz gap between adjacent channels to relax filtering 2 symbol duration (1 more for data) • Frame preamble: 1 -3 TV channels – 1728*N sub-carriers – Short preamble is optional (short) Submission (long) 29 Carlos Cordeiro, Philips
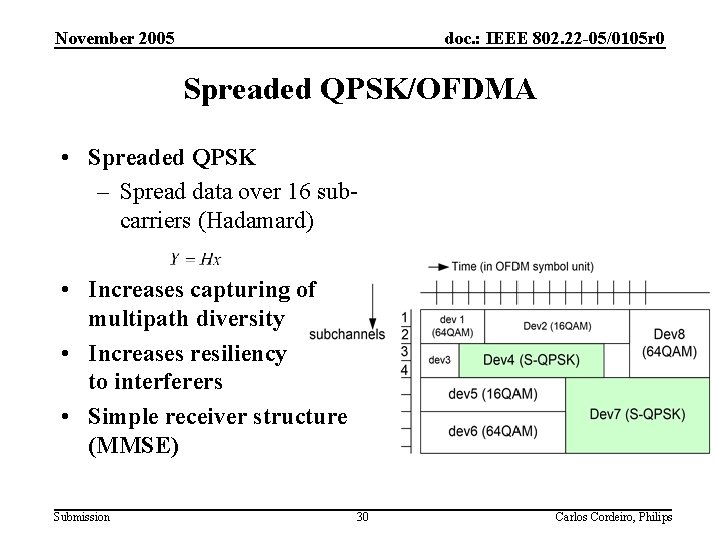
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Spreaded QPSK/OFDMA • Spreaded QPSK – Spread data over 16 subcarriers (Hadamard) • Increases capturing of multipath diversity • Increases resiliency to interferers • Simple receiver structure (MMSE) Submission 30 Carlos Cordeiro, Philips
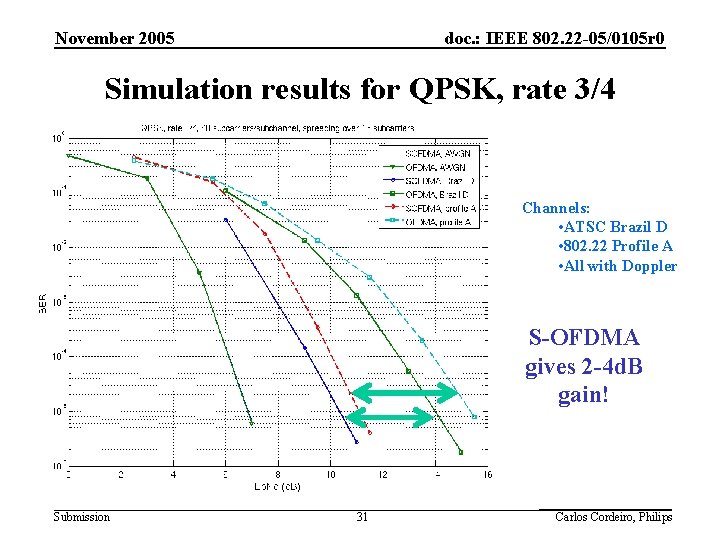
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Simulation results for QPSK, rate 3/4 Channels: • ATSC Brazil D • 802. 22 Profile A • All with Doppler S-OFDMA gives 2 -4 d. B gain! Submission 31 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Preliminary Link Budget(LOS) Submission 32 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Other Features • Ranging • Transmitter Power control (TPC) • Consideration of multiple antenna Submission 33 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Channel Measurement • Received signal strength – Quality – Channel ‘busy’ detection – RSSI on a pilot-tone basis • Signal feature detection – Detection of the type of the signal • ATSC, DVB-T, Part 74, etc – Coherent detection – Should be robust to receiver imperfections Submission 34 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Received Signal Strength • Can be measured in a number of ways – FFT, IOTA/FFT, simple low-pass filter etc • Possibility to measure a part of the spectrum – – Various degrees of performance Integration time and threshold is very important BS sets essential parameters (constant) Either the BS makes the detection decision based on the collective measurement results or CPE’s can make the decision • Can also be used for – Quality measurement of its own signal, TPC – Or simply as fast Channel ‘busy’ detection Submission 35 Carlos Cordeiro, Philips
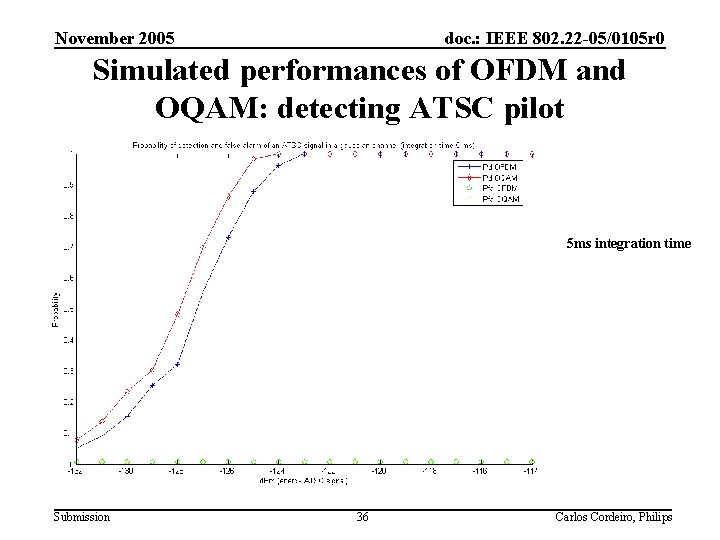
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Simulated performances of OFDM and OQAM: detecting ATSC pilot 5 ms integration time Submission 36 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 DTV signal feature detection • Should not be sensitive to frequency selective fading, and receiver impairments (e. g. , frequency error) • Use field sync correlation detection for ATSC, similar correlation for other standards – Characterized theoretical performance – Experimental tests Submission 37 Carlos Cordeiro, Philips
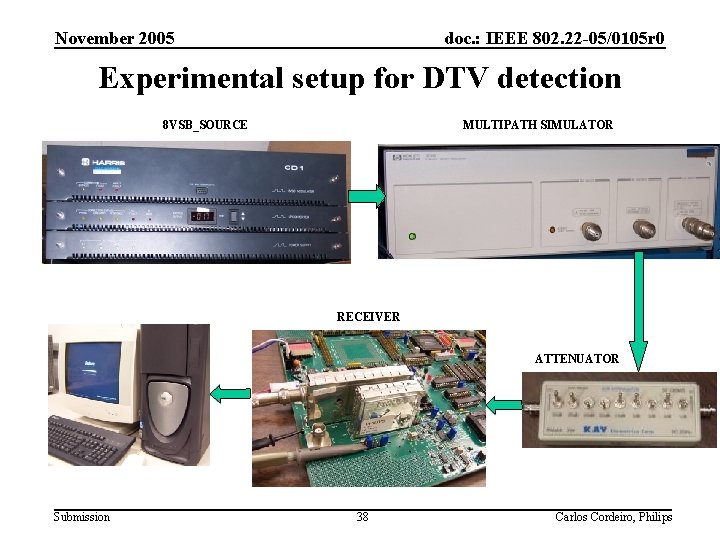
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Experimental setup for DTV detection 8 VSB_SOURCE MULTIPATH SIMULATOR RECEIVER ATTENUATOR Submission 38 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Based on DTV Laboratory Test Plan (Group C. 1) “Static Echoes at various delays”. Submission 39 Carlos Cordeiro, Philips
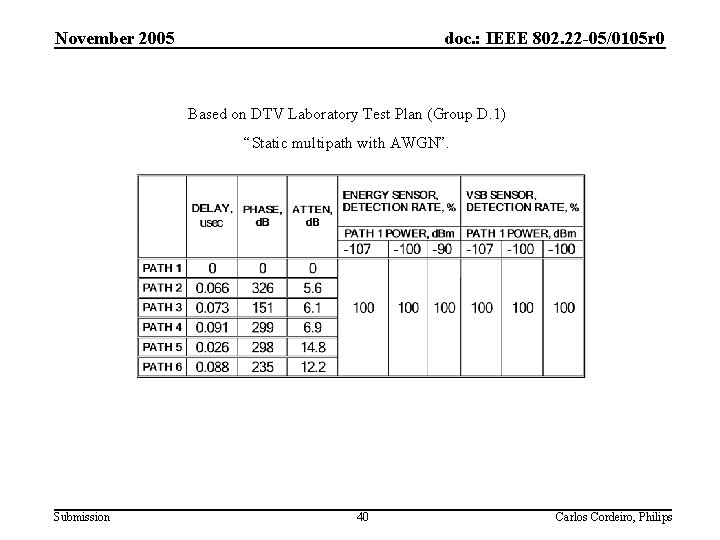
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Based on DTV Laboratory Test Plan (Group D. 1) “Static multipath with AWGN”. Submission 40 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Based on Doc. : IEEE 802. 22 -05/0055 r 7. Profile A. Submission 41 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Based on Doc. : IEEE 802. 22 -05/0055 r 7. Profile B. Submission 42 Carlos Cordeiro, Philips
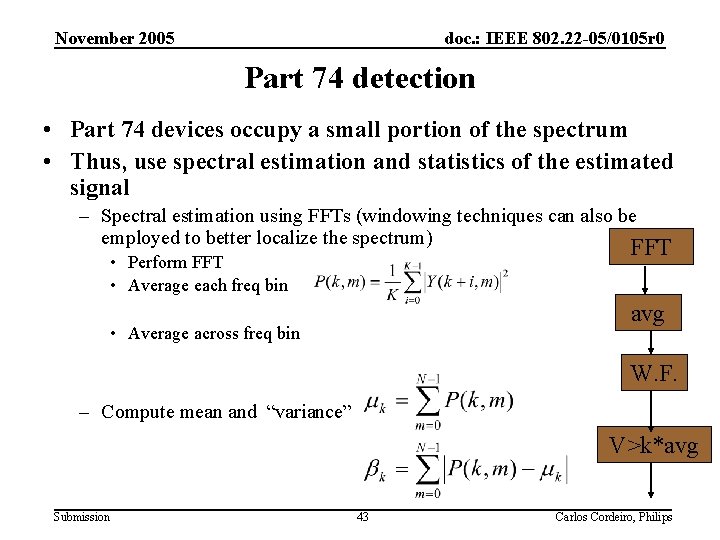
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Part 74 detection • Part 74 devices occupy a small portion of the spectrum • Thus, use spectral estimation and statistics of the estimated signal – Spectral estimation using FFTs (windowing techniques can also be employed to better localize the spectrum) FFT • Perform FFT • Average each freq bin avg • Average across freq bin W. F. – Compute mean and “variance” V>k*avg Submission 43 Carlos Cordeiro, Philips
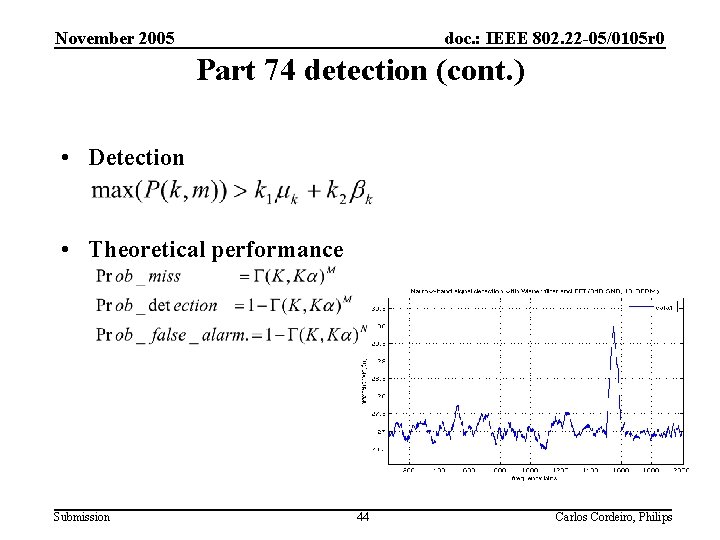
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Part 74 detection (cont. ) • Detection • Theoretical performance Submission 44 Carlos Cordeiro, Philips
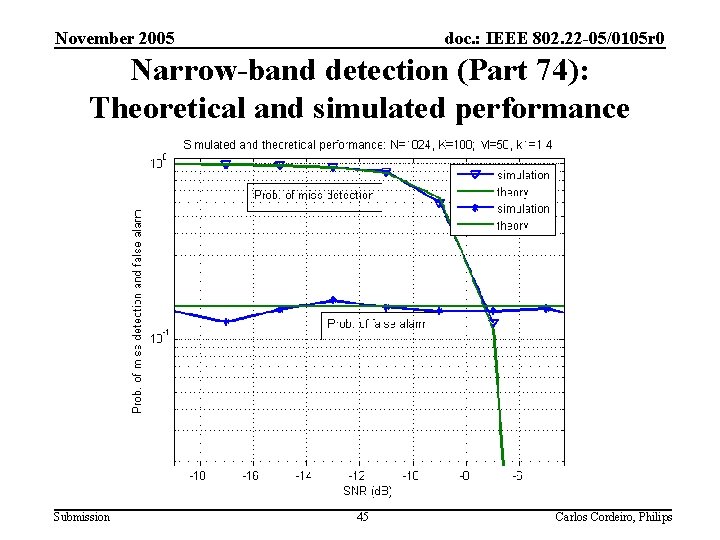
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Narrow-band detection (Part 74): Theoretical and simulated performance Submission 45 Carlos Cordeiro, Philips
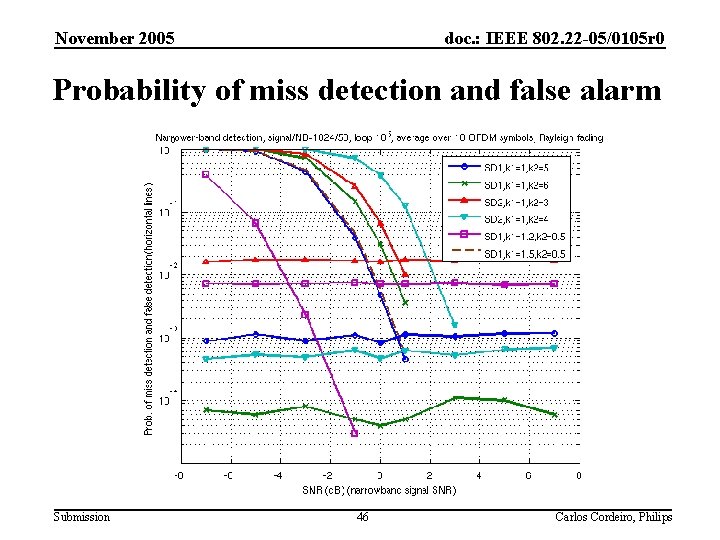
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Probability of miss detection and false alarm Submission 46 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 PHY Presentation Outline • • Background Top-level description of modulation/coding Channel bonding Modulation Parameters Spreading OFDMA Sensing techniques OQAM/OFDMA Duo-binary CTC Submission 47 Carlos Cordeiro, Philips
doc. : IEEE 802. 22 -05/0105 r 0 OFDM/OQAM Outline • Principles of OFDM/OQAM • The IOTA Waveform • Advantages of OFDM/OQAM • Simulation results Submission
doc. : IEEE 802. 22 -05/0105 r 0 OFDM/OQAM principles (1) • Aim: to increase OFDM spectral efficiency by : – Removing the guard interval (cyclic prefix); – Delivering a sharper spectral signal than OFDM. • How: The waveform that modulates OFDM subcarriers is as much as possible localized in time and frequency domains to minimize inter-symbol and intercarrier interferences. Submission
doc. : IEEE 802. 22 -05/0105 r 0 OFDM/OQAM principles (2) • The waveform must guarantee orthogonality between sub-carriers and multi-carrier symbols. – Orthogonality in the frequency domain (between sub-carriers) is guaranteed by OFDM; – Orthogonality in the real domain Offset. QAM on each subcarrier. • Example: IOTA waveform (optimally localized in time and frequency). Submission
doc. : IEEE 802. 22 -05/0105 r 0 OFDM/OQAM principles (2) • OFDM/QAM Transmitted signal: • takes the complex value representing the transmitted encoded data sent on the mth sub-carrier at the nth symbol; • and the basic functions are obtained by translation in time and frequency of a prototype function such as: • With • Unity function x used in OFDM has weak frequency localization. • OFDM/OQAM • Introduces a time offset between real and imaginary parts of symbols • takes real values; • And with Submission
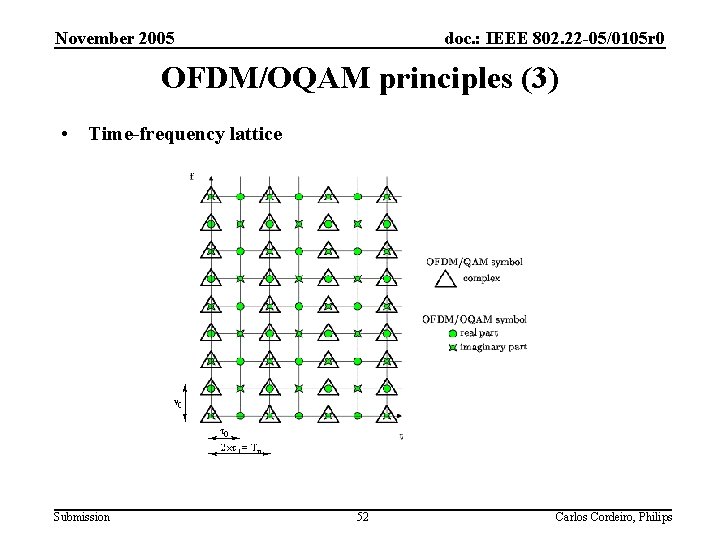
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 OFDM/OQAM principles (3) • Time-frequency lattice Submission 52 Carlos Cordeiro, Philips
doc. : IEEE 802. 22 -05/0105 r 0 The IOTA function (1) IOTA = Isotropic Orthogonal Transform Algorithm • IOTA is a prototype function obtained by the orthogonalization of the Gaussian function • Its particularity: the IOTA waveform modulating each sub-carrier is: – Quasi-optimally localized in both time and frequency – Isotropic: it has the same shape as its Fourier transform => delay spread and Doppler are both equally managed Submission
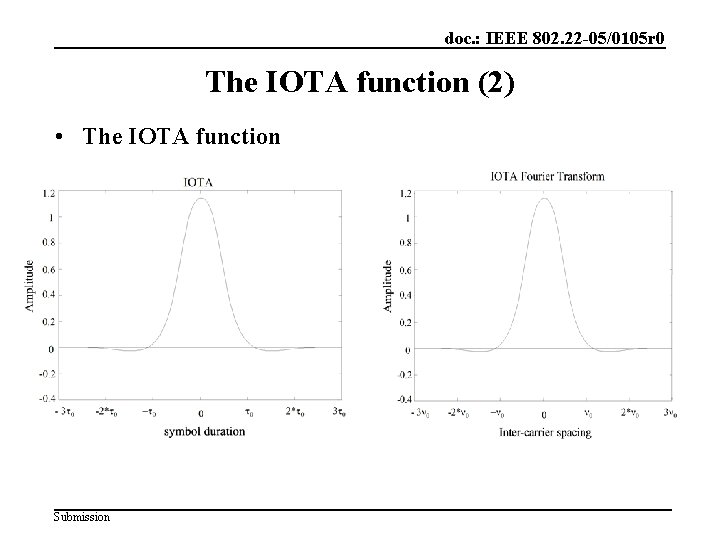
doc. : IEEE 802. 22 -05/0105 r 0 The IOTA function (2) • The IOTA function Submission
doc. : IEEE 802. 22 -05/0105 r 0 The IOTA function (3) • The IOTA function can be denoted by: Where: • The transmitted signal is: Submission
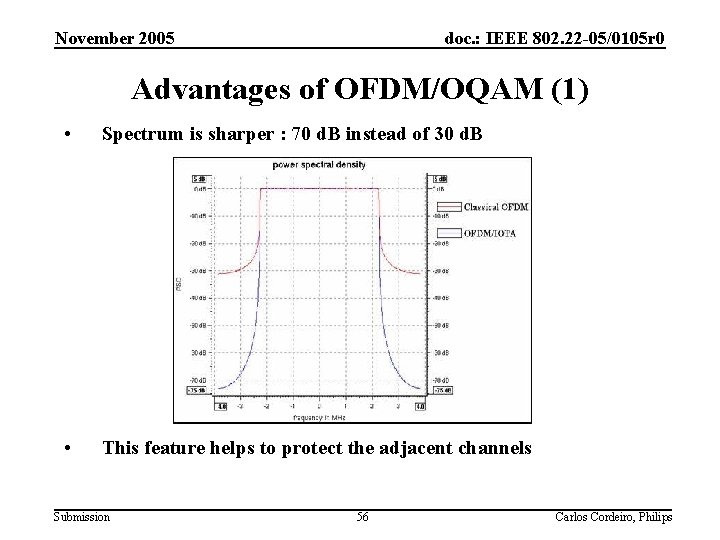
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Advantages of OFDM/OQAM (1) • Spectrum is sharper : 70 d. B instead of 30 d. B • This feature helps to protect the adjacent channels Submission 56 Carlos Cordeiro, Philips
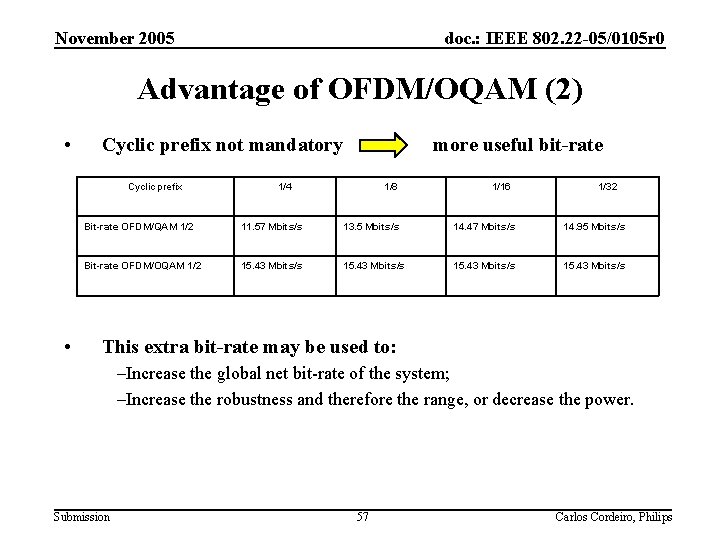
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Advantage of OFDM/OQAM (2) • Cyclic prefix not mandatory Cyclic prefix • more useful bit-rate 1/4 1/8 1/16 1/32 Bit-rate OFDM/QAM 1/2 11. 57 Mbits/s 13. 5 Mbits/s 14. 47 Mbits/s 14. 95 Mbits/s Bit-rate OFDM/OQAM 1/2 15. 43 Mbits/s This extra bit-rate may be used to: –Increase the global net bit-rate of the system; –Increase the robustness and therefore the range, or decrease the power. Submission 57 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Simulation results • Simulation parameters: – – – Submission Constellation : 64 QAM Coding rate : ½ Bandwidth : 7 MHZ Channel: 641 MHz Channel model: Model 1 of WRAN 58 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 OFDM/OQAM vs OFDM/QAM with Convolutional FEC Simulations under progress Submission 59 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 OFDM/OQAM vs OFDM/QAM with Duo-binary Turbo-codes Simulations under progress Submission 60 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 State of the art • OQAM waveform has been standardized by TIA committee TR 8 for Private Land Mobile applications Submission 61 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 PHY Presentation Outline • • Background Top-level description of modulation/coding Channel bonding Modulation Parameters Spreading OFDMA Sensing techniques OQAM/OFDMA Duo-binary CTC Submission 62 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Duo-binary Turbo-codes Outline • Duo-Binary Turbo Codes • Internal interleaver • Flexibility • Performance • Simulations Submission 63 Carlos Cordeiro, Philips
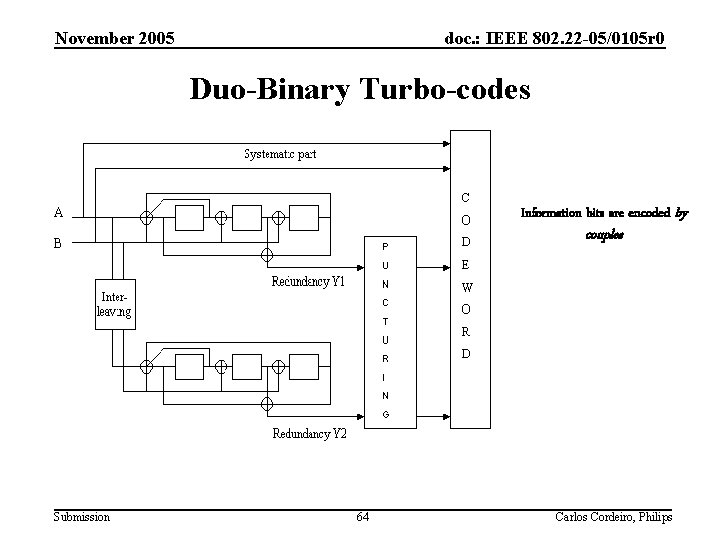
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Duo-Binary Turbo-codes Information bits are encoded by couples Submission 64 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Duo-Binary Turbo-code • Duo-Binary input: two decoded bit output at a time – Reduction of latency and complexity per decoded bit (compared to Binary TC) – Better convergence • Circular (tail-biting) encoding – No trellis termination overhead • Original interleaving scheme – Larger minimum distances – Improved asymptotic performances Submission 65 Carlos Cordeiro, Philips
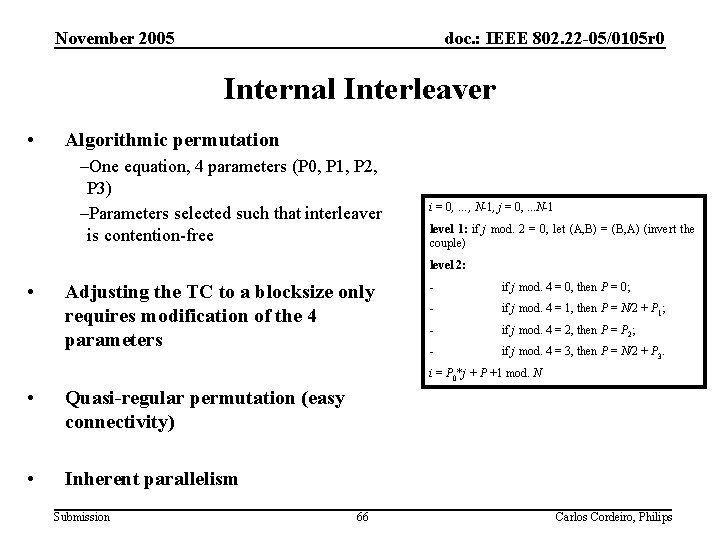
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Internal Interleaver • Algorithmic permutation –One equation, 4 parameters (P 0, P 1, P 2, P 3) –Parameters selected such that interleaver is contention-free i = 0, …, N-1, j = 0, . . . N-1 level 1: if j mod. 2 = 0, let (A, B) = (B, A) (invert the couple) level 2: • Adjusting the TC to a blocksize only requires modification of the 4 parameters - if j mod. 4 = 0, then P = 0; - if j mod. 4 = 1, then P = N/2 + P 1; - if j mod. 4 = 2, then P = P 2; - if j mod. 4 = 3, then P = N/2 + P 3. i = P 0*j + P +1 mod. N • Quasi-regular permutation (easy connectivity) • Inherent parallelism Submission 66 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Flexibility • Can be easily adjusted to any blocksize –Storage of the 4 parameters for all blocksizes considered –Possibility of a generic approach (default parameters) • All coding rates are possible –Through puncturing patterns –Natural coding rate is ½: increased robustness to puncturing • Performance vs complexity: several adjustments are possible –Number of iterations, Decoding algorithm, … • Implementation: interleaver enables different degrees of parallelism –Can be adjusted to meet complexity/throughput requirements Submission 67 Carlos Cordeiro, Philips
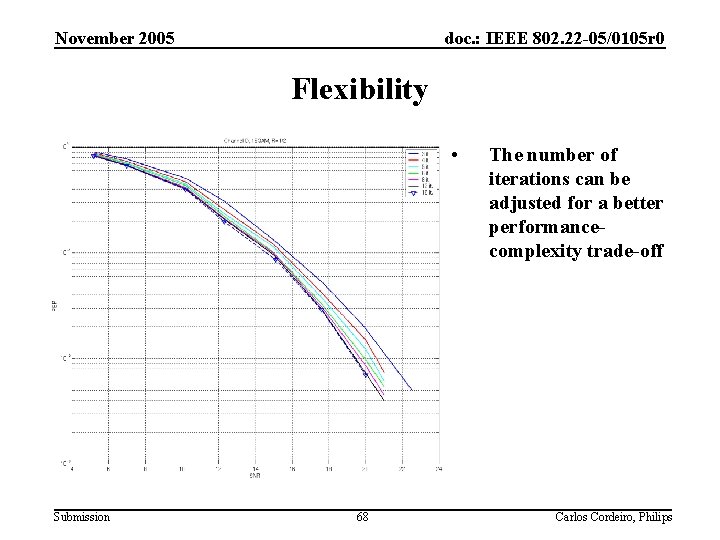
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Flexibility • Submission 68 The number of iterations can be adjusted for a better performancecomplexity trade-off Carlos Cordeiro, Philips
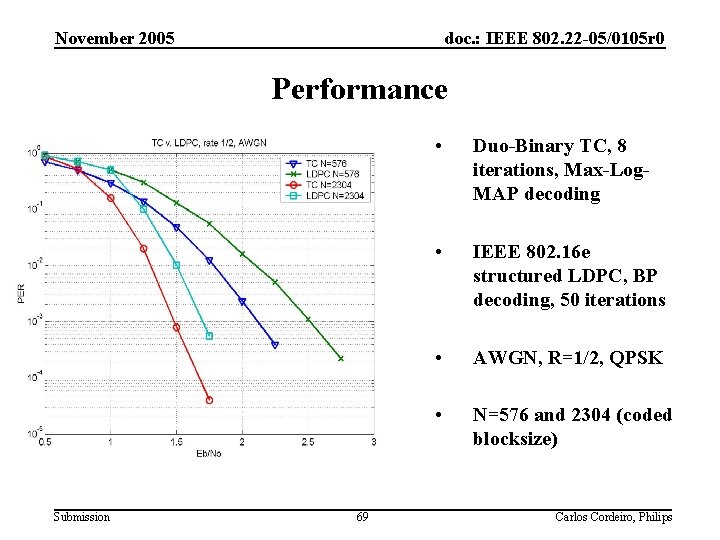
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Performance Submission 69 • Duo-Binary TC, 8 iterations, Max-Log. MAP decoding • IEEE 802. 16 e structured LDPC, BP decoding, 50 iterations • AWGN, R=1/2, QPSK • N=576 and 2304 (coded blocksize) Carlos Cordeiro, Philips
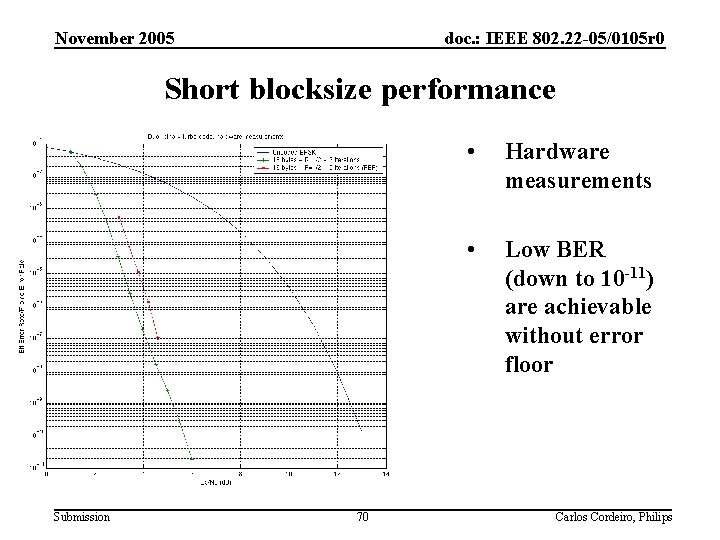
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Short blocksize performance Submission 70 • Hardware measurements • Low BER (down to 10 -11) are achievable without error floor Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Simulation results • Simulation parameters – – – Submission Constellation : 64 QAM Coding rate : ½ Bandwidth : 7 MHZ Channel: 641 MHz Channel model: Model 1 of WRAN 71 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Duo-binary Turbo-codes vs Convolutional with OFDM/QAM modulation Simulations under progress Submission 72 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Duo-binary Turbo-codes vs Convolutional with OFDM/OQAM modulation Simulations under progress Submission 73 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Advantages of Duo-binary Turbo-codes • Good performance for a very wide range of blocksizes • Highly flexible scheme, enabling a very fine granularity – Same encoder/decoder for all blocksizes/coding rates. – Several trade-off in performance (number of iterations, decoding algorithm), implementation complexity (degrees of parallelism). • Reasonable complexity – Approximately 35% decrease in complexity per decoded bit compared to Binary TC. Submission 74 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 State of the art • Duo-binary Turbo-code is a mature technology • This technology has already been selected by several standardization groups – – Submission IEEE 802. 16 / Wi. MAX; DVB-RCS; DVB-RCT; ETSI HIPERMAN 75 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Summary: Gains brought by OQAM and DTC • OFDM/OQAM brings 10% more bit-rate – When converted in error protection enables to go from ¾ rate to 2/3 – Gain between 1 and 1, 5 d. B in C/N • Duo-binary TC offers 3, 5 to 4 d. B • When combined the gain is at least 4, 5 d. B that allows to increase the radius by 7, 6 km (17%) with QPSK modulation in a Gaussian channel. Submission 76 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Final conclusion for WRAN PHY • OFDMA/Channel bonding – Good answer to flexibility requirements • Spreading QPSK – Captures multipath diversity and increases resiliency to interference (2 -4 d. B gain) • OQAM waveform – Increases efficiency and incumbent protection • Duo-binary Turbo-codes – Powerful error protection technique Submission 77 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction – A Glimpse of IEEE 802. 22 • The Cognitive PHY Proposal • The Cognitive MAC Proposal • Conclusions Submission 78 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 CMAC Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 79 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 CMAC Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 80 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Introduction • A Cognitive MAC (CMAC) layer is proposed to be used as the future IEEE 802. 22 MAC for WRANs • Some aspects of CMAC have been inspired by the IEEE 802. 16 MAC standard • However, major enhancements have been made – Support of multiple channel operation; – Coexistence with both incumbents and itself (self-coexistence); • • • Measurements (incumbents and itself) Spectrum management (time, frequency and power) The Coexistence Beacon Protocol (CBP) Synchronization of overlapping BSs The Incumbent Detection Recovery Protocol (IDRP) Embedded wireless microphone beacon mechanism – Clustering support; etc. Submission 81 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 82 Carlos Cordeiro, Philips
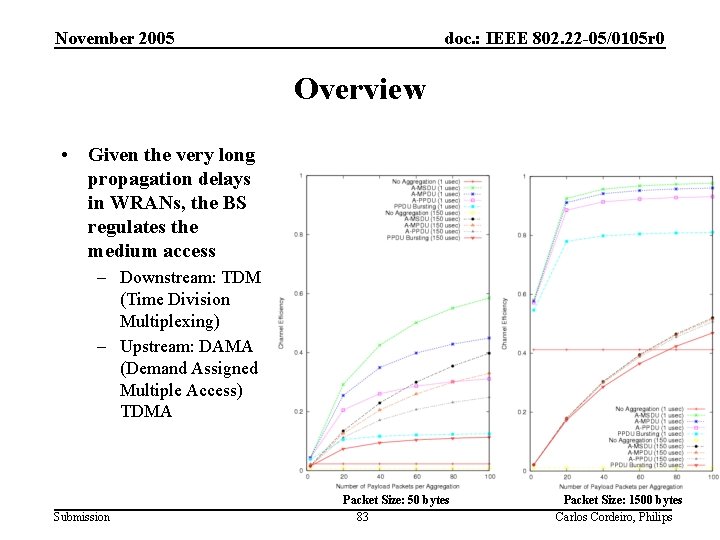
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Overview • Given the very long propagation delays in WRANs, the BS regulates the medium access – Downstream: TDM (Time Division Multiplexing) – Upstream: DAMA (Demand Assigned Multiple Access) TDMA Submission Packet Size: 50 bytes 83 Packet Size: 1500 bytes Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Overview (cont. ) • Combination of polling, contention and unsolicited bandwidth grants mechanisms • Support of Unicast/Multicast/Broadcast for both management and data • Connection-oriented MAC – Connection identifier (CID) is a key component – Defines a mapping between peer processes – Defines a service flow (Qo. S provisioning) Submission 84 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 85 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Protocol Stack Architecture • Flexibility, scalability and efficiency are core elements • Spectrum manager could be implemented in many ways Submission 86 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Protocol Stack Architecture (cont. ) • Flexible channel assignment – Implementers decide on the algorithm Submission 87 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 88 Carlos Cordeiro, Philips
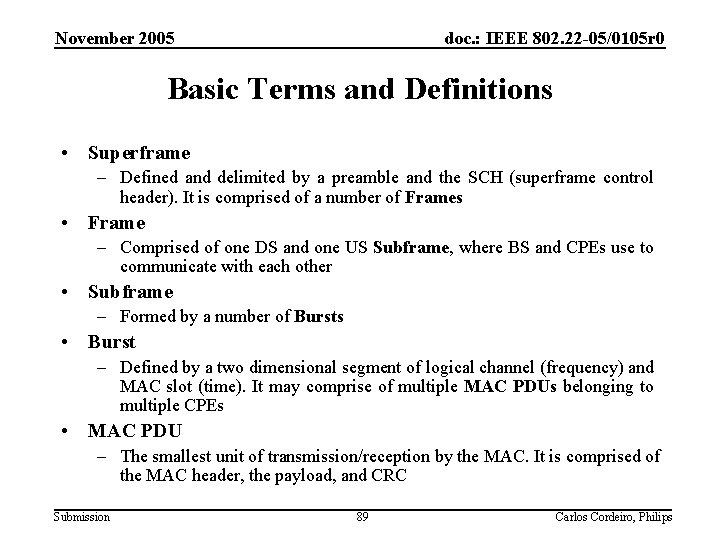
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Basic Terms and Definitions • Superframe – Defined and delimited by a preamble and the SCH (superframe control header). It is comprised of a number of Frames • Frame – Comprised of one DS and one US Subframe, where BS and CPEs use to communicate with each other • Subframe – Formed by a number of Bursts • Burst – Defined by a two dimensional segment of logical channel (frequency) and MAC slot (time). It may comprise of multiple MAC PDUs belonging to multiple CPEs • MAC PDU – The smallest unit of transmission/reception by the MAC. It is comprised of the MAC header, the payload, and CRC Submission 89 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Motivation • The problem – How to offer enhanced capacity and higher data rates? • The fact – Spectrum occupancy measurements conducted by Shared Spectrum Company from January/2004 to August/2005 have shown that: • “There is a significant amount of spectrum available in continuous blocks that are 1 MHz and wider ” • “A dynamic spectrum sharing radio with a low agility, contiguous waveform will provide high utility” • The solution – Simultaneous use of multiple contiguous TV channels Submission 90 Carlos Cordeiro, Philips
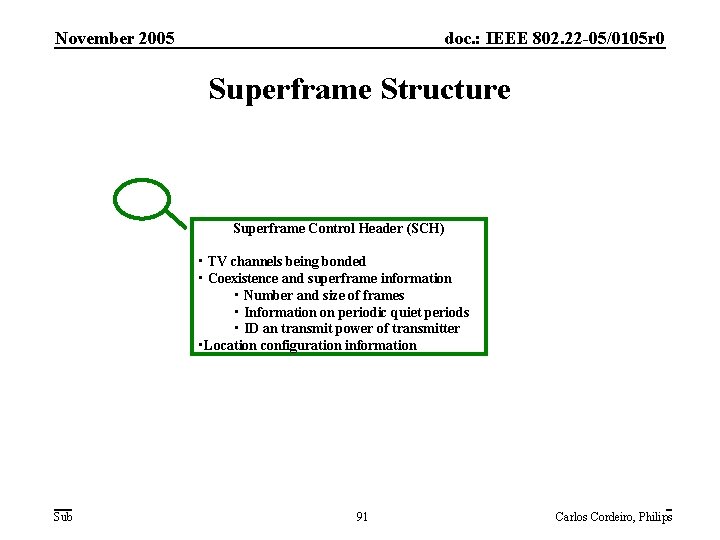
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Superframe Structure Superframe Control Header (SCH) • TV channels being bonded • Coexistence and superframe information • Number and size of frames • Information on periodic quiet periods • ID an transmit power of transmitter • Location configuration information Submission 91 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Frame Structure • CMAC is based on a TDD frame structure only – Reduced complexity – The flexible architecture (with the Spectrum Manager) already brings with it aspects of FDD • The CMAC frame structure is comprised of two parts – A predominantly downstream (DS) subframe – An upstream (US) subframe Submission 92 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Frame Structure (cont. ) Submission 93 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Time/Frequency Structure of a MAC Frame Submission 94 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Network Entry and Initialization • The key problem Submission 95 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Downstream (DS) Transmissions • DS = core messages + data (transmitted in bursts) – Two core DS messages: DCD and DS-MAP – Bursts identified by DIUC (Downstream Interval Usage Code) – Each burst may contain data for several CPEs • DCD (Downstream Channel Descriptor) – Establishes association between DIUC and actual PHY parameters (e. g. , modulation and coding) • DS-MAP (Downstream map) – Defines the usage (i. e. , scheduling) of the downstream – Critical, hence first message in each frame – For self-coexistence purposes, the BS may choose to use part of DS subframe for CBP protocol operation Submission 96 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Upstream (US) Transmissions • US = core messages + data (contention and bursts) – Two core DS messages: UCD and US-MAP – Bursts identified by UIUC (Upstream Interval Usage Code) – The upstream can be segmented into several UIUC • Contention-based – Initialization, Bandwidth Request, Urgent Coexistence Situation (UCS), CBP slots (SCS) • Data Bursts • UCD (Upstream Channel Descriptor) – Establishes association between UIUC and actual PHY parameters (e. g. , modulation and coding) • US-MAP (Upstream map) – Defines the usage (i. e. , scheduling) of the upstream – Contains “grants”addressed to a particular CPE or a set of CPEs (e. g. , for selfcoexistence) Submission 97 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Bandwidth Management: Request/Grant Scheme • Self correcting – No acknowledgement – All errors are handled the same way (i. e. , periodic aggregate requests) • Bandwidth requests – Are always per connection – Can specify DS/US Traffic Constraint IEs for better self-coexistence • Bandwidth grants – Can be either per connection or per CPE – Grants (given as durations) are carried in US-MAP messages – CPE converts time into amount of data using information about the UIUC Submission 98 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Scheduling Services • Unsolicited Grant Services (UGS) – For CBR and CBR-like flows (T 1/E 1) – No specific bandwidth request issued by CPE • Real-time Polling Service (rt. PS) – For rt-VBR-like service flows such as MPEG video – CPEs are polled to meet delay requirements • Non-real-time Polling Service (nrt. PS) – For non-real-time flows with better than best effort service such as bandwidth-intensive file transfer – CPEs are polled and can use contention interval • Best Effort (BE) – E. g. , Web surfing – CPEs use contention interval only Submission 99 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 100 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Coexistence • Two primary types – With incumbents (TV service and Part 74 devices) – With other overlapping 802. 22 cells • Self-Coexistence • Measurements can be classified as: – In-band • In case of incumbents, requires quiet periods – Out-of-band • No need for quiet periods • Coexistence is achieved by a joint application of: – Spectrum management (frequency and power) – “Interference-free” traffic scheduling (time) Submission 101 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Measurements • Measurements form a key component of CMAC – Protection of incumbents and self-coexistence • The BS may request multiple measurements in a single management message – E. g. , ATSC, DVB, Wireless Microphone, 802. 22 • Measurement messages may be transmitted through multicast – Allows the implementation of advanced features such as clustering – Bandwidth efficient Submission 102 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Measurements (cont. ) • Bulk Measurement Request (BLM-REQ) – Transmitted by the BS to CPEs – Includes information such as • Channels to measure • Multiple single measurement requests • Bulk Measurement Response (BLM-RSP) – Transmitted by CPE to BS – If needed, acknowledges the receipt of the BLM-REQ message • Bulk Measurement Report (BLM-REP) – Transmitted by CPE to BS – Returns multiple single measurement reports • Bulk Measurement Acknowledgement (BLM-ACK) – Transmitted by BS to CPE – Acknowledges receipt of measurement report Submission 103 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Measurements (cont. ) • Single measurements can be of various types – Signal specific measurement request • TV system and Wireless microphones – Beacon measurement request • CBP, BS, and Wireless microphone beacons – CPE statistics measurement request – Stop measurement request – Location configuration measurement request • A range of parameters can be specified Submission 104 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Measurements (cont. ) • There is almost a one-to-one correspondence between measurement requests and reports • Some of the individual reports are: – Signal specific measurement report • TV/Wireless Microphone system type, measured value, precision, etc. – Beacon measurement report • Information on any CBP, BS, or Wireless microphone beacons received – CPE statistics measurement report • E. g. , Packet error rate – Location configuration measurement report • If known, location information (GPS, triangulization, and so on) Submission 105 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Channel Management • Channel management is key to effective network coordination, coexistence and sharing • Included in two modes – Embedded – Non-embedded • A set of messages are defined to allow flexible management of channels, including: – Add/remove channel(s) to/from current set of channels – Switch channel(s) of operation – Quiet selected channel(s) – possibly to perform in-band measurement Submission 106 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 107 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Coexistence with Incumbents • Accomplished through the following steps: – Measurements (discussed earlier) – Detection • TV: For more info, please see PHY proposal. • Wireless Microphones – PHY solution: For more info, please see PHY proposal. – MAC solution: See next slide. – Incumbent Notification – Incumbent Detection Recovery Submission 108 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Coexistence with Incumbents • Accomplished through the following steps: – Measurements (discussed earlier) – Detection • TV: For more info, please see PHY proposal. • Wireless Microphones – PHY solution: For more info, please see PHY proposal. – MAC solution: See next slide. – Incumbent Notification – Incumbent Detection Recovery Submission 109 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 MAC Layer Detection of Wireless Microphones • Wireless microphone beacons (WMB) can be of two types – Embedded • 802. 22 device which has the additional capability of emitting WMBs – Non-embedded • Currently addressed by the Part 74 Study/Task Group • Based on the proposed MAC layer, we have developed an embedded WMB approach that: – Reliably detects multiple collocated 802. 22 networks – Upon sending WMBs, this mechanism causes minimal, if any, harmful interference to collocated 802. 22 networks – Once either BSs or CPEs detect the WMB, a dissemination is made and all present 802. 22 networks vacate the channel Submission 110 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Incumbent Notification • The problem – How to notify the BS about the presence of incumbents in a timely fashion? • Two solutions are possible – CPEs with upstream bandwidth allocation • Send report provided bandwidth and time are available; and/or • Set dedicated bits in MAC header – CPEs without upstream bandwidth allocation • Urgent Coexistence Situation (UCS) Notification slots reserved specifically for incumbent notification purposes – Can use either contention-based or contention-based CDMA access • The size of a slot fits the smallest MAC frame necessary to perform the incumbent notification Submission 111 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Incumbent Notification (cont. ) Submission 112 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Incumbent Notification (cont. ) • The BS can use various strategies depending upon how reliable it wants the notification to be – Trade-off between overhead and data efficiency – Scalability Submission 113 Carlos Cordeiro, Philips
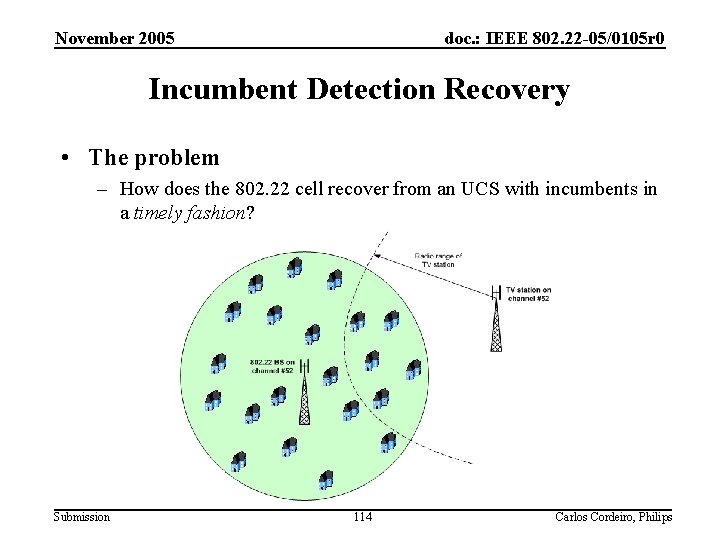
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Incumbent Detection Recovery • The problem – How does the 802. 22 cell recover from an UCS with incumbents in a timely fashion? Submission 114 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Incumbent Detection Recovery (cont. ) • The Incumbent Detection Recovery Protocol (IDRP) – Introduces the concept of a Backup Channel – The 802. 22 network not only performs in-band measurements, but also out-of-band measurements • Out-of-band measurements will determine a suitable Backup Channel – The 802. 22 network falls back to the Backup Channel in case communication is disrupted due to an in-band incumbent – The algorithms at both the BS and CPEs are provided • These algorithms also account for the case when no Backup Channel is available Submission 115 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 116 Carlos Cordeiro, Philips
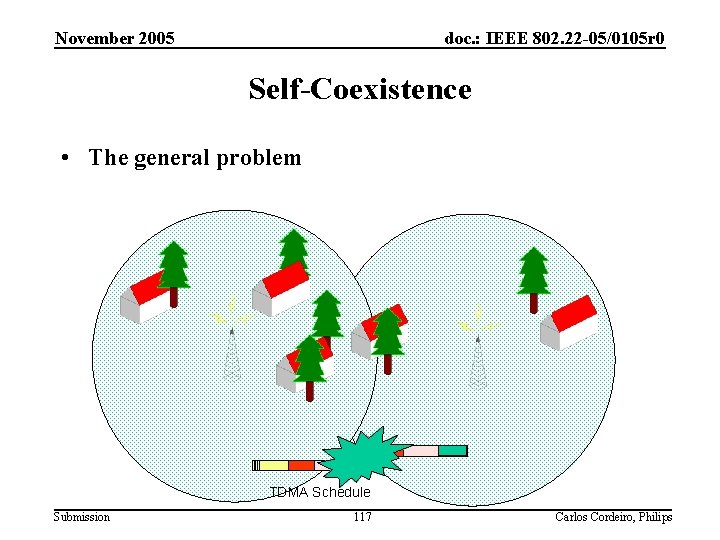
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Self-Coexistence • The general problem TDMA Schedule Submission 117 Carlos Cordeiro, Philips
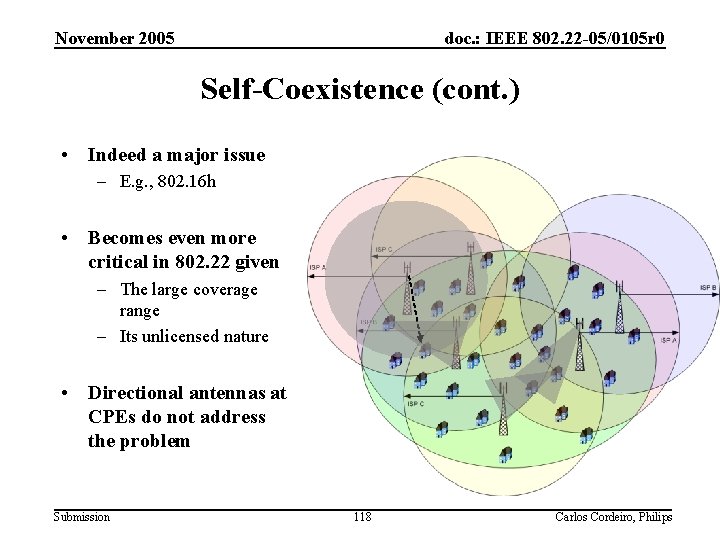
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Self-Coexistence (cont. ) • Indeed a major issue – E. g. , 802. 16 h • Becomes even more critical in 802. 22 given – The large coverage range – Its unlicensed nature • Directional antennas at CPEs do not address the problem Submission 118 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Self-Coexistence (cont. ) • Some approaches to better self-coexistence – Over the backhaul • Pros – 802. 22 can wash its hands (throw the “hot potato” to somebody else) • Cons – Will there be really a “common backhaul” between competing WISPs? Can 802. 22 rely on that? – What if this “common backhaul” is down? – Can 802. 22 rely on the “upper layers” to take care of self-coexistence? – Coordination is an active process (e. g. , quiet periods), and not a “once-in-a-month thing” – Over-the-air • Pros – Built-in and self-healing 802. 22 system • Cons – More complex MAC layer (but just a little more) Submission 119 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Self-Coexistence (cont. ) • Two solutions are proposed – BS beacon based – The Coexistence Beacon Protocol (CBP) • Both solutions: – Can be implemented either over-the-air or via a backbone • Here, we focus on the over-the-air implementation – Allow either one-way or two-way (i. e. , negotiation) communication • The BS and its CPEs shall participate in the selfcoexistence task Submission 120 Carlos Cordeiro, Philips
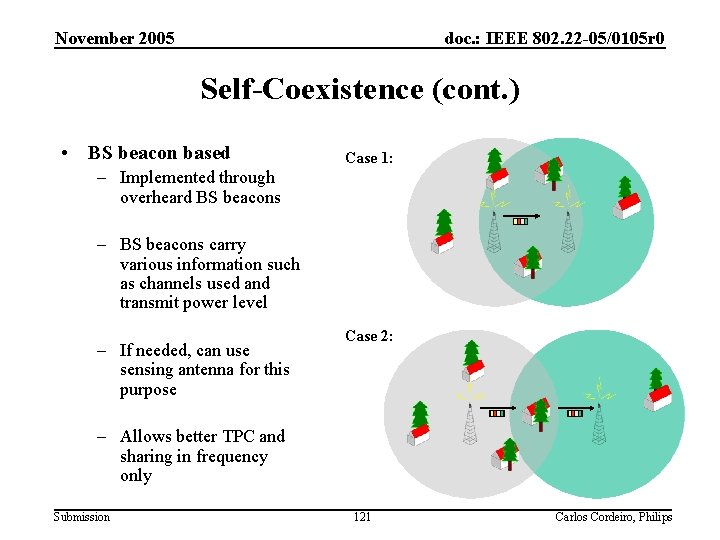
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Self-Coexistence (cont. ) • BS beacon based Case 1: – Implemented through overheard BS beacons – BS beacons carry various information such as channels used and transmit power level – If needed, can use sensing antenna for this purpose Case 2: – Allows better TPC and sharing in frequency only Submission 121 Carlos Cordeiro, Philips
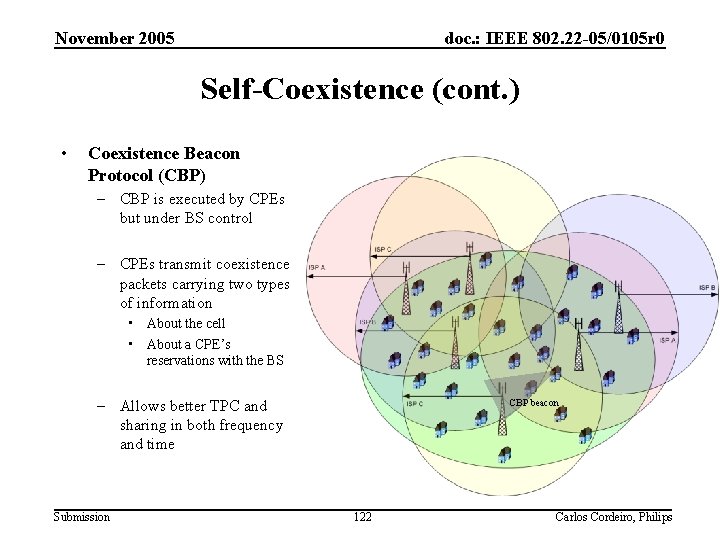
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Self-Coexistence (cont. ) • Coexistence Beacon Protocol (CBP) – CBP is executed by CPEs but under BS control – CPEs transmit coexistence packets carrying two types of information • About the cell • About a CPE’s reservations with the BS – Allows better TPC and sharing in both frequency and time Submission CBP beacon 122 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Self-Coexistence (cont. ) Submission 123 Carlos Cordeiro, Philips
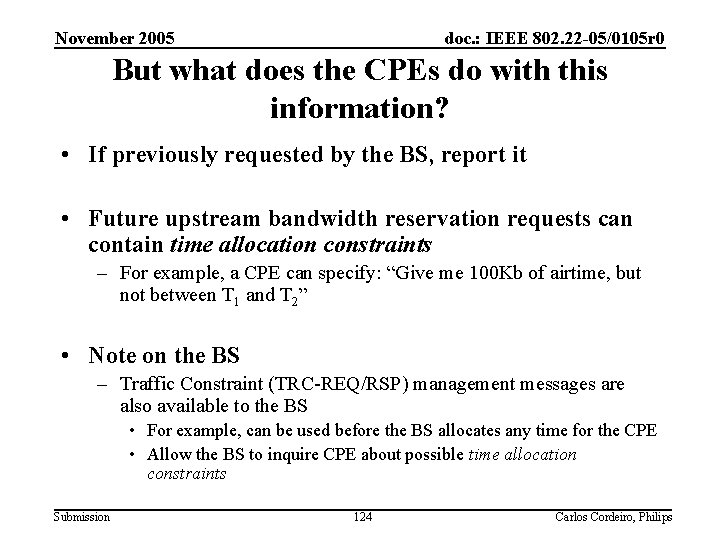
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 But what does the CPEs do with this information? • If previously requested by the BS, report it • Future upstream bandwidth reservation requests can contain time allocation constraints – For example, a CPE can specify: “Give me 100 Kb of airtime, but not between T 1 and T 2” • Note on the BS – Traffic Constraint (TRC-REQ/RSP) management messages are also available to the BS • For example, can be used before the BS allocates any time for the CPE • Allow the BS to inquire CPE about possible time allocation constraints Submission 124 Carlos Cordeiro, Philips
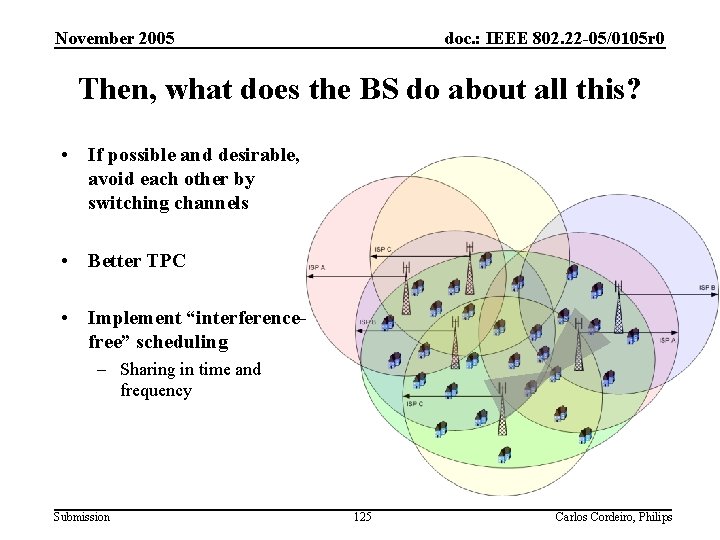
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Then, what does the BS do about all this? • If possible and desirable, avoid each other by switching channels • Better TPC • Implement “interferencefree” scheduling – Sharing in time and frequency Submission 125 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 126 Carlos Cordeiro, Philips
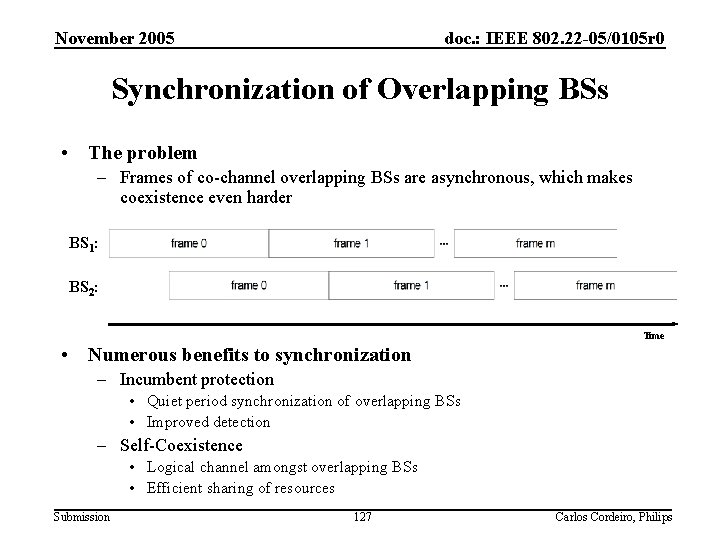
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Synchronization of Overlapping BSs • The problem – Frames of co-channel overlapping BSs are asynchronous, which makes coexistence even harder BS 1: BS 2: Time • Numerous benefits to synchronization – Incumbent protection • Quiet period synchronization of overlapping BSs • Improved detection – Self-Coexistence • Logical channel amongst overlapping BSs • Efficient sharing of resources Submission 127 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Synchronization of Overlapping BSs (cont. ) • Synchronization is proposed amongst multiple collocated 802. 22 networks Submission 128 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 129 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Clustering • Alleviate much of the redundancy involved in the execution of the coexistence mechanisms – So, very suitable for 802. 22 – Can be employed in all coexistence mechanisms, except for the protection of Wireless Microphone services • Based on key observations – Sensing outcome of close-by CPEs are likely to be “similar” – CPEs are stationary • It is a two-step process conducted by the BS – Formation of Physical Cluster – Formation of Logical Cluster Submission 130 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Clustering: Physical Cluster (cont. ) • Creation of Physical Clusters is totally localized at the BS – No direct involvement from CPEs • The BS groups together CPEs sensing “similar” characteristics of the incumbent signal Submission 131 Carlos Cordeiro, Philips
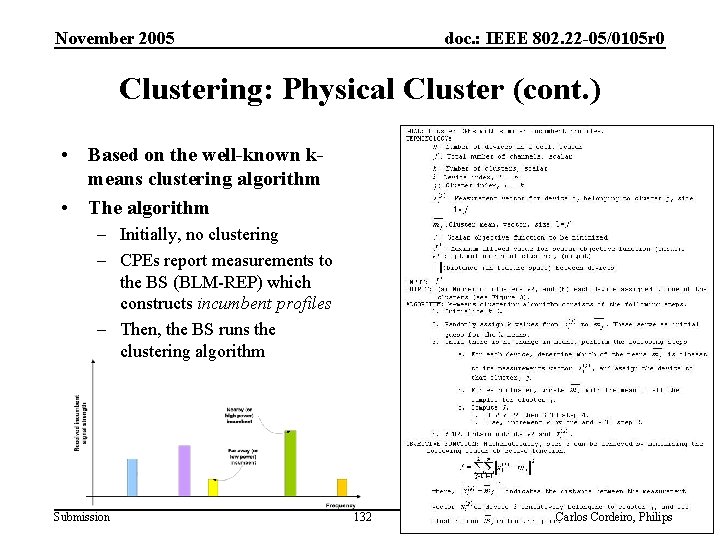
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Clustering: Physical Cluster (cont. ) • Based on the well-known kmeans clustering algorithm • The algorithm – Initially, no clustering – CPEs report measurements to the BS (BLM-REP) which constructs incumbent profiles – Then, the BS runs the clustering algorithm Submission 132 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Clustering: Logical Cluster (cont. ) • Formed by CPEs belonging to different Physical Clusters • Allows the BS to group those CPEs that are less likely to contend for the same airtime • CPEs within a Logical Cluster perform the same “coexistence task” Submission 133 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 134 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Security Sublayer • Based on IEEE 802. 16 e/D 12 security sublayer – Generic security framework made specifically for BWA networks – Meets all the security requirements identified for the 802. 22 WRAN Standard – Deeply studied and improved by various security experts (including IEEE and IETF ones) • Composed of two sublayers – A Privacy Key Management protocol (PKM): provides authentication, authorization and secure key distribution between the BS and the CPE – An encapsulation protocol which provides data packets protection Submission 135 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Security Sublayer (cont. ) • Mutual Authentication of the devices – Either using RSA and digital certificates – Or using EAP and EAP-method specific credentials • Authentication of the subscribers (optional) – Using EAP and EAP-method specific credentials • Authorization based on authenticated CPE and/or subscriber identity – Give access to dedicated service flows Submission 136 Carlos Cordeiro, Philips

November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Security Sublayer (cont. ) • Data packets encryption – Using strong cryptographic algorithms (AES) • Management frames integrity protection – Using keyed message authentication codes • Protection against Deny of Service and other attacks – – Submission Protection of management frames against forgery and replay attacks Protection of data frames against replay attacks Protection of EAP packets during subscribers authentication Protection of every key negotiation phase, using digital signatures and random numbers 137 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction • The CMAC Protocol – Architecture – Data communication • Superframe and Frame Structures • Network entry and initialization • Downstream and Upstream scheduling – Coexistence • • Incumbents Self-Coexistence Synchronization of overlapping BSs Clustering – Security • Performance Evaluation Submission 138 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Performance Evaluation • All aspects of CMAC are being implemented in OPNET – – Channel bonding Incumbents Self-coexistence … • Some preliminary results are presented next – More detailed results are expected to be available during the presentation at the November meeting Submission 139 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Throughput at the MAC SAP • Evaluate throughput of CMAC under varying number of bonded TV channels – Every CPE performs detection in all in-band channel (e. g. , N-1, N, and N+1 in case of only a single TV channel) – DFS model is implemented as per the requirements document – No fragmentation/packing • Some simulation parameters – – – – Submission Superframe size = 12 frames Frame size = 40 ms Packet size = 1 Kbyte Detection time per TV channel (based on feature detection) = 13 ms 64 -QAM rate 2/3 Symbol Time = 310 µs 1 BS and 127 CPEs 140 Carlos Cordeiro, Philips
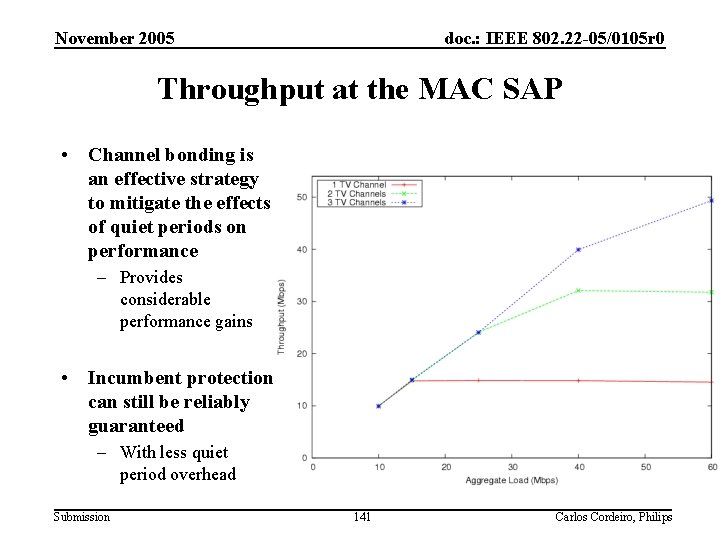
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Throughput at the MAC SAP • Channel bonding is an effective strategy to mitigate the effects of quiet periods on performance – Provides considerable performance gains • Incumbent protection can still be reliably guaranteed – With less quiet period overhead Submission 141 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Presentation Outline • Introduction – A Glimpse of IEEE 802. 22 • The Cognitive PHY Proposal • The Cognitive MAC Proposal • Conclusions Submission 142 Carlos Cordeiro, Philips
November 2005 doc. : IEEE 802. 22 -05/0105 r 0 Conclusions • Proposed a PHY and MAC that addresses the requirements set forth by the 802. 22 WG • PHY – Based on OFDMA • Spreaded OFDMA • O-QAM – Flexible channel configurations (6, 12, and 18 MHz) – TV and Part 74 detection • MAC – Coexistence is a key feature • Incumbent protection • Self-coexistence – CBP and IDRP protocols, superframes, support of channel bonding, etc. Submission 143 Carlos Cordeiro, Philips
- Slides: 142