No Silver Bullet How Malware Defeats Security Measures

No Silver Bullet How Malware Defeats Security Measures and What You Can Do About it Ziv Cohen – Director, EMEA April 2012 1 © 2012 Trusteer Confidential
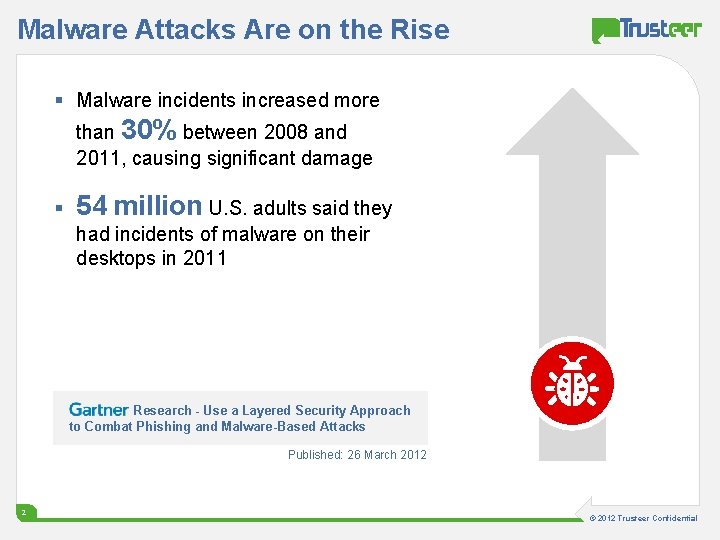
Malware Attacks Are on the Rise § Malware incidents increased more than 30% between 2008 and 2011, causing significant damage § 54 million U. S. adults said they had incidents of malware on their desktops in 2011 Research - Use a Layered Security Approach to Combat Phishing and Malware-Based Attacks Published: 26 March 2012 2 © 2012 Trusteer Confidential

Online Banking Fraud is Happening Online Banking Fraud Losses Estimated at 1 B$ in US and Europe 3 © 2012 Trusteer Confidential
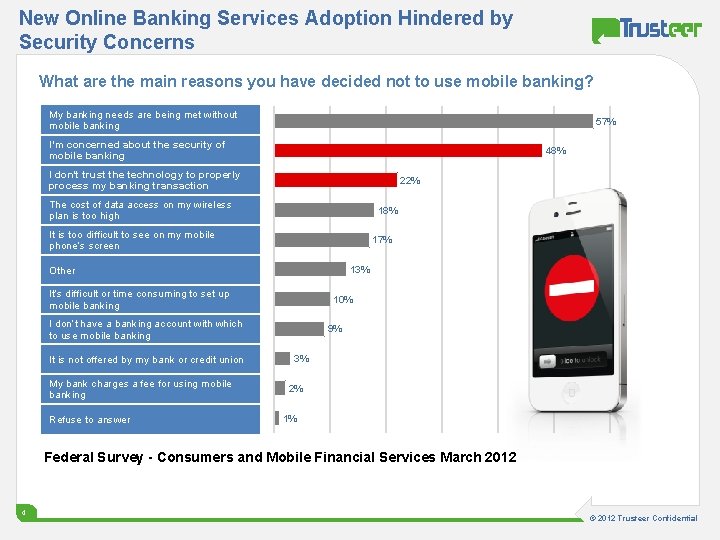
New Online Banking Services Adoption Hindered by Security Concerns What are the main reasons you have decided not to use mobile banking? My banking needs are being met without mobile banking 57% I’m concerned about the security of mobile banking 48% I don't trust the technology to properly process my banking transaction 22% The cost of data access on my wireless plan is too high 18% It is too difficult to see on my mobile phone’s screen 17% 13% Other It’s difficult or time consuming to set up mobile banking 10% I don’t have a banking account with which to use mobile banking It is not offered by my bank or credit union My bank charges a fee for using mobile banking Refuse to answer 9% 3% 2% 1% Federal Survey - Consumers and Mobile Financial Services March 2012 4 © 2012 Trusteer Confidential
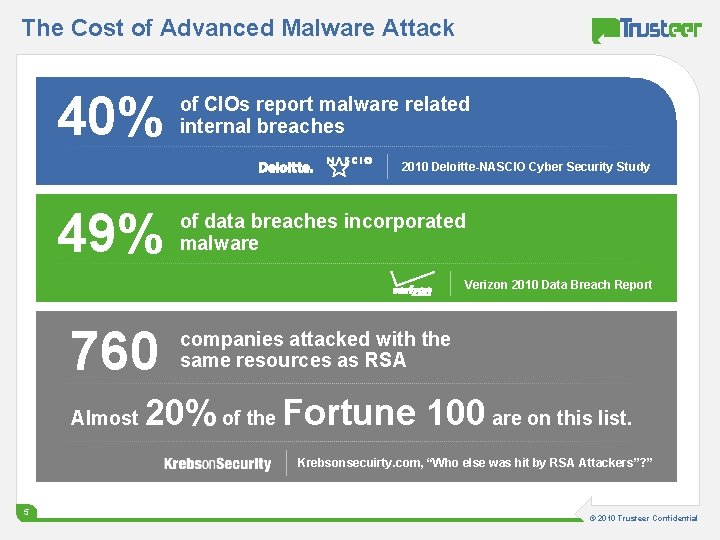
The Cost of Advanced Malware Attack 40% of CIOs report malware related internal breaches 2010 Deloitte-NASCIO Cyber Security Study 49% of data breaches incorporated malware Verizon 2010 Data Breach Report 760 Almost companies attacked with the same resources as RSA 20% of the Fortune 100 are on this list. Krebsonsecuirty. com, “Who else was hit by RSA Attackers”? ” 55 © 2012 2010 Trusteer Confidential
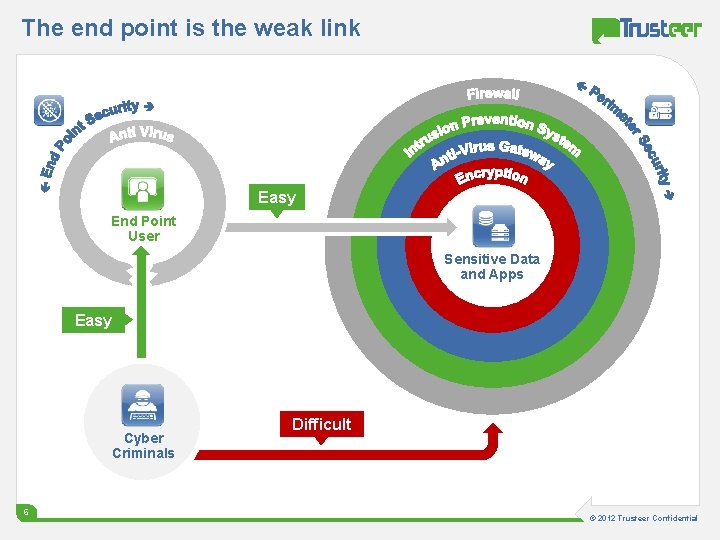
The end point is the weak link Easy End Point User Sensitive Data and Apps Easy Cyber Criminals 66 Difficult © 2012 Trusteer Confidential
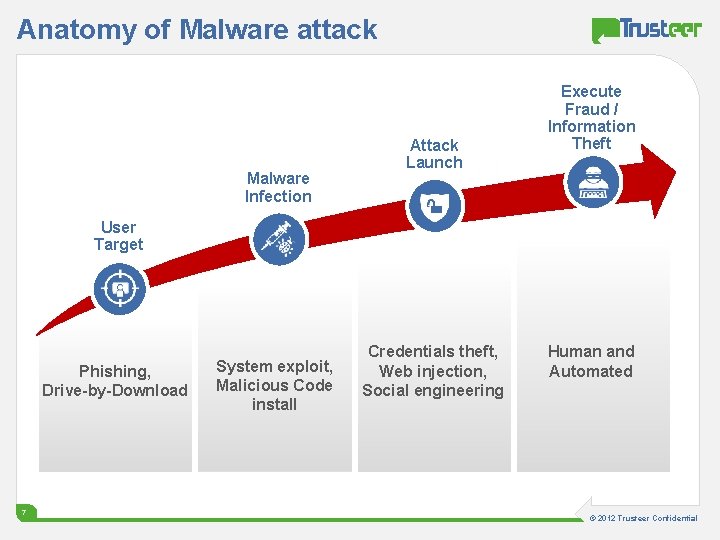
Anatomy of Malware attack Malware Infection Attack Launch Execute Fraud / Information Theft User Target Phishing, Drive-by-Download 7 System exploit, Malicious Code install Credentials theft, Web injection, Social engineering Human and Automated © 2012 Trusteer Confidential
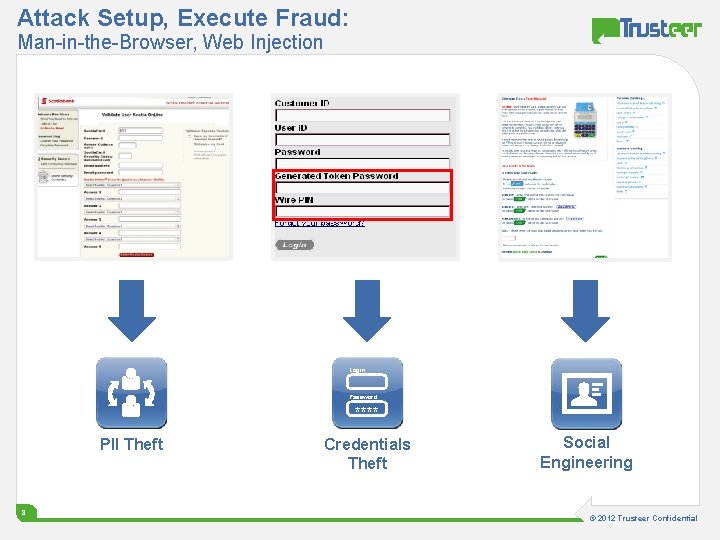
Attack Setup, Execute Fraud: Man-in-the-Browser, Web Injection Login: Password: **** PII Theft 8 Credentials Theft Social Engineering © 2012 Trusteer Confidential
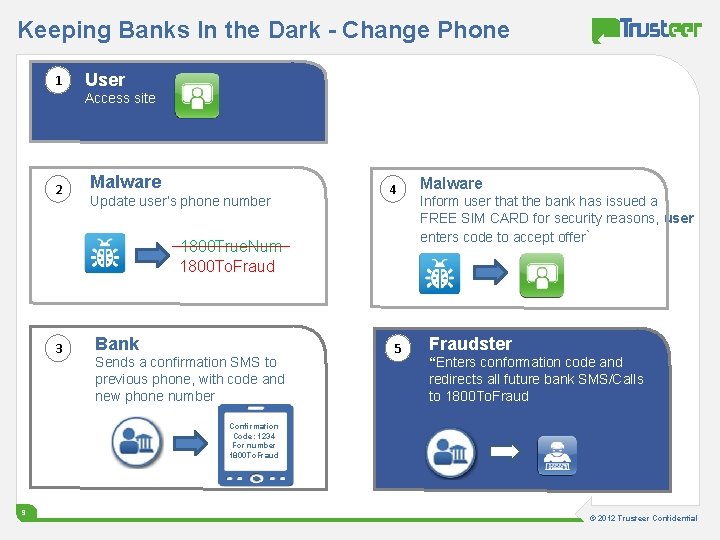
Keeping Banks In the Dark - Change Phone 1 User Access site 2 Malware Update user’s phone number 4 1800 True. Num 1800 To. Fraud 3 Bank Sends a confirmation SMS to previous phone, with code and new phone number 5 Malware Inform user that the bank has issued a FREE SIM CARD for security reasons, user enters code to accept offer` Fraudster “Enters conformation code and redirects all future bank SMS/Calls to 1800 To. Fraud Confirmation Code: 1234 For number 1800 To. Fraud 9 © 2012 Trusteer Confidential
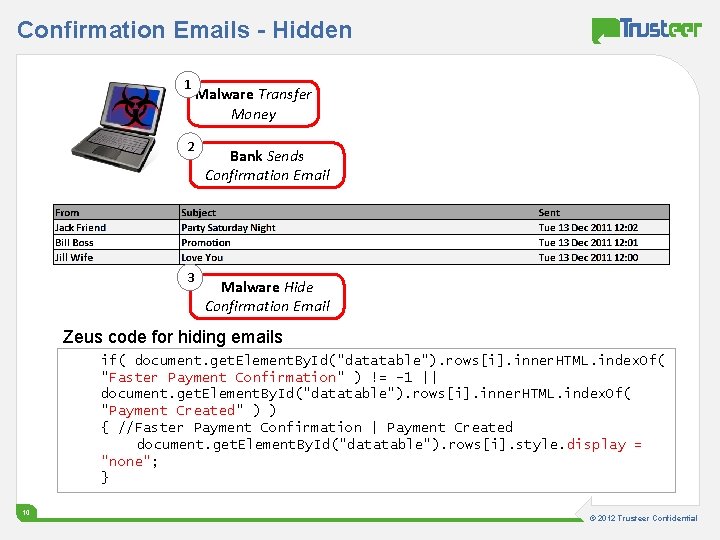
Confirmation Emails - Hidden 1 2 3 Malware Transfer Money Bank Sends Confirmation Email Malware Hide Confirmation Email Zeus code for hiding emails if( document. get. Element. By. Id("datatable"). rows[i]. inner. HTML. index. Of( "Faster Payment Confirmation" ) != -1 || document. get. Element. By. Id("datatable"). rows[i]. inner. HTML. index. Of( "Payment Created" ) ) { //Faster Payment Confirmation | Payment Created document. get. Element. By. Id("datatable"). rows[i]. style. display = "none"; } 10 © 2012 Trusteer Confidential
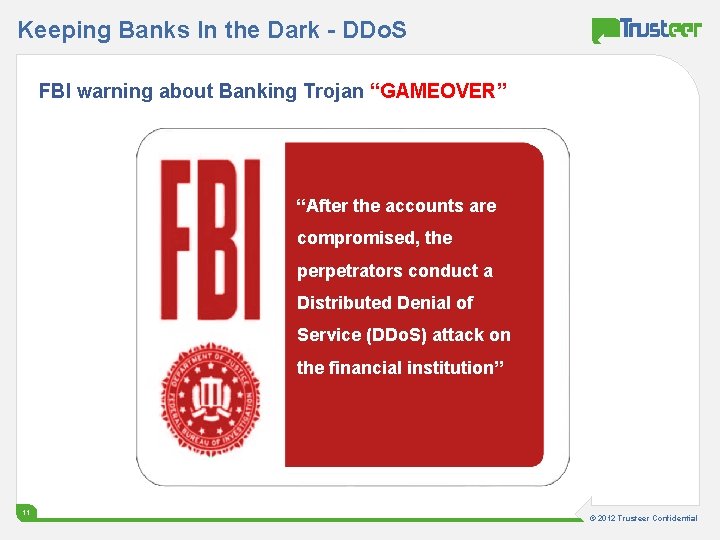
Keeping Banks In the Dark - DDo. S FBI warning about Banking Trojan “GAMEOVER” “After the accounts are compromised, the perpetrators conduct a Distributed Denial of Service (DDo. S) attack on the financial institution” 11 © 2012 Trusteer Confidential
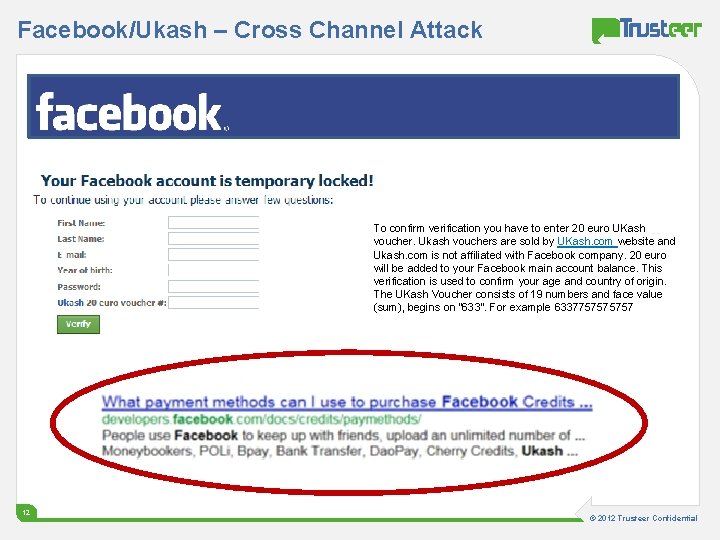
Facebook/Ukash – Cross Channel Attack To confirm verification you have to enter 20 euro UKash voucher. Ukash vouchers are sold by UKash. com website and Ukash. com is not affiliated with Facebook company. 20 euro will be added to your Facebook main account balance. This verification is used to confirm your age and country of origin. The UKash Voucher consists of 19 numbers and face value (sum), begins on “ 633”. For example 633775757 12 © 2012 Trusteer Confidential
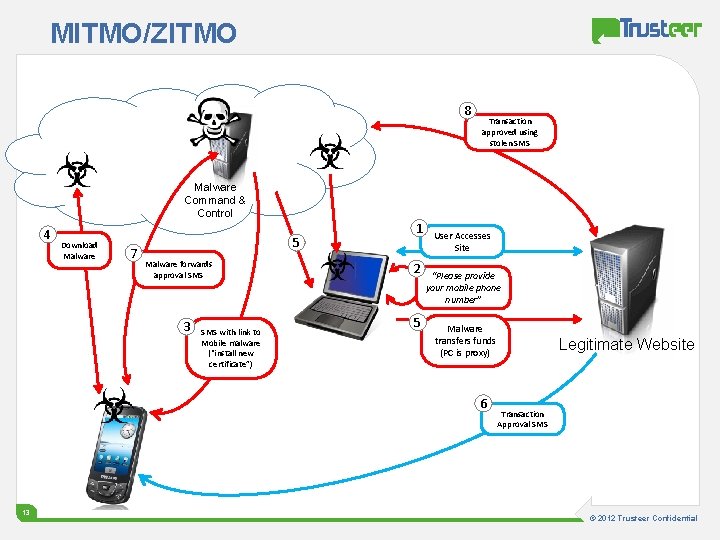
MITMO/ZITMO 8 Transaction approved using stolen SMS Malware Command & Control 4 Download Malware 7 5 Malware forwards approval SMS 3 SMS with link to Mobile malware (“install new certificate”) 1 2 5 User Accesses Site “Please provide your mobile phone number” Malware transfers funds (PC is proxy) 6 13 Legitimate Website Transaction Approval SMS © 2012 Trusteer Confidential
FFIEC Recognizes Malware as the Root Cause of Most Cybercrime Activities “Controls implemented in conformance with the Guidance several years ago have become less effective. . ” “Malware can compromise some of the most robust online authentication techniques” 14 © 2012 Trusteer Confidential
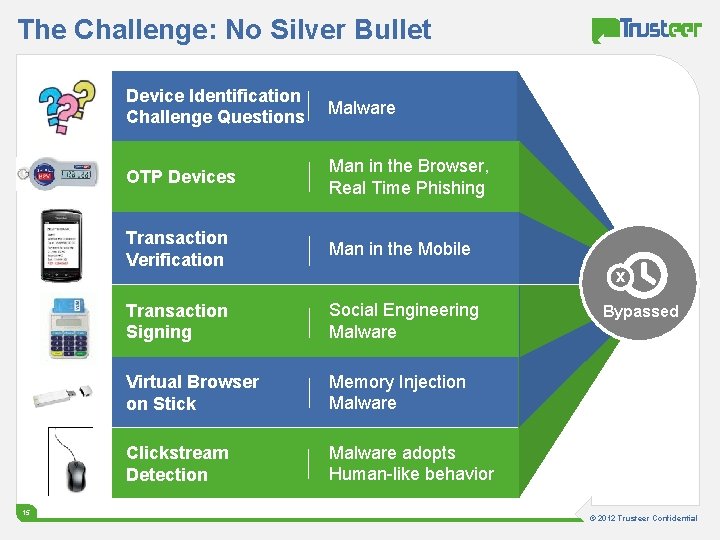
The Challenge: No Silver Bullet 15 Device Identification Challenge Questions Malware OTP Devices Man in the Browser, Real Time Phishing Transaction Verification Man in the Mobile Transaction Signing Social Engineering Malware Virtual Browser on Stick Memory Injection Malware Clickstream Detection Malware adopts Human-like behavior x Bypassed © 2012 Trusteer Confidential
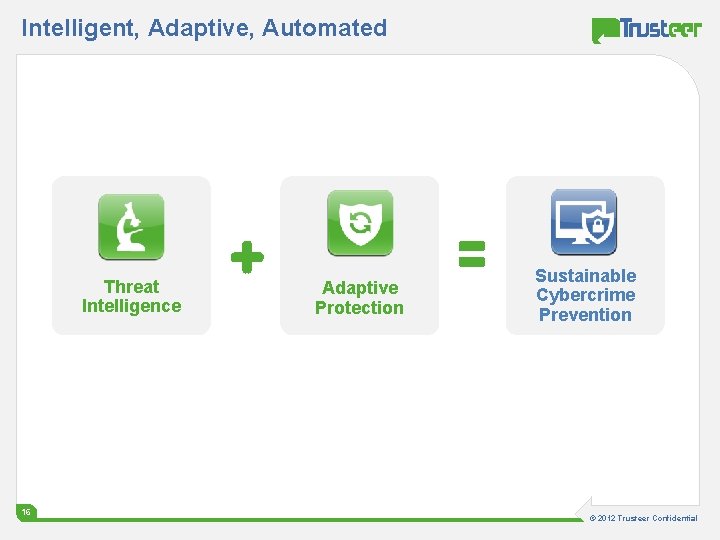
Intelligent, Adaptive, Automated Threat Intelligence 16 16 Adaptive Protection Sustainable Cybercrime Prevention © 2012 Trusteer Confidential
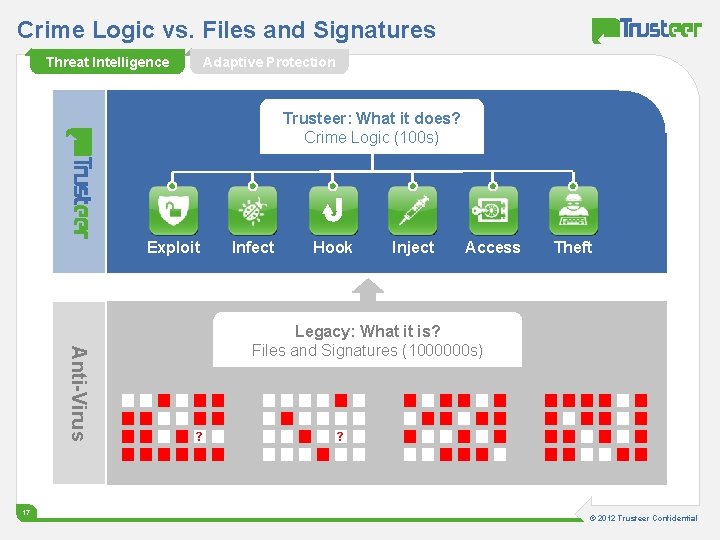
Crime Logic vs. Files and Signatures Threat Intelligence Adaptive Protection Trusteer: What it does? Crime Logic (100 s) Exploit Anti-Virus 17 Infect Hook Inject Access Theft Legacy: What it is? Files and Signatures (1000000 s) ? ? © 2012 Trusteer Confidential
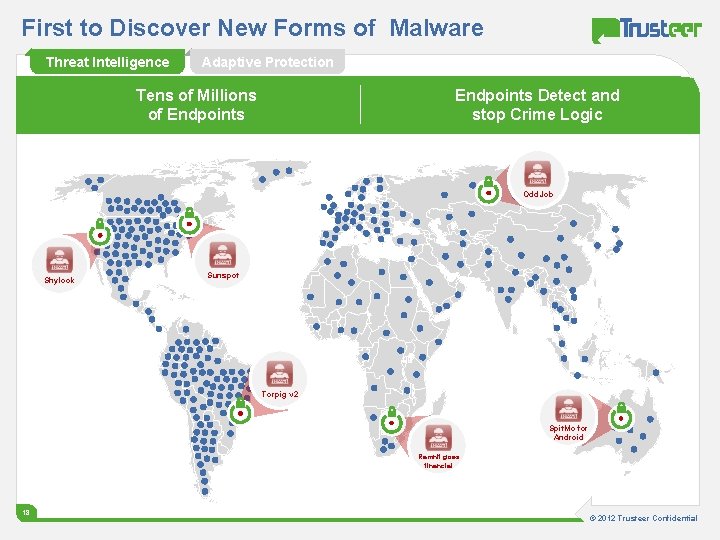
First to Discover New Forms of Malware Threat Intelligence Adaptive Protection Endpoints Detect and stop Crime Logic Tens of Millions of Endpoints Odd. Job Shylock Sunspot Torpig v 2 Spit. Mo for Android Ramnit goes financial 18 © 2012 Trusteer Confidential

Ready, Before the Threat Reaches You Threat Intelligence Adaptive Protection Endpoints Detect and stop Crime Logic Tens of Millions of Endpoints Odd. Job Shylock Sunspot Torpig v 2 Spit. Mo for Android Ramint goes financial 19 © 2012 Trusteer Confidential
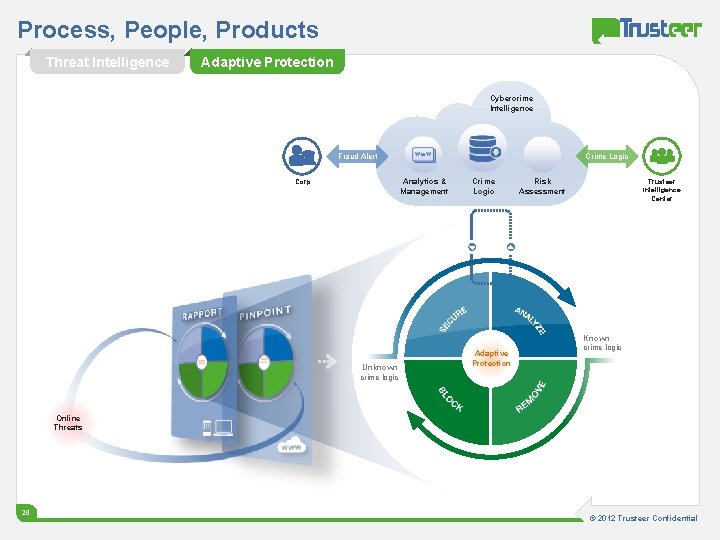
Process, People, Products Threat Intelligence Adaptive Protection Cybercrime Intelligence Fraud Alert Crime Logic Analytics & Management Corp Crime Logic Unknown crime logic Risk Assessment Trusteer Intelligence Center Adaptive Protection Known crime logic Online Threats 20 © 2012 Trusteer Confidential
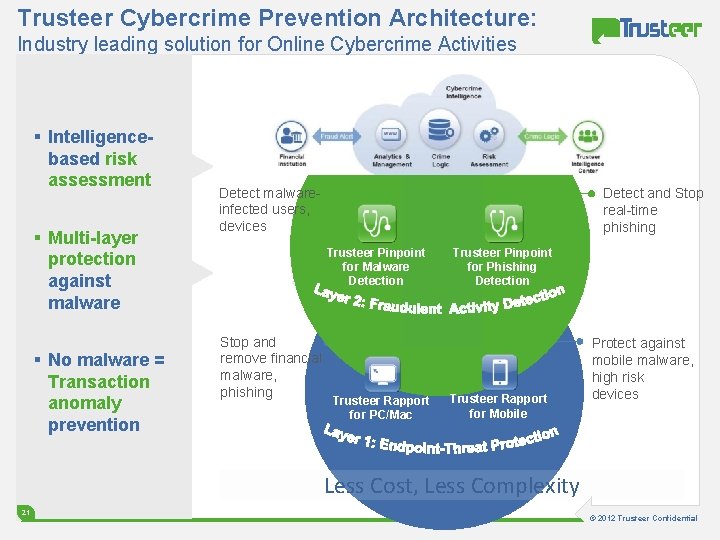
Trusteer Cybercrime Prevention Architecture: Industry leading solution for Online Cybercrime Activities § Intelligencebased risk assessment § Multi-layer protection against malware § No malware = Transaction anomaly prevention Detect malwareinfected users, devices Detect and Stop real-time phishing Trusteer Pinpoint for Malware Detection Stop and remove financial malware, phishing Trusteer Rapport for PC/Mac Trusteer Pinpoint for Phishing Detection Trusteer Rapport for Mobile Protect against mobile malware, high risk devices Less Cost, Less Complexity 21 © 2012 Trusteer Confidential

Thank You 22 © 2012 Trusteer Confidential
- Slides: 22