Nils gentschen Felde Tobias Guggemos Tobias Heider and
Nils gentschen Felde, Tobias Guggemos, Tobias Heider and Dieter Kranzlmüller MNM-Team Ludwig-Maximilians-Universität München Secure Group Key Distribution in Constrained Environments with IKEv 2 2017 IEEE Conference on Dependable and Secure Computing Taipei • Taiwan Secure Group Key Distribution in Constrained Environments with IKEv 2 1
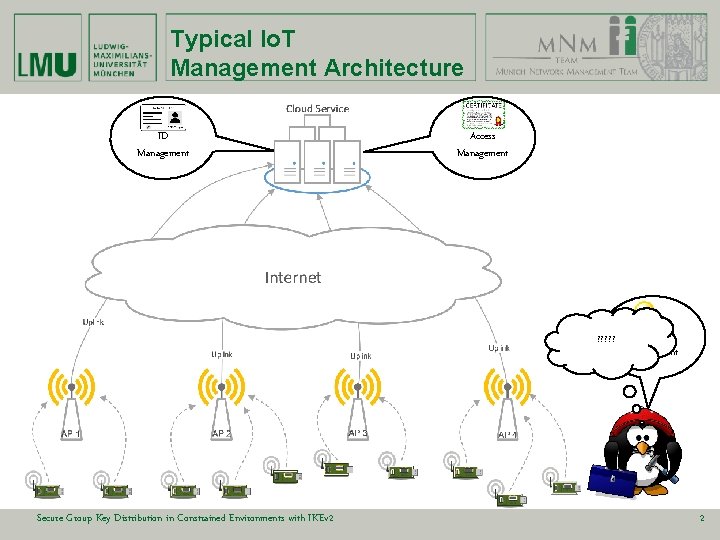
Typical Io. T Management Architecture ID Management Access Management ? ? ? Secure Group Key Distribution in Constrained Environments with IKEv 2 Key Management 2
Question Group key distribution also enables universal key distribution In this work, we focus on the problem of Key Management in the special case of group communication includes most major Io. Trelated communication models Secure Group Key Distribution in Constrained Environments with IKEv 2 Securing groups can help securing Io. T in general 3
Challenge of interoperability Re-using existing solution and make them suitable for constrained environments Secure Group Key Distribution in Constrained Environments with IKEv 2 4
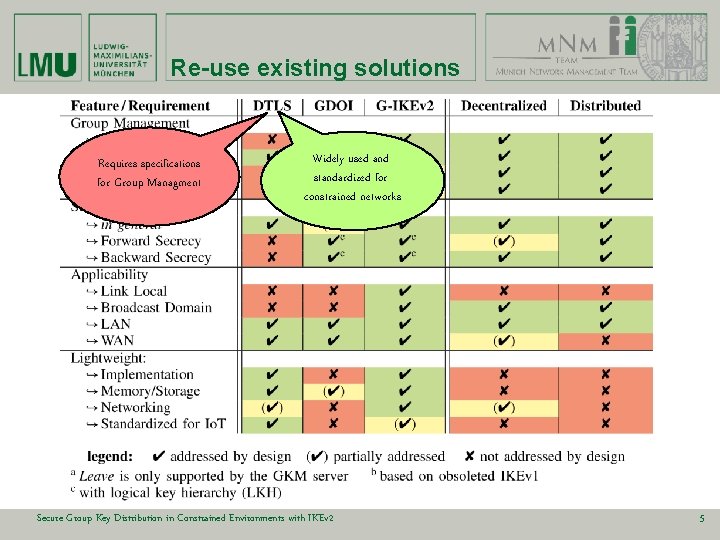
Re-use existing solutions Requires specifications for Group Managment Widely used and standardized for constrained networks Secure Group Key Distribution in Constrained Environments with IKEv 2 5
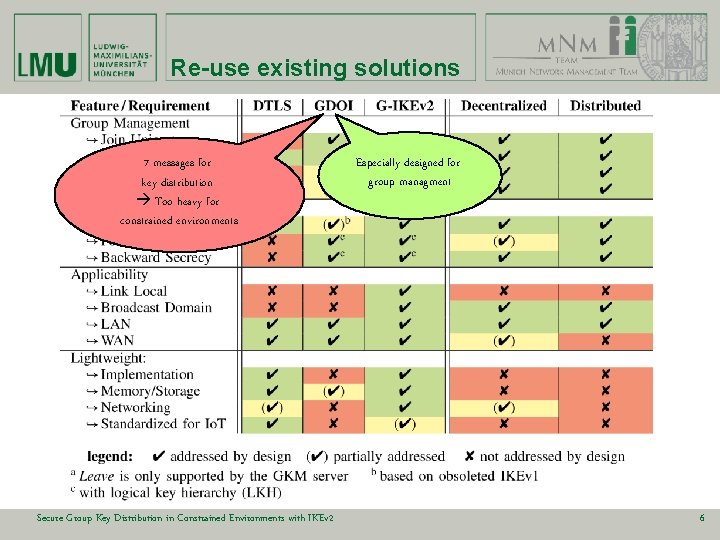
Re-use existing solutions 7 messages for key distribution Too heavy for constrained environments Secure Group Key Distribution in Constrained Environments with IKEv 2 Especially designed for group managment 6
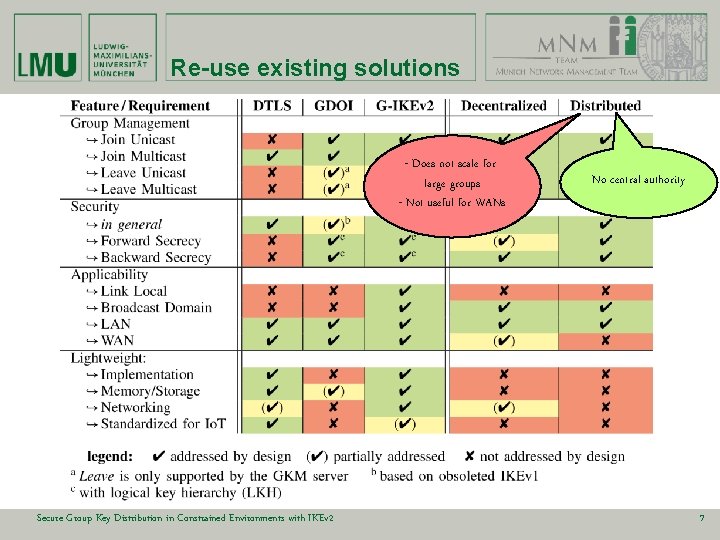
Re-use existing solutions - Does not scale for large groups - Not useful for WANs Secure Group Key Distribution in Constrained Environments with IKEv 2 No central authority 7
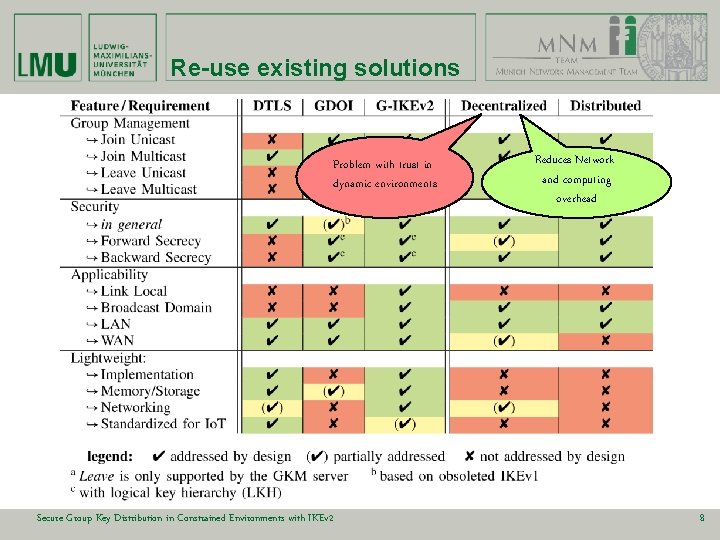
Re-use existing solutions Problem with trust in dynamic environments Secure Group Key Distribution in Constrained Environments with IKEv 2 Reduces Network and computing overhead 8
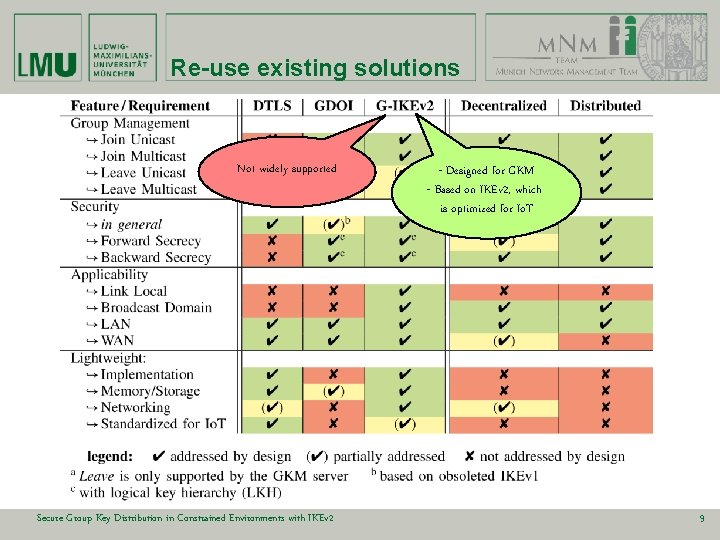
Re-use existing solutions Not widely supported Secure Group Key Distribution in Constrained Environments with IKEv 2 - Designed for GKM - Based on IKEv 2, which is optimized for Io. T 9
Evaluation How does G-IKEv 2 perform on constrained environments Secure Group Key Distribution in Constrained Environments with IKEv 2 10
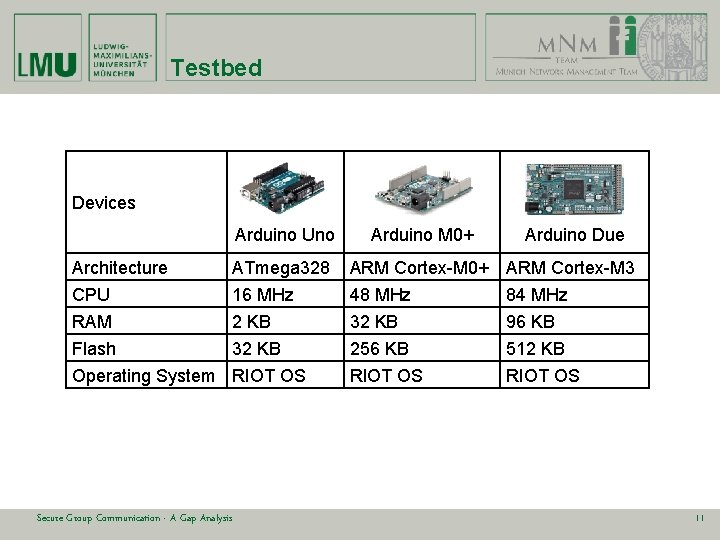
Testbed Devices Arduino Uno Arduino M 0+ Arduino Due Architecture ATmega 328 ARM Cortex-M 0+ ARM Cortex-M 3 CPU RAM Flash Operating System 16 MHz 2 KB 32 KB RIOT OS 48 MHz 32 KB 256 KB RIOT OS Secure Group Communication - A Gap Analysis 84 MHz 96 KB 512 KB RIOT OS 11
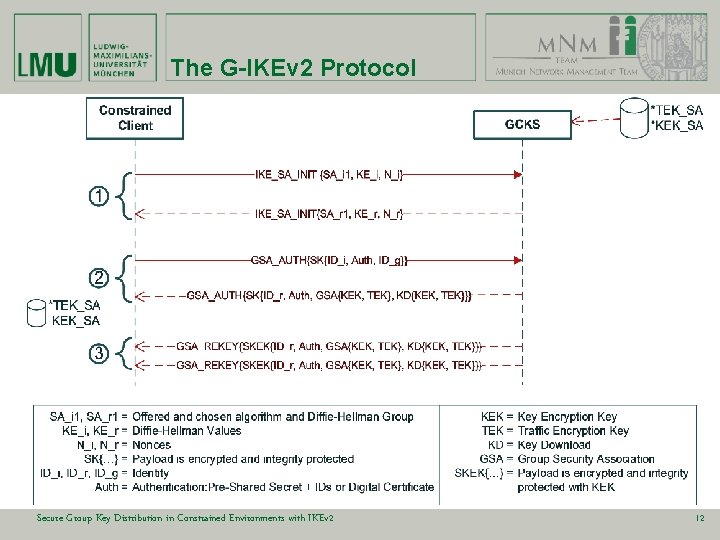
The G-IKEv 2 Protocol Secure Group Key Distribution in Constrained Environments with IKEv 2 12
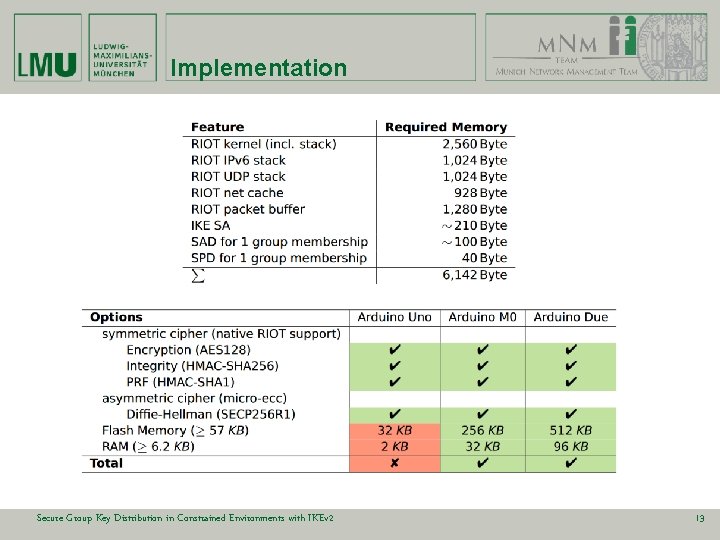
Implementation Secure Group Key Distribution in Constrained Environments with IKEv 2 13
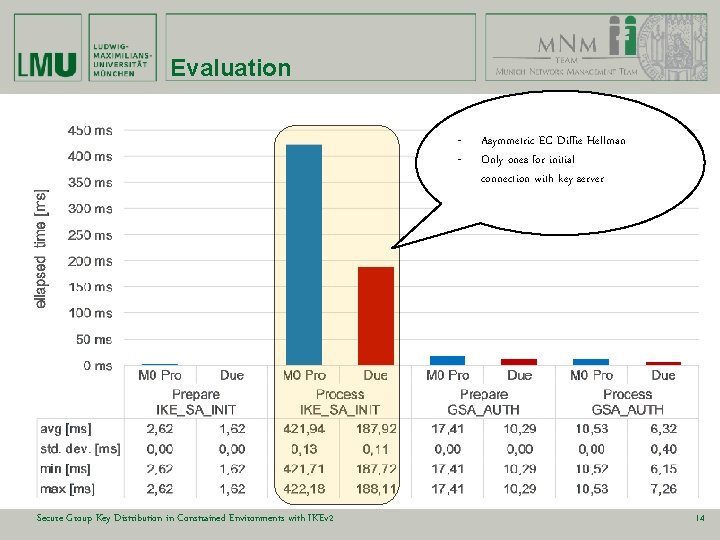
Evaluation - Secure Group Key Distribution in Constrained Environments with IKEv 2 Asymmetric EC Diffie Hellman Only ones for initial connection with key server 14
Conclusion • Group Management will become more important for Io. T • GKM is widely studied, but underrepresented for constrained scenarios • IKEv 2 is already used for Key Distribution in Wireless Networks (e. g. 802. 15. 4) G-IKEv 2 is an interesting option for group key management in Io. T scenarios Secure Group Key Distribution in Constrained Environments with IKEv 2 15
The End Curious? MNM-Team Ludwig-Maximilians-Universität München http: //www. mnm-team. org/projects/embedded Secure Group Key Distribution in Constrained Environments with IKEv 2 16
- Slides: 16