NGinx Warhead Sergey Belov whoami Pentester in Digital
NGinx Warhead Sergey Belov
whoami • Pentester in Digital Security / ERPScan; • Writer (habrahabr. ru, “Xakep”); • CTF Player; • Bug bounty member (Google, Yandex); • bugscollector. com creator.
intro • Very easy • 0$ • Not mentioned in the wild
Part 1/3 NGinx – reverse proxy
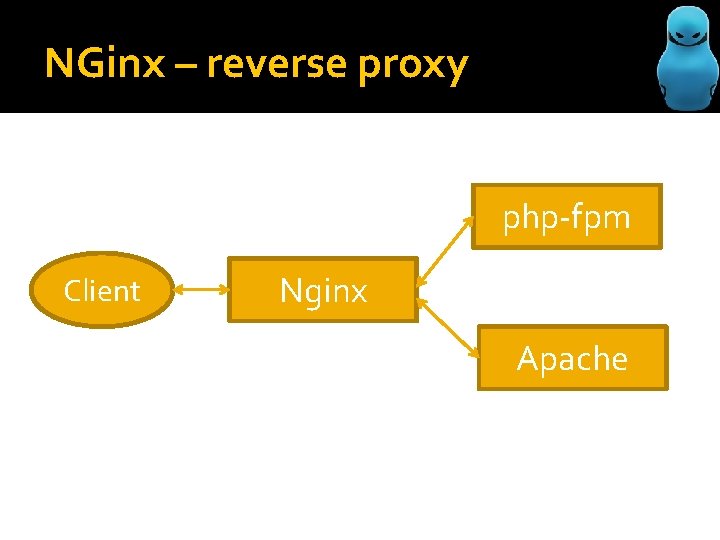
NGinx – reverse proxy php-fpm Client Nginx Apache
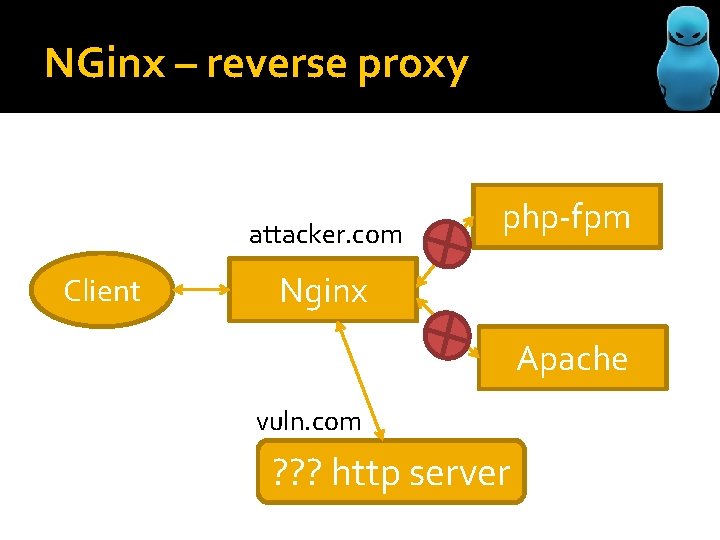
NGinx – reverse proxy attacker. com Client php-fpm Nginx Apache vuln. com ? ? ? http server
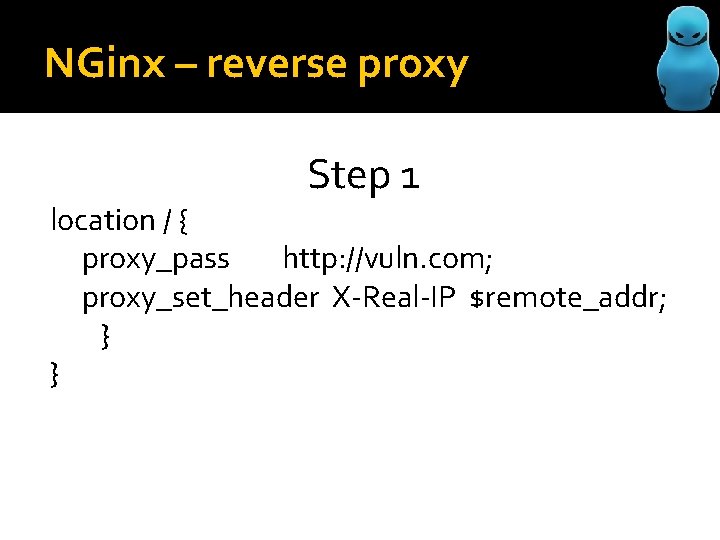
NGinx – reverse proxy Step 1 location / { proxy_pass http: //vuln. com; proxy_set_header X-Real-IP $remote_addr; } }
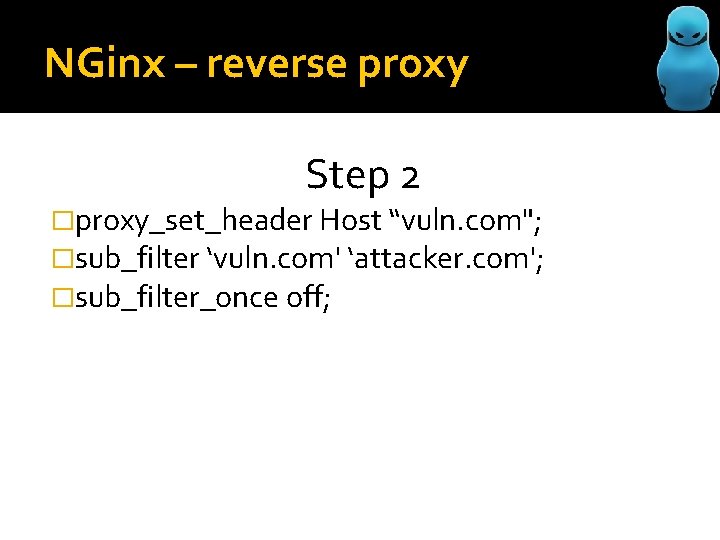
NGinx – reverse proxy Step 2 �proxy_set_header Host “vuln. com"; �sub_filter ‘vuln. com' ‘attacker. com'; �sub_filter_once off;
NGinx – reverse proxy
Part 2/3 Phishing
Phishing NGinx – tool for Mit. M/phishing? �+ Identical design �+ Fully functional working �+ Logging all data (POST/GET) �+ Add custom JS/HTML �- Another domain (DNS poising / router hacking, malware, evil apn config e. t. c. )
Phishing Pentest �Random exploit’s? �Change response data (rights of social networks apps) �Change apps swf -> java (exploit) �? ? ?
Part 3/3 DNS rebinding
DNS rebinding • -Another domain • - Very unstable • + Can attack internal resources
DNS rebinding Internal, not external!
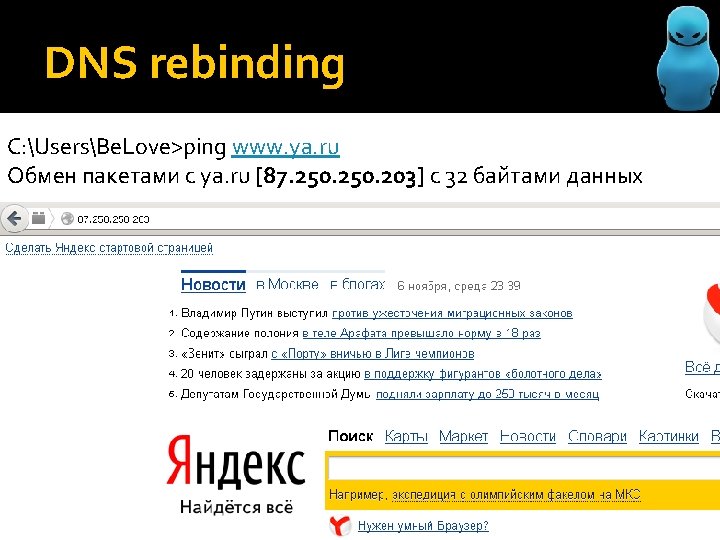
DNS rebinding C: UsersBe. Love>ping www. ya. ru Обмен пакетами с ya. ru [87. 250. 203] с 32 байтами данных
DNS rebinding Remove it from: • Pentester’s reports • Most famous security scanners

Thanks! demo: http: //zn. sergeybelove. ru http: //twitter. com/sergeybelove
- Slides: 18