New Modular Authenication Architecture in Apache 2 2
- Slides: 27
New Modular Authenication Architecture in Apache 2. 2 Brad Nicholes Senior Software Engineer, Novell, Inc. Member, Apache Software Foundation bnicholes@novell. com
Agenda • Introduction • Advantages • New Modules • Difference between Apache 2. 0 and 2. 2 • Configuration Authentication and Authorization • Mix and match providers and methods • • Mod_authn_alias • Conclusion 2 © 9/15/2020 2005 Novell Inc
Introduction Terms / Authentication Elements: • Authentication Type – Type of encryption used during transport of the authentication credentials (Basic or Digest) • Authentication Method/Provider - Process by which a user is verified to be who they say they are • Authorization - Process by which authenticated users are granted or denied access based on specific criteria Previous to Apache 2. 2, every authentication module had to implement all three elements • Choosing an Auth. Type limited which authentication and authorization methods could be used • Potential for inconsistencies across authentication modules Note: Pay close attention to the words Authentication vs. Authorization through out the presentation 3 © 9/15/2020 2005 Novell Inc
What Are The Advantages? • Flexibility: Ability to choose between Authentication Type vs. Authentication Method vs. Authorization Method • Ability to use multiple different authorization methods • Mixing and matching is not a problem • • Consistency: Authorization methods are guaranteed to work the same no matter which authentication method is chosen • Ability to use the same authentication and authorization methods for all authentication types • • Reuse: Implementing a new authentication provider module does not require the reimplementation or duplication of existing authorization methods • The inverse of the above statement is also true • Ability to create your own custom authentication providers and reuse them throughout your configuration • 4 © 9/15/2020 2005 Novell Inc
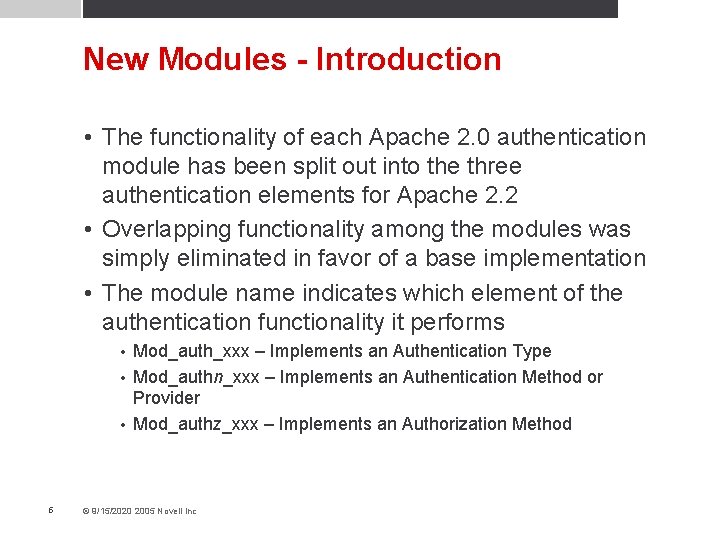
New Modules - Introduction • The functionality of each Apache 2. 0 authentication module has been split out into the three authentication elements for Apache 2. 2 • Overlapping functionality among the modules was simply eliminated in favor of a base implementation • The module name indicates which element of the authentication functionality it performs Mod_auth_xxx – Implements an Authentication Type • Mod_authn_xxx – Implements an Authentication Method or Provider • Mod_authz_xxx – Implements an Authorization Method • 5 © 9/15/2020 2005 Novell Inc
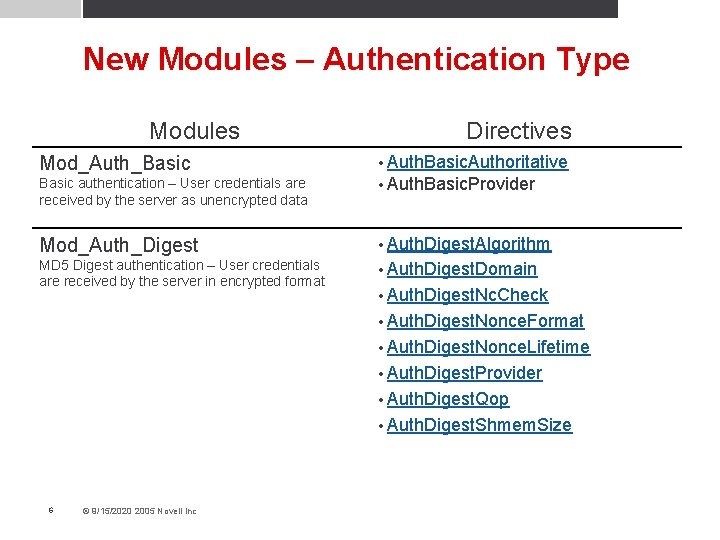
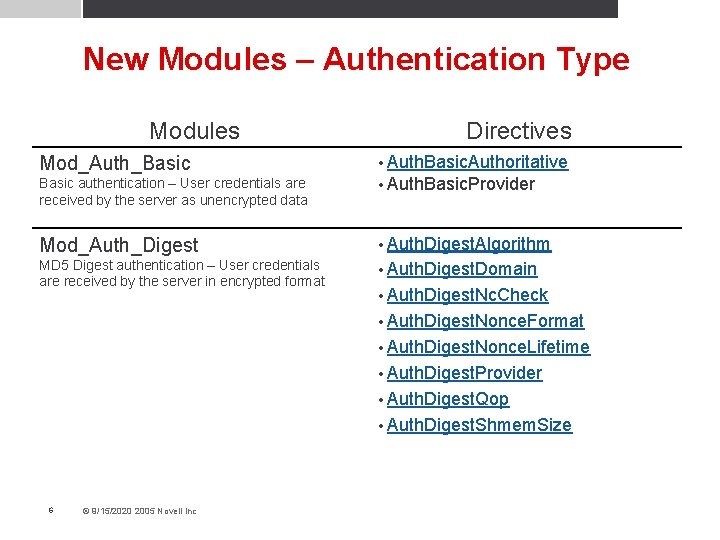
New Modules – Authentication Type Modules Mod_Auth_Basic authentication – User credentials are received by the server as unencrypted data Directives • Auth. Basic. Authoritative • Auth. Basic. Provider Mod_Auth_Digest • Auth. Digest. Algorithm MD 5 Digest authentication – User credentials are received by the server in encrypted format • Auth. Digest. Domain • Auth. Digest. Nc. Check • Auth. Digest. Nonce. Format • Auth. Digest. Nonce. Lifetime • Auth. Digest. Provider • Auth. Digest. Qop • Auth. Digest. Shmem. Size 6 © 9/15/2020 2005 Novell Inc
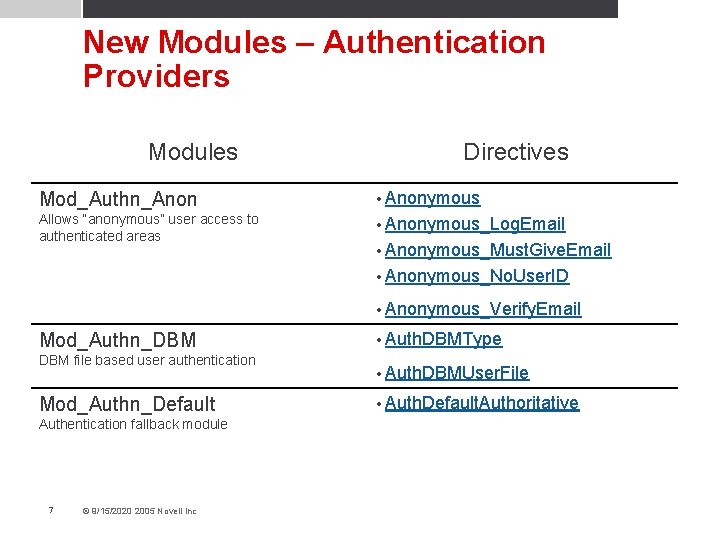
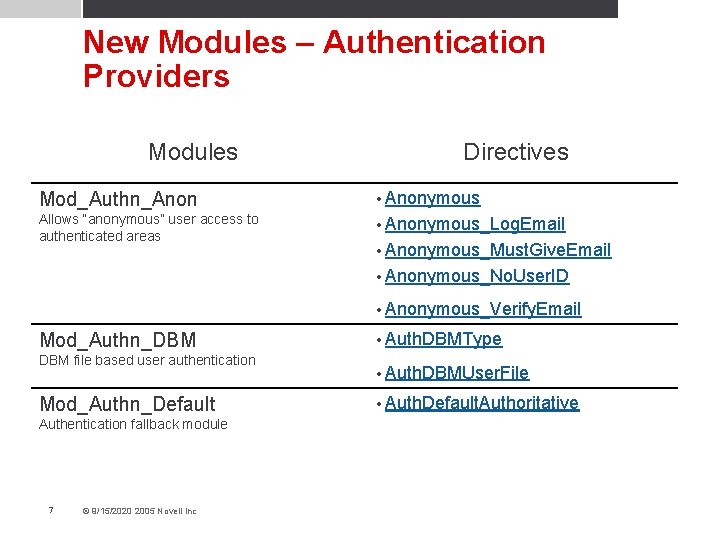
New Modules – Authentication Providers Modules Directives Mod_Authn_Anon • Anonymous Allows “anonymous” user access to authenticated areas • Anonymous_Log. Email • Anonymous_Must. Give. Email • Anonymous_No. User. ID • Anonymous_Verify. Email Mod_Authn_DBM file based user authentication Mod_Authn_Default Authentication fallback module 7 © 9/15/2020 2005 Novell Inc • Auth. DBMType • Auth. DBMUser. File • Auth. Default. Authoritative
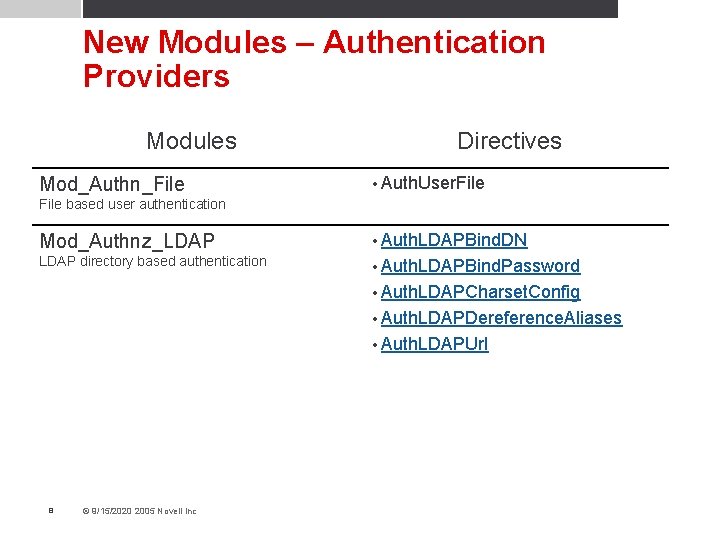
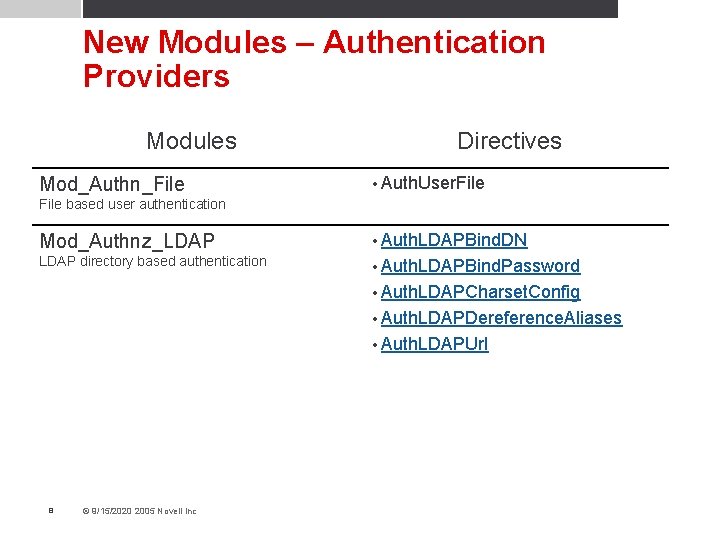
New Modules – Authentication Providers Modules Mod_Authn_File Directives • Auth. User. File based user authentication Mod_Authnz_LDAP • Auth. LDAPBind. DN LDAP directory based authentication • Auth. LDAPBind. Password • Auth. LDAPCharset. Config • Auth. LDAPDereference. Aliases • Auth. LDAPUrl 8 © 9/15/2020 2005 Novell Inc
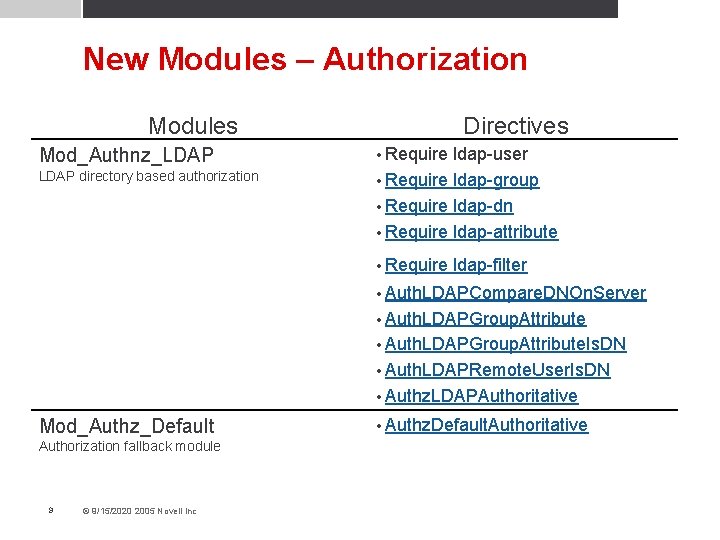
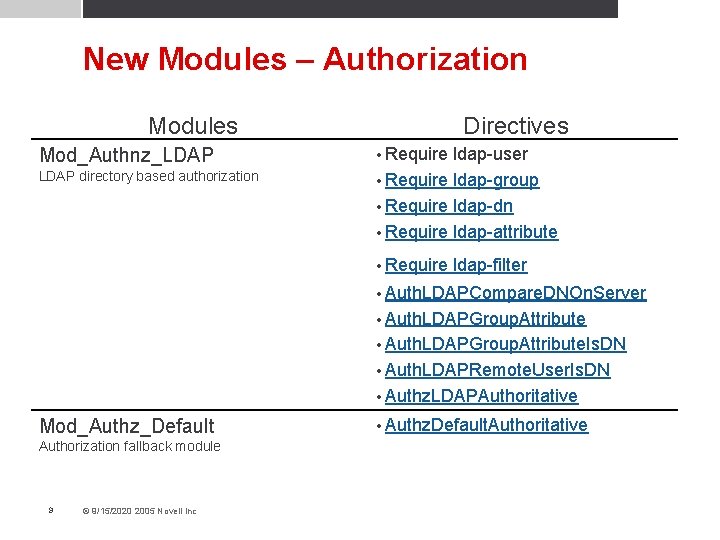
New Modules – Authorization Modules Mod_Authnz_LDAP directory based authorization Directives • Require ldap-user • Require ldap-group • Require ldap-dn • Require ldap-attribute • Require ldap-filter • Auth. LDAPCompare. DNOn. Server • Auth. LDAPGroup. Attribute. Is. DN • Auth. LDAPRemote. User. Is. DN • Authz. LDAPAuthoritative Mod_Authz_Default Authorization fallback module 9 © 9/15/2020 2005 Novell Inc • Authz. Default. Authoritative
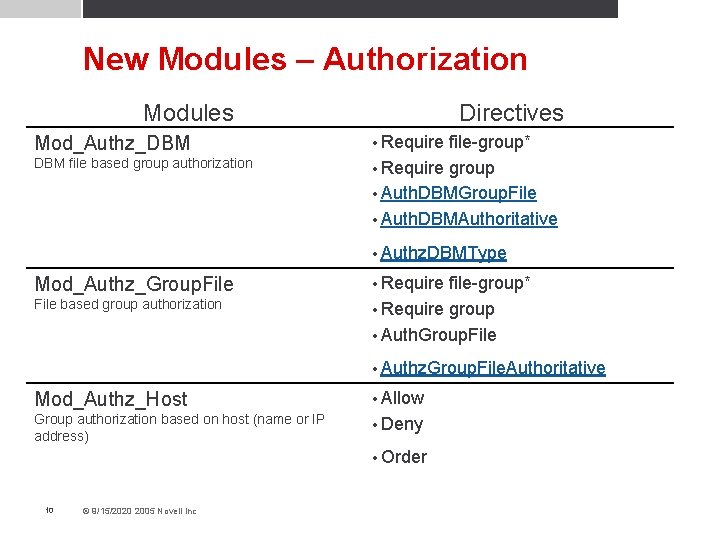
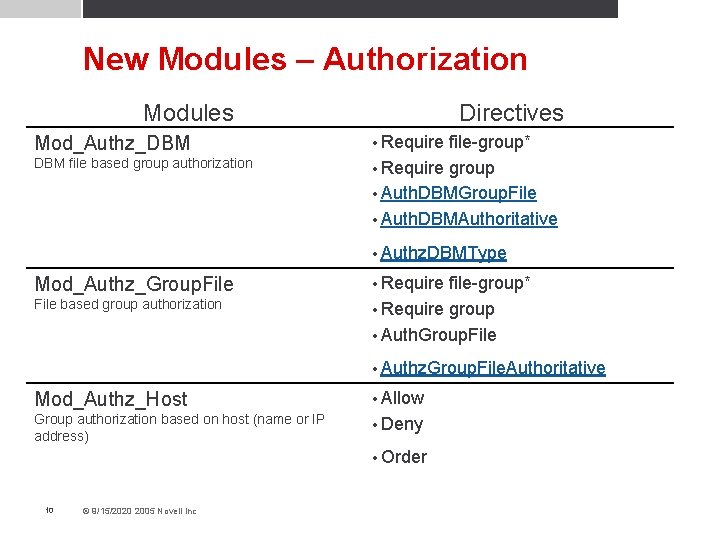
New Modules – Authorization Modules Mod_Authz_DBM file based group authorization Directives • Require file-group* • Require group • Auth. DBMGroup. File • Auth. DBMAuthoritative • Authz. DBMType Mod_Authz_Group. File based group authorization • Require file-group* • Require group • Auth. Group. File • Authz. Group. File. Authoritative Mod_Authz_Host • Allow Group authorization based on host (name or IP address) • Deny • Order 10 © 9/15/2020 2005 Novell Inc
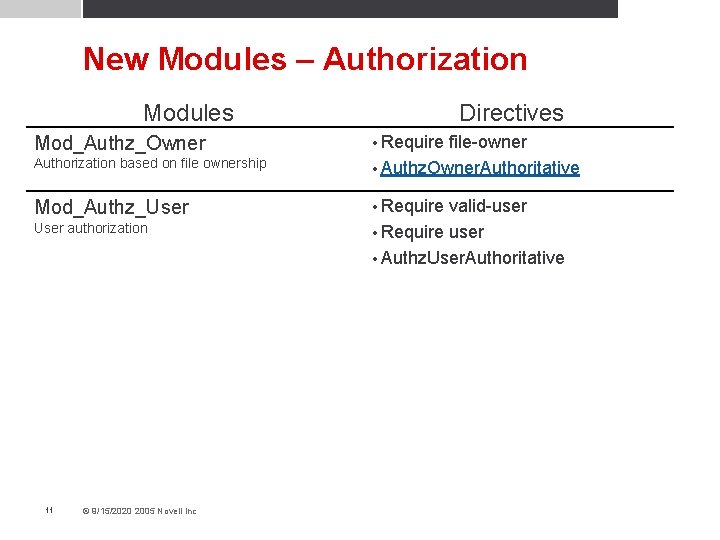
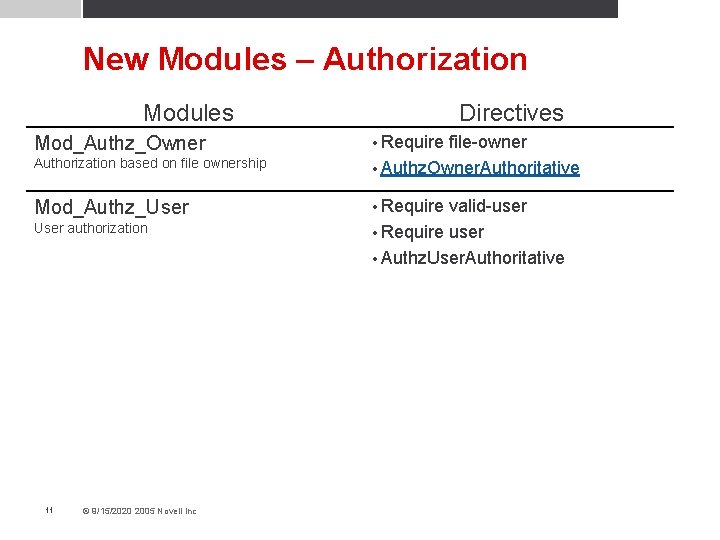
New Modules – Authorization Modules Directives Authorization based on file ownership file-owner • Authz. Owner. Authoritative Mod_Authz_User • Require Mod_Authz_Owner User authorization 11 © 9/15/2020 2005 Novell Inc • Require valid-user • Require user • Authz. User. Authoritative
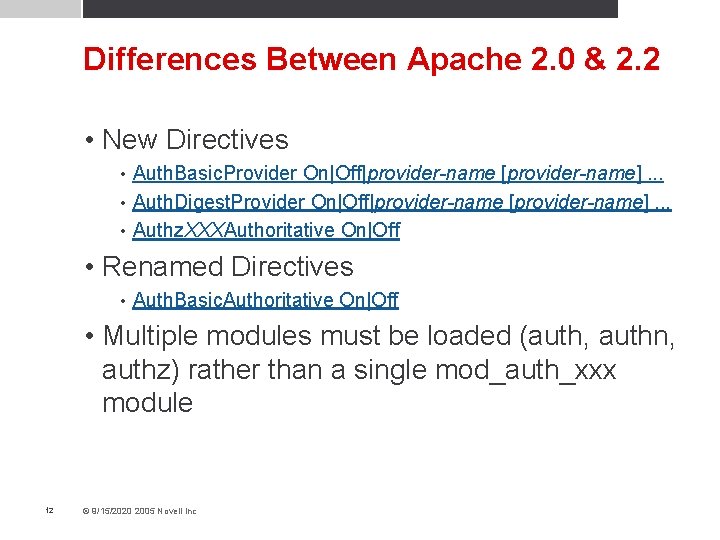
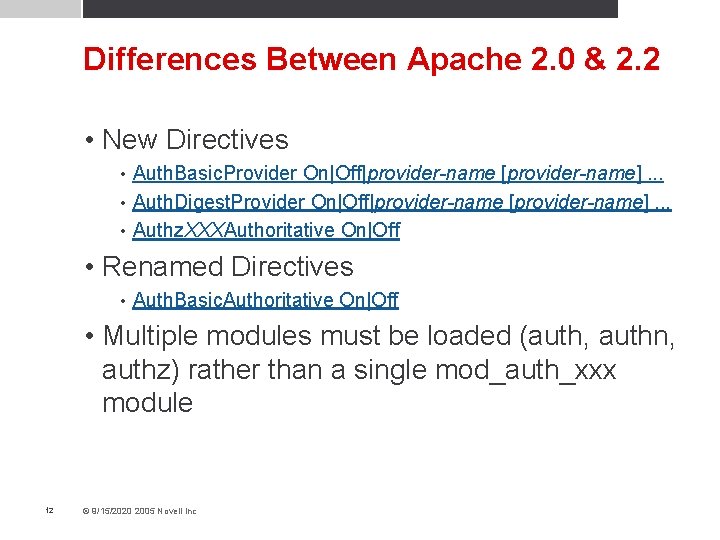
Differences Between Apache 2. 0 & 2. 2 • New Directives Auth. Basic. Provider On|Off|provider-name [provider-name]. . . • Auth. Digest. Provider On|Off|provider-name [provider-name]. . . • Authz. XXXAuthoritative On|Off • • Renamed Directives • Auth. Basic. Authoritative On|Off • Multiple modules must be loaded (auth, authn, authz) rather than a single mod_auth_xxx module 12 © 9/15/2020 2005 Novell Inc
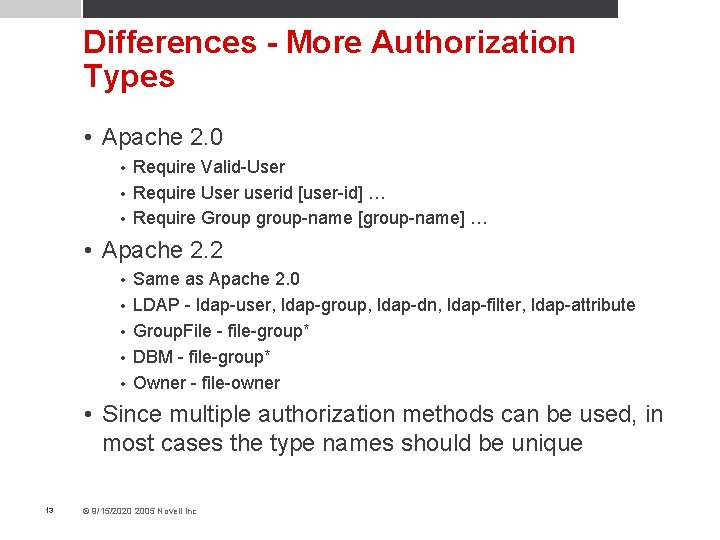
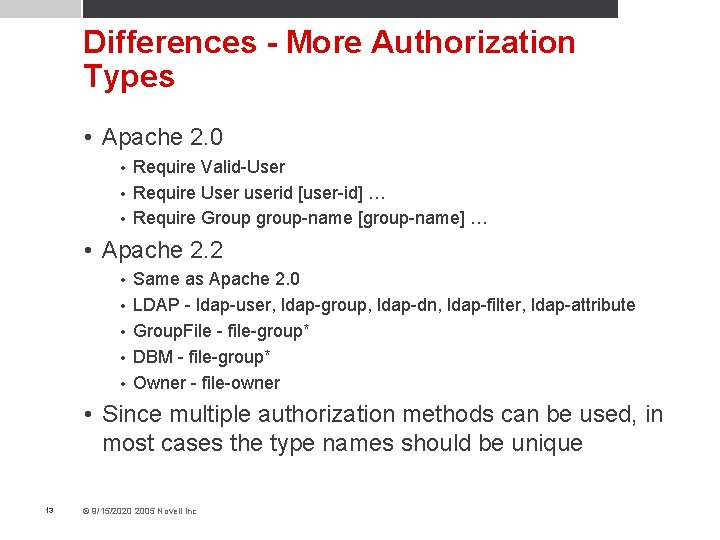
Differences - More Authorization Types • Apache 2. 0 Require Valid-User • Require User userid [user-id] … • Require Group group-name [group-name] … • • Apache 2. 2 • • • Same as Apache 2. 0 LDAP - ldap-user, ldap-group, ldap-dn, ldap-filter, ldap-attribute Group. File - file-group* DBM - file-group* Owner - file-owner • Since multiple authorization methods can be used, in most cases the type names should be unique 13 © 9/15/2020 2005 Novell Inc
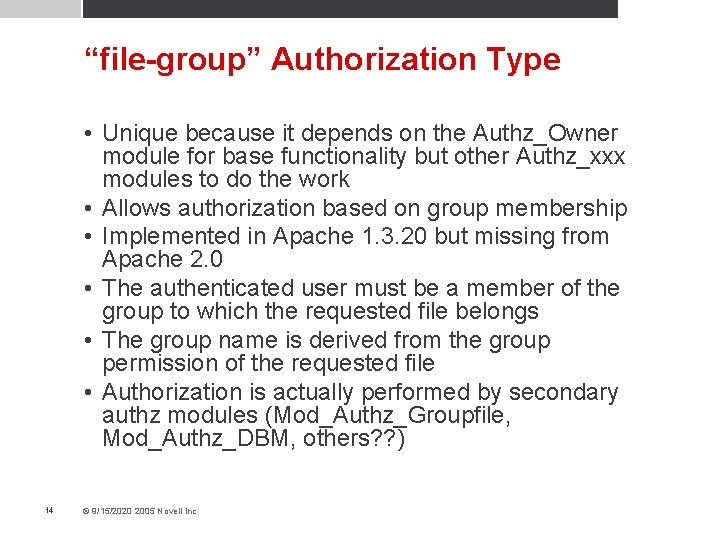
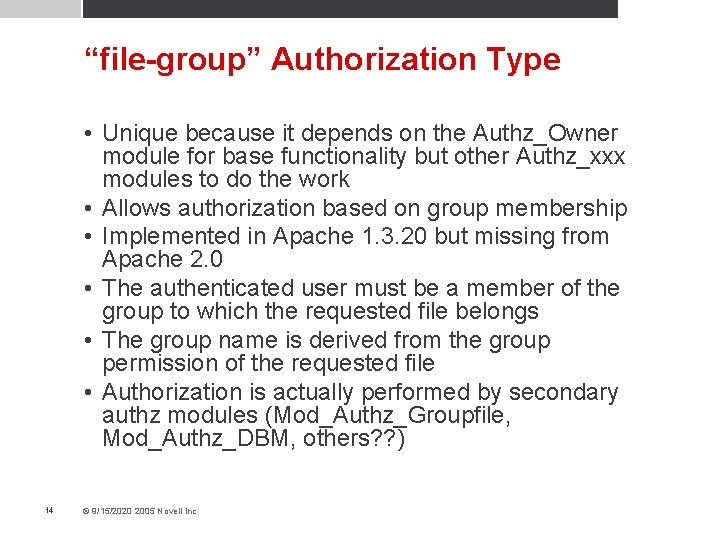
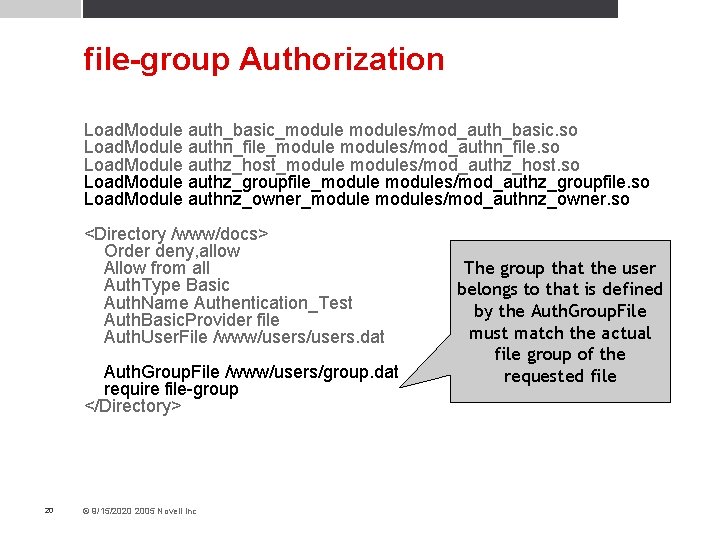
“file-group” Authorization Type • Unique because it depends on the Authz_Owner module for base functionality but other Authz_xxx modules to do the work • Allows authorization based on group membership • Implemented in Apache 1. 3. 20 but missing from Apache 2. 0 • The authenticated user must be a member of the group to which the requested file belongs • The group name is derived from the group permission of the requested file • Authorization is actually performed by secondary authz modules (Mod_Authz_Groupfile, Mod_Authz_DBM, others? ? ) 14 © 9/15/2020 2005 Novell Inc
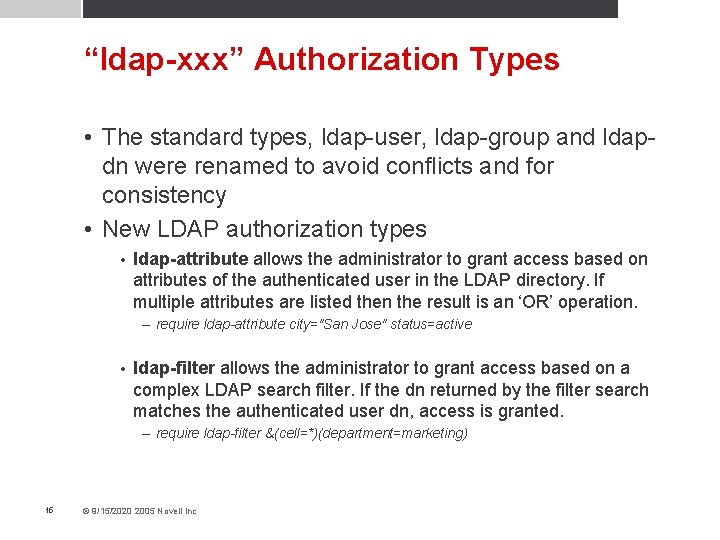
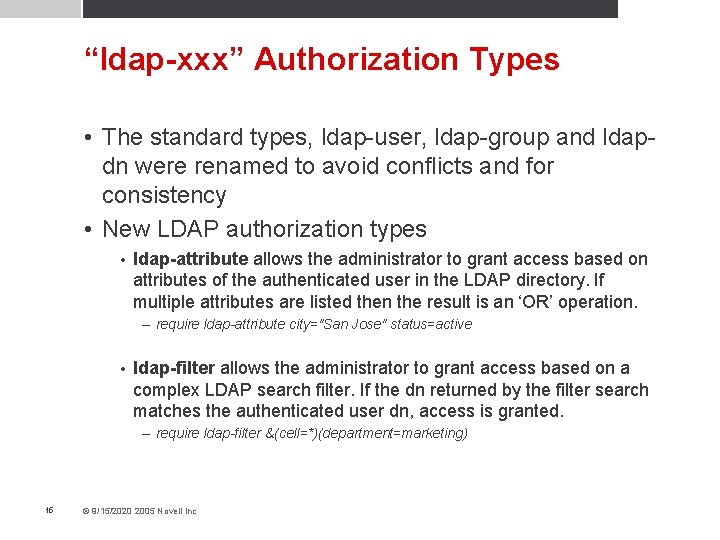
“ldap-xxx” Authorization Types • The standard types, ldap-user, ldap-group and ldapdn were renamed to avoid conflicts and for consistency • New LDAP authorization types • ldap-attribute allows the administrator to grant access based on attributes of the authenticated user in the LDAP directory. If multiple attributes are listed then the result is an ‘OR’ operation. – require ldap-attribute city="San Jose" status=active • ldap-filter allows the administrator to grant access based on a complex LDAP search filter. If the dn returned by the filter search matches the authenticated user dn, access is granted. – require ldap-filter &(cell=*)(department=marketing) 15 © 9/15/2020 2005 Novell Inc
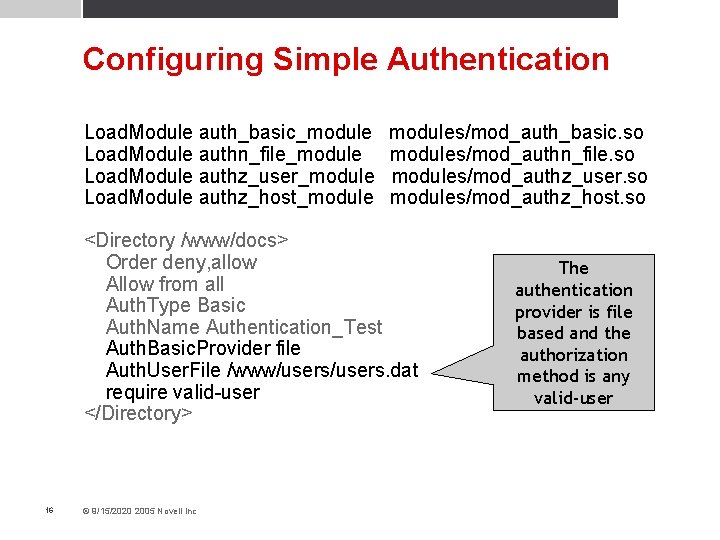
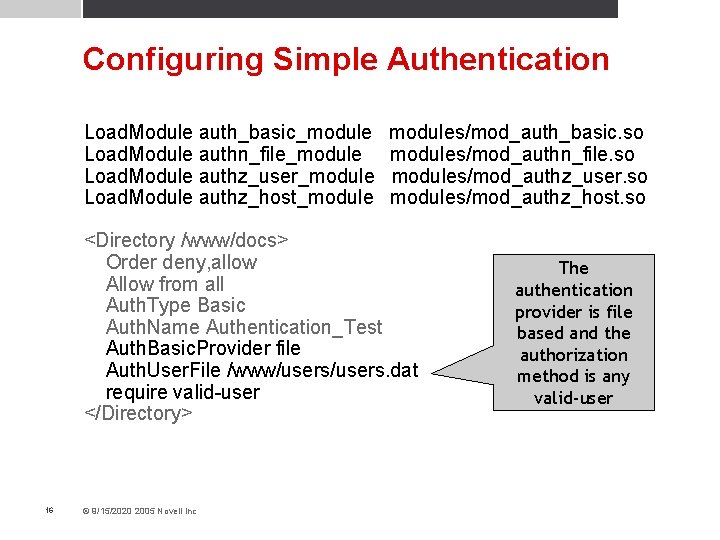
Configuring Simple Authentication Load. Module auth_basic_module Load. Module authn_file_module Load. Module authz_user_module Load. Module authz_host_modules/mod_auth_basic. so modules/mod_authn_file. so modules/mod_authz_user. so modules/mod_authz_host. so <Directory /www/docs> Order deny, allow Allow from all Auth. Type Basic Auth. Name Authentication_Test Auth. Basic. Provider file Auth. User. File /www/users. dat require valid-user </Directory> 16 © 9/15/2020 2005 Novell Inc The authentication provider is file based and the authorization method is any valid-user
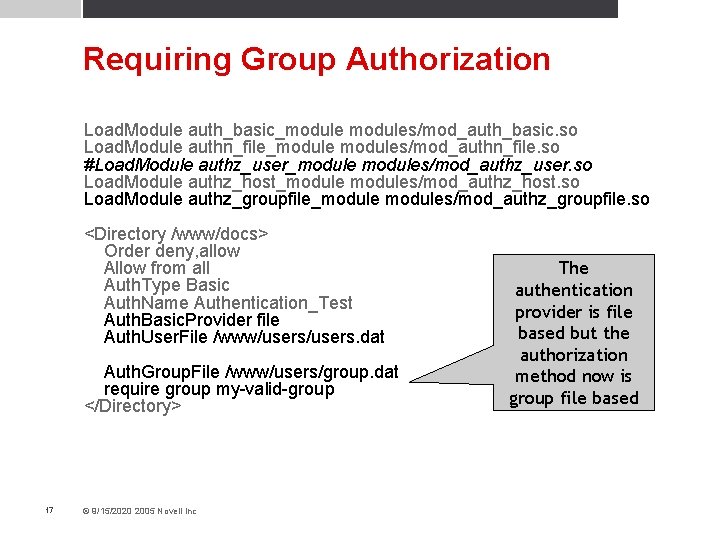
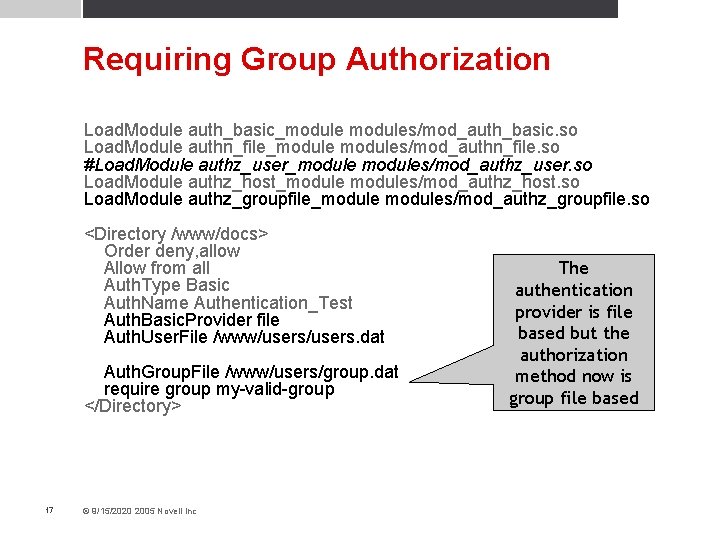
Requiring Group Authorization Load. Module auth_basic_modules/mod_auth_basic. so Load. Module authn_file_modules/mod_authn_file. so #Load. Module authz_user_modules/mod_authz_user. so Load. Module authz_host_modules/mod_authz_host. so Load. Module authz_groupfile_modules/mod_authz_groupfile. so <Directory /www/docs> Order deny, allow Allow from all Auth. Type Basic Auth. Name Authentication_Test Auth. Basic. Provider file Auth. User. File /www/users. dat Auth. Group. File /www/users/group. dat require group my-valid-group </Directory> 17 © 9/15/2020 2005 Novell Inc The authentication provider is file based but the authorization method now is group file based
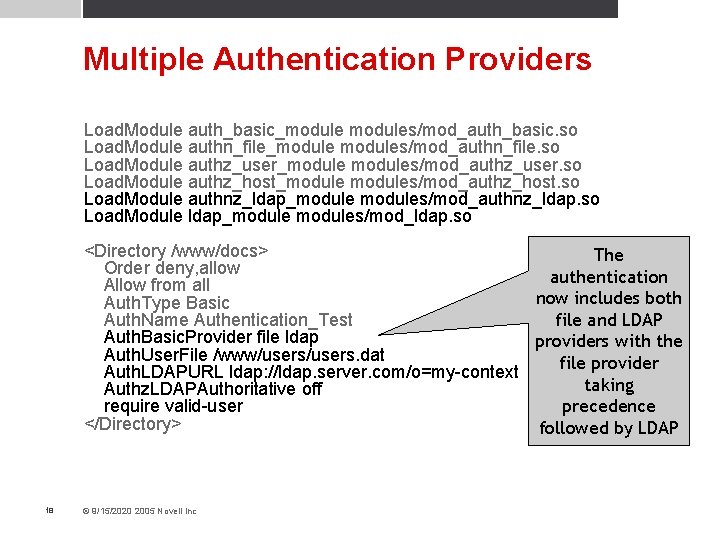
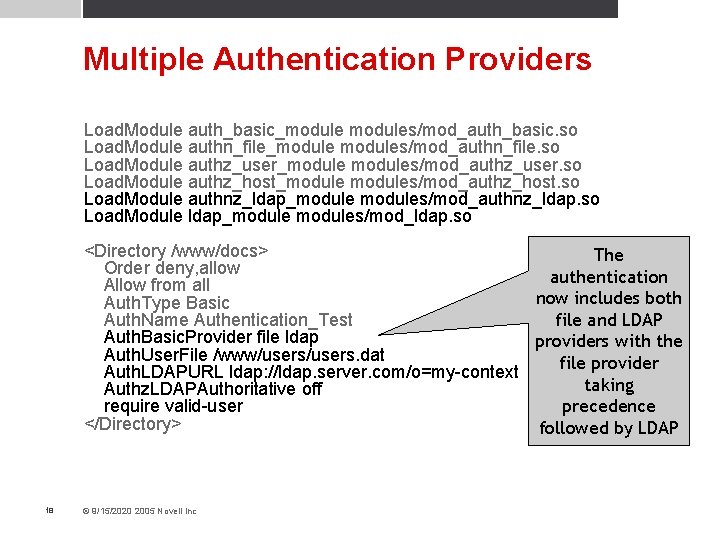
Multiple Authentication Providers Load. Module auth_basic_modules/mod_auth_basic. so Load. Module authn_file_modules/mod_authn_file. so Load. Module authz_user_modules/mod_authz_user. so Load. Module authz_host_modules/mod_authz_host. so Load. Module authnz_ldap_modules/mod_authnz_ldap. so Load. Module ldap_modules/mod_ldap. so <Directory /www/docs> The Order deny, allow authentication Allow from all now includes both Auth. Type Basic file and LDAP Auth. Name Authentication_Test Auth. Basic. Provider file ldap providers with the Auth. User. File /www/users. dat file provider Auth. LDAPURL ldap: //ldap. server. com/o=my-context taking Authz. LDAPAuthoritative off precedence require valid-user </Directory> followed by LDAP 18 © 9/15/2020 2005 Novell Inc
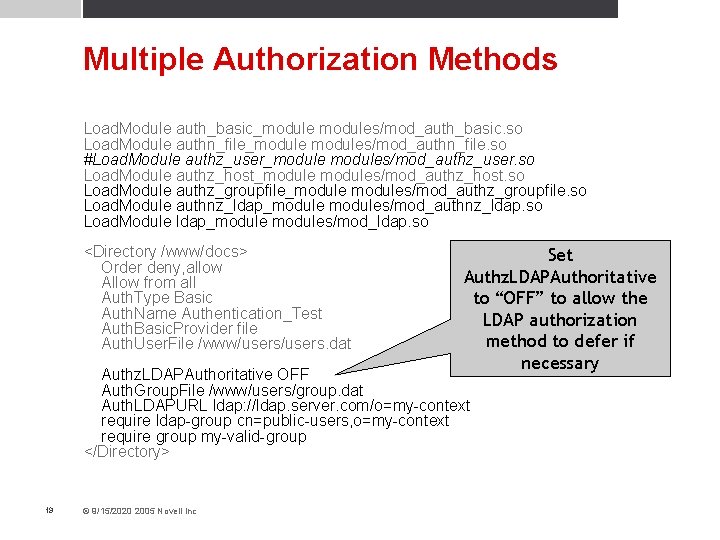
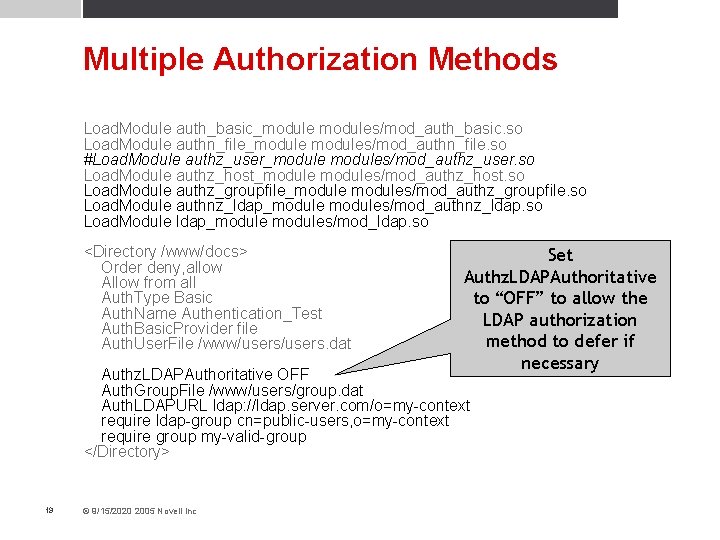
Multiple Authorization Methods Load. Module auth_basic_modules/mod_auth_basic. so Load. Module authn_file_modules/mod_authn_file. so #Load. Module authz_user_modules/mod_authz_user. so Load. Module authz_host_modules/mod_authz_host. so Load. Module authz_groupfile_modules/mod_authz_groupfile. so Load. Module authnz_ldap_modules/mod_authnz_ldap. so Load. Module ldap_modules/mod_ldap. so <Directory /www/docs> Order deny, allow Allow from all Auth. Type Basic Auth. Name Authentication_Test Auth. Basic. Provider file Auth. User. File /www/users. dat Set Authz. LDAPAuthoritative to “OFF” to allow the LDAP authorization method to defer if necessary Authz. LDAPAuthoritative OFF Auth. Group. File /www/users/group. dat Auth. LDAPURL ldap: //ldap. server. com/o=my-context require ldap-group cn=public-users, o=my-context require group my-valid-group </Directory> 19 © 9/15/2020 2005 Novell Inc
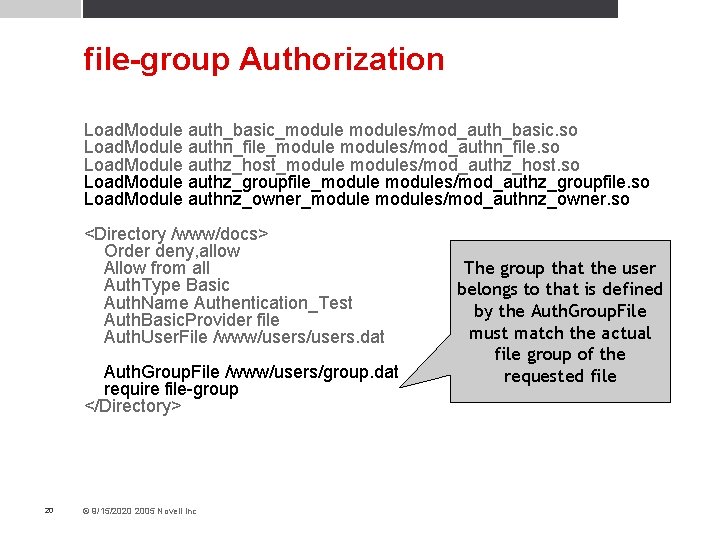
file-group Authorization Load. Module auth_basic_modules/mod_auth_basic. so Load. Module authn_file_modules/mod_authn_file. so Load. Module authz_host_modules/mod_authz_host. so Load. Module authz_groupfile_modules/mod_authz_groupfile. so Load. Module authnz_owner_modules/mod_authnz_owner. so <Directory /www/docs> Order deny, allow Allow from all Auth. Type Basic Auth. Name Authentication_Test Auth. Basic. Provider file Auth. User. File /www/users. dat Auth. Group. File /www/users/group. dat require file-group </Directory> 20 © 9/15/2020 2005 Novell Inc The group that the user belongs to that is defined by the Auth. Group. File must match the actual file group of the requested file
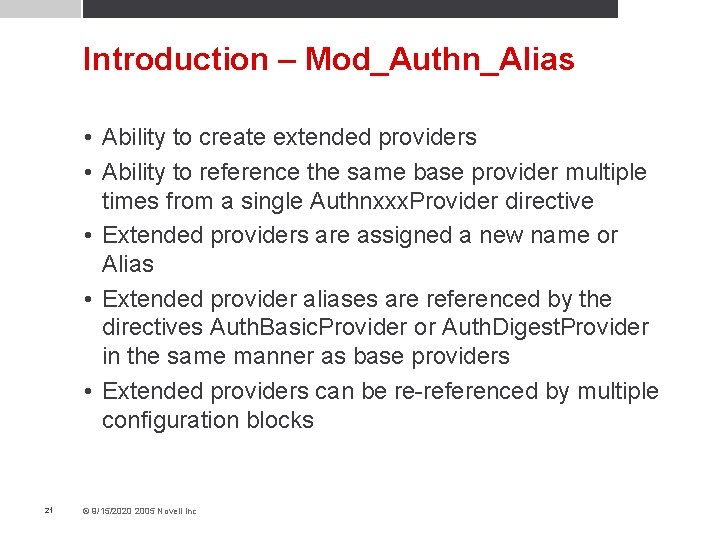
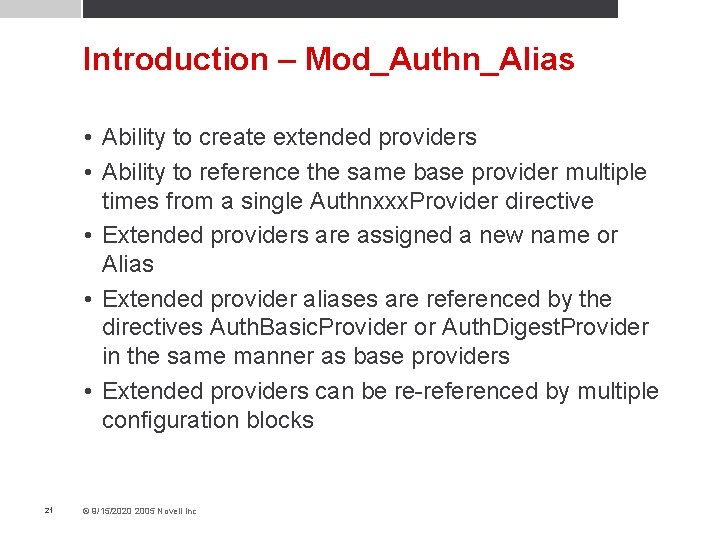
Introduction – Mod_Authn_Alias • Ability to create extended providers • Ability to reference the same base provider multiple times from a single Authnxxx. Provider directive • Extended providers are assigned a new name or Alias • Extended provider aliases are referenced by the directives Auth. Basic. Provider or Auth. Digest. Provider in the same manner as base providers • Extended providers can be re-referenced by multiple configuration blocks 21 © 9/15/2020 2005 Novell Inc
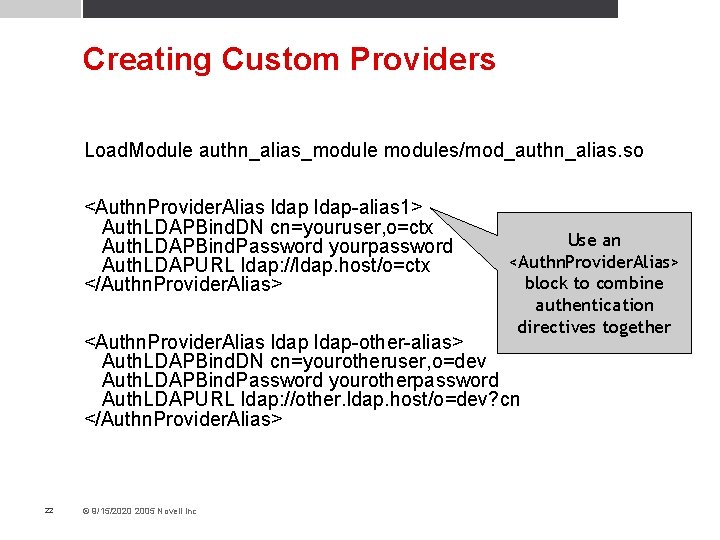
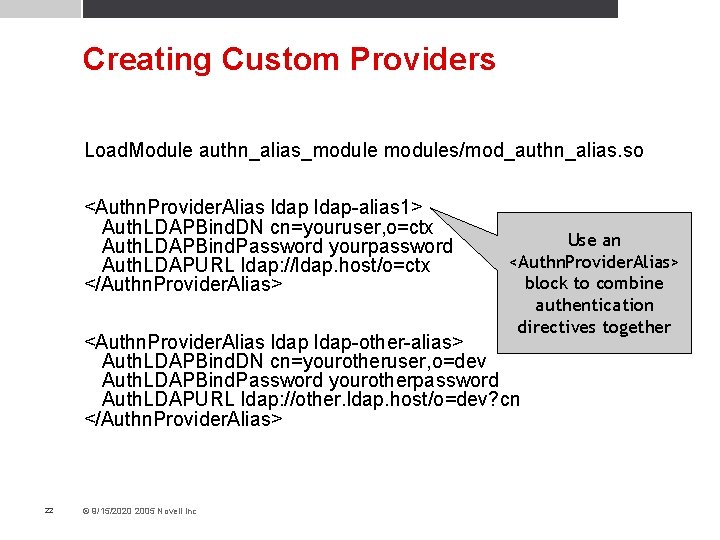
Creating Custom Providers Load. Module authn_alias_modules/mod_authn_alias. so <Authn. Provider. Alias ldap-alias 1> Auth. LDAPBind. DN cn=youruser, o=ctx Auth. LDAPBind. Password yourpassword Auth. LDAPURL ldap: //ldap. host/o=ctx </Authn. Provider. Alias> Use an <Authn. Provider. Alias> block to combine authentication directives together <Authn. Provider. Alias ldap-other-alias> Auth. LDAPBind. DN cn=yourotheruser, o=dev Auth. LDAPBind. Password yourotherpassword Auth. LDAPURL ldap: //other. ldap. host/o=dev? cn </Authn. Provider. Alias> 22 © 9/15/2020 2005 Novell Inc
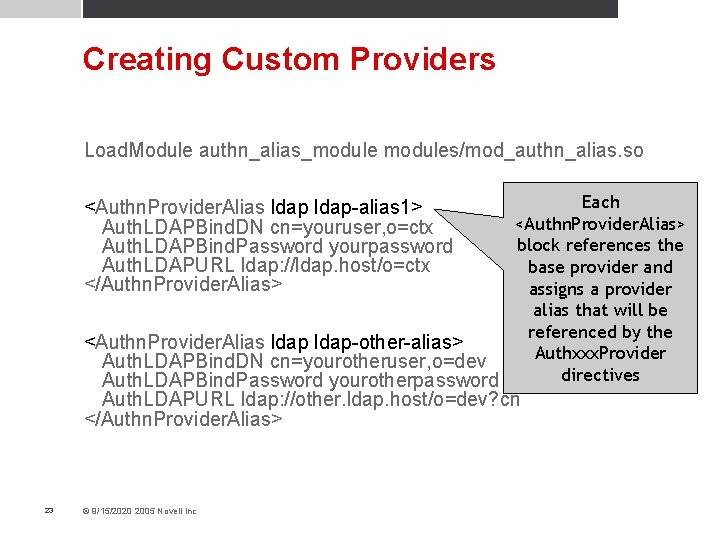
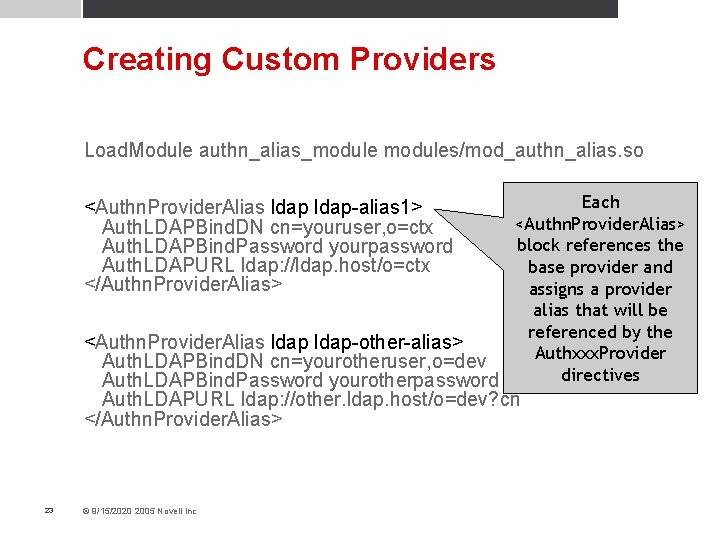
Creating Custom Providers Load. Module authn_alias_modules/mod_authn_alias. so Each <Authn. Provider. Alias> block references the base provider and assigns a provider alias that will be referenced by the <Authn. Provider. Alias ldap-other-alias> Authxxx. Provider Auth. LDAPBind. DN cn=yourotheruser, o=dev directives Auth. LDAPBind. Password yourotherpassword <Authn. Provider. Alias ldap-alias 1> Auth. LDAPBind. DN cn=youruser, o=ctx Auth. LDAPBind. Password yourpassword Auth. LDAPURL ldap: //ldap. host/o=ctx </Authn. Provider. Alias> Auth. LDAPURL ldap: //other. ldap. host/o=dev? cn </Authn. Provider. Alias> 23 © 9/15/2020 2005 Novell Inc
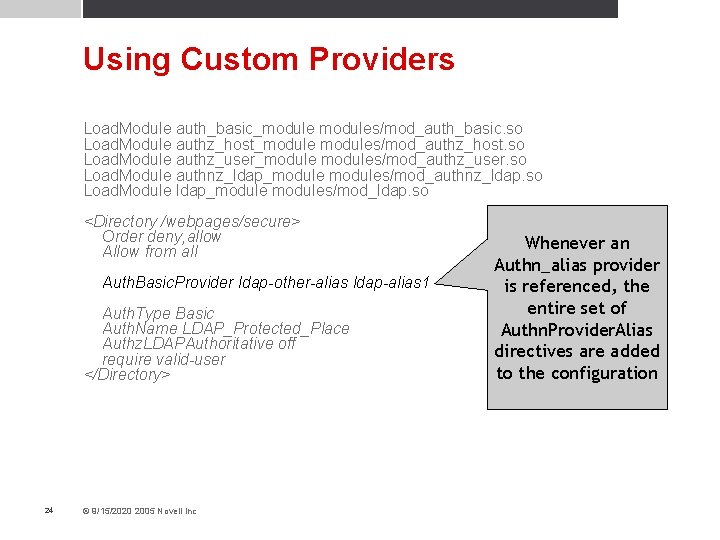
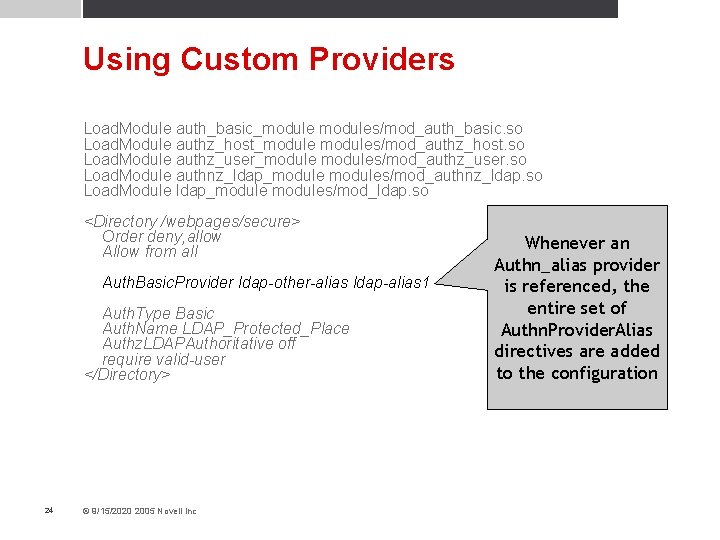
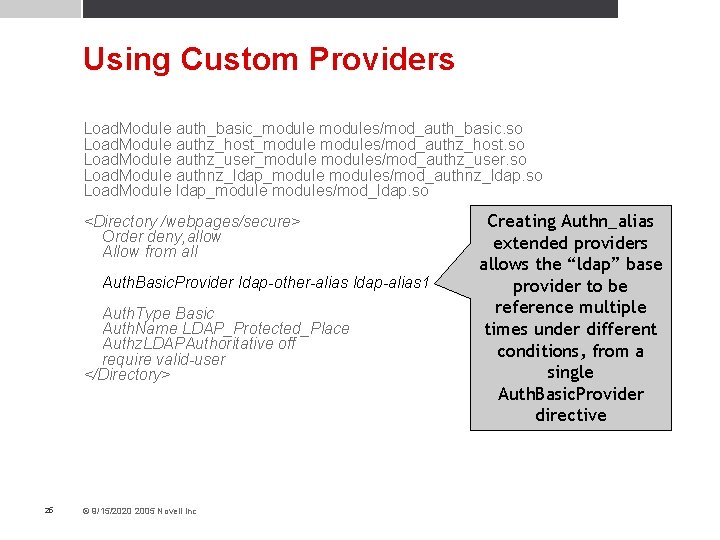
Using Custom Providers Load. Module auth_basic_modules/mod_auth_basic. so Load. Module authz_host_modules/mod_authz_host. so Load. Module authz_user_modules/mod_authz_user. so Load. Module authnz_ldap_modules/mod_authnz_ldap. so Load. Module ldap_modules/mod_ldap. so <Directory /webpages/secure> Order deny, allow Allow from all Auth. Basic. Provider ldap-other-alias ldap-alias 1 Auth. Type Basic Auth. Name LDAP_Protected_Place Authz. LDAPAuthoritative off require valid-user </Directory> 24 © 9/15/2020 2005 Novell Inc Whenever an Authn_alias provider is referenced, the entire set of Authn. Provider. Alias directives are added to the configuration
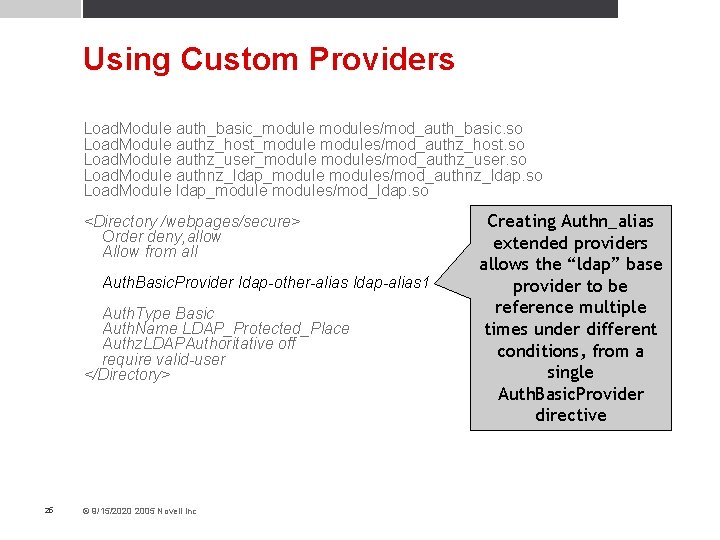
Using Custom Providers Load. Module auth_basic_modules/mod_auth_basic. so Load. Module authz_host_modules/mod_authz_host. so Load. Module authz_user_modules/mod_authz_user. so Load. Module authnz_ldap_modules/mod_authnz_ldap. so Load. Module ldap_modules/mod_ldap. so <Directory /webpages/secure> Order deny, allow Allow from all Auth. Basic. Provider ldap-other-alias ldap-alias 1 Auth. Type Basic Auth. Name LDAP_Protected_Place Authz. LDAPAuthoritative off require valid-user </Directory> 25 © 9/15/2020 2005 Novell Inc Creating Authn_alias extended providers allows the “ldap” base provider to be reference multiple times under different conditions, from a single Auth. Basic. Provider directive
Summary • Choosing the way authentication and authorization is done is now more modular • No longer bound to a specific authentication method based on authentication type • No longer bound to an authorization method based on the chosen authentication module • Ability to use multiple authentication providers along with multiple different authorization methods • Create, use and reuse custom authorization providers • Reuse the same authentication base provider under different conditions from the same Authnxxx. Provider directive • Much more powerful, flexible and consistent 26 © 9/15/2020 2005 Novell Inc
Questions