Networking with UWB MAC for UWB MariaGabriella Di
Networking with UWB © MAC for UWB Maria-Gabriella Di Benedetto University of Rome La Sapienza, Engineering School Department of Information and Communication INFOCOM Rome, Italy 1
MAC functionalities can be be summarized as as follows: • • MAC – Multiple Access • Resource Sharing • Resource Access • Resource Sharing – Packet Scheduling • Resource Access – Multiple Access – Admission Control – Addressing and Routing – Packet Scheduling – Admission Control – Addressing and Routing 2
Outline – Time Hopping Multiple Access – Multi-user system performance for Impulse Radio • The 2 PPM-TH-UWB case • The 2 PAM-DS-UWB case – Limit of application of the Standard Gaussian Approximation – Multi User Interference based on Pulse Collision – (UWB)2 MAC 3
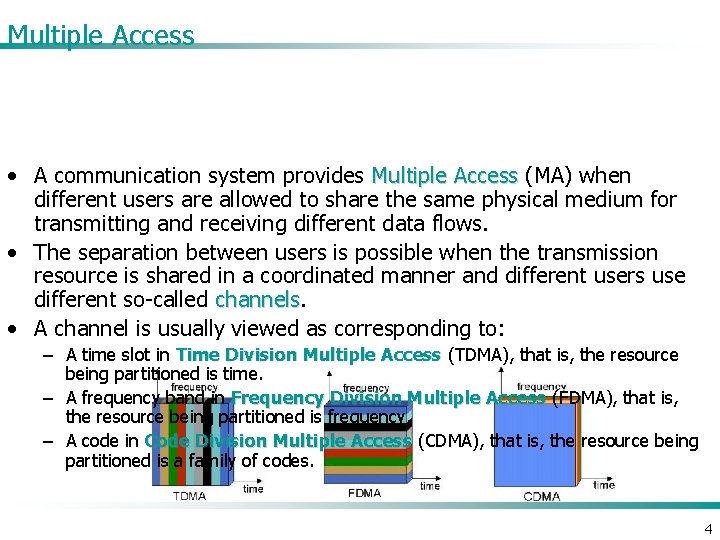
Multiple Access • A communication system provides Multiple Access (MA) when different users are allowed to share the same physical medium for transmitting and receiving different data flows. • The separation between users is possible when the transmission resource is shared in a coordinated manner and different users use different so-called channels • A channel is usually viewed as corresponding to: – A time slot in Time Division Multiple Access (TDMA), that is, the resource being partitioned is time. – A frequency band in Frequency Division Multiple Access (FDMA), that is, the resource being partitioned is frequency. – A code in Code Division Multiple Access (CDMA), that is, the resource being partitioned is a family of codes. 4
– The current trend in the IEEE 802. 15. 3 a adopts a TDMA-based strategy for the UWB physical layer Time Hopping Multiple Access • Impulse Radio, however, offers the possibility of partitioning time in a peculiar way because of the intrinsic short and limited duration of the pulses – The same codes which are used to shape the spectrum of the transmitted signal can also serve as users’ signatures and ensure access to the medium to multiple users – This manner of partitioning the resource is called Time-Hopping Multiple Access (THMA) THMA 5
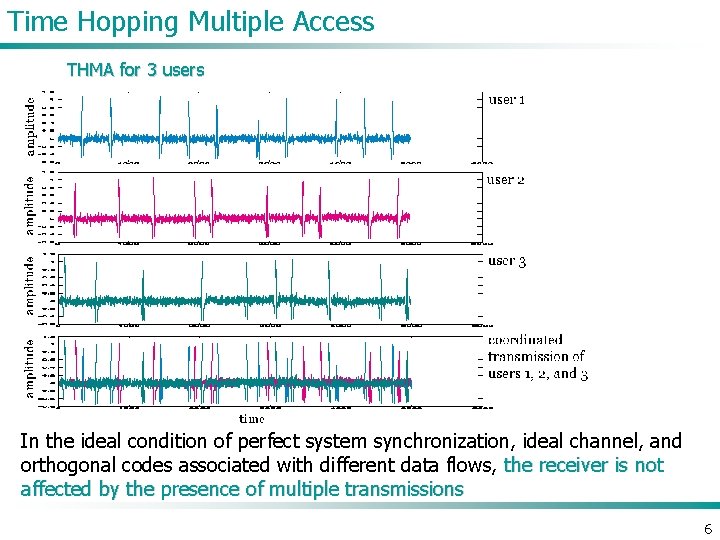
Time Hopping Multiple Access THMA for 3 users In the ideal condition of perfect system synchronization, ideal channel, and orthogonal codes associated with different data flows, the receiver is not affected by the presence of multiple transmissions 6
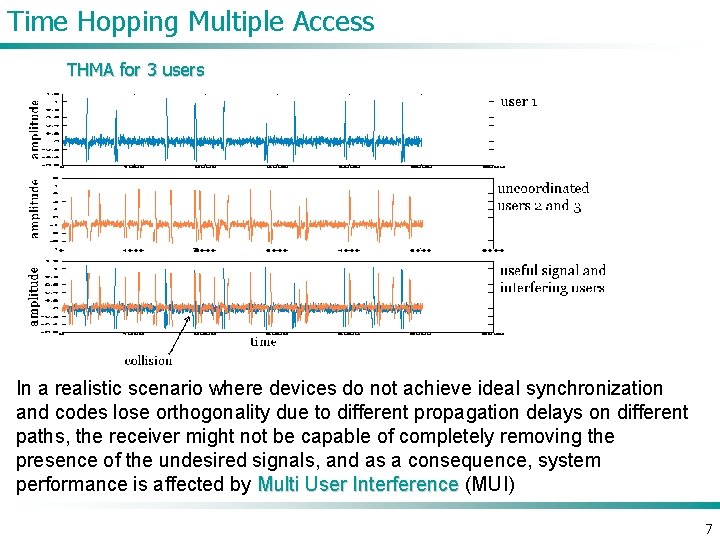
Time Hopping Multiple Access THMA for 3 users In a realistic scenario where devices do not achieve ideal synchronization and codes lose orthogonality due to different propagation delays on different paths, the receiver might not be capable of completely removing the presence of the undesired signals, and as a consequence, system performance is affected by Multi User Interference (MUI) 7
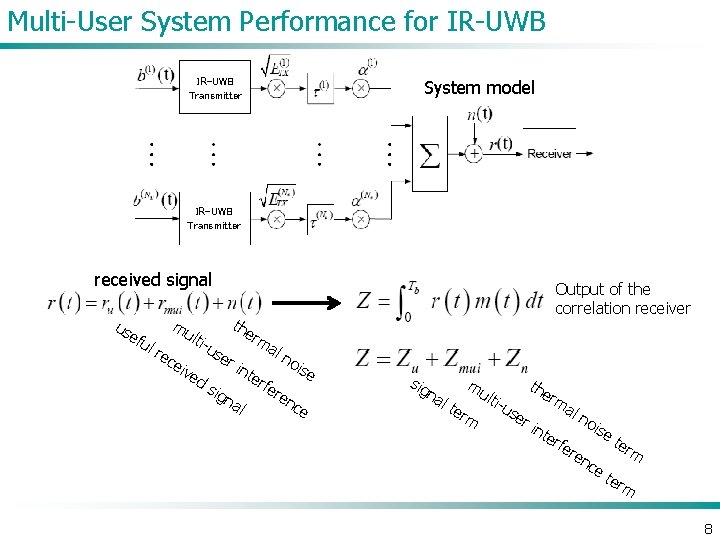
Multi-User System Performance for IR-UWB Transmitter System model IR-UWB Transmitter received signal us efu lr mu ec eiv lti- us ed s Output of the correlation receiver the rm er i ign nte al al rfe no ren ise ce sig na l ter mu m lti- us er the rm int erf al no ere ise nc e ter m 8
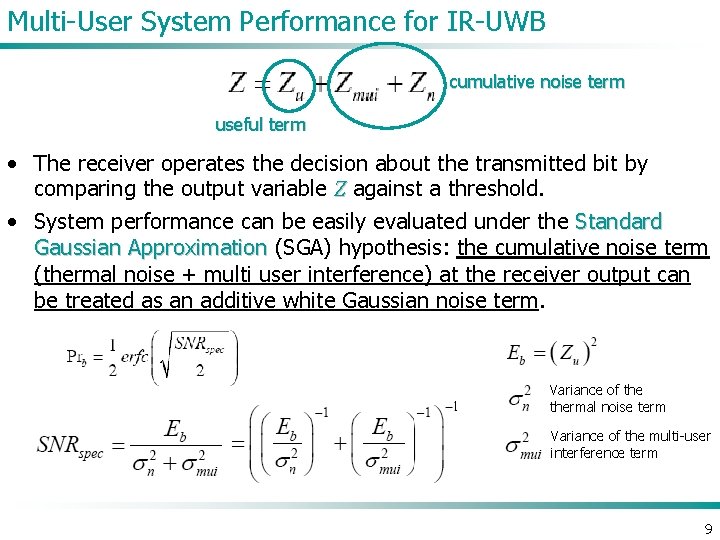
Multi-User System Performance for IR-UWB cumulative noise term useful term • The receiver operates the decision about the transmitted bit by comparing the output variable Z against a threshold. • System performance can be easily evaluated under the Standard Gaussian Approximation (SGA) hypothesis: the cumulative noise term (thermal noise + multi user interference) at the receiver output can be treated as an additive white Gaussian noise term. Variance of thermal noise term Variance of the multi-user interference term 9
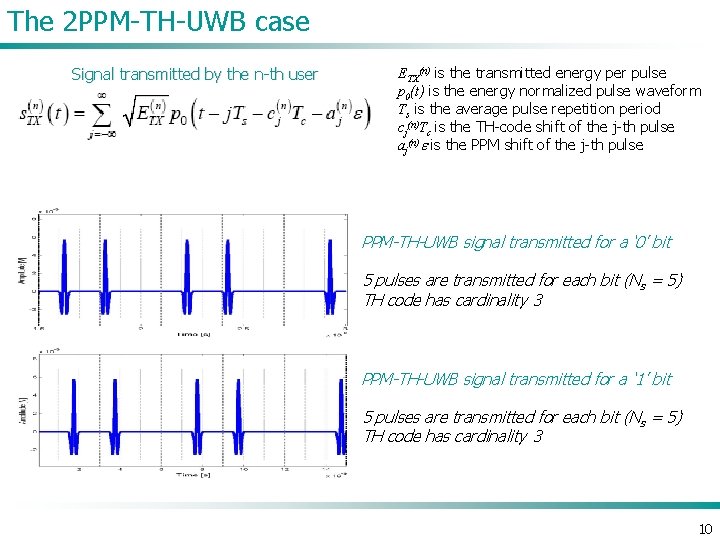
The 2 PPM-TH-UWB case Signal transmitted by the n-th user ETX(n) is the transmitted energy per pulse p 0(t) is the energy normalized pulse waveform Ts is the average pulse repetition period cj(n)Tc is the TH-code shift of the j-th pulse aj(n)e is the PPM shift of the j-th pulse PPM-TH-UWB signal transmitted for a ‘ 0’ bit 5 pulses are transmitted for each bit (Ns = 5) TH code has cardinality 3 PPM-TH-UWB signal transmitted for a ‘ 1’ bit 5 pulses are transmitted for each bit (Ns = 5) TH code has cardinality 3 10
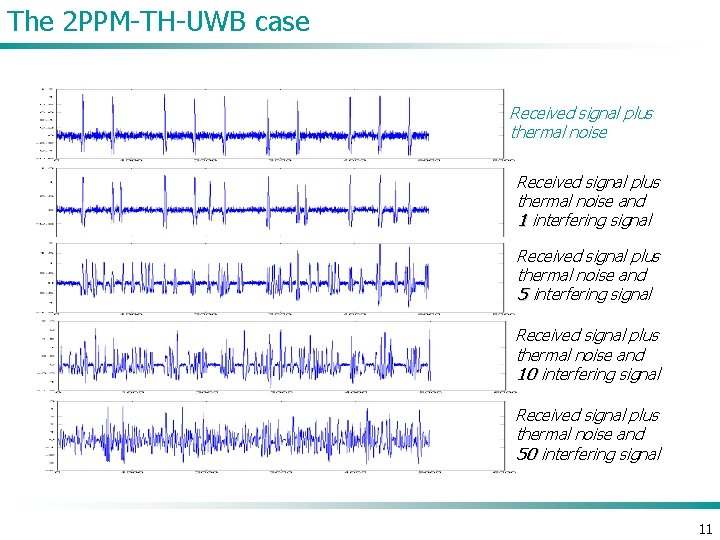
The 2 PPM-TH-UWB case Received signal plus thermal noise and 1 interfering signal Received signal plus thermal noise and 5 interfering signal Received signal plus thermal noise and 10 interfering signal Received signal plus thermal noise and 50 interfering signal 11
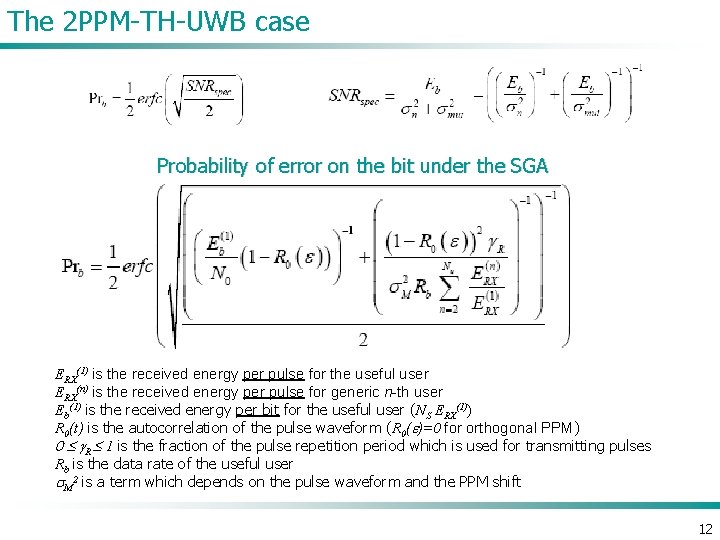
The 2 PPM-TH-UWB case Probability of error on the bit under the SGA ERX(1) is the received energy per pulse for the useful user ERX(n) is the received energy per pulse for generic n-th user Eb(1) is the received energy per bit for the useful user (NS ERX(1)) R 0(t) is the autocorrelation of the pulse waveform (R 0(e)=0 for orthogonal PPM) 0 g. R 1 is the fraction of the pulse repetition period which is used for transmitting pulses Rb is the data rate of the useful user s. M 2 is a term which depends on the pulse waveform and the PPM shift 12
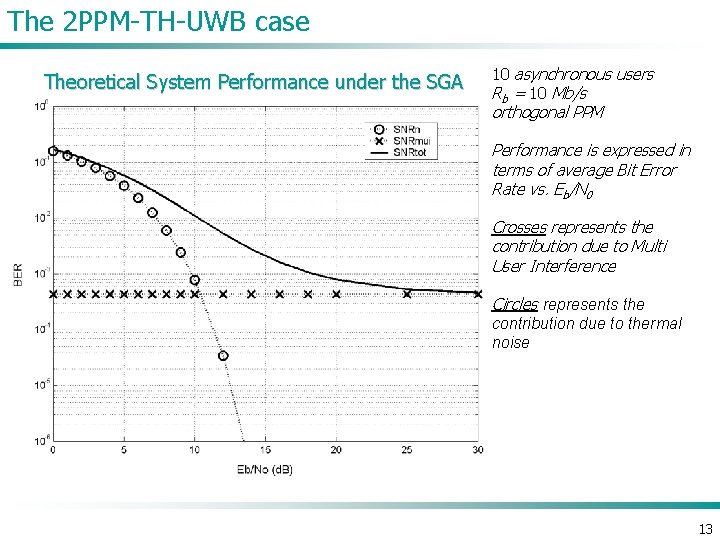
The 2 PPM-TH-UWB case Theoretical System Performance under the SGA 10 asynchronous users Rb = 10 Mb/s orthogonal PPM Performance is expressed in terms of average Bit Error Rate vs. Eb/N 0 Crosses represents the contribution due to Multi User Interference Circles represents the contribution due to thermal noise 13
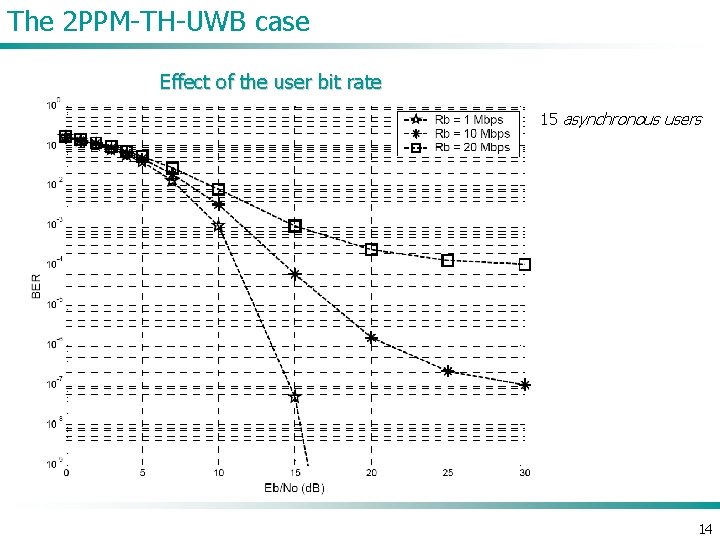
The 2 PPM-TH-UWB case Effect of the user bit rate 15 asynchronous users 14
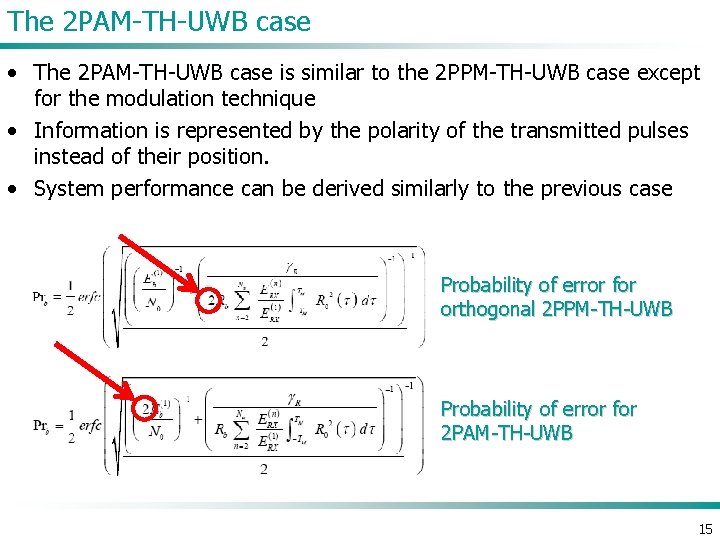
The 2 PAM-TH-UWB case • The 2 PAM-TH-UWB case is similar to the 2 PPM-TH-UWB case except for the modulation technique • Information is represented by the polarity of the transmitted pulses instead of their position. • System performance can be derived similarly to the previous case Probability of error for orthogonal 2 PPM-TH-UWB Probability of error for 2 PAM-TH-UWB 15
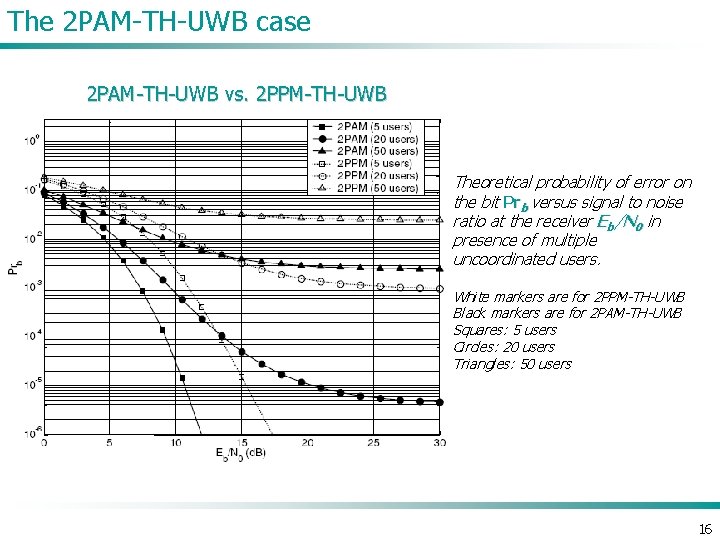
The 2 PAM-TH-UWB case 2 PAM-TH-UWB vs. 2 PPM-TH-UWB Theoretical probability of error on the bit Prb versus signal to noise ratio at the receiver Eb/N 0 in presence of multiple uncoordinated users. White markers are for 2 PPM-TH-UWB Black markers are for 2 PAM-TH-UWB Squares: 5 users Circles: 20 users Triangles: 50 users 16
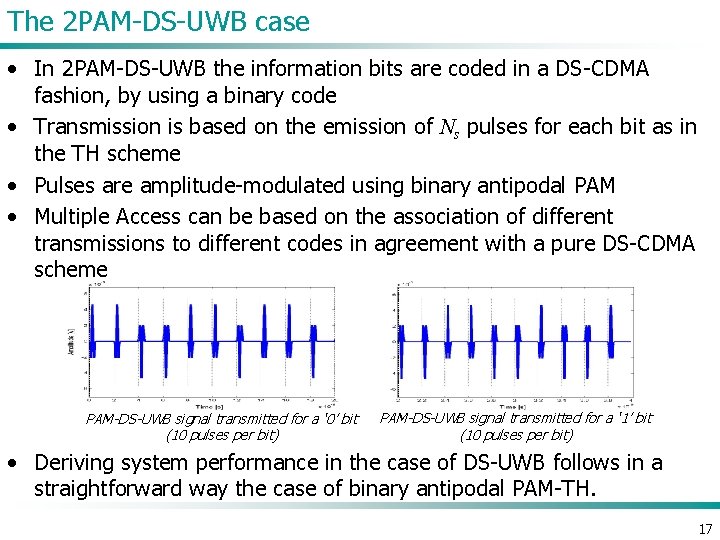
The 2 PAM-DS-UWB case • In 2 PAM-DS-UWB the information bits are coded in a DS-CDMA fashion, by using a binary code • Transmission is based on the emission of Ns pulses for each bit as in the TH scheme • Pulses are amplitude-modulated using binary antipodal PAM • Multiple Access can be based on the association of different transmissions to different codes in agreement with a pure DS-CDMA scheme PAM-DS-UWB signal transmitted for a ‘ 0’ bit (10 pulses per bit) PAM-DS-UWB signal transmitted for a ‘ 1’ bit (10 pulses per bit) • Deriving system performance in the case of DS-UWB follows in a straightforward way the case of binary antipodal PAM-TH. 17
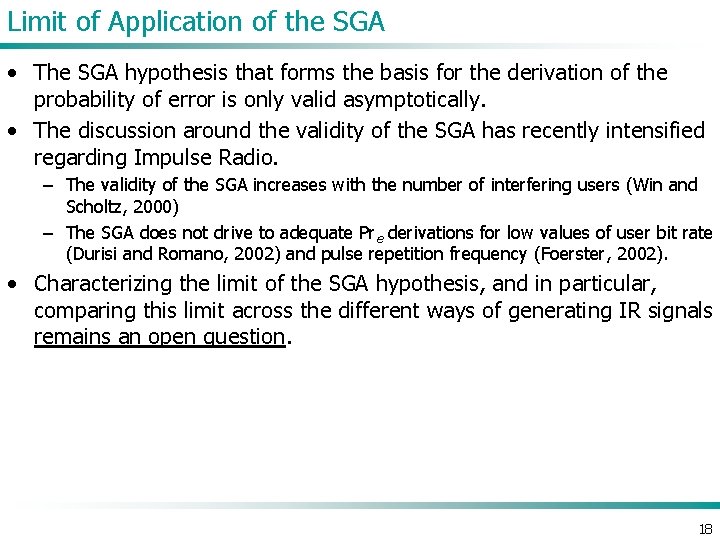
Limit of Application of the SGA • The SGA hypothesis that forms the basis for the derivation of the probability of error is only valid asymptotically. • The discussion around the validity of the SGA has recently intensified regarding Impulse Radio. – The validity of the SGA increases with the number of interfering users (Win and Scholtz, 2000) – The SGA does not drive to adequate Pre derivations for low values of user bit rate (Durisi and Romano, 2002) and pulse repetition frequency (Foerster, 2002). • Characterizing the limit of the SGA hypothesis, and in particular, comparing this limit across the different ways of generating IR signals remains an open question. 18
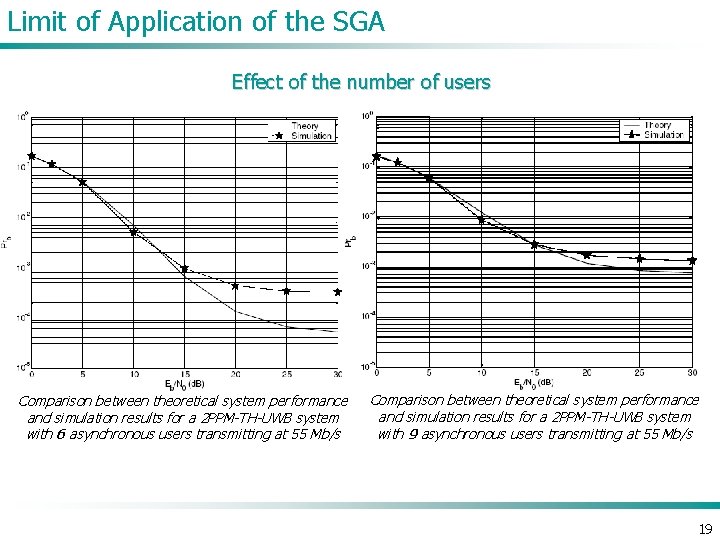
Limit of Application of the SGA Effect of the number of users Comparison between theoretical system performance and simulation results for a 2 PPM-TH-UWB system with 6 asynchronous users transmitting at 55 Mb/s Comparison between theoretical system performance and simulation results for a 2 PPM-TH-UWB system with 9 asynchronous users transmitting at 55 Mb/s 19
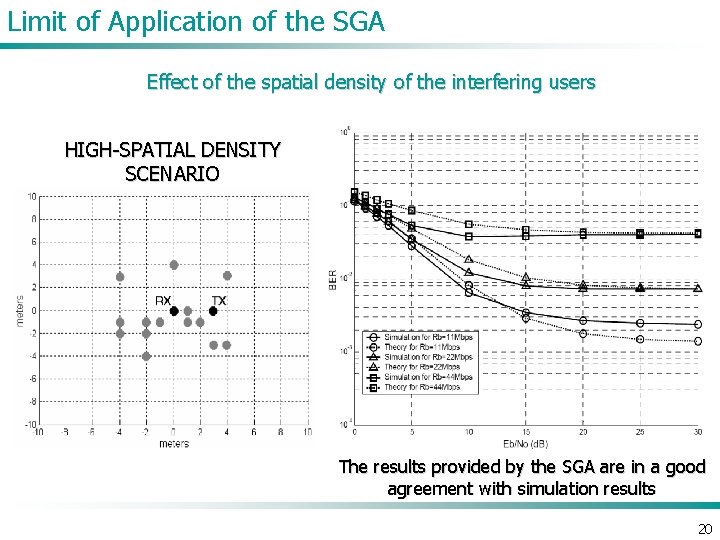
Limit of Application of the SGA Effect of the spatial density of the interfering users HIGH-SPATIAL DENSITY SCENARIO The results provided by the SGA are in a good agreement with simulation results 20
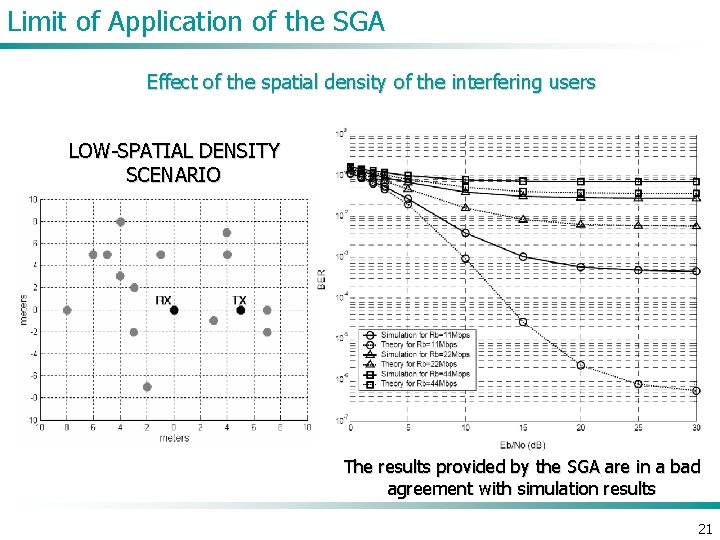
Limit of Application of the SGA Effect of the spatial density of the interfering users LOW-SPATIAL DENSITY SCENARIO The results provided by the SGA are in a bad agreement with simulation results 21
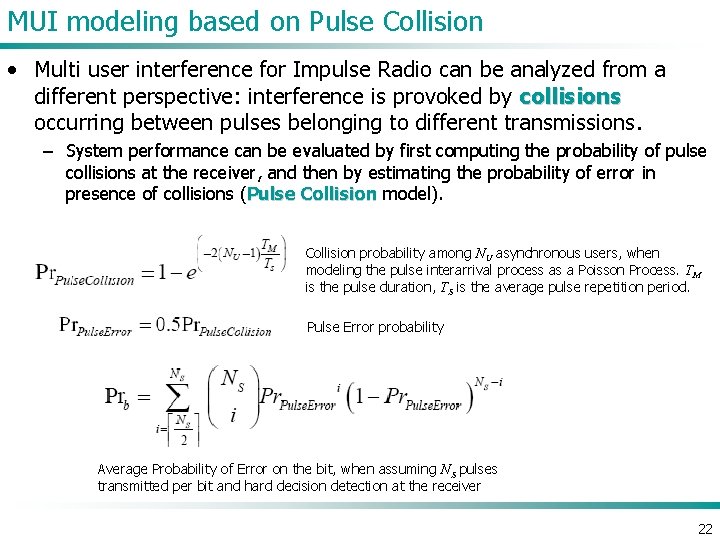
MUI modeling based on Pulse Collision • Multi user interference for Impulse Radio can be analyzed from a different perspective: interference is provoked by collisions occurring between pulses belonging to different transmissions. – System performance can be evaluated by first computing the probability of pulse collisions at the receiver, and then by estimating the probability of error in presence of collisions (Pulse Collision model). Collision probability among NU asynchronous users, when modeling the pulse interarrival process as a Poisson Process. TM is the pulse duration, TS is the average pulse repetition period. Pulse Error probability Average Probability of Error on the bit, when assuming NS pulses transmitted per bit and hard decision detection at the receiver 22
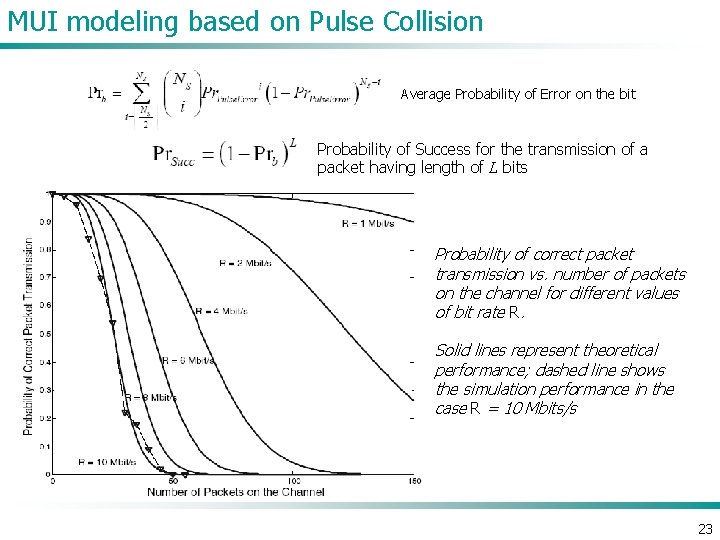
MUI modeling based on Pulse Collision Average Probability of Error on the bit Probability of Success for the transmission of a packet having length of L bits Probability of correct packet transmission vs. number of packets on the channel for different values of bit rate R. Solid lines represent theoretical performance; dashed line shows the simulation performance in the case R = 10 Mbits/s 23
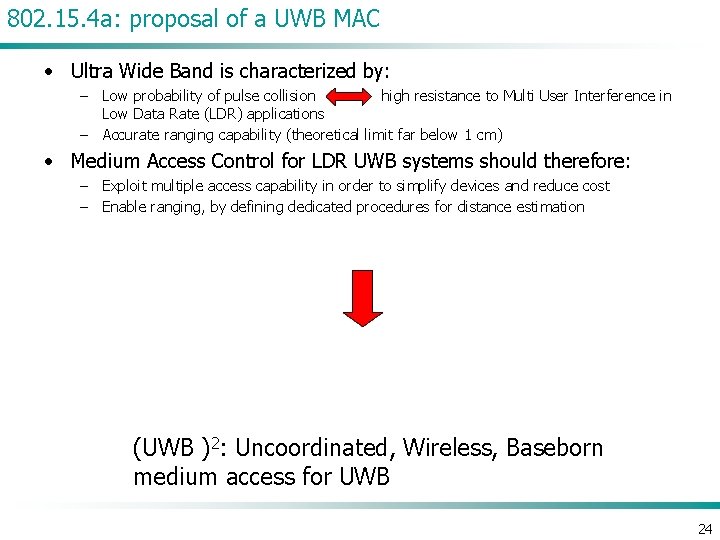
802. 15. 4 a: proposal of a UWB MAC • Ultra Wide Band is characterized by: – Low probability of pulse collision high resistance to Multi User Interference in Low Data Rate (LDR) applications – Accurate ranging capability (theoretical limit far below 1 cm) • Medium Access Control for LDR UWB systems should therefore: – Exploit multiple access capability in order to simplify devices and reduce cost – Enable ranging, by defining dedicated procedures for distance estimation (UWB )2: Uncoordinated, Wireless, Baseborn medium access for UWB 24
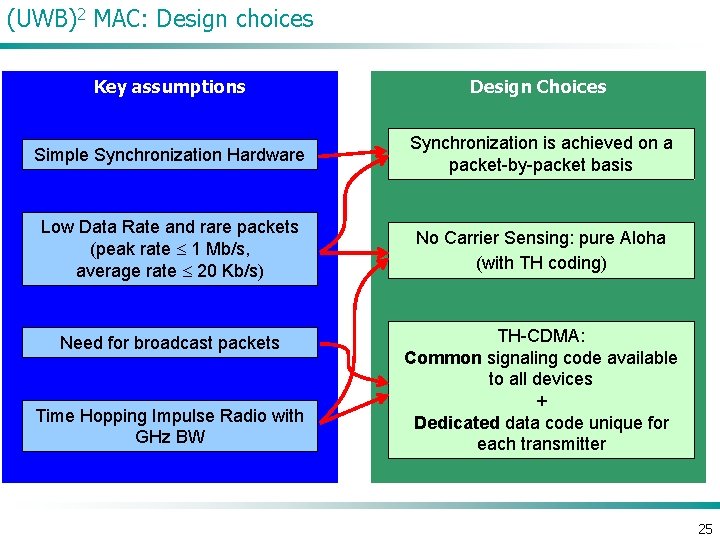
(UWB)2 MAC: Design choices Key assumptions Design Choices Simple Synchronization Hardware Synchronization is achieved on a packet-by-packet basis Low Data Rate and rare packets (peak rate 1 Mb/s, average rate 20 Kb/s) No Carrier Sensing: pure Aloha (with TH coding) Need for broadcast packets Time Hopping Impulse Radio with GHz BW TH-CDMA: Common signaling code available to all devices + Dedicated data code unique for each transmitter 25
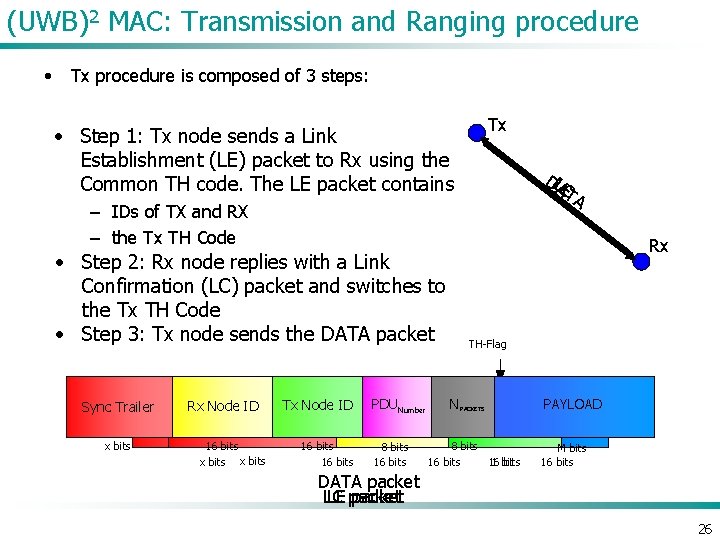
(UWB)2 MAC: Transmission and Ranging procedure • Tx procedure is composed of 3 steps: • Step 1: Tx node sends a Link Establishment (LE) packet to Rx using the Common TH code. The LE packet contains Tx DLLAEC TA – IDs of TX and RX – the Tx TH Code • Step 2: Rx node replies with a Link Confirmation (LC) packet and switches to the Tx TH Code • Step 3: Tx node sends the DATA packet Sync Trailer x bits Rx TH-Flag N PACKETS PAYLOAD Tx Node ID Rx. PDU Rx Node Number Tx Node ID ID Sync. ID Trailer Sync Trailer Rx Node IDNode Tx Node ID TH-Code 16 bits x bits 16 bits 8 bits 16 bits 1 bit 16 bits M bits 16 bits DATA packet LE packet LC 26
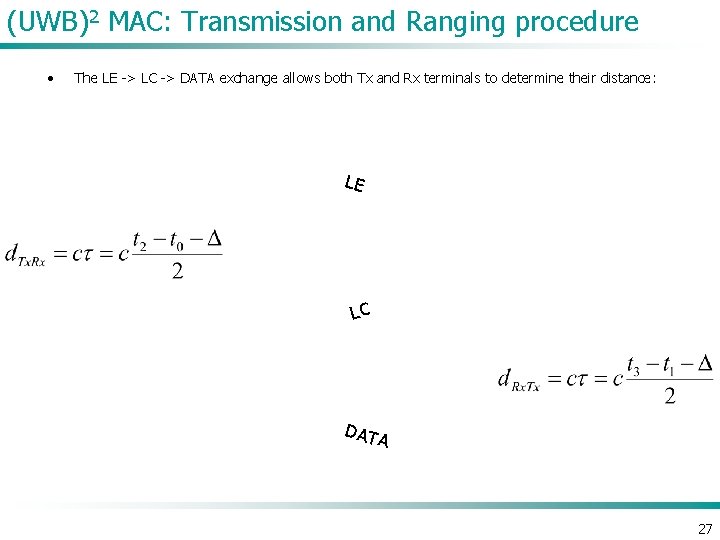
(UWB)2 MAC: Transmission and Ranging procedure • The LE -> LC -> DATA exchange allows both Tx and Rx terminals to determine their distance: LE LC DAT A 27
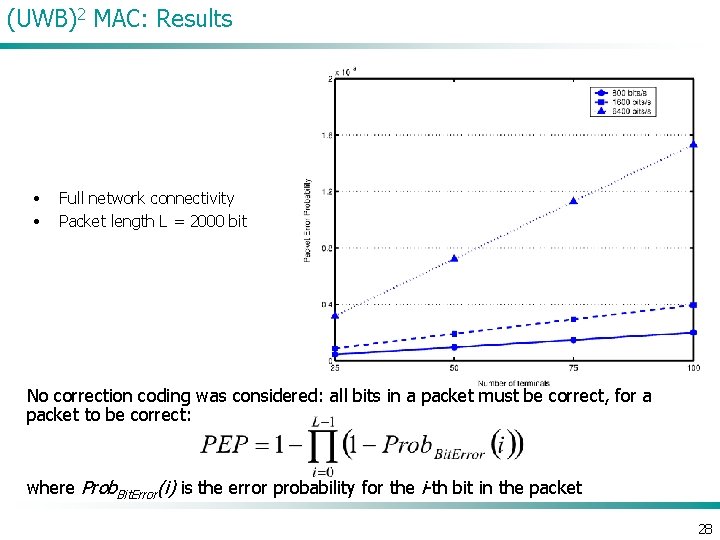
(UWB)2 MAC: Results • • Full network connectivity Packet length L = 2000 bit No correction coding was considered: all bits in a packet must be correct, for a packet to be correct: where Prob. Bit. Error(i) is the error probability for the i-th bit in the packet 28
References • IEEE 802. 15. 3 -2003, “IEEE standard for information technology - telecommunications and information exchange between systems - local and metropolitan area networks - specific requirements part 15. 3: wireless medium access control (MAC) and physical layer (PHY) specifications for high rate wireless personal area networks (WPANs)” (September 2003). • IEEE 802. 15. 4 -2003, “IEEE standard for information technology - telecommunications and information exchange between systems - local and metropolitan area networks specific requirements part 15. 4: wireless medium access control (MAC) and physical layer (PHY) specifications for low-rate wireless personal area networks (LR-WPANs)” (October 2003). • De Nardis, L. , and M. -G. Di Benedetto, “Medium Access Control design in UWB networks: review and trends, ” Journal of Communication and Networks, Special Issue on Ultra-Wideband Communications, Volume: 5, Issue: 4 (December 2003), 386– 393. • Di Benedetto, M. -G. , L. De Nardis, M. Junk, and G. Giancola, “(UWB)2: Uncoordinated, Wireless, Baseborn medium access for UWB communication networks, ” in press in Mobile Networks and Applications special issue on WLAN Optimization at the MAC and Network Levels (2 nd quarter 2004). 29

References • • • • • Abramson, N. , “The Throughput of Packet Broadcasting Channels, ” IEEE Transactions on Communications , Volume: COM-25, Issue: 1 (January 1977), 117– 128. Aida, H. , Y. Tamura, Y. Tobe, and H. Tokuda, “Wireless packet scheduling with signal-to-noise ratio monitoring, ” Proceedings of IEEE Conference on Local Computer Networks (November 2000), 32– 41. Baldi, P. , L. De Nardis, and M. -G. Di Benedetto, “Modeling and optimization of UWB communication networks through a flexible cost function, ” IEEE Journal on Selected Areas in Communications , Volume: 20, Issue: 9 (December 2002), 1733– 1744. Bambos, N. , “Toward power-sensitive network architectures in wireless communications: Concepts, issues, and design aspects, ” IEEE Personal Communications , Volume: 5, Issue: 3 (June 1998), 50– 59. Bertsekas, D. , and R. Gallager, Data Networks, 2 nd Edition, Upper Saddle River, NJ: Prentice Hall (1992). Bharghavan, V. , A. Demers, S. Shenker, and L. Zhang, “MACAW: A medium access protocol for wireless LANs, ” Proceedings of the conference on Applications, Technologies, Architectures and Protocols for Computer Communication (August 1994), 212– 225. Breslau, L. , D. Estrin, K. Fall, S. Floyd, J. Heidemann, A. Helmy, P. Huang, S. Mc. Canne, K. Varadhan, Y. Xu, and H. Yu, “ Advances in Network Simulation, ” IEEE Computer, Volume: 33, Issue: 5 (May 2000), 59– 67. Chandra, A. , V. Gummalla, and J. O. Limb, “Wireless Medium Access Control Protocols, ” IEEE Communication Surveys (2 nd quarter 2000), 2– 15. Choi, H. , and N. Moayeri, “Evaluation procedure for 802. 16 MAC Protocols, ” Available at www. ieee 802. org/16/tg 1/mac/pres/802161 mp-00_16. pdf (April 2000). Crow, B. P. , I. Widjaja, J. G. Kim, and P. T. Sakai, “IEEE 802. 11: Wireless Local Area Networks, ” IEEE Communications Magazine , Volume: 35, Issue: 9 (September 1997), 116– 26. Cuomo, F. , C. Martello, A. Baiocchi, and F. Capriotti, “Radio Resource Sharing for Ad Hoc Networking with UWB, ” IEEE Journal on Selected Areas in Communications , Volume: 20, Issue: 9 (December 2002), 1722– 1732. Cuomo, F. , C. Martello, and S. Caputo, “An interference-controlled admission control scheme for Qo. S support in distributed UWB networks, ” Proceedings of the IST Mobile & Wireless Communications Summit (June 2003), 508– 512. Cuomo, F. , and C. Martello, “Improving Wireless Access Control Schemes via Adaptive Power Regulation, ” Proceedings of Personal Wireless Communications 8 th International Conference (September 2003), 114– 127. Dastangoo, S. , B. R. Vojcic, and J. N. Daigle, “Performance Analysis of Multi-Code Spread Slotted ALOHA (MCSSA) System, ” IEEE Global Telecommunications Conference , Volume: 3 (November 1998), 1839– 1847. Demers, A. , S. Keshav, and S. Shenker, “Analysis and Simulation of a Fair Queueing Algorithm, ” Proceedings of the Conference on Applications, Technologies, Architectures and Protocols for Computer Communication (September 1989), 1– 12. Deng, J. , and Z. J. Haas, “Dual Busy Tones Multiple Access (DBTMA): A New Medium Access Control for Packet Radio Networks, ” IEEE International Conference on Universal Personal Communications , Volume: 2 (October 1998), 973– 977. De Nardis, L. , G. Giancola, and M. -G. Di Benedetto, “A Position Based Routing Strategy for UWB Networks, ” IEEE Conference on Ultra Wideband Systems and Technologies (November 2003), 200– 204. De Nardis, L. , and M. -G. Di Benedetto, “Medium Access Control design in UWB networks: review and trends, ” Journal of Communication and Networks, Special Issue on Ultra-Wideband Communications , Volume: 5, Issue: 4 (December 2003), 386– 393. Di Benedetto, M. -G. , and P. Baldi, “A model for self-organizing large-scale wireless networks, ” Invited paper, Proceedings of the International Workshop on 3 G Infrastructure and Services (July 2001), 210– 213. Di Benedetto, M. -G. , L. De Nardis, M. Junk, and G. Giancola, “(UWB)2: Uncoordinated, Wireless, Baseborn medium access for UWB communication networks, ” in press in Mobile Networks and Applications special issue on WLAN Optimization at the MAC and Network Levels (2 nd quarter 2004). 30
References • • • • • Fontana, R. J. , E. Richley, and J. Barney, “Commercialization of an Ultra Wideband Precision Asset Location System, ” IEEE Conference on Ultra Wideband Systems and Technologies (November 2003), 369– 373. Fullmer, C. L. , and J. J. Garcia-Luna-Aceves, “Floor acquisition Multiple Access (FAMA) for Packet Radio Networks, ” Proceedings of the conference on Applications, Technologies, Architectures and Protocols for Computer Communication (September 1995), 262– 273. Garcia-Luna-Aceves, J. J. , and J. Raju, “Distributed Assignment of codes for multihop packet-radio networks, ” Proceedings of IEEE Military Communications Conference , Volume: 1 (November 1997), 450– 454. Golmie, N. Chevrollier, and I. El. Bakkouri, “Interference aware Bluetooth packet scheduling, ” Proceedings of IEEE Global Telecommunications Conference , Volume: 5 (November 25– 29 2001), 2857– 2863. Gupta, P. , and P. R. Kumar, “The capacity of wireless networks, ” IEEE Transactions on Information Theory , Volume: 46, Issue: 2 (March 2000), 388– 404. Haartsen, J. C. , “The Bluetooth Radio System, ” IEEE Personal Communications , Volume: 7, Issue: 1 (February 2000), 28– 36. Iacobucci, M. S. , and M. -G. Di Benedetto, Computer method for pseudo-random codes generation , National Italian patent number RM 2001 A 000592 (2001). IEEE 802. 15. 3 -2003, “IEEE standard for information technology - telecommunications and information exchange between systems - local and metropolitan area networks specific requirements part 15. 3: wireless medium access control (MAC) and physical layer (PHY) specifications for high rate wireless personal area networks ( WPANs)” (September 2003). IEEE 802. 15. 4 -2003, “IEEE standard for information technology - telecommunications and information exchange between systems - local and metropolitan area networks specific requirements part 15. 4: wireless medium access control (MAC) and physical layer (PHY) specifications for low-rate wireless personal area networks (LR- WPANs)” (October 2003). Karn, P. , “MACA-A new Channel Access Protocol for Packet Radio, ” Proceedings of the ARRL/CRRL Amateur Radio Ninth Computer Networking Conference (September 1990), 134– 140. Khun-Jush, J. , G. Malmgren, P. Schramm, and J. Torsner, “Overview and performance of HIPERLAN type 2 -a standard for broadband wireless communications, ” Proceedings of IEEE 51 st Vehicular Technology Conference , Volume: 1 (May 2000), 112– 117. Kleinrock, L. , and F. A. Tobagi, “Packet Switching in Radio Channels: Part I–Carrier Sense Multiple-Access Modes and Their Throughput-Delay Characteristics, ” IEEE Transactions on Communications , Volume: 23, Issue: 12 (December 1975), 1400– 1416. Ko, Y. B. , and N. H Vaidya. , “Using location information to improve routing in ad hoc networks, ” Technical Report 97 -013, CS Dept, Texas AM University (December 1997). Lin, T. -Y. , Y. -K. Liu, and Y. -C. Tseng, “An Improved Packet collision analysis for Multi-Bluetooth Piconets considering Frequency-Hopping Guard Time Effect, ” IEEE Vehicular Technology Conference Proceedings (October 2003), 577– 581. Lu, S. , V. Bharghavan, and R. Srikant, “Fair scheduling in wireless packet networks, ” IEEE/ACM Transactions on Networking , Volume: 7, Issue: 4 (August 1999), 473– 489. Mouly, M. , and M. B. Pautet, The GSM System for Mobile Communication , Palaiseau, France: CELL&SYS (1992). Nagle, J. , “On Packet Switches with Infinite Storage, ” IEEE Transactions on Communications , Volume: 35, Issue: 4 (April 1987), 435– 438. Nahrstedt, K. , and R. Steinmetz, “Resource Management in Networked Multimedia Systems, ” IEEE Computer, Volume: 28, Issue: 5 (May 1995), 52– 63. Polydoros, A. , and J. Silvester, “Slotted Random Access Spread-Spectrum Networks: An Analytical Framework, ” IEEE Journal on Selected Areas in Communications , Volume: 5, Issue: 6 (July 1987), 989– 1002. Raychaudhuri, D. , “Performance Analysis of Random Access Packet-Switched Code Division Multiple Access Systems, ” IEEE Transactions on Communications , Volume: 29, Issue: 6 (June 1981), 895– 901. 31
References • • • Talucci, F. , and M. Gerla, “MACA-BI (MACA By Invitation): A wireless MAC protocol for high speed ad hoc networking, ” IEEE 6 th International Conference on Proceedings of Universal Personal Communications , Volume: 2 (October 1997), 913– 917. Tobagi, F. A. , and L. Kleinrock, “Packet Switching in Radio Channels: Part II – The Hidden Terminal Problem in Carrier Sense Multiple Access and the Busy Tone Solution, ” IEEE Transactions on Communications , Volume: 23, Issue: 12 (December 1975), 1417– 1433. Valaee, S. , and B. Li, “Distributed Call Admission control for Ad-hoc networks, ” Proceedings of IEEE 56 th Vehicular Technology Conference , Volume: 2 (September 2002), 1244– 1248. Varga, A. , “OMNe. T++” in the column “Software Tools for Networking, ” IEEE Network Interactive , Volume: 16, Issue: 4, Available at www. comsoc. org/ni/Public/2002/Jul/index. html (July 2002). Yang, Y. , and R. Kravets, “Contention-Aware Admission Control for Ad Hoc Networks, ” University of Illinois in Urbana-Champaign Technical Report UIUCDCS-R-2003 -2337 (April 2003). Wu, C. S. , and V. O. K. Lee, “Receiver Initiated Busy Tone Multiple Access in Packet Radio Networks, ” Proceedings of ACM SIGCOMM’ 87 (1987), 336– 342. 32
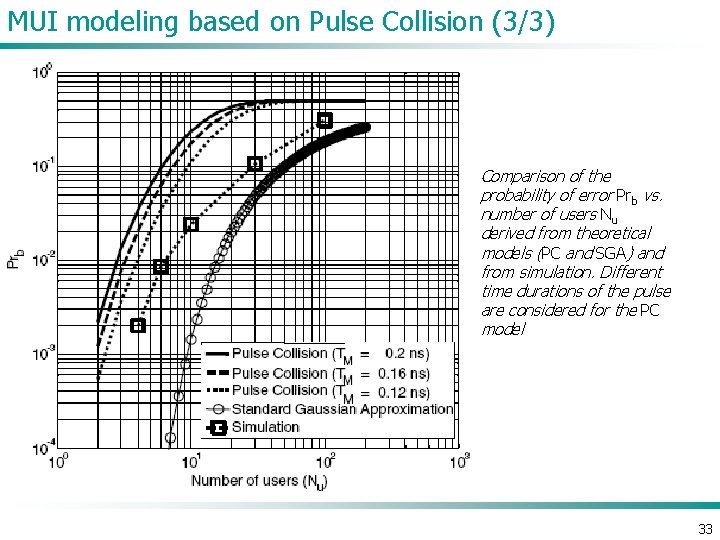
MUI modeling based on Pulse Collision (3/3) Comparison of the probability of error Prb vs. number of users Nu derived from theoretical models (PC and SGA) and from simulation. Different time durations of the pulse are considered for the PC model 33
- Slides: 33