Networking and the Internet J Glenn Brookshear 202139
Networking and the Internet J. Glenn Brookshear 蔡 文 能 2021/3/9 交大資 蔡文能 計概 Slide 4 -1
Agenda üNetwork Fundamentals • The Internet • The World Wide Web • Network Protocols • Security 2021/3/9 交大資 蔡文能 計概 Slide 4 -2
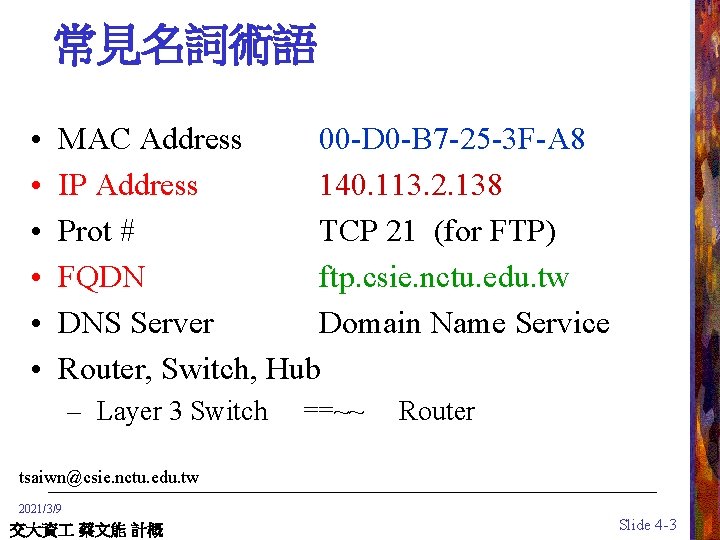
常見名詞術語 • • • MAC Address 00 -D 0 -B 7 -25 -3 F-A 8 IP Address 140. 113. 2. 138 Prot # TCP 21 (for FTP) FQDN ftp. csie. nctu. edu. tw DNS Server Domain Name Service Router, Switch, Hub – Layer 3 Switch ==~~ Router tsaiwn@csie. nctu. edu. tw 2021/3/9 交大資 蔡文能 計概 Slide 4 -3
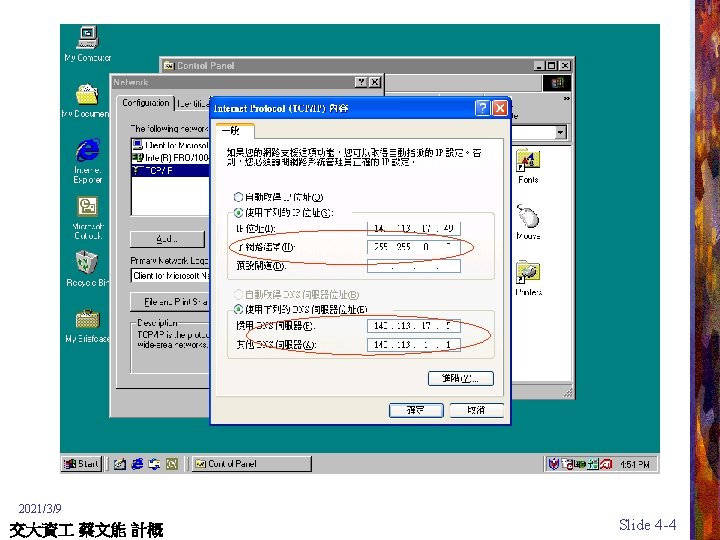
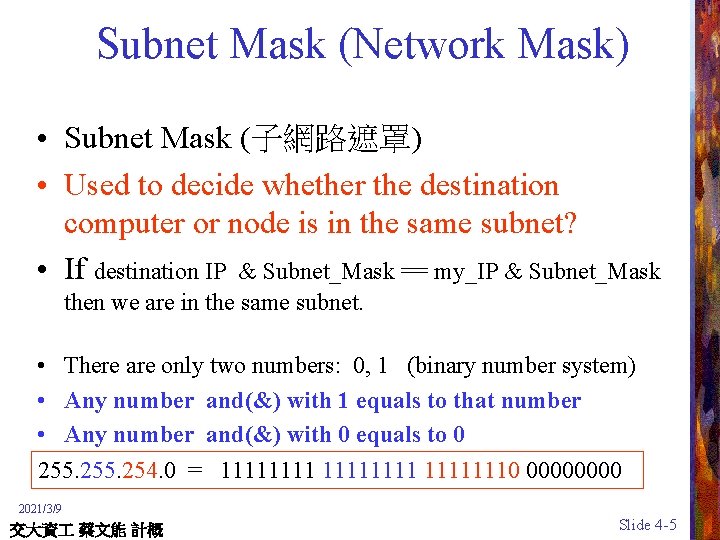
Subnet Mask (Network Mask) • Subnet Mask (子網路遮罩) • Used to decide whether the destination computer or node is in the same subnet? • If destination IP & Subnet_Mask == my_IP & Subnet_Mask then we are in the same subnet. • There are only two numbers: 0, 1 (binary number system) • Any number and(&) with 1 equals to that number • Any number and(&) with 0 equals to 0 255. 254. 0 = 111111110 0000 2021/3/9 交大資 蔡文能 計概 Slide 4 -5
Networks and Distributed Systems • Interaction of computers via networking has become common • Distributed systems – Examples: global information retrieval system, company-wide accounting and inventory systems, some computer games – Consists of units executing on different computers in a network • Network software is evolving into a network-wide operating system 2021/3/9 Mail/FTP/BBS/News/WWW/ICQ/MSN… 交大資 蔡文能 計概 Slide 4 -6
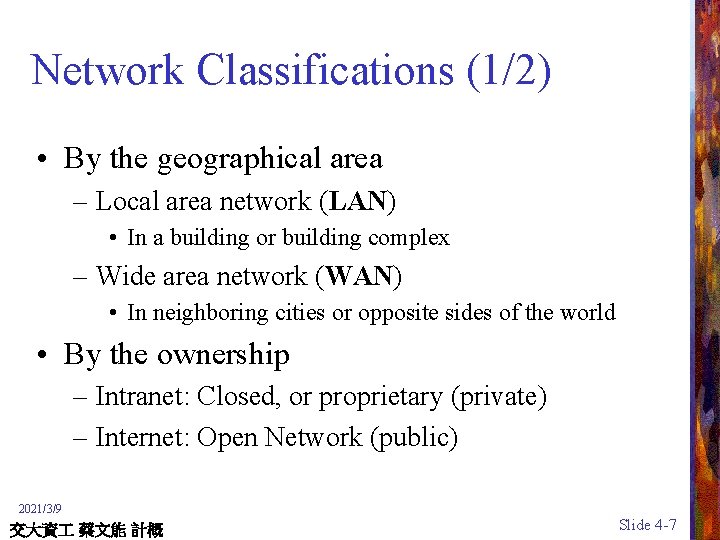
Network Classifications (1/2) • By the geographical area – Local area network (LAN) • In a building or building complex – Wide area network (WAN) • In neighboring cities or opposite sides of the world • By the ownership – Intranet: Closed, or proprietary (private) – Internet: Open Network (public) 2021/3/9 交大資 蔡文能 計概 Slide 4 -7
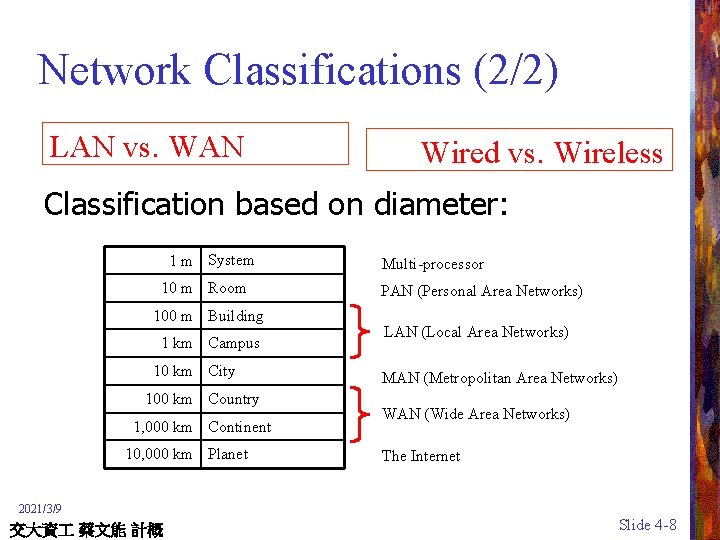
Network Classifications (2/2) LAN vs. WAN Wired vs. Wireless Classification based on diameter: 1 m System 10 m Room 100 m Building 1 km Campus 10 km City 100 km Country 1, 000 km Continent 10, 000 km Planet Multi-processor PAN (Personal Area Networks) LAN (Local Area Networks) MAN (Metropolitan Area Networks) WAN (Wide Area Networks) The Internet 2021/3/9 交大資 蔡文能 計概 Slide 4 -8
Network Logical Topology(1/2) (Network Configurations) Objective : to provide maximum possible reliability of data or information and give the end user the best possible response time and throughput • Bus Topology 匯流排拓樸架構 • Ring Topology 環狀拓樸架構 • Star Topology 星狀拓樸架構 2021/3/9 交大資 蔡文能 計概 Slide 4 -9
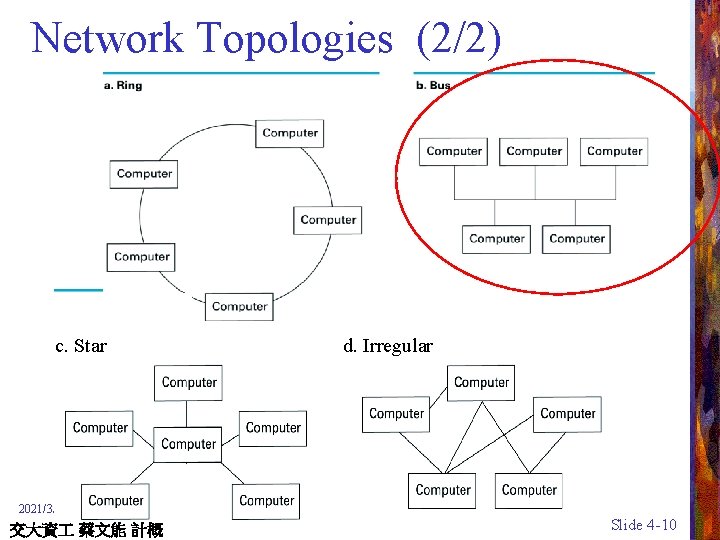
Network Topologies (2/2) c. Star d. Irregular 2021/3/9 交大資 蔡文能 計概 Slide 4 -10

Connecting Networks • Bridge (橋接器) – Connects two compatible networks – Connecting homogeneous domains • Router (路由器) – Connects two incompatible networks – Connecting heterogeneous domains – Resulting “network” is called an internet 2021/3/9 交大資 蔡文能 計概 Slide 4 -11
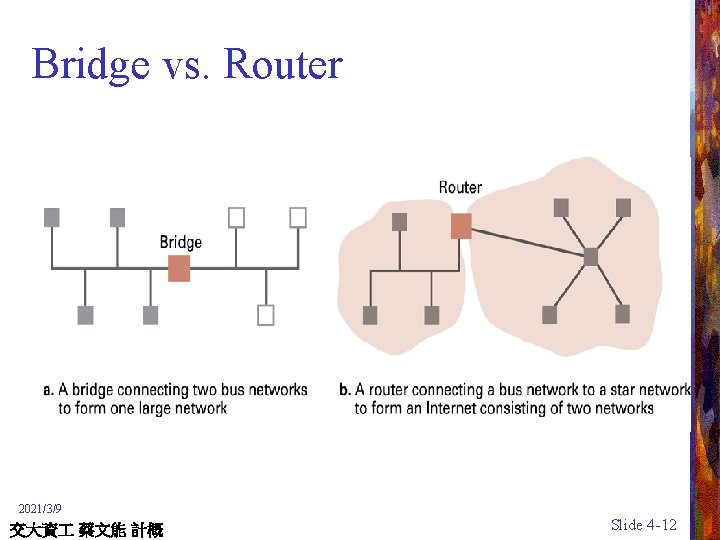
Bridge vs. Router 2021/3/9 交大資 蔡文能 計概 Slide 4 -12

網路中繼設備 (Repeater) • 路由器(Router) no CSMA/CD at hub; network adapters detect collisions • 交換器(Switch) 與 集線器(Hub) Router vs. Bridge ? tsaiwn@csie. nctu. edu. tw 2021/3/9 交大資 蔡文能 計概 Slide 4 -13

Bridges (橋接器) • Link layer device (不認識 IP address) – stores and forwards Ethernet frames – examines frame header and selectively forwards frame based on MAC dest address – when frame is to be forwarded on segment, uses CSMA/CD to access segment • transparent – hosts are unaware of presence of bridges • plug-and-play, self-learning – bridges do not need to be configured 2021/3/9 交大資 蔡文能 計概 Slide 4 -14
Inter-Process Communication • Client-server – One server, many clients – Server must run continuously – Client initiates communication • Peer-to-peer – Two processes communicating as equals – Both as the client and server 2021/3/9 交大資 蔡文能 計概 Slide 4 -15
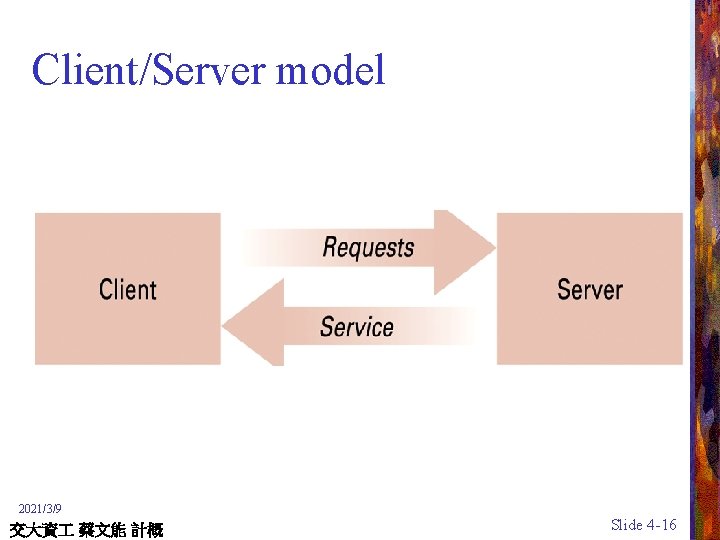
Client/Server model 2021/3/9 交大資 蔡文能 計概 Slide 4 -16

Client-Server vs. P 2 P 2021/3/9 交大資 蔡文能 計概 Slide 4 -17
Distributed Systems • Software consists of parts running on different computers in a network • Also known as network applications • Infrastructure usually provided by standardized toolkits • Example: Enterprise Java Beans from Sun Microsystems • Example: . NET framework from Microsoft • Example – Global information retrieval system such as WWW – World-wide entertainment systems such as the online games (線上遊戲) – Company-wide accounting and inventory systems such as online banks (網路銀行) 2021/3/9 交大資 蔡文能 計概 Slide 4 -18
Agenda Network Fundamentals üThe Internet The World Wide Web Network Protocols Security 2021/3/9 交大資 蔡文能 計概 Slide 4 -19
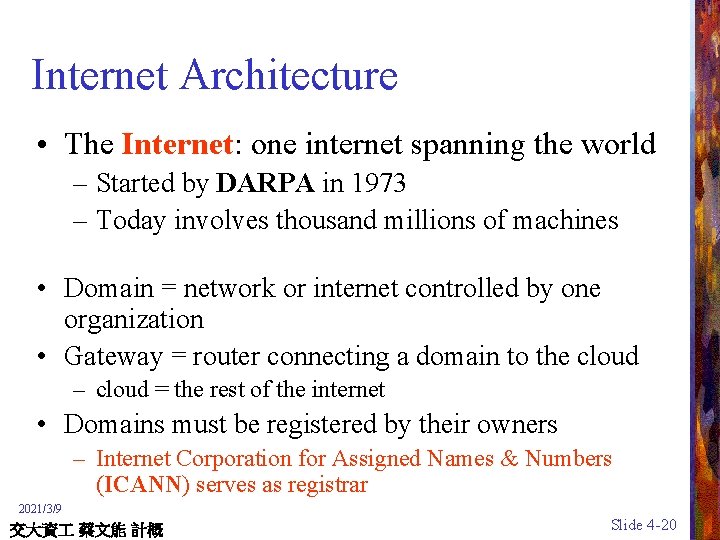
Internet Architecture • The Internet: one internet spanning the world – Started by DARPA in 1973 – Today involves thousand millions of machines • Domain = network or internet controlled by one organization • Gateway = router connecting a domain to the cloud – cloud = the rest of the internet • Domains must be registered by their owners – Internet Corporation for Assigned Names & Numbers (ICANN) serves as registrar 2021/3/9 交大資 蔡文能 計概 Slide 4 -20
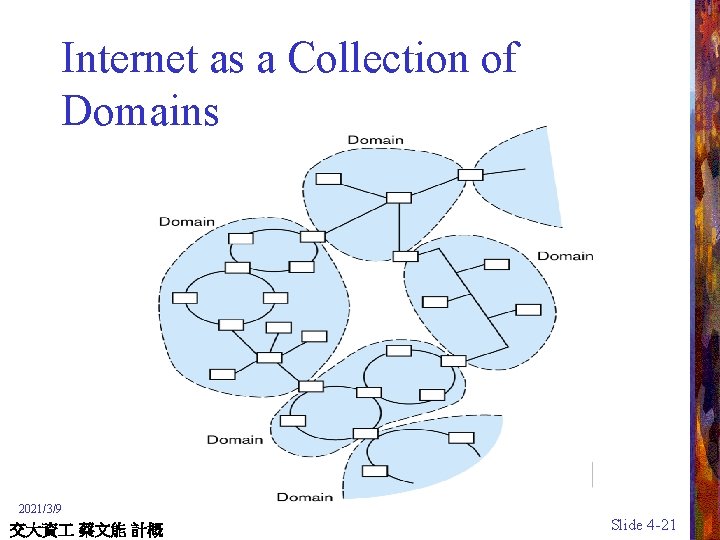
Internet as a Collection of Domains 2021/3/9 交大資 蔡文能 計概 Slide 4 -21
Establishment and Operation of Domains • Register with ICANN (Internet Corporation for Assigned Names and Numbers) • Attached to a network already in the Internet by a router (gateway, as the domain’s gate to the outside world, or cloud) • Any message being transmitted to a destination within the domain is handled within the domain • Any message being transmitted to a destination outside the domain is directed toward the gateway, where it is sent out to the cloud 2021/3/9 交大資 蔡文能 計概 Slide 4 -22
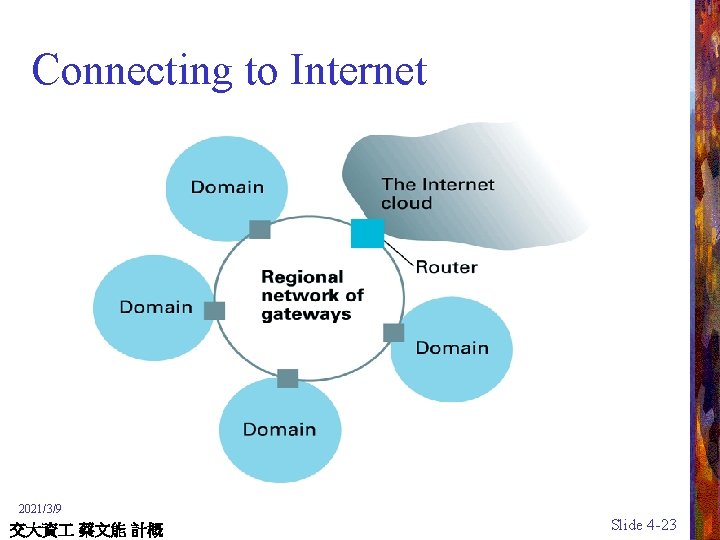
Connecting to Internet 2021/3/9 交大資 蔡文能 計概 Slide 4 -23
Strategies for connecting to the Internet • Large organization: buy a direct connection • Small organization or individual: link domain to the domain of an ISP • Individual: temporarily link computer into ISP’s domain ISP : Internet Service Provider 2021/3/9 交大資 蔡文能 計概 Slide 4 -24
Individuals Seeking Internet Access • Can register, implement, and maintain their domains • More common via a domain established by an organization or an Internet Service Provider (ISP) • Most cases takes the form of a temporary telephone connection (Dial-up MODEM, ADSL) 2021/3/9 交大資 蔡文能 計概 Slide 4 -25
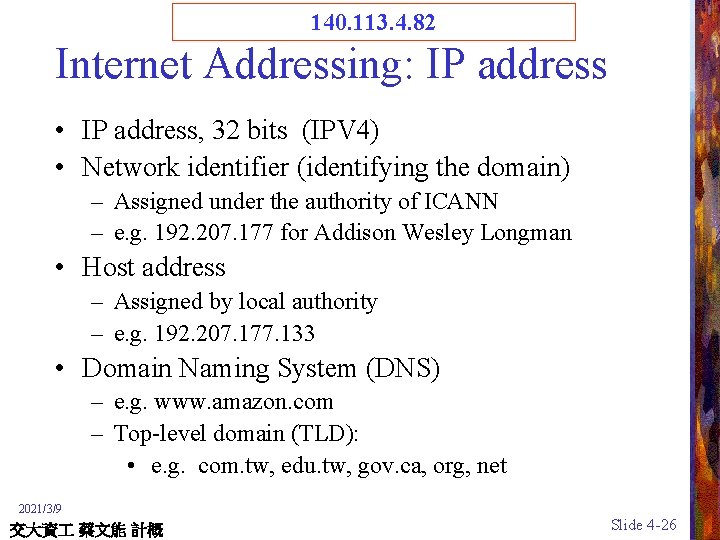
140. 113. 4. 82 Internet Addressing: IP address • IP address, 32 bits (IPV 4) • Network identifier (identifying the domain) – Assigned under the authority of ICANN – e. g. 192. 207. 177 for Addison Wesley Longman • Host address – Assigned by local authority – e. g. 192. 207. 177. 133 • Domain Naming System (DNS) – e. g. www. amazon. com – Top-level domain (TLD): • e. g. com. tw, edu. tw, gov. ca, org, net 2021/3/9 交大資 蔡文能 計概 Slide 4 -26
www. nctu. edu. tw Internet Addressing: host names • Host name = mnemonic name ( 注意 mn的 m 不發音) – Example: mymachine. aw. com – Domain name = part assigned by a registrar • Example: aw. com • Top level domain = classification of domain owner – By usage – Example: . com = commercial – By country – Example: . au = Australia – Subdomains and individual machine names • Assigned by domain owner • Domain owner must run a name server. 2021/3/9 交大資 蔡文能 計概 Slide 4 -27
www. nctu. edu. tw <--> 140. 113. 4. 82 Name server (Domain Name Service) • Maintains a directory containing the mnemonic address and the corresponding numeric IP address within the domain • Responds to requests regarding address information • All of the name servers throughout the Internet constitute an Internet-wide directory system • When a human requests that a message be sent to a destination given in mnemonic form, this system of name servers converts that mnemonic address into equivalent bit-pattern form • Such a task is normally completed in a fraction of a second 2021/3/9 交大資 蔡文能 計概 Slide 4 -28

The four formats of IP Addresses Class A 0 Net. ID B 10 Host. ID Net. ID C 110 D 1110 8 bits Host. ID Net. ID Multicast Address 8 bits 2021/3/9 交大資 蔡文能 計概 Slide 4 -29

Classes of IP Addresses According to the First Byte • Class A: 1– 126 (16 M hosts each) – 18 mit. edu; 試試 ping fahrvergnugen. mit. edu • Class B: 128 – 191 (65, 536 hosts each) – 140. 113 交大; 140. 114 清大; 140. 112 台大; 140. 115 中央; 140. 116 成大 • • Class C: 192 – 223 (256 hosts each) Class D: 224 – 239 (multicast mode) Class E: 240 – 255 (for future use) Loopback address: 127. 0. 0. 1 (localhost) 2021/3/9 交大資 蔡文能 計概 Slide 4 -30
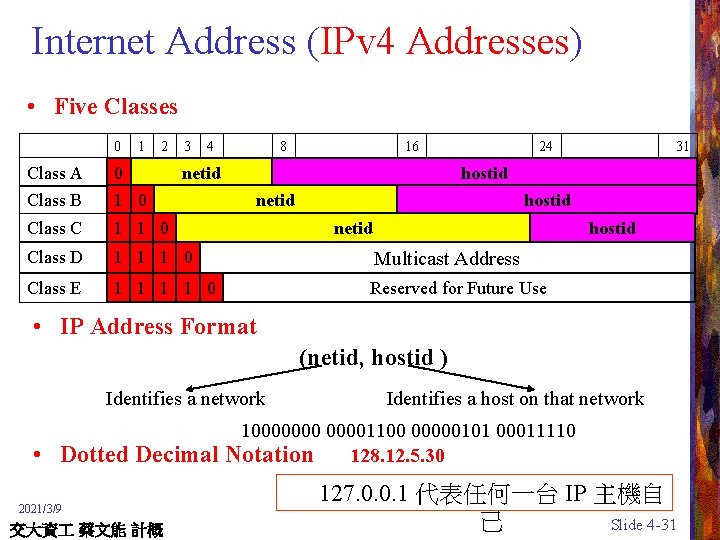
Internet Address (IPv 4 Addresses) • Five Classes 0 1 2 3 4 8 16 netid 24 Class A 0 Class B 1 0 Class C 1 1 0 Class D 1 1 1 0 Multicast Address Class E 1 1 0 Reserved for Future Use 31 hostid netid hostid • IP Address Format (netid, hostid ) Identifies a network • Identifies a host on that network 100000001100 00000101 00011110 Dotted Decimal Notation 128. 12. 5. 30 2021/3/9 交大資 蔡文能 計概 127. 0. 0. 1 代表任何一台 IP 主機自 己 Slide 4 -31


Internet Applications • • Electronic main (e-mail) File Transfer Protocol (FTP) Remote login: telnet, etc. World Wide Web (HTTP) 2021/3/9 交大資 蔡文能 計概 Slide 4 -33

Electronic mail • Mail server: set up by domain owner – Mail sent from domain members goes through mail server – Mail sent to domain members is collected by mail server – SMTP protocol (Simple Mail Transfer Protocol) – Mail delivered to clients on demand • POP 3 • IMAP 2021/3/9 交大資 蔡文能 計概 Slide 4 -34

Agenda Network Fundamentals The Internet üThe World Wide Web Network Protocols Network Security 2021/3/9 交大資 蔡文能 計概 Slide 4 -35

World Wide Web • Intertwined web of related information implemented on the Internet • Hypertext – Documents contain text, images, sound, and video, and may be linked to other documents (Hyperlinks) • Web pages – Hypertext document on the World Wide Web • Web site – Collection of closely related Web pages 2021/3/9 交大資 蔡文能 計概 Slide 4 -36
Browser and Web Page Server • Browser – As a client – Obtains materials requested by the user and presents these materials to the user in an organized manner • Web page server – Provides access to the documents on the machine as requested by clients 2021/3/9 交大資 蔡文能 計概 Slide 4 -37
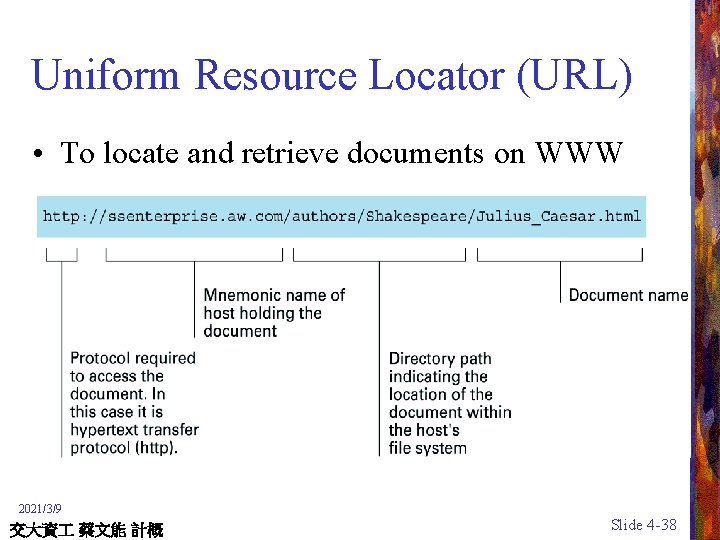
Uniform Resource Locator (URL) • To locate and retrieve documents on WWW 2021/3/9 交大資 蔡文能 計概 Slide 4 -38
Hypertext document format • Entire document is printable characters • Contains tags to control display – Display appearance – Links to other documents and content – Dynamic functions 2021/3/9 交大資 蔡文能 計概 Slide 4 -39
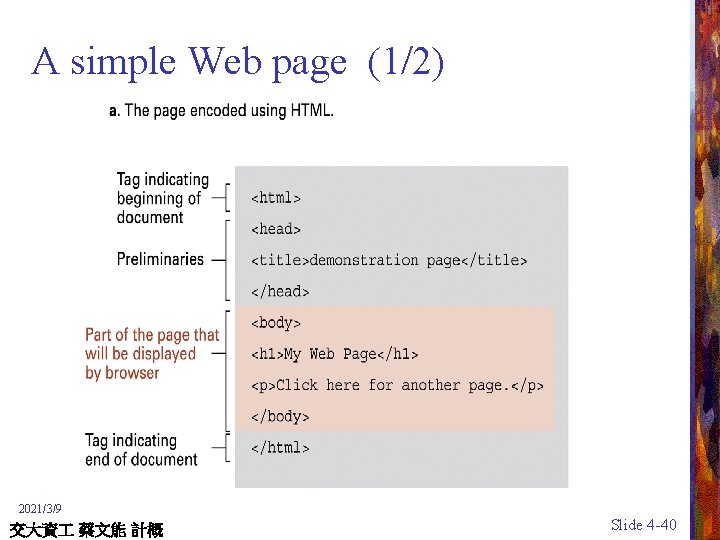
A simple Web page (1/2) 2021/3/9 交大資 蔡文能 計概 Slide 4 -40

A simple Web page (2/2) 2021/3/9 交大資 蔡文能 計概 Slide 4 -41
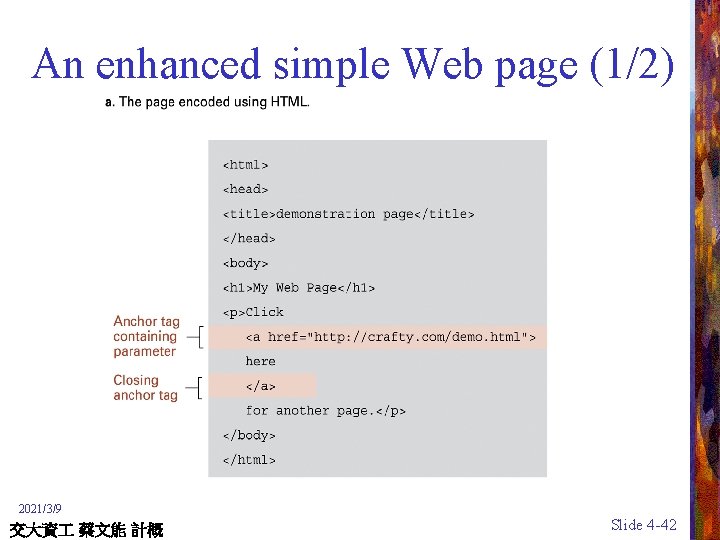
An enhanced simple Web page (1/2) 2021/3/9 交大資 蔡文能 計概 Slide 4 -42

An enhanced simple Web page (2/2) 2021/3/9 交大資 蔡文能 計概 Slide 4 -43

Dynamic web pages • Client-side – Examples: java applets, javascript/VBScript, Macromedia Flash • Server-side – Common Gateway Interface (CGI) – Servlets – ASP, PHP, JSP 2021/3/9 交大資 蔡文能 計概 Slide 4 -44
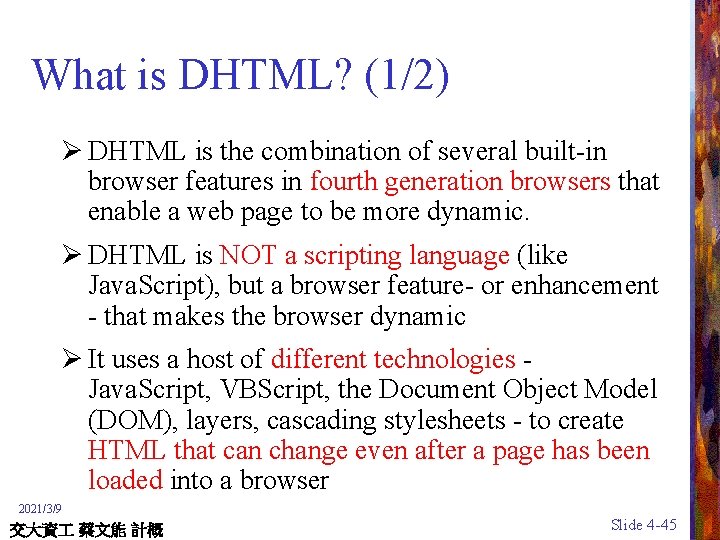
What is DHTML? (1/2) Ø DHTML is the combination of several built-in browser features in fourth generation browsers that enable a web page to be more dynamic. Ø DHTML is NOT a scripting language (like Java. Script), but a browser feature- or enhancement - that makes the browser dynamic Ø It uses a host of different technologies - Java. Script, VBScript, the Document Object Model (DOM), layers, cascading stylesheets - to create HTML that can change even after a page has been loaded into a browser 2021/3/9 交大資 蔡文能 計概 Slide 4 -45

What is DHTML? (2/2) Ø It is considered to be made up of – HTML – Cascading Style Sheets (CSS) – Scripting Language Ø All three of these components are linked via Document Object Model (DOM) Ø DOM is the interface that allows scripting languages to access the content, style, and structure of the web documents and change them dynamically 2021/3/9 交大資 蔡文能 計概 Slide 4 -46
Tools of DHTML Ø HTML and XML – Partitions and Organizes the content Ø CSS, XSL - CSS 1, CSSP, CSS 2 – Defines the Presentation of the content Ø Scripting - Java. Script, JScript, VBScript – Adds interactivity to the page Ø DOM- Document Object Model – Defines what and how elements are exposed for script access 2021/3/9 交大資 蔡文能 計概 Slide 4 -47
What is XUL ? • XML-based User interface Language (“zool”) • Makes UI building easier and faster • Uses W 3 C standards: HTML, XML, CSS, DOM • XPToolkit is the finite set of interface-specific elements created in XUL • XPFE (cross Platform Front End) is the front end created from XPToolkit • XUL provides flexibility and ease of use – Cross-platform UI easily – Power enough to build application UI – Ready-made widgets 2021/3/9 交大資 蔡文能 計概 Slide 4 -48
XUL and Java. Script • XUL interface is a collection of disconnected widgets until programmed • Using Java. Script and/or C++ • Java. Script included in XUL or a separate file <html: script> function Init. Window() { var checkbox = document. get. Element. By. ID(“remember”); if (checkbox) checkbox. checked = true; } </html: script> <html: script language=“javascript” src=“myscript. js”/> 2021/3/9 交大資 蔡文能 計概 Slide 4 -49

http: //W 3. org 2021/3/9 交大資 蔡文能 計概 Slide 4 -50
What is CSS? (1/2) Ø CSS is Cascading Style Sheets Ø It is a specification controlled by the World Wide Web Consortium (W 3 C). Ø HTML controls the organization of a Web page document Ø CSS controls the presentation and layout of the Web page document elements http: //w 3 c. org 2021/3/9 交大資 蔡文能 計概 Slide 4 -51
What is CSS? (2/2) Ø CSS 1 - visual presentation of elements Ø CSSP - positioning of elements Ø CSS 2 -visual and audio presentation of elements. It includes attributes from CSS 1 and CSS-P Ø What CSS is to HTML, XSL is to XML 2021/3/9 交大資 蔡文能 計概 Slide 4 -52
What CSS can do? Ø With CSS you can separate form from structure Ø Control layout (alignment, spacing, margins, colors, floating elements etc) Ø Maintain and update many pages faster and easier 2021/3/9 交大資 蔡文能 計概 Slide 4 -53
e. Xtensible Markup Language (XML) • XML: a language for constructing markup languages, similar to HTML – A descendant of SGML • Allows the development of new markup languages in that they emphasize semantics rather than appearance • http: //www. xml. org/ 2021/3/9 交大資 蔡文能 計概 Slide 4 -54

CSS-Terminology ØCSS is declared as rules: - Eg: H 1 {color: green} - Means that all text surrounded by the <H 1></H 1> tags should be displayed in green color ØA rule has two parts - H 1 {color: green} SELECTOR { DECLARATION } 2021/3/9 交大資 蔡文能 計概 Slide 4 -55
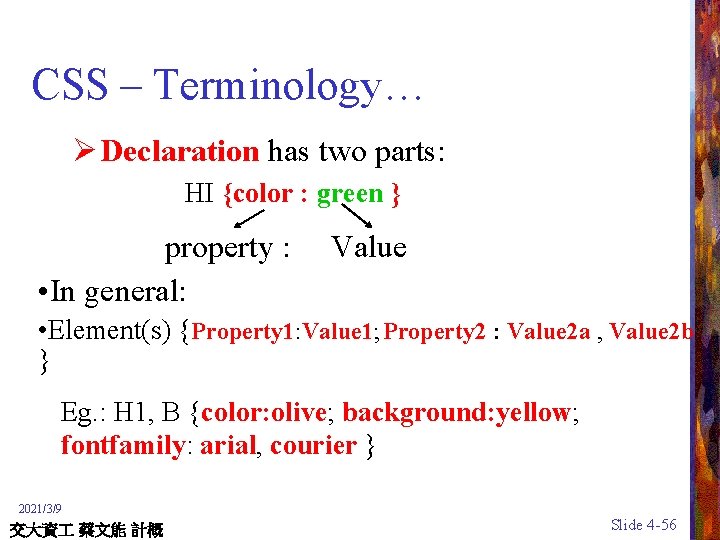
CSS – Terminology… Ø Declaration has two parts: HI {color : green } property : • In general: Value Property 1: Value 1; Property 2 : Value 2 a , Value 2 b • Element(s) { } Eg. : H 1, B {color: olive; background: yellow; fontfamily: arial, courier } 2021/3/9 交大資 蔡文能 計概 Slide 4 -56
CSS-Adding styles to web pages Ø Four ways – Embed a style sheet within HTML document – Link to an external stylesheet from the HTML document – Add styles inline in the HTML document – Importing style sheets 2021/3/9 交大資 蔡文能 計概 Slide 4 -57
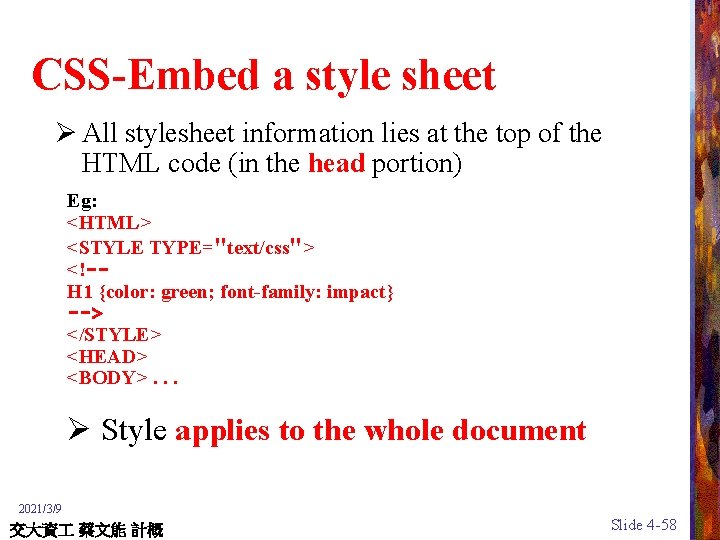
CSS-Embed a style sheet Ø All stylesheet information lies at the top of the HTML code (in the head portion) Eg: <HTML> <STYLE TYPE="text/css"> <!-H 1 {color: green; font-family: impact} --> </STYLE> <HEAD> <BODY>. . . Ø Style applies to the whole document 2021/3/9 交大資 蔡文能 計概 Slide 4 -58
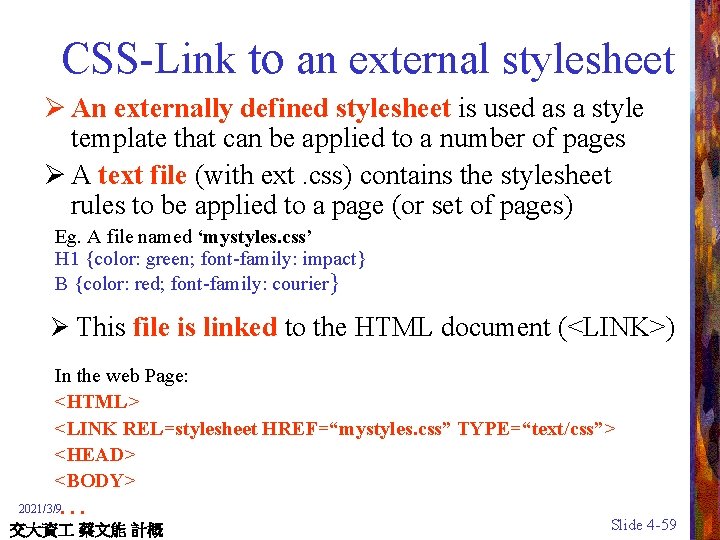
CSS-Link to an external stylesheet Ø An externally defined stylesheet is used as a style template that can be applied to a number of pages Ø A text file (with ext. css) contains the stylesheet rules to be applied to a page (or set of pages) Eg. A file named ‘mystyles. css’ H 1 {color: green; font-family: impact} B {color: red; font-family: courier} Ø This file is linked to the HTML document (<LINK>) In the web Page: <HTML> <LINK REL=stylesheet HREF=“mystyles. css” TYPE=“text/css”> <HEAD> <BODY> 2021/3/9 . . . 交大資 蔡文能 計概 Slide 4 -59

CSS-Add styles inline Ø Applying stylesheets rules to particular HTML tags Eg: <B STYLE="color: purple; background: yellow">Adding Inline styles</B> Ø The style applies to only that particular <B> tag 2021/3/9 交大資 蔡文能 計概 Slide 4 -60
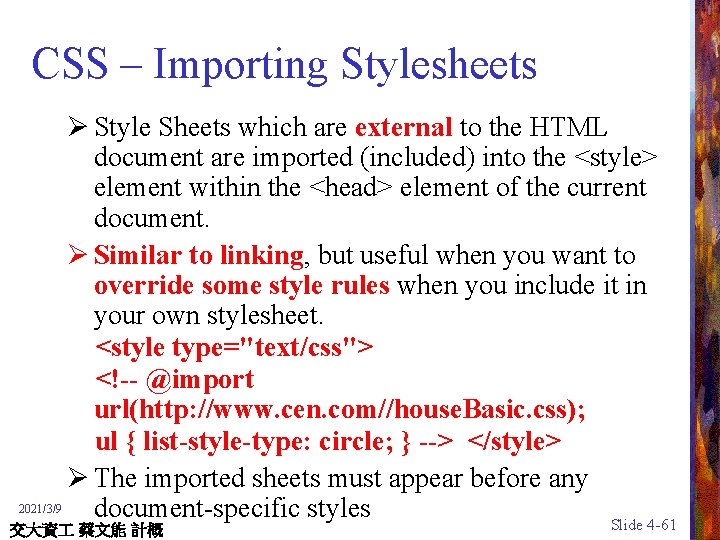
CSS – Importing Stylesheets Ø Style Sheets which are external to the HTML document are imported (included) into the <style> element within the <head> element of the current document. Ø Similar to linking, but useful when you want to override some style rules when you include it in your own stylesheet. <style type="text/css"> <!-- @import url(http: //www. cen. com//house. Basic. css); ul { list-style-type: circle; } --> </style> Ø The imported sheets must appear before any 2021/3/9 document-specific styles Slide 4 -61 交大資 蔡文能 計概
Agenda Network Fundamentals The Internet The World Wide Web üWeb. Network Protocols Network Security 2021/3/9 交大資 蔡文能 計概 Slide 4 -62
Network Protocols • Rules that govern the communication between different components within a computer system • Rules Obeyed by All Parties • Network protocols define the details of each activity – Delegate the right (privilege) to transmit message – Address messages – Package and unpack messages • Examples of Link layer protocol – Token ring protocol – CSMA/CD 2021/3/9 交大資 蔡文能 計概 Slide 4 -63
Token Ring Protocol (1/2) • • Popular in networks based on the ring topology All machines transmit message in a common direction Token, a unique bit pattern is passed around the ring Possession of the token gives a machine the authority to transmit its own messages • Without the token, a machine is only allowed to forward messages • Token is forwarded to next machine when a message has completed its cycle along the ring 2021/3/9 交大資 蔡文能 計概 Slide 4 -64
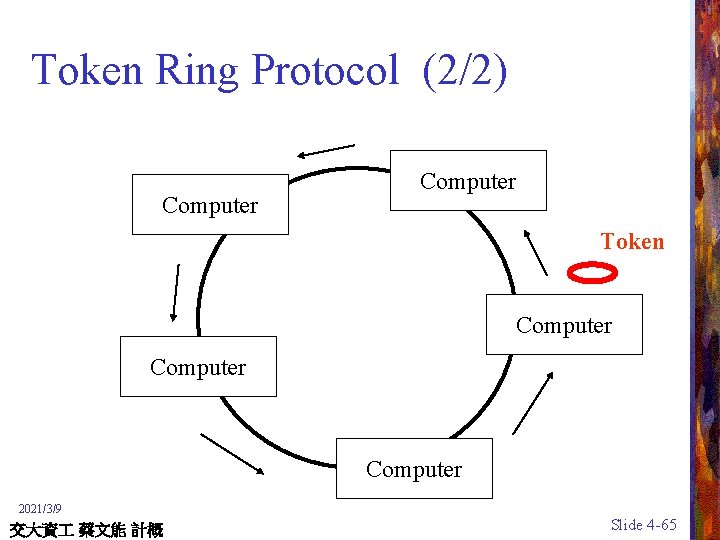
Token Ring Protocol (2/2) Computer Token Computer 2021/3/9 交大資 蔡文能 計概 Slide 4 -65

CSMA/CD Protocol (1/2) • Carrier Sense, Multiple Access with Collision Detection • Popular in Ethernet • Each message is broadcasted on the bus • Each machine monitors all messages but keeps only those addressed to itself • Wait until the bus is silent to transmit a message • When collision occurs, both machine pause for a brief random period of time before trying again 2021/3/9 交大資 蔡文能 計概 Slide 4 -66
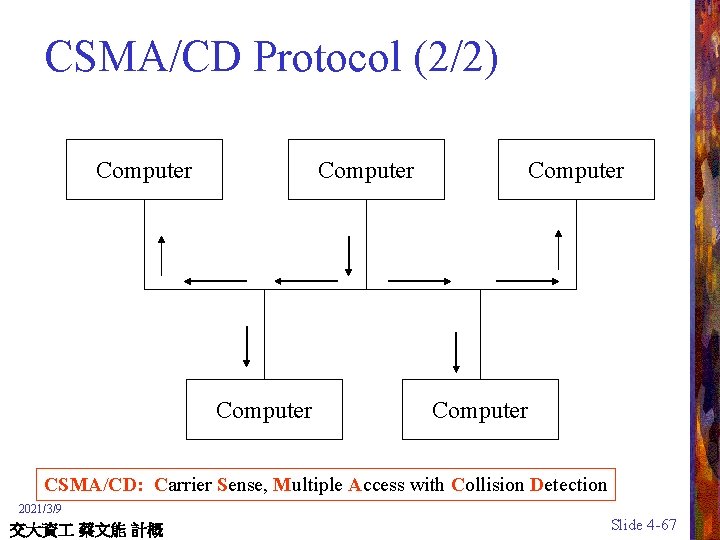
CSMA/CD Protocol (2/2) Computer Computer CSMA/CD: Carrier Sense, Multiple Access with Collision Detection 2021/3/9 交大資 蔡文能 計概 Slide 4 -67
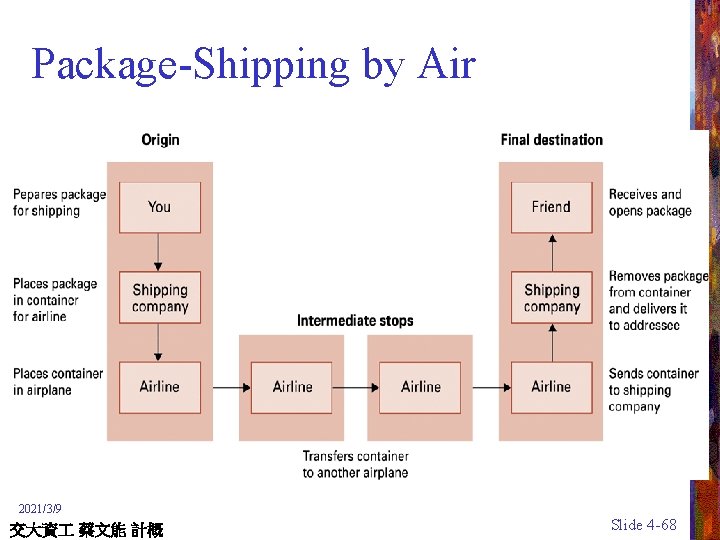
Package-Shipping by Air 2021/3/9 交大資 蔡文能 計概 Slide 4 -68

Message-Shipping by Internet 2021/3/9 交大資 蔡文能 計概 Slide 4 -69
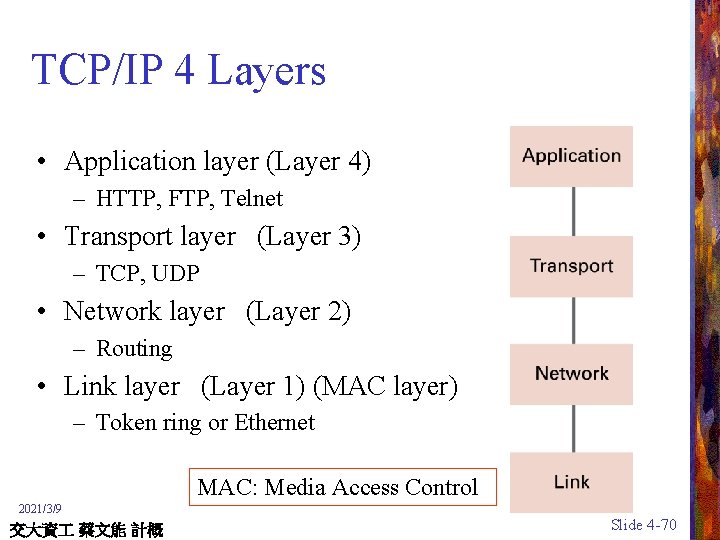
TCP/IP 4 Layers • Application layer (Layer 4) – HTTP, FTP, Telnet • Transport layer (Layer 3) – TCP, UDP • Network layer (Layer 2) – Routing • Link layer (Layer 1) (MAC layer) – Token ring or Ethernet MAC: Media Access Control 2021/3/9 交大資 蔡文能 計概 Slide 4 -70
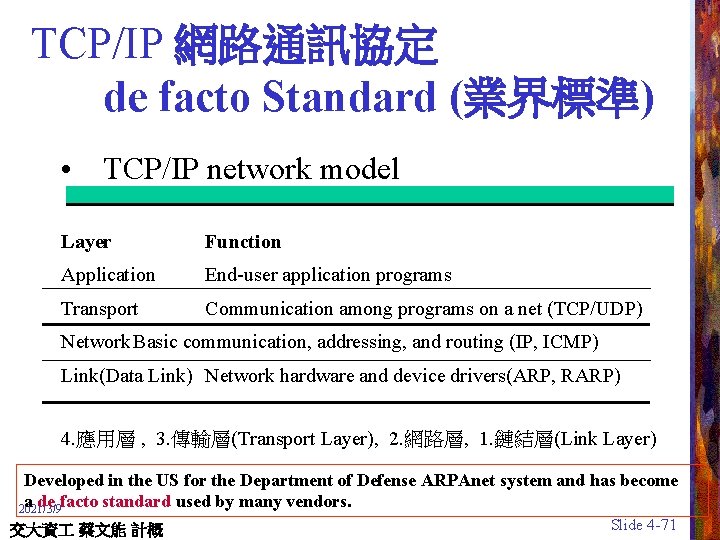
TCP/IP 網路通訊協定 de facto Standard (業界標準) • TCP/IP network model Layer Function Application End-user application programs Transport Communication among programs on a net (TCP/UDP) Network Basic communication, addressing, and routing (IP, ICMP) Link(Data Link) Network hardware and device drivers(ARP, RARP) 4. 應用層 , 3. 傳輸層(Transport Layer), 2. 網路層, 1. 鏈結層(Link Layer) Developed in the US for the Department of Defense ARPAnet system and has become a de facto standard used by many vendors. 2021/3/9 交大資 蔡文能 計概 Slide 4 -71

TCP/IP網路通訊協定 Layer 4 arp rlogin, talk, ftp, DNS 3 TCP 2 NFS, DNS UDP IP 1 traceroute ICMP ARP, Device Drivers Ethernet Header 2021/3/9 交大資 蔡文能 計概 IP Header TCP Header Application Data Ethernet Trailer ETHERNET FRAME Slide 4 -72
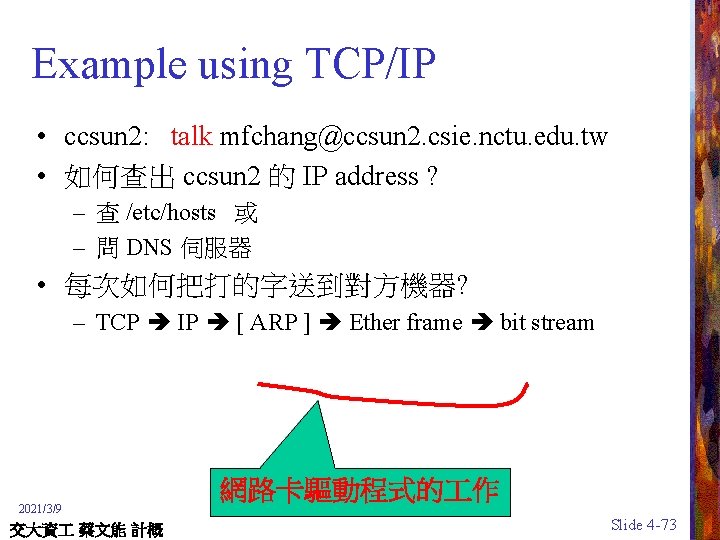
Example using TCP/IP • ccsun 2: talk mfchang@ccsun 2. csie. nctu. edu. tw • 如何查出 ccsun 2 的 IP address ? – 查 /etc/hosts 或 – 問 DNS 伺服器 • 每次如何把打的字送到對方機器? – TCP IP [ ARP ] Ether frame bit stream 2021/3/9 交大資 蔡文能 計概 網路卡驅動程式的 作 Slide 4 -73
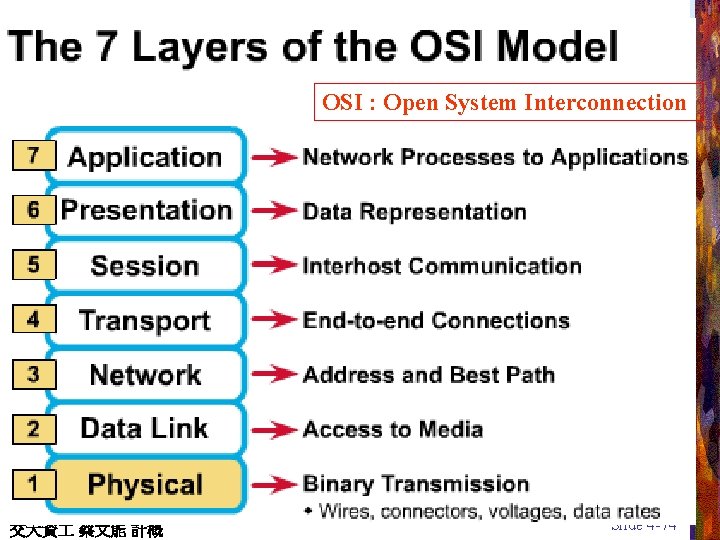
OSI : Open System Interconnection 2021/3/9 交大資 蔡文能 計概 Slide 4 -74
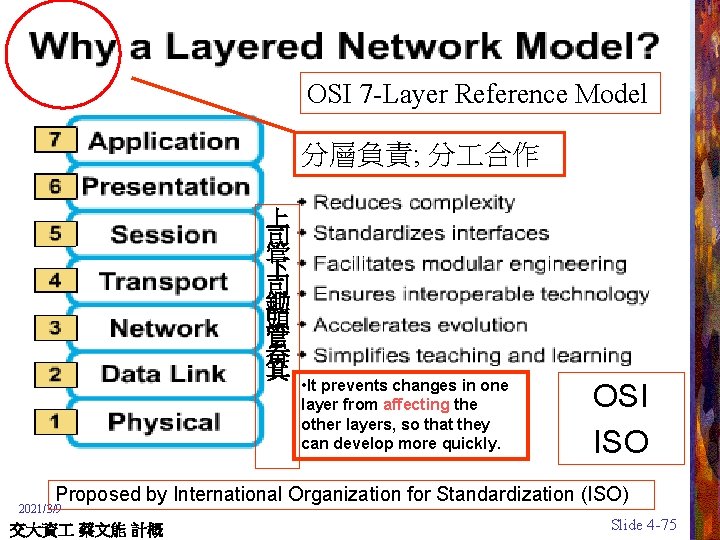
OSI 7 -Layer Reference Model 分層負責; 分 合作 上 司 管 下 司 鋤 頭 管 畚 箕 • It prevents changes in one layer from affecting the other layers, so that they can develop more quickly. OSI ISO Proposed by International Organization for Standardization (ISO) 2021/3/9 交大資 蔡文能 計概 Slide 4 -75
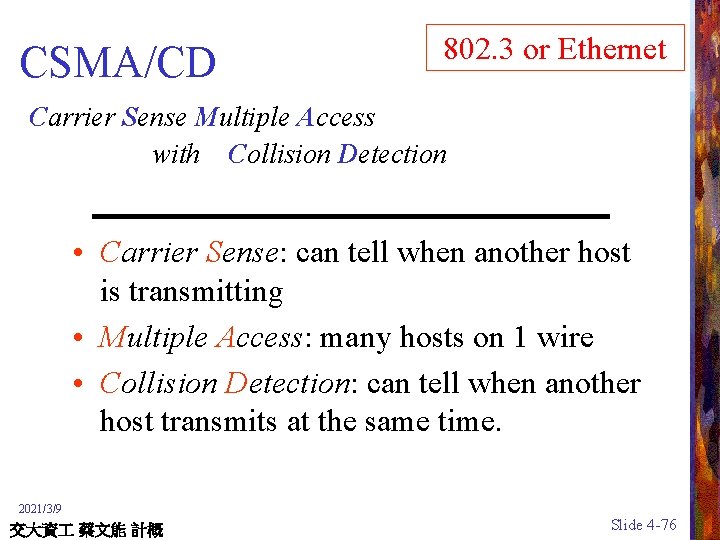
802. 3 or Ethernet CSMA/CD Carrier Sense Multiple Access with Collision Detection • Carrier Sense: can tell when another host is transmitting • Multiple Access: many hosts on 1 wire • Collision Detection: can tell when another host transmits at the same time. 2021/3/9 交大資 蔡文能 計概 Slide 4 -76

The Mechanisms of CSMA/CD • Each computer listens on the Ethernet – If not sensing data on the carrier, OK to send its own data (Carrier Sense, Multiple Access) – If sensing data on the carrier, check whether the data is addressed for itself • In case of simultaneous transmissions, (collisions) (Collision Detection) – The computer waits a random period of time before re-send – Exponential back-off 2021/3/9 CSMA/CD: Carrier Sense, Multiple Access with Collision Detection 交大資 蔡文能 計概 Slide 4 -77

Ethernet - IEEE 802. 3 (1/2 ) • Hub (集線器)– bus topology – Collision : CSMA/CD – 10 Mbps shared, 100 Mbps shared – Cheap • Switch (交換器)– star topology – No collision (送第一次仍會廣播, 之後記住MAC) – 100 Mbps each; 1 Gbps each for Gbit Switch – Expensive for Gbit Switch at now (2005) 其實 Ethernet 與 IEEE 802. 3 並非完全一樣 2021/3/9 交大資 蔡文能 計概 Slide 4 -78
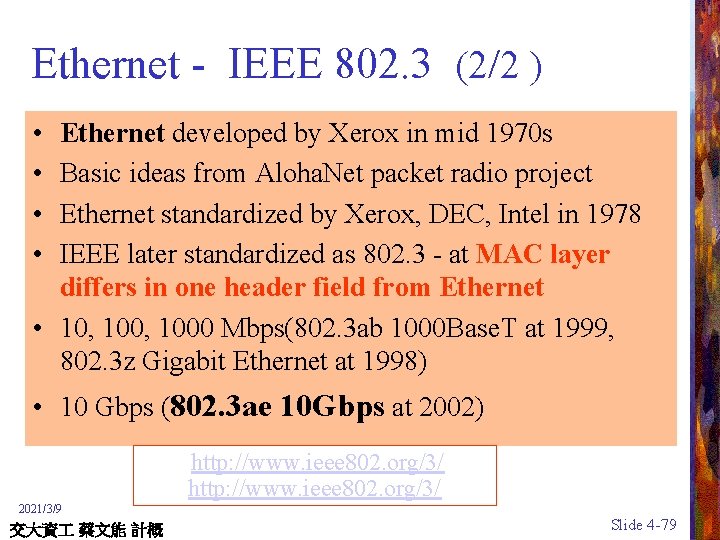
Ethernet - IEEE 802. 3 (2/2 ) • • Ethernet developed by Xerox in mid 1970 s Basic ideas from Aloha. Net packet radio project Ethernet standardized by Xerox, DEC, Intel in 1978 IEEE later standardized as 802. 3 - at MAC layer differs in one header field from Ethernet • 10, 1000 Mbps(802. 3 ab 1000 Base. T at 1999, 802. 3 z Gigabit Ethernet at 1998) • 10 Gbps (802. 3 ae 10 Gbps at 2002) http: //www. ieee 802. org/3/ 2021/3/9 交大資 蔡文能 計概 Slide 4 -79
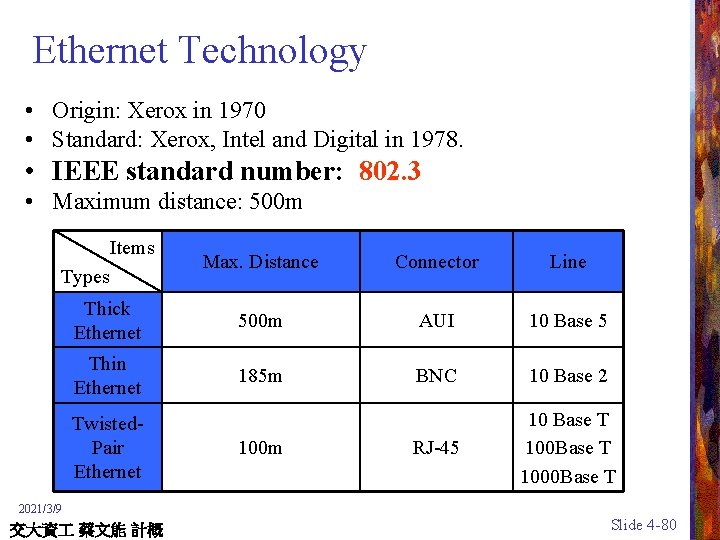
Ethernet Technology • Origin: Xerox in 1970 • Standard: Xerox, Intel and Digital in 1978. • IEEE standard number: 802. 3 • Maximum distance: 500 m Items Max. Distance Connector Line Thick Ethernet 500 m AUI 10 Base 5 Thin Ethernet 185 m BNC 10 Base 2 RJ-45 10 Base T 1000 Base T Types Twisted. Pair Ethernet 100 m 2021/3/9 交大資 蔡文能 計概 Slide 4 -80
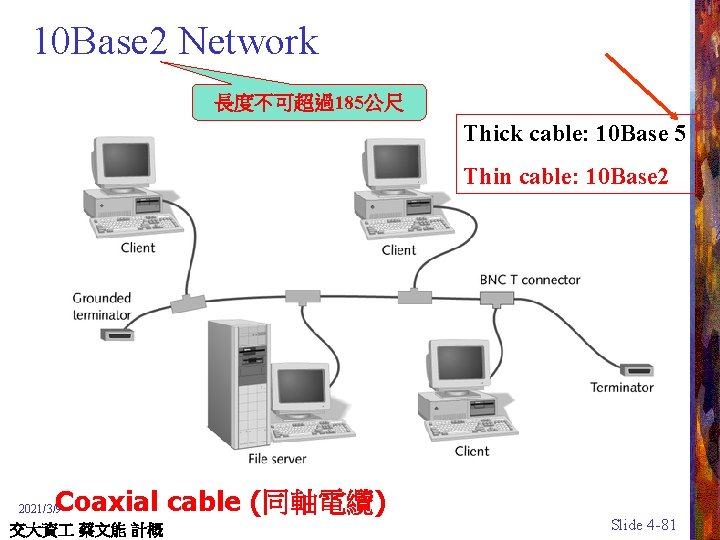
10 Base 2 Network 長度不可超過185公尺 Thick cable: 10 Base 5 Thin cable: 10 Base 2 Coaxial cable (同軸電纜) 2021/3/9 交大資 蔡文能 計概 Slide 4 -81
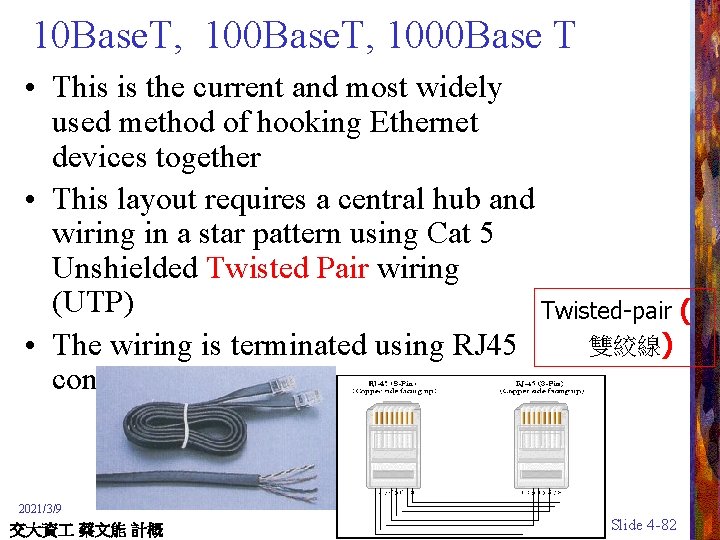
10 Base. T, 100 Base. T, 1000 Base T • This is the current and most widely used method of hooking Ethernet devices together • This layout requires a central hub and wiring in a star pattern using Cat 5 Unshielded Twisted Pair wiring (UTP) Twisted-pair ( 雙絞線) • The wiring is terminated using RJ 45 connectors 2021/3/9 交大資 蔡文能 計概 Slide 4 -82
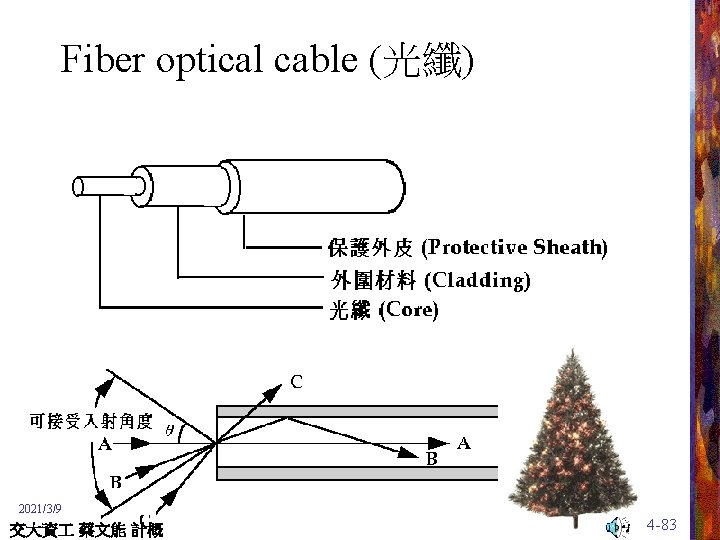
Fiber optical cable (光纖) 2021/3/9 交大資 蔡文能 計概 Slide 4 -83
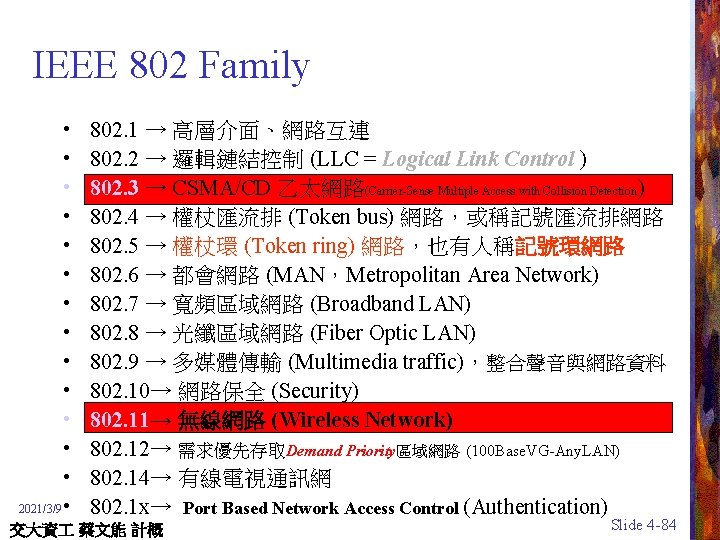
IEEE 802 Family • • • • 2021/3/9 • 802. 1 → 高層介面、網路互連 802. 2 → 邏輯鏈結控制 (LLC = Logical Link Control ) 802. 3 → CSMA/CD 乙太網路(Carrier-Sense Multiple Access with Collision Detection ) 802. 4 → 權杖匯流排 (Token bus) 網路,或稱記號匯流排網路 802. 5 → 權杖環 (Token ring) 網路,也有人稱記號環網路 802. 6 → 都會網路 (MAN,Metropolitan Area Network) 802. 7 → 寬頻區域網路 (Broadband LAN) 802. 8 → 光纖區域網路 (Fiber Optic LAN) 802. 9 → 多媒體傳輸 (Multimedia traffic),整合聲音與網路資料 802. 10→ 網路保全 (Security) 802. 11→ 無線網路 (Wireless Network) 802. 12→ 需求優先存取Demand Priority區域網路 (100 Base. VG-Any. LAN) 802. 14→ 有線電視通訊網 802. 1 x→ Port Based Network Access Control (Authentication) 交大資 蔡文能 計概 Slide 4 -84
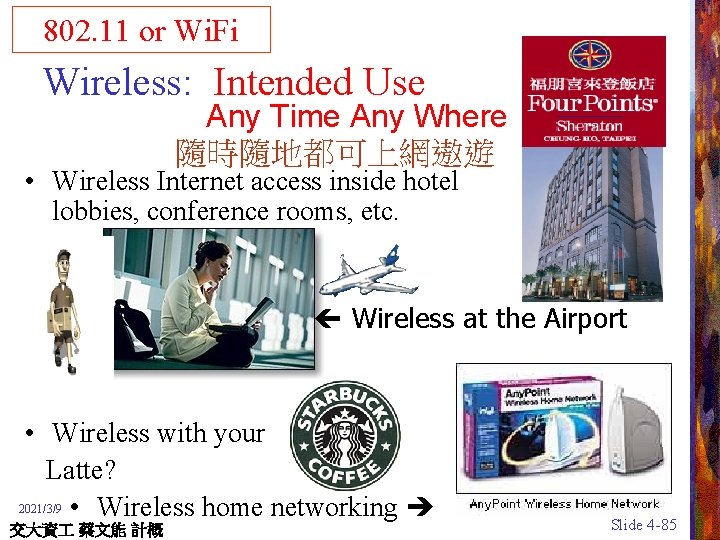
802. 11 or Wi. Fi Wireless: Intended Use Any Time Any Where 隨時隨地都可上網遨遊 • Wireless Internet access inside hotel lobbies, conference rooms, etc. Wireless at the Airport • Wireless with your Latte? 2021/3/9 • Wireless home networking . 交大資 蔡文能 計概 Slide 4 -85
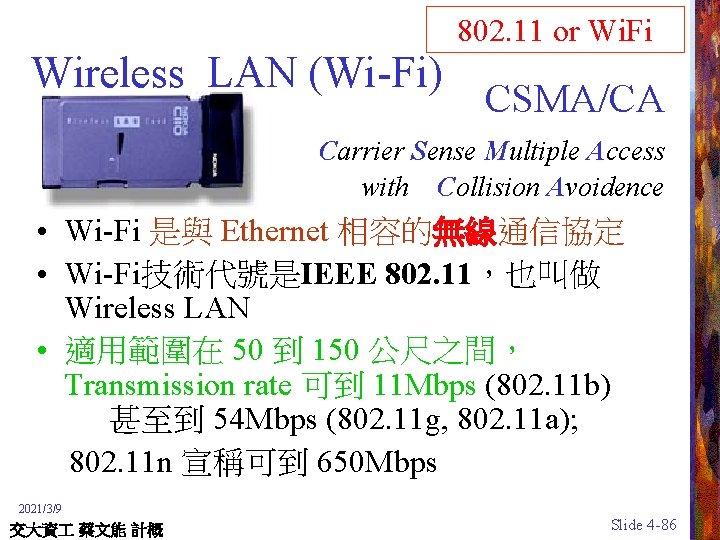
Wireless LAN (Wi-Fi) 802. 11 or Wi. Fi CSMA/CA Carrier Sense Multiple Access with Collision Avoidence • Wi-Fi 是與 Ethernet 相容的無線通信協定 • Wi-Fi技術代號是IEEE 802. 11,也叫做 Wireless LAN • 適用範圍在 50 到 150 公尺之間, Transmission rate 可到 11 Mbps (802. 11 b) 甚至到 54 Mbps (802. 11 g, 802. 11 a); 802. 11 n 宣稱可到 650 Mbps 2021/3/9 交大資 蔡文能 計概 Slide 4 -86

Differences between IEEE 802. 11? Frequency IEEE 802. 11 b IEEE 802. 11 a IEEE 802. 11 g 2. 4 G Hz 5 G Hz 2. 4 G Hz Transmission Rate 1~2 Mbps 1~11 Mbps 6~54 Mbps 22~54 Mbps Modulation Technique FHSS/DSSS OFDM PBCC-22 + CCK-OFDM 802. 11 n ? 2021/3/9 交大資 蔡文能 計概 Slide 4 -87
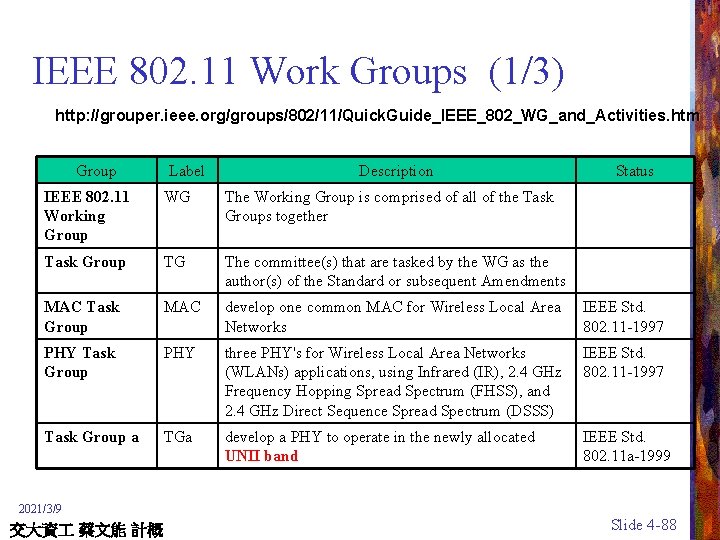
IEEE 802. 11 Work Groups (1/3) http: //grouper. ieee. org/groups/802/11/Quick. Guide_IEEE_802_WG_and_Activities. htm Group Label Description Status IEEE 802. 11 Working Group WG The Working Group is comprised of all of the Task Groups together Task Group TG The committee(s) that are tasked by the WG as the author(s) of the Standard or subsequent Amendments MAC Task Group MAC develop one common MAC for Wireless Local Area Networks IEEE Std. 802. 11 -1997 PHY Task Group PHY three PHY's for Wireless Local Area Networks (WLANs) applications, using Infrared (IR), 2. 4 GHz Frequency Hopping Spread Spectrum (FHSS), and 2. 4 GHz Direct Sequence Spread Spectrum (DSSS) IEEE Std. 802. 11 -1997 Task Group a TGa develop a PHY to operate in the newly allocated UNII band IEEE Std. 802. 11 a-1999 2021/3/9 交大資 蔡文能 計概 Slide 4 -88

IEEE 802. 11 Work Group(2/3) Group Label Description Status Task Group b TGb develop a standard for a higher rate PHY in the 2. 4 GHz band IEEE Std. 802. 11 b-1999 Task Group bcor 1 TGb. Cor 1 correct deficiencies in the MIB definition of 802. 11 b Ongoing Task Group c TGc add a subclause under 2. 5 Support of the Internal Sub- Part of IEEE Layer Service by specific MAC Procedures to cover 802. 1 D bridge operation with IEEE 802. 11 MACs Task Group d TGd define the physical layer requirements Ongoing Task Group e TGe Enhance the 802. 11 Medium Access Control (MAC) to improve and manage Quality of Service, provide classes of service, and enhanced security and authentication mechanisms Ongoing 2021/3/9 交大資 蔡文能 計概 Slide 4 -89

IEEE 802. 11 Work Group(3/3) Group Label Description Status Task Group f TGf develop recommended practices for an Inter-Access Point Ongoing Protocol (IAPP) which provides the necessary capabilities to achieve multi-vendor Access Point interoperability Task Group g TGg develop a higher speed(s) PHY extension to the 802. 11 b standard Ongoing Task Group h TGh Enhance the 802. 11 Medium Access Control (MAC) standard and 802. 11 a High Speed Physical Layer (PHY) in the 5 GHz Band Ongoing Task Group i TGi Enhance the 802. 11 Medium Access Control (MAC) to enhance security and authentication mechanisms Ongoing Study Group SG Investigates the interest of placing something in the Standard 2021/3/9 交大資 蔡文能 計概 Slide 4 -90

IEEE 802. 11 (Wireless Ethernet) 802. 11 or Wi. Fi • CSMA/CA • Why can’t we use regular Ethernet for wireless? – Ethernet: A sees B, B sees C, A sees C – Wireless: Hidden node problem A sees B, B sees C, yet A does not see C CSMA/CA A B C Carrier Sense Multiple Access with Collision Avoidence 2021/3/9 交大資 蔡文能 計概 Slide 4 -91
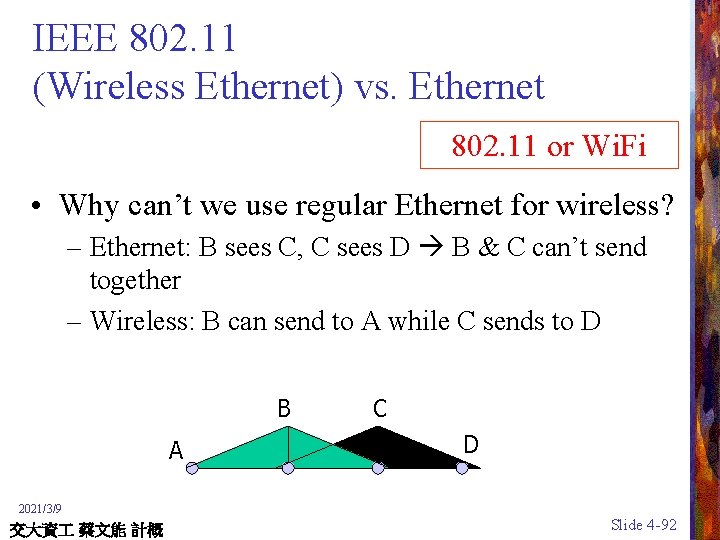
IEEE 802. 11 (Wireless Ethernet) vs. Ethernet 802. 11 or Wi. Fi • Why can’t we use regular Ethernet for wireless? – Ethernet: B sees C, C sees D B & C can’t send together – Wireless: B can send to A while C sends to D B A C D 2021/3/9 交大資 蔡文能 計概 Slide 4 -92
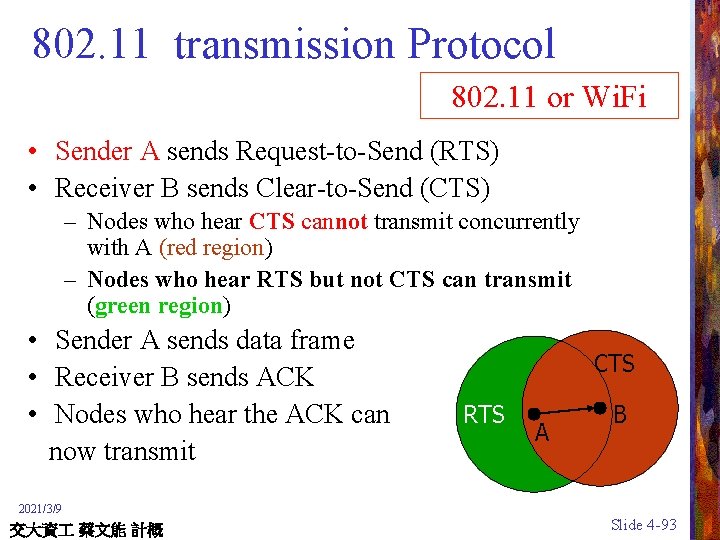
802. 11 transmission Protocol 802. 11 or Wi. Fi • Sender A sends Request-to-Send (RTS) • Receiver B sends Clear-to-Send (CTS) – Nodes who hear CTS cannot transmit concurrently with A (red region) – Nodes who hear RTS but not CTS can transmit (green region) • Sender A sends data frame • Receiver B sends ACK • Nodes who hear the ACK can now transmit CTS RTS A B 2021/3/9 交大資 蔡文能 計概 Slide 4 -93
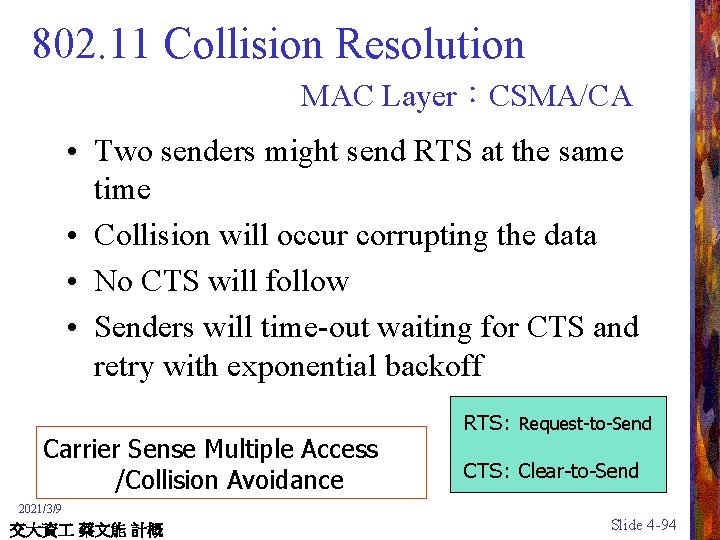
802. 11 Collision Resolution MAC Layer:CSMA/CA • Two senders might send RTS at the same time • Collision will occur corrupting the data • No CTS will follow • Senders will time-out waiting for CTS and retry with exponential backoff Carrier Sense Multiple Access /Collision Avoidance RTS: Request-to-Send CTS: Clear-to-Send 2021/3/9 交大資 蔡文能 計概 Slide 4 -94
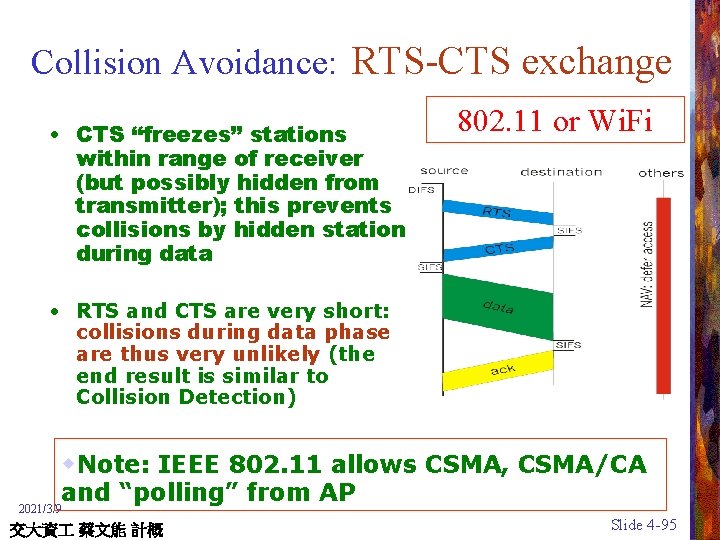
Collision Avoidance: RTS-CTS exchange • CTS “freezes” stations within range of receiver (but possibly hidden from transmitter); this prevents collisions by hidden station during data 802. 11 or Wi. Fi • RTS and CTS are very short: collisions during data phase are thus very unlikely (the end result is similar to Collision Detection) w. Note: IEEE 802. 11 allows CSMA, CSMA/CA and “polling” from AP 2021/3/9 交大資 蔡文能 計概 Slide 4 -95
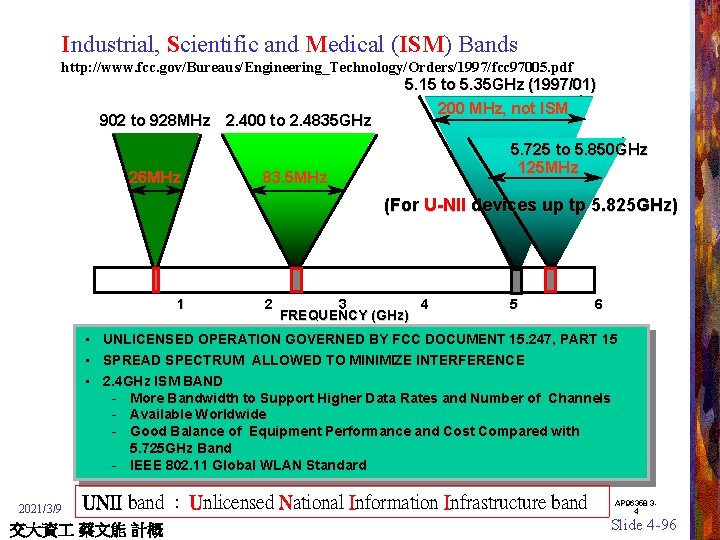
Industrial, Scientific and Medical (ISM) Bands http: //www. fcc. gov/Bureaus/Engineering_Technology/Orders/1997/fcc 97005. pdf 902 to 928 MHz 2. 400 to 2. 4835 GHz 26 MHz 5. 15 to 5. 35 GHz (1997/01) 200 MHz, not ISM 5. 725 to 5. 850 GHz 125 MHz 83. 5 MHz (For U-NII devices up tp 5. 825 GHz) 1 • • • 2021/3/9 2 3 4 FREQUENCY (GHz) 5 6 UNLICENSED OPERATION GOVERNED BY FCC DOCUMENT 15. 247, PART 15 SPREAD SPECTRUM ALLOWED TO MINIMIZE INTERFERENCE 2. 4 GHz ISM BAND - More Bandwidth to Support Higher Data Rates and Number of Channels - Available Worldwide - Good Balance of Equipment Performance and Cost Compared with 5. 725 GHz Band - IEEE 802. 11 Global WLAN Standard UNII band : Unlicensed National Information Infrastructure band 交大資 蔡文能 計概 AP 96358 34 Slide 4 -96
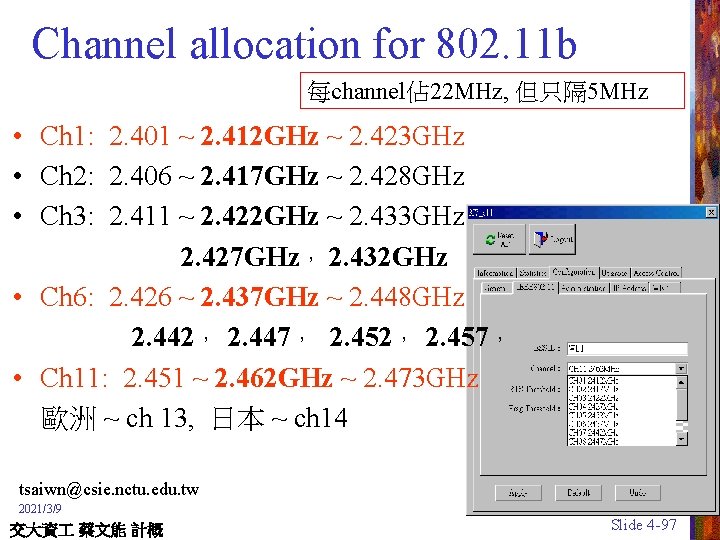
Channel allocation for 802. 11 b 每channel佔 22 MHz, 但只隔 5 MHz • Ch 1: 2. 401 ~ 2. 412 GHz ~ 2. 423 GHz • Ch 2: 2. 406 ~ 2. 417 GHz ~ 2. 428 GHz • Ch 3: 2. 411 ~ 2. 422 GHz ~ 2. 433 GHz 2. 427 GHz, 2. 432 GHz • Ch 6: 2. 426 ~ 2. 437 GHz ~ 2. 448 GHz 2. 442, 2. 447, 2. 452, 2. 457, • Ch 11: 2. 451 ~ 2. 462 GHz ~ 2. 473 GHz 歐洲 ~ ch 13, 日本 ~ ch 14 tsaiwn@csie. nctu. edu. tw 2021/3/9 交大資 蔡文能 計概 Slide 4 -97

Channel assignment 802. 11 or Wi. Fi 三 樓 Ch 11 Ch 6 Ch 11 Ch 1 二 樓 一 樓 Ch 1 Ch 6 Ch 11 2021/3/9 交大資 蔡文能 計概 Slide 4 -98

Wireless Signal /Noise Ratio (S/N Ratio) tsaiwn@csie. nctu. edu. tw 2021/3/9 交大資 蔡文能 計概 Slide 4 -99
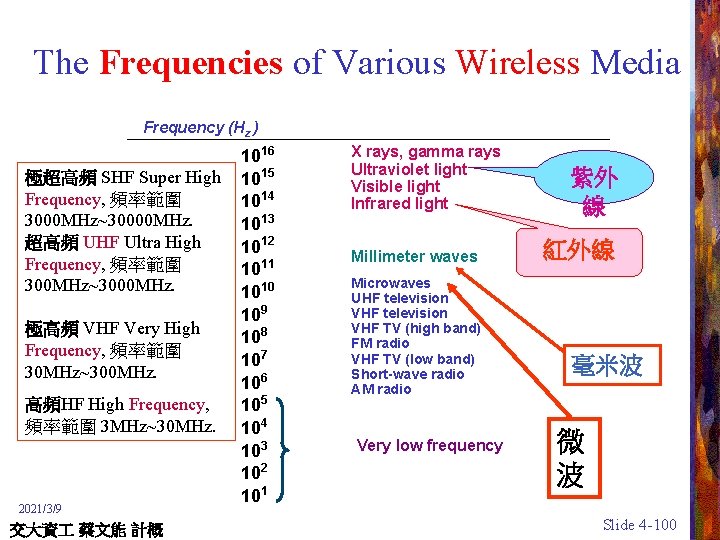
The Frequencies of Various Wireless Media Frequency (Hz ) 1016 極超高頻 SHF Super High 1015 Frequency, 頻率範圍 1014 3000 MHz~30000 MHz. 1013 超高頻 UHF Ultra High 1012 Frequency, 頻率範圍 1011 300 MHz~3000 MHz. 1010 109 極高頻 VHF Very High 108 Frequency, 頻率範圍 107 30 MHz~300 MHz. 106 高頻HF High Frequency, 105 頻率範圍 3 MHz~30 MHz. 104 103 102 101 X rays, gamma rays Ultraviolet light Visible light Infrared light Millimeter waves Microwaves UHF television VHF TV (high band) FM radio VHF TV (low band) Short-wave radio AM radio Very low frequency 紫外 線 紅外線 毫米波 微 波 2021/3/9 交大資 蔡文能 計概 Slide 4 -100

tracert ( traceroute) ( 或也有系統用 tr ) 利用封包中的 TTL 2021/3/9 tracert 140. 113. 1. 1 交大資 蔡文能 計概 Slide 4 -101


Agenda Network Fundamentals The Internet The World Wide Web Network Protocols üNetwork Security 2021/3/9 交大資 蔡文能 計概 Slide 4 -104
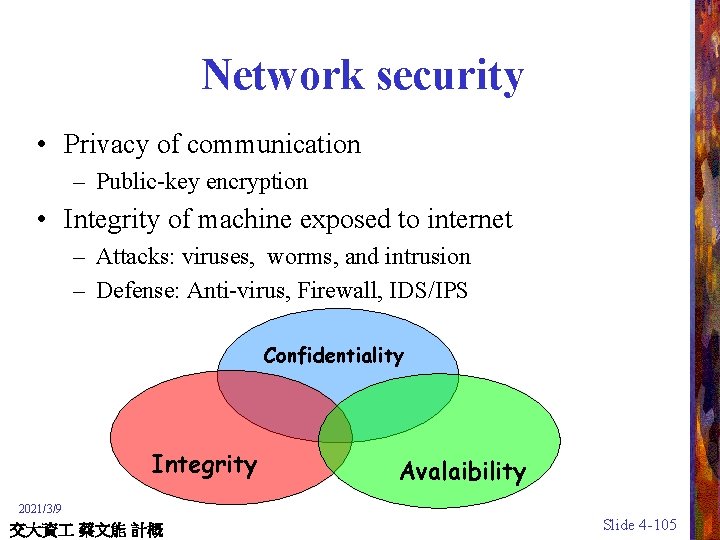
Network security • Privacy of communication – Public-key encryption • Integrity of machine exposed to internet – Attacks: viruses, worms, and intrusion – Defense: Anti-virus, Firewall, IDS/IPS Confidentiality Integrity Avalaibility 2021/3/9 交大資 蔡文能 計概 Slide 4 -105
Public-Key Encryption (1/2) • Public key is used to encode messages and is known by all people authorized to generate messages • Private key is required to decode messages and is known by only the person who is to receive messages 2021/3/9 交大資 蔡文能 計概 Slide 4 -106
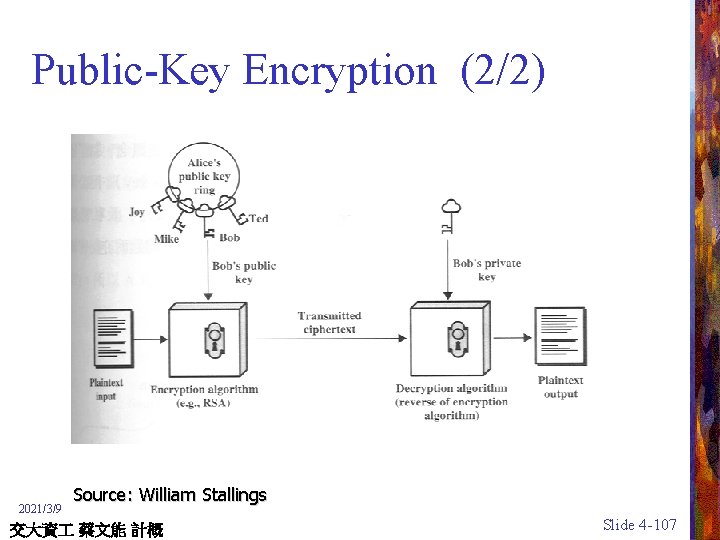
Public-Key Encryption (2/2) 2021/3/9 Source: William Stallings 交大資 蔡文能 計概 Slide 4 -107

Digital Signature 數位簽章 for Authentication 2021/3/9 Source: William Stallings 交大資 蔡文能 計概 Slide 4 -108

Public-Key Cryptographic Algorithms • RSA and Diffie-Hellman • RSA - Ron Rives, Adi Shamir and Len Adleman at MIT, in 1977. – RSA is a block cipher – The most widely implemented • Diffie-Hellman in 1976 一次切取一區塊(例 64 Bytes)來加解密 – Echange a secret key securely – Compute discrete logarithms Block cipher vs. Stream cipher 2021/3/9 交大資 蔡文能 計概 Slide 4 -109
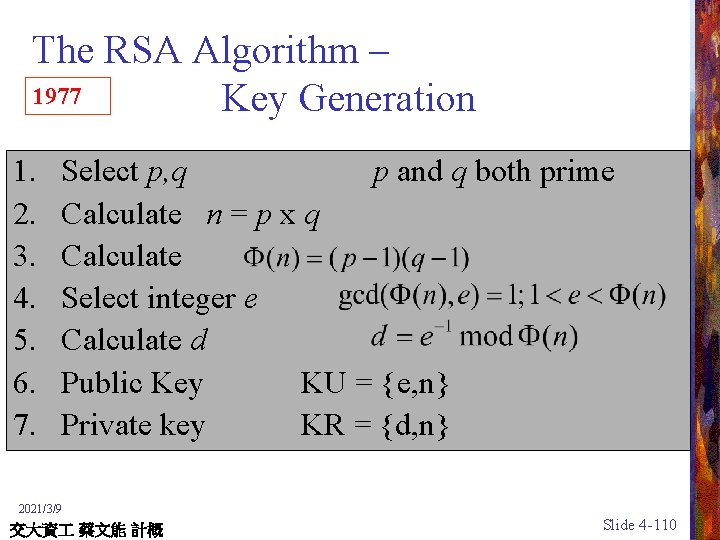
The RSA Algorithm – 1977 Key Generation 1. 2. 3. 4. 5. 6. 7. Select p, q p and q both prime Calculate n = p x q Calculate Select integer e Calculate d Public Key KU = {e, n} Private key KR = {d, n} 2021/3/9 交大資 蔡文能 計概 Slide 4 -110
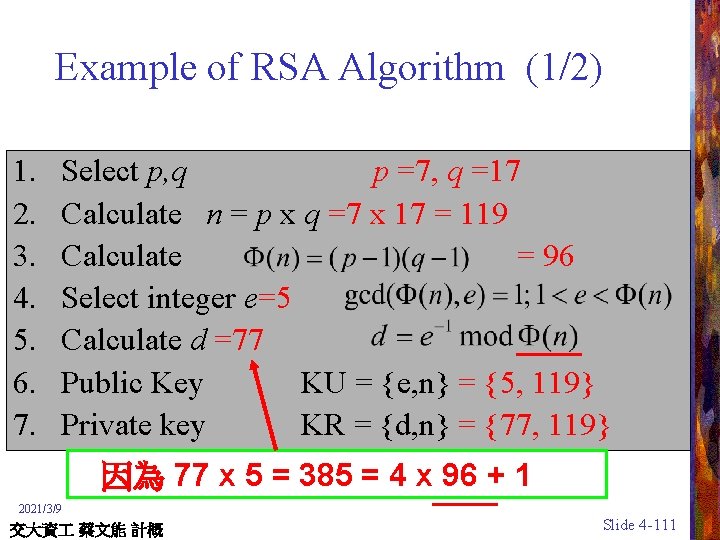
Example of RSA Algorithm (1/2) 1. 2. 3. 4. 5. 6. 7. Select p, q p =7, q =17 Calculate n = p x q =7 x 17 = 119 Calculate = 96 Select integer e=5 Calculate d =77 Public Key KU = {e, n} = {5, 119} Private key KR = {d, n} = {77, 119} 因為 77 x 5 = 385 = 4 x 96 + 1 2021/3/9 交大資 蔡文能 計概 Slide 4 -111
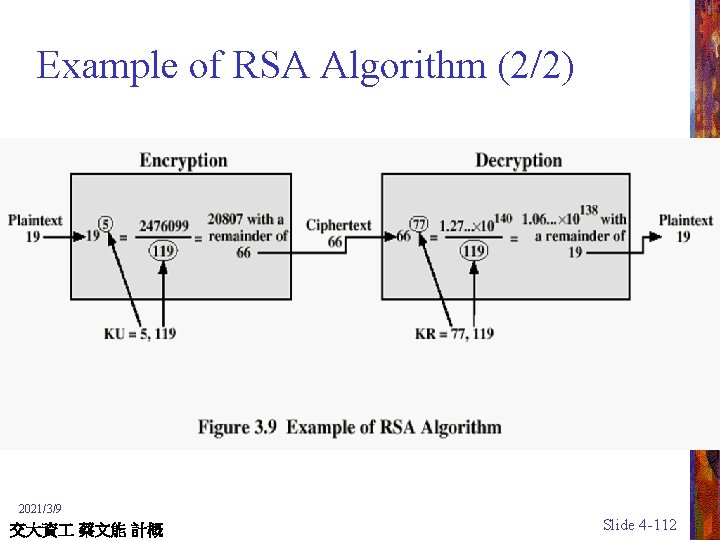
Example of RSA Algorithm (2/2) 2021/3/9 交大資 蔡文能 計概 Slide 4 -112

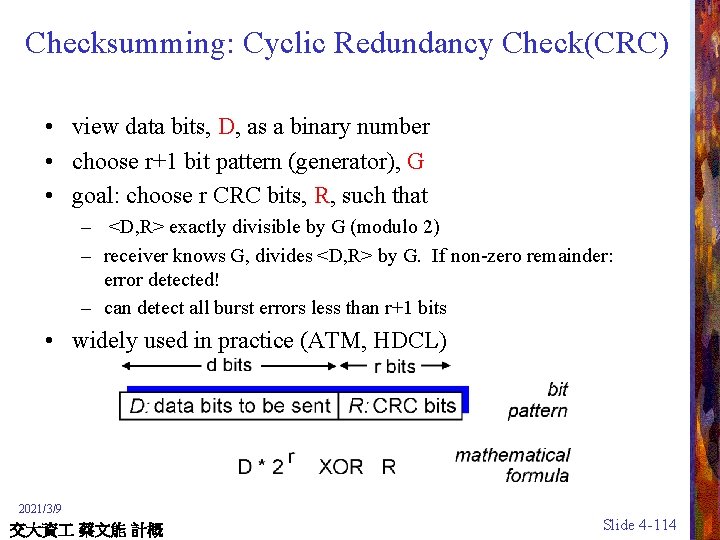
Checksumming: Cyclic Redundancy Check(CRC) • view data bits, D, as a binary number • choose r+1 bit pattern (generator), G • goal: choose r CRC bits, R, such that – <D, R> exactly divisible by G (modulo 2) – receiver knows G, divides <D, R> by G. If non-zero remainder: error detected! – can detect all burst errors less than r+1 bits • widely used in practice (ATM, HDCL) 2021/3/9 交大資 蔡文能 計概 Slide 4 -114

CRC Example Want: D. 2 r XOR R = n. G equivalently: D. 2 r = n. G XOR R equivalently: if we divide D. 2 r by G, want remainder R R = remainder[ D. 2 r G ] 2021/3/9 交大資 蔡文能 計概 Slide 4 -115
Security Attacks • Interruption: This is an attack on availability • Interception: This is an attack on confidentiality • Modification: This is an attack on integrity • Fabrication: This is an attack on authenticity 2021/3/9 交大資 蔡文能 計概 Slide 4 -116



Malicious codes • Undesired code that might cause damage to your computer system – Virus – Worm – Trojan horse 2021/3/9 交大資 蔡文能 計概 Slide 4 -122
Viruses • Program segment that attaches itself to other programs in the computer system • When executed the virus may perform malicious acts that are readily noticeable or merely search for other programs to which it can attach copies of itself • If an infected program is transferred to a new machine, the virus will begin to infect programs on the new machine as soon as it is executed 2021/3/9 交大資 蔡文能 計概 Slide 4 -123
Worms • Autonomous program that transfers itself through a network, taking up residence in the machines and forwarding copies of itself through the network • Can be designed merely to replicate themselves or to perform additional vandalism • 蠕蟲 電腦蠕蟲病毒是一種惡意程式(或一組程式), 可將本身的功能或程式碼透過網路散播到其他電腦。 參考: 趨勢科技網站http: //www. trend. com. tw/ 2021/3/9 交大資 蔡文能 計概 Slide 4 -124
Trojan Horse • Propagation – A program that does not replicate • Spreading model – Someone emails a Trojan Horse to you – You copy a program with embedded Trojan Horse – Visit a Web site contains Trojan Horse 2021/3/9 交大資 蔡文能 計概 Slide 4 -125
Distinction between them • Virus – Fast spreading within a system • Worm – Fast spreading across systems • Trojan horse vs. the other two – No self-replication 2021/3/9 交大資 蔡文能 計概 Slide 4 -126
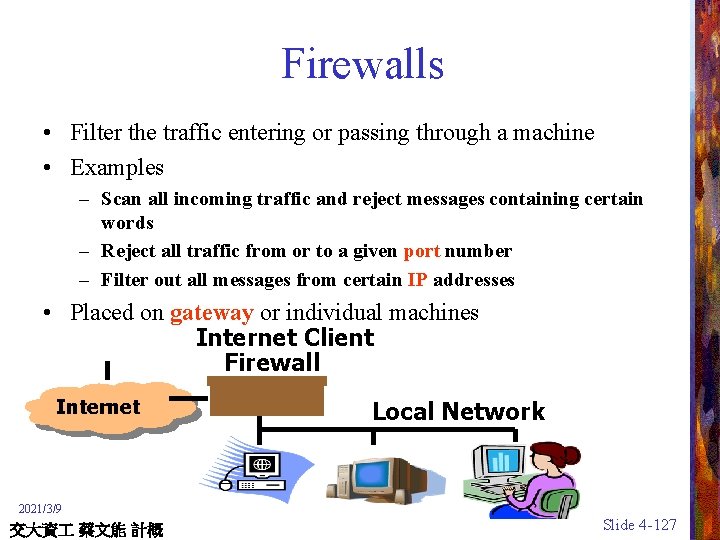
Firewalls • Filter the traffic entering or passing through a machine • Examples – Scan all incoming traffic and reject messages containing certain words – Reject all traffic from or to a given port number – Filter out all messages from certain IP addresses • Placed on gateway or individual machines Internet Client Firewall Internet Local Network 2021/3/9 交大資 蔡文能 計概 Slide 4 -127
Thank You! Networking and the Internet 謝謝捧場 tsaiwn@csie. nctu. edu. tw 2021/3/9 交大資 蔡文能 計概 蔡文能 Slide 4 -128
- Slides: 128