Network Security Principles Practices By Saadat Malik Cisco
Network Security Principles & Practices By Saadat Malik Cisco Press 2003 Network Security
– Chapter 3 – Device Security • A device is a node helping to form the topology of the network. • A compromised device may be used by the attacker as a jumping board. • A Do. S attack may be launched against a device. Network Security 2
Two aspects of device security • Physical security – Placing the device in a secure location • Logical security – Securing the device against nonphysical attacks Network Security 3
Physical security Considerations: • Using redundant devices? • Network topology (serialized, star, fully meshed? ) • Where to place the network devices? • Media security (wire tapping, physical eavesdropping) • Adequate/uninterrupted power supply • disasters Network Security 4
Device Redundancy • A backup device (router, switch, gateway, …) is configured to take over the functionality of a failed active device. • Means of achieving redundancy: A. Use routing to enable redundancy B. Use a redundancy protocol – Hot Standby Router Protocol (HSRP) – Virtual Router Redundancy Protocol (VRRP) – Failover protocols Network Security 5
Cisco Command Reference • Cisco IOS Commands Master List, Release 12. 2 http: //www. cisco. com/univercd/cc/td/doc/product/software/ios 122/122 mindx/l 22 index. htm • Network Access Security Commands http: //www. cisco. com/en/US/products/sw/iosswrel/ps 1824/products_command_reference_chapter 09186 a 0080087141. html • Configuration Guide for the Cisco Secure PIX Firewall Version 6. 0: http: //www. cisco. com/univercd/cc/td/doc/product/iaabu/pix_60/config/index. htm • PIX Command Reference: http: //www. cisco. com/univercd/cc/td/doc/product/iaabu/pix_60/config/commands. htm#xtocid 0 Note: A PDF file may be downloaded from the above sites. • Cisco Command Summary: • Other useful sites: http: //networking. ringofsaturn. com/Cisco/ciscocommandguide. php – – – http: //www. elings. com/ Windows Administration Support Portal http: //www. freebraindumps. com/CCIE/ http: //www. groupstudy. com/ Network Security 6
EIGRP (used in Example 3 -1) • • IGRP: Cisco’s Interior Gateway Routing Protocol EIGRP: Enhanced IGRP – – – • A router running EIGRP stores all its neighbors' routing tables so that it can quickly adapt to alternate routes. If no appropriate route exists, EIGRP queries its neighbors to discover an alternate route. These queries propagate until an alternate route is found. To enable EIGRP on the router you simply need to enable eigrp and define a network number. This is done as follows: Router# conf t Router(config)# router eigrp 1 Router(config-router)# network 172. 16. 0. 0 • http: //networking. ringofsaturn. com/Cisco/eigrp. php Network Security 7
Routing-enabled Redundancy • To set up routing in such a way that the routing protocols converge to one set of routes under normal conditions, and a different set of routes when some of the devices fail. 1. (floating) static routes with varying weights: example 3 -1 2. Dynamic routing protocols: e. g. , Routing Information Protocol (RIP) http: //www. cisco. com/univercd/cc/td/doc/cisintwk/ito_doc/rip. htm Network Security 8
Dynamic routing using RIP • Alternative paths are used when the normal path fails. • Fig. 3 -3 Network Security 9
HSRP • Host Standby Routing Protocol • proprietary (Cisco) • A host uses a IP address as its default gateway. • A virtual router is set up for that IP: – a pair of IP and MAC addresses • The addresses are ‘taken’ by a set of routers configured with HSRP • One of the routers is designated as the active router. • When the active router fails, one of the standby routers takes ownership of the IP and the MAC addresses. Network Security 10
HSRP • HSRP group (aka. standby group) • election protocol • Packet format of HSRP messages: Fig. 3 -4 • Messages: hello, coup hello, resign • How HSRP provides redundancy? Fig. 3 -5 (next slide) A virtual IP is shared between router A and B, so when B becomes the active router, no change of default gateway IP is needed in the end hosts. Network Security 11
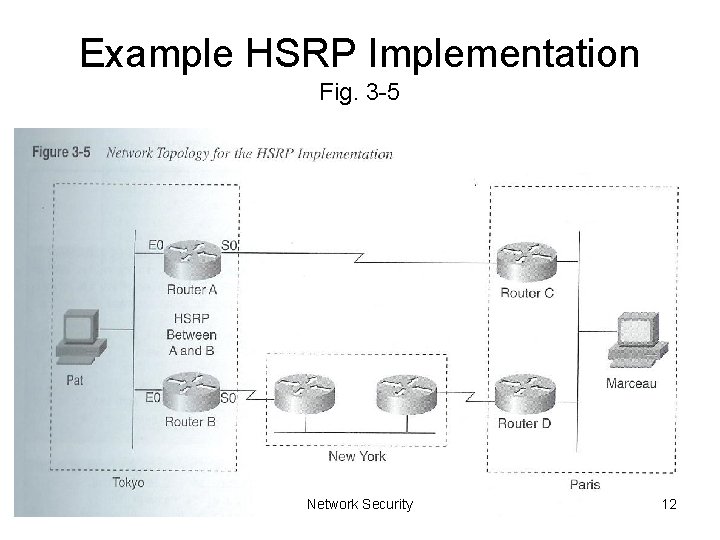
Example HSRP Implementation Fig. 3 -5 Network Security 12
HSRP • Drawback: not very secure The authentication field contains a password that is transmitted as clear text. • c. f. , VRRP provides better security. Network Security 13
VRRP • Virtual Router Redundancy Protocol • RFC 2338, RFC 3768 (4/04): ftp: //ftp. rfc-editor. org/in-notes/rfc 3768. txt • Non-proprietary (unlike HSRP) • an election protocol that dynamically assigns responsibility for a virtual router to one of the VRRP routers on a LAN (the master router) • The election process provides dynamic fail over in the forwarding responsibility should the Master become unavailable. • allows any of the virtual router IP addresses on the LAN to be used as the default first hop router by end-hosts. Network Security 14
VRRP • When is the master router considered down? – The master router periodically sends out an advertisement message that contains an advertisement interval. – Each backup router uses a timer to decide when the master router is down. • The election process: – When a backup router detects that the master router is down, it sends an advertisement message with its own priority value in it. – The backup router with the highest priority value becomes the new master router. Network Security 15
VRRP • Question: How if an attacker injects a fake VRRP advertisement message (possibly with very high priority value) into the network? Would it then be elected to be the new master router? • The answer: VRRP security features – Three authentication methods 1. No authentication 2. Simple clear-text passwords 3. Strong authentication (using IP authentication with MD 5 HMAC) Q: What’s the Implication? Shared key – A mechanism that protects against VRRP packets being injected from a remote network • sets TTL = 255 Network Security 16
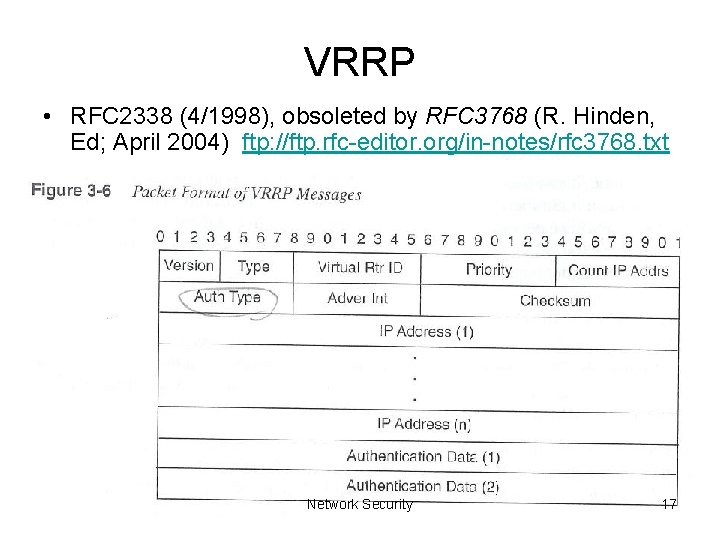
VRRP • RFC 2338 (4/1998), obsoleted by RFC 3768 (R. Hinden, Ed; April 2004) ftp: //ftp. rfc-editor. org/in-notes/rfc 3768. txt Network Security 17
Failover Protocol • Cisco PIX firewall • The functionality of a failed firewall is taken over by a standby firewall. • See chapter 8 for details Network Security 18
Security of major devices • Next: – Router security – Firewall security Network Security 19
- Slides: 19