Network Security Chapter 3 PublicKey Cryptography and Message
Network Security Chapter 3 Public-Key Cryptography and Message Authentication Slides by H. Johnson & S. Malladi- Modified & Translated by Sukchatri P.
2 University of Phayao 11/09/2021 Overview • • • Message Authentication Secure Hash Functions and HMAC Public-Key Cryptography Principles Public-Key Cryptography Algoroithms Digital Signatures Key Management
3 University of Phayao 11/09/2021 Authentication • “A message, file, document or data is said to be authentic when it is genuine and came from its alleged source. ” ขอความ , ไฟลเอกสารหรอขอมลทมการกลาวถงเปนจรงเมอมนเ ปนของแทและมาจากแหลงทถกตอง • Encryption prevents against passive attacks ( eavesdropping) การเขารหสปองกนการโจมตแบบพาสซฟ (แอบฟง ( • Message Authentication prevents against active attacks or falsification. ขอความรบรองความถกตองปองกนการโจมตทใชงานหรอกา
4 University of Phayao 11/09/2021 Message Authentication • Requirements - must be able to verify that: )ความตองการ – ตองสามารถตรวจสอบไดวา ( 1. Message came from apparent source or author, ขอความมาจากแหลงขอมลทชดเจนหรอผเขยนจรง 2. Contents have not been altered, เนอหาไมถกแกไข 3. Sometimes, it was sent at a certain time or sequence. บางครงอาจจะถกสงไปกบบางชวงเวลาหรอลำดบ • Protection against active attack (falsification of
5 University of Phayao 11/09/2021 Approaches to Message Authentication • Authentication Using Conventional Encryptionการตรวจสอบการใชการเขารหสลบแบบปกตดงเ ดม ▫ Only the sender and receiver should share a key เฉพาะผสงและผรบควรใชคยรวมกน • Message Authentication without Message Encryption ขอความการตรวจสอบสทธโดยปราศจาก การเขารหสขอความ ▫ An authentication tag is generated and appended to each message แทกการตรวจสอบจะถกสรางและผนวกเขากบแตละขอความ • Message Authentication Code การตรวจสอบรหสขอความ
6 University of Phayao 11/09/2021 Message Authentication • Using Encryption ▫ Assume only sender and receiver share a key สมมตผสงเทานนและหนรบสำคญ ▫ Then a correctly encrypted message should be from the sender จากนนขอความทเขารหสไดอยางถกตองควรจะเปนจากผ สง • Usually also contains error-detection code, sequence number and time stamp โดยปกตแลวยงมรหสขอผดพลาดตรวจสอบหมายเลขลำดบและ การลงเวลา
7 University of Phayao 11/09/2021
8 University of Phayao 11/09/2021 Message Authentication • • Without Encryption No confidentiality is preferred when: การรกษาความลบไมเปนทตองการเมอ 1. Same message is broadcast to many destinations ขอความเดยวกนนมการถายทอดไปยงปลายทางจำนวนมาก 2. Heavy load and cannot decrypt all messages – some chosen at random ภาระหนกและไมสามารถถอดรหสขอความทงหมด -บางสวนเลอกโดยการสม 3. No danger in sending plaintext
9 University of Phayao 11/09/2021 Message Authentication • Message Authentication Code (MAC) ▫ Small block of data that is appended to the message บลอกเลกของขอมลถกตอทายขอความ ▫ MAC is generated by using a secret key ; MAC จะถกสรางขนโดยใชรหสลบ ▫ Assumes both parties A, B share common secret key KAB ▫ Code is function of message and key MACM= F(KAB, M) ▫ Message plus code are transmitted
10 University of Phayao 11/09/2021 Message Authentication Code • If received code matches calculated code then หากรหสตรงกบรหสทไดรบการคำนวณแลว ▫ Receiver is sure message has not been altered ผรบแนใจวาขอความไมมการเปลยนแปลงใดๆ ▫ Message is from sender since only sender shares the key ผสงเทานนทใหรหสไปพรอมกบการสงขอความ ▫ If the message includes correct sequence number, that number could not have been altered by hacker ถาขอความหมายมลำดบทถกตองรวมถงจำนวนขอความท ไมไดถกเปลยนแปลงโดยแฮกเกอร
11 University of Phayao 11/09/2021 Message Authentication Code • Different from encryption ทแตกตางกนจากการเขารหส ▫ MAC does not have to be reversible as the cipher text does in encryption ; MAC ไมตองมการยอนกลบและขณะท cipher text ทำการเขารหส ▫ Because of mathematical properties, it is less vulnerable to being broken than encryption เนองจากคณสมบตทางคณตศาสตร จะมชองโหวนอยกวาการเขารหส • 16 to 32 bit code is typical โดยทวไปแลวคอรหสบต
12 University of Phayao 11/09/2021
13 University of Phayao 11/09/2021 One-way HASH function • Alternative to Message Authentication Code ทางเลอกในรหสการตรวจสอบขอความ • Accepts a variable size message M as input and produces a fixed-size message digest H (M) as output ยอมรบตวแปรขนาด M ขอความเ ขณะทการเขาและการสรางขอความขนาดคงทถกยอยออกเปน H (M) •
14 One-way HASH function University of Phayao 11/09/2021
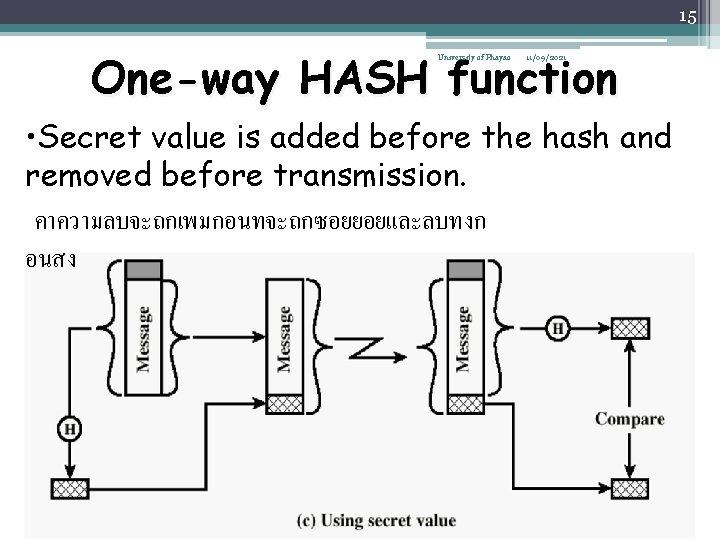
15 One-way HASH function University of Phayao 11/09/2021 • Secret value is added before the hash and removed before transmission. คาความลบจะถกเพมกอนทจะถกซอยยอยและลบทงก อนสง
16 Secure HASH Functions University of Phayao • Purpose of the HASH function is to produce 11/09/2021 a “fingerprint” • Used in message authentication and digital signatures • Properties of a HASH function H : 1. H can be applied to a block of data at any size 2. H produces a fixed length output 3. H(x) is easy to compute for any given x. 4. For any given block x, it is computationally infeasible to find x such that H(x) = h (one-way property) 5. For any given block x, it is computationally infeasible to find with H(y) = H(x). (weak collision resistance) บอบบางตอความตานทานการปะทะกน 6. It is computationally infeasible to find any pair (x, y) such that H(x) = H(y) ( strong collsion resistance)
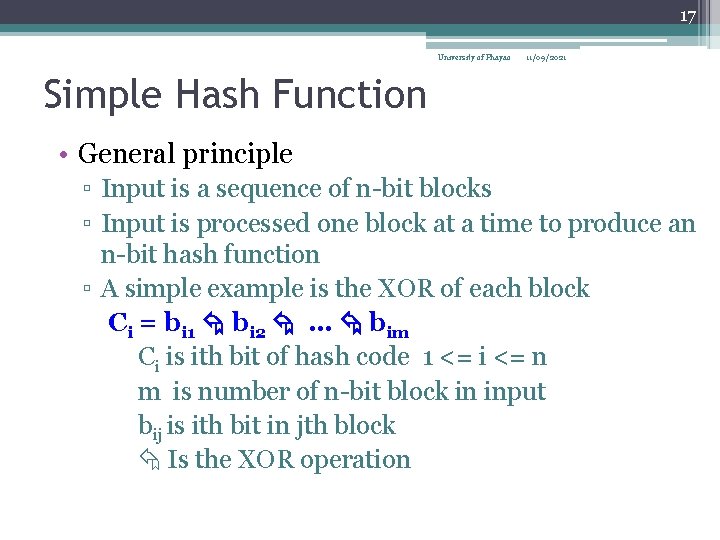
17 University of Phayao 11/09/2021 Simple Hash Function • General principle ▫ Input is a sequence of n-bit blocks ▫ Input is processed one block at a time to produce an n-bit hash function ▫ A simple example is the XOR of each block Ci = bi 1 bi 2 … bim Ci is ith bit of hash code 1 <= i <= n m is number of n-bit block in input bij is ith bit in jth block Is the XOR operation
18 Simple Hash Function University of Phayao 11/09/2021
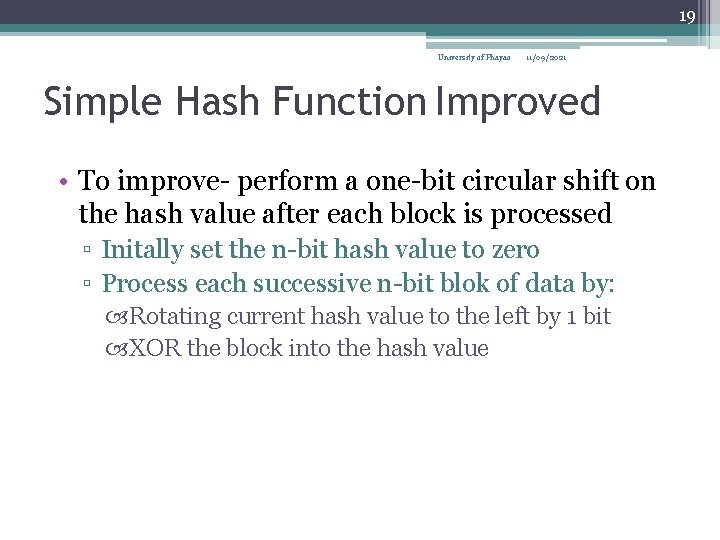
19 University of Phayao 11/09/2021 Simple Hash Function Improved • To improve- perform a one-bit circular shift on the hash value after each block is processed ▫ Initally set the n-bit hash value to zero ▫ Process each successive n-bit blok of data by: Rotating current hash value to the left by 1 bit XOR the block into the hash value
20 University of Phayao 11/09/2021 SHA-1 Secure Hash Function • The Secure Hash Algorithm( SHA) was developed by the National Institute of Standards and Technology and published in 1993. SHA-1 is 1995 revised version. ฉบบแกไขเพมเตม • It takes as input a message with maximum length < 264 bits and produces a 160 -bit message digest. รองรบขอความทเขามาไดถงความยาวสงสด 264 บตและขอความยอยขาออกได 160 bit • It is processed in 512 -bit blocks. มนจะถกประมวลผลในบลอก 512 - bit
21 Message Digest Generation Using SHA-1 University of Phayao 11/09/2021
22 SHA-1 Processing of single 512 -Bit Block University of Phayao 11/09/2021
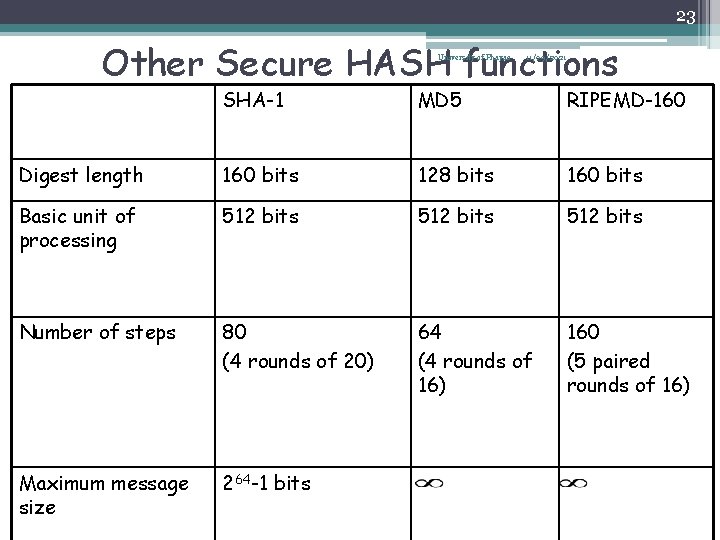
23 Other Secure HASH functions University of Phayao 11/09/2021 SHA-1 MD 5 RIPEMD-160 Digest length 160 bits 128 bits 160 bits Basic unit of processing 512 bits Number of steps 80 (4 rounds of 20) 64 (4 rounds of 16) 160 (5 paired rounds of 16) Maximum message size 264 -1 bits
24 University of Phayao 11/09/2021 HMAC • Use a MAC derived from a cryptographic hash code, such as SHA-1. ใช MAC ทไดจากการเขารหสลบรหสแฮชเชน SHA - 1 • Motivations: ▫ Cryptographic hash functions executes faster in software than encryptoin algorithms such as DES ฟงกชนแฮช Cryptographic ประมวลผลไดเรวกวาในซอฟตแวรกวาขนตอนวธ encryptoin เชน DES ▫ Library code for cryptographic hash functions is widely available มคลงรหสสำหรบฟงกชนแฮชการเขารหสลบมใชอยางกวางขว าง
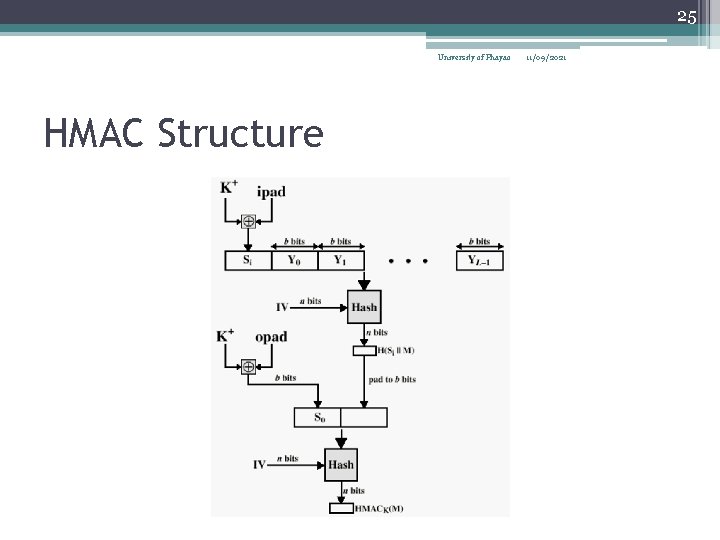
25 University of Phayao HMAC Structure 11/09/2021
26 Public-Key Cryptography Principles University of Phayao 11/09/2021 • The use of two keys has consequences in: key distribution, confidentiality and authentication. • The scheme has six ingredients (see Figure 3. 7) – – – Plaintext Encryption algorithm Public and private key Ciphertext Decryption algorithm
27 University of Phayao 11/09/2021 Encryption using Public-Key system
28 Authentication using Public. Key System University of Phayao 11/09/2021
29 University of Phayao 11/09/2021 Applications for Public-Key Cryptosystems • Three categories: ▫ Encryption/decryption: The sender encrypts a message with the recipient’s public key. ▫ Digital signature: The sender ”signs” a message with its private key. ▫ Key exchange: Two sides cooperate to exhange a session key.
30 University of Phayao 11/09/2021 Requirements for Public Key Cryptography 1. Computationally easy for a party B to generate a pair (public key KUb, private key KRb) 2. Easy for sender to generate ciphertext: 3. Easy for the receiver to decrypt ciphertect using private key:
31 University of Phayao 11/09/2021 Requirements for Public Key Cryptography 4. Computationally infeasible to determine private key (KRb) knowing public key (KUb) 5. Computationally infeasible to recover message M, knowing KUb and ciphertext C 6. Either of the two keys can be used for encryption, with the other used for decryption:
32 University of Phayao 11/09/2021 Public Key Algorithms- RSA • RSA (1977, Ron Rivest, Adi Shamir and Len Adleman), MIT • Most popular and widely implemented • Block cipher • Plain text and cipher text are integers between 0 and (n-1) for some n • C = Me mod n • M = Cd mod n = (Me mod n)d = (Med mod n)
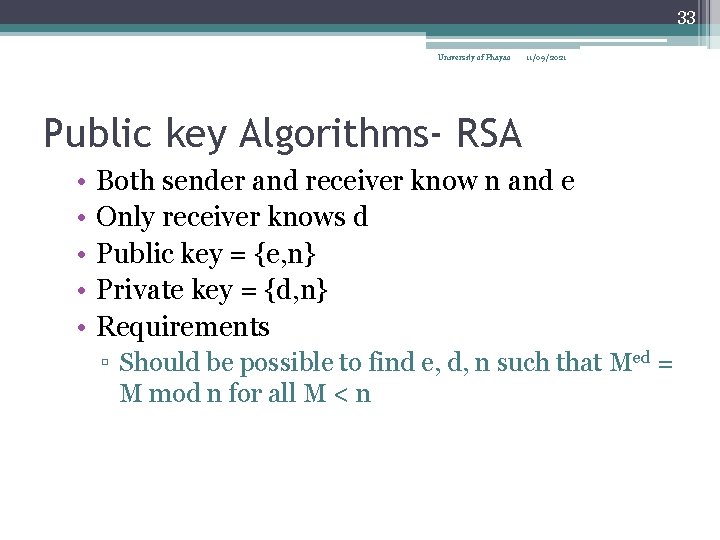
33 University of Phayao 11/09/2021 Public key Algorithms- RSA • • • Both sender and receiver know n and e Only receiver knows d Public key = {e, n} Private key = {d, n} Requirements ▫ Should be possible to find e, d, n such that Med = M mod n for all M < n
34 University of Phayao 11/09/2021 Requirements continued… • Easy to calculate Me and Cd for all M < n • Infeasible to determine d, given e and n • First two requirements are easy. • Third one is also possible if e, n are large
35 University of Phayao 11/09/2021 Steps • Given in text book including examples ▫ See figure on the next slide • We also did some examples in class and in the assignment • Please refer solutions for assignment 2
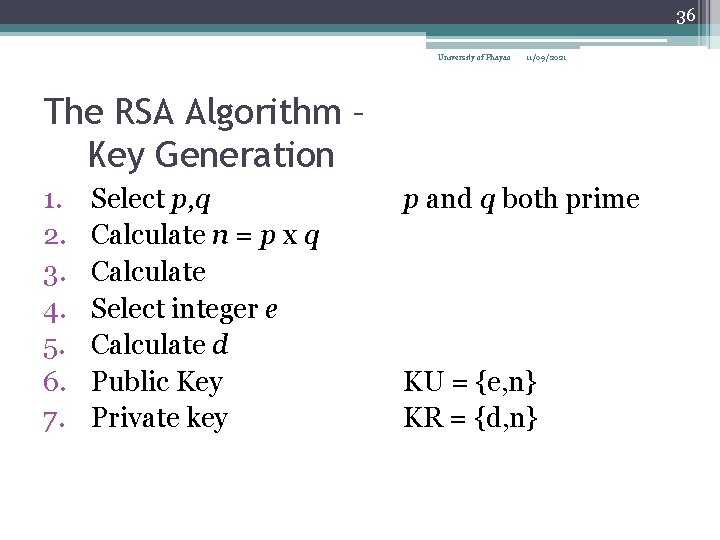
36 University of Phayao 11/09/2021 The RSA Algorithm – Key Generation 1. 2. 3. 4. 5. 6. 7. Select p, q Calculate n = p x q Calculate Select integer e Calculate d Public Key Private key p and q both prime KU = {e, n} KR = {d, n}
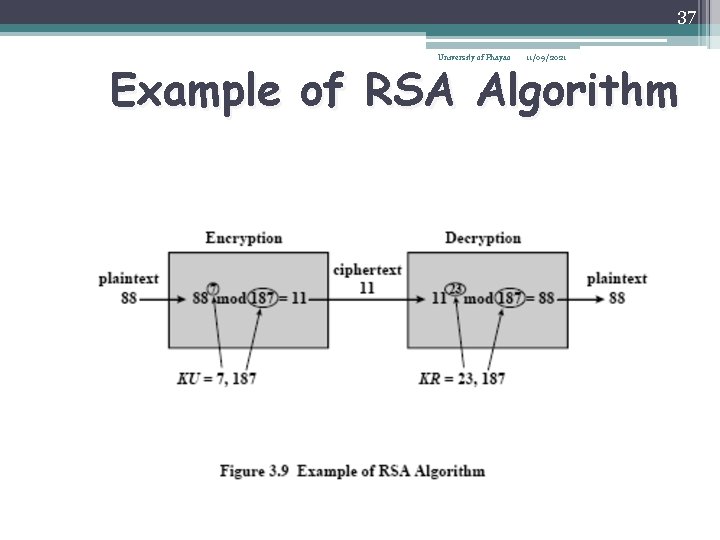
37 University of Phayao 11/09/2021 Example of RSA Algorithm
38 University of Phayao 11/09/2021 The RSA Algorithm - Encryption • Plaintext: M<n • Ciphertext: C = Me (mod n)
39 University of Phayao 11/09/2021 The RSA Algorithm - Decryption • Ciphertext: C • Plaintext: M = Cd (mod n)
40 University of Phayao 11/09/2021 Public Key Algorithm Diffie-Hellman • First introduced by Diffie-Hellman in 1976 • Mathematical functions rather than simple operations on bit patterns • Allows two separate keys ▫ Exchange keys securely ▫ Compute discrete logarithms • Some misconceptions, corrected ▫ NOT more secure than symmetric key ▫ Does NOT Makes symmetric key obsolete ▫ Central agent is needed for both
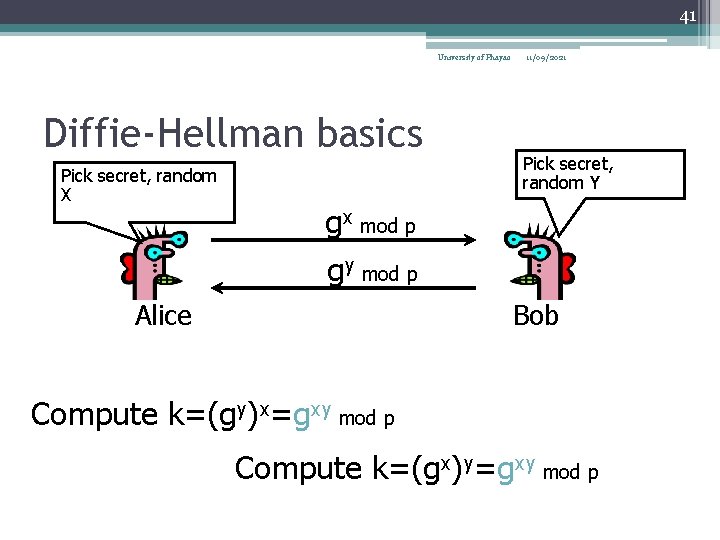
41 University of Phayao Diffie-Hellman basics Pick secret, random X 11/09/2021 Pick secret, random Y gx mod p gy mod p Alice Bob Compute k=(gy)x=gxy mod p Compute k=(gx)y=gxy mod p
42 Diffie-Hellman Key Echange University of Phayao 11/09/2021
43 University of Phayao 11/09/2021 Diffie-Hellman • Key exchange algorithm using public and private values • Based on the discrete logarithm problem • To understand the discrete logarithm problem ▫ Define the primitive root of p to be one whose powers generate all the integers from 1 to (p-1) from some prime number p
44 University of Phayao 11/09/2021 DH details • i. e. if a is a primitive root of prime p, • a mod p, a 2 mod p, … , ap-1 mod p are distinct and contain 1 through (p-1) in some order • For b less than p and a, find unique exponent i such that • b = ai mod p 0 <= i <= (p-1)
45 University of Phayao 11/09/2021 DH details continued… • i is the discrete logarithm • Denoted inda, p(b) • It is hard to calculate it given ai mod p
46 Other Public-Key Cryptographic Algorithms University of Phayao 11/09/2021 • Digital Signature Standard (DSS) – Makes use of the SHA-1 – Not for encryption or key echange • Elliptic-Curve Cryptography (ECC) – Good for smaller bit size – Low confidence level, compared with RSA – Very complex
47 University of Phayao 11/09/2021 Digital signatures • A digital signature is an encryption of a document with the creator’s private key • It is attached to a document that validates the creator of the document • Any one can validate it by decrypting the signature with the claimed creator’s public key
48 University of Phayao 11/09/2021 Digital signatures on hashes • A more efficient way for a digital signature is by creating an authenticator of the document first (a hash) • Then sign the hash (i. e. encrypt the hash using private key) • If M is the message (or document), Hash(M) = H • sig. PV(A)(H) represents sigining H • i. e. encrypting H with A’s private key
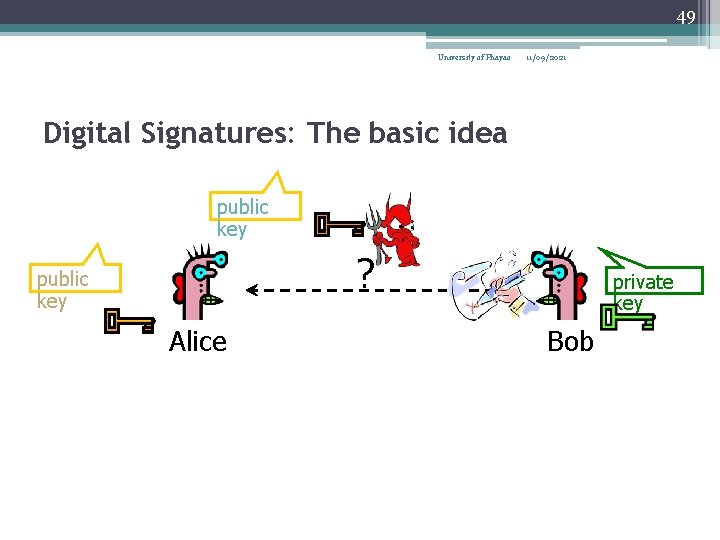
49 University of Phayao 11/09/2021 Digital Signatures: The basic idea public key ? public key Alice private key Bob
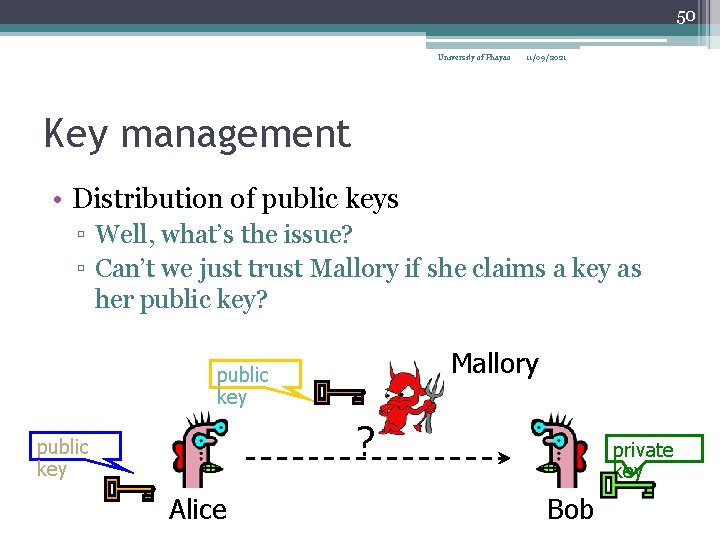
50 University of Phayao 11/09/2021 Key management • Distribution of public keys ▫ Well, what’s the issue? ▫ Can’t we just trust Mallory if she claims a key as her public key? Mallory public key ? public key Alice private key Bob
51 University of Phayao 11/09/2021 Public keys to exchange secret keys • Using public-keys to exchange secret keys ▫ why exchange secret keys? ▫ aren’t public keys sufficient?
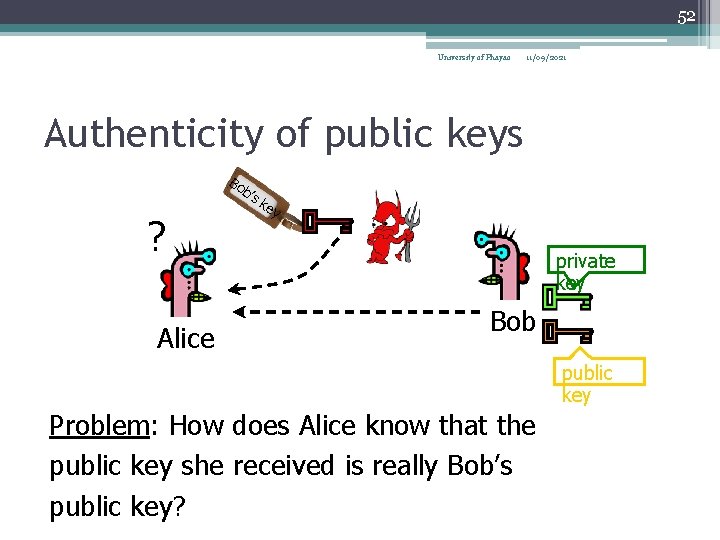
52 University of Phayao 11/09/2021 Authenticity of public keys Bo b’s ? Alice ke y private key Bob public key Problem: How does Alice know that the public key she received is really Bob’s public key?
53 University of Phayao 11/09/2021 Public-key certificates • Anyone can forge public-keys • Therefore, use public-key certificates • A public-key certificate is a public-key that was signed by a trusted third party (called a certificate authority or CA) • See figure on next slide
54 Key Management Public-Key Certificate Use University of Phayao 11/09/2021
55 University of Phayao 11/09/2021 Public-key distribution of secret keys • How to establish a secret symmetric key between two strangers? • Shall we use Diffie-Hellman ▫ Does Diffie-Hellman have authentication before values are exchanged • How about Stallings’ idea?
56 University of Phayao 11/09/2021 Stallings idea continued… ▫ Prepare a message ▫ Encrypt that message using conventional encryption with a onetime conventional session key ▫ Encrypt the session key using public-key encryption with Alice’s public key ▫ Attach the encrypted session key to the message and send it to Alice • Stallings thinks this is secure • Do you think so? • Do I think so? Yes • Do I think it is meaningful? No
57 University of Phayao 11/09/2021 Why? • Well it is secure but it serves no purpose • There is no authentication message • How does Alice know from whom it came from? • Anyone can prepare that message • What is the point of a “secure” and secret message if I can’t trust the person who sent it? • Would you let your kid accept a gift box that is highly secure (locked etc. ) from a stranger and walk home with it after school?
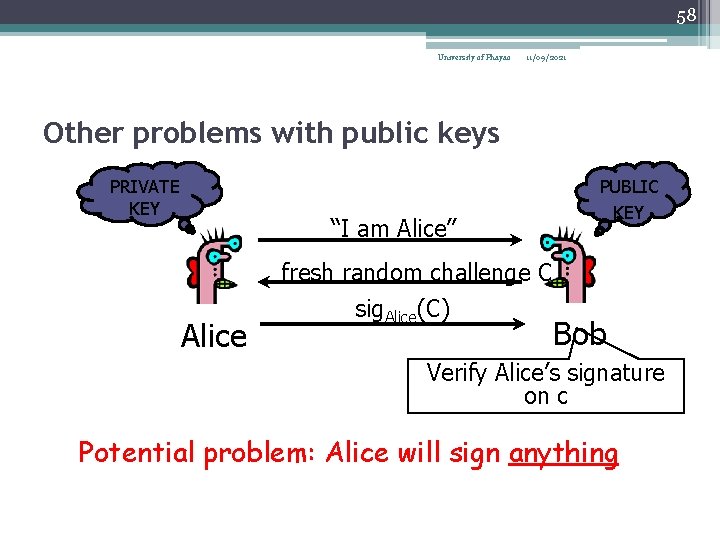
58 University of Phayao 11/09/2021 Other problems with public keys PRIVATE KEY “I am Alice” Alice fresh random challenge C sig. Alice(C) PUBLIC KEY Bob Verify Alice’s signature on c Potential problem: Alice will sign anything
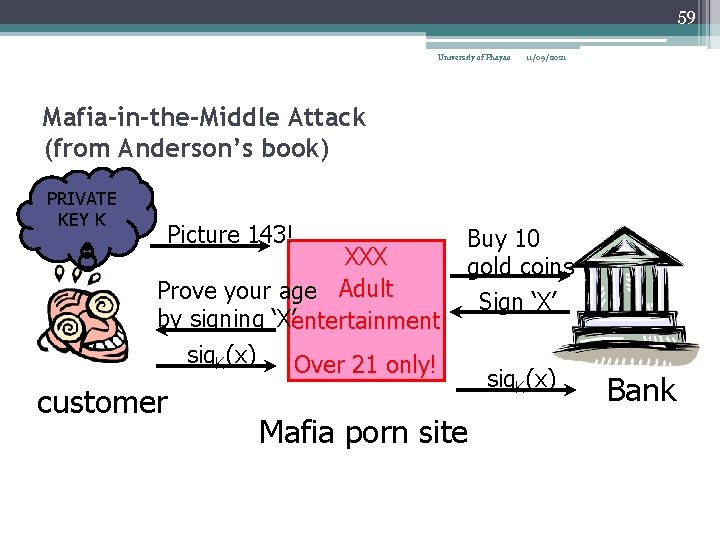
59 University of Phayao 11/09/2021 Mafia-in-the-Middle Attack (from Anderson’s book) PRIVATE KEY K Picture 143! XXX Prove your age Adult by signing ‘X’entertainment sig. K(x) Over 21 only! customer Buy 10 gold coins Sign ‘X’ Mafia porn site sig. K(x) Bank
60 University of Phayao Merci 11/09/2021
- Slides: 60