Network Security Bijendra Jain bnjcse iitd ernet in
Network Security Bijendra Jain (bnj@cse. iitd. ernet. in) 12/6/2020 Tutorial on Network Security: Sep 2003 1
Lecture 1: Introduction 12/6/2020 Tutorial on Network Security: Sep 2003 2
Top-level issues Safety, security and privacy l Security policy l – – l threats, both external and internal economic gains cost of securing resources cryptographic methods vs. physical security Information security: – – 12/6/2020 nature of resources (HW, SW, information) during storage, access and communication limited to a single computer vs. network security various layers (physical through application layers) Tutorial on Network Security: Sep 2003 3

Security threats Intentional vs. accidental l Various forms of violations: l – – l Non-destructive Destructive Repudiation Denial of service Threat techniques: – – – 12/6/2020 crypt-analysis snooping masquerading replay attacks virus, worms etc. Tutorial on Network Security: Sep 2003 4
Security services Services (or functions) vs. mechanisms l Security functions: l – confidentiality – authentication – integrity – non-repudiation – access control – availability 12/6/2020 Tutorial on Network Security: Sep 2003 5
Security mechanisms l l l Physical controls Audit trails Fraud detection (data mining) Steganography Encryption: – private-key vs. public-key encryption – key generation, exchange, and management – certification Firewalls l etc. l 12/6/2020 Tutorial on Network Security: Sep 2003 6
Lecture 2: Symmetric-key encryption 12/6/2020 Tutorial on Network Security: Sep 2003 7
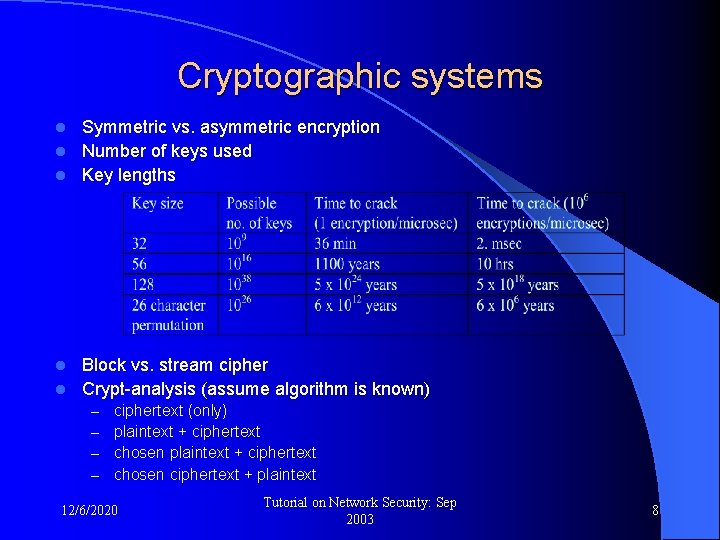
Cryptographic systems Symmetric vs. asymmetric encryption l Number of keys used l Key lengths l Block vs. stream cipher l Crypt-analysis (assume algorithm is known) l – – ciphertext (only) plaintext + ciphertext chosen ciphertext + plaintext 12/6/2020 Tutorial on Network Security: Sep 2003 8
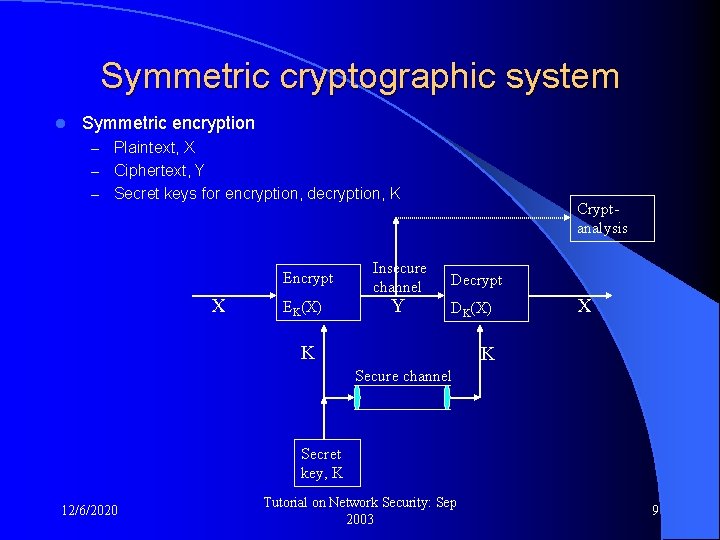
Symmetric cryptographic system l Symmetric encryption – Plaintext, X – Ciphertext, Y – Secret keys for encryption, decryption, K Encrypt X EK(X) Insecure channel Y Cryptanalysis Decrypt DK(X) K X K Secure channel Secret key, K 12/6/2020 Tutorial on Network Security: Sep 2003 9
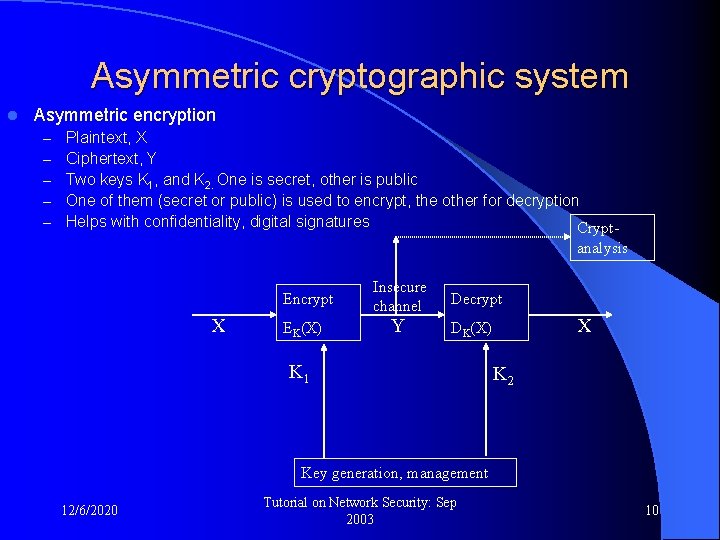
Asymmetric cryptographic system l Asymmetric encryption – – – Plaintext, X Ciphertext, Y Two keys K 1, and K 2. One is secret, other is public One of them (secret or public) is used to encrypt, the other for decryption Helps with confidentiality, digital signatures Cryptanalysis Encrypt X EK(X) Insecure channel Y Decrypt X DK(X) K 1 K 2 Key generation, management 12/6/2020 Tutorial on Network Security: Sep 2003 10
Symmetric encryption l l l Substitution cipher Transposition cipher DES Triple DES Blowfish, RC 5, RC 4, etc. 12/6/2020 Tutorial on Network Security: Sep 2003 11
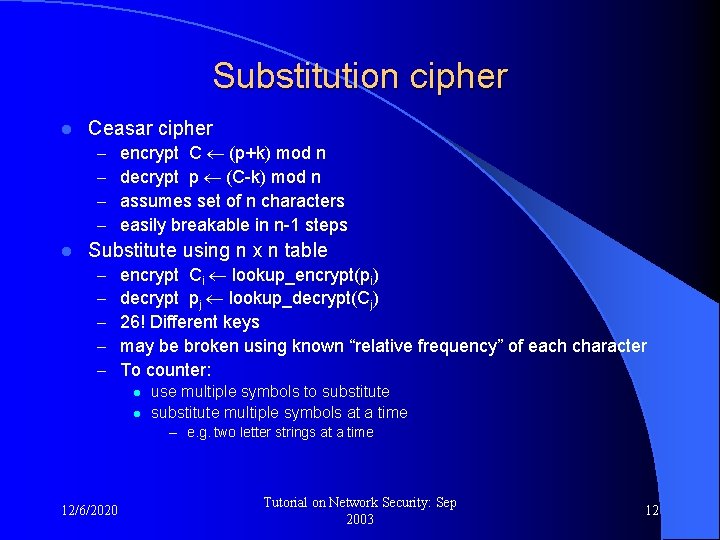
Substitution cipher l Ceasar cipher – – l encrypt C (p+k) mod n decrypt p (C-k) mod n assumes set of n characters easily breakable in n-1 steps Substitute using n x n table – – – encrypt Ci lookup_encrypt(pi) decrypt pj lookup_decrypt(Cj) 26! Different keys may be broken using known “relative frequency” of each character To counter: l l use multiple symbols to substitute multiple symbols at a time – e. g. two letter strings at a time 12/6/2020 Tutorial on Network Security: Sep 2003 12
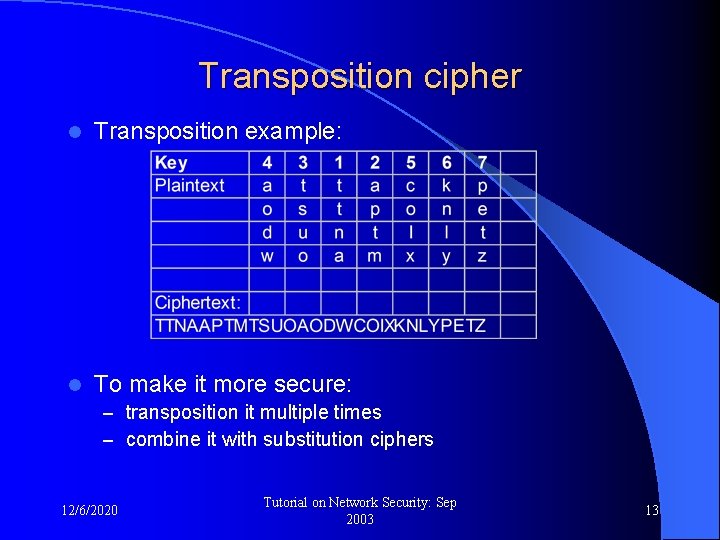
Transposition cipher l Transposition example: l To make it more secure: – transposition it multiple times – combine it with substitution ciphers 12/6/2020 Tutorial on Network Security: Sep 2003 13
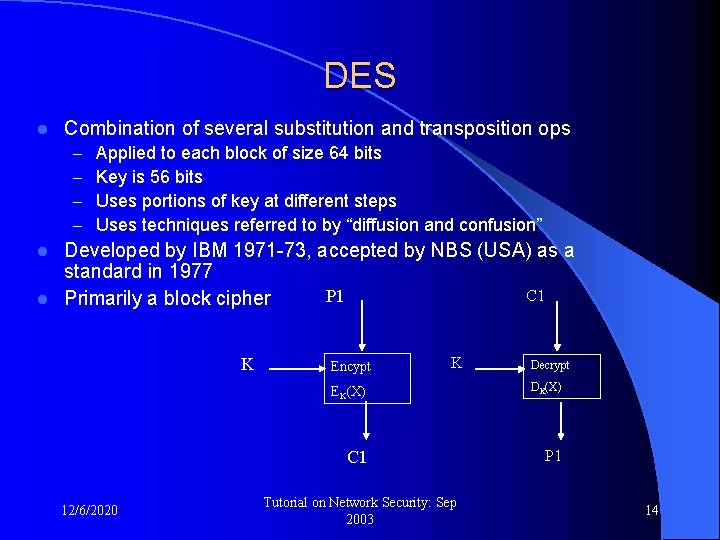
DES l Combination of several substitution and transposition ops – – Applied to each block of size 64 bits Key is 56 bits Uses portions of key at different steps Uses techniques referred to by “diffusion and confusion” Developed by IBM 1971 -73, accepted by NBS (USA) as a standard in 1977 C 1 P 1 l Primarily a block cipher l K 12/6/2020 Encypt K Decrypt EK(X) DK(X) C 1 P 1 Tutorial on Network Security: Sep 2003 14
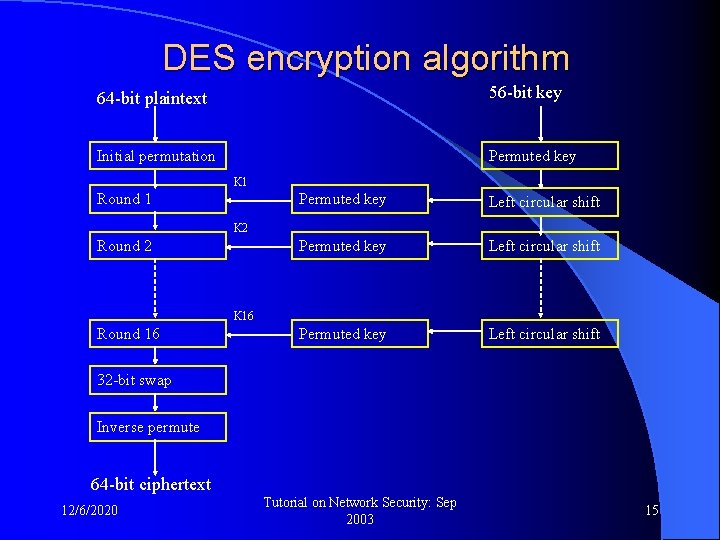
DES encryption algorithm 64 -bit plaintext 56 -bit key Initial permutation Permuted key K 1 Round 1 Permuted key Left circular shift K 2 Round 2 K 16 Round 16 32 -bit swap Inverse permute 64 -bit ciphertext 12/6/2020 Tutorial on Network Security: Sep 2003 15
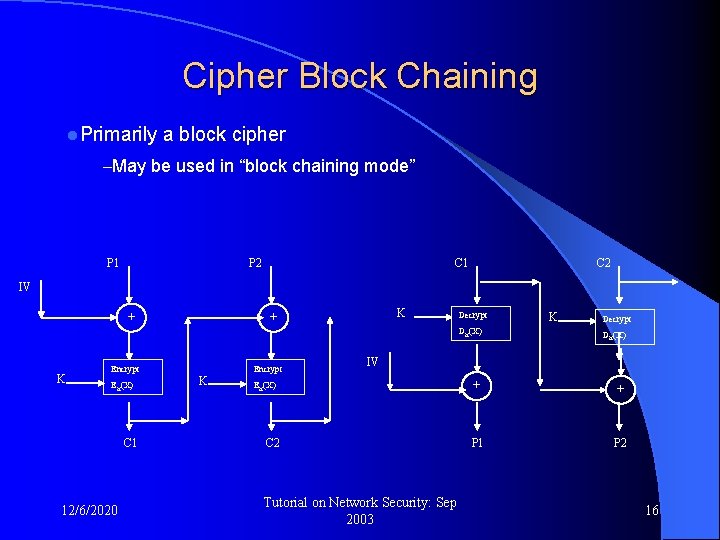
Cipher Block Chaining l. Primarily a block cipher –May be used in “block chaining mode” P 1 P 2 C 1 C 2 IV + K Encrypt EK(X) C 1 12/6/2020 K + K Encrypt Decrypt K Decrypt DK(X) + + P 1 P 2 IV EK(X) C 2 Tutorial on Network Security: Sep 2003 16

Strength of DES l Key size of 56 bits appears to be too small – In 1993 Weiner developed HW device for $100 K with 5760 search engines to break it in 35 hours – In 1997, 70, 000 systems on Internet discovered the key in less than 96 days (part of plaintext is given) – Automating the process is difficult, unless plaintext is known l Perhaps breakable by studying and exploiting weakness – Differential cryptanalysis – Linear cryptanalysis l Trapdoor – US Govt changed the original design l Continues to enjoy wide acceptibility – Particularly with triple-DES (used in PGP) 12/6/2020 Tutorial on Network Security: Sep 2003 17
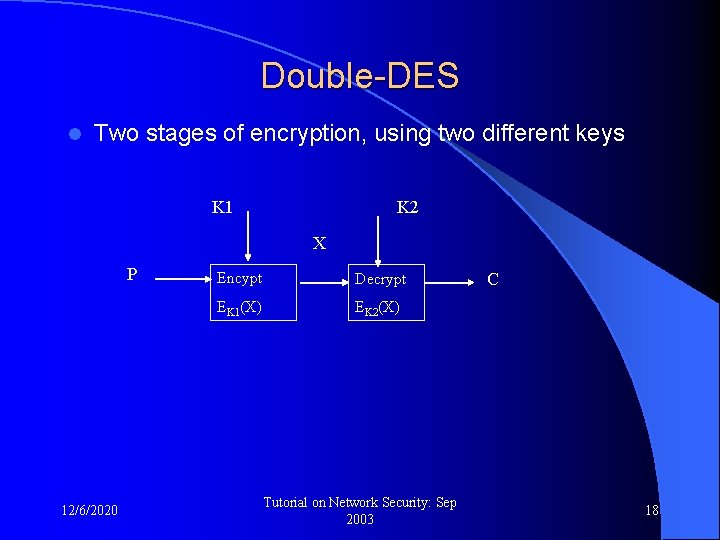
Double-DES l Two stages of encryption, using two different keys K 1 K 2 X P 12/6/2020 Encypt Decrypt EK 1(X) EK 2(X) Tutorial on Network Security: Sep 2003 C 18
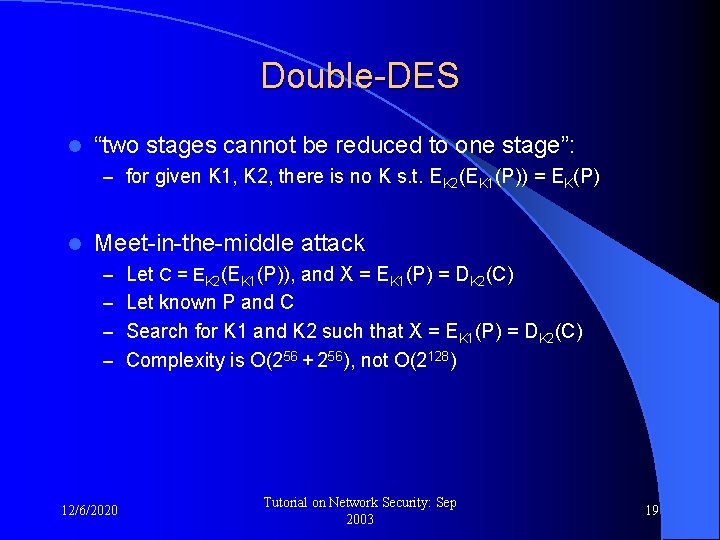
Double-DES l “two stages cannot be reduced to one stage”: – for given K 1, K 2, there is no K s. t. EK 2(EK 1(P)) = EK(P) l Meet-in-the-middle attack – Let C = EK 2(EK 1(P)), and X = EK 1(P) = DK 2(C) – Let known P and C – Search for K 1 and K 2 such that X = EK 1(P) = DK 2(C) – Complexity is O(256 + 256), not O(2128) 12/6/2020 Tutorial on Network Security: Sep 2003 19
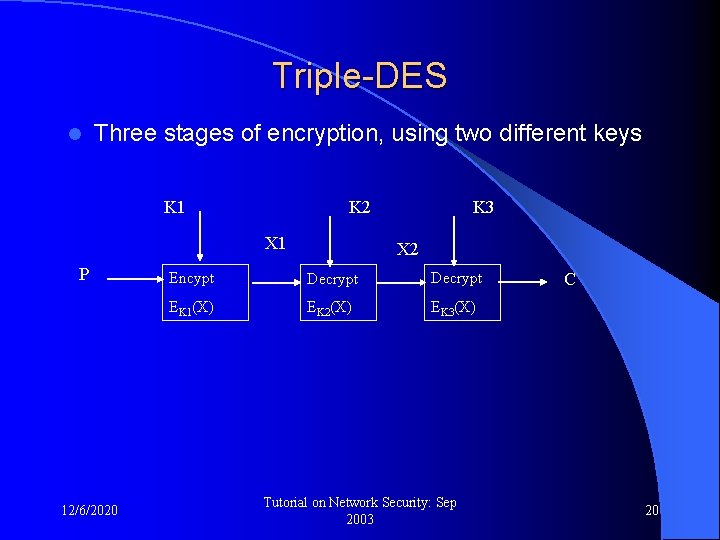
Triple-DES l Three stages of encryption, using two different keys K 1 X 1 P 12/6/2020 K 3 K 2 X 2 Encypt Decrypt EK 1(X) EK 2(X) EK 3(X) Tutorial on Network Security: Sep 2003 C 20
IDEA l l l International data encryption algorithm (IDEA) developed in 1991, gaining ground block cipher better understood US government has had no role in its design principle: – block size 64 bits – key length 128 bits – more emphasis on “diffusion” and “confusion” l uses three operations: – “exclusive-OR”, “addition”, “multiplication” – some effort to make HW implementation easier 12/6/2020 Tutorial on Network Security: Sep 2003 21
RC 5 developed by Rivest, in 1994 l suitable for HW or SW implementation on microprocessors l – simple – different word length – low memory l high level of security – simpler determination of strength – variable no. of “rounds”, key length 12/6/2020 Tutorial on Network Security: Sep 2003 22
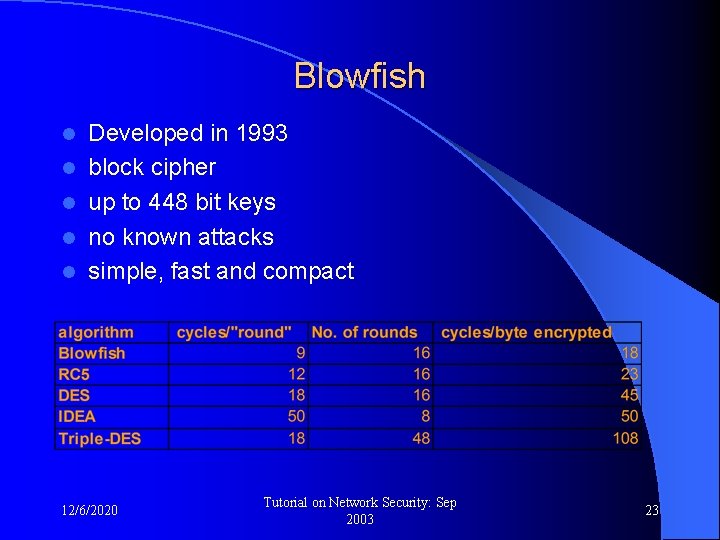
Blowfish l l l Developed in 1993 block cipher up to 448 bit keys no known attacks simple, fast and compact 12/6/2020 Tutorial on Network Security: Sep 2003 23
Summary: symmetric key encryption Since the same key is used to encrypt and decrypt, the system is also know as private-key encryption l Symmetric key encryption l – uses shared secret keys – also known as “private-key” encryption l Primarily used for purpose of confidentiality – but may be used to authenticate as well, but may be “repudiated” l Key sharing or management is an issue – particularly when the no. of clients sharing the key is “large” 12/6/2020 Tutorial on Network Security: Sep 2003 24
Application to confidentiality Private-key encryption may be used to provide confidentiality of messages during transfer over LANs and/or WANs l At issue: l – what information: l User data vs. headers l Identity of correspondents vs. node/route identity – in what layer, and between what points l Link-layer vs. end-to-end vs. application level l Assumption: data over physical network is accessible – Wireless links – Employee of the network service provider – Your own colleagues 12/6/2020 Tutorial on Network Security: Sep 2003 25
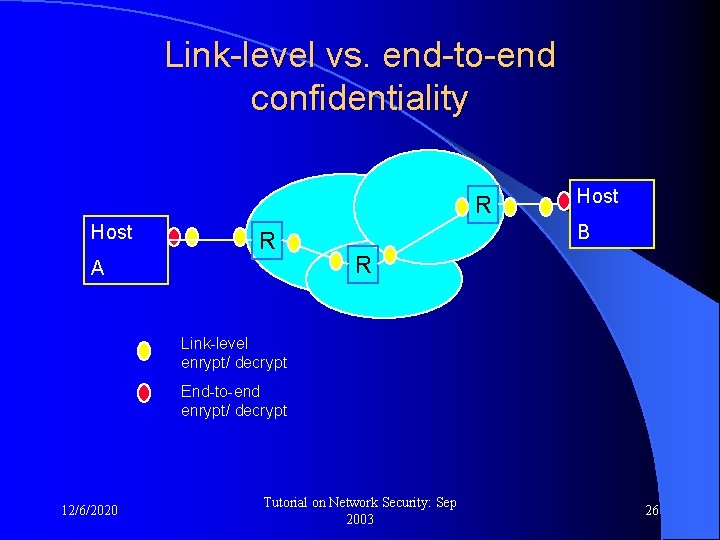
Link-level vs. end-to-end confidentiality R Host R A Host B R Link-level enrypt/ decrypt End-to-end enrypt/ decrypt 12/6/2020 Tutorial on Network Security: Sep 2003 26
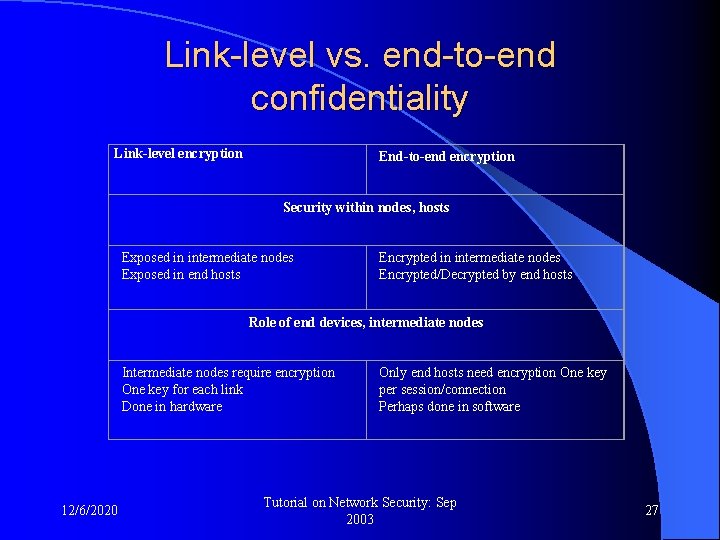
Link-level vs. end-to-end confidentiality Link-level encryption End-to-end encryption Security within nodes, hosts Exposed in intermediate nodes Exposed in end hosts Encrypted in intermediate nodes Encrypted/Decrypted by end hosts Role of end devices, intermediate nodes Intermediate nodes require encryption One key for each link Done in hardware 12/6/2020 Only end hosts need encryption One key per session/connection Perhaps done in software Tutorial on Network Security: Sep 2003 27
Traffic confidentiality l Issues: – Identity of communicating entities – Identity of hosts, routers – Traffic volumes, patterns Link-level encryption offers better confidentiality l Padding may be used to “hide” patterns and volumes l 12/6/2020 Tutorial on Network Security: Sep 2003 28
Key distribution Secret key must be distributed between the communicating entities, say A and B l Link level encryption requires L number of keys to be distributed, one for each device at the end of a link l Host-to-host encryption requires N*(N-1)/2 keys to be distributed l Two techniques: l – Physical delivery (works only in a very limited environs) l A delivers it to B l A trusted third party C delivers the key to A and to B – Electronic delivery using an established secure connection or session l l 12/6/2020 A delivers it to B after suitably encrypting it A trusted third party C delivers the key to A and to B using secure channels to A and to B. Tutorial on Network Security: Sep 2003 29
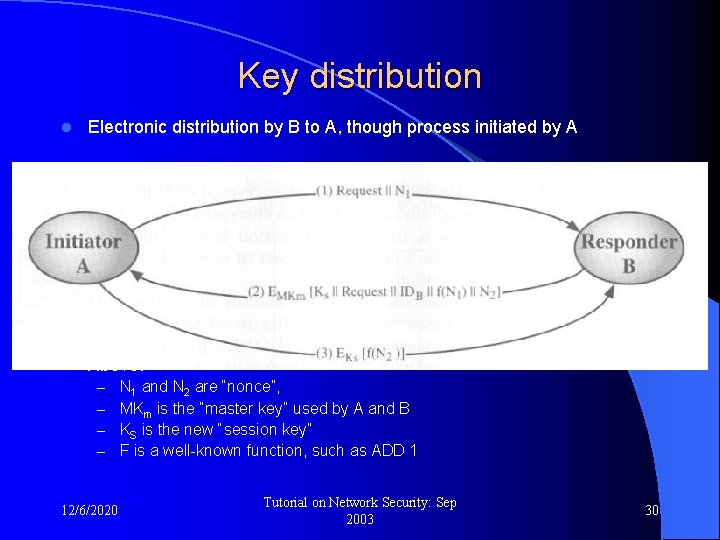
Key distribution l Electronic distribution by B to A, though process initiated by A l Above: – – 12/6/2020 N 1 and N 2 are “nonce”, MKm is the “master key” used by A and B KS is the new “session key” F is a well-known function, such as ADD 1 Tutorial on Network Security: Sep 2003 30
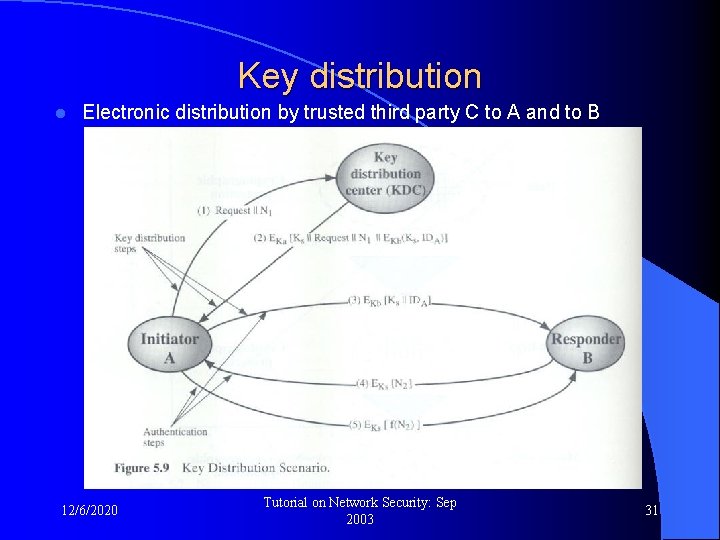
Key distribution l Electronic distribution by trusted third party C to A and to B 12/6/2020 Tutorial on Network Security: Sep 2003 31
Key distribution l Above: – KA and KB are keys used by A and B, respectively, to communicate with C – IDA identifies entity A 12/6/2020 Tutorial on Network Security: Sep 2003 32
Key distribution l Secure operation of these schemes, against: – Masquerade – replay attacks l Other issues: – Hierarchy of keys – Lifetime of a session key – Generation of Nonce or Random numbers 12/6/2020 Tutorial on Network Security: Sep 2003 33

Thanks 12/6/2020 Tutorial on Network Security: Sep 2003 34
- Slides: 34