Network Security Basics 2 1 Message Digests Computationally
Network Security Basics 2 1
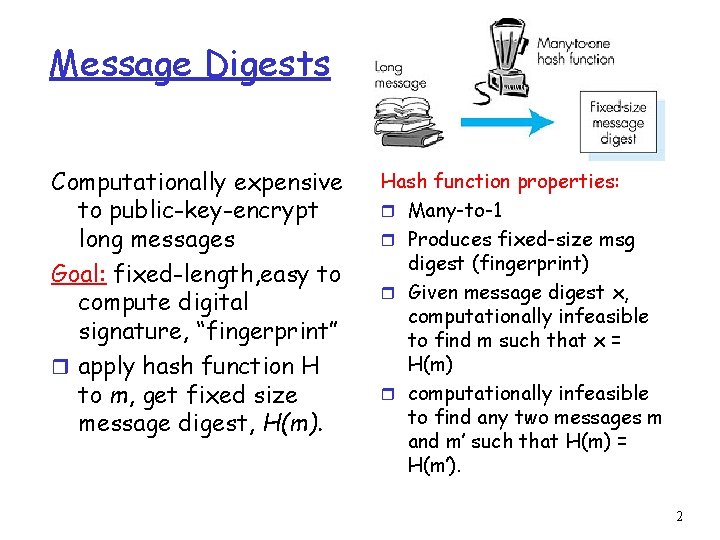
Message Digests Computationally expensive to public-key-encrypt long messages Goal: fixed-length, easy to compute digital signature, “fingerprint” r apply hash function H to m, get fixed size message digest, H(m). Hash function properties: r Many-to-1 r Produces fixed-size msg digest (fingerprint) r Given message digest x, computationally infeasible to find m such that x = H(m) r computationally infeasible to find any two messages m and m’ such that H(m) = H(m’). 2
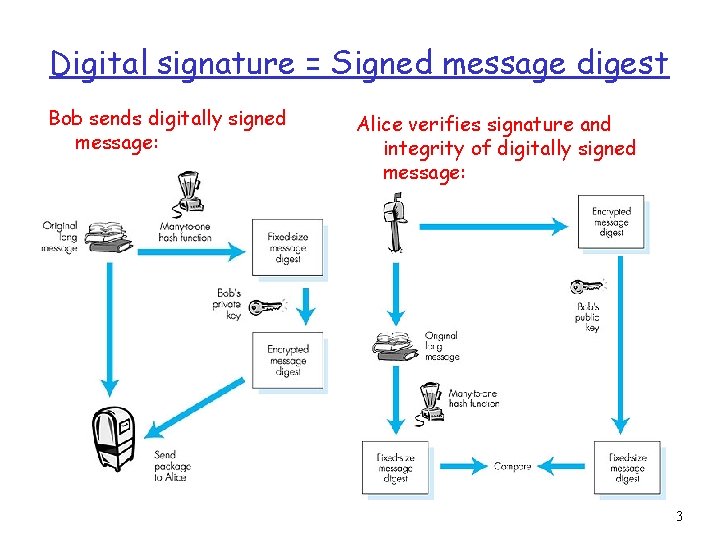
Digital signature = Signed message digest Bob sends digitally signed message: Alice verifies signature and integrity of digitally signed message: 3
Hash Function Algorithms r Internet checksum would make a poor message digest. m Too easy to find two messages with same checksum. r MD 5 hash function widely used. m Computes 128 -bit message digest in 4 -step process. m arbitrary 128 -bit string x, appears difficult to construct msg m whose MD 5 hash is equal to x. r SHA-1 is also used. m US standard m 160 -bit message digest 4
Trusted Intermediaries Problem: m How do two entities m When Alice obtains establish shared Bob’s public key secret key over (from web site, enetwork? mail, diskette), how does she know it is Solution: Bob’s public key, not m trusted key Trudy’s? distribution center Solution: (KDC) acting as intermediary m trusted certification between entities authority (CA) 5
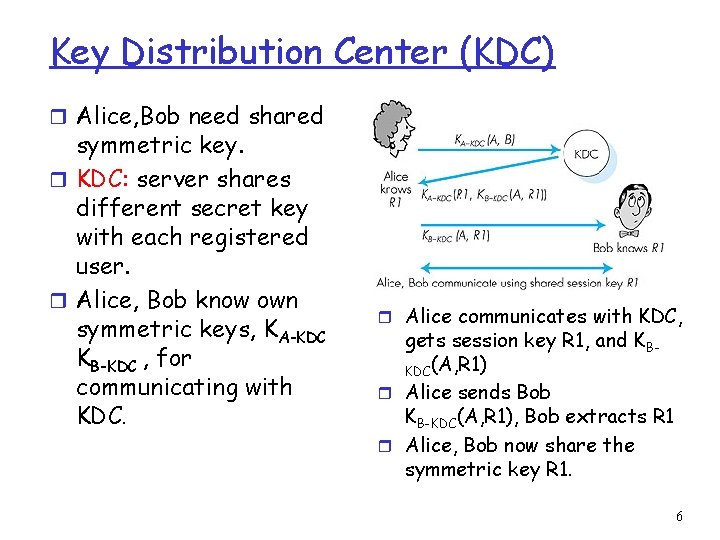
Key Distribution Center (KDC) r Alice, Bob need shared symmetric key. r KDC: server shares different secret key with each registered user. r Alice, Bob know own symmetric keys, KA-KDC KB-KDC , for communicating with KDC. r Alice communicates with KDC, gets session key R 1, and KBKDC(A, R 1) r Alice sends Bob KB-KDC(A, R 1), Bob extracts R 1 r Alice, Bob now share the symmetric key R 1. 6
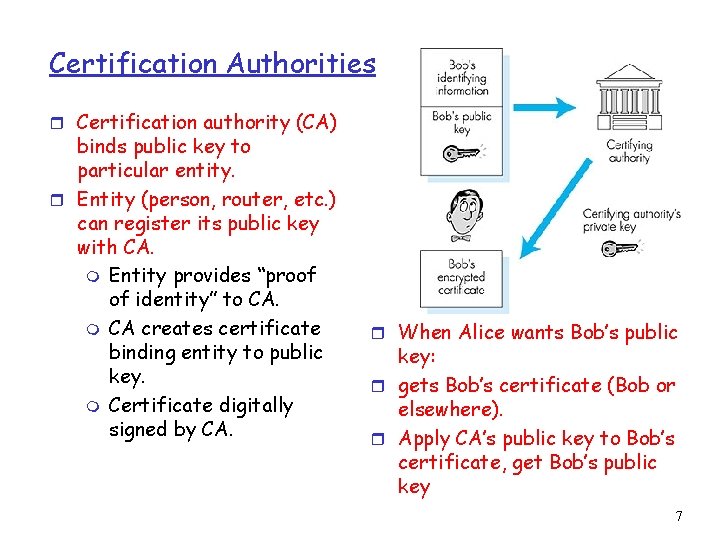
Certification Authorities r Certification authority (CA) binds public key to particular entity. r Entity (person, router, etc. ) can register its public key with CA. m Entity provides “proof of identity” to CA. m CA creates certificate binding entity to public key. m Certificate digitally signed by CA. r When Alice wants Bob’s public key: r gets Bob’s certificate (Bob or elsewhere). r Apply CA’s public key to Bob’s certificate, get Bob’s public key 7

Secure e-mail • Alice wants to send secret e-mail message, m, to Bob. • generates random symmetric private key, KS. • encrypts message with KS • also encrypts KS with Bob’s public key. • sends both KS(m) and e. B(KS) to Bob. 8
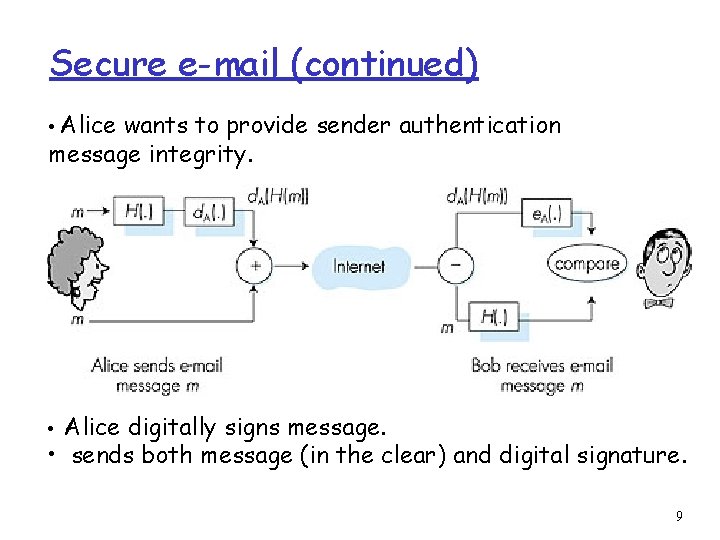
Secure e-mail (continued) • Alice wants to provide sender authentication message integrity. • Alice digitally signs message. • sends both message (in the clear) and digital signature. 9
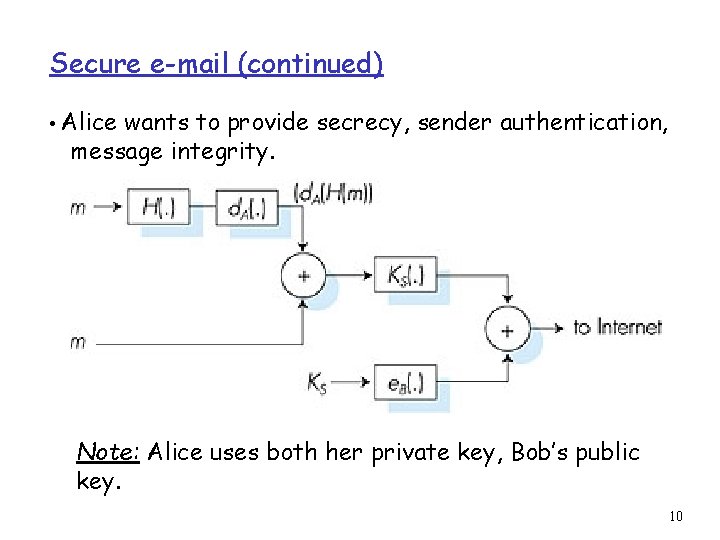
Secure e-mail (continued) • Alice wants to provide secrecy, sender authentication, message integrity. Note: Alice uses both her private key, Bob’s public key. 10
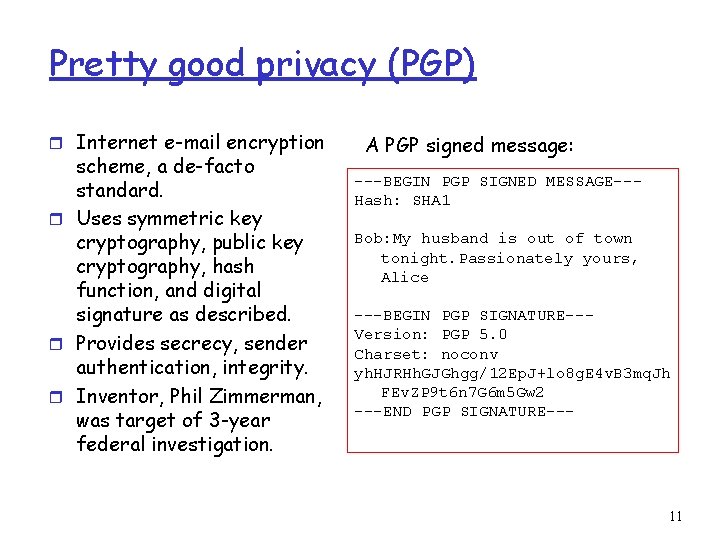
Pretty good privacy (PGP) r Internet e-mail encryption scheme, a de-facto standard. r Uses symmetric key cryptography, public key cryptography, hash function, and digital signature as described. r Provides secrecy, sender authentication, integrity. r Inventor, Phil Zimmerman, was target of 3 -year federal investigation. A PGP signed message: ---BEGIN PGP SIGNED MESSAGE--Hash: SHA 1 Bob: My husband is out of town tonight. Passionately yours, Alice ---BEGIN PGP SIGNATURE--Version: PGP 5. 0 Charset: noconv yh. HJRHh. GJGhgg/12 Ep. J+lo 8 g. E 4 v. B 3 mq. Jh FEv. ZP 9 t 6 n 7 G 6 m 5 Gw 2 ---END PGP SIGNATURE--- 11
Secure sockets layer (SSL) r PGP provides security for a specific network app. r SSL works at transport layer. Provides security to any TCP-based app using SSL services. r SSL: used between WWW browsers, servers for Icommerce (shttp). r SSL security services: m m m server authentication data encryption client authentication (optional) r Server authentication: m m m SSL-enabled browser includes public keys for trusted CAs. Browser requests server certificate, issued by trusted CA. Browser uses CA’s public key to extract server’s public key from certificate. r Visit your browser’s security menu to see its trusted CAs. 12
SSL (continued) Encrypted SSL session: r Browser generates symmetric session key, encrypts it with server’s public key, sends encrypted key to server. r Using its private key, server decrypts session key. r Browser, server agree that future msgs will be encrypted. r All data sent into TCP socket (by client or server) i encrypted with session key. r SSL: basis of IETF Transport Layer Security (TLS). r SSL can be used for non. Web applications, e. g. , IMAP. r Client authentication can be done with client certificates. 13
Secure electronic transactions (SET) r designed for payment-card transactions over Internet. r provides security services among 3 players: m customer m merchant’s bank All must have certificates. r SET specifies legal meanings of certificates. m apportionment of liabilities for transactions r Customer’s card number passed to merchant’s bank without merchant ever seeing number in plain text. m Prevents merchants from stealing, leaking payment card numbers. r Three software components: m Browser wallet m Merchant server m Acquirer gateway r See text for description of SET transaction. 14
Ipsec: Network Layer Security r Network-layer secrecy: sending host encrypts the data in IP datagram m TCP and UDP segments; ICMP and SNMP messages. r Network-layer authentication m destination host can authenticate source IP address r Two principle protocols: m authentication header (AH) protocol m encapsulation security payload (ESP) protocol m r For both AH and ESP, source, destination handshake: m create network-layer logical channel called a service agreement (SA) r Each SA unidirectional. r Uniquely determined by: m security protocol (AH or ESP) m source IP address m 32 -bit connection ID 15
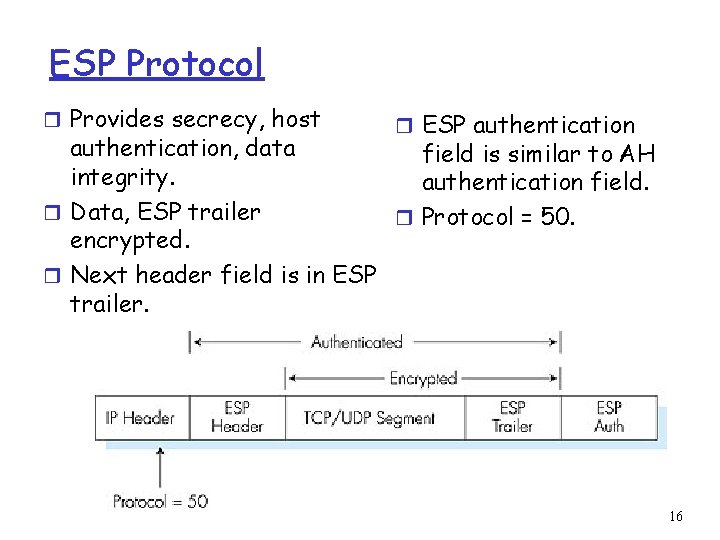
ESP Protocol r Provides secrecy, host r ESP authentication, data field is similar to AH integrity. authentication field. r Data, ESP trailer r Protocol = 50. encrypted. r Next header field is in ESP trailer. 16
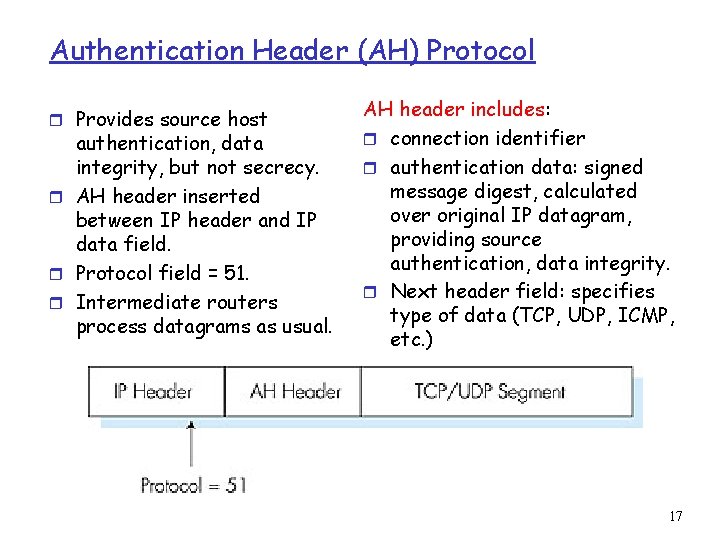
Authentication Header (AH) Protocol r Provides source host authentication, data integrity, but not secrecy. r AH header inserted between IP header and IP data field. r Protocol field = 51. r Intermediate routers process datagrams as usual. AH header includes: r connection identifier r authentication data: signed message digest, calculated over original IP datagram, providing source authentication, data integrity. r Next header field: specifies type of data (TCP, UDP, ICMP, etc. ) 17
Network Security (summary) Basic techniques…. . . r cryptography (symmetric and public) r authentication r message integrity …. used in many different security scenarios r secure email r secure transport (SSL) r IP sec See also: firewalls , in network management 18
- Slides: 18