Network security Basic encryption techniques Luk Stoops VUB
Network security Basic encryption techniques Luk Stoops VUB - programming laboratory
Security Problems • Student • To have fun snooping on people’s email • Hacker • To test out someone’s security system; steal data • Sales rep • To claim to represent all of Europe, not just Andorra • Businessman • To discover a competitor’s strategic marketing plan
Security Problems • Ex-employee • To get revenge for being fired • Accountant • To Embezzle money from a company • Stockbroker • To deny a promise made to a customer by email
Security Problems • Con man • To steal creditcard numbers for sale • Spy • To learn an enemy’s military strength • Terrorist • To steal germ warfare secrets • … • . . .
Network Security • Secrecy • user authorisation • Authentication • determining who you are talking to • Nonrepudiation • signatures • Integrity control • received message, is it not modified ?

Traditional Cryptography Encryption key Ek Plaintext P Encryption Decryption Key Dk Ciphertext C=Ek(P) Intruder Decryption Plaintext P
Some Terminology • Cryptanalysis • The art of breaking ciphers • Cryptography • The art of devising ciphers • Cryptology • Cryptanalysis & Cryptography

Method of Encryption • Cryptanalyst knows method of encryption • Amount of effort to invent, test and install a new method every time the old method is compromised or thought to be compromised has always made it impractical to keep this secret • This is where the key enters
The Key • Combination Lock • 2 digits = 100 possibilities • 3 digits = 1000 possibilities • Workfactor for the cryptanalyst by exhaustive search of the key space is exponential in the key length • range from 64 -bit to 256 -bits keys
Cryptoanalyst Variations • Ciphertext only • only ciphertext • Known plaintext (“please login”) • matched ciphertext and plaintext • Chosen plaintext • matched ciphertext and chosen plaintext
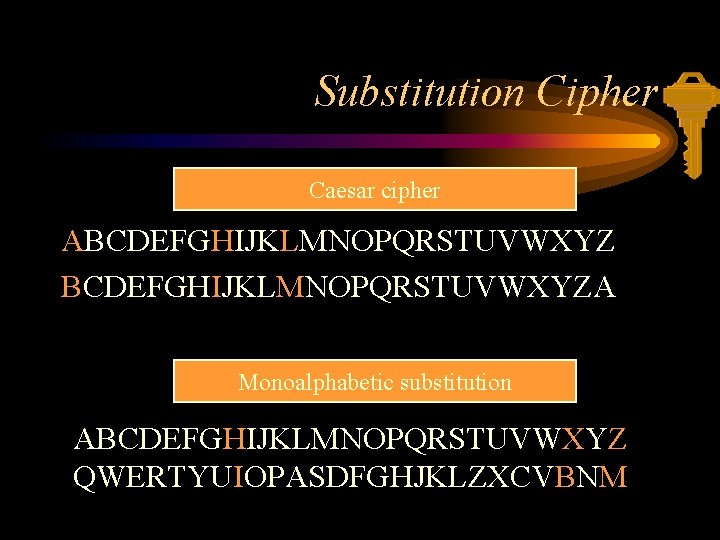
Substitution Cipher Caesar cipher ABCDEFGHIJKLMNOPQRSTUVWXYZA Monoalphabetic substitution ABCDEFGHIJKLMNOPQRSTUVWXYZ QWERTYUIOPASDFGHJKLZXCVBNM
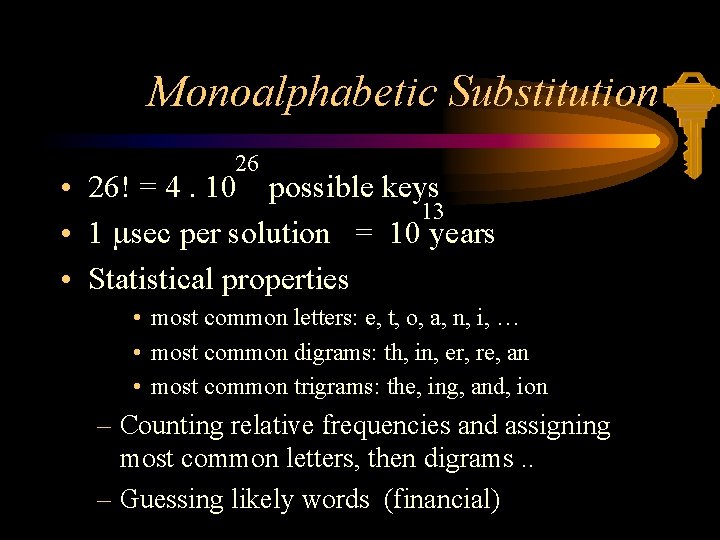
Monoalphabetic Substitution 26 • 26! = 4. 10 possible keys 13 • 1 msec per solution = 10 years • Statistical properties • most common letters: e, t, o, a, n, i, … • most common digrams: th, in, er, re, an • most common trigrams: the, ing, and, ion – Counting relative frequencies and assigning most common letters, then digrams. . – Guessing likely words (financial)

Transposition Cipher • Reorder the letters but do not disguise them • afllskaselawabtoosscdlnmoman esilyntrnntsoepaedobueriricc • Breaking transposition ciphers – Frequency analysis: normal pattern – guess number of columns • digrams depend on keylength – ordering found by english plaintext digrams MEGABUCK 74512836 pleasetr ansferon emillion dollarst omyswiss bankacco untabcde
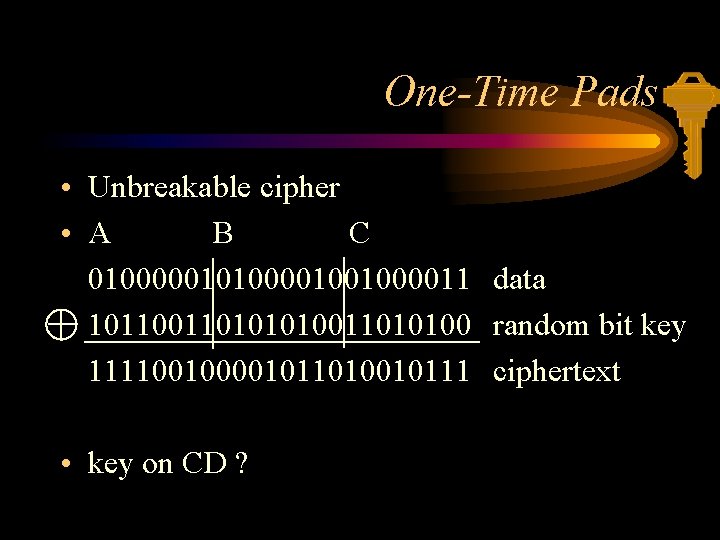
One-Time Pads • Unbreakable cipher • A B C 010000010100001001000011 data 10110101010011010100 random bit key 111100100001011010010111 ciphertext • key on CD ?
Cryptographic principles • All encrypted messages must contain some redundancy information – active intruders cannot send random junk – easier to break the message • Prevent active intruders from playing back old messages (timestamps)
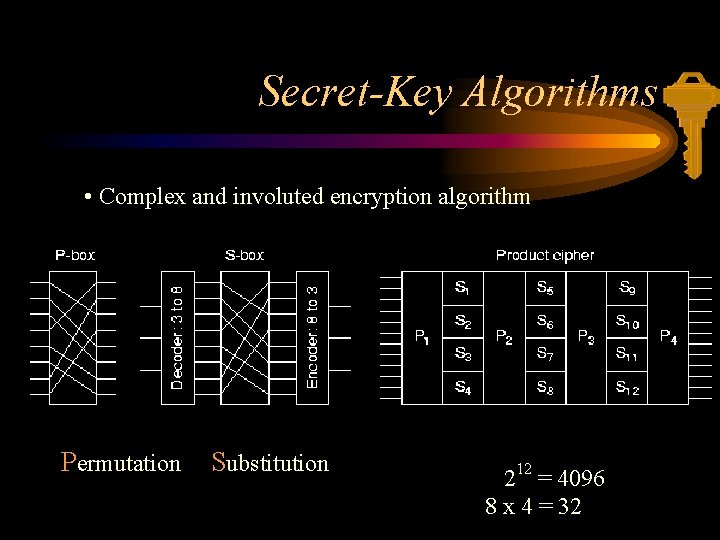
Secret-Key Algorithms • Complex and involuted encryption algorithm Permutation Substitution 212 = 4096 8 x 4 = 32
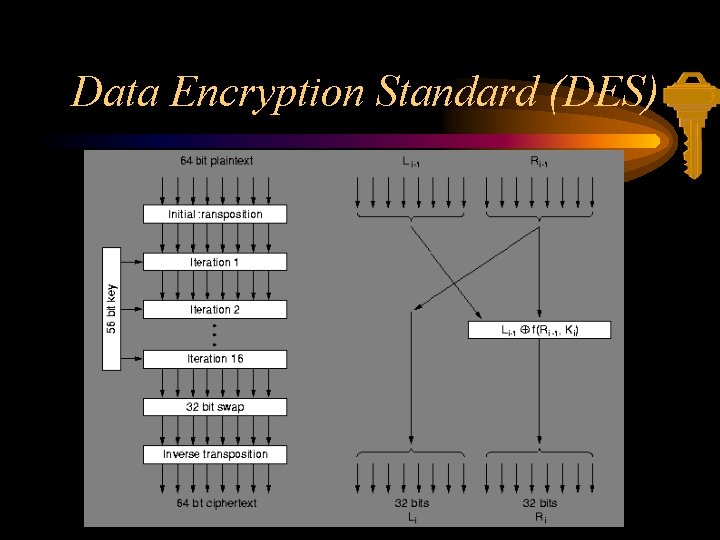
Data Encryption Standard (DES)
DES (cont. ) • • • IBM 1977 No longer secure in its original form Parameterised by 56 -bit key 19 stages Decryption with same key in reverse order Complexity lies in iteration function (S- & P boxes)

DES Subversion • DES is basically a monoalphabetic substitution • Encrypting a longer message is done by breaking it up in consecutive 8 -byte (64 -bit) blocks

DES Chaining • Chaining makes block i a function of all previous blocks • Same plaintext no longer maps onto the same cyphertext Random initialisation vector IV

DES Cipher Feedback Mode • Byte-by-byte encryption • initialisation vector needed
Breaking DES • • Original 128 -bit key reduced to 56 under NSA pressure 1977 20 million $ DES breaking machine in one day 140. 000 people checking 7 x 1016 keys in a month Chinese Lottery – 1. 2 billion people with chip that searches 1 million encryption's / sec • within 60 sec key is found Congratulations ! You have won the Chinese Lottery. To collect, please call 0800 -1111
Des Cracker • • July 17, 1998: EFF Builds DES Cracker $220, 000 device Average of 4. 5 days to crack a key June 8, 1998: government : – “FBI is unable to crack DES” • 56 -bit key is too short http: //www. eff. org/descracker/

Breaking DES (cont. ) • Insecure DES is still widely used for secure applications such as banking • Using DES 2 times ? – 2112 = 1033 – 1 billion DES chips, 1 billion operations / sec takes 100 million years 57 – meet-in-the-middle attack: 2 operations
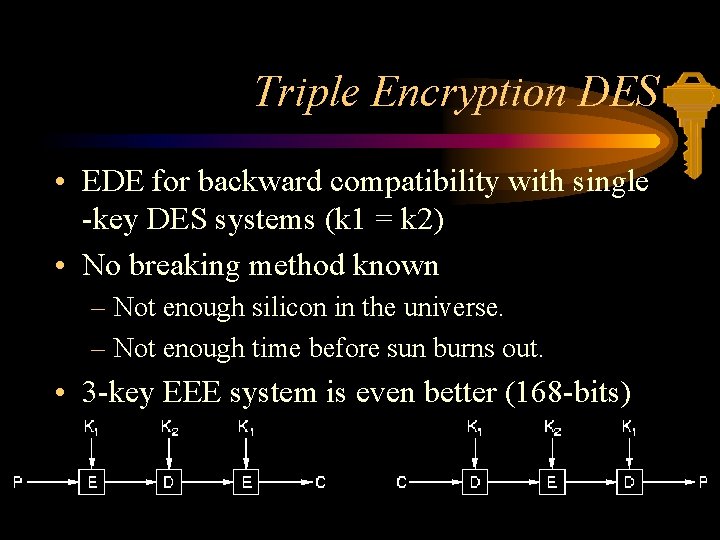
Triple Encryption DES • EDE for backward compatibility with single -key DES systems (k 1 = k 2) • No breaking method known – Not enough silicon in the universe. – Not enough time before sun burns out. • 3 -key EEE system is even better (168 -bits)
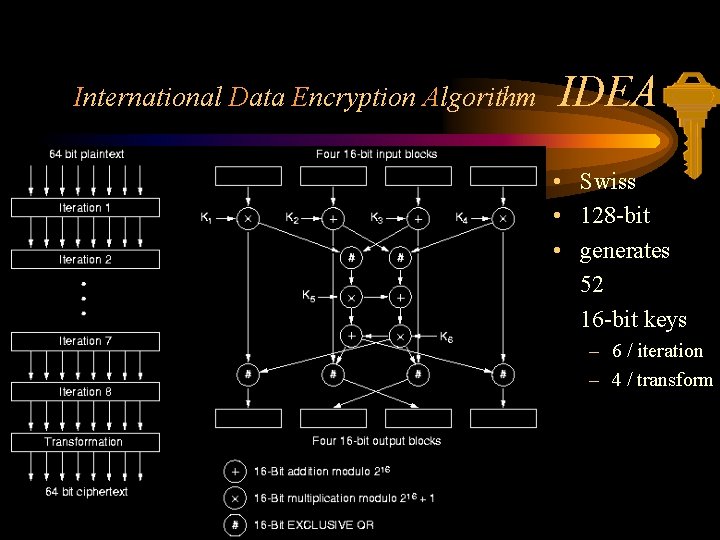
International Data Encryption Algorithm IDEA • Swiss • 128 -bit • generates 52 16 -bit keys – 6 / iteration – 4 / transform
Advanced Encryption Standard • 1972: National Institute of Standards and Technology – public request for encryption algorithm • DES • • January 1997: new public request for AES 15 submissions in June 1998 (12 survived) March 1999 (5 candidates) January 2000 (winner) http: //www. nist. gov/aes/
Public-Key Algorithms • • Key protection and distribution problem 1976 Diffie and Hellman (Stanford univ. ) encryption and decryption key are different decryption key can not be derived from the encryption key • encryption key is made public Ea Da A Eb(p) B Eb Db
RSA Algorithm • Rivest, Shamir, Adleman • based on the difficulty of factoring large numbers • Factoring a 200 -digit number requires 4 billion years of computer time • too slow for encrypting large volumes of data • Used to distribute a one-time session keys for use with DES or IDEA
Knapsack algorithm • Merkle and Hellmann 1978 – Large number of objects with different weight – selecting a subset in knapsack – total weight and list of possible objects is public • broken by Shamir and Rivest
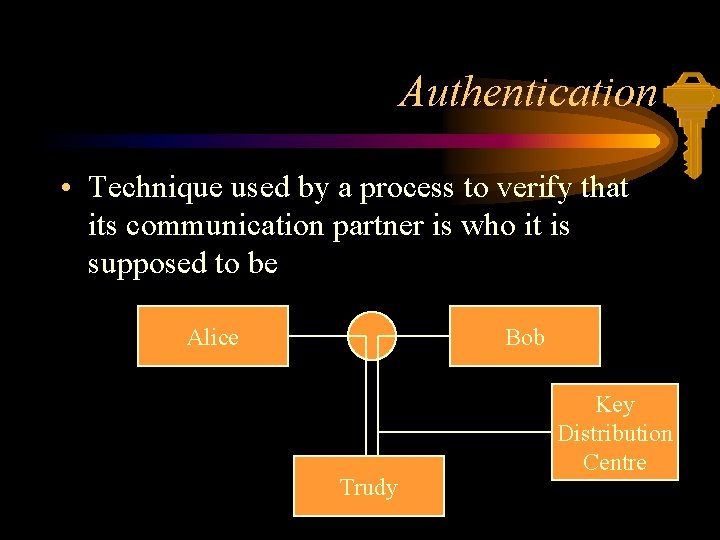
Authentication • Technique used by a process to verify that its communication partner is who it is supposed to be Alice Bob Trudy Key Distribution Centre
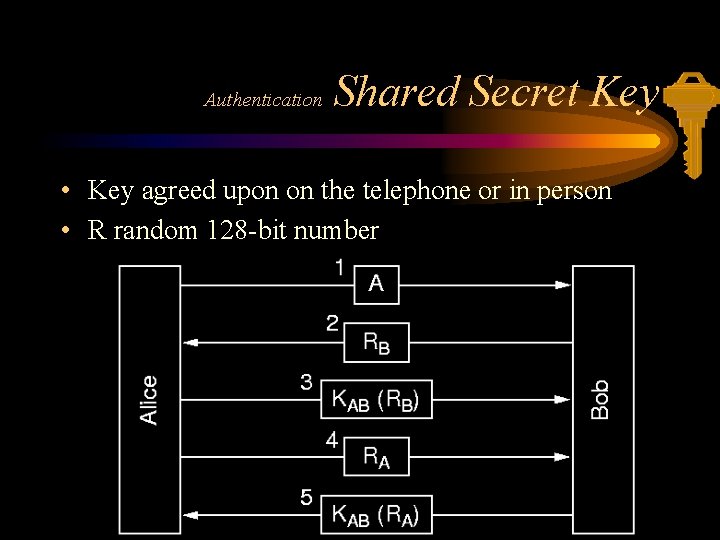
Authentication Shared Secret Key • Key agreed upon on the telephone or in person • R random 128 -bit number
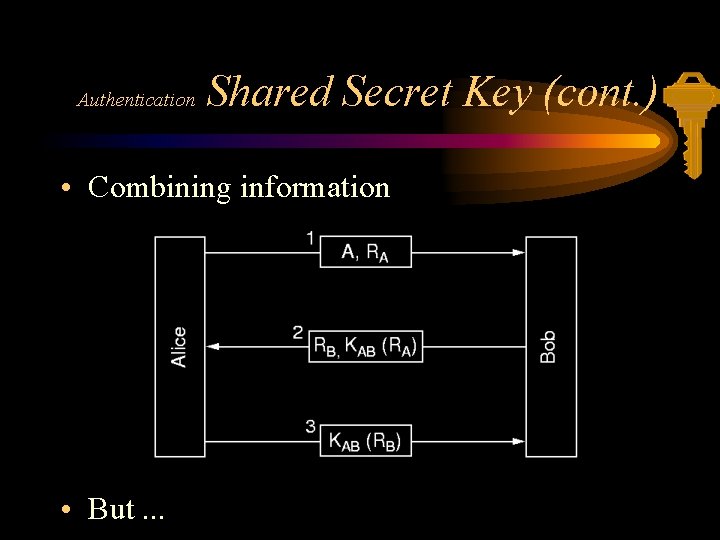
Authentication Shared Secret Key (cont. ) • Combining information • But. . .
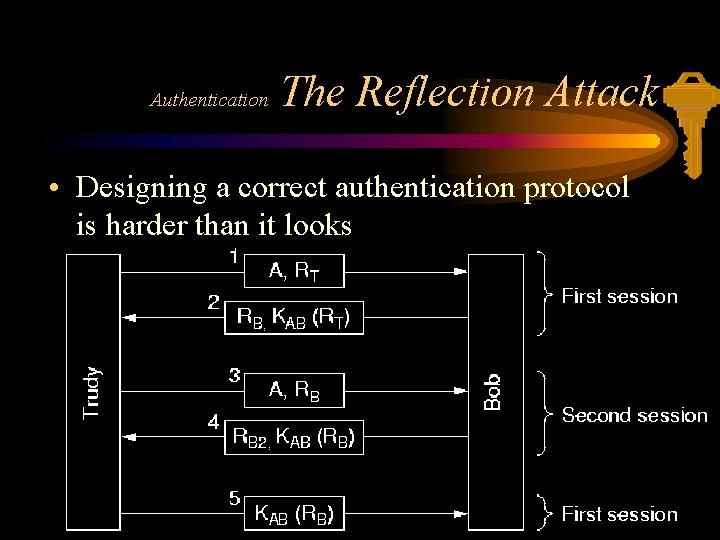
Authentication The Reflection Attack • Designing a correct authentication protocol is harder than it looks
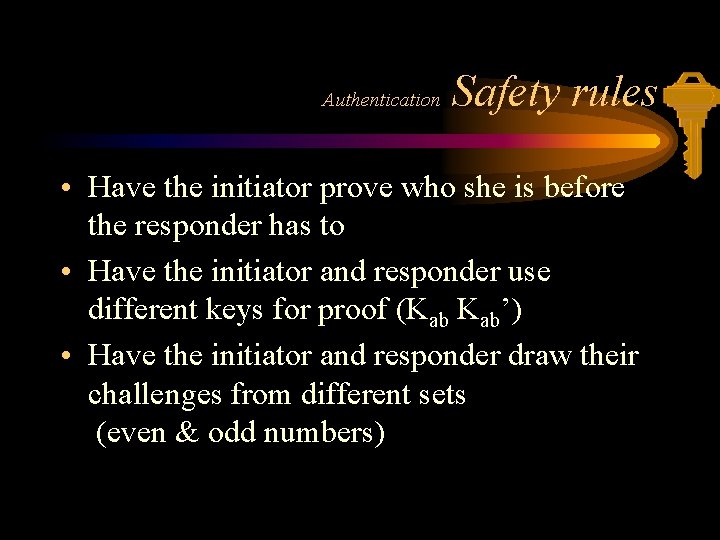
Authentication Safety rules • Have the initiator prove who she is before the responder has to • Have the initiator and responder use different keys for proof (Kab Kab’) • Have the initiator and responder draw their challenges from different sets (even & odd numbers)
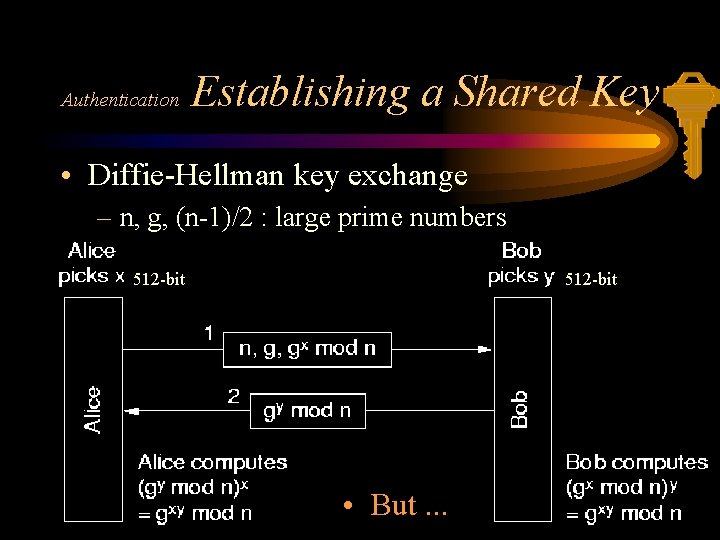
Authentication Establishing a Shared Key • Diffie-Hellman key exchange – n, g, (n-1)/2 : large prime numbers 512 -bit • But. . .
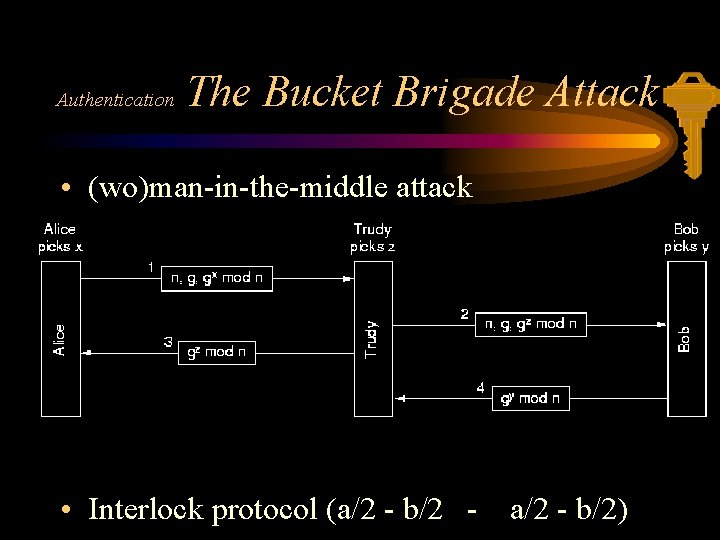
Authentication The Bucket Brigade Attack • (wo)man-in-the-middle attack • Interlock protocol (a/2 - b/2 - a/2 - b/2)
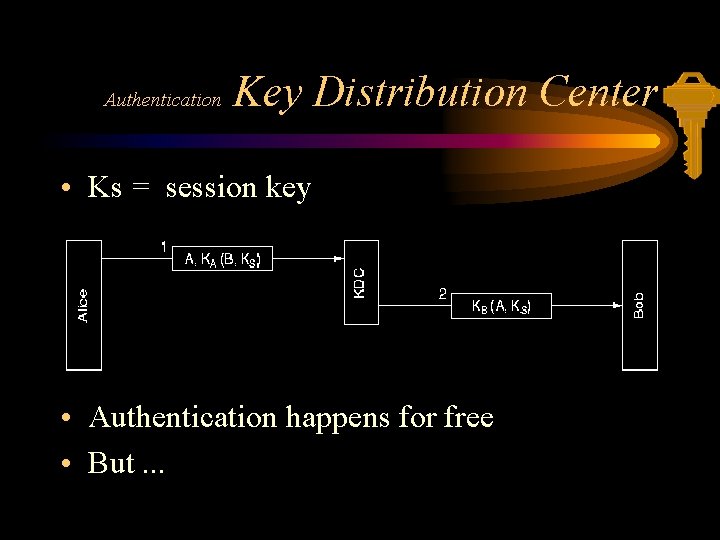
Authentication Key Distribution Center • Ks = session key • Authentication happens for free • But. . .
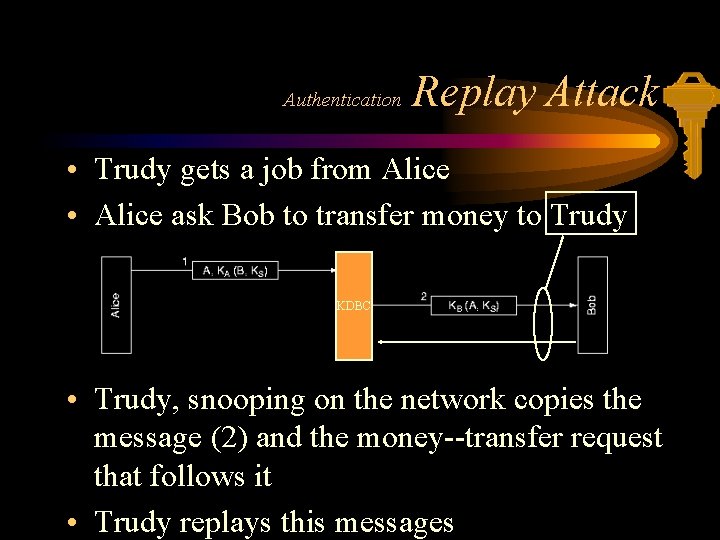
Authentication Replay Attack • Trudy gets a job from Alice • Alice ask Bob to transfer money to Trudy KDBC • Trudy, snooping on the network copies the message (2) and the money--transfer request that follows it • Trudy replays this messages
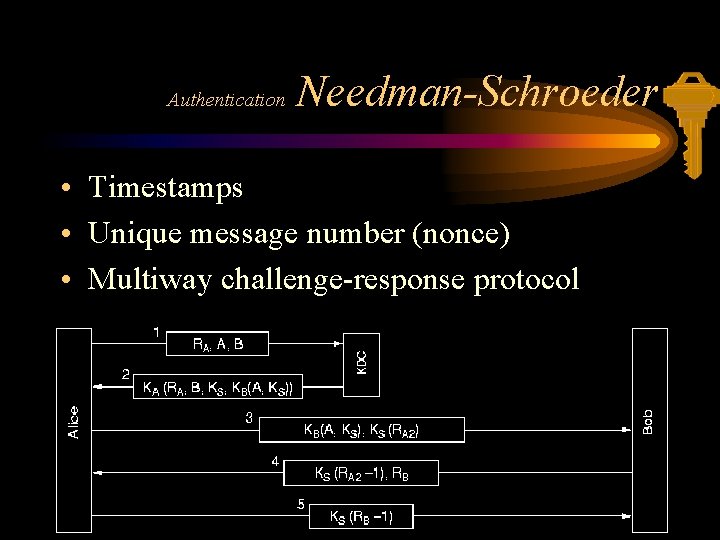
Authentication Needman-Schroeder • Timestamps • Unique message number (nonce) • Multiway challenge-response protocol
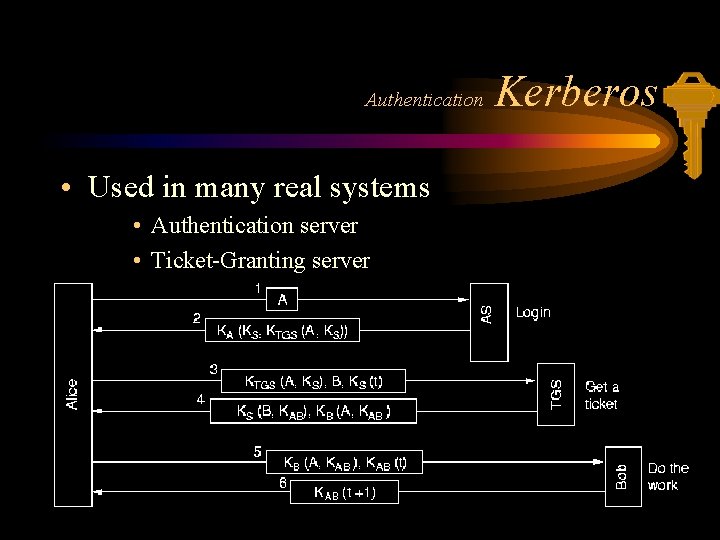
Authentication • Used in many real systems • Authentication server • Ticket-Granting server Kerberos
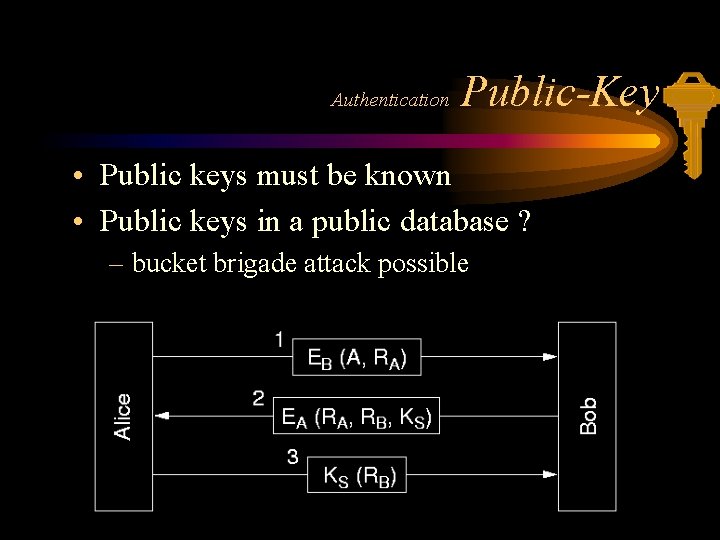
Authentication Public-Key • Public keys must be known • Public keys in a public database ? – bucket brigade attack possible

Digital Signatures • Signing (an order to buy a ton of gold) 1 The receiver can verify the claimed identity of the sender 2 The sender cannot later repudiate the contents of the message 3 The receiver cannot possibly have concocted the message himself
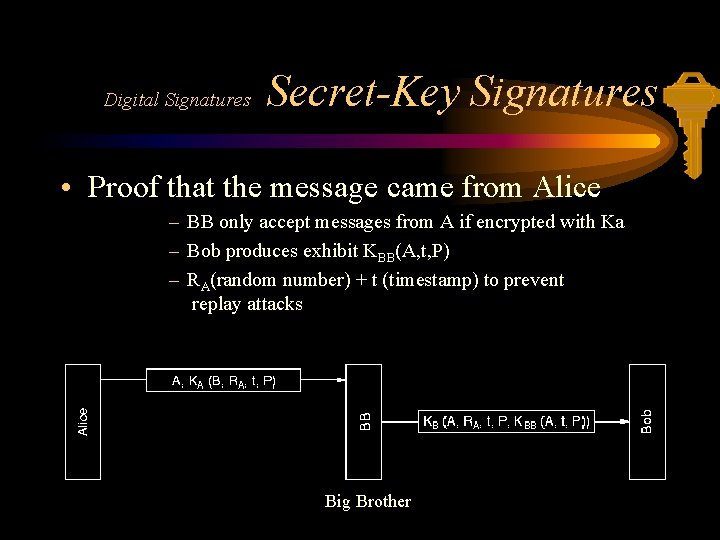
Digital Signatures Secret-Key Signatures • Proof that the message came from Alice – BB only accept messages from A if encrypted with Ka – Bob produces exhibit KBB(A, t, P) – RA(random number) + t (timestamp) to prevent replay attacks Big Brother
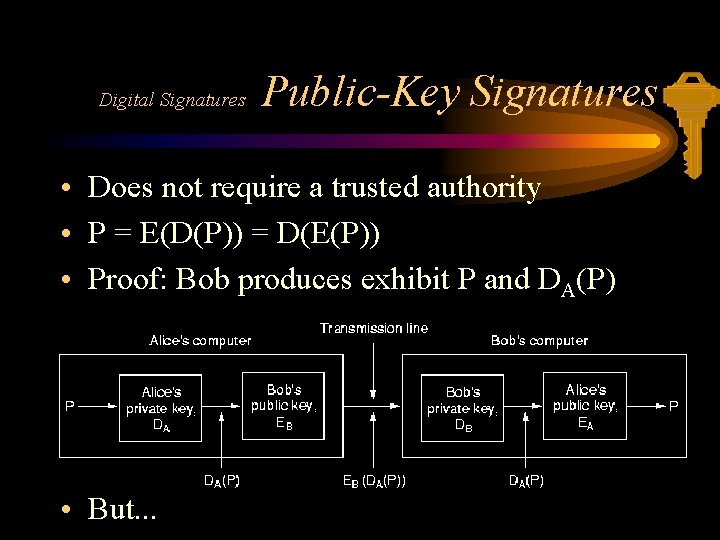
Digital Signatures Public-Key Signatures • Does not require a trusted authority • P = E(D(P)) = D(E(P)) • Proof: Bob produces exhibit P and DA(P) • But. . .
Digital Signatures Public-Key Problems • Alice discloses her secret key – If the price of gold drops, she can repudiate here message to Bob by telling the police here key was stolen • Alice decides to change her key – Some authority should record all key changes and their dates
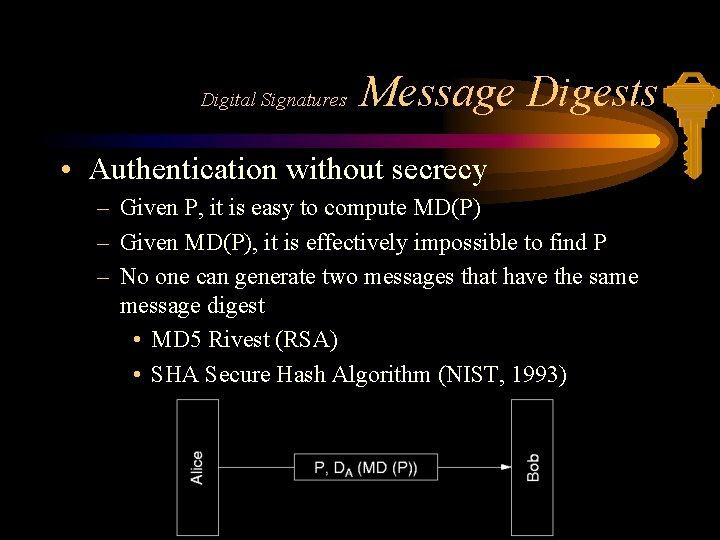
Digital Signatures Message Digests • Authentication without secrecy – Given P, it is easy to compute MD(P) – Given MD(P), it is effectively impossible to find P – No one can generate two messages that have the same message digest • MD 5 Rivest (RSA) • SHA Secure Hash Algorithm (NIST, 1993)
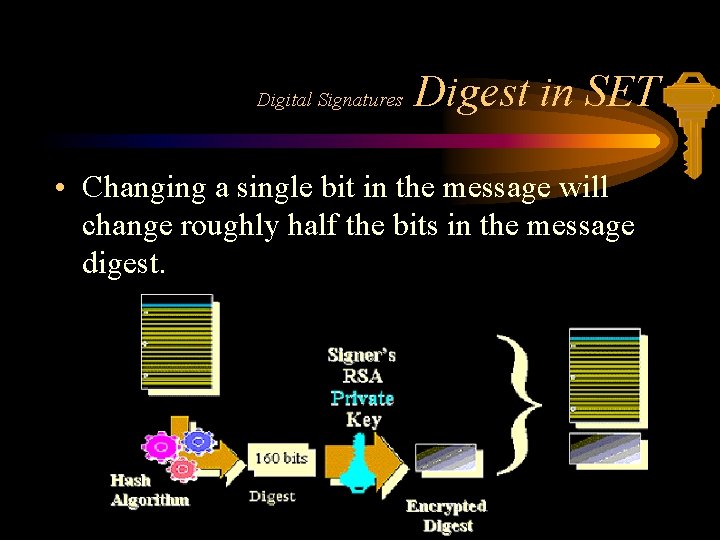
Digital Signatures Digest in SET • Changing a single bit in the message will change roughly half the bits in the message digest.
Digital Signatures Digital Signature Standard • 1991, National Institute of Standards and Technology • El Gamal public-key algorithm • difficulty of computing discrete logarithms Too secret (NSA) Too new (not yet thoroughly analysed) Too slow (10 to 40 times slower than RSA) Too insecure (512 -bit key)

Email Privacy • Pretty Good Privacy (Zimmermann) – Privacy – Authentication – Digital signatures – Compression – Free of charge via the Internet • Privacy Enhanced Mail
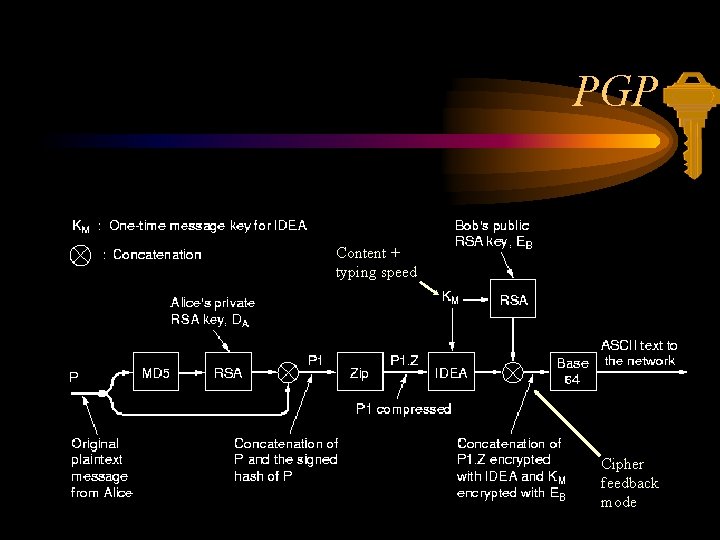
PGP Content + typing speed Cipher feedback mode
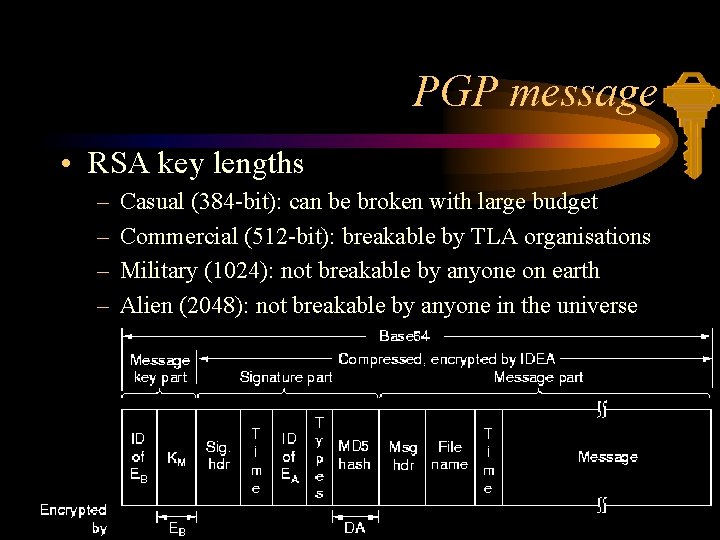
PGP message • RSA key lengths – – Casual (384 -bit): can be broken with large budget Commercial (512 -bit): breakable by TLA organisations Military (1024): not breakable by anyone on earth Alien (2048): not breakable by anyone in the universe
Browser security • SSL (Secure Socket Layer) - Netscape • Public key cryptography. • Certificates (verisign, Belsign, AT&T …) – data encryption – server authentication – message integrity – client authentication
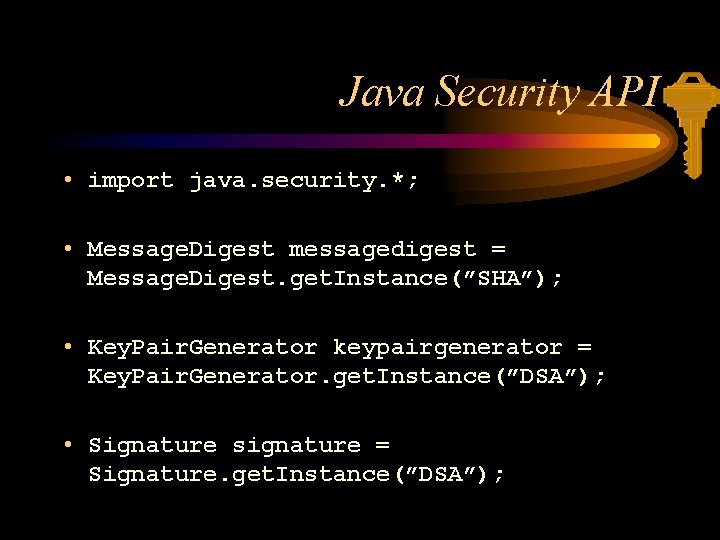
Java Security API • import java. security. *; • Message. Digest messagedigest = Message. Digest. get. Instance(”SHA”); • Key. Pair. Generator keypairgenerator = Key. Pair. Generator. get. Instance(”DSA”); • Signature signature = Signature. get. Instance(”DSA”);
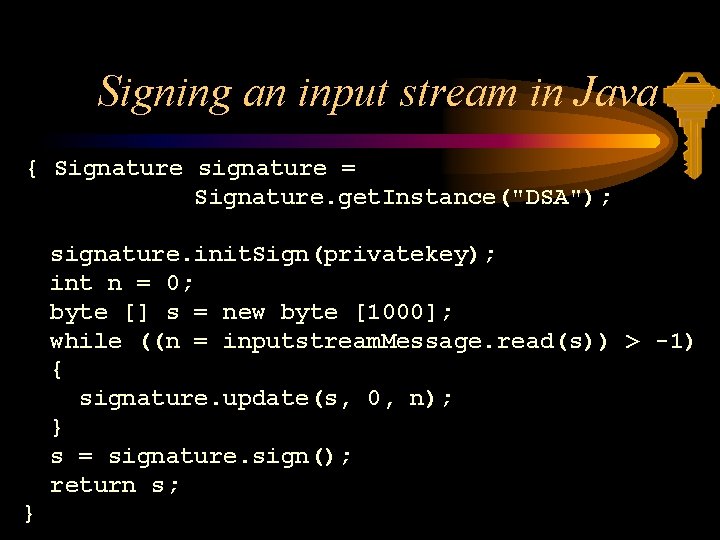
Signing an input stream in Java { Signature signature = Signature. get. Instance("DSA"); signature. init. Sign(privatekey); int n = 0; byte [] s = new byte [1000]; while ((n = inputstream. Message. read(s)) > -1) { signature. update(s, 0, n); } s = signature. sign(); return s; }
Suggested Readings • • • Tanenbaum, Andrew, S. , ”Computer Networks” Anderson, R. , “Why Cryptosystems Fail” Kaufman et al. , “Network Security” Schneier, “Applied Crypthography” Dr. Dobb’s journal, december 1998
- Slides: 56