Network Intrusion Detection David La Porte davidlaporteharvard edu

![NICK [XDCC]SLT-L 482{A} USER b 0 b 32. : XDCC{A} MODE [XDCC]SLT-L 482 +i{A} NICK [XDCC]SLT-L 482{A} USER b 0 b 32. : XDCC{A} MODE [XDCC]SLT-L 482 +i{A}](https://slidetodoc.com/presentation_image_h2/596b58077fc7ad7a06c8054902459eb1/image-9.jpg)

- Slides: 20

Network Intrusion Detection David La. Porte david_laporte@harvard. edu
Topics ® What is IDS? ® HIDS v. NIDS ® Signatures ® Active Response / IPS ® NIDS on the Cheap ® Additional Resources
What is IDS? the art of detecting inappropriate, incorrect, or anomalous activity. ID systems that operate on a host to detect malicious activity on that host are called host-based ID systems, and ID systems that operate on network data flows are called network-based ID systems. http: //www. sans. org/newlook/resources/IDFAQ/what_is_ID. htm
HIDS v. NIDS ® Defense in depth, layered security ® HIDS ® Typically software installed on a system ® Agent-based ® Monitors multiple data sources, including file system meta-data, log files ® Wrapper-based ® Acts like a firewall – denies or accepts connections or logins based on defined policy
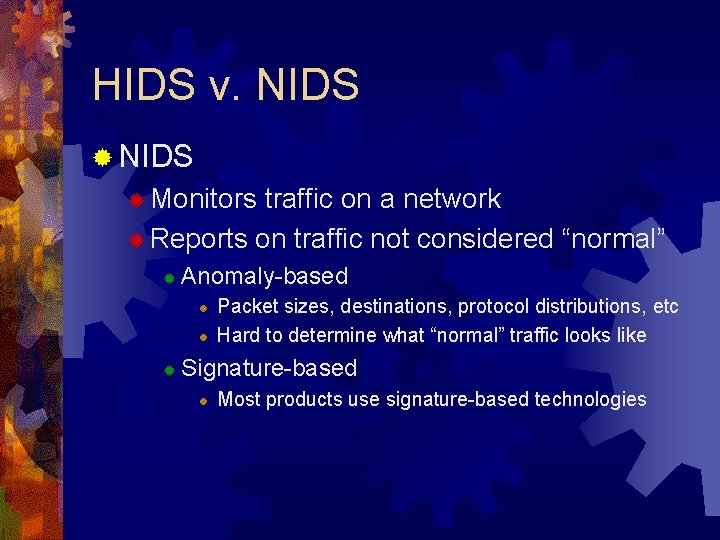
HIDS v. NIDS ® Monitors traffic on a network ® Reports on traffic not considered “normal” ® Anomaly-based l l ® Packet sizes, destinations, protocol distributions, etc Hard to determine what “normal” traffic looks like Signature-based l Most products use signature-based technologies
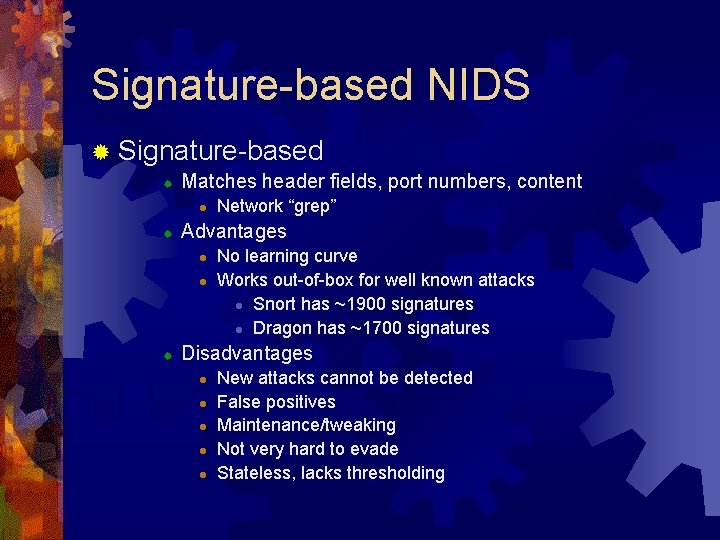
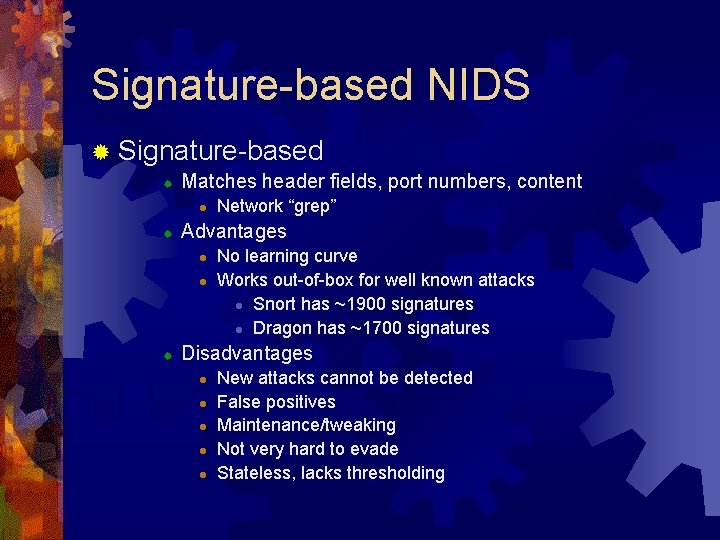
Signature-based NIDS ® Signature-based ® Matches header fields, port numbers, content l ® Advantages l l ® Network “grep” No learning curve Works out-of-box for well known attacks l Snort has ~1900 signatures l Dragon has ~1700 signatures Disadvantages l l l New attacks cannot be detected False positives Maintenance/tweaking Not very hard to evade Stateless, lacks thresholding
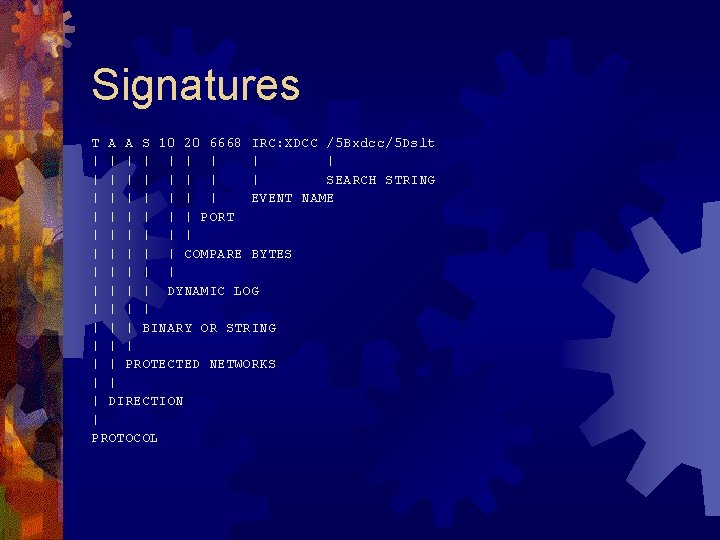
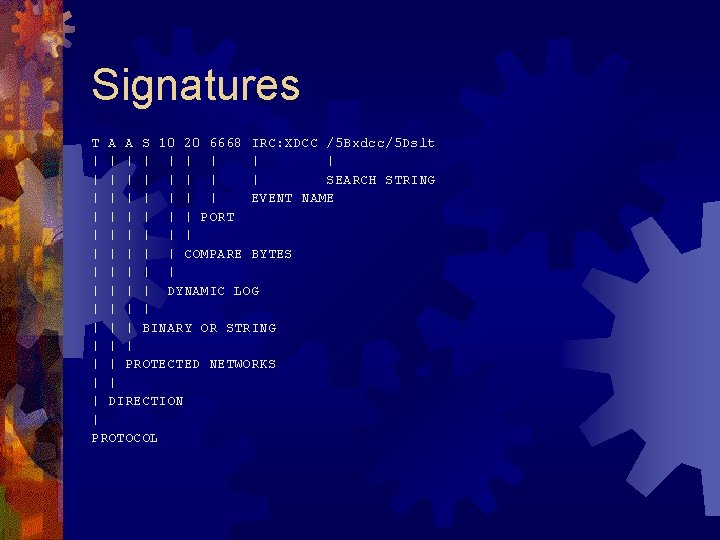
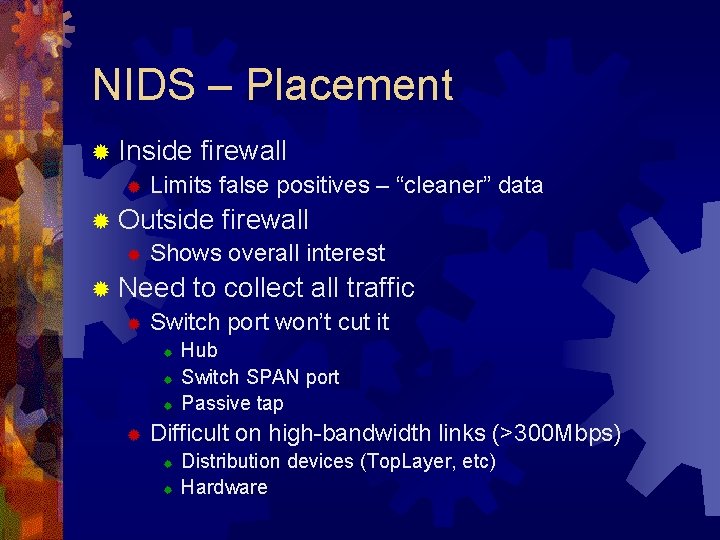
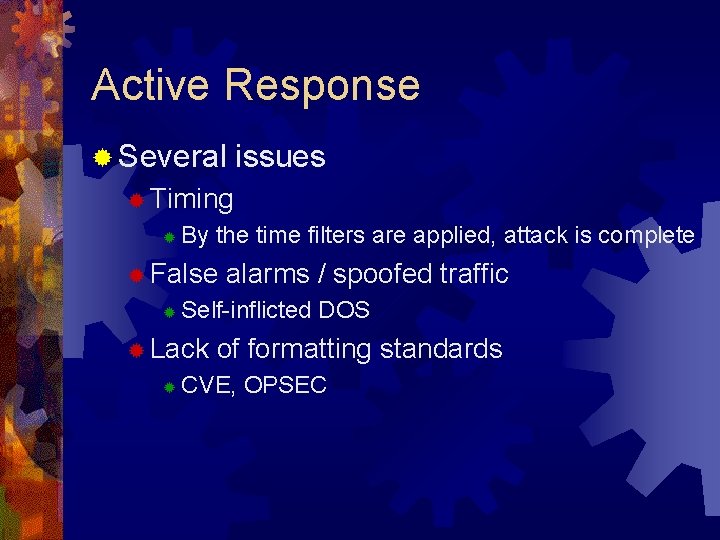
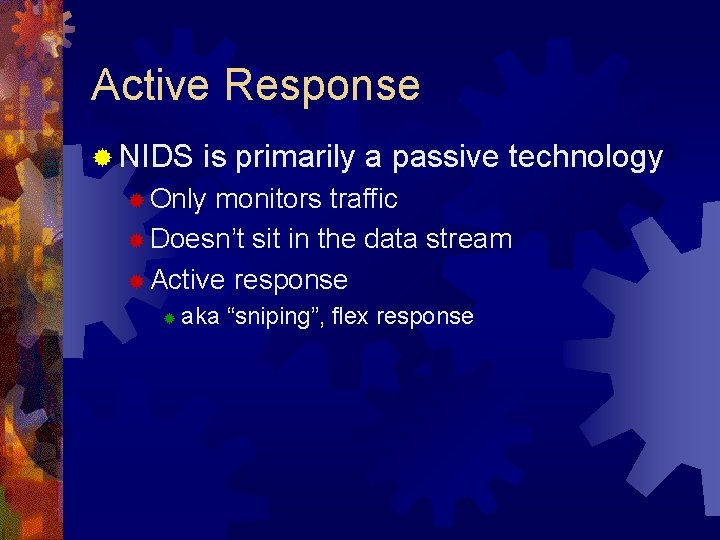
Signatures T A A S 10 20 6668 IRC: XDCC /5 Bxdcc/5 Dslt | | | | | SEARCH STRING | | | | EVENT NAME | | | PORT | | | COMPARE BYTES | | | | | DYNAMIC LOG | | | | BINARY OR STRING | | | PROTECTED NETWORKS | | | DIRECTION | PROTOCOL
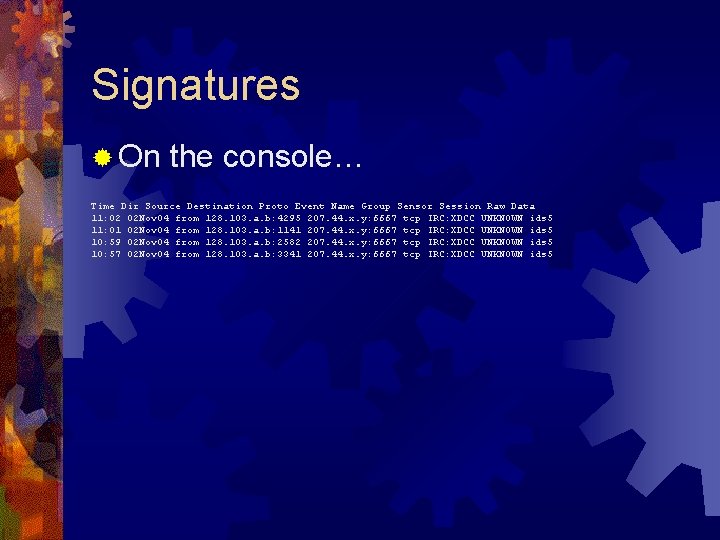
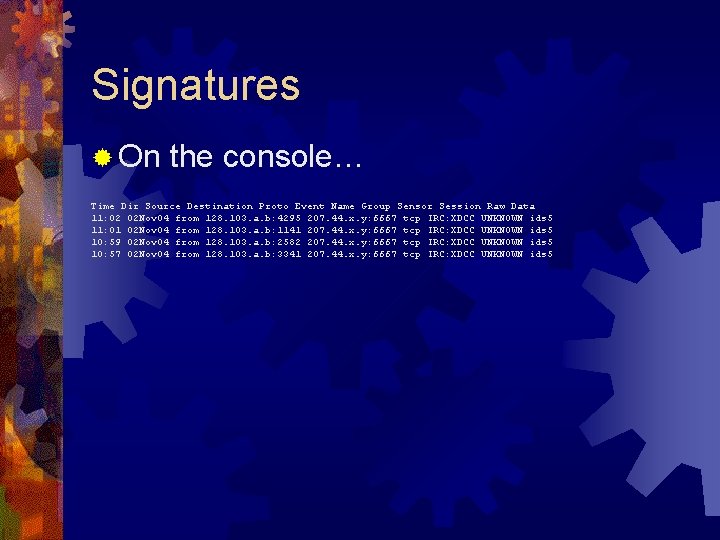
Signatures ® On the console… Time Dir Source Destination Proto Event Name Group Sensor Session Raw Data 11: 02 02 Nov 04 from 128. 103. a. b: 4295 207. 44. x. y: 6667 tcp IRC: XDCC UNKNOWN ids 5 11: 01 02 Nov 04 from 128. 103. a. b: 1141 207. 44. x. y: 6667 tcp IRC: XDCC UNKNOWN ids 5 10: 59 02 Nov 04 from 128. 103. a. b: 2582 207. 44. x. y: 6667 tcp IRC: XDCC UNKNOWN ids 5 10: 57 02 Nov 04 from 128. 103. a. b: 3341 207. 44. x. y: 6667 tcp IRC: XDCC UNKNOWN ids 5
![NICK XDCCSLTL 482A USER b 0 b 32 XDCCA MODE XDCCSLTL 482 iA NICK [XDCC]SLT-L 482{A} USER b 0 b 32. : XDCC{A} MODE [XDCC]SLT-L 482 +i{A}](https://slidetodoc.com/presentation_image_h2/596b58077fc7ad7a06c8054902459eb1/image-9.jpg)
NICK [XDCC]SLT-L 482{A} USER b 0 b 32. : XDCC{A} MODE [XDCC]SLT-L 482 +i{A} : snagged. wi. us. criten. net NOTICE AUTH : *** Looking up your hostname. . . {A} : snagged. wi. us. criten. net NOTICE AUTH : *** Found your hostname, cached{A} : snagged. wi. us. criten. net NOTICE AUTH : *** Checking Ident{A} : snagged. wi. us. criten. net 001 [XDCC]SLT-L 482 : Welcome to the Criten IRC Network [XDCC]SLT-L 482!~b 0 b@jojo. harvard. edu{D}{A} : snagged. wi. us. criten. net 002 [XDCC]SLT-L 482 : Your host is snagged. wi. us. criten. net[@0. 0], running version bahamut-1. 4(34){D}{A} : snagged. wi. us. criten. net 003 [XDCC]SLT-L 482 : This server was created Fri Oct 18 2002 at 12: 49: 34 CDT{D}{A} : snagged. wi. us. criten. net 004 [XDCC]SLT-L 482 snagged. wi. us. criten. net bahamut-1. 4(34) oiwscrknfyda. Abghe bikl. Lm. Mnopr. Rstvc {D}{A} : snagged. wi. us. criten. net 005 [XDCC]SLT-L 482 NOQUIT WATCH=128 SAFELIST MODES=13 MAXCHANNELS=15 MAXBANS=100 NICKLEN=30 TO PICLEN=307 KICKLEN=307 CHANTYPES=&# PREFIX=( ov)@+ NETWORK=Criten SILENCE=10 CASEMAPPING=ascii : are available on this serv er{D}{A} : snagged. wi. us. criten. net 251 [XDCC]SLT-L 482 : There are 59 users and 6470 invisible on 17 servers{D}{A} : snagged. wi. us. criten. net 252 [XDCC]SLT-L 482 30 : IRC Operators online{D}{A} : snagged. wi. us. criten. net 253 [XDCC]SLT-L 482 84 : unknown connection(s){D}{A} : snagged. wi. us. criten. net 254 [XDCC]SLT-L 482 738 : channels formed{D}{A} : snagged. wi. us. criten. net 255 [XDCC]SLT-L 482 : I have 705 clients and 1 servers{D}{A} : snagged. wi. us. criten. net 265 [XDCC]SLT-L 482 : Current local users: 705 Max: 3506{D}{A} : snagged. wi. us. criten. net 266 [XDCC]SLT-L 482 : Current global users: 6529 Max: 13238{D}{A} : snagged. wi. us. criten. net NOTICE [XD: snagged. wi. us. criten. net NOTICE AUTH : *** Found your hostname, cached{A} : snagged. wi. us. criten. net NOTICE AUTH : *** Checking Ident{A} : snagged. wi. us. criten. net 001 [XDCC]SLT-L 482 : Welcome to the Criten IRC Network [XDCC]SLT-L 482!~b 0 b@dhcp-108 -176. harv ard. edu{D}{A} : snagged. wi. us. criten. net 002 [XDCC]SLT-L 482 : Your host is snagged. wi. us. criten. net[@0. 0], running version bahamut-1. 4(34){D}{A} : snagged. wi. us. criten. net 003 [XDCC]SLT-L 482 : This server was created Fri Oct 18 2002 at 12: 49: 34 CDT{D}{A} : snagged. wi. us. criten. net 004 [XDCC]SLT-L 482 snagged. wi. us. criten. net bahamut-1. 4(34) oiwscrknfyda. Abghe bikl. Lm. Mnopr. Rstvc {D}{A} : snagged. wi. us. criten. net 005 [XDCC]SLT-L 482 NOQUIT WATCH=128 SAFELIST MODES=13 MAXCHANNELS=15 MAXBANS=100 NICKLEN=30 TO PICLEN=307 KICKLEN=307 CHANTYPES=&# PREFIX=( ov)@+ NETWORK=Criten SILENCE=10 CASEMAPPING=ascii : are available on this serv er{D}{A} : snagged. wi. us. criten. net 251 [XDCC]SLT-L 482 : There are 59 users and 6470 invisible on 17 servers{D}{A} : snagged. wi. us. criten. net 252 [XDCC]SLT-L 482 30 : IRC Operators online{D}{A} : snagged. wi. us. criten. net 253 [XDCC]SLT-L 482 84 : unknown connection(s){D}{A} : snagged. wi. us. criten. net 254 [XDCC]SLT-L 482 738 : channels formed{D}{A} : snagged. wi. us. criten. net 255 [XDCC]SLT-L 482 : I have 705 clients and 1 servers{D}{A} : snagged. wi. us. criten. net 265 [XDCC]SLT-L 482 : Current local users: 705 Max: 3506{D}{A} : snagged. wi. us. criten. net 266 [XDCC]SLT-L 482 : Current global users: 6529 Max: 13238{D}{A} : snagged. wi. us. criten. net NOTICE [XD{A}
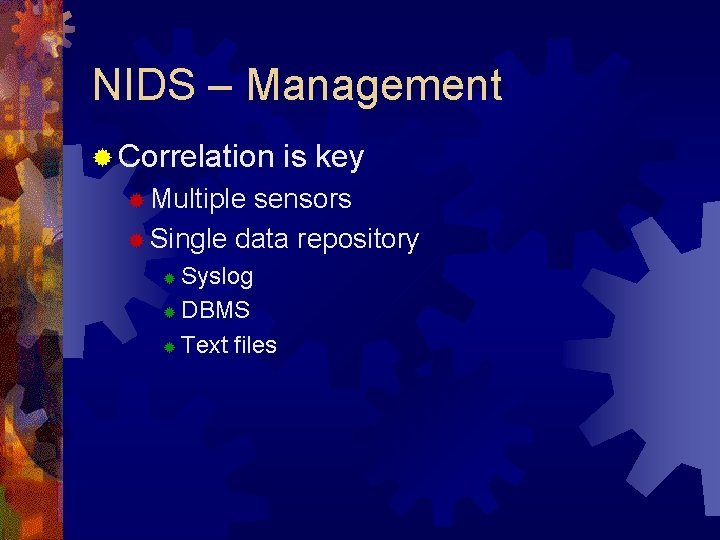
NIDS – Management ® Correlation ® Multiple is key sensors ® Single data repository Syslog ® DBMS ® Text files ®
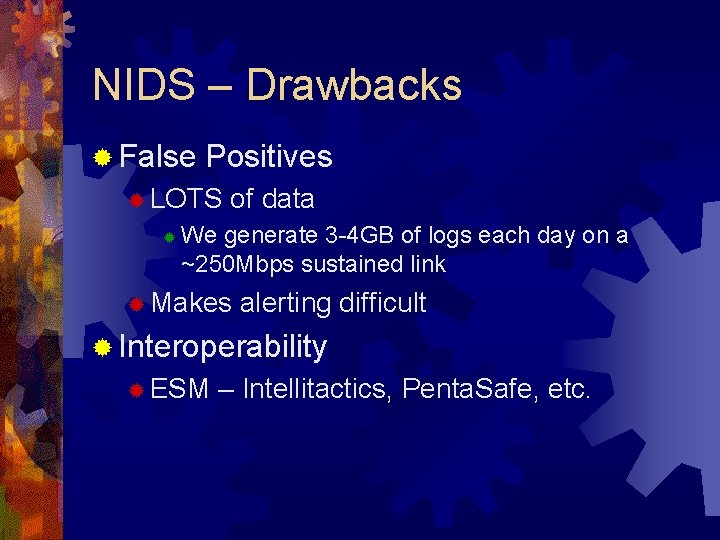
NIDS – Placement ® Inside firewall ® Limits false positives – “cleaner” data ® Outside firewall ® Shows overall interest ® Need to collect all traffic ® Switch port won’t cut it ® ® Hub Switch SPAN port Passive tap Difficult on high-bandwidth links (>300 Mbps) ® ® Distribution devices (Top. Layer, etc) Hardware
NIDS – Drawbacks ® False Positives ® LOTS ® of data We generate 3 -4 GB of logs each day on a ~250 Mbps sustained link ® Makes alerting difficult ® Interoperability ® ESM – Intellitactics, Penta. Safe, etc.
NIDS - Drawbacks ® Evasion ® Packet fragmentation Out of order, overlapping ® Fragroute ® ® Character ® encodings / padding Unicode, mixed case, . . /. . ’s, �’s ® OS stack behavior ® A simple “grep” of a packet won’t work
Active Response ® NIDS is primarily a passive technology ® Only monitors traffic ® Doesn’t sit in the data stream ® Active response ® aka “sniping”, flex response
Active Response ® Several issues ® Timing ® By the time filters are applied, attack is complete ® False ® Self-inflicted DOS ® Lack ® alarms / spoofed traffic of formatting standards CVE, OPSEC
Intrusion Prevention ® Place system in-line ® Hardware ® Redundancy ® Acts as an IDS/Firewall hybrid ® Hogwash
NIDS on the Cheap ® So you want ® Snort ® ® Open-source DBMS ACID ® ® Open-source NIDS Quickly becoming the “Apache” of IDS Runs on Windows and most Unix variants My. SQL ® ® a NIDS? Great web-based front-end for Snort/Mysql A place to collect traffic ® ® Your NIC is fine if you have only one machine Use a hub if you’ve got a LAN
Additional Resources ® ® ® Fragroute ® http: //monkey. org/~dugsong/fragroute/ Insertion, Evasion, and Denial of Service: Eluding Network Intrusion Detection ® http: //secinf. net/info/idspaper/idspaper. html HIDS Products Port. Sentry ® http: //www. psionic. com/products/portsentry. html Tripwire ® http: //www. tripwire. com/ AIDE ® http: //www. cs. tut. fi/~rammer/aide. html
Additional Resources ® NIDS Products ® Snort ® http: //www. snort. org ® Dragon ® http: //www. enterasys. com/ids/ ® Cisco. Secure IDS ® ISS Real. Secure ® http: //www. iss. net/products_services/enterprise_protection/rsnetwork/index. php ACID ® http: //www. andrew. cmu. edu/~rdanyliw/snortacid. html ® Hogwash ® http: //hogwash. sourceforge. net/ ®

Questions?