Network Guide to Networks Third Edition Chapter 9
- Slides: 51
Network+ Guide to Networks Third Edition Chapter 9: Networking with Unix and Linux
Objectives: üDescribe the origins and history of the UNIX operating system üIdentify similarities and differences between popular implementations of UNIX üUnderstand why you might choose a UNIX or Linux server for a corporate network Network + 2
Objectives: (continued) üExplain and execute basic UNIX and Linux commands üInstall Linux on an Intel-based PC üUse Linux to add groups and users and to change file access permissions üExplain how UNIX and Linux can be internetworked with other operating systems Network + 3
A Brief History of UNIX • AT&T Source code • System V. • BSD (Berkeley Software Distribution) • The SCO Group • The Open Group Network + 4
Varieties of UNIX • UNIX features: • Multiple, simultaneously logged on users • Multiple, simultaneously running tasks • Mount disk partitions upon demand • Permissions for file and directory access • Uniform method of issuing or receiving data from hardware devices, files, and running programs Network + 5
Varieties of UNIX (continued) • UNIX features: • The ability to start a program without interfering • • • with a currently running program Hundreds of subsystems, including dozens of programming languages Source code portability Window interfaces that the user can configure, the most popular of which is the X Window system Network + 6
Varieties of UNIX (continued) • Proprietary UNIX • Licensed copy from The SCO Group • Popular Vendors • Sun Microsystems--Solaris • IBM--AIX • HP--HP-UX, Network + 7
Varieties of UNIX (continued) • Proprietary UNIX system advantages: • Accountability and support • Optimization of hardware and software • Predictability and compatibility • One drawback • No access to the system’s source code Network + 8
Open Source UNIX • Open source software or Freely distributable software • GNU • BSD • Linux Network + 9
Open Source UNIX (continued) • Open Source UNIX • Primary advantage • Cost • Users can modify its code • Freely distributable • Run not only on Intel-based processors, but also on other processor brands Network + 10
Why Choose Linux? • What considerations: • Is it compatible with my existing infrastructure? • Will it provide the security required by my • • • resources? Can my technical staff manage it effectively? Will my applications run smoothly on it? Will it accommodate future growth (is it scalable)? Network + 11
Why Choose Linux? (continued) • What considerations: (cont. ) • Does it support the additional services required by • • • my users? Does it fit my budget? What additional training will it require? Can I count on competent and consistent support from its manufacturer? Network + 12
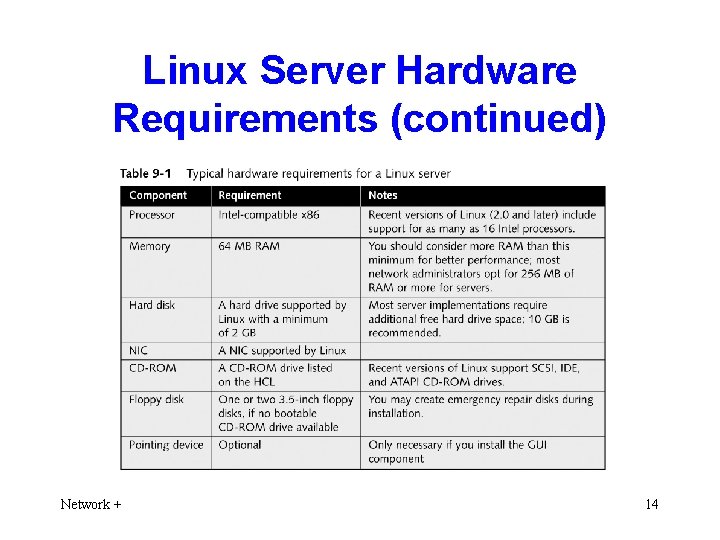
Linux Server Hardware Requirements • Table 9 -1 shows the minimum hardware • requirements for the various components of a Linux server. Hardware compatibility list (HCL) at www. tldp. org/HOWTO/Hardware-HOWTO/. Network + 13
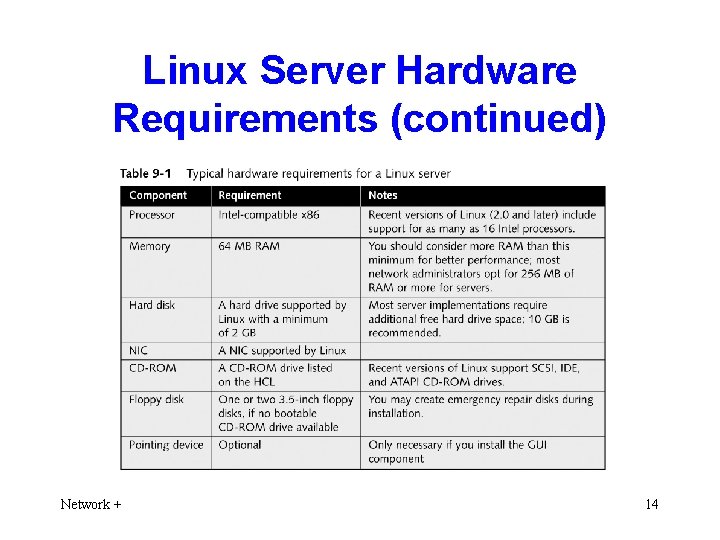
Linux Server Hardware Requirements (continued) Network + 14
Linux Server Hardware Requirements (continued) • What additional hardware your server may require: • Which applications and services will run • How many users • How much random access memory (RAM) • How much secondary storage (hard disk) Network + 15
A Closer Look at Linux • Linux Multiprocessing • In addition to processes, Linux also supports • • threads Allocates separate resources (such as memory space) to each process as it is created Symmetric multiprocessing (SMP) Network + 16
A Closer Look at Linux (continued) • The Linux Memory Model • Use both physical and virtual memory efficiently • Allocates a memory area for each application • Attempts to decrease the inefficiency of this practice, however, by sharing memory between programs wherever it can Network + 17
A Closer Look at Linux (continued) • The Linux Kernel • Kernel • Core of the Linux system • Kernel module • Instructions for performing a specific task Network + 18
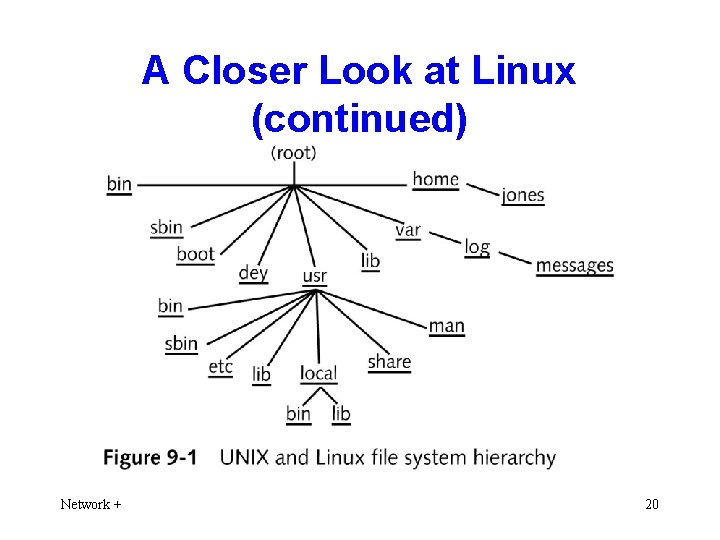
A Closer Look at Linux (continued) • Linux File and Directory Structure • Hierarchical file system • UNIX system was one of the first to implement • Method of organizing files and directories on a disk in which directories may contain files and other directories • Most operating systems use hierarchical file systems Network + 19
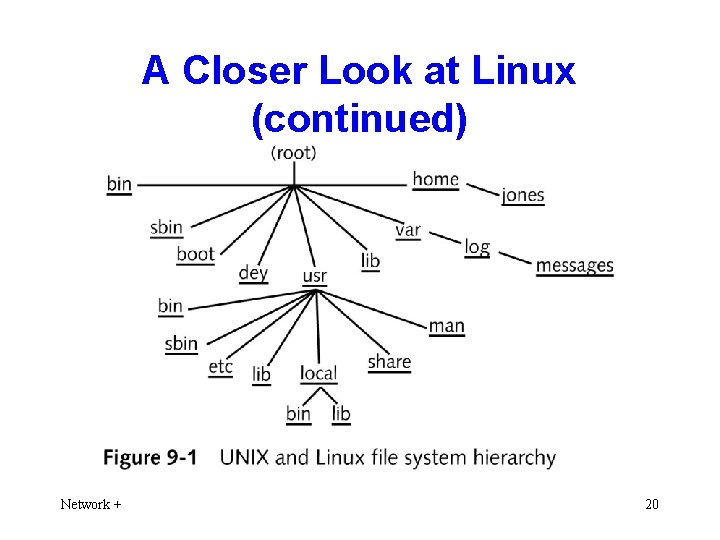
A Closer Look at Linux (continued) Network + 20
A Closer Look at Linux (continued) • Linux File Services • Native file system type, called ext 3 • Allows you to access DOS FAT as well as NTFS • Can both attach shared file systems and share local partitions with other users • Windows or Net. Ware • Network File System (NFS) Network + 21
A Closer Look at Linux (continued) • Linux Internet Services • UNIX-based systems have deep roots in Internet • • • services Leading Internet Web server is an open source software application called Apache Original Web tools—including the first browsers and servers—were developed on UNIX-based systems Full range of Internet services as standard components Network + 22
A Linux Command Sampler • The command line is the primary method of interacting with a Linux system • Command interpreter • Shell Network + 23
A Linux Command Sampler (continued) • Manual pages (Online documentation) • Section 1 covers the commands that you most typically enter while typing in a command window. • Sections 2 through 5 document the programmer’s interface to the Linux system. • Section 6 documents some of the amusements and games that are included in the Linux system. Network + 24
A Linux Command Sampler (continued) • Manual pages (Online documentation) • Section 7 describes the device drivers for the system. • Section 8 covers the commands used by administrators to manage the system. • Section 9 documents the Linux kernel functions programmers use when writing device drivers. Network + 25
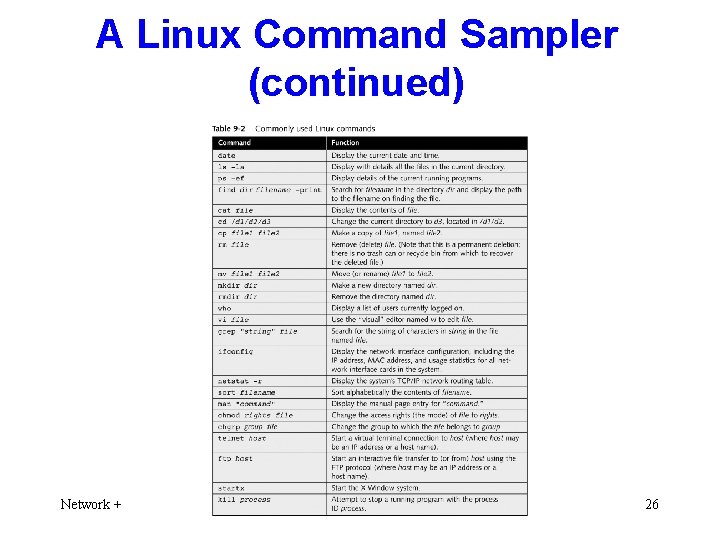
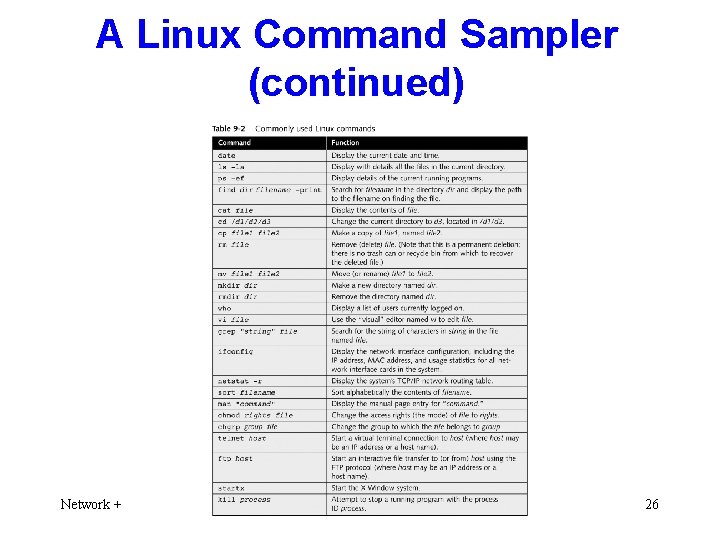
A Linux Command Sampler (continued) Network + 26
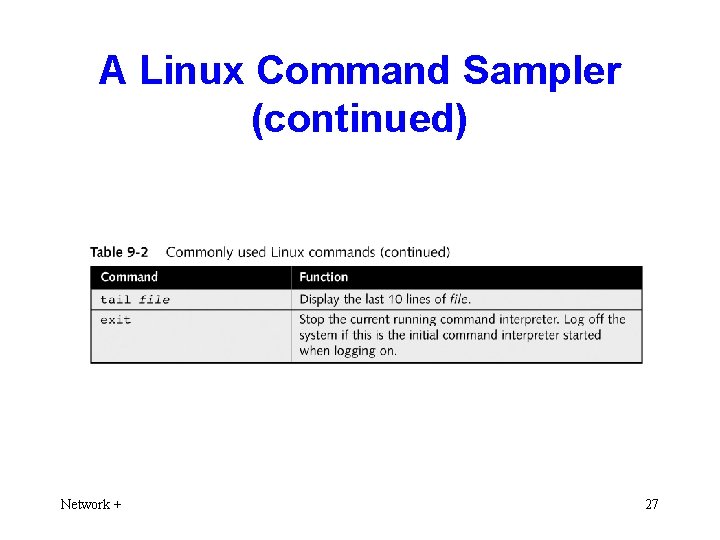
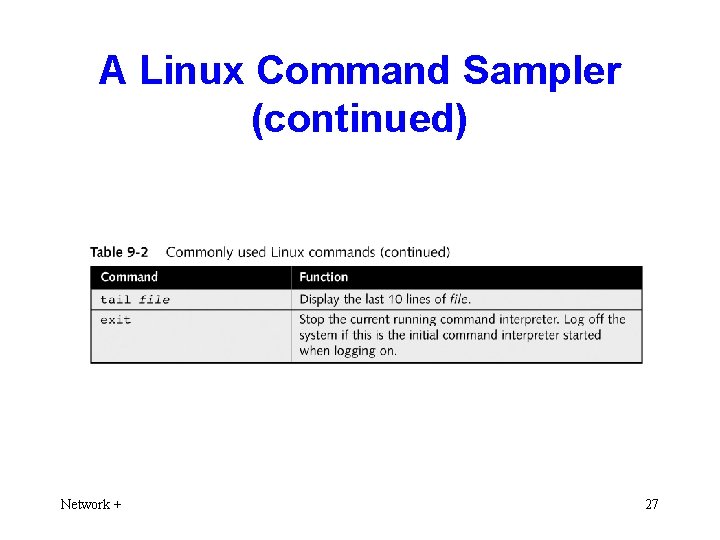
A Linux Command Sampler (continued) Network + 27
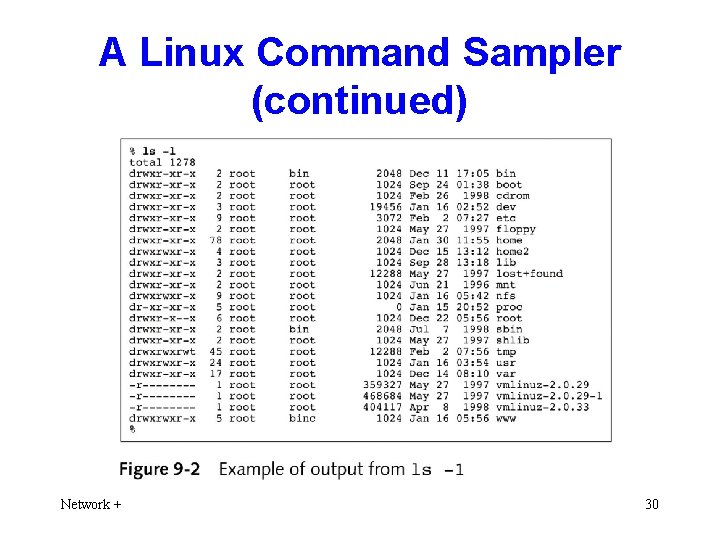
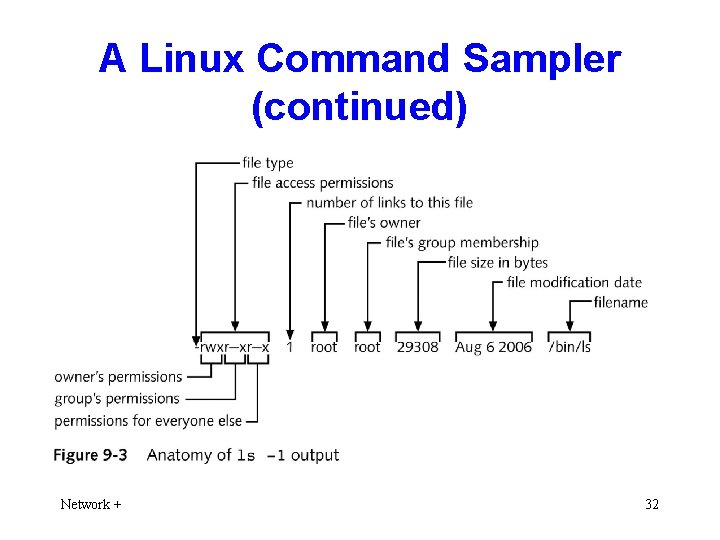
A Linux Command Sampler (continued) • Command ls (with -l) • Learn everything about a file except its contents: • The filename • The file size (in bytes) • The date and time that the file was created • The date and time that the file was last accessed (viewed or printed) Network + 28
A Linux Command Sampler (continued) • Command ls (with -l) (cont. ) • The date and time that the file contents were last modified • The number of “aliases” or links to the file • The numeric identifier of the user who owns the file • The numeric identifier of the group to which the file belongs • The access rights for the owner, the group, and all others Network + 29
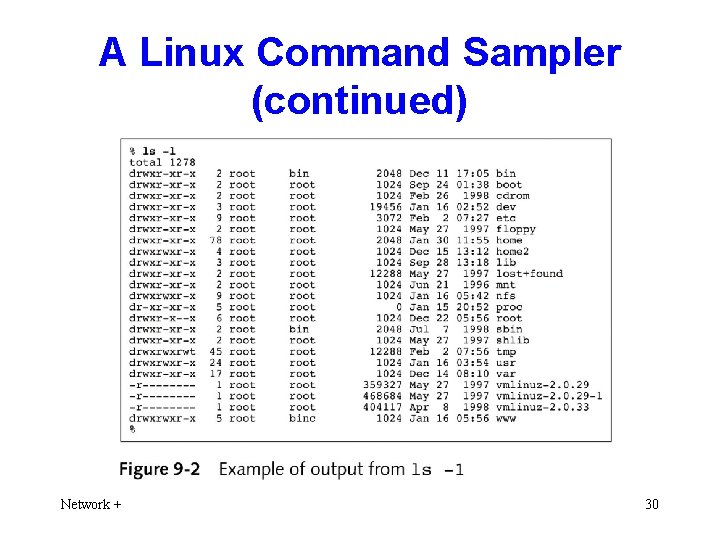
A Linux Command Sampler (continued) Network + 30
A Linux Command Sampler (continued) • Command ls (with -l) (cont. ) • Files with a type of “d” are directories • “-” are regular files such as word-processing files • • • or spreadsheet files “l” for symbolic link files “b” for block device files “c” for character device files Network + 31
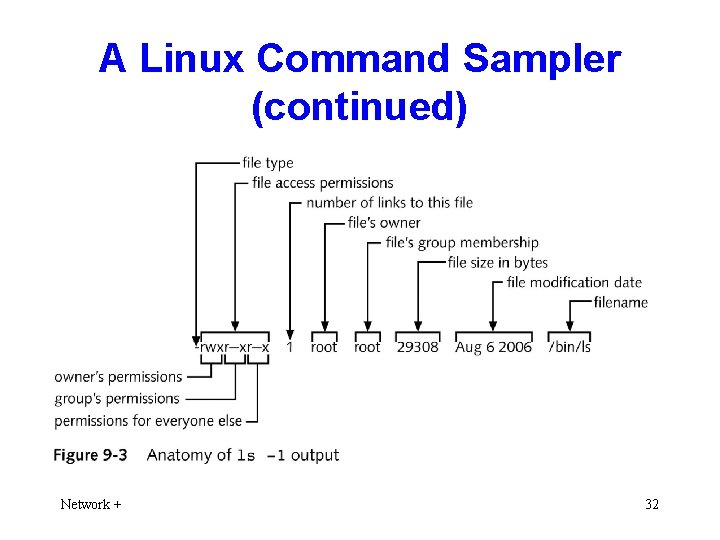
A Linux Command Sampler (continued) Network + 32
Planning for Installation • Answer the following questions: • What is the new server’s name? • What is the server’s IP address? • What kind of video card is installed in the server? • What do you want the administrative user’s • password to be? How can I remember all of this information? Network + 33
Installing and Configuring a Red Hat Linux Server • Step by step • Select the language the system will use • Confirm the keyboard layout • Confirm your mouse type • Select disk drive partitioning options • Choose booting options Network + 34
Installing and Configuring a Red Hat Linux Server (continued) • Step by step (cont. ) • Configure the network interface (or interfaces) • Configure the network firewall options • Add support for additional languages • Set the time and time zone • Enter (and confirm) the root (administrator) password Network + 35
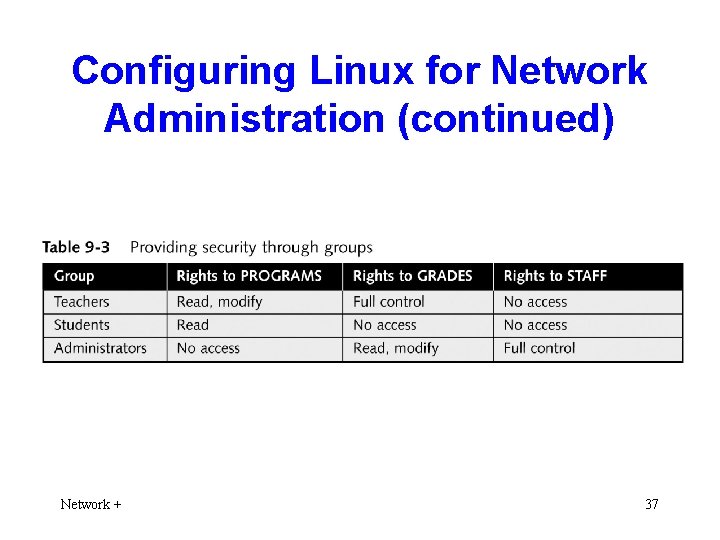
Configuring Linux for Network Administration • The basics of adding users and groups • The basics of modifying file access permissions • Two commands: • groupadd • useradd. Network + 36
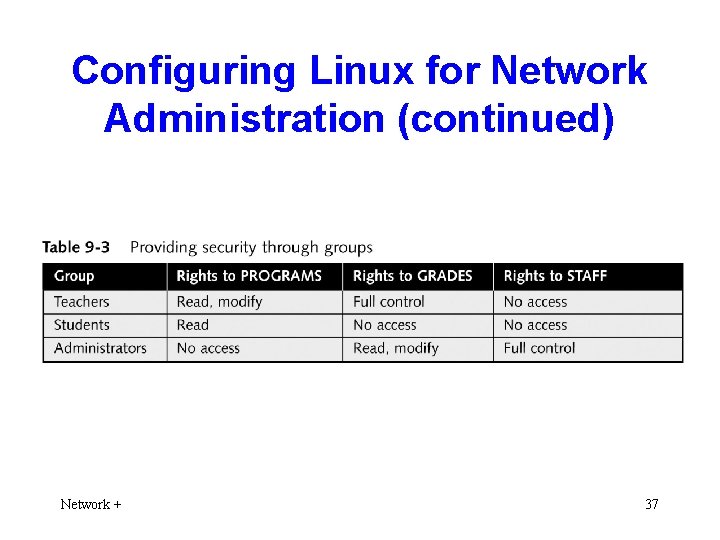
Configuring Linux for Network Administration (continued) Network + 37
Configuring Linux for Network Administration (continued) • To add group IDs to your Linux system: 1. Type groupadd instructors and then press Enter at the command prompt. The group instructors is added. 2. Type groupadd students and then press Enter. The group students is added. 3. Type groupadd administrators and then press Enter. The group administrators is added. Network + 38
Configuring Linux for Network Administration (continued) • To add a new user and assign the user a password: 1. 2. Network + Type useradd –g users –G instructors thomas and then press Enter to add a new user account named thomas. Type passwd thomas and then press Enter. 39
Configuring Linux for Network Administration (continued) 3. Linux prompts you to type the new password. 4. Linux prompts you to retype your password. Enter the same password again; this confirmation helps ensure that you type your new password accurately. Network + 40
Configuring Linux for Network Administration (continued) • Changing File Access Permissions • To create a directory and assign it to a group 1. If you are still logged on to your Linux system, log off by typing exit and then pressing Enter. 2. To log back on to your system as user thomas, type thomas at the login prompt and then press Enter. Network + 41
Configuring Linux for Network Administration (continued) 3. Type the password you assigned for thomas and then press Enter. 4. You see a command window and a command prompt. To create the new directory, type mkdir PROGRAMS and then press Enter. Network + 42
Configuring Linux for Network Administration (continued) 5. Type ls -l and then press Enter. Notice that the directory belongs to the group users. That’s because the primary group to which the user thomas belongs is users. 6. Type chgrp instructors PROGRAMS and then press Enter to assign ownership of the PROGRAMS directory to the group instructors. Network + 43
Configuring Linux for Network Administration (continued) 7. Type ls -l and then press Enter. Notice that the directory is now assigned to the group instructors. Network + 44
Configuring Linux for Network Administration (continued) • To change the access permissions for the PROGRAMS directory: 1. Log on as the user thomas (whose primary directory is instructors). Type chmod g+w PROGRAMS and then press Enter. This command adds write access for the instructors group to the directory PROGRAMS. 2. Next, you will remove read and write access to the PROGRAMS directory for all others. To do so, type chmod o-rw PROGRAMS and then press Enter. Network + 45
Configuring Linux for Network Administration (continued) 3. Type ls -l and then press Enter to view the access permissions assigned to PROGRAMS. You should see a line for PROGRAMS that includes permissions of drwxrwx--x. Network + 46
Internetworking with Other Network Operating Systems • Samba • Communicates with Windows servers • WINE • Enables Windows programs to run on Linux • VMware • Emulates a complete Intel-based computer • Telnet Network + 47
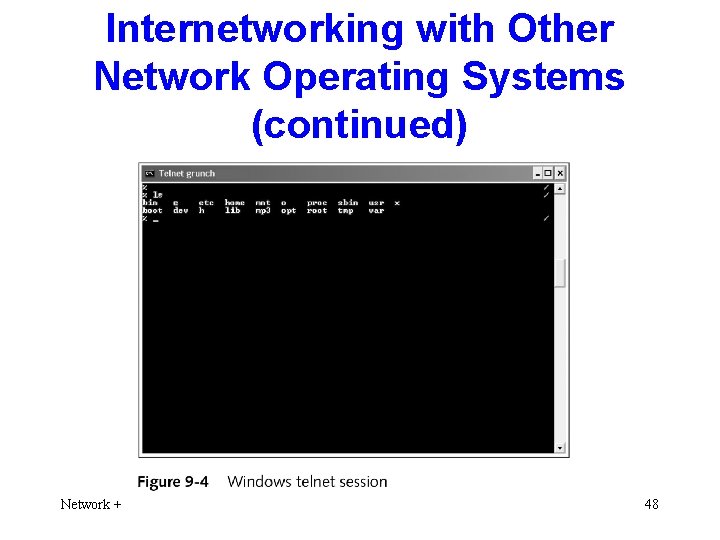
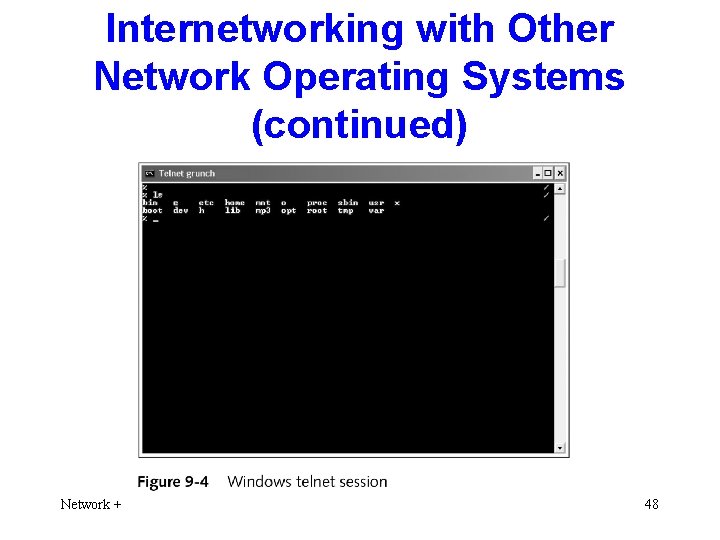
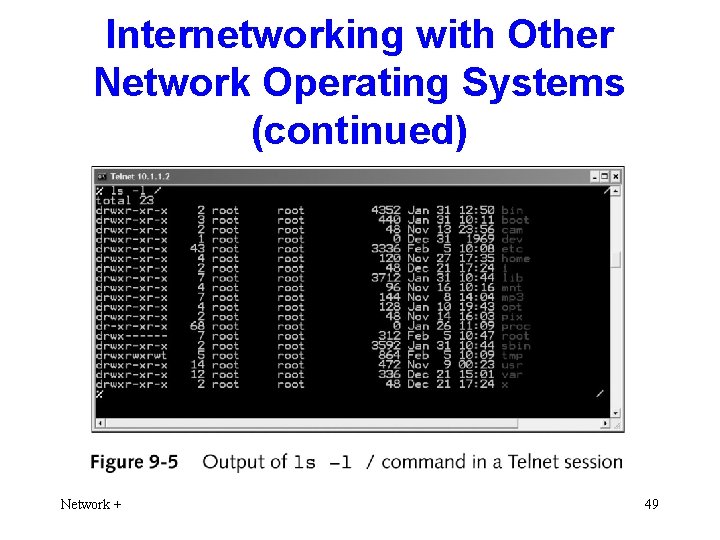
Internetworking with Other Network Operating Systems (continued) Network + 48
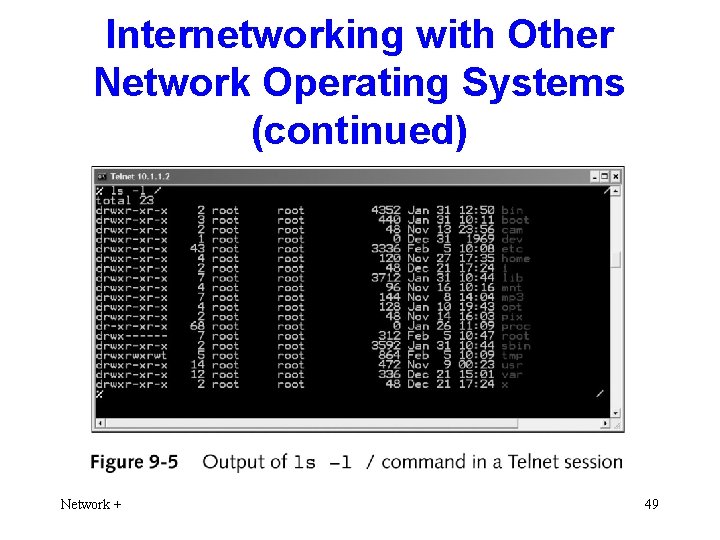
Internetworking with Other Network Operating Systems (continued) Network + 49
Chapter summary • Describe the origins and history of the • • UNIX operating system Identify similarities and differences between popular implementations of UNIX Understand why you might choose a UNIX or Linux server for a corporate network Network + 50
Chapter summary (continued) • Explain and execute basic UNIX and Linux • • • commands Install Linux on an Intel-based PC Use Linux to add groups and users and to change file access permissions Explain how UNIX and Linux can be internetworked with other operating systems Network + 51