Network FlowBased Anomaly Detection of DDo S Attacks
Network Flow-Based Anomaly Detection of DDo. S Attacks Vassilis Chatzigiannakis National Technical University of Athens, Greece vhatzi@netmode. ntua. gr TNC 2004
Intrusion Detection An IDS is a system used for detecting network attacks They detect both successful and unsuccessful attacks They Detect attacks from insiders IDS Categories: Host /Network based They use Misuse /Anomaly detection Distributed Intrusion Detection Systems Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Intrusion Detection(2) Misuse Detection Sniffs network packets If known a signature is matched, it detects the attack Resembles to an anti-virus system Must be updated night and day Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Intrusion Detection(3) Anomaly Detection Checks for great variation from the normal behaviour of an entity An entity could be a user, a computer or network link Use of an expert system The system has to be trained to become operational Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Denial of Service Attacks An attack to suspend the availability of a service Until recently the "bad guys" tried to enter our systems. Now it’s: "If not us, then Nobody" Do. S: single correctly made malicious packets against the target machine Distributed Do. S: traffic flows from various sources to exhaust network or computing resources Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Main Characteristics of Do. S Variable targets: Single hosts or whole domains Computer systems or networks Important: Active network components (e. g. routers) also vulnerable and possible targets! Variable uses & effects: Hacker "turf" wars High profile commercial targets (or just competitors…). Useful in cyber-warfare, terrorism etc. Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
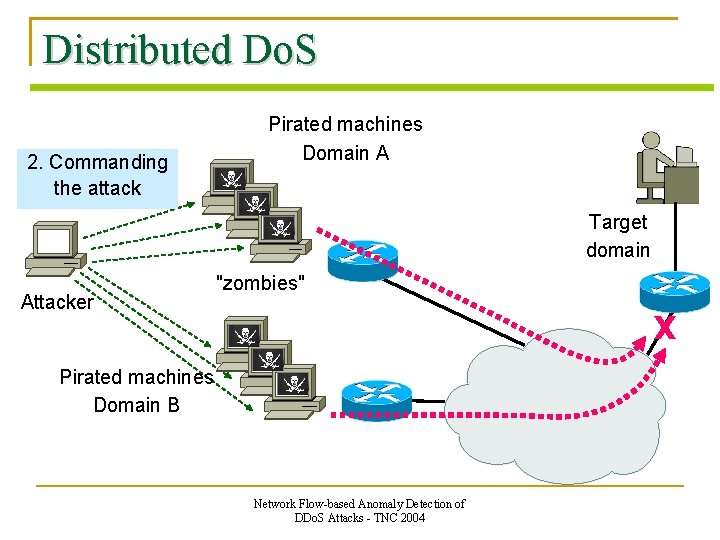
Distributed Do. S 2. Commanding 1. Taking the attack Control Pirated machines Domain A Target domain Attacker "zombies" X Pirated machines Domain B Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
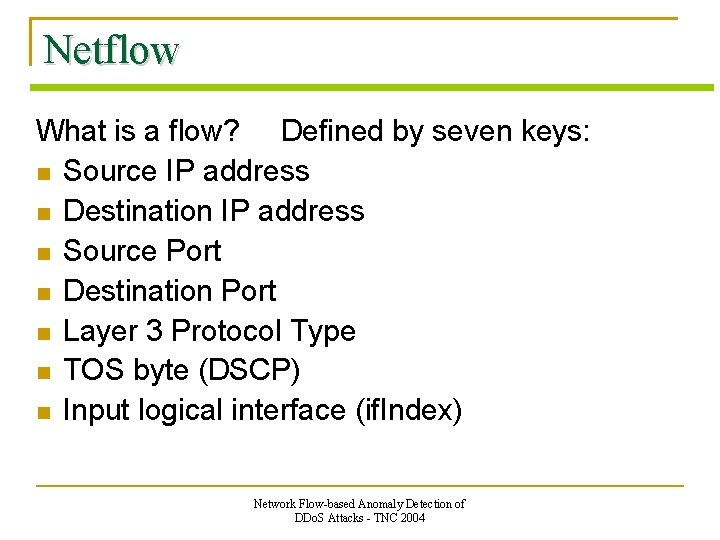
Netflow What is a flow? Defined by seven keys: Source IP address Destination IP address Source Port Destination Port Layer 3 Protocol Type TOS byte (DSCP) Input logical interface (if. Index) Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
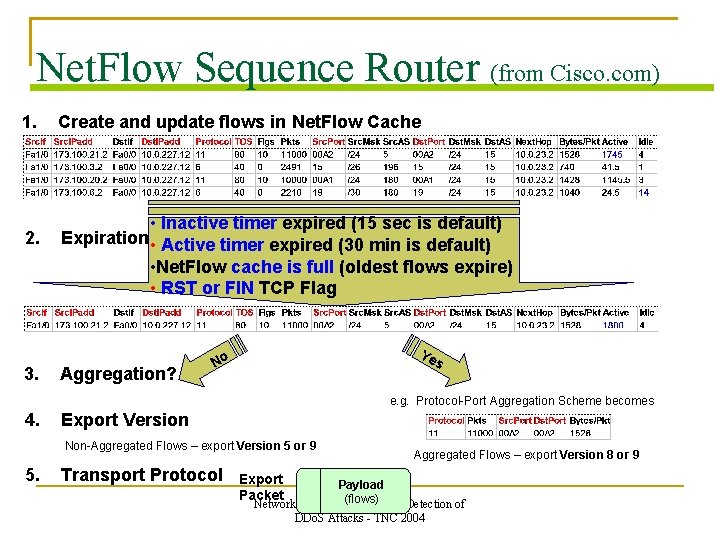
Net. Flow Sequence Router (from Cisco. com) 1. Create and update flows in Net. Flow Cache 2. • Inactive timer expired (15 sec is default) Expiration • Active timer expired (30 min is default) • Net. Flow cache is full (oldest flows expire) • RST or FIN TCP Flag 3. Aggregation? Ye No s e. g. Protocol-Port Aggregation Scheme becomes 4. Export Version Non-Aggregated Flows – export Version 5 or 9 5. Transport Protocol Aggregated Flows – export Version 8 or 9 Export Packet Payload (flows) Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Our Solution: An anomaly detection tool Open. Eye
Open. Eye DDo. S Attack Detection Tool Analyses flows that are exported from Cisco Netflow enabled routers Compatible with Netflow v 9 Works with IPv 4 and IPv 6 traffic Uses anomaly detection algorithm based on specific metrics and thresholds Written in Java language Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Implementation Two main modules: - Collector The Collector is responsible for receiving flow data from the Netflow enabled routers, information is analyzed and stored in a local data structure. - Detector The Detector is responsible for calculating the metrics and comparing the results to detection thresholds. It is periodically activated, implements extensive logging of detection events and generates e-mail notifications with security alerts to the administrator. Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
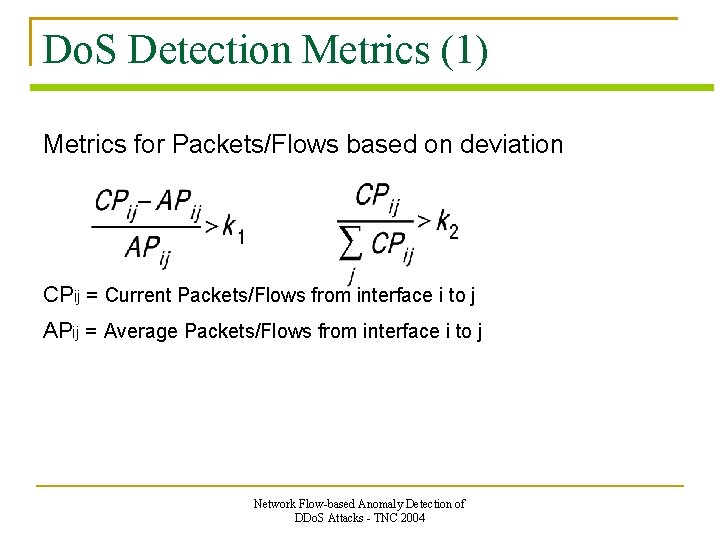
Do. S Detection Metrics (1) Metrics for Packets/Flows based on deviation CPij = Current Packets/Flows from interface i to j APij = Average Packets/Flows from interface i to j Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Do. S Detection Metrics (2) Number of flows with very small lifetime Number of flows with a very small number of packets Percentages of TCP/UDP traffic Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Data structures Tables for number of packets and number of flows for every pair of interfaces Hash Tables with the Dst IP (key) and the number of packets and flows (values) for each IP for every pair of interfaces Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
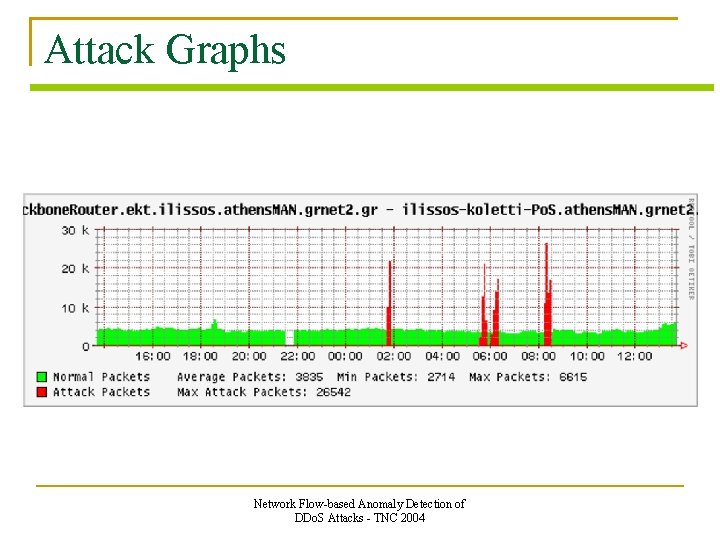
Attack Graphs Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Future Work More experiments Detection of worms Creation and testing of new metrics Usage of Open. Eye as a part of a Distributed Intrusion Detection System Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Acknowledgements Panoptis Gr. Net http: //www. grnet. gr Ntua NOC http: //panoptis. sourceforge. net/ http: //noc. ntua. gr Netmode http: //netmode. ntua. gr Network Flow-based Anomaly Detection of DDo. S Attacks - TNC 2004
Questions and Answers
- Slides: 19