Network Access Control Schemes Vulnerable to Covert Channels
Network Access Control Schemes Vulnerable to Covert Channels 11/03/2004 Florent Bersani & Anne-Sophie Duserre The present document contains information that remains the property of France Telecom. The recipient’s acceptance of this document implies his or her acknowledgement of the confidential nature of its contents and his or her obligation not to reproduce, transmit to a third party, disclose or use for commercial purposes any of its contents whatsoever without France Telecom’s prior written agreement. France Telecom Research & Development D 1 - 04/03/2021
Agenda s s s Context Q Network Access Control ? Q Covert channels ? Examples Q In mobile phone networks : DECT, GSM Q In IEEE 802. 11 WLANs Discussion Q Impact Q Solutions France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 2 - 04/03/2021
Agenda s s s Context Q Network Access Control ? Q Covert channels ? Examples Q In mobile phone networks : DECT, GSM Q In IEEE 802. 11 WLANs Discussion Q Impact Q Solutions France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 3 - 04/03/2021
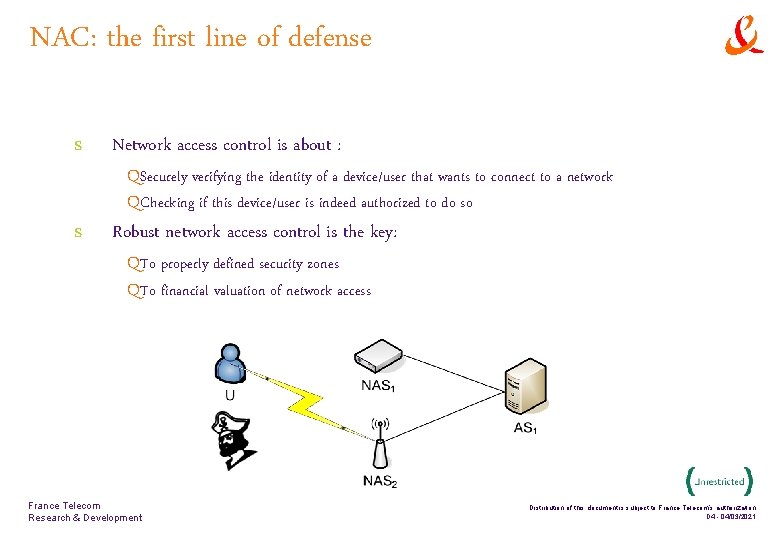
NAC: the first line of defense s s Network access control is about : QSecurely verifying the identity of a device/user that wants to connect to a network QChecking if this device/user is indeed authorized to do so Robust network access control is the key: QTo properly defined security zones QTo financial valuation of network access France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 4 - 04/03/2021
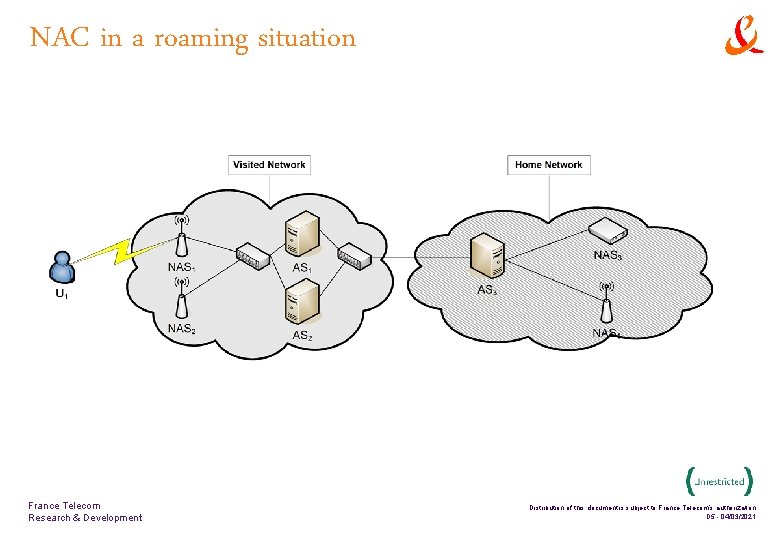
NAC in a roaming situation France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 5 - 04/03/2021
Covert channels: abusing protocols s s A communication channel is covert if it is neither designed nor intended to transfer information at all. [Lampson 73] For network protocols, a covert channel is rather a communication channel that is abused to unnoticeably transfer unexpected data. QThese channels provide venues to circumvent the policy France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 6 - 04/03/2021
Agenda s s s Context Q Network Access Control ? Q Covert channels ? Examples Q In mobile phone networks : DECT, GSM Q In IEEE 802. 11 WLANs Discussion Q Impact Q Solutions France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 7 - 04/03/2021
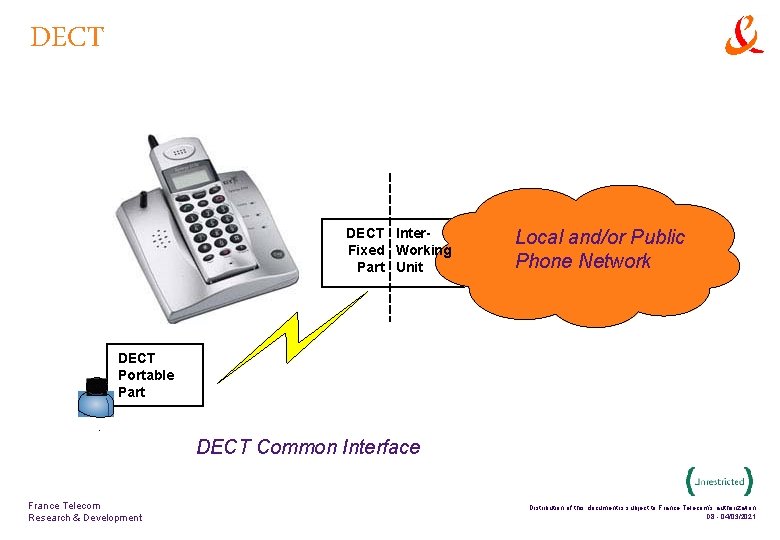
DECT Inter. Fixed Working Part Unit Local and/or Public Phone Network DECT Portable Part 1 DECT Common Interface France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 8 - 04/03/2021
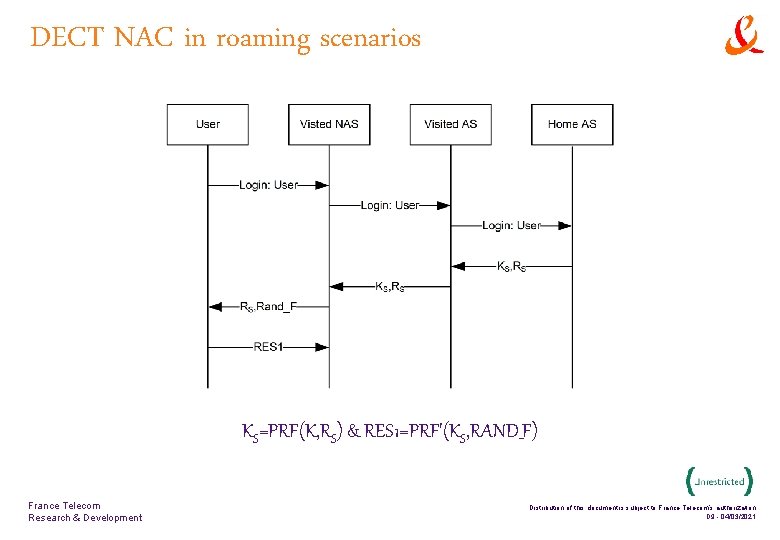
DECT NAC in roaming scenarios KS=PRF(K, RS) & RES 1=PRF'(KS, RAND_F) France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 9 - 04/03/2021
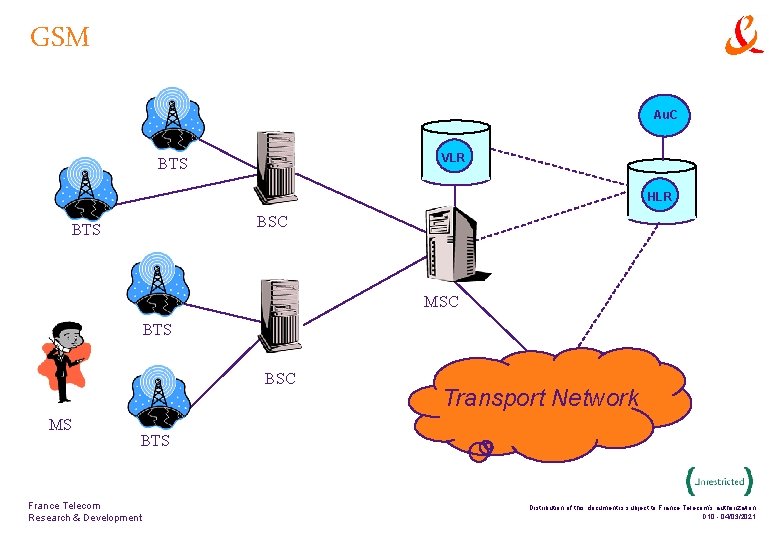
GSM Au. C VLR BTS HLR BSC BTS MSC BTS BSC MS Transport Network BTS France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 10 - 04/03/2021
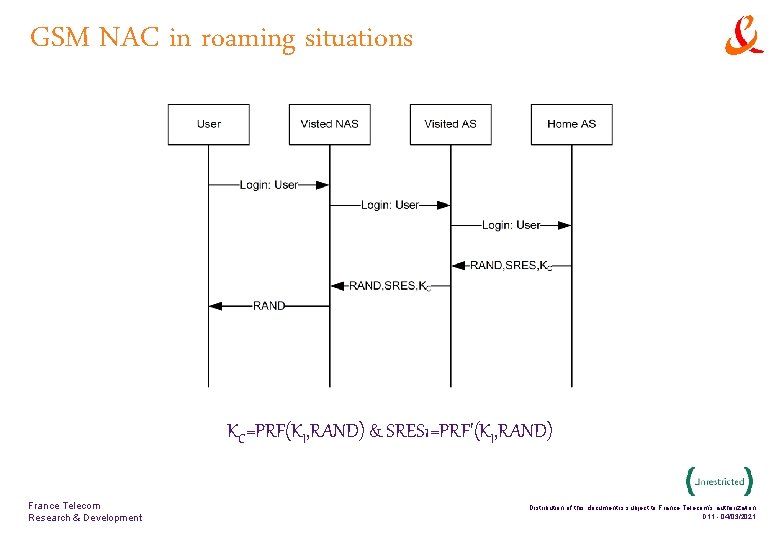
GSM NAC in roaming situations KC=PRF(KI, RAND) & SRES 1=PRF'(KI, RAND) France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 11 - 04/03/2021
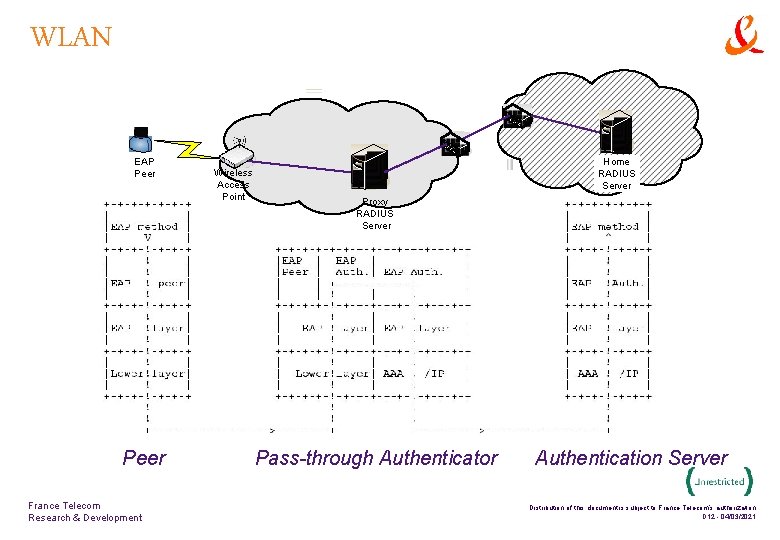
WLAN EAP Peer 1 Peer France Telecom Research & Development Wireless Access Point 2 Home RADIUS Server Proxy RADIUS Server Pass-through Authenticator Authentication Server Distribution of this document is subject to France Telecom’s authorization D 12 - 04/03/2021
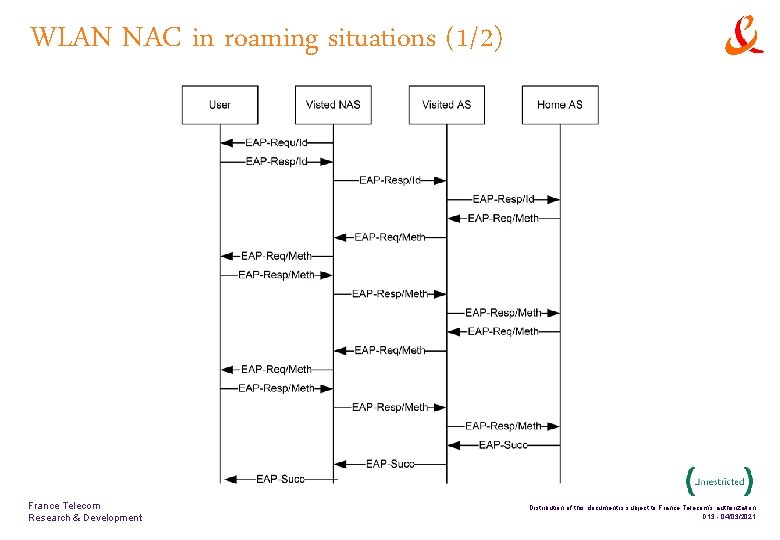
WLAN NAC in roaming situations (1/2) France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 13 - 04/03/2021
![WLAN NAC in roaming situations (2/2) s s EAP [RFC 3748] may transport EAP WLAN NAC in roaming situations (2/2) s s EAP [RFC 3748] may transport EAP](http://slidetodoc.com/presentation_image_h/234bd8705ace1bb6145b175fa06c0d09/image-14.jpg)
WLAN NAC in roaming situations (2/2) s s EAP [RFC 3748] may transport EAP methods that are opaque to the Visited AS, e. g. PEAP or EAP-PSK A rogue Home AS may use this communication channel that it is granted with its user for other purposes than authentication! France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 14 - 04/03/2021
Agenda s s s Context Q Network Access Control ? Q Covert channels ? Examples Q In mobile phone networks : DECT, GSM Q In IEEE 802. 11 WLANs Discussion Q Impact Q Solutions France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 15 - 04/03/2021
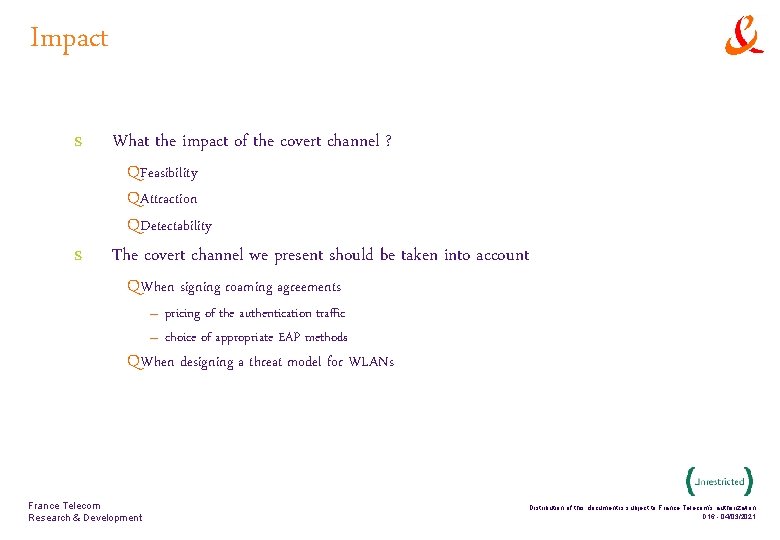
Impact s s What the impact of the covert channel ? QFeasibility QAttraction QDetectability The covert channel we present should be taken into account QWhen signing roaming agreements – pricing of the authentication traffic – choice of appropriate EAP methods QWhen designing a threat model for WLANs France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 16 - 04/03/2021
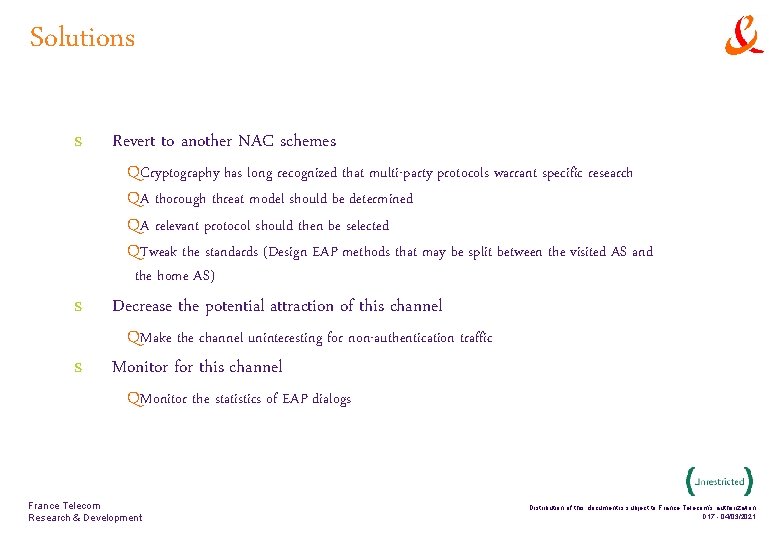
Solutions s Revert to another NAC schemes QCryptography has long recognized that multi-party protocols warrant specific research QA thorough threat model should be determined QA relevant protocol should then be selected QTweak the standards (Design EAP methods that may be split between the visited AS and the home AS) Decrease the potential attraction of this channel QMake the channel uninteresting for non-authentication traffic Monitor for this channel QMonitor the statistics of EAP dialogs France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 17 - 04/03/2021
Questions & Comments France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 18 - 04/03/2021
Questions & Comments florent. bersani@francetelecom. com France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 19 - 04/03/2021
![References s s [Lampson 73] B. W. Lampson, "A Note on the Confinement Problem, References s s [Lampson 73] B. W. Lampson, "A Note on the Confinement Problem,](http://slidetodoc.com/presentation_image_h/234bd8705ace1bb6145b175fa06c0d09/image-20.jpg)
References s s [Lampson 73] B. W. Lampson, "A Note on the Confinement Problem, " Communications of the ACM, 16: 10, pp. 613 -615, October 1973. [RFC 3748] B. Aboba, L. Blunk, J. Vollbrecht, J. Carlson, and H. Levkowetz, Extensible Authentication Protocol (EAP), June 2004, RFC 3748 France Telecom Research & Development Distribution of this document is subject to France Telecom’s authorization D 20 - 04/03/2021
- Slides: 20