NETW 703 Dr Eng Amr T AbdelHamid Protocol
NETW 703 Dr. Eng. Amr T. Abdel-Hamid Protocol Engineering Formal Verification: Modeling Lectures are based on slides by: • K. Havelund & Agroce, Reliable Software: Testing and Monitoring, CMU. • E. Clarke, Formal Methods, to be updated by course name • S. Tahar, E. Cerny and X. Song, “ Formal Verification of Systems”. Spring 2020
Testing “for” Coverage Protocol Engineering Ø Never seek to improve coverage just for the sake of increasing coverage Ø Coverage is not the goal ØFinding failures that expose faults is the goal ØNo amount of coverage will prove that the program cannot fail Dr. Amr Talaat “Program testing can be used to show the presence of bugs, but never to show their absence!” – E. Dijkstra, Notes On Structured Programming
Testing (Simulation) Drawbacks Protocol Engineering Ø Bottom line: Not feasible to simulate all input sequences to completely verify a design. Ø Example 1: Suppose you want to test a 64 -bit floating-point division routine. There are 2128 combinations. At 1 test/ms, it will take 1025 years Ø Example 2: How long does it take to exhaustively simulate a 256 bit RAM? 2256=1080 combinations of initial states and inputs Ø Assume Ø Use all the matter in our galaxy (1017 kg) to build computers Ø Each computer is of the size of single electron (10 -30 kg) Ø Each computer simulates 1012 per second Dr. Amr Talaat Ø 1010 years will reach 0. 05% of test cases!
Formal Verification: Alternative to Testing Protocol Engineering Ø Formal Verification is the process of constructing a proof that a target system will behave in accordance with its specification. Ø Use of mathematical reasoning to prove that an implementation satisfies a specification Ø Like a mathematical proof: correctness of a formally verified hardware design holds regardless of input values. Ø Consideration of all cases is implicit in formal verification. Ø Must establish: Dr. Amr Talaat Ø A formal specification (properties or high-level behavior). Ø A formal description of the implementation (design at higher level of abstraction —model (observationally) equivalent to implementation or implied by implementation).
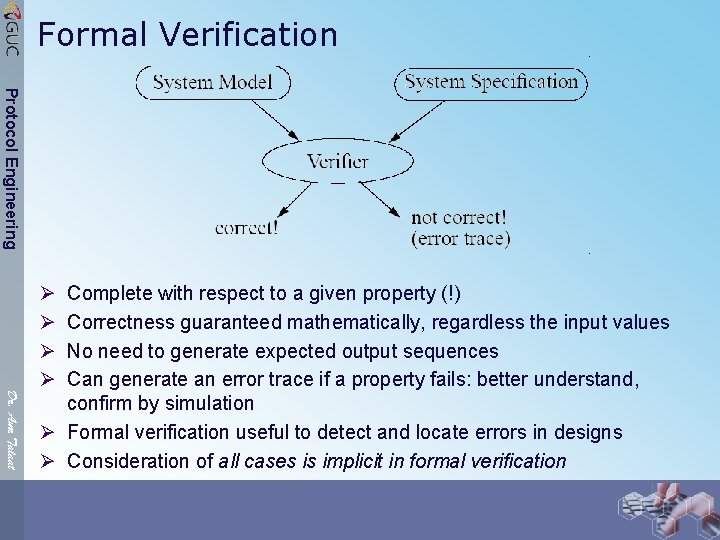
Formal Verification Protocol Engineering Ø Ø Dr. Amr Talaat Complete with respect to a given property (!) Correctness guaranteed mathematically, regardless the input values No need to generate expected output sequences Can generate an error trace if a property fails: better understand, confirm by simulation Ø Formal verification useful to detect and locate errors in designs Ø Consideration of all cases is implicit in formal verification
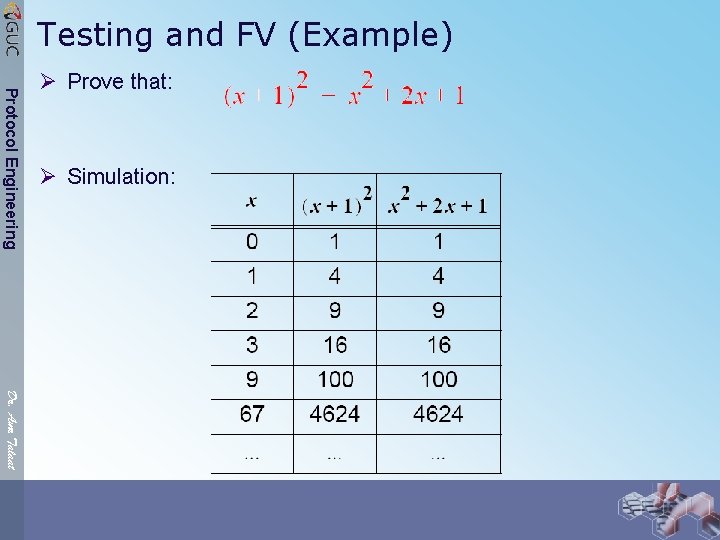
Testing and FV (Example) Protocol Engineering Ø Prove that: Ø Simulation: Dr. Amr Talaat
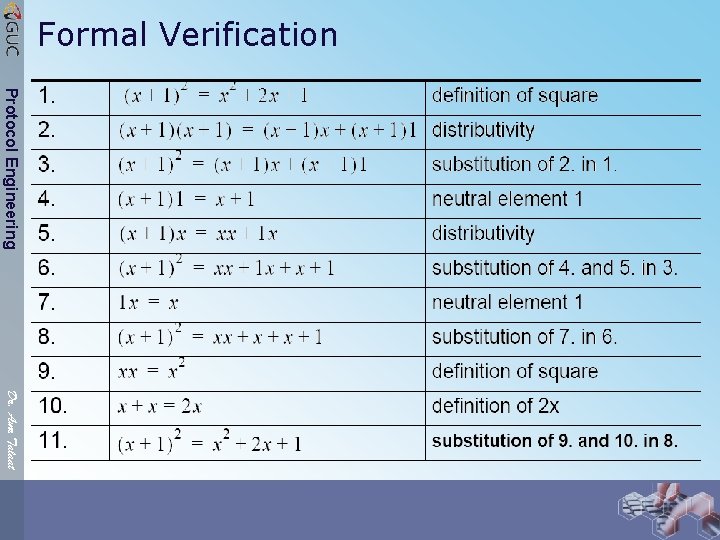
Formal Verification Protocol Engineering Dr. Amr Talaat
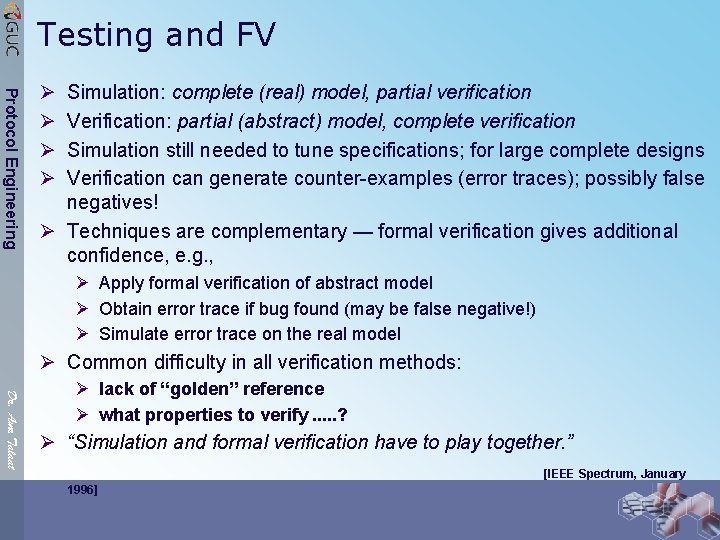
Testing and FV Protocol Engineering Ø Ø Simulation: complete (real) model, partial verification Verification: partial (abstract) model, complete verification Simulation still needed to tune specifications; for large complete designs Verification can generate counter-examples (error traces); possibly false negatives! Ø Techniques are complementary — formal verification gives additional confidence, e. g. , Ø Apply formal verification of abstract model Ø Obtain error trace if bug found (may be false negative!) Ø Simulate error trace on the real model Ø Common difficulty in all verification methods: Dr. Amr Talaat Ø lack of “golden” reference Ø what properties to verify. . . ? Ø “Simulation and formal verification have to play together. ” [IEEE Spectrum, January 1996]
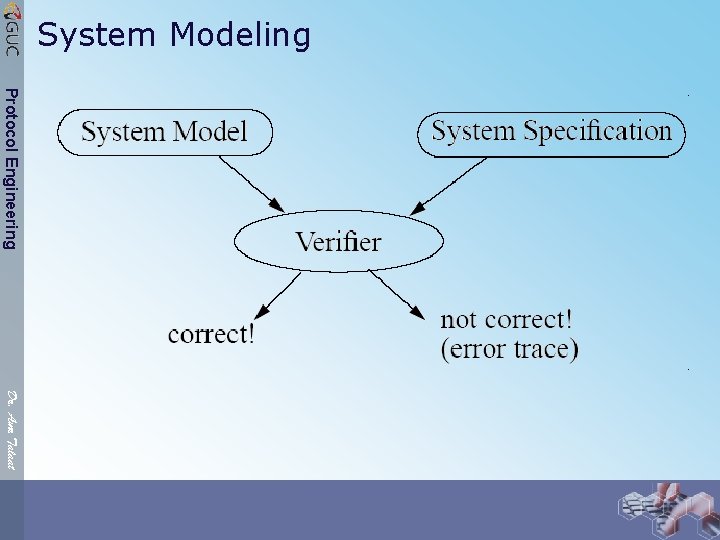
System Modeling Protocol Engineering Dr. Amr Talaat
Formal Logic Protocol Engineering Ø What Does “Formal” mean? Ø Webster’s dictionary gives the following as one of the definitions of “formal”: “related to, concerned with, or constituting the outward form of something as distinguished from its content” Ø A method is formal if its rules for manipulation are based on form (syntax) and not on content (semantics) Ø Majority of existing formal techniques are based on some flavor of formal (symbolic) logic: Propositional logic, Predicate logic, other logics. Dr. Amr Talaat Ø Formal logic Ø Every logic comprises a formal language for making statements about objects and reasoning about properties of these objects. Ø Statements in a logic language are constructed according to a predefined set of formation rules (depending on the language) called syntax rules. Ø A logic language can be used in different ways.
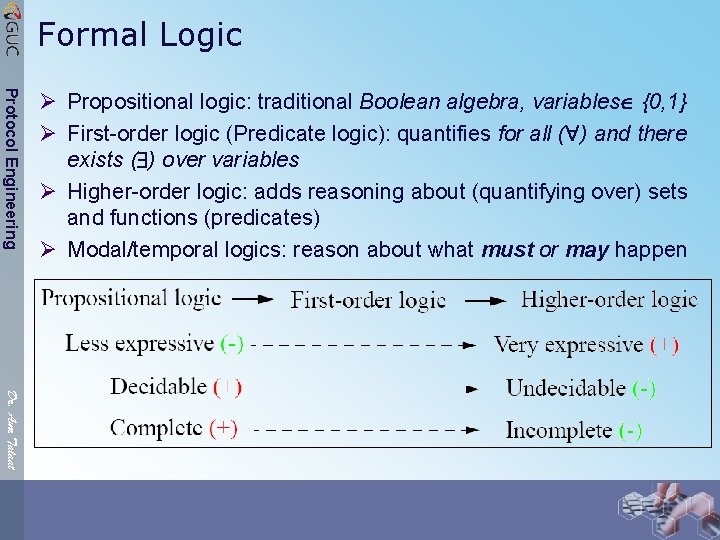
Formal Logic Protocol Engineering Ø Propositional logic: traditional Boolean algebra, variables {0, 1} Ø First-order logic (Predicate logic): quantifies for all ( ) and there exists ( ) over variables Ø Higher-order logic: adds reasoning about (quantifying over) sets and functions (predicates) Ø Modal/temporal logics: reason about what must or may happen Dr. Amr Talaat
Formal Logic: Proof Theory Protocol Engineering Ø A formal logic system consists of: Ø a notation (syntax) Ø a set of axioms (facts) Ø a set of inference (deduction) rules Ø A formal proof is a sequence of statements where every statement follows from a preceding one by a rule of inference Ø Purely syntactic (mechanical) activity; not concerned with the meaning of statements, but with the arrangement of these statements, and whether proofs can be constructed Dr. Amr Talaat
Model Theory Protocol Engineering Ø The second use of a logic language is for expressing statements that receive a meaning when given an interpretation Ø The language of logic is used here to formalize properties of structures, to determine when a statement is true on a structure Ø This use of a logic language is called model theory Forces a precise and rigorous definition of the concept of truth on a structure Dr. Amr Talaat
Formal Logic Protocol Engineering Ø Logic = Syntax + Semantics Ø Syntax and semantics of logic are not independent Ø A logic language has a syntax, and the meaning of statements by an interpretation on a structure Ø The interaction between model theory and proof theory makes logic an interesting and effective tool Dr. Amr Talaat
Proof System Protocol Engineering Ø Given a logic (syntax and semantics), there can be one or more proof systems, e. g. HOL and PVS are two proof systems based on higher-order logic. Ø Issues of proof systems Ø Consistency (Soundness): all provable formulas (theorems) are logically (semantically) true Ø Completeness: all valid formulas (semantically true) are provable (theorems) Ø Decidability: there is an algorithm for deciding the (semantical) truth of any formula )theorems) Dr. Amr Talaat A proof system is acceptable only if it is consistent (may not be complete nor decidable)
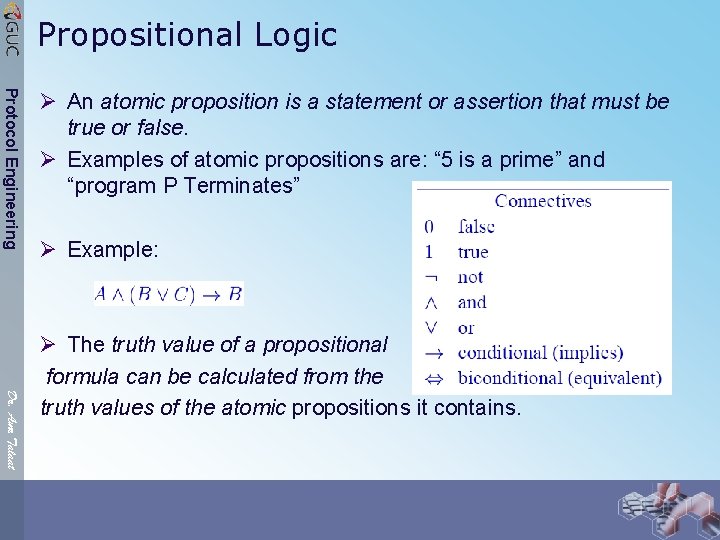
Propositional Logic Protocol Engineering Ø An atomic proposition is a statement or assertion that must be true or false. Ø Examples of atomic propositions are: “ 5 is a prime” and “program P Terminates” Ø Example: Dr. Amr Talaat Ø The truth value of a propositional formula can be calculated from the truth values of the atomic propositions it contains.
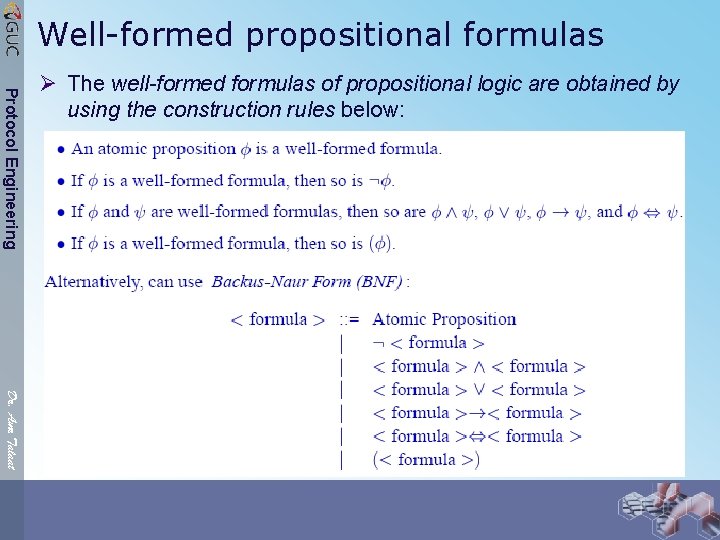
Well-formed propositional formulas Protocol Engineering Ø The well-formed formulas of propositional logic are obtained by using the construction rules below: Dr. Amr Talaat
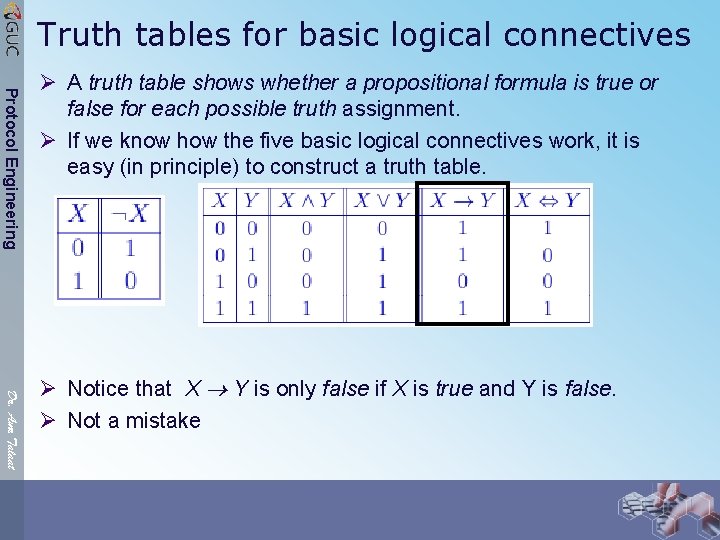
Truth tables for basic logical connectives Protocol Engineering Ø A truth table shows whether a propositional formula is true or false for each possible truth assignment. Ø If we know how the five basic logical connectives work, it is easy (in principle) to construct a truth table. Dr. Amr Talaat Ø Notice that X Y is only false if X is true and Y is false. Ø Not a mistake
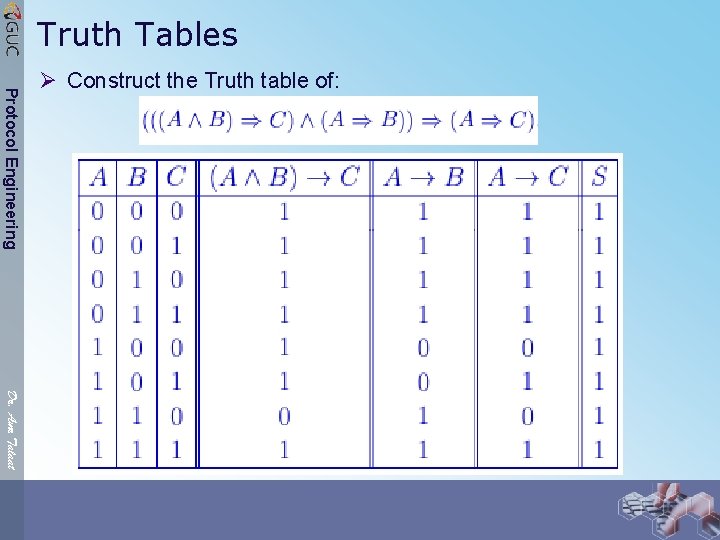
Truth Tables Protocol Engineering Ø Construct the Truth table of: Dr. Amr Talaat
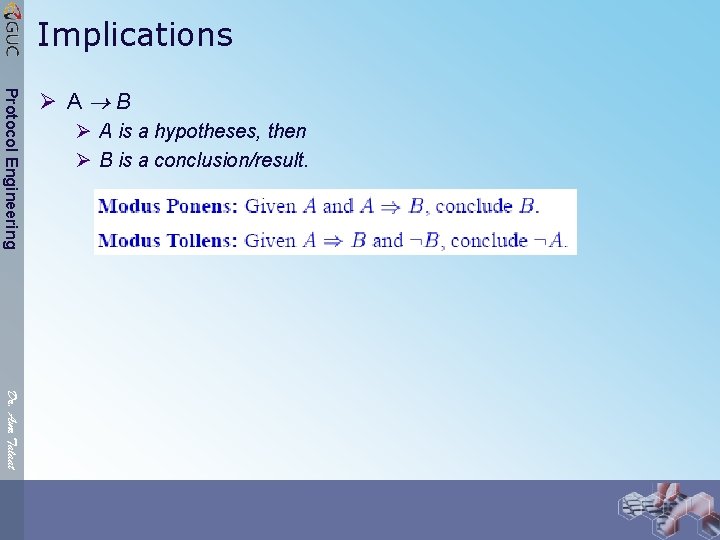
Implications Protocol Engineering Ø A B Ø A is a hypotheses, then Ø B is a conclusion/result. Dr. Amr Talaat
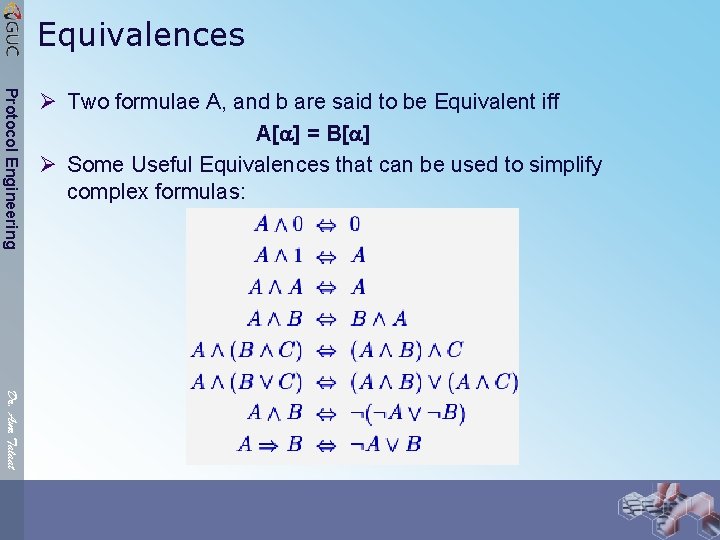
Equivalences Protocol Engineering Ø Two formulae A, and b are said to be Equivalent iff A[ ] = B[ ] Ø Some Useful Equivalences that can be used to simplify complex formulas: Dr. Amr Talaat
Valid and Invalid Arguments Protocol Engineering Ø Which of the following arguments are valid? Ø If I am wealthy, then I am happy. Therefore, I am wealthy. Ø If John drinks beer, he is at least 18 years old. John does not drink beer. Therefore, John is not yet 18 years old. Ø If I study, then I will not fail basket weaving 101. If I do not play cards to often, then I will study. I failed basket weaving 101. Therefore, I played cards too often. Dr. Amr Talaat
Protocol Engineering Dr. Amr Talaat
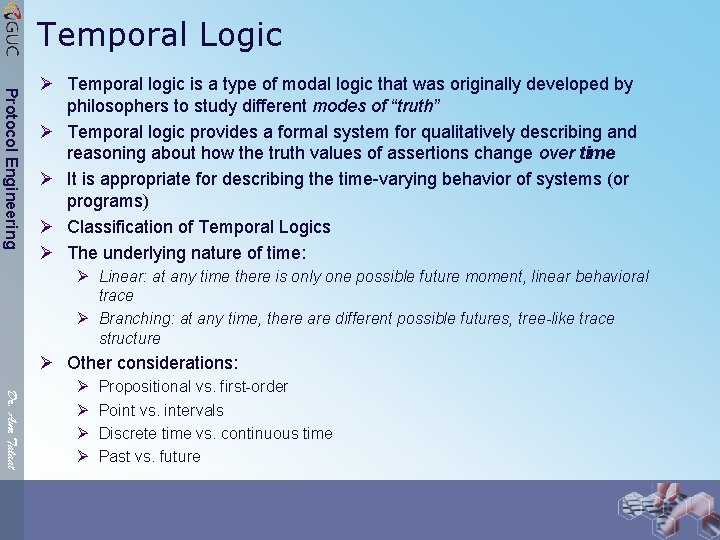
Temporal Logic Protocol Engineering Ø Temporal logic is a type of modal logic that was originally developed by philosophers to study different modes of “truth” Ø Temporal logic provides a formal system for qualitatively describing and reasoning about how the truth values of assertions change over time Ø It is appropriate for describing the time-varying behavior of systems (or programs) Ø Classification of Temporal Logics Ø The underlying nature of time: Ø Linear: at any time there is only one possible future moment, linear behavioral trace Ø Branching: at any time, there are different possible futures, tree-like trace structure Ø Other considerations: Dr. Amr Talaat Ø Ø Propositional vs. first-order Point vs. intervals Discrete time vs. continuous time Past vs. future
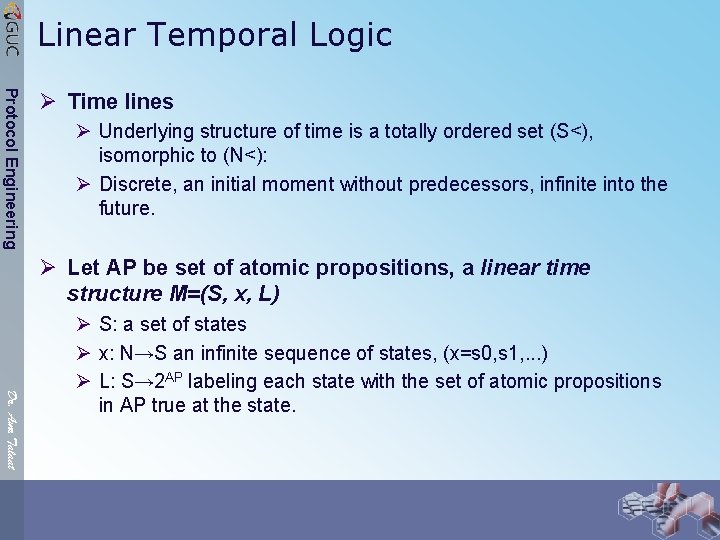
Linear Temporal Logic Protocol Engineering Ø Time lines Ø Underlying structure of time is a totally ordered set (S<), isomorphic to (N<): Ø Discrete, an initial moment without predecessors, infinite into the future. Ø Let AP be set of atomic propositions, a linear time structure M=(S, x, L) Dr. Amr Talaat Ø S: a set of states Ø x: N→S an infinite sequence of states, (x=s 0, s 1, . . . ) Ø L: S→ 2 AP labeling each state with the set of atomic propositions in AP true at the state.
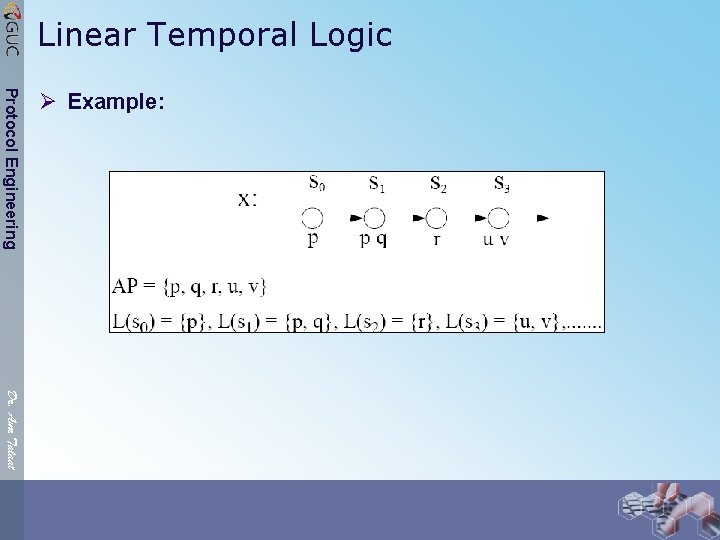
Linear Temporal Logic Protocol Engineering Ø Example: Dr. Amr Talaat
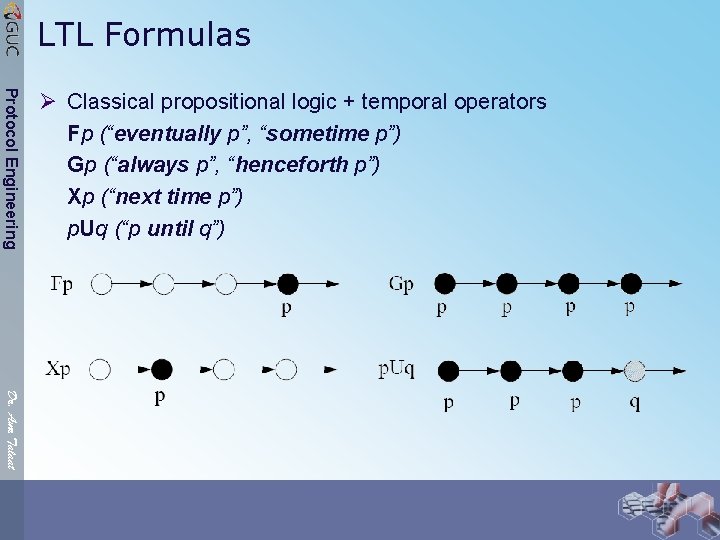
LTL Formulas Protocol Engineering Ø Classical propositional logic + temporal operators Fp (“eventually p”, “sometime p”) Gp (“always p”, “henceforth p”) Xp (“next time p”) p. Uq (“p until q”) Dr. Amr Talaat
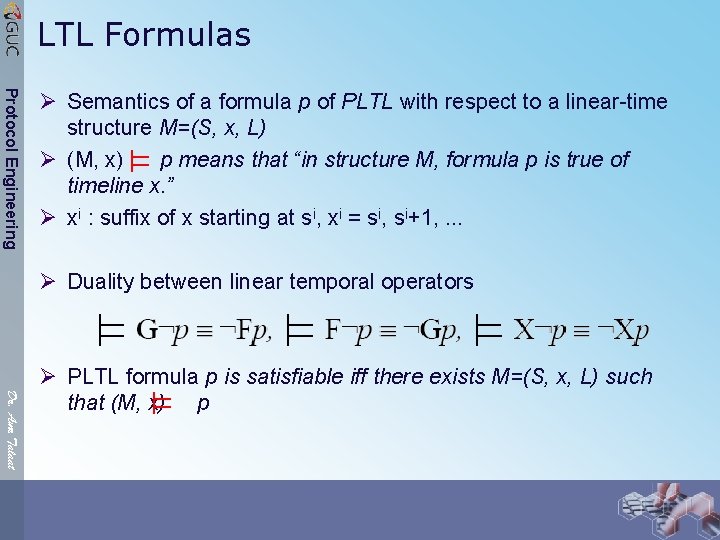
LTL Formulas Protocol Engineering Ø Semantics of a formula p of PLTL with respect to a linear-time structure M=(S, x, L) Ø (M, x) p means that “in structure M, formula p is true of timeline x. ” Ø xi : suffix of x starting at si, xi = si, si+1, . . . Ø Duality between linear temporal operators Dr. Amr Talaat Ø PLTL formula p is satisfiable iff there exists M=(S, x, L) such that (M, x) p
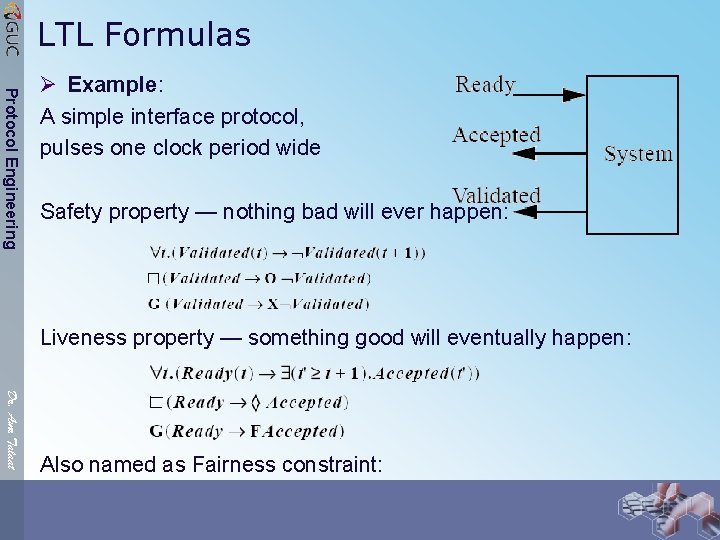
LTL Formulas Protocol Engineering Ø Example: A simple interface protocol, pulses one clock period wide Safety property — nothing bad will ever happen: Liveness property — something good will eventually happen: Dr. Amr Talaat Also named as Fairness constraint:
Branching Time Temporal Logic (BTTL) Protocol Engineering Dr. Amr Talaat Ø Structure of time: an infinite tree, each instant may have many successor instants Ø Along each path in the tree, the corresponding timeline is isomorphic to N Ø State quantifiers: Xp, Fp, Gp, p. Uq (like in linear temporal logic) Ø Path quantifiers: for All paths (A) and there Exists a path (E) from a given state A=∀E=∃ Ø In linear time logic, temporal operators are provided for describing events along a single future, however, when a linear formula is used for specification, there is usually an implicit universal quantification over all possible futures (linear traces) Ø In contrast, in branching time logic the operators usually reflect the branching nature of time by allowing explicit quantification over possible futures in any state
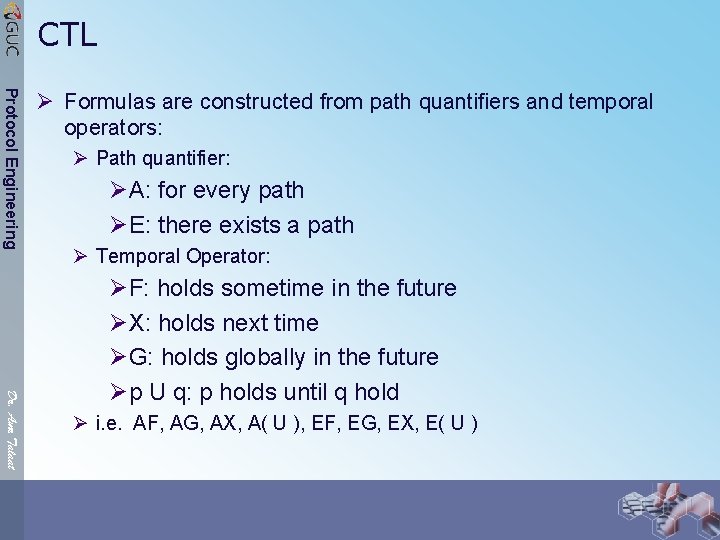
CTL Protocol Engineering Ø Formulas are constructed from path quantifiers and temporal operators: Ø Path quantifier: ØA: for every path ØE: there exists a path Ø Temporal Operator: Dr. Amr Talaat ØF: holds sometime in the future ØX: holds next time ØG: holds globally in the future Øp U q: p holds until q hold Ø i. e. AF, AG, AX, A( U ), EF, EG, EX, E( U )
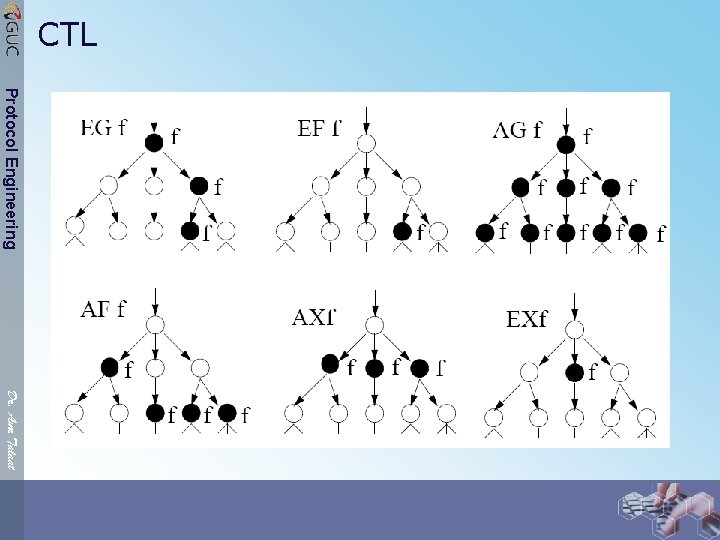
CTL Protocol Engineering Dr. Amr Talaat
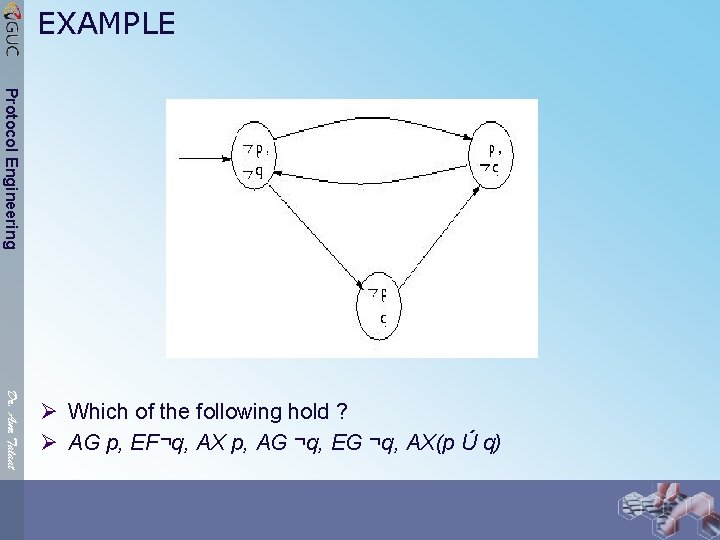
EXAMPLE Protocol Engineering Dr. Amr Talaat Ø Which of the following hold ? Ø AG p, EF¬q, AX p, AG ¬q, EG ¬q, AX(p Ú q)
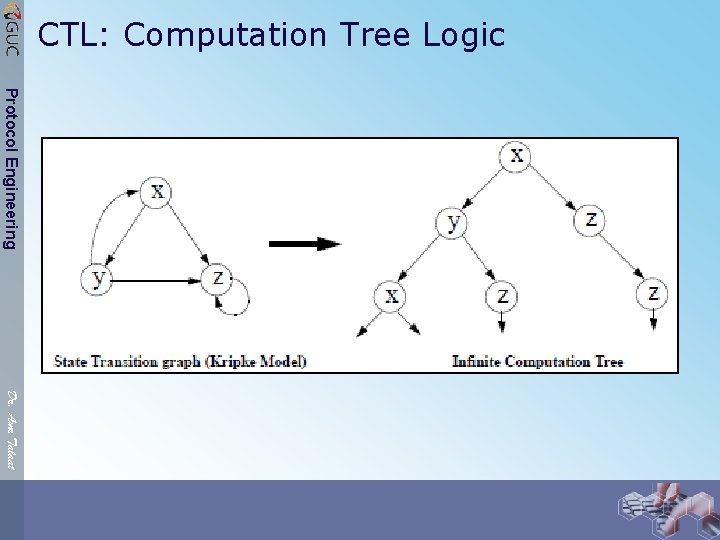
CTL: Computation Tree Logic Protocol Engineering Dr. Amr Talaat
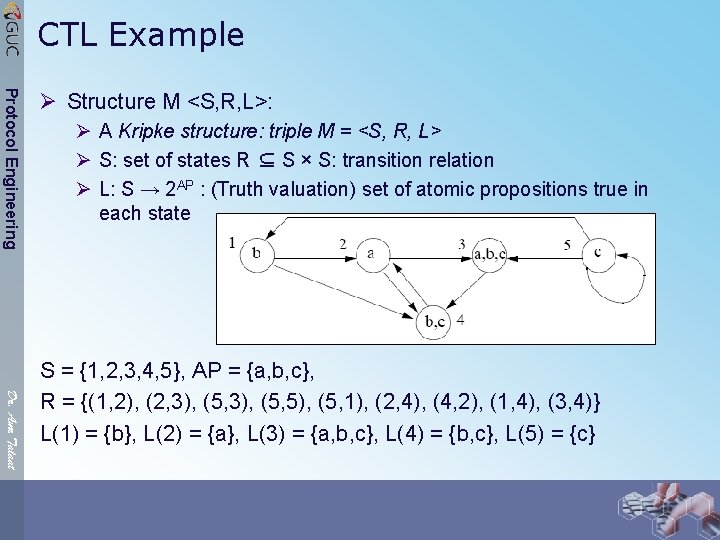
CTL Example Protocol Engineering Ø Structure M <S, R, L>: Ø A Kripke structure: triple M = <S, R, L> Ø S: set of states R ⊆ S × S: transition relation Ø L: S → 2 AP : (Truth valuation) set of atomic propositions true in each state Dr. Amr Talaat S = {1, 2, 3, 4, 5}, AP = {a, b, c}, R = {(1, 2), (2, 3), (5, 5), (5, 1), (2, 4), (4, 2), (1, 4), (3, 4)} L(1) = {b}, L(2) = {a}, L(3) = {a, b, c}, L(4) = {b, c}, L(5) = {c}
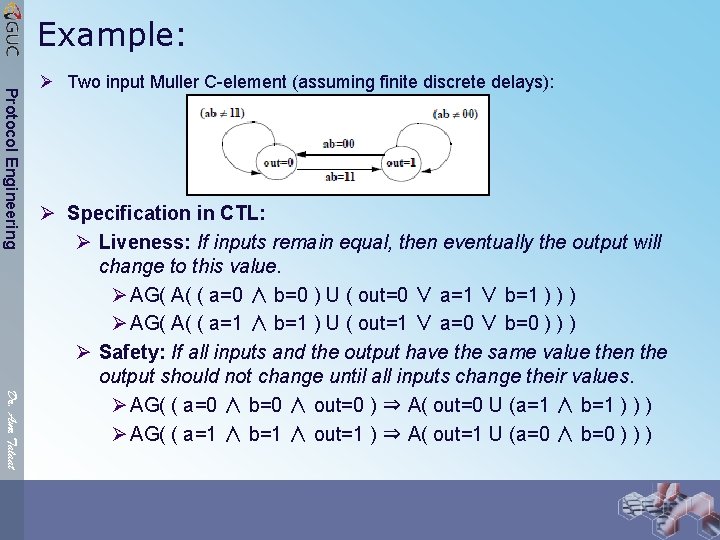
Example: Protocol Engineering Ø Two input Muller C-element (assuming finite discrete delays): Dr. Amr Talaat Ø Specification in CTL: Ø Liveness: If inputs remain equal, then eventually the output will change to this value. Ø AG( A( ( a=0 ∧ b=0 ) U ( out=0 ∨ a=1 ∨ b=1 ) ) ) Ø AG( A( ( a=1 ∧ b=1 ) U ( out=1 ∨ a=0 ∨ b=0 ) ) ) Ø Safety: If all inputs and the output have the same value then the output should not change until all inputs change their values. Ø AG( ( a=0 ∧ b=0 ∧ out=0 ) ⇒ A( out=0 U (a=1 ∧ b=1 ) ) ) Ø AG( ( a=1 ∧ b=1 ∧ out=1 ) ⇒ A( out=1 U (a=0 ∧ b=0 ) ) )
Model Checking Problem Protocol Engineering Ø Given an FSM M (equivalent Kripke structure) and a temporal logic formula p, does M define a model of p? Ø Determine the truth of a formula with respect to a given (initial) state in M Ø Find all states s of M such that (M, s) p Ø For any propositional temporal logic, the model checking problem is decidable: exhaustive search of all paths through the finite input structure Dr. Amr Talaat
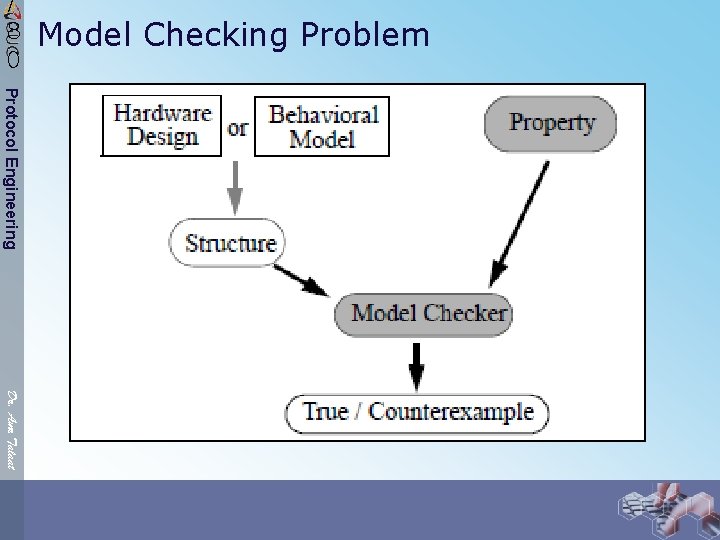
Model Checking Problem / 8 0 Protocol Engineering Dr. Amr Talaat
![/ 8 0 Theoretical Background Protocol Engineering Dr. Amr Talaat Ø Theorem [Wolper, 1986]: / 8 0 Theoretical Background Protocol Engineering Dr. Amr Talaat Ø Theorem [Wolper, 1986]:](http://slidetodoc.com/presentation_image_h2/736632f3e95dcffc3e2080e4e872bc19/image-39.jpg)
/ 8 0 Theoretical Background Protocol Engineering Dr. Amr Talaat Ø Theorem [Wolper, 1986]: The model checking for CTL is in deterministic polynomial time Ø Theorem [Sistla & Clark, 1985]: The model checking problem for PLTL is PSPACE complete Ø Theorem [Emerson & Lei, 1987]: Given any modelchecking algorithm for a linear logic LTL, there is a model checking algorithm for the corresponding branching logic BTL, whose basic modalities are defined by the LTL, of the same order of complexity Ø • Theorem [Clark, Emerson & Sistla, 1986]: The model checking problem for CTL* is PSPACE-complete
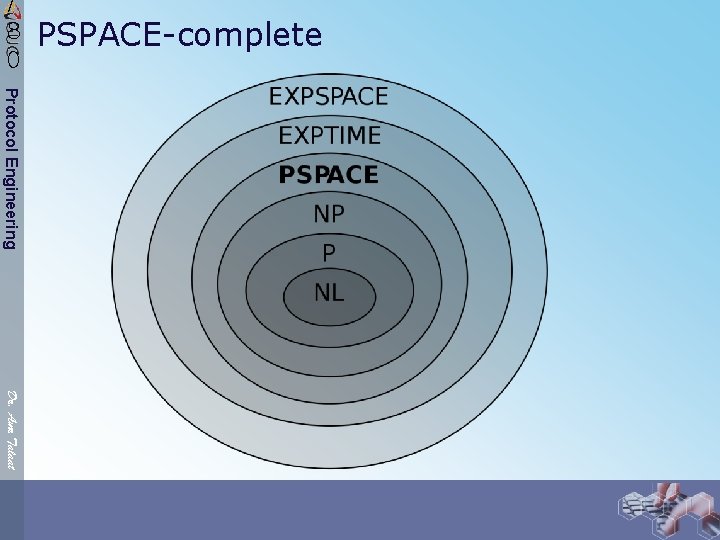
PSPACE-complete / 8 0 Protocol Engineering Dr. Amr Talaat
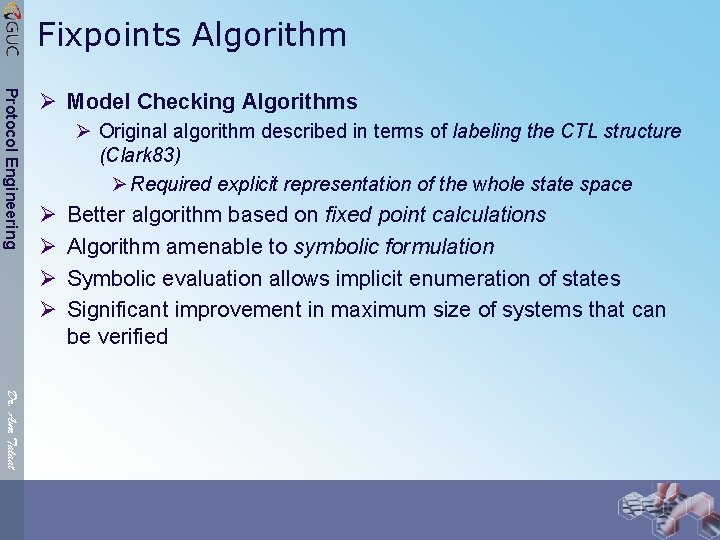
Fixpoints Algorithm Protocol Engineering Ø Model Checking Algorithms Ø Original algorithm described in terms of labeling the CTL structure (Clark 83) Ø Required explicit representation of the whole state space Ø Ø Better algorithm based on fixed point calculations Algorithm amenable to symbolic formulation Symbolic evaluation allows implicit enumeration of states Significant improvement in maximum size of systems that can be verified Dr. Amr Talaat
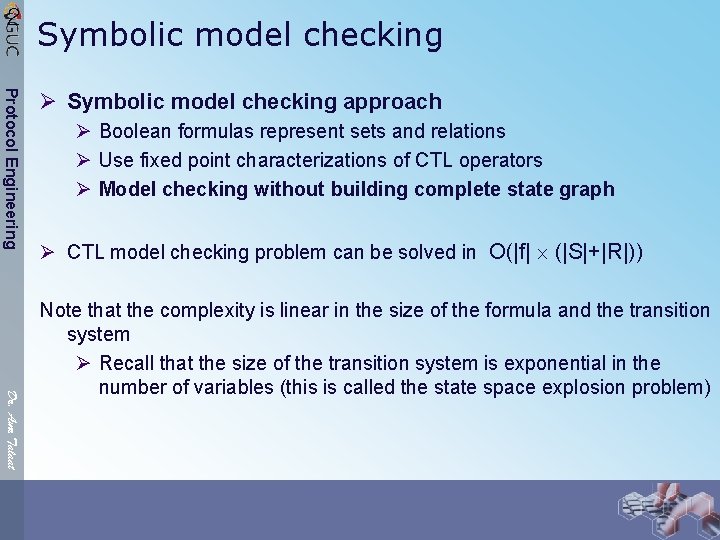
2 Symbolic model checking Protocol Engineering Ø Symbolic model checking approach Ø Boolean formulas represent sets and relations Ø Use fixed point characterizations of CTL operators Ø Model checking without building complete state graph Ø CTL model checking problem can be solved in O(|f| (|S|+|R|)) Dr. Amr Talaat Note that the complexity is linear in the size of the formula and the transition system Ø Recall that the size of the transition system is exponential in the number of variables (this is called the state space explosion problem)
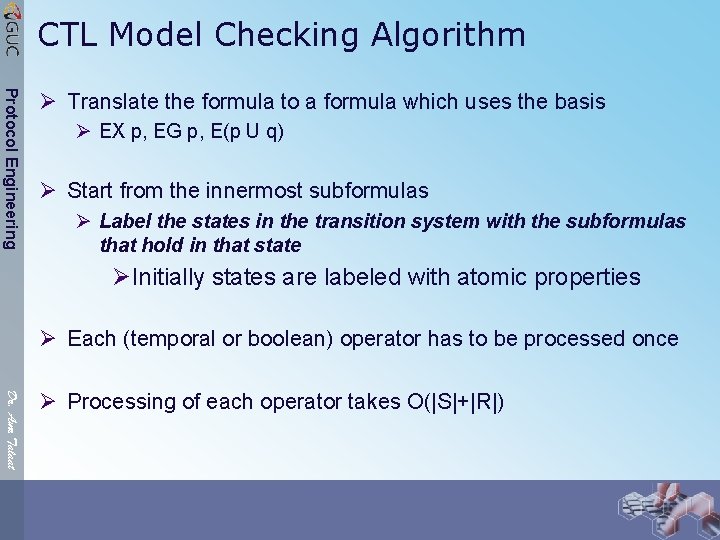
CTL Model Checking Algorithm Protocol Engineering Ø Translate the formula to a formula which uses the basis Ø EX p, EG p, E(p U q) Ø Start from the innermost subformulas Ø Label the states in the transition system with the subformulas that hold in that state ØInitially states are labeled with atomic properties Ø Each (temporal or boolean) operator has to be processed once Dr. Amr Talaat Ø Processing of each operator takes O(|S|+|R|)
CTL Model Checking Algorithm Protocol Engineering Ø Boolean operators are easy Ø p : Each state which is not labeled with p should be labeled with p Ø p q : Each state which is labeled with both p and q should be labeled with p q Ø p q : Each state which is labeled with p or q should be labeled with p q Dr. Amr Talaat
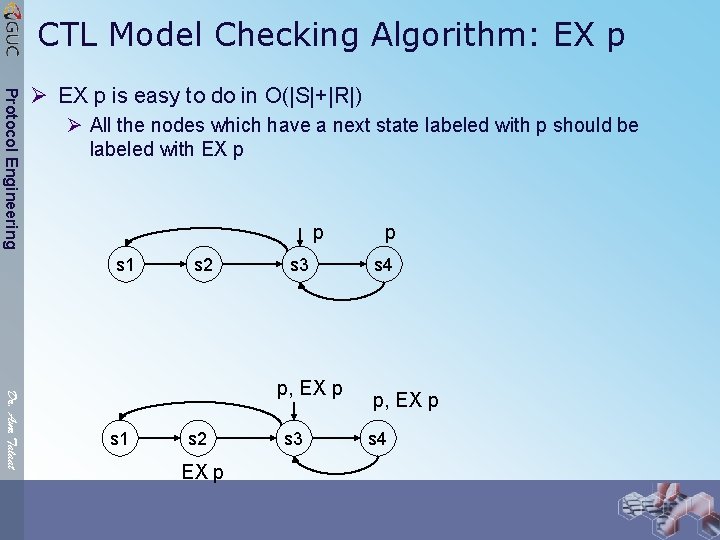
CTL Model Checking Algorithm: EX p Protocol Engineering Ø EX p is easy to do in O(|S|+|R|) Ø All the nodes which have a next state labeled with p should be labeled with EX p p s 1 s 2 s 3 Dr. Amr Talaat p, EX p s 1 s 2 EX p s 3 p s 4 p, EX p s 4
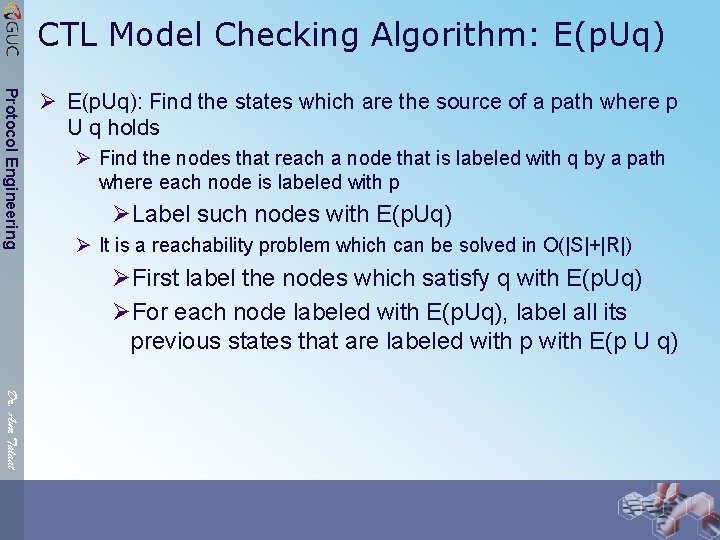
CTL Model Checking Algorithm: E(p. Uq) Protocol Engineering Ø E(p. Uq): Find the states which are the source of a path where p U q holds Ø Find the nodes that reach a node that is labeled with q by a path where each node is labeled with p ØLabel such nodes with E(p. Uq) Ø It is a reachability problem which can be solved in O(|S|+|R|) ØFirst label the nodes which satisfy q with E(p. Uq) ØFor each node labeled with E(p. Uq), label all its previous states that are labeled with p with E(p U q) Dr. Amr Talaat
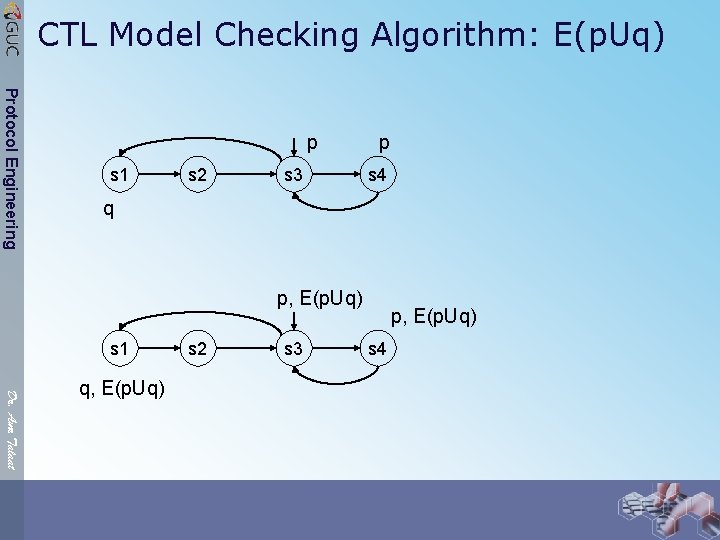
CTL Model Checking Algorithm: E(p. Uq) Protocol Engineering p s 1 s 2 s 3 p s 4 q p, E(p. Uq) s 1 Dr. Amr Talaat q, E(p. Uq) s 2 s 3 p, E(p. Uq) s 4
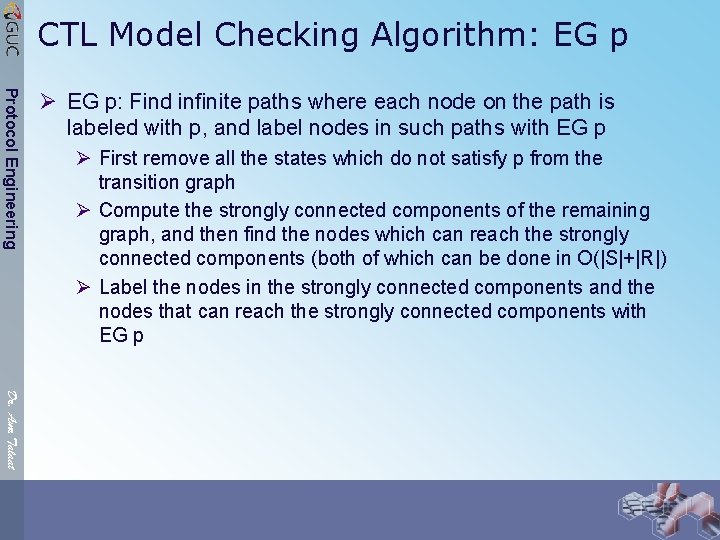
CTL Model Checking Algorithm: EG p Protocol Engineering Ø EG p: Find infinite paths where each node on the path is labeled with p, and label nodes in such paths with EG p Ø First remove all the states which do not satisfy p from the transition graph Ø Compute the strongly connected components of the remaining graph, and then find the nodes which can reach the strongly connected components (both of which can be done in O(|S|+|R|) Ø Label the nodes in the strongly connected components and the nodes that can reach the strongly connected components with EG p Dr. Amr Talaat
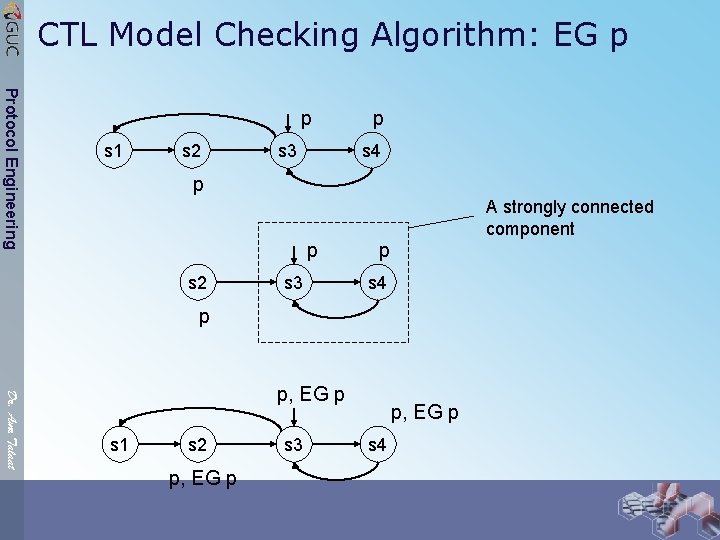
CTL Model Checking Algorithm: EG p Protocol Engineering p s 1 s 2 s 3 p s 4 p A strongly connected component p s 2 s 3 p s 4 p Dr. Amr Talaat p, EG p s 1 s 2 p, EG p s 3 p, EG p s 4
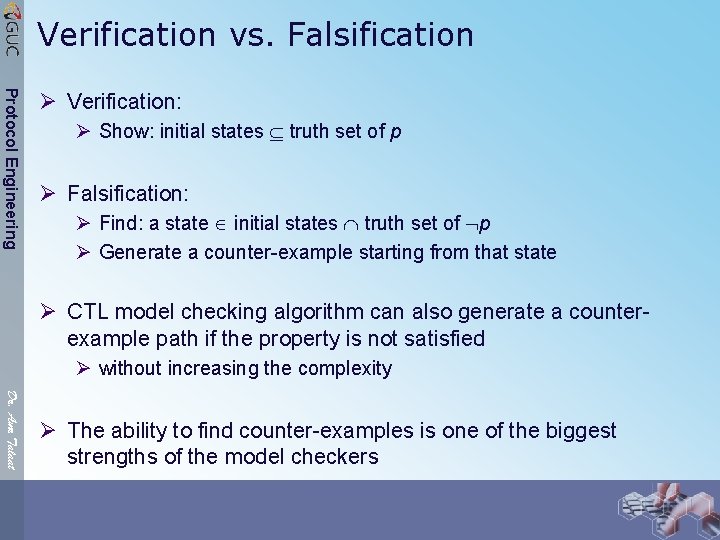
Verification vs. Falsification Protocol Engineering Ø Verification: Ø Show: initial states truth set of p Ø Falsification: Ø Find: a state initial states truth set of p Ø Generate a counter-example starting from that state Ø CTL model checking algorithm can also generate a counterexample path if the property is not satisfied Ø without increasing the complexity Dr. Amr Talaat Ø The ability to find counter-examples is one of the biggest strengths of the model checkers
![Temporal Properties Fixpoints [Emerson and Clarke 80] Protocol Engineering Here are some interesting CTL Temporal Properties Fixpoints [Emerson and Clarke 80] Protocol Engineering Here are some interesting CTL](http://slidetodoc.com/presentation_image_h2/736632f3e95dcffc3e2080e4e872bc19/image-51.jpg)
Temporal Properties Fixpoints [Emerson and Clarke 80] Protocol Engineering Here are some interesting CTL equivalences: AG p = p AX AG p EG p = p EX EG p AF p = p AX AF p EF p = p EX EF p A(p U q) = q (p AX A(p U q)) p EU q = q (p EX E(p U q)) Dr. Amr Talaat Note that we wrote the CTL temporal operators in terms of themselves and EX and AX operators
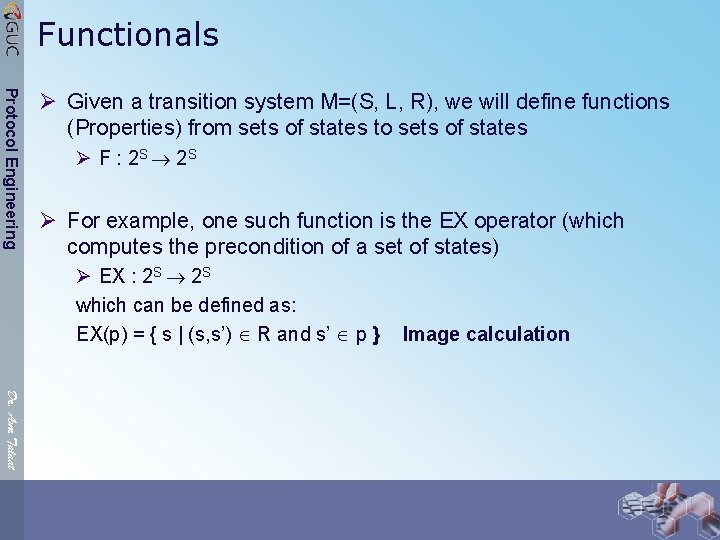
Functionals Protocol Engineering Ø Given a transition system M=(S, L, R), we will define functions (Properties) from sets of states to sets of states Ø F : 2 S 2 S Ø For example, one such function is the EX operator (which computes the precondition of a set of states) Ø EX : 2 S which can be defined as: EX(p) = { s | (s, s’) R and s’ p } Image calculation Dr. Amr Talaat
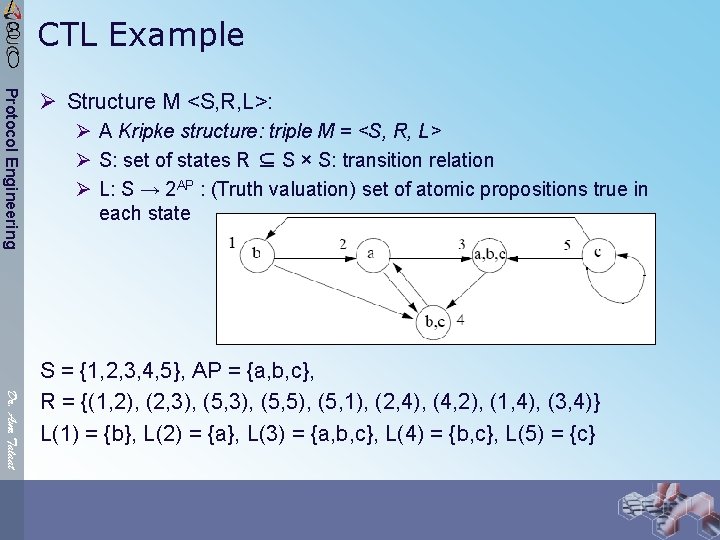
/ 8 0 CTL Example Protocol Engineering Ø Structure M <S, R, L>: Ø A Kripke structure: triple M = <S, R, L> Ø S: set of states R ⊆ S × S: transition relation Ø L: S → 2 AP : (Truth valuation) set of atomic propositions true in each state Dr. Amr Talaat S = {1, 2, 3, 4, 5}, AP = {a, b, c}, R = {(1, 2), (2, 3), (5, 5), (5, 1), (2, 4), (4, 2), (1, 4), (3, 4)} L(1) = {b}, L(2) = {a}, L(3) = {a, b, c}, L(4) = {b, c}, L(5) = {c}
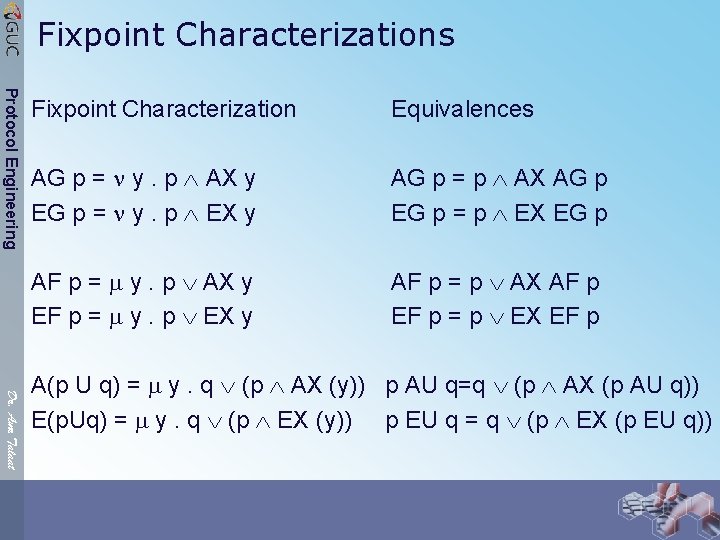
Fixpoint Characterizations Protocol Engineering Fixpoint Characterization Equivalences AG p = y. p AX y EG p = y. p EX y AG p = p AX AG p EG p = p EX EG p AF p = y. p AX y EF p = y. p EX y AF p = p AX AF p EF p = p EX EF p Dr. Amr Talaat A(p U q) = y. q (p AX (y)) p AU q=q (p AX (p AU q)) E(p. Uq) = y. q (p EX (y)) p EU q = q (p EX (p EU q))
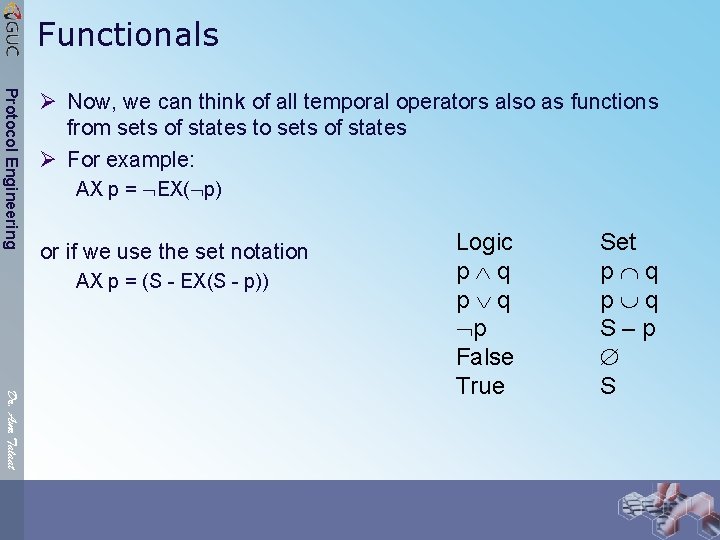
Functionals Protocol Engineering Ø Now, we can think of all temporal operators also as functions from sets of states to sets of states Ø For example: AX p = EX( p) or if we use the set notation AX p = (S - EX(S - p)) Dr. Amr Talaat Logic p q p False True Set p q S–p S
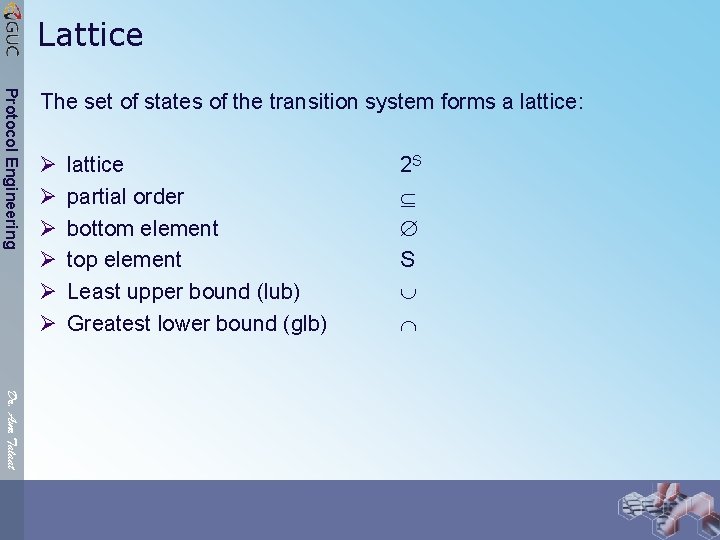
Lattice Protocol Engineering The set of states of the transition system forms a lattice: Ø Ø Ø lattice partial order bottom element top element Least upper bound (lub) Greatest lower bound (glb) 2 S S Dr. Amr Talaat
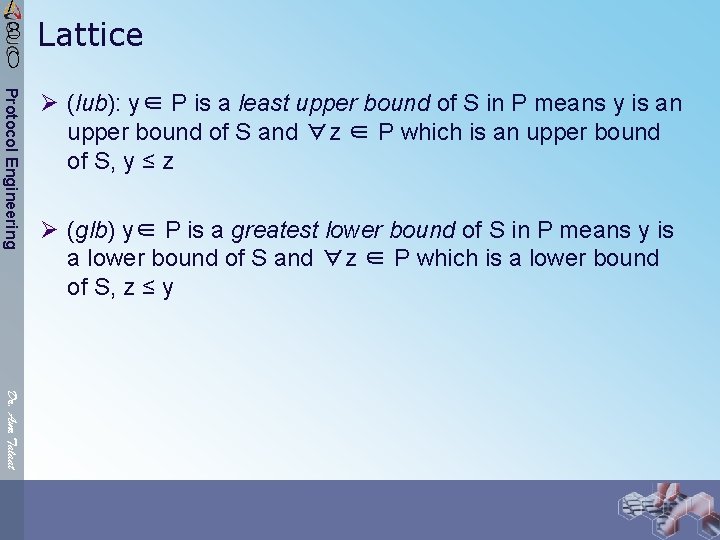
/ 8 0 Lattice Protocol Engineering Ø (lub): y∈ P is a least upper bound of S in P means y is an upper bound of S and ∀z ∈ P which is an upper bound of S, y ≤ z Ø (glb) y∈ P is a greatest lower bound of S in P means y is a lower bound of S and ∀z ∈ P which is a lower bound of S, z ≤ y Dr. Amr Talaat
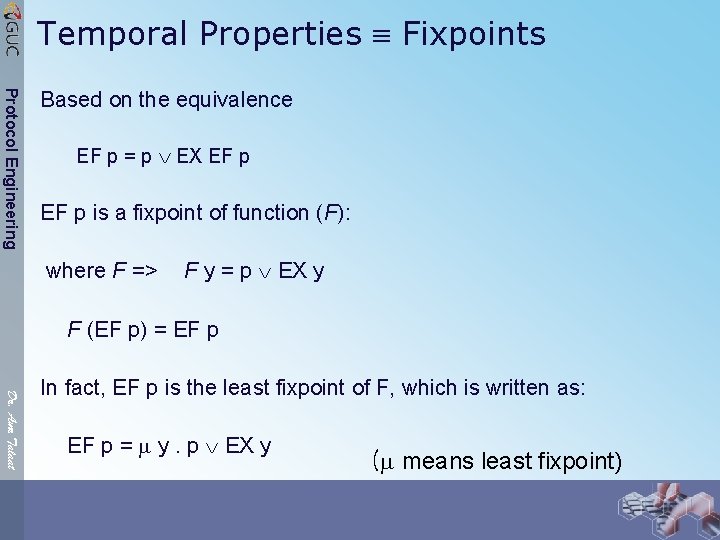
Temporal Properties Fixpoints Protocol Engineering Based on the equivalence EF p = p EX EF p is a fixpoint of function (F): where F => F y = p EX y F (EF p) = EF p Dr. Amr Talaat In fact, EF p is the least fixpoint of F, which is written as: EF p = y. p EX y ( means least fixpoint)
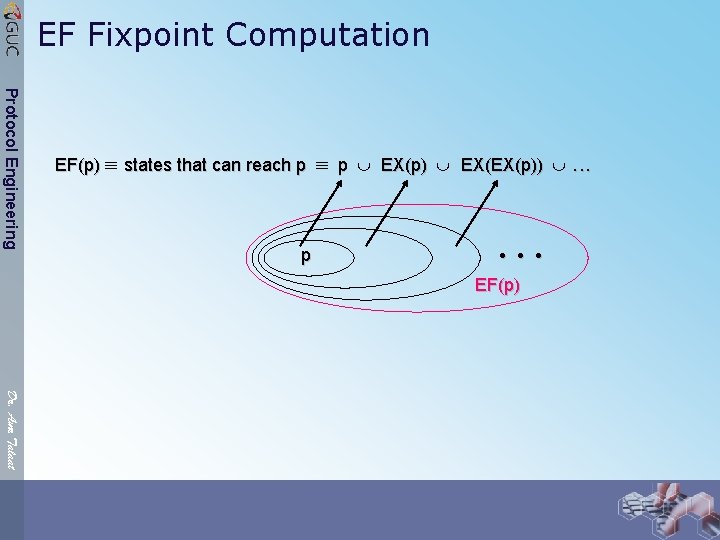
EF Fixpoint Computation Protocol Engineering EF(p) states that can reach p p p EX(p) EX(EX(p)) . . . • • • EF(p) Dr. Amr Talaat
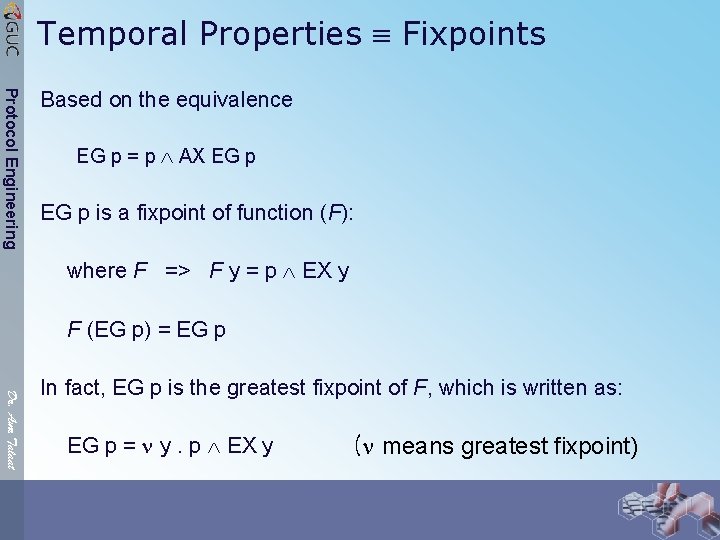
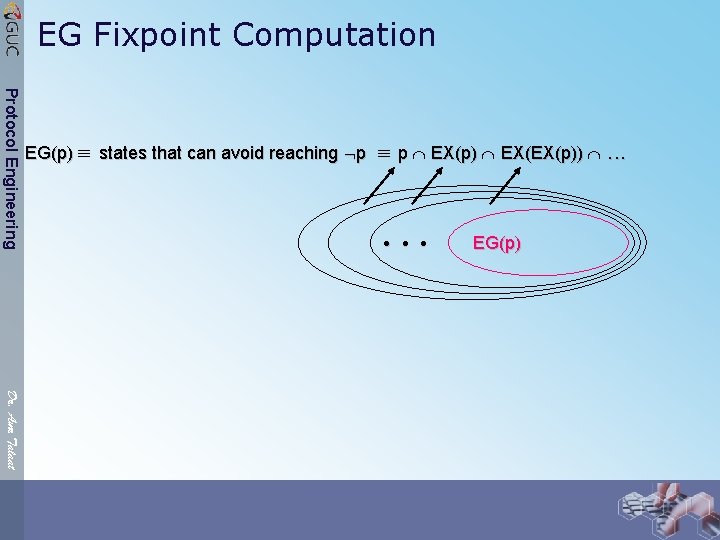
Temporal Properties Fixpoints Protocol Engineering Based on the equivalence EG p = p AX EG p is a fixpoint of function (F): where F => F y = p EX y F (EG p) = EG p Dr. Amr Talaat In fact, EG p is the greatest fixpoint of F, which is written as: EG p = y. p EX y ( means greatest fixpoint)
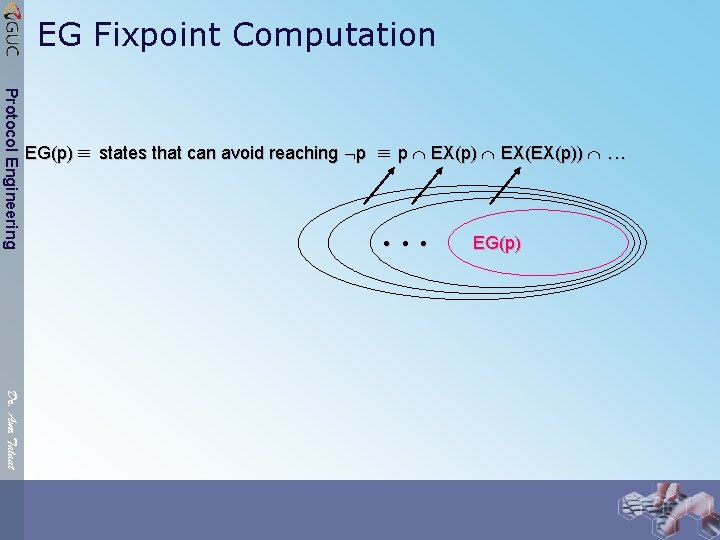
EG Fixpoint Computation Protocol Engineering EG(p) states that can avoid reaching p p EX(p) EX(EX(p)) . . . • • • EG(p) Dr. Amr Talaat
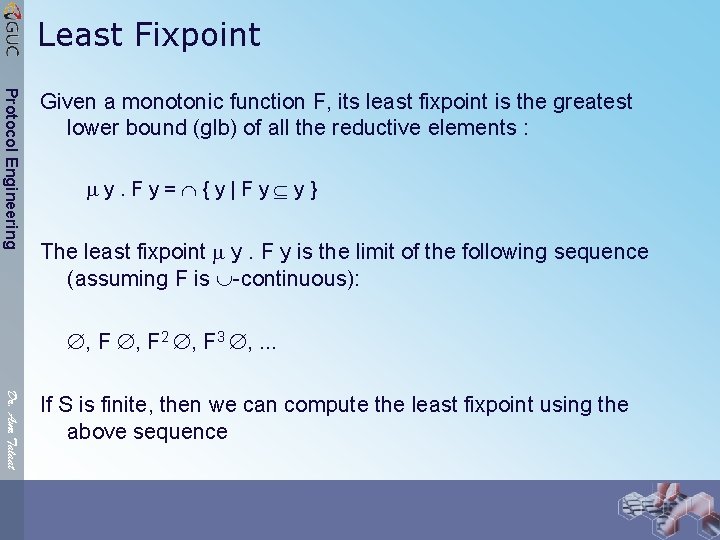
Least Fixpoint Protocol Engineering Given a monotonic function F, its least fixpoint is the greatest lower bound (glb) of all the reductive elements : y. Fy= {y|Fy y} The least fixpoint y. F y is the limit of the following sequence (assuming F is -continuous): , F 2 , F 3 , . . . Dr. Amr Talaat If S is finite, then we can compute the least fixpoint using the above sequence
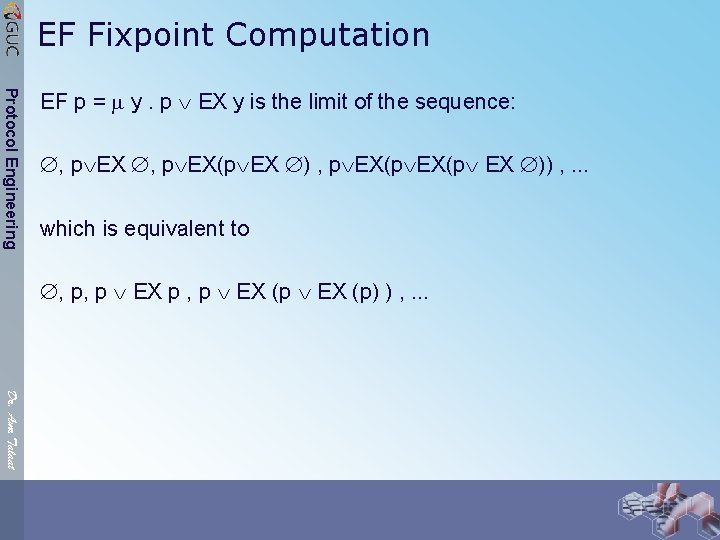
EF Fixpoint Computation Protocol Engineering EF p = y. p EX y is the limit of the sequence: , p EX(p EX )) , . . . which is equivalent to , p, p EX p , p EX (p) ) , . . . Dr. Amr Talaat
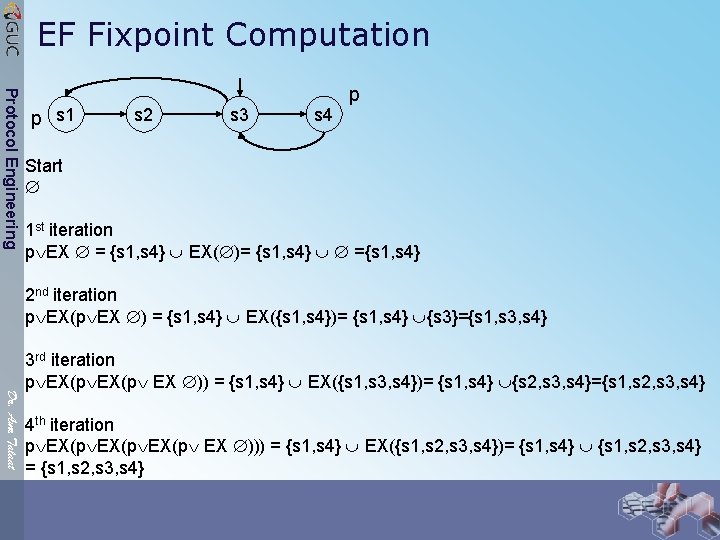
EF Fixpoint Computation Protocol Engineering p s 1 s 2 s 3 s 4 p Start 1 st iteration p EX = {s 1, s 4} EX( )= {s 1, s 4} ={s 1, s 4} 2 nd iteration p EX(p EX ) = {s 1, s 4} EX({s 1, s 4})= {s 1, s 4} {s 3}={s 1, s 3, s 4} Dr. Amr Talaat 3 rd iteration p EX(p EX )) = {s 1, s 4} EX({s 1, s 3, s 4})= {s 1, s 4} {s 2, s 3, s 4}={s 1, s 2, s 3, s 4} 4 th iteration p EX(p EX ))) = {s 1, s 4} EX({s 1, s 2, s 3, s 4})= {s 1, s 4} {s 1, s 2, s 3, s 4} = {s 1, s 2, s 3, s 4}
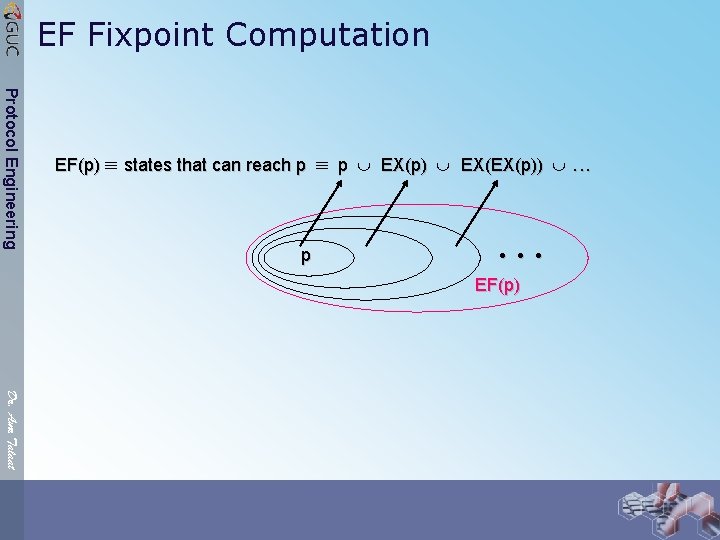
EF Fixpoint Computation Protocol Engineering EF(p) states that can reach p p p EX(p) EX(EX(p)) . . . • • • EF(p) Dr. Amr Talaat
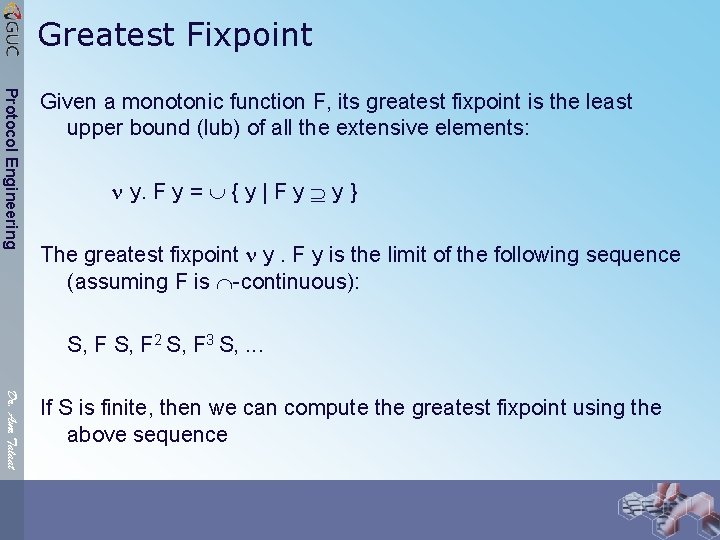
Greatest Fixpoint Protocol Engineering Given a monotonic function F, its greatest fixpoint is the least upper bound (lub) of all the extensive elements: y. F y = { y | F y y } The greatest fixpoint y. F y is the limit of the following sequence (assuming F is -continuous): S, F 2 S, F 3 S, . . . Dr. Amr Talaat If S is finite, then we can compute the greatest fixpoint using the above sequence
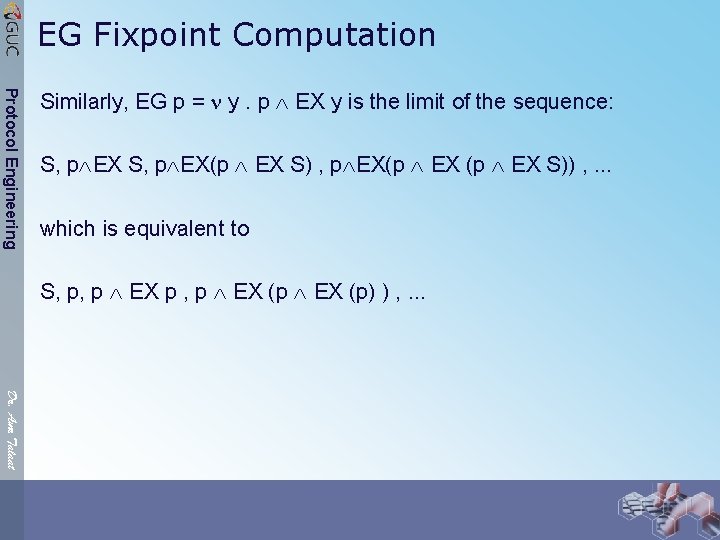
EG Fixpoint Computation Protocol Engineering Similarly, EG p = y. p EX y is the limit of the sequence: S, p EX(p EX S)) , . . . which is equivalent to S, p, p EX p , p EX (p) ) , . . . Dr. Amr Talaat
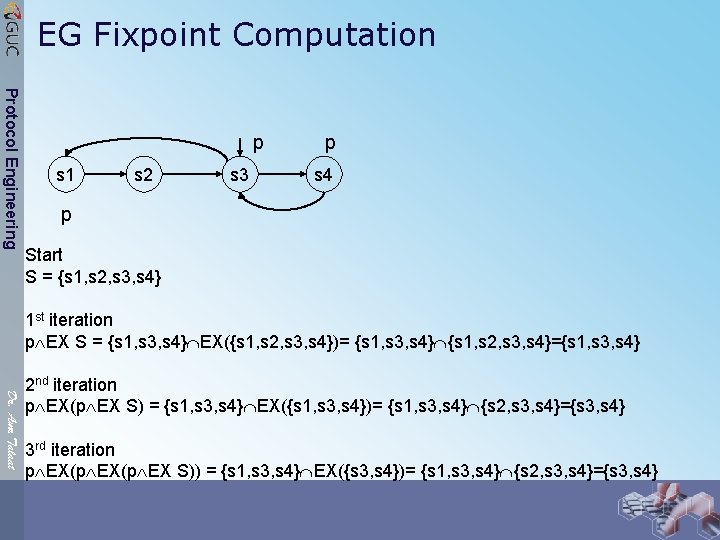
EG Fixpoint Computation Protocol Engineering p s 1 s 2 s 3 p s 4 p Start S = {s 1, s 2, s 3, s 4} 1 st iteration p EX S = {s 1, s 3, s 4} EX({s 1, s 2, s 3, s 4})= {s 1, s 3, s 4} {s 1, s 2, s 3, s 4}={s 1, s 3, s 4} Dr. Amr Talaat 2 nd iteration p EX(p EX S) = {s 1, s 3, s 4} EX({s 1, s 3, s 4})= {s 1, s 3, s 4} {s 2, s 3, s 4}={s 3, s 4} 3 rd iteration p EX(p EX S)) = {s 1, s 3, s 4} EX({s 3, s 4})= {s 1, s 3, s 4} {s 2, s 3, s 4}={s 3, s 4}
EG Fixpoint Computation Protocol Engineering EG(p) states that can avoid reaching p p EX(p) EX(EX(p)) . . . • • • EG(p) Dr. Amr Talaat
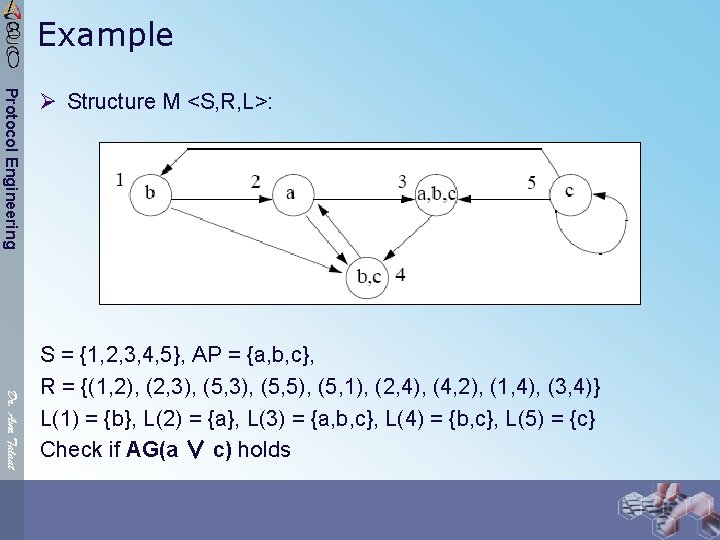
/ 8 0 Example Protocol Engineering Ø Structure M <S, R, L>: Dr. Amr Talaat S = {1, 2, 3, 4, 5}, AP = {a, b, c}, R = {(1, 2), (2, 3), (5, 5), (5, 1), (2, 4), (4, 2), (1, 4), (3, 4)} L(1) = {b}, L(2) = {a}, L(3) = {a, b, c}, L(4) = {b, c}, L(5) = {c} Check if AG(a ∨ c) holds
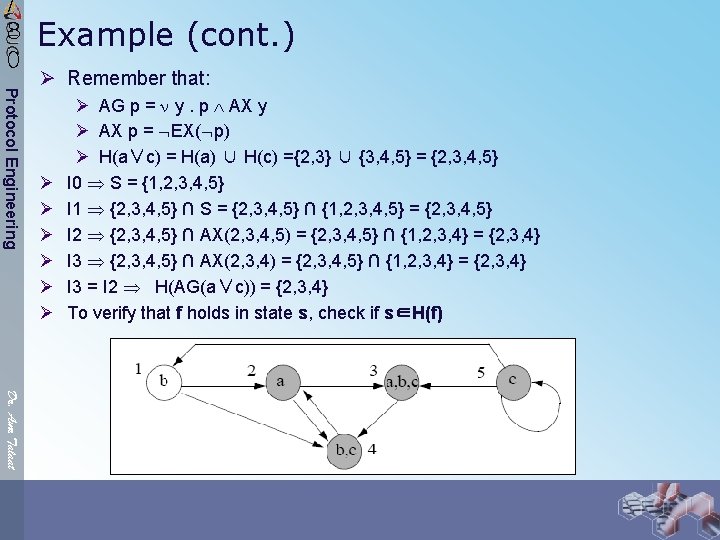
/ 8 0 Example (cont. ) Protocol Engineering Ø Remember that: Ø Ø Ø Ø AG p = y. p AX y Ø AX p = EX( p) Ø H(a∨c) = H(a) ∪ H(c) ={2, 3} ∪ {3, 4, 5} = {2, 3, 4, 5} I 0 S = {1, 2, 3, 4, 5} I 1 {2, 3, 4, 5} ∩ S = {2, 3, 4, 5} ∩ {1, 2, 3, 4, 5} = {2, 3, 4, 5} I 2 {2, 3, 4, 5} ∩ AX(2, 3, 4, 5) = {2, 3, 4, 5} ∩ {1, 2, 3, 4} = {2, 3, 4} I 3 {2, 3, 4, 5} ∩ AX(2, 3, 4) = {2, 3, 4, 5} ∩ {1, 2, 3, 4} = {2, 3, 4} I 3 = I 2 H(AG(a∨c)) = {2, 3, 4} To verify that f holds in state s, check if s∈H(f) Dr. Amr Talaat
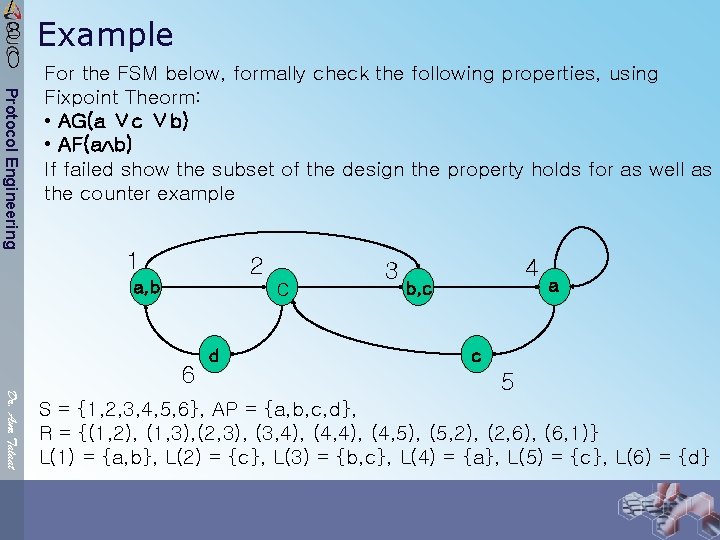
/ 8 0 Example Protocol Engineering For the FSM below, formally check the following properties, using Fixpoint Theorm: • AG(a ∨c ∨b) • AF(a b) If failed show the subset of the design the property holds for as well as the counter example 1 2 a, b 6 d c 3 4 b, c a c Dr. Amr Talaat 5 S = {1, 2, 3, 4, 5, 6}, AP = {a, b, c, d}, R = {(1, 2), (1, 3), (2, 3), (3, 4), (4, 5), (5, 2), (2, 6), (6, 1)} L(1) = {a, b}, L(2) = {c}, L(3) = {b, c}, L(4) = {a}, L(5) = {c}, L(6) = {d}
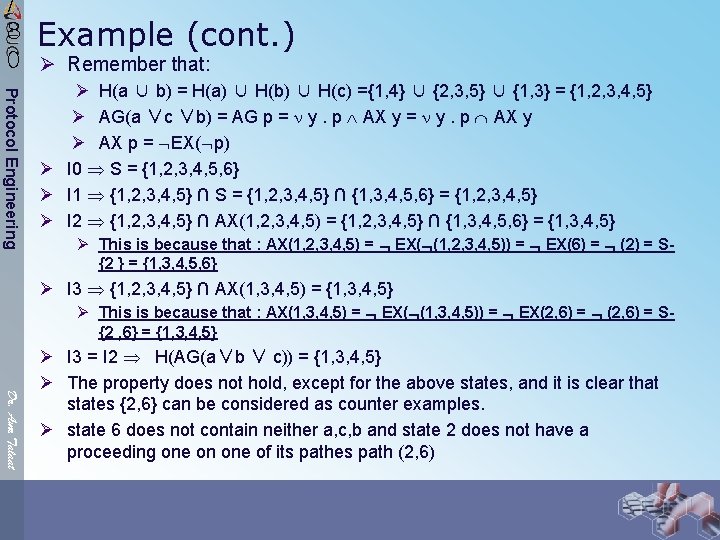
/ 8 Example (cont. ) 0 Ø Remember that: Protocol Engineering Ø H(a ∪ b) = H(a) ∪ H(b) ∪ H(c) ={1, 4} ∪ {2, 3, 5} ∪ {1, 3} = {1, 2, 3, 4, 5} Ø AG(a ∨c ∨b) = AG p = y. p AX y Ø AX p = EX( p) Ø I 0 S = {1, 2, 3, 4, 5, 6} Ø I 1 {1, 2, 3, 4, 5} ∩ S = {1, 2, 3, 4, 5} ∩ {1, 3, 4, 5, 6} = {1, 2, 3, 4, 5} Ø I 2 {1, 2, 3, 4, 5} ∩ AX(1, 2, 3, 4, 5) = {1, 2, 3, 4, 5} ∩ {1, 3, 4, 5, 6} = {1, 3, 4, 5} Ø This is because that : AX(1, 2, 3, 4, 5) = EX( (1, 2, 3, 4, 5)) = EX(6) = (2) = S{2 } = {1, 3, 4, 5, 6} Ø I 3 {1, 2, 3, 4, 5} ∩ AX(1, 3, 4, 5) = {1, 3, 4, 5} Ø This is because that : AX(1, 3, 4, 5) = EX( (1, 3, 4, 5)) = EX(2, 6) = S{2 , 6} = {1, 3, 4, 5} Dr. Amr Talaat Ø I 3 = I 2 H(AG(a∨b ∨ c)) = {1, 3, 4, 5} Ø The property does not hold, except for the above states, and it is clear that states {2, 6} can be considered as counter examples. Ø state 6 does not contain neither a, c, b and state 2 does not have a proceeding one on one of its pathes path (2, 6)
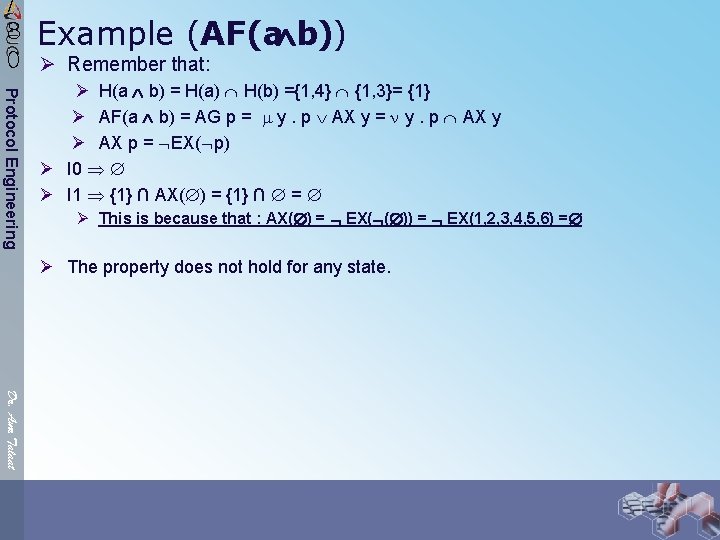
/ 8 Example (AF(a b)) 0 Ø Remember that: Protocol Engineering Ø H(a b) = H(a) H(b) ={1, 4} {1, 3}= {1} Ø AF(a b) = AG p = y. p AX y Ø AX p = EX( p) Ø I 0 Ø I 1 {1} ∩ AX( ) = {1} ∩ = Ø This is because that : AX( ) = EX( ( )) = EX(1, 2, 3, 4, 5, 6) = Ø The property does not hold for any state. Dr. Amr Talaat
/ 8 0 Model Checking Tools (non-commercial) Protocol Engineering Ø SMV (Symbolic Model Verifier) Ø A tool for checking finite state systems against specifications in the temporal logic CTL. Ø Developed at Carnegie Mellon University by E. Clarke, K. Mc. Millan et. al. Ø Supports a simple input language: SMV Ø For more information: http: //www. cs. cmu. edu/~modelcheck/smv. html Ø Cadence SMV Dr. Amr Talaat Ø Updated version of SMV by K. Mc. Millan at Berkeley Cadence Labs Ø Input languages: extended SMV and synchronous Verilog Ø Supports temporal logics CTL and LTL, finite automata, embedded assertions, and refinement specifications. Ø Features compositional reasoning, link with a simple theorem prover, an easy-touse graphical user interface and source level debugging capabilities Ø For more information: http: //www-cad. eecs. berkeley. edu/~kenmcmil/smv/
/ 8 0 Model Checking Tools (commercial) Protocol Engineering Ø Formal. Check Ø Supports the synthesizable subsets of Verilog and VHDL hardware design languages. Ø User supplies Formal. Check with a set of queries (properties and constraints) Ø Each property is defined using semantics of the class of omega automata. Ø Tool provides powerful model reduction options. Ø For more information: http: //www. cadence. com/datasheets/formalcheck. html Dr. Amr Talaat
7 Model Checking Protocol Engineering Ø Automatic verification (or falsification) of finite state systems Ø Explicit State Representation ⇒ State Explosion Problem (about 108 states maximum) Ø Breakthrough: Implicit State Representation using ROBDD (about 1020 states). Ø Use Boolean characteristic functions represented by ROBDDs to encode sets of states and transition relations. Dr. Amr Talaat
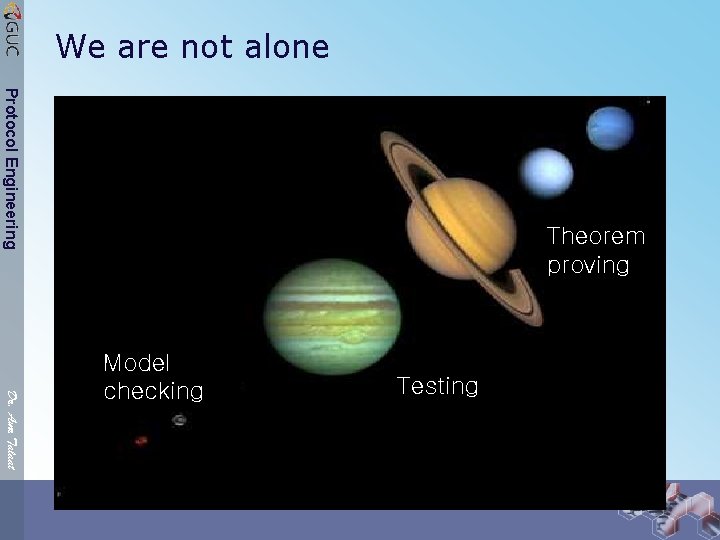
We are not alone Protocol Engineering Theorem proving Dr. Amr Talaat Model checking Testing
Hybrid Verification Protocol Engineering Ø Formal Verification using Ø Theorem Proving + Model Checking Theorem Proving Model Checking Dr. Amr Talaat
Scientists Quotes Protocol Engineering “Teaching to unsuspecting youngsters the effective use of formal methods is one of the joys of life because it is so extremely rewarding” “A formula is worth a thousand pictures” Edsger Wybe Dijkstra (1930– 2002) Dr. Amr Talaat
- Slides: 80