Net Op Tech Gmb H Remote Control Education
Net. Op Tech Gmb. H Remote Control. Education. Security Moving expertise – not people Net. Op Remote Control – Desktop Management for OS/2 - e. Com. Station Warpstock Europe 2007 Andreas Kietzmann Managing Director Net. Op Tech Gmb. H
Net. Op Tech Gmb. H Agenda § Introduction of Net. Op Tech Gmb. H § Net. Op Product Pillars § Remote Control/Management Functionality § OS-Platforms § Presentation of Net. Op Host for OS/2 - e. Com. Station Remote Control. Education. Security
Net. Op Tech Gmb. H § Subsidary of Danware A/S § Established October 2006 in Stuttgart § Location since April 2007: Neu-Isenburg near Frankfurt § Objectives: Sales, marketing and support of the Net. Op solutions § Number of employees: 9 § 100% indirect sales through channel Remote Control. Education. Security
Net. Op Tech Gmb. H Remote Control. Education. Security Net. Op – Product Pillars Net. Op Process Control -Scaleable safety solution with central management console for the monitoring of processes and communication on Desktop/Laptop computers Net. Op Net Filter – Centrally manageable Web filter. Net. Op Desktop Firewall Net. Op Net. Filter Net. Op Learning Center – e. Learning Content Management Solution. Net. Op School - Solution for education, training and instruction in computer-based classrooms. Net. Op Instruct - Solution for computer-based advanced training, teamwork and internal communication in enterprises. Net. Op Learning Center Net. Op School Net. Op Instruct

Net. Op Tech Gmb. H Remote Control. Education. Security Net. Op – Product Pillars Net. Op Remote Control – highly scalable software solution for remote maintenance of heterogeneous, complex IT environments for enterprises of all size. Net. Op Remote Control Net. Op Mobile Net. Op On Demand Net. Op Mobile - The remote control solution for the remote administration of mobile and industrial devices e. g. mobile phone, PDAs, Windows CE/Mobile was based controls. Net. Op On Demand - Web based remote control solution for the flexible employment e. g. for the support of external customers.
Net. Op Tech Gmb. H Remote Control. Education. Security The complete, scalable and secure remote control software for IT professionals § Complete - one product covers all Remote control across multiple platforms - Windows, Linux, Mac, OS/2, Sun Remote Management Unrivalled connectivity solutions available for LAN, WAN/Internet § Scalable – from few to thousands of users Hierarchical, sharable address book Integration with Directory Services Multiple Guest users sharing same screen § Secure – advanced authentication and unbreakable encryption Authentication by e. g. Smart Card, RSA Secure. ID and Directory Services Net. Op Security Server for extended authentication and authorization Encryption implemented according to the toughest industry standards. When quality matters
Net. Op Tech Gmb. H Remote Control. Education. Security Net. Op Remote Control today § Net. Op Remote Control is designed specifically to meet the needs of corporate business, and is packed with numerous features to help IT professionals get the most out of remote control technology. § Net. Op is typically used for – Remote access to the user’s own computer – Remote server administration – Remote user support from a corporate Helpdesk
Net. Op Tech Gmb. H Remote Control. Education. Security Net. Op Modules § Guest – § Host – § An extended Host module that can route Net. Op traffic across different communication protocols. Name Server – § Allows a computer to be remote controlled by any computer running the Guest module. Gateway – § Allows a computer to remote control any computer running the Host module. An extended Host module that can store Net. Op names and resolve them into IP addresses. Security Server – An extended Host module that can control Net. Op security management and logging.
Net. Op Tech Gmb. H Remote Control. Education. Security Key Features § Remote control – superior quality supporting a large range of platforms. § Remote Management – computer management controlling services, registry, tasks, event log, shares and system state. § File transfer – split screen, copy, move, sync, clone, crash recovery and delta transfer. § Scripting – schedule file transfers and other operations like inventory scanning. § Active. X components – integrate remote control and file transfer into other applications. § Chat, Audio Chat, Video Chat – allow users to communicate in text mode or verbally – supported by webcam video.
Net. Op Tech Gmb. H Remote Control. Education. Security Key Features … § Multi Guest session – allows a number of Guest users to view and control the same Host desktop. § Run Program – launch programs at the remote computer. § Send Message – distribute popup messages in Rich Text Format which allows links to e. g. web sites. § Get Inventory – collect hardware and software information from remote computers. § Request Help – contact the help desk via Net. Op and run an external application to auto-generate trouble tickets. § Communication devices – TCP/IP (IPv 4), TCP/IP (IPv 6), IPX, Net. BIOS, Serial, TAPI, CAPI, Ir. DA.
Net. Op Tech Gmb. H Remote Control. Education. Security Key Features … § Security – local and centralized, Native Net. Op, Directory Services, RSA Secur. ID, Smart Card and Windows-integrated. § Encryption – implemented according to the toughest industry standards. § Event logging – local, centralized, Windows-integrated and management-integrated. § Session recording – save the Host screen activities in a file for later replay. § Snapshot - save the current Host desktop image as a file. § Deployment Utility – roll-out a large number of Net. Op Hosts unattended.
Net. Op Tech Gmb. H Remote Control. Education. Security Remote Control § Remote control allows a user to view the desktop of a remote computer from ones computer. § Take full control of remote keyboard and mouse. § Host desktops can be displayed in full-screen, optionally autoscrolling window or fit window mode. Support for full-screen command prompt. § Remote control windows and the Guest application window are separate. § Multiple Guest sessions allow multiple Guests to view the same Host desktop. § Cascade remote control can chain Guest-Host sessions.
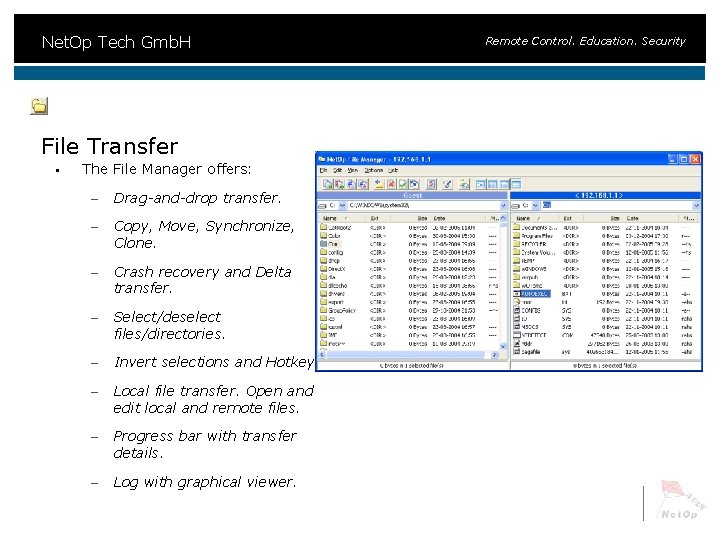
Net. Op Tech Gmb. H File Transfer § The File Manager offers: – Drag-and-drop transfer. – Copy, Move, Synchronize, Clone. – Crash recovery and Delta transfer. – Select/deselect files/directories. – Invert selections and Hotkeys. – Local file transfer. Open and edit local and remote files. – Progress bar with transfer details. – Log with graphical viewer. Remote Control. Education. Security
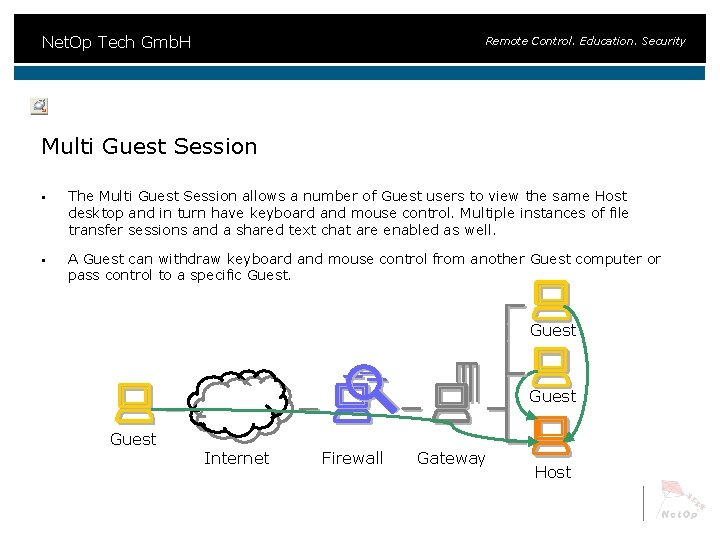
Net. Op Tech Gmb. H Remote Control. Education. Security Multi Guest Session § The Multi Guest Session allows a number of Guest users to view the same Host desktop and in turn have keyboard and mouse control. Multiple instances of file transfer sessions and a shared text chat are enabled as well. § A Guest can withdraw keyboard and mouse control from another Guest computer or pass control to a specific Guest Internet Firewall Gateway Host
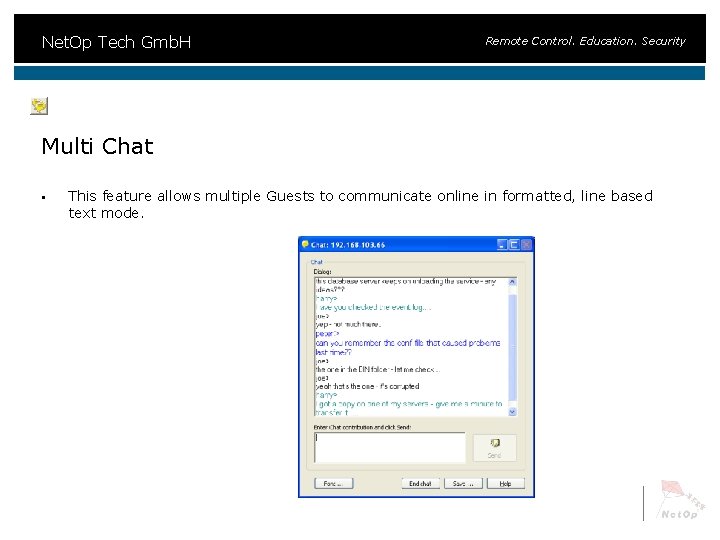
Net. Op Tech Gmb. H Remote Control. Education. Security Multi Chat § This feature allows multiple Guests to communicate online in formatted, line based text mode.
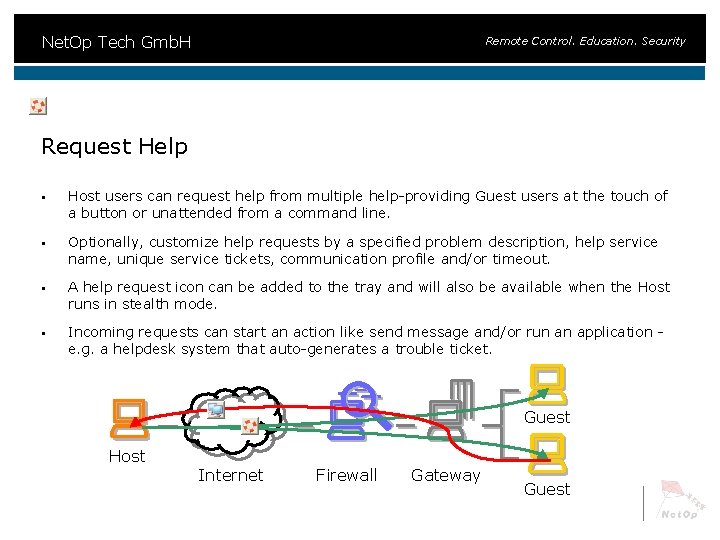
Net. Op Tech Gmb. H Remote Control. Education. Security Request Help § Host users can request help from multiple help-providing Guest users at the touch of a button or unattended from a command line. § Optionally, customize help requests by a specified problem description, help service name, unique service tickets, communication profile and/or timeout. § A help request icon can be added to the tray and will also be available when the Host runs in stealth mode. § Incoming requests can start an action like send message and/or run an application e. g. a helpdesk system that auto-generates a trouble ticket. Guest Host Internet Firewall Gateway Guest
Net. Op Tech Gmb. H Key Features § High Performance § Security § Stability § Superior Cross-platform Support § Multi-protocol Communication § Scalability Remote Control. Education. Security
Net. Op Tech Gmb. H Remote Control. Education. Security High Performance § Among the fastest in the world. § Only screen changes are transferred. § Windows version uses GDI-hooking. § Advanced event-driven region technique. § Uses bitmap caching. § Non-polling communication engine. § Strong compression algorithm. Guest Host
Net. Op Tech Gmb. H Key Benefits § High Performance § Security § Stability § Superior Cross-platform Support § Multi-protocol Communication § Scalability Remote Control. Education. Security
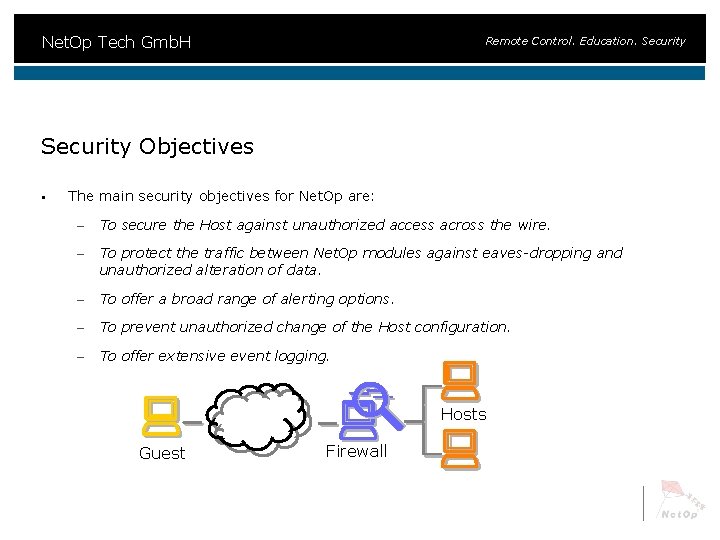
Net. Op Tech Gmb. H Remote Control. Education. Security Objectives § The main security objectives for Net. Op are: – To secure the Host against unauthorized access across the wire. – To protect the traffic between Net. Op modules against eaves-dropping and unauthorized alteration of data. – To offer a broad range of alerting options. – To prevent unauthorized change of the Host configuration. – To offer extensive event logging. Hosts Guest Firewall
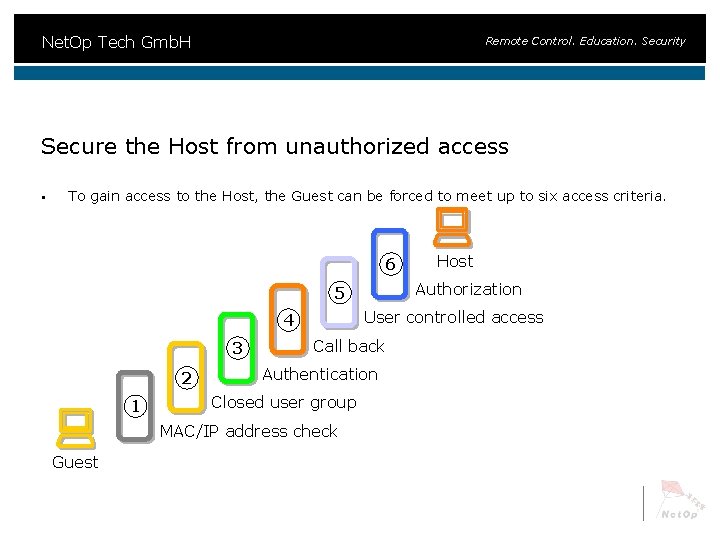
Net. Op Tech Gmb. H Remote Control. Education. Security Secure the Host from unauthorized access § To gain access to the Host, the Guest can be forced to meet up to six access criteria. 6 Authorization 5 User controlled access 4 3 2 1 Call back Authentication Closed user group MAC/IP address check Guest Host
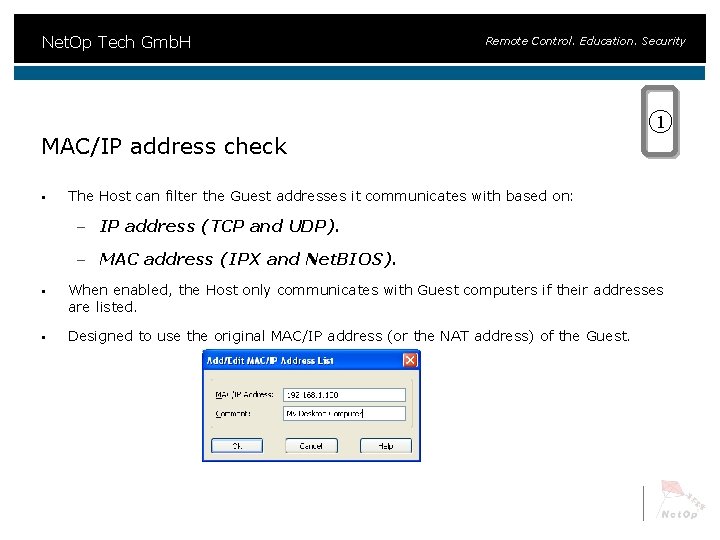
Net. Op Tech Gmb. H Remote Control. Education. Security 1 MAC/IP address check § The Host can filter the Guest addresses it communicates with based on: – IP address (TCP and UDP). – MAC address (IPX and Net. BIOS). § When enabled, the Host only communicates with Guest computers if their addresses are listed. § Designed to use the original MAC/IP address (or the NAT address) of the Guest.
Net. Op Tech Gmb. H Remote Control. Education. Security 2 Closed User Group § Closed User Group serial numbers are supplied by Danware to: – Deny any communication with modules not using the same Closed User Group serial number. – Prevent employees from using the modules outside the organization. – Prevent outside access to the organization. 1234…. ? 4321…. Guest Host
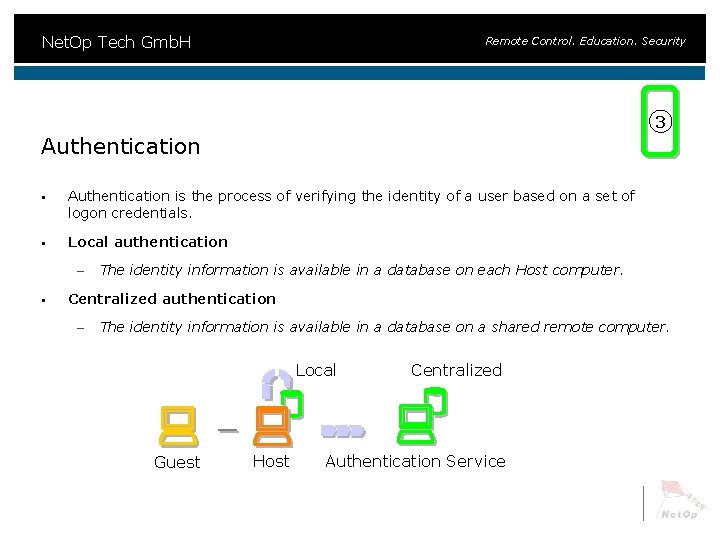
Net. Op Tech Gmb. H Remote Control. Education. Security 3 Authentication § Authentication is the process of verifying the identity of a user based on a set of logon credentials. § Local authentication – § The identity information is available in a database on each Host computer. Centralized authentication – The identity information is available in a database on a shared remote computer. Local Guest Host Centralized Authentication Service
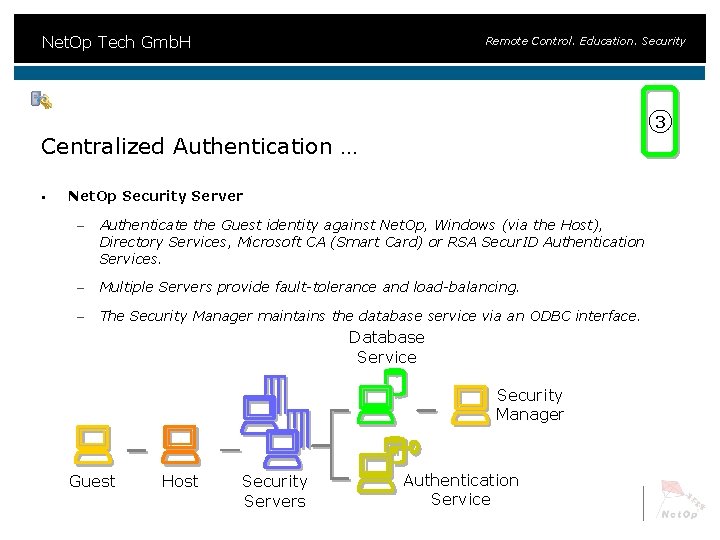
Net. Op Tech Gmb. H Remote Control. Education. Security 3 Centralized Authentication … § Net. Op Security Server – Authenticate the Guest identity against Net. Op, Windows (via the Host), Directory Services, Microsoft CA (Smart Card) or RSA Secur. ID Authentication Services. – Multiple Servers provide fault-tolerance and load-balancing. – The Security Manager maintains the database service via an ODBC interface. Database Service Security Manager Guest Host Security Servers Authentication Service
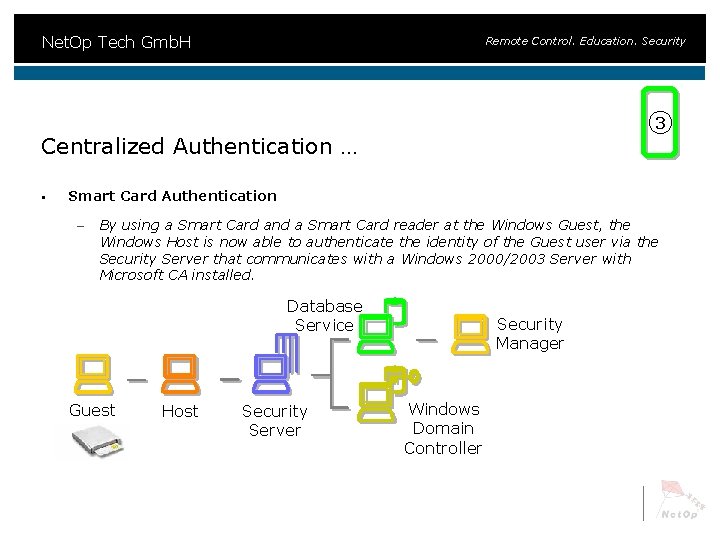
Net. Op Tech Gmb. H Remote Control. Education. Security 3 Centralized Authentication … § Smart Card Authentication – By using a Smart Card and a Smart Card reader at the Windows Guest, the Windows Host is now able to authenticate the identity of the Guest user via the Security Server that communicates with a Windows 2000/2003 Server with Microsoft CA installed. Database Service Guest Host Security Server Security Manager Windows Domain Controller
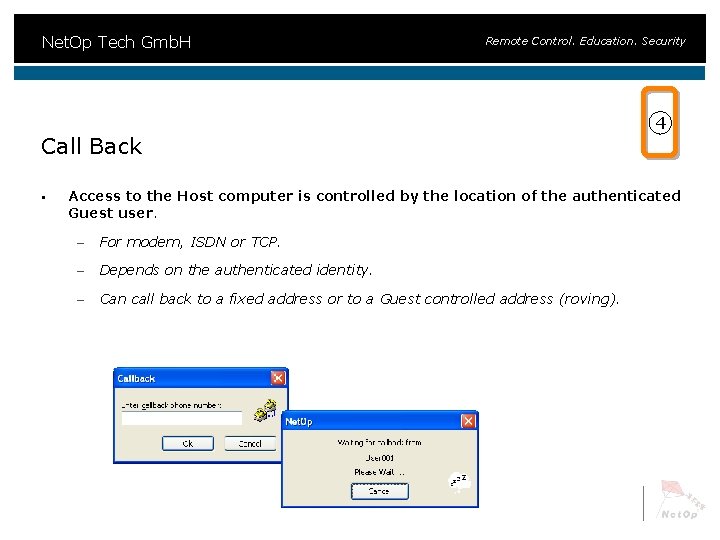
Net. Op Tech Gmb. H Remote Control. Education. Security Call Back § 4 Access to the Host computer is controlled by the location of the authenticated Guest user. – For modem, ISDN or TCP. – Depends on the authenticated identity. – Can call back to a fixed address or to a Guest controlled address (roving).
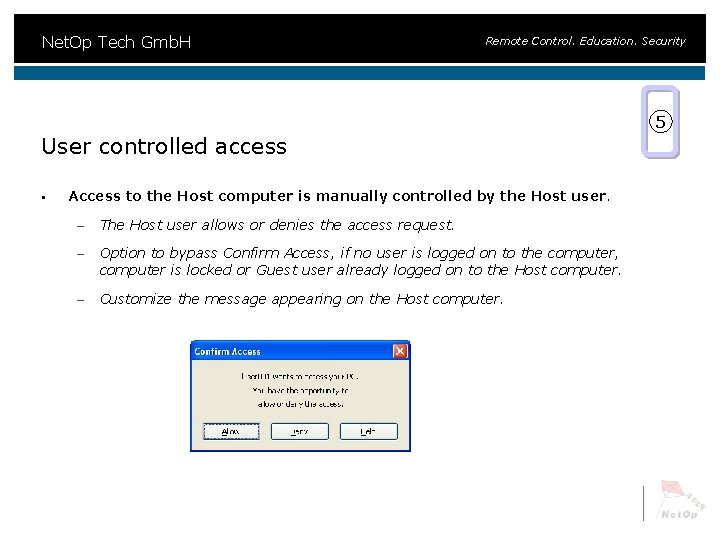
Net. Op Tech Gmb. H Remote Control. Education. Security 5 User controlled access § Access to the Host computer is manually controlled by the Host user. – The Host user allows or denies the access request. – Option to bypass Confirm Access, if no user is logged on to the computer, computer is locked or Guest user already logged on to the Host computer. – Customize the message appearing on the Host computer.
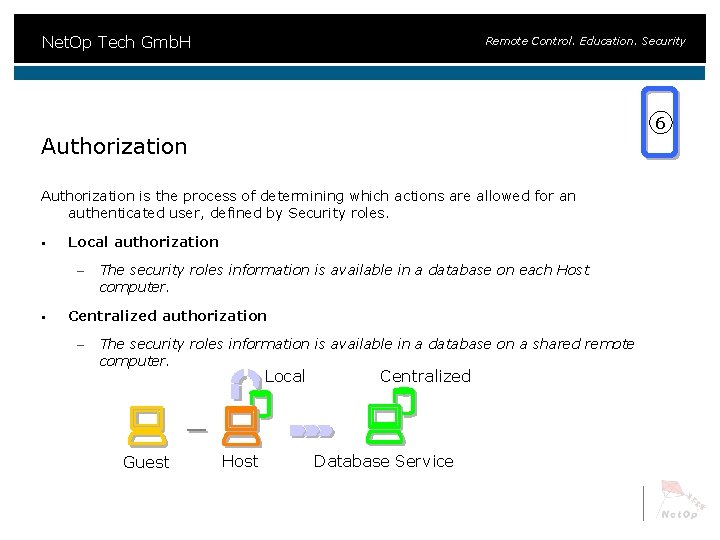
Net. Op Tech Gmb. H Remote Control. Education. Security 6 Authorization is the process of determining which actions are allowed for an authenticated user, defined by Security roles. § Local authorization – § The security roles information is available in a database on each Host computer. Centralized authorization – The security roles information is available in a database on a shared remote computer. Local Guest Host Centralized Database Service
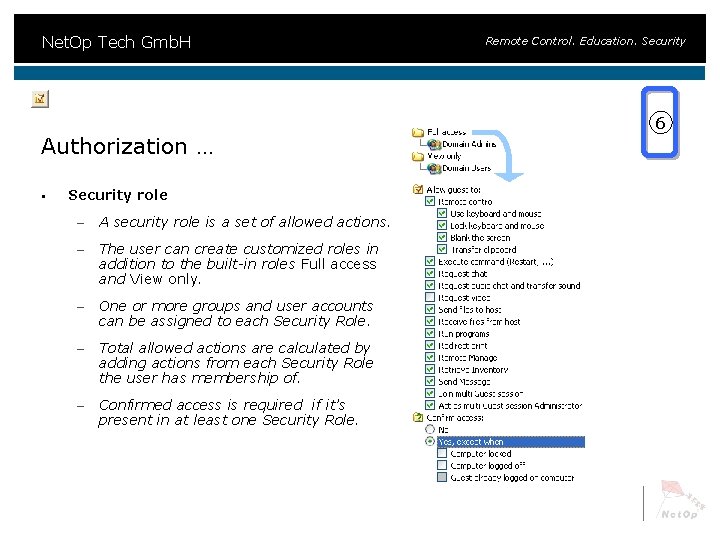
Net. Op Tech Gmb. H Authorization … § Security role – A security role is a set of allowed actions. – The user can create customized roles in addition to the built-in roles Full access and View only. – One or more groups and user accounts can be assigned to each Security Role. – Total allowed actions are calculated by adding actions from each Security Role the user has membership of. – Confirmed access is required if it’s present in at least one Security Role. Remote Control. Education. Security 6
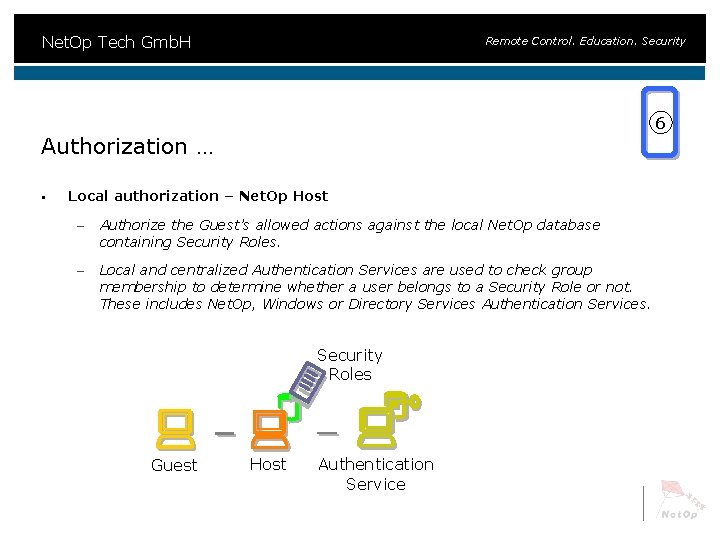
Net. Op Tech Gmb. H Remote Control. Education. Security 6 Authorization … § Local authorization – Net. Op Host – Authorize the Guest’s allowed actions against the local Net. Op database containing Security Roles. – Local and centralized Authentication Services are used to check group membership to determine whether a user belongs to a Security Role or not. These includes Net. Op, Windows or Directory Services Authentication Services. Security Roles Guest Host Authentication Service
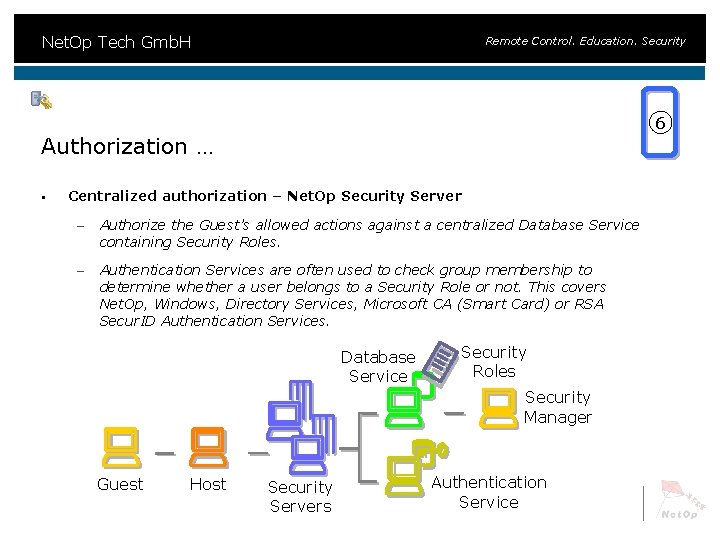
Net. Op Tech Gmb. H Remote Control. Education. Security 6 Authorization … § Centralized authorization – Net. Op Security Server – Authorize the Guest’s allowed actions against a centralized Database Service containing Security Roles. – Authentication Services are often used to check group membership to determine whether a user belongs to a Security Role or not. This covers Net. Op, Windows, Directory Services, Microsoft CA (Smart Card) or RSA Secur. ID Authentication Services. Database Service Security Roles Security Manager Guest Host Security Servers Authentication Service
Net. Op Tech Gmb. H Remote Control. Education. Security Protect the traffic § Encryption – § Integrity and message authentication – § Data transmitted between Windows, Linux, Solaris and Mac OS X modules can be encrypted using the Advanced Encryption Standard (AES) with key lengths up to 256 -bits. 7 different levels are available including Net. Op 6. x/5. x compatible for communication with older Net. Op modules. The integrity and authenticity of encrypted data is verified using the Keyed -Hash Message Authentication Code (HMAC) based on the Secure Hash Standards SHA-1 (160 -bit) or SHA-256 (256 -bit). Key exchange – Encryption keys for encrypted data transmissions are exchanged using the Diffie-Hellman method with key lengths up to 2048 bits and up to 256 -bit AES and up to 512 -bit SHA HMAC verification.
Net. Op Tech Gmb. H Remote Control. Education. Security policies and options § Action after exceeding max. invalid logon attempts – § Action after disconnect: – § § § Disconnect, Disable Host or Restart Windows. None, Lock computer, Log off Windows or Restart Windows. File Transfer – Disable file transfer before local logon. – Protect Host computer files. – Ensure that Host user file rights are enabled. Record sessions – Save session-recordings for documentation. – Enforce recording and disconnect if it fails. Timeouts – Confirm Access, Authentication and Inactivity.
Net. Op Tech Gmb. H Remote Control. Education. Security policies and options … § Stealth mode – § Host name not public – § Host does not respond to broadcast communication and hides its names and addresses. User name disabled – § Host is not displayed on the screen. Host does not respond to connection attempts using the logged-on user name. Connection notification – Message and/or sound upon and/or during connection. – Connection list. – Balloon tips. – Animated icon.
Net. Op Tech Gmb. H Remote Control. Education. Security Prevent unauthorized change of the Host configuration § Host maintenance password – Protects Guest access security. – Protects all other configuration. – Prevents the Host user from unloading the Host and stopping Host communication. – Protects Host configuration files and disables the Tools menu commands, when the: • Host is connected. • Host is communicating.
Net. Op Tech Gmb. H Remote Control. Education. Security Extensive event logging § § Multiple logging destinations: – Local file – log Net. Op events on the local computer. – Net. Op Server – log Net. Op events in the database of a central Net. Op Security Server group. – Windows event log – log Net. Op events to the local or a remote Windows Event Log. – Management console – log Net. Op events by sending SNMP traps to a SNMP enabled central management console like HP Open. View. Large set of events – More than 100 Net. Op events can be logged.
Net. Op Tech Gmb. H Key Benefits § High Performance § Security § Stability § Superior Cross-platform Support § Multi-protocol Communication § Scalability Remote Control. Education. Security
Net. Op Tech Gmb. H Remote Control. Education. Security Stability § Net. Op offers an incredible powerful feature set that interferes very little with the operating system: – Display device drivers are NOT replaced by a cover driver to capture the Host screen activity. – On-the-fly configuration check of core settings. – Recovery mechanism to provide high availability of the Host module. – Low CPU utilization. – Unique communication recovery.
Net. Op Tech Gmb. H Key Benefits § High Performance § Security § Stability § Superior Cross-platform Support § Multi-protocol Communication § Scalability Remote Control. Education. Security
Net. Op Tech Gmb. H Remote Control. Education. Security Superior Cross-Platform Support § By using a unique forwards and backwards compatible design Net. Op can offer remote control across different operating systems: – Windows Server 2003, XP, 2000, NT 4. 0, ME, 9 x – Windows CE, Windows Mobile – Solaris/Linux – Mac OS X – OS/2, e. Com. Station – DOS / Windows 3. 1 x * – Active. X – Terminal Services / Citrix – Symbian OS * * Available in other versions
Net. Op Tech Gmb. H Remote Control. Education. Security Superior Cross-Platform Support example… § OS/2 - e. Com. Station Host – Remote control. – Enhanced bitmap mode. – UDP, TCP, IPX, Serial, CAPI, APPC. – Default password security. – Individual Guest ID and password security. – Security Server authentication. – Confirm access. – File transfer. – Text chat.
Net. Op Tech Gmb. H Key Benefits § High Performance § Security § Stability § Superior Cross-platform Support § Multi-protocol Communication § Scalability Remote Control. Education. Security
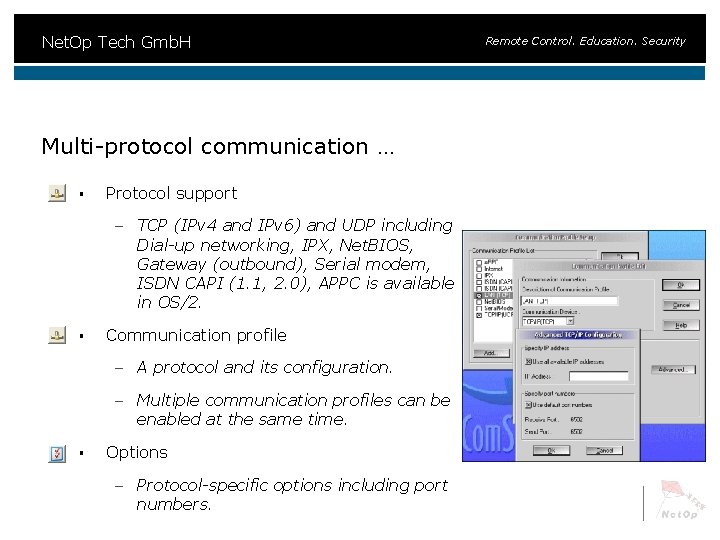
Net. Op Tech Gmb. H Multi-protocol communication … § Protocol support – TCP (IPv 4 and IPv 6) and UDP including Dial-up networking, IPX, Net. BIOS, Gateway (outbound), Serial modem, ISDN CAPI (1. 1, 2. 0), APPC is available in OS/2. § Communication profile – A protocol and its configuration. – Multiple communication profiles can be enabled at the same time. § Options – Protocol-specific options including port numbers. Remote Control. Education. Security
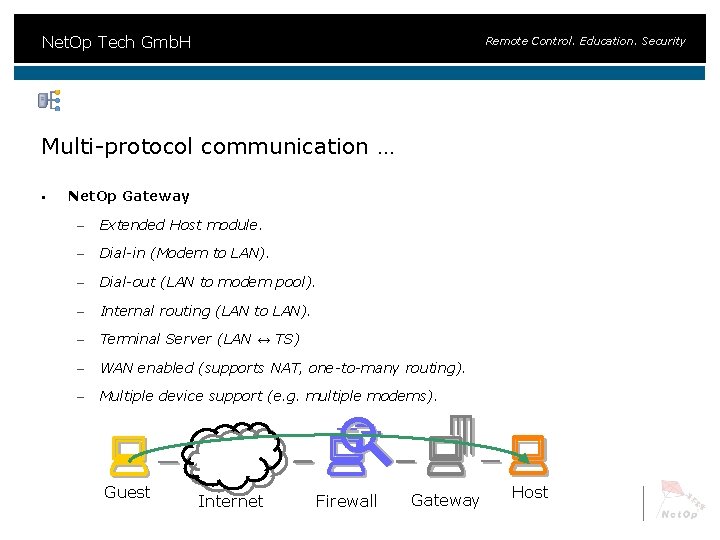
Net. Op Tech Gmb. H Remote Control. Education. Security Multi-protocol communication … § Net. Op Gateway – Extended Host module. – Dial-in (Modem to LAN). – Dial-out (LAN to modem pool). – Internal routing (LAN to LAN). – Terminal Server (LAN ↔ TS) – WAN enabled (supports NAT, one-to-many routing). – Multiple device support (e. g. multiple modems). Guest Internet Firewall Gateway Host
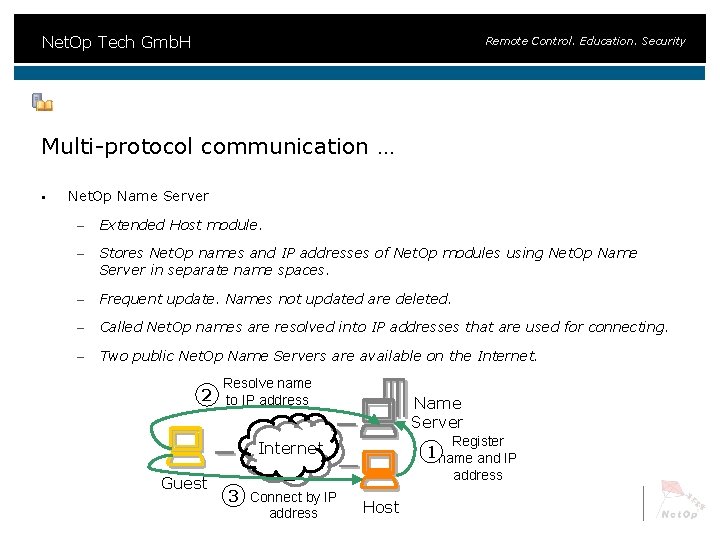
Net. Op Tech Gmb. H Remote Control. Education. Security Multi-protocol communication … § Net. Op Name Server – Extended Host module. – Stores Net. Op names and IP addresses of Net. Op modules using Net. Op Name Server in separate name spaces. – Frequent update. Names not updated are deleted. – Called Net. Op names are resolved into IP addresses that are used for connecting. – Two public Net. Op Name Servers are available on the Internet. Resolve name 2 to IP address Name Server Register Internet Guest 1 name and IP address 3 Connect by IP address Host
Net. Op Tech Gmb. H Remote Control. Education. Security Scalability § Net. Op is designed with scalability in mind to fit any organization. – The Guest can handle from one Host and upwards. – Number of phonebook entries is only limited by disk space. – Number of concurrent connections is only limited by memory and CPU power. – Net. Op generates only a modest amount of network traffic during a session and uses a non-polling communication engine which only transmits if something changes or a command is issued. – Multiple protocol-support spans from simple point-to-point connections and up to enterprise WAN. – And finally Net. Op can integrate into most management systems.
Net. Op Tech Gmb. H Remote Control. Education. Security Technical Support § Net. Op Tech offers 2 nd level support in German language § Support exclusively to partners § Knowledgebase http: //help. netop. com
Net. Op Tech Gmb. H Remote Control. Education. Security Thank you for your attention. Any Questions? Andreas Kietzmann Managing Director Net. Op Tech Gmb. H, Dornhofstrasse 18, D-63263 Neu-Isenburg Tel: +49 -6102 -83399 -0 http: //www. netop. com/de
- Slides: 49