NATIONAL CYBERSECURITY AWARENESS MONTH RANSOMWARE WHAT IS IT
NATIONAL CYBERSECURITY AWARENESS MONTH RANSOMWARE: WHAT IS IT, HOW TO AVOID IT AND HOW TO PROTECT YOUR
NATIONAL CYBERSECURITY AWARENESS MONTH AGENDA ▸ What is Ransomware ▸ What it does ▸ How it works ▸ Examples ▸ How to avoid Ransomware ▸ How to protect your data ▸ Discussion/Questions 2
NATIONAL CYBERSECURITY AWARENESS MONTH ABOUT US ▸ Arijana Sarkic ▸ Security Engineer ▸ Brian Markham ▸ AVP, Information Security and Compliance Services 3
NATIONAL CYBERSECURITY AWARENESS MONTH 4 WHAT IS RANSOMWARE? ▸ Ransomware is a specific type of malware that locks (encrypt) user files and will only unlock (decrypt) those files once a ransom is paid. ▸ Can have a devastating impact on an individual or an organization. ▸ Many types of Ransomware; rapidly evolving ▸ Profitable! (1 BTC = $613. 64 USD) ▸ First known Ransomware: (1989) AIDS Trojan: distributed via floppy to WHO AIDS conference attendees.
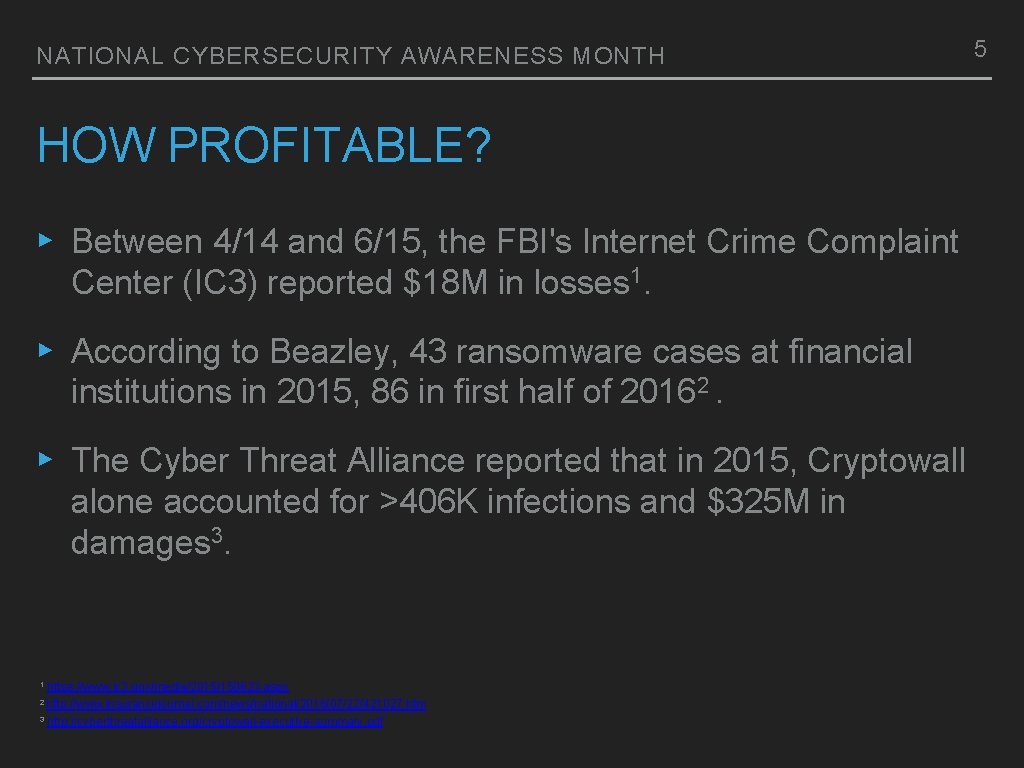
NATIONAL CYBERSECURITY AWARENESS MONTH HOW PROFITABLE? ▸ Between 4/14 and 6/15, the FBI's Internet Crime Complaint Center (IC 3) reported $18 M in losses 1. ▸ According to Beazley, 43 ransomware cases at financial institutions in 2015, 86 in first half of 20162. ▸ The Cyber Threat Alliance reported that in 2015, Cryptowall alone accounted for >406 K infections and $325 M in damages 3. 1 https: //www. ic 3. gov/media/2015/150623. aspx 2 http: //www. insurancejournal. com/news/national/2016/07/22/421027. htm 3 http: //cyberthreatalliance. org/cryptowall-executive-summary. pdf 5

6 Source: https: //blogs. sophos. com/2015/03/03/anatomy-of-a-ransomware-attack-cryptolocker-cryptowall-and-how-to-stay-safe-infographic/

NATIONAL CYBERSECURITY AWARENESS MONTH 7 WHAT DOES RANSOMWARE DO? ▸ Each different strain of Ransomware operates differently. ▸ Delivery methods: exploit kits, e-mail (malicious attachments), driveby attacks, malvertising. ▸ Connects to a remote server to obtain encryption key, encrypts specific files (jpg, doc, xls, pdf, mp 3, etc. ). ▸ Provides instructions and customer service so that victims can easily pay the ransom. ▸ Decryption has been observed to not always work, even after the ransom has been paid.
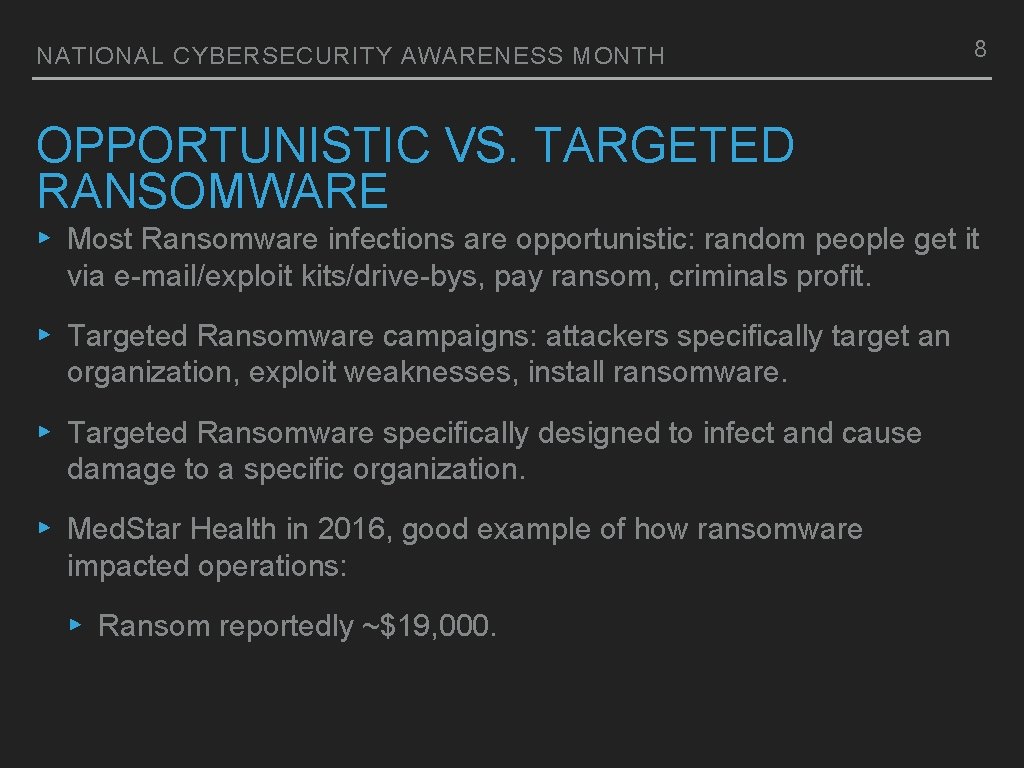
NATIONAL CYBERSECURITY AWARENESS MONTH 8 OPPORTUNISTIC VS. TARGETED RANSOMWARE ▸ Most Ransomware infections are opportunistic: random people get it via e-mail/exploit kits/drive-bys, pay ransom, criminals profit. ▸ Targeted Ransomware campaigns: attackers specifically target an organization, exploit weaknesses, install ransomware. ▸ Targeted Ransomware specifically designed to infect and cause damage to a specific organization. ▸ Med. Star Health in 2016, good example of how ransomware impacted operations: ▸ Ransom reportedly ~$19, 000.
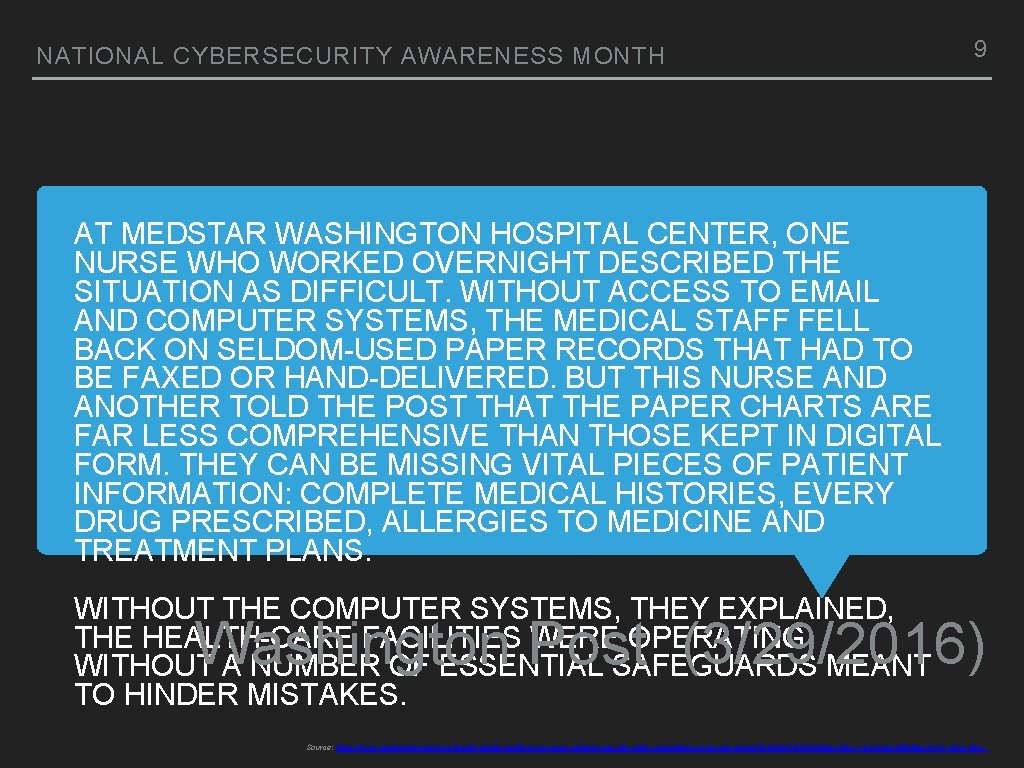
NATIONAL CYBERSECURITY AWARENESS MONTH 9 AT MEDSTAR WASHINGTON HOSPITAL CENTER, ONE NURSE WHO WORKED OVERNIGHT DESCRIBED THE SITUATION AS DIFFICULT. WITHOUT ACCESS TO EMAIL AND COMPUTER SYSTEMS, THE MEDICAL STAFF FELL BACK ON SELDOM-USED PAPER RECORDS THAT HAD TO BE FAXED OR HAND-DELIVERED. BUT THIS NURSE AND ANOTHER TOLD THE POST THAT THE PAPER CHARTS ARE FAR LESS COMPREHENSIVE THAN THOSE KEPT IN DIGITAL FORM. THEY CAN BE MISSING VITAL PIECES OF PATIENT INFORMATION: COMPLETE MEDICAL HISTORIES, EVERY DRUG PRESCRIBED, ALLERGIES TO MEDICINE AND TREATMENT PLANS. WITHOUT THE COMPUTER SYSTEMS, THEY EXPLAINED, THE HEALTH-CARE FACILITIES WERE OPERATING WITHOUT A NUMBER OF ESSENTIAL SAFEGUARDS MEANT TO HINDER MISTAKES. Washington Post (3/29/2016) Source: https: //www. washingtonpost. com/local/medstar-health-turns-away-patients-one-day-after-cyberattack-on-its-computers/2016/03/29/252626 ae-f 5 bc-11 e 5 -a 3 ce-f 06 b 5 ba 21 f 33_story. html
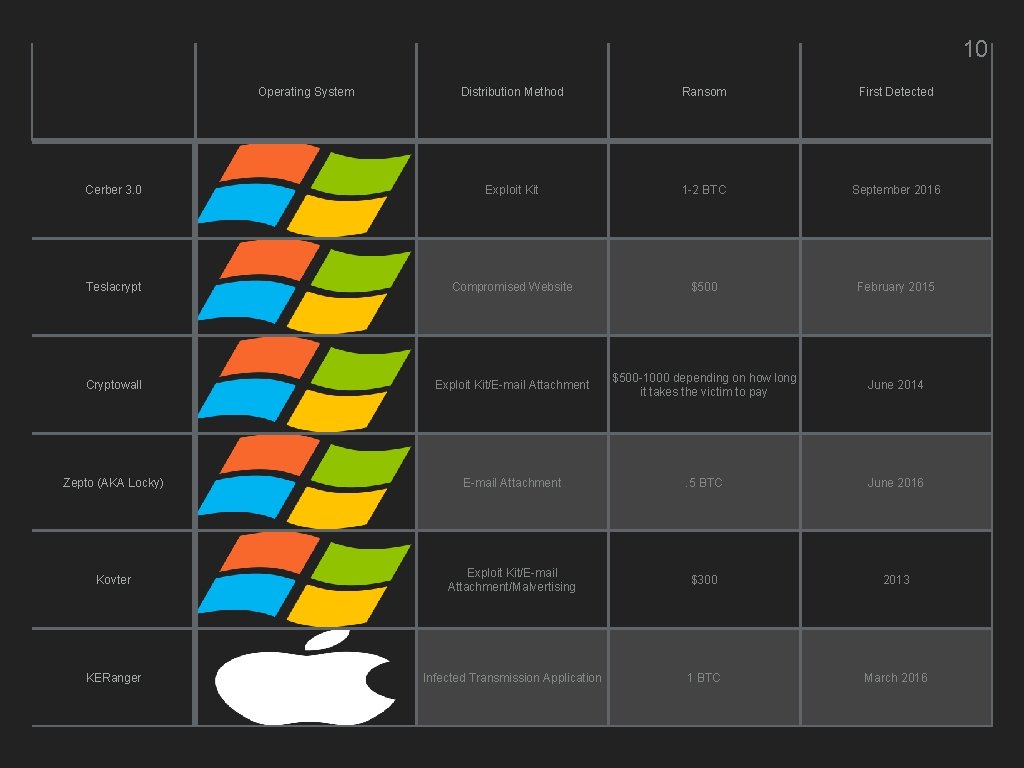
10 Operating System Distribution Method Ransom First Detected Cerber 3. 0 Exploit Kit 1 -2 BTC September 2016 Teslacrypt Compromised Website $500 February 2015 Cryptowall Exploit Kit/E-mail Attachment $500 -1000 depending on how long it takes the victim to pay June 2014 Zepto (AKA Locky) E-mail Attachment . 5 BTC June 2016 Kovter Exploit Kit/E-mail Attachment/Malvertising $300 2013 KERanger Infected Transmission Application 1 BTC March 2016

NATIONAL CYBERSECURITY AWARENESS MONTH ZCRYPTOR ▸ Encrypts and self-propagates ▸ Not spread through e-mail or exploit kits. ▸ Initial infection through fake software installer (like Adobe Flash) or a malicious Microsoft Office macro. ▸ Once on a system, the Ransomware behaves like a worm infecting other network stores. ▸ 1. 2 to 5 BTC for ransom 11
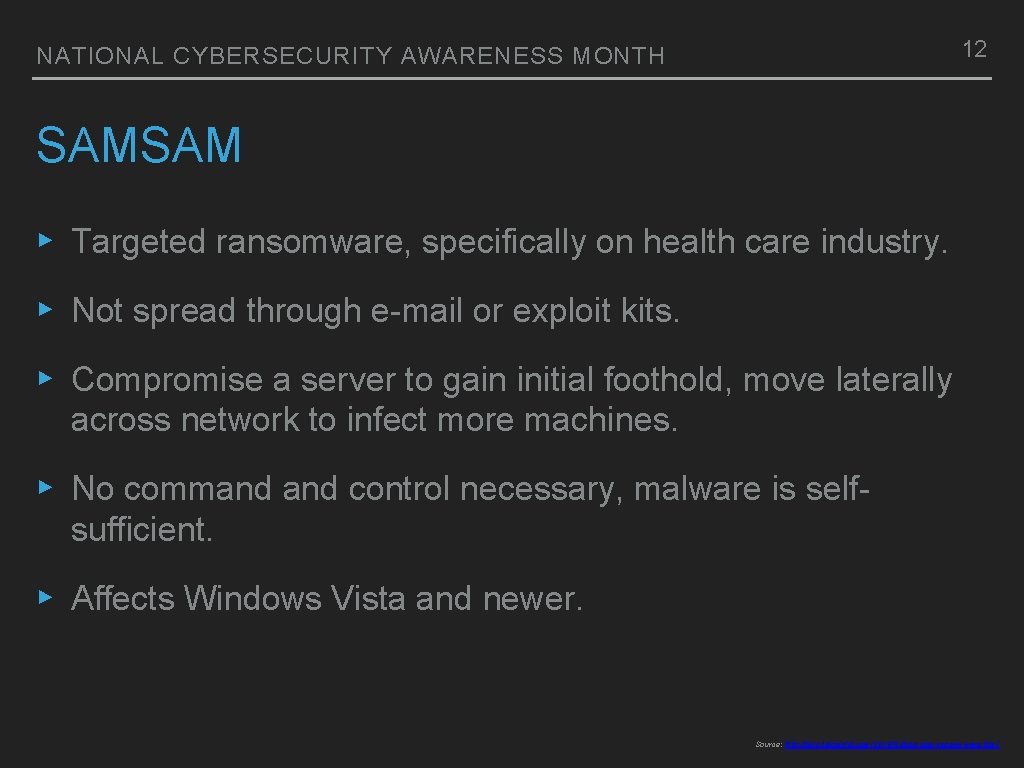
12 NATIONAL CYBERSECURITY AWARENESS MONTH SAMSAM ▸ Targeted ransomware, specifically on health care industry. ▸ Not spread through e-mail or exploit kits. ▸ Compromise a server to gain initial foothold, move laterally across network to infect more machines. ▸ No command control necessary, malware is selfsufficient. ▸ Affects Windows Vista and newer. Source: http: //blog. talosintel. com/2016/03/samsam-ransomware. html
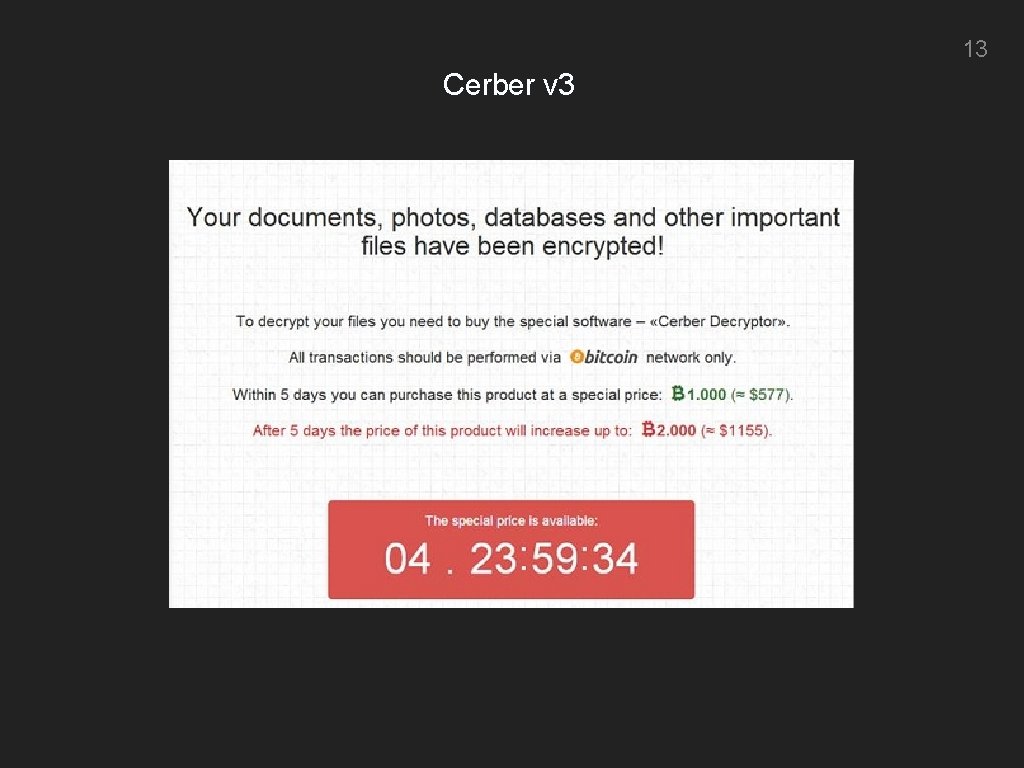
13 Cerber v 3
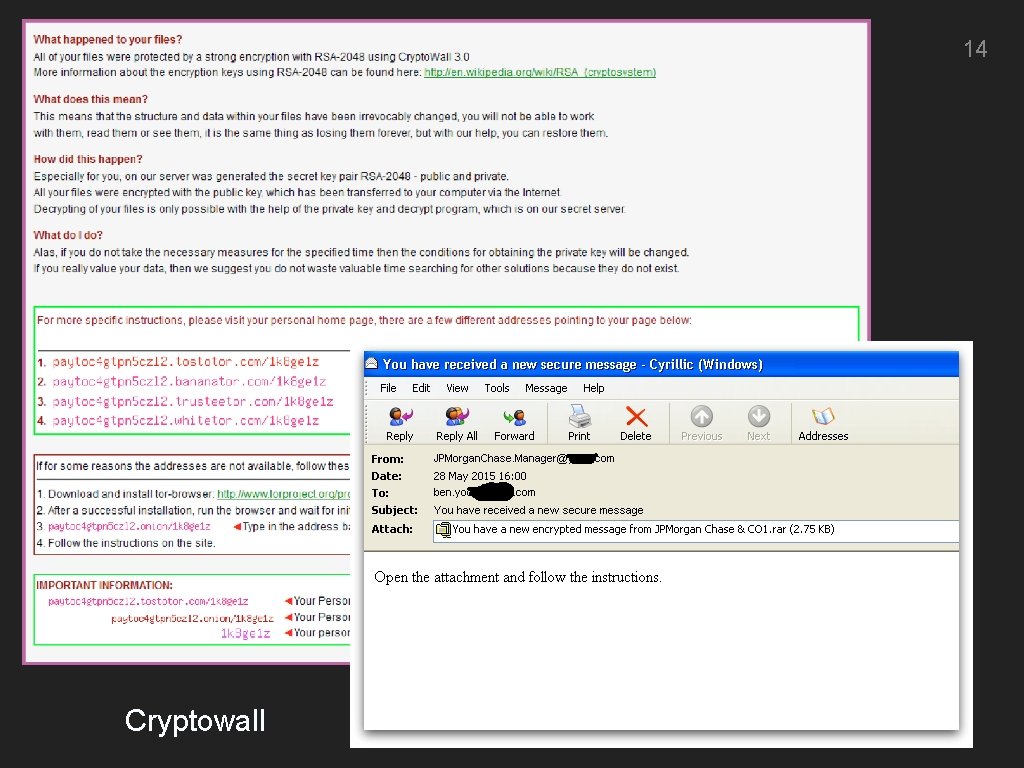
14 Cryptowall
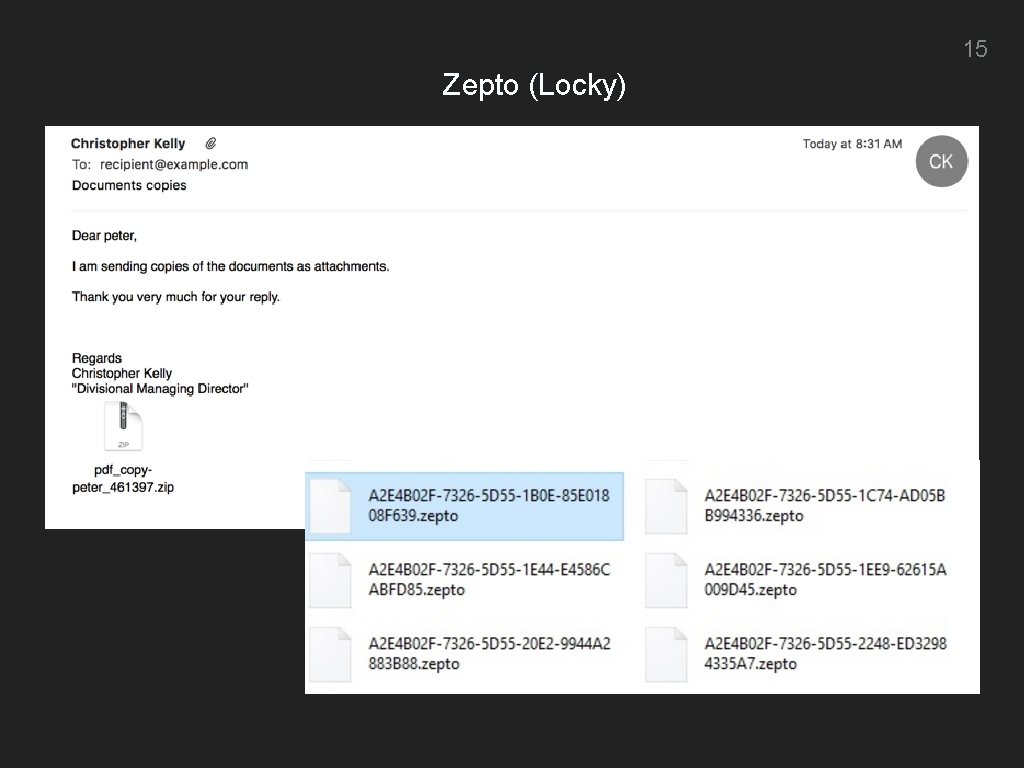
15 Zepto (Locky)
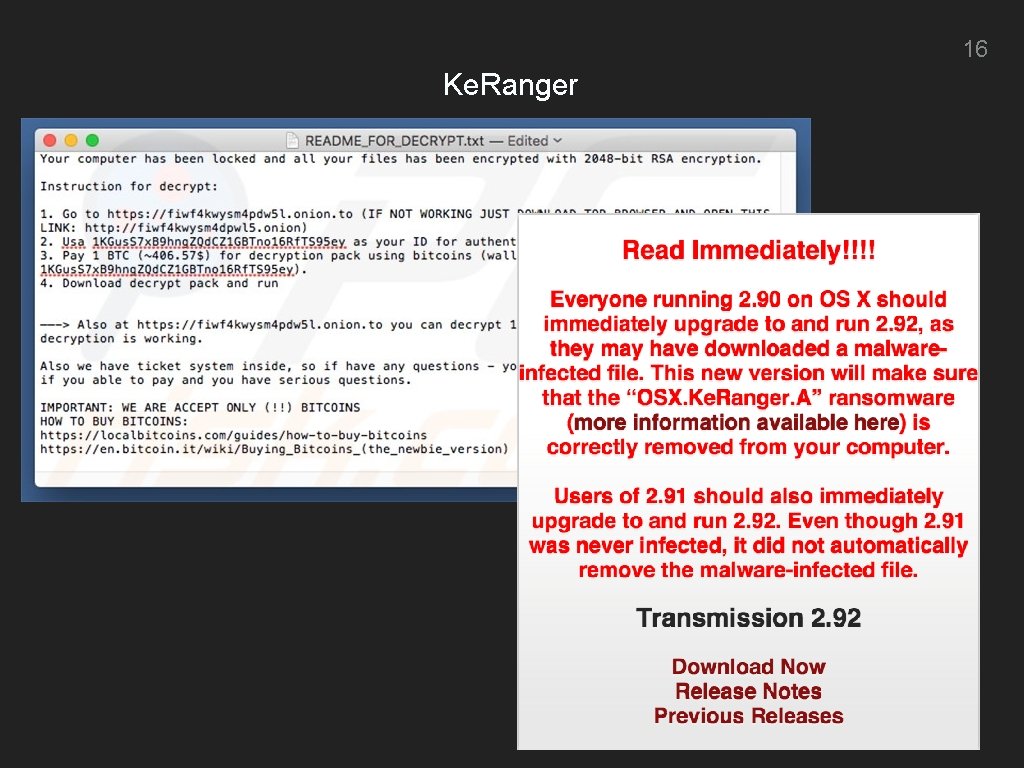
16 Ke. Ranger

NATIONAL CYBERSECURITY AWARENESS MONTH 17 HOW TO AVOID RANSOMWARE 1. Back up your files (store backups offline). 2. Employ practices that reduce your chances of getting ransomware on your computer.
NATIONAL CYBERSECURITY AWARENESS MONTH HOW TO PROTECT YOUR DATA ▸ Back up your files! ▸ Disconnect removable storage when not in use. ▸ Many options: ▸ Removable storage (USB); ▸ mac. OS Time Machine to external drive; ▸ Windows 10 File History to external drive; and ▸ Third-Party services (Backblaze, Crash Plan). 18
NATIONAL CYBERSECURITY AWARENESS MONTH HOW TO AVOID RANSOMWARE ▸ Many of the same tactics used to avoid malware. ▸ Be conscious of what you download: ▸ Torrents; and ▸ Untrustworthy software. ▸ E-mail attachments. ▸ Malicious Websites. 19
NATIONAL CYBERSECURITY AWARENESS MONTH HOW TO AVOID RANSOMWARE ▸ Do not enable macros in Microsoft Office. ▸ Apply updates to OS, browser, web plug-ins. ▸ Use Symantec Endpoint Protection (known malware protection): ▸ Free download from it. gwu. edu. ▸ Ransomwhere? by Patrick Wardle (objective-see. com) for mac. OS. 20

NATIONAL CYBERSECURITY AWARENESS MONTH SHOULD I PAY THE RANSOM? ▸ NO ▸ Paying the ransom: ▸ Tells attackers that the campaign is working; ▸ Incentivizes future Ransomware campaigns; and ▸ Leads to more/better Ransomware over time. 21
22 DISCUSSIO N/QUESTIO
- Slides: 22