NAT Traversal for Vo IP AiChun Pang Graduate
![Flavors of NAT [1/3] Static NAT n n Requires the same number of globally Flavors of NAT [1/3] Static NAT n n Requires the same number of globally](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-7.jpg)
![Flavors of NAT [2/3] Dynamic NAT n n Collect the public IP addresses into Flavors of NAT [2/3] Dynamic NAT n n Collect the public IP addresses into](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-8.jpg)
![Flavors of NAT [3/3] NAPT (Network Address and Port Translation) n A special case Flavors of NAT [3/3] NAPT (Network Address and Port Translation) n A special case](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-9.jpg)
![Restricted Cone NAT [1/2] n n n Client sends a packet to public address Restricted Cone NAT [1/2] n n n Client sends a packet to public address](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-12.jpg)
![Restricted Cone NAT [2/2] n n n Client sends another packet to public address Restricted Cone NAT [2/2] n n n Client sends another packet to public address](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-13.jpg)
![Two Distinct Cases – NAT Deployment [1/2] Case I : SIP Provider is the Two Distinct Cases – NAT Deployment [1/2] Case I : SIP Provider is the](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-19.jpg)
![Two Distinct Cases – NAT Deployment [2/2] Case II : SIP Provider is NOT Two Distinct Cases – NAT Deployment [2/2] Case II : SIP Provider is NOT](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-20.jpg)
![Solution for Case I – ALG [1/2] Separate Application Layer NAT from IP Layer Solution for Case I – ALG [1/2] Separate Application Layer NAT from IP Layer](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-21.jpg)
![Solution for Case I – ALG [2/2] INVITE Binding Request: To give a private Solution for Case I – ALG [2/2] INVITE Binding Request: To give a private](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-22.jpg)
![SIP Extension to NAT Friendly [2/2] Server Behavior n Examines the Via header field SIP Extension to NAT Friendly [2/2] Server Behavior n Examines the Via header field](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-25.jpg)
![Example [1/2] Client A: 10. 1. 1. 1 Proxy B: 68. 44. 10. 3 Example [1/2] Client A: 10. 1. 1. 1 Proxy B: 68. 44. 10. 3](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-26.jpg)
![Example [2/2] l l Server B receives the response SIP/2. 0 200 OK Via: Example [2/2] l l Server B receives the response SIP/2. 0 200 OK Via:](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-27.jpg)
![UPn. P [1/2] n n Universal Plug and Play It is being pushed by UPn. P [1/2] n n Universal Plug and Play It is being pushed by](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-28.jpg)
![UPn. P [2/2] n A: Private Network n n n UPn. P-aware Internet gateway UPn. P [2/2] n A: Private Network n n n UPn. P-aware Internet gateway](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-29.jpg)

![STUN Message [1/3] n n n TLV (type-length-value) Start with a STUN header, followed STUN Message [1/3] n n n TLV (type-length-value) Start with a STUN header, followed](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-34.jpg)
![STUN Message [2/3] STUN Header STUN Payload (can have none to many blocks) Message STUN Message [2/3] STUN Header STUN Payload (can have none to many blocks) Message](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-35.jpg)
![STUN Message [3/3] STUN Header STUN Payload (can have none to many blocks) Attribute STUN Message [3/3] STUN Header STUN Payload (can have none to many blocks) Attribute](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-36.jpg)
![Automatic Detection of NAT Environment [1/2] STUN Client Environment Port 1 STUN Server Port Automatic Detection of NAT Environment [1/2] STUN Client Environment Port 1 STUN Server Port](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-37.jpg)
![Automatic Detection of NAT Environment [2/2] Test I UDP Blocked No Resp? Yes Same Automatic Detection of NAT Environment [2/2] Test I UDP Blocked No Resp? Yes Same](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-38.jpg)
- Slides: 55
NAT Traversal for Vo. IP Ai-Chun Pang Graduate Institute of Networking and Multimedia Dept. of Comp. Sci. and Info. Engr. National Taiwan University 1
References n n n “SIP, NAT and Firewalls”, Fredrik Thernelius Baruch Sterman and David Schwartz, “NAT Traversal in SIP”, Deltathree “STUN – Simple Traversal of UDP Through Network Address Translators”, RFC 3489, IETF “An Extension to the SIP for Symmetric Response Routing”, RFC 3581, IETF “TURN – Traversal Using Relay NAT”, Internet Draft, IETF 2
Outline n n n Introduction Problems of NAT Traversal for Vo. IP Possible Solutions for Vo. IP over NAT 3
What is NAT? n n NAT - Network Address Translation Converts Network Address (and Port) between private and public realm Works on IP layer Transparent to Upper-layer Applications 4
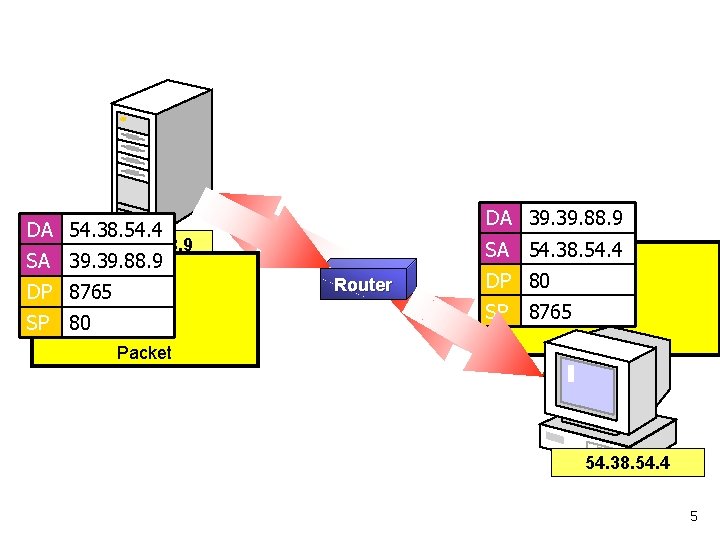
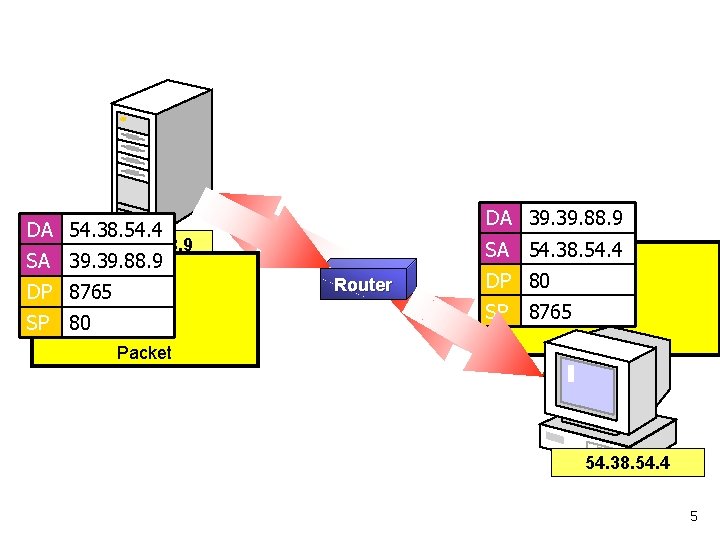
DA 39. 88. 9 DA 54. 38. 54. 4 39. 88. 9 SA 54. 38. 54. 4 SA 39. 88. 9 Router DP 8765 DP 80 SP SP 80 Packet 8765 Packet 54. 38. 54. 4 5
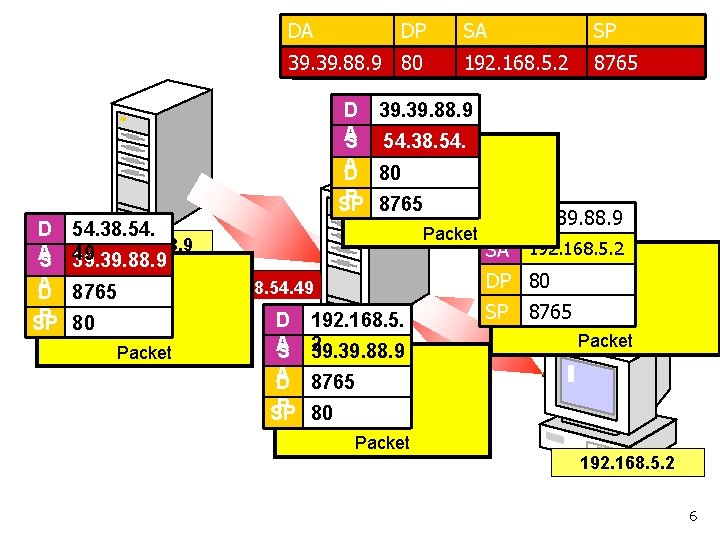
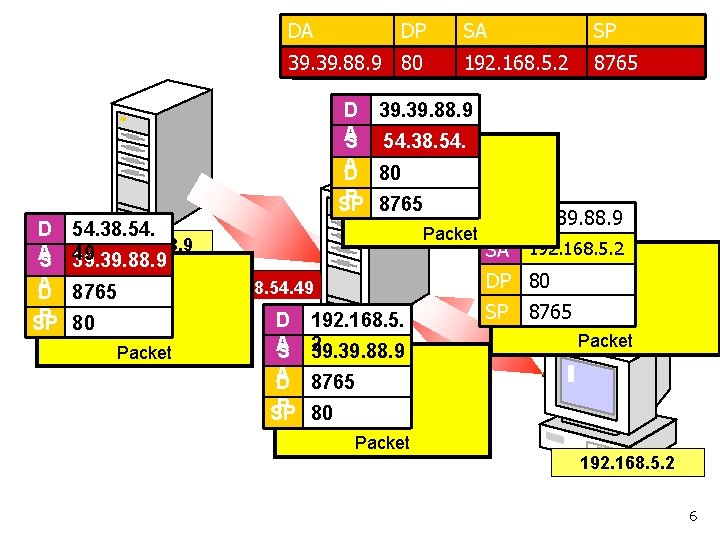
DA DA DA DP DP DP SA SA 39. 39. 88. 9 80 80 SP SP 192. 168. 5. 2 8765 D 39. 88. 9 A S 54. 38. 54. A D 80 49 P 8765 SP D 54. 38. 54. 39. 88. 9 A 49 S 39. 88. 9 A D 8765 P 80 SP Packet DA 39. 88. 9 SA 192. 168. 5. 2 DP 80 54. 38. 54. 49 D 192. 168. 5. A S 2 39. 88. 9 A D 8765 SP 8765 Packet P 80 SP Packet 192. 168. 5. 2 6
![Flavors of NAT 13 Static NAT n n Requires the same number of globally Flavors of NAT [1/3] Static NAT n n Requires the same number of globally](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-7.jpg)
Flavors of NAT [1/3] Static NAT n n Requires the same number of globally IP addresses as that of hosts in the private environment Maps between internal IP addresses and external addresses is set manually n This mapping intends to stay for a long period of time 7
![Flavors of NAT 23 Dynamic NAT n n Collect the public IP addresses into Flavors of NAT [2/3] Dynamic NAT n n Collect the public IP addresses into](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-8.jpg)
Flavors of NAT [2/3] Dynamic NAT n n Collect the public IP addresses into an IP address pool A host connecting to the outside network is allocated an external IP address from the address pool managed by NAT 8
![Flavors of NAT 33 NAPT Network Address and Port Translation n A special case Flavors of NAT [3/3] NAPT (Network Address and Port Translation) n A special case](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-9.jpg)
Flavors of NAT [3/3] NAPT (Network Address and Port Translation) n A special case of Dynamic NAT n n Use port numbers as the basis for the address translation Most commonly used 9
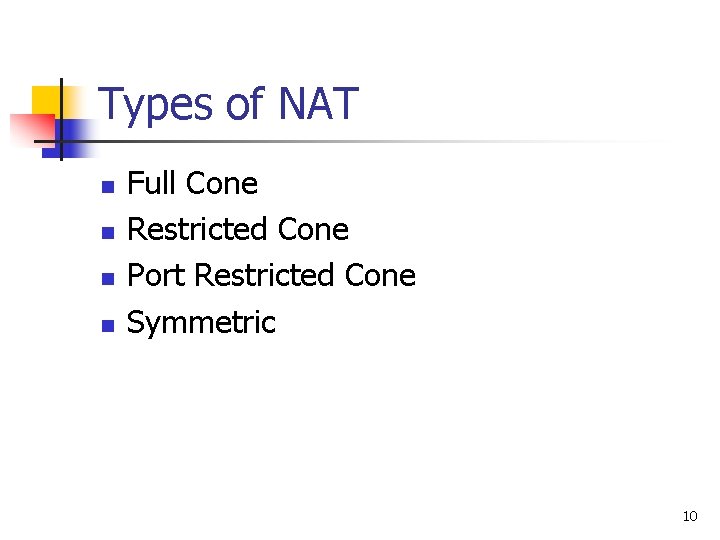
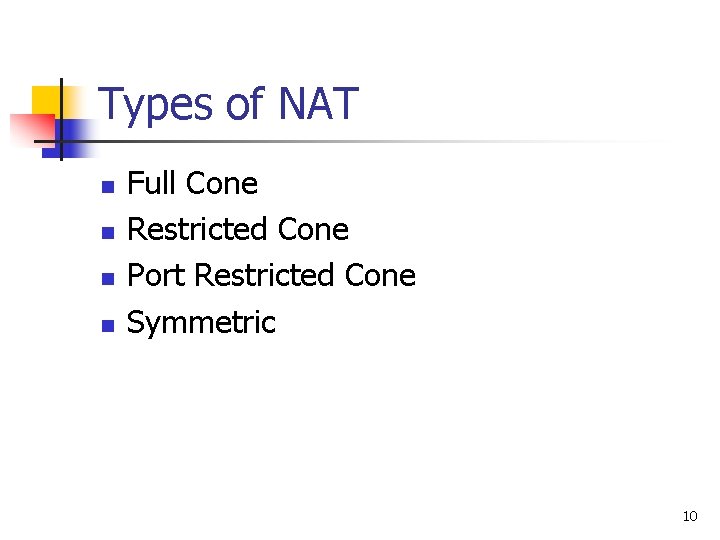
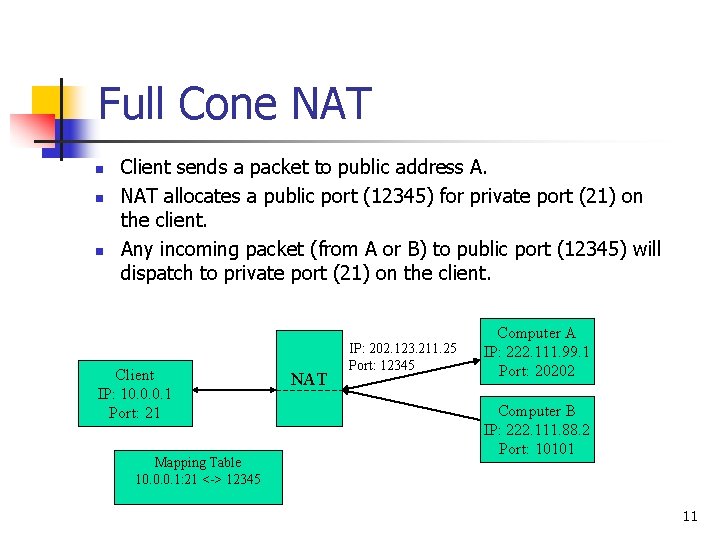
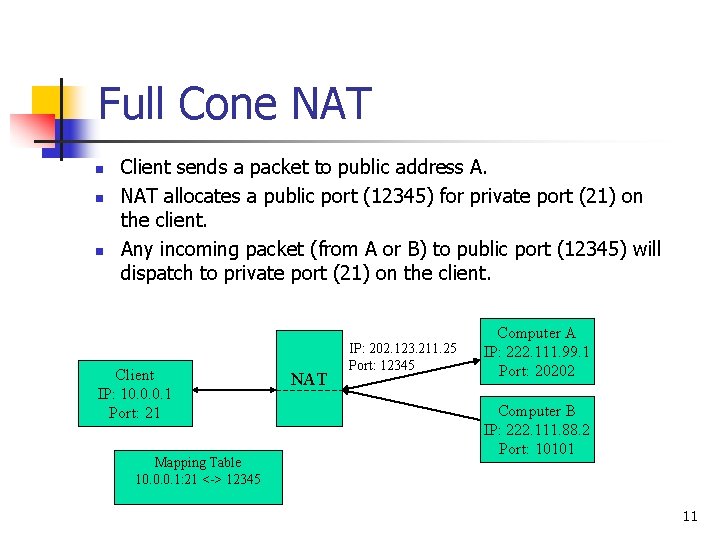
Types of NAT n n Full Cone Restricted Cone Port Restricted Cone Symmetric 10
Full Cone NAT n n n Client sends a packet to public address A. NAT allocates a public port (12345) for private port (21) on the client. Any incoming packet (from A or B) to public port (12345) will dispatch to private port (21) on the client. Client IP: 10. 0. 0. 1 Port: 21 Mapping Table 10. 0. 0. 1: 21 <-> 12345 NAT IP: 202. 123. 211. 25 Port: 12345 Computer A IP: 222. 111. 99. 1 Port: 20202 Computer B IP: 222. 111. 88. 2 Port: 10101 11
![Restricted Cone NAT 12 n n n Client sends a packet to public address Restricted Cone NAT [1/2] n n n Client sends a packet to public address](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-12.jpg)
Restricted Cone NAT [1/2] n n n Client sends a packet to public address A. NAT allocate a public port (12345) for private port (21) on the client. Only incoming packet from A to public port (12345) will dispatch to private port (21) on the client. Client IP: 10. 0. 0. 1 Port: 21 NAT Mapping Table 10. 0. 0. 1: 21 <-> 12345 (for A) IP: 202. 123. 211. 25 Port: 12345 Computer A IP: 222. 111. 99. 1 Port: 20202 Computer B IP: 222. 111. 88. 2 Port: 10101 12
![Restricted Cone NAT 22 n n n Client sends another packet to public address Restricted Cone NAT [2/2] n n n Client sends another packet to public address](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-13.jpg)
Restricted Cone NAT [2/2] n n n Client sends another packet to public address B. NAT will reuse allocated public port (12345) for private port (21) on the client. Incoming packet from B to public port (12345) will now dispatch to private port (21) on the client. Client IP: 10. 0. 0. 1 Port: 21 NAT Mapping Table 10. 0. 0. 1: 21 <-> 12345 (for A) 10. 0. 0. 1: 21 <-> 12345 (for B) IP: 202. 123. 211. 25 Port: 12345 Computer A IP: 222. 111. 99. 1 Port: 20202 Computer B IP: 222. 111. 88. 2 Port: 10101 13
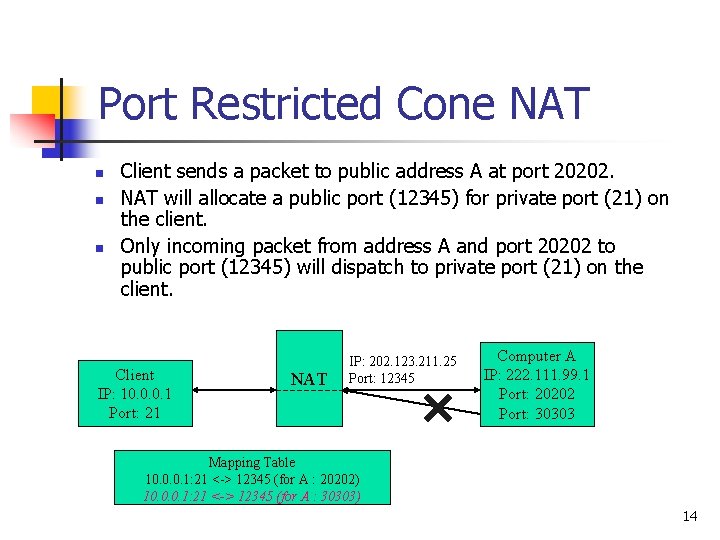
Port Restricted Cone NAT n n n Client sends a packet to public address A at port 20202. NAT will allocate a public port (12345) for private port (21) on the client. Only incoming packet from address A and port 20202 to public port (12345) will dispatch to private port (21) on the client. Client IP: 10. 0. 0. 1 Port: 21 NAT IP: 202. 123. 211. 25 Port: 12345 Computer A IP: 222. 111. 99. 1 Port: 20202 Port: 30303 Mapping Table 10. 0. 0. 1: 21 <-> 12345 (for A : 20202) 10. 0. 0. 1: 21 <-> 12345 (for A : 30303) 14
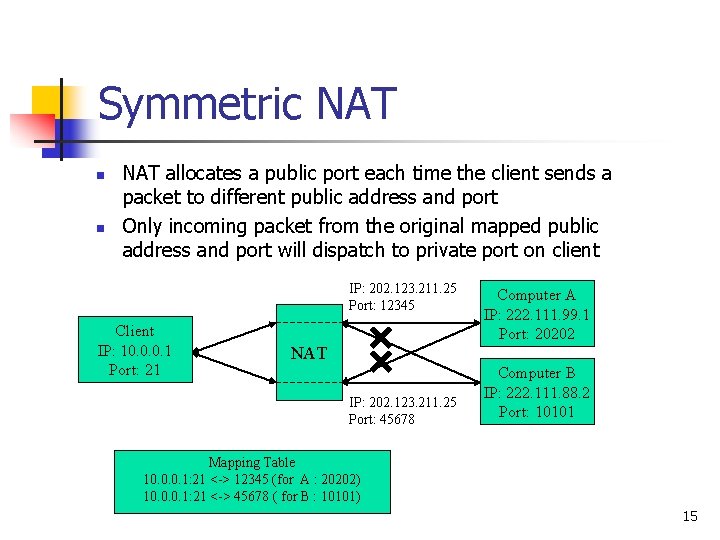
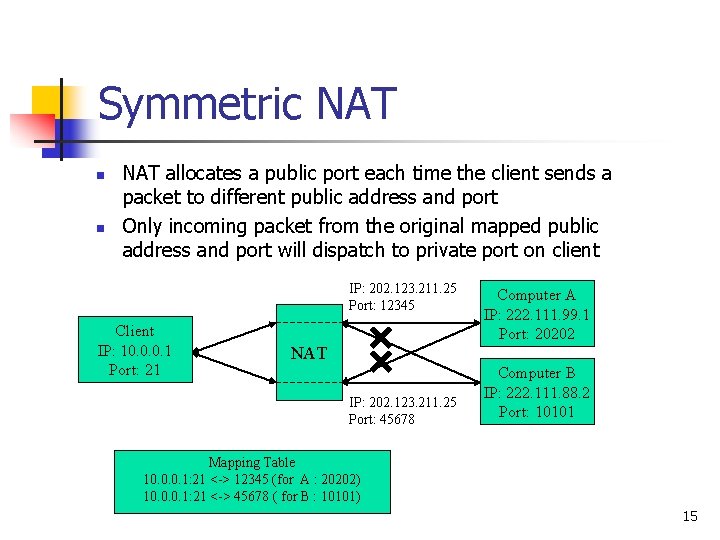
Symmetric NAT n n NAT allocates a public port each time the client sends a packet to different public address and port Only incoming packet from the original mapped public address and port will dispatch to private port on client IP: 202. 123. 211. 25 Port: 12345 Client IP: 10. 0. 0. 1 Port: 21 Computer A IP: 222. 111. 99. 1 Port: 20202 NAT IP: 202. 123. 211. 25 Port: 45678 Computer B IP: 222. 111. 88. 2 Port: 10101 Mapping Table 10. 0. 0. 1: 21 <-> 12345 (for A : 20202) 10. 0. 0. 1: 21 <-> 45678 ( for B : 10101) 15
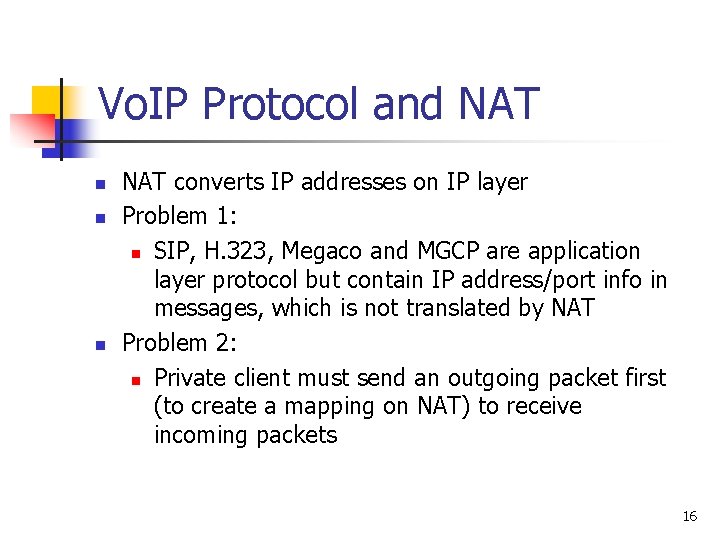
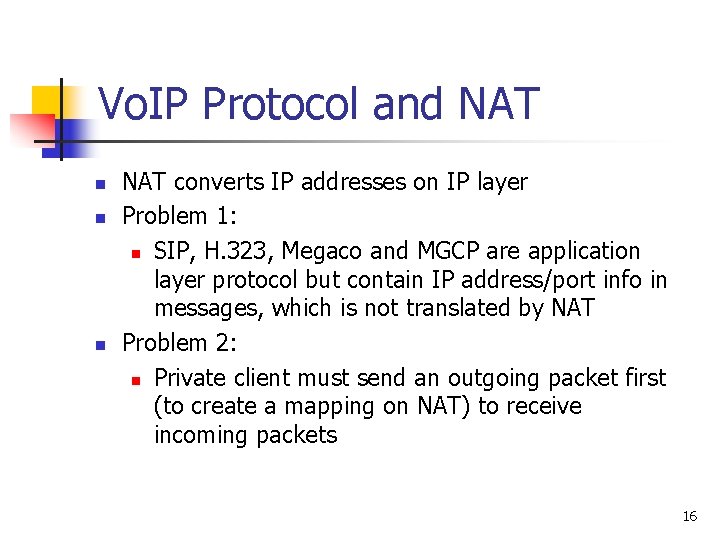
Vo. IP Protocol and NAT n n n NAT converts IP addresses on IP layer Problem 1: n SIP, H. 323, Megaco and MGCP are application layer protocol but contain IP address/port info in messages, which is not translated by NAT Problem 2: n Private client must send an outgoing packet first (to create a mapping on NAT) to receive incoming packets 16
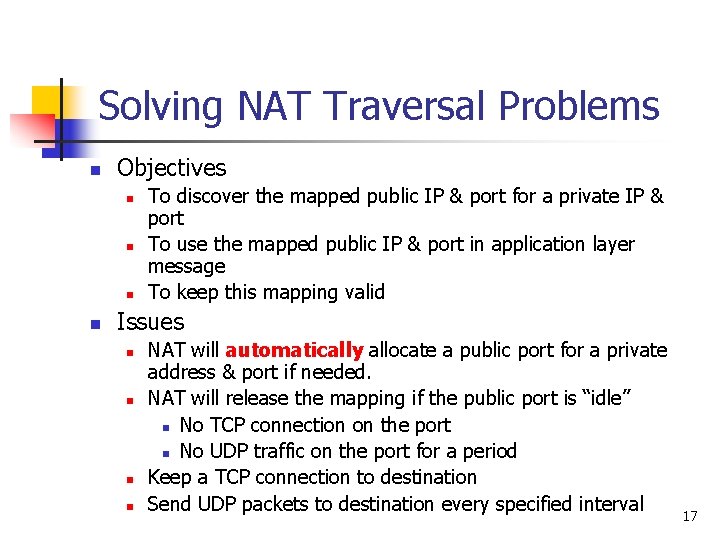
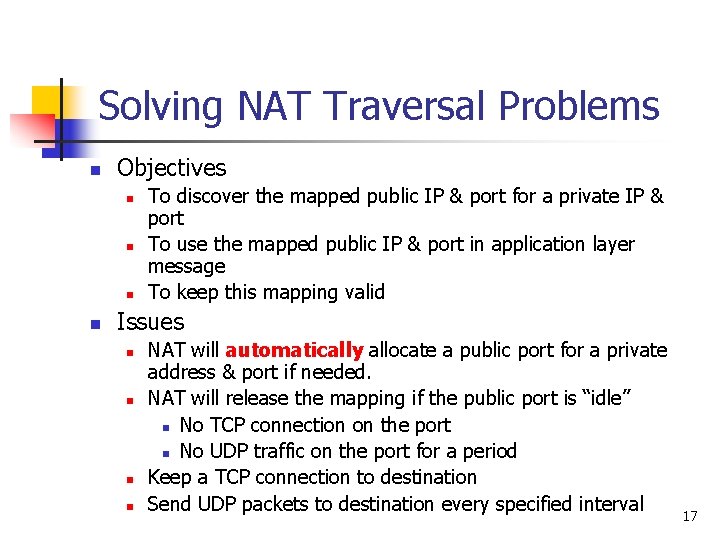
Solving NAT Traversal Problems n Objectives n n To discover the mapped public IP & port for a private IP & port To use the mapped public IP & port in application layer message To keep this mapping valid Issues n n NAT will automatically allocate a public port for a private address & port if needed. NAT will release the mapping if the public port is “idle” n No TCP connection on the port n No UDP traffic on the port for a period Keep a TCP connection to destination Send UDP packets to destination every specified interval 17
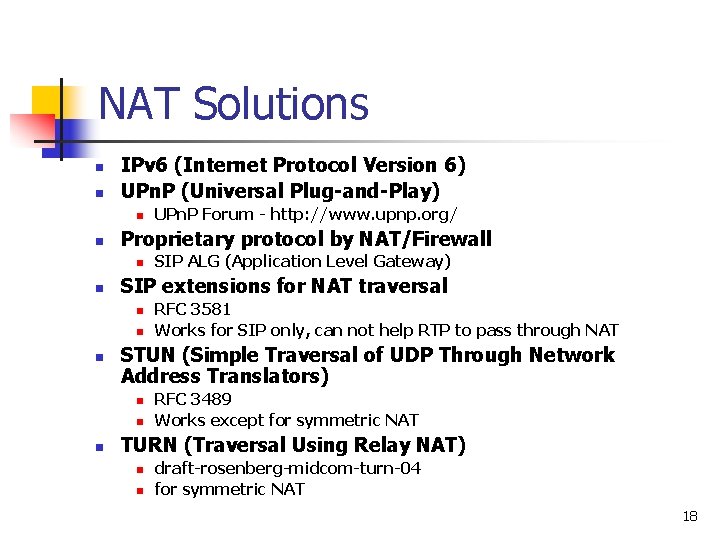
NAT Solutions n n IPv 6 (Internet Protocol Version 6) UPn. P (Universal Plug-and-Play) n n Proprietary protocol by NAT/Firewall n n n RFC 3581 Works for SIP only, can not help RTP to pass through NAT STUN (Simple Traversal of UDP Through Network Address Translators) n n n SIP ALG (Application Level Gateway) SIP extensions for NAT traversal n n UPn. P Forum - http: //www. upnp. org/ RFC 3489 Works except for symmetric NAT TURN (Traversal Using Relay NAT) n n draft-rosenberg-midcom-turn-04 for symmetric NAT 18
![Two Distinct Cases NAT Deployment 12 Case I SIP Provider is the Two Distinct Cases – NAT Deployment [1/2] Case I : SIP Provider is the](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-19.jpg)
Two Distinct Cases – NAT Deployment [1/2] Case I : SIP Provider is the IP Network Provider 19
![Two Distinct Cases NAT Deployment 22 Case II SIP Provider is NOT Two Distinct Cases – NAT Deployment [2/2] Case II : SIP Provider is NOT](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-20.jpg)
Two Distinct Cases – NAT Deployment [2/2] Case II : SIP Provider is NOT IP Network Provider 20
![Solution for Case I ALG 12 Separate Application Layer NAT from IP Layer Solution for Case I – ALG [1/2] Separate Application Layer NAT from IP Layer](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-21.jpg)
Solution for Case I – ALG [1/2] Separate Application Layer NAT from IP Layer NAT l Like MEGACO Decomposition Ø MG = Packet Filter Decomposed Firewall/NAT Proxy Server/ALG Ø MGC = Control Proxy Firewall/NAT Packet Filter Control l Advantages Ø Better scaling Ø Load balancing SIP RTP Ø Low cost 21
![Solution for Case I ALG 22 INVITE Binding Request To give a private Solution for Case I – ALG [2/2] INVITE Binding Request: To give a private](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-22.jpg)
Solution for Case I – ALG [2/2] INVITE Binding Request: To give a private address and obtain a public address Binding Release Open Hole (firewall) Close Hole (firewall) 200 OK n n n BINDING INVITE 200 OK OPEN ACK Firewall/NAT n BIND REQ Proxy n A control Protocol between application-layer NATs and IP-layer NATs Main Requirements PC n 22
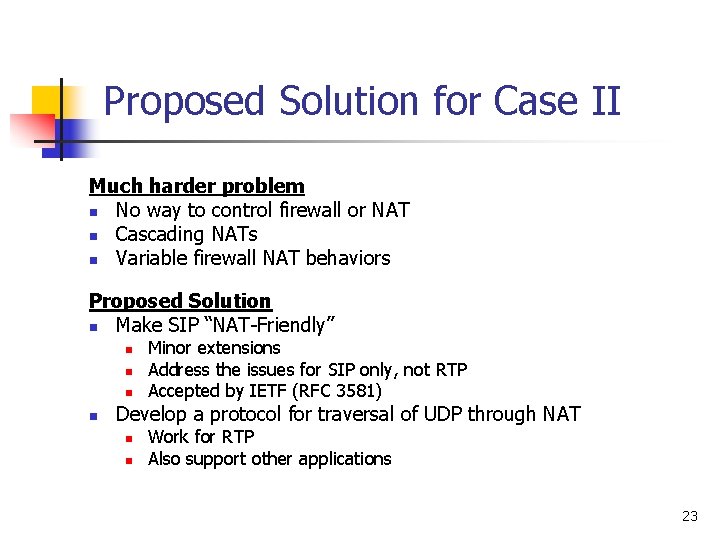
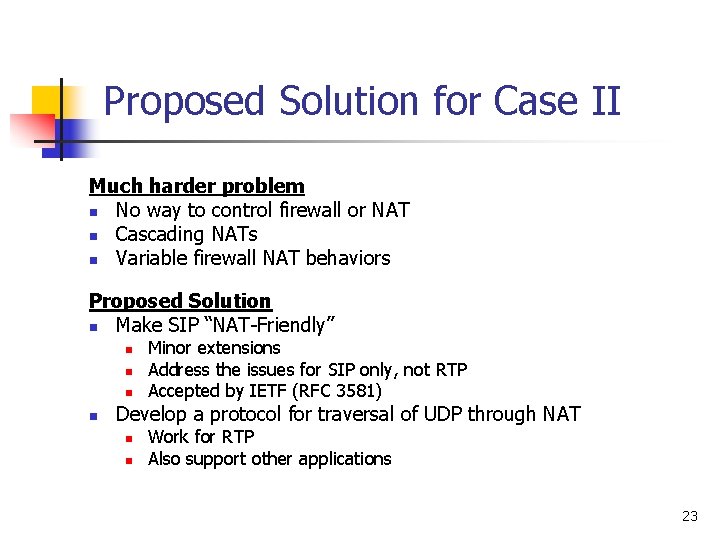
Proposed Solution for Case II Much harder problem n No way to control firewall or NAT n Cascading NATs n Variable firewall NAT behaviors Proposed Solution n Make SIP “NAT-Friendly” n n Minor extensions Address the issues for SIP only, not RTP Accepted by IETF (RFC 3581) Develop a protocol for traversal of UDP through NAT n n Work for RTP Also support other applications 23
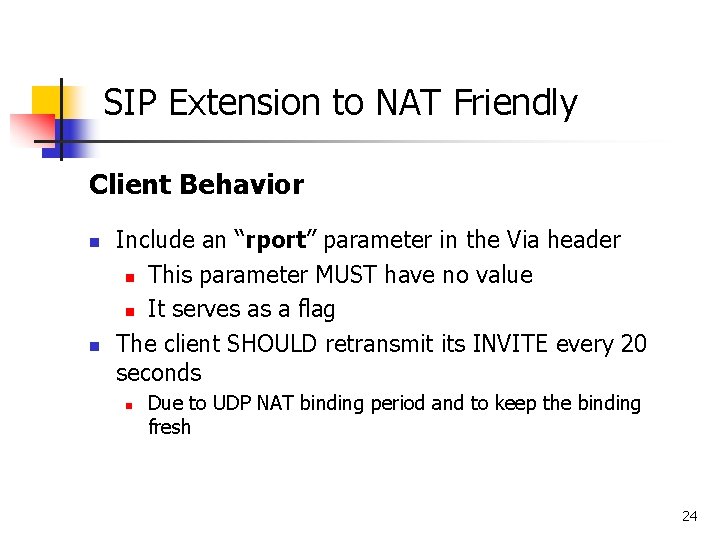
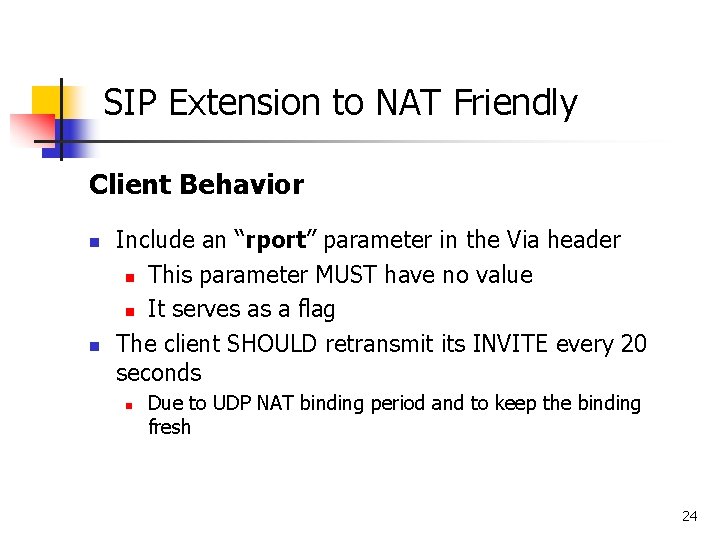
SIP Extension to NAT Friendly Client Behavior n n Include an “rport” parameter in the Via header n This parameter MUST have no value n It serves as a flag The client SHOULD retransmit its INVITE every 20 seconds n Due to UDP NAT binding period and to keep the binding fresh 24
![SIP Extension to NAT Friendly 22 Server Behavior n Examines the Via header field SIP Extension to NAT Friendly [2/2] Server Behavior n Examines the Via header field](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-25.jpg)
SIP Extension to NAT Friendly [2/2] Server Behavior n Examines the Via header field value of the request n n If it contains an “rport” parameter, n A “received” parameter n An “rport” parameter The response MUST be sent to the IP address listed in the “received” parameter, and the port in the “rport” parameter. 25
![Example 12 Client A 10 1 1 1 Proxy B 68 44 10 3 Example [1/2] Client A: 10. 1. 1. 1 Proxy B: 68. 44. 10. 3](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-26.jpg)
Example [1/2] Client A: 10. 1. 1. 1 Proxy B: 68. 44. 10. 3 NAT C: 68. 44. 20. 1 n n A issues request INVITE sip: user@domain SIP/2. 0 Via: SIP/2. 0/UDP 10. 1. 1. 1: 4540; rport A C (mapping port 9988) B INVITE sip: user@domain SIP/2. 0 Via: SIP/2. 0/UDP proxy. domain. com Via: SIP/2. 0/UDP 10. 1. 1. 1: 4540; received=68. 44. 20. 1; rport=9988; 26
![Example 22 l l Server B receives the response SIP2 0 200 OK Via Example [2/2] l l Server B receives the response SIP/2. 0 200 OK Via:](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-27.jpg)
Example [2/2] l l Server B receives the response SIP/2. 0 200 OK Via: SIP/2. 0/UDP proxy. domain. com Via: SIP/2. 0/UDP 10. 1. 1. 1: 4540; received=68. 44. 20. 1; rport=9988; B (68. 44. 10. 3: 5060) C (68. 44. 20. 1: 9988) A SIP/2. 0 200 OK Via: SIP/2. 0/UDP 10. 1. 1. 1: 4540; received=68. 44. 20. 1; rport=9988; 27
![UPn P 12 n n Universal Plug and Play It is being pushed by UPn. P [1/2] n n Universal Plug and Play It is being pushed by](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-28.jpg)
UPn. P [1/2] n n Universal Plug and Play It is being pushed by Microsoft n n n http: //www. upnp. org/ Windows® Messenger A UPn. P-aware client can ask the UPn. Penabled NAT how it would map a particular IP: port through UPn. P It will not work in the case of cascading NATs 28
![UPn P 22 n A Private Network n n n UPn Paware Internet gateway UPn. P [2/2] n A: Private Network n n n UPn. P-aware Internet gateway](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-29.jpg)
UPn. P [2/2] n A: Private Network n n n UPn. P-aware Internet gateway device The UPn. P-enabled NAT allows “A” to be aware of its external IP B: Public Internet n “B” and “A” can communicate with each other Private Network Public Internet A UPn. Penabled NAT B 29
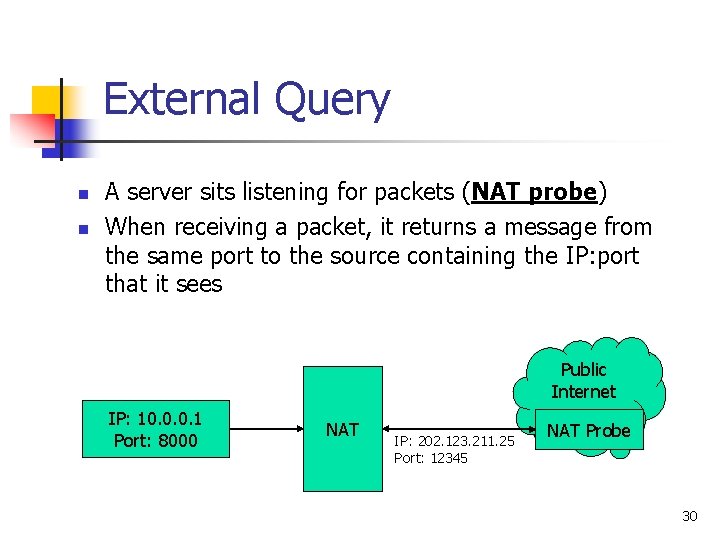
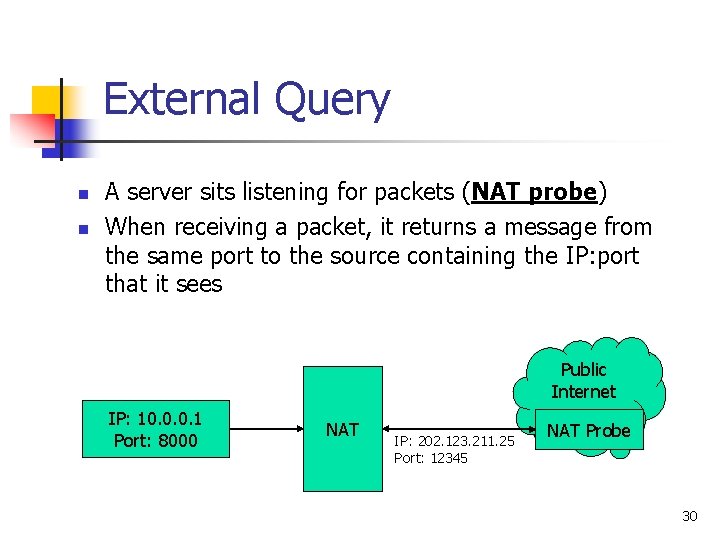
External Query n n A server sits listening for packets (NAT probe) When receiving a packet, it returns a message from the same port to the source containing the IP: port that it sees Public Internet IP: 10. 0. 0. 1 Port: 8000 NAT IP: 202. 123. 211. 25 Port: 12345 NAT Probe 30
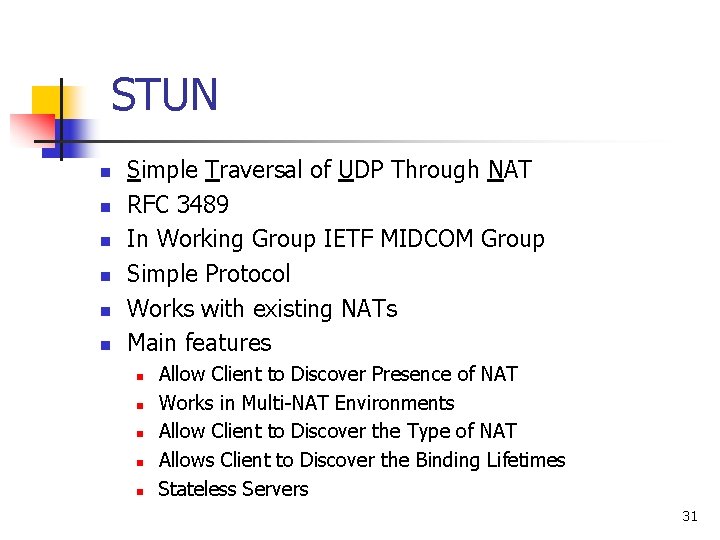
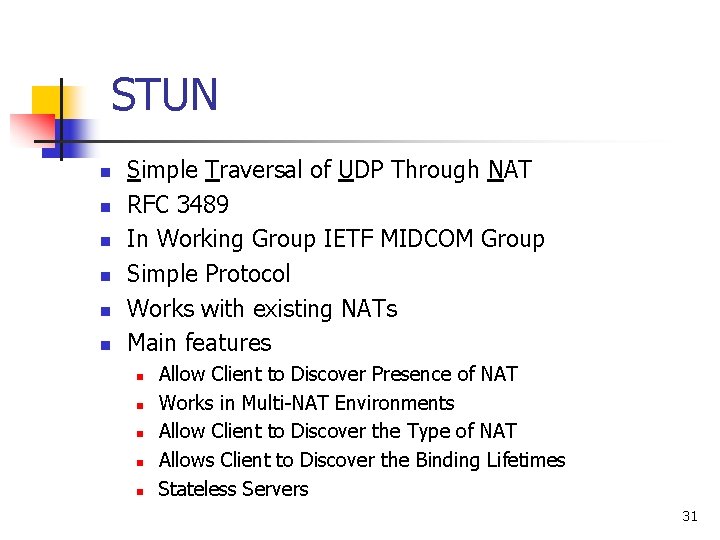
STUN n n n Simple Traversal of UDP Through NAT RFC 3489 In Working Group IETF MIDCOM Group Simple Protocol Works with existing NATs Main features n n n Allow Client to Discover Presence of NAT Works in Multi-NAT Environments Allow Client to Discover the Type of NAT Allows Client to Discover the Binding Lifetimes Stateless Servers 31

STUN Server n n Allow client to discover if it is behind a NAT, what type of NAT it is, and the public address & port NAT will use. A simple protocol, easy to implement, little load Client wants to receive packet at port 5060 Send a query to STUN server from port 5060 Client IP: 10. 0. 0. 1 Port: 5060 NAT STUN Server receives packet from 202. 123. 211. 25 port 12345 IP: 202. 123. 211. 25 Port: 12345 STUN Server IP: 222. 111. 99. 1 Port: 20202 STUN Server send a response packet to client. Tell him his public address is 202. 123. 211. 25 port 12345 32
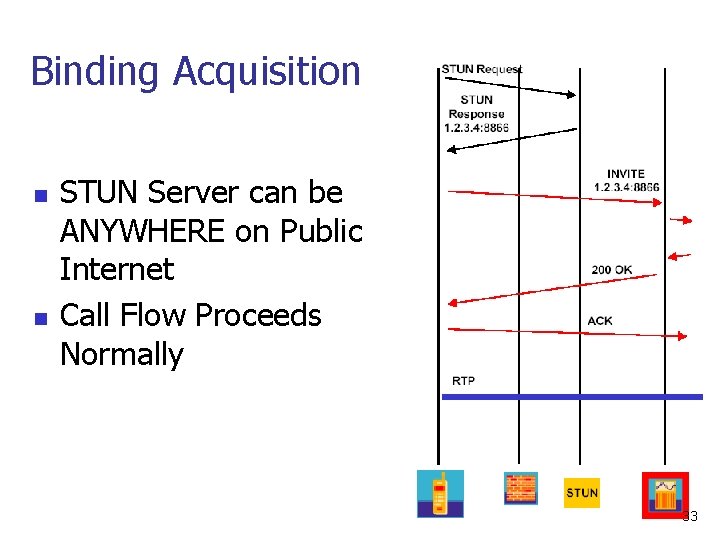
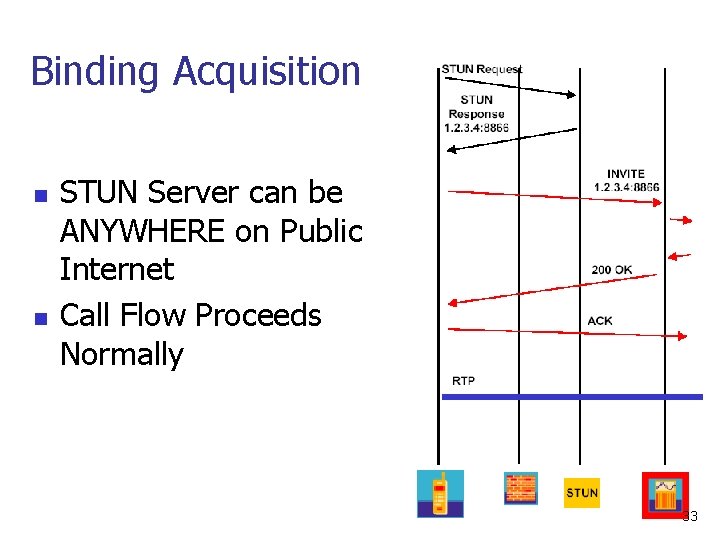
Binding Acquisition n n STUN Server can be ANYWHERE on Public Internet Call Flow Proceeds Normally 33
![STUN Message 13 n n n TLV typelengthvalue Start with a STUN header followed STUN Message [1/3] n n n TLV (type-length-value) Start with a STUN header, followed](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-34.jpg)
STUN Message [1/3] n n n TLV (type-length-value) Start with a STUN header, followed by a STUN payload (a series of STUN attributes depending on the message type) Format STUN Header STUN Payload (can have none to many blocks) 34
![STUN Message 23 STUN Header STUN Payload can have none to many blocks Message STUN Message [2/3] STUN Header STUN Payload (can have none to many blocks) Message](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-35.jpg)
STUN Message [2/3] STUN Header STUN Payload (can have none to many blocks) Message Type (16 bits) Message Length (16 bits) Transaction ID (128 bits) Message Types 0 x 0001: Binding Request 0 x 0111: Binding Error Response 0 x 0101: Binding Response 0 x 0002: Shared Secret Request 0 x 0102: Shared Secret Response 0 x 0112: Shared Secret Error Response 35
![STUN Message 33 STUN Header STUN Payload can have none to many blocks Attribute STUN Message [3/3] STUN Header STUN Payload (can have none to many blocks) Attribute](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-36.jpg)
STUN Message [3/3] STUN Header STUN Payload (can have none to many blocks) Attribute Type (16 bits) Attribute Length (16 bits) Attribute Value (Variable length) Attribute Types 0 x 0001: MAPPED-ADDRESS 0 x 0003: CHANGE-REQUEST 0 x 0005: CHANGED-ADDRESS 0 x 0007: PASSWORD 0 x 0009: ERROR-CODE 0 x 000 b: REFLECTED-FROM 0 x 0002: RESPONSE-ADDRESS 0 x 0004: SOURCE-ADDRESS 0 x 0006: USERNAME 0 x 0008: MESSAGE-INTEGRITY 0 x 000 a: UNKNOWN-ATTRIBUTES 36
![Automatic Detection of NAT Environment 12 STUN Client Environment Port 1 STUN Server Port Automatic Detection of NAT Environment [1/2] STUN Client Environment Port 1 STUN Server Port](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-37.jpg)
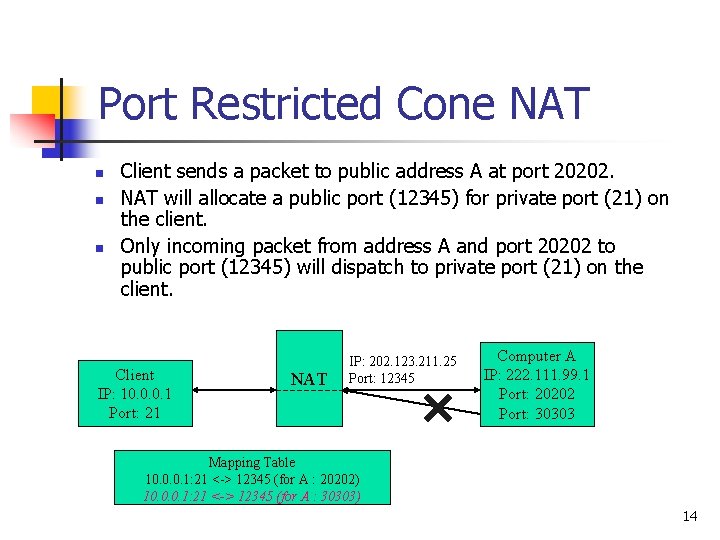
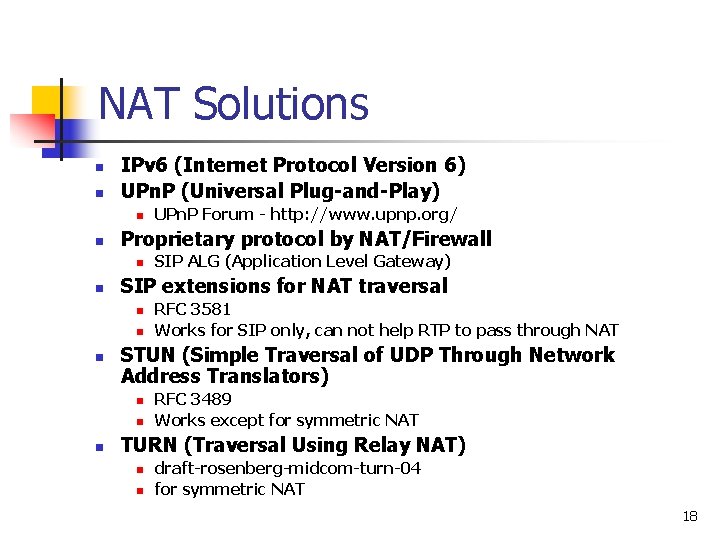
Automatic Detection of NAT Environment [1/2] STUN Client Environment Port 1 STUN Server Port 2 IP 1 Test I II IV Port 2 STUN Server Port 1 IP 2 37
![Automatic Detection of NAT Environment 22 Test I UDP Blocked No Resp Yes Same Automatic Detection of NAT Environment [2/2] Test I UDP Blocked No Resp? Yes Same](https://slidetodoc.com/presentation_image_h/27fc6159cbc7fecfd4a88fd4c64f5968/image-38.jpg)
Automatic Detection of NAT Environment [2/2] Test I UDP Blocked No Resp? Yes Same Yes IP and Port as original? No Test II Symmetric NAT No Same IP and Port as Test I? Test III Yes Test IV Resp? Yes Restricted NAT No Resp? Yes Full Cone NAT Test II Resp? No Sym UDP Firewall Yes Open Internet No Port Restricted NAT 38
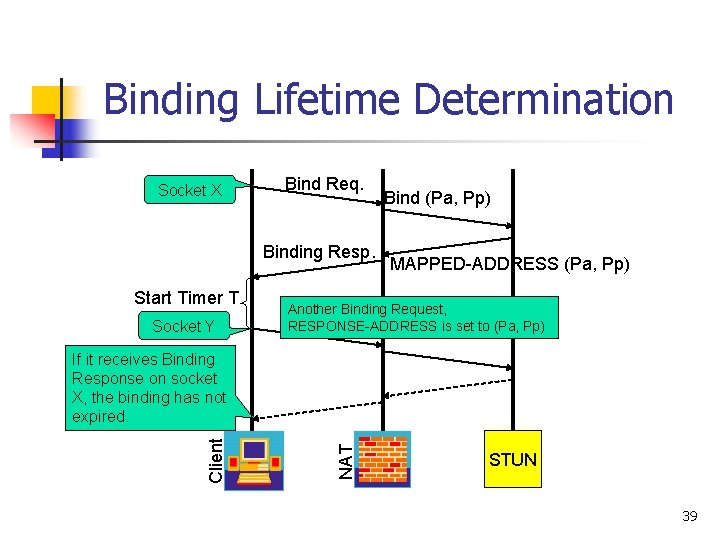
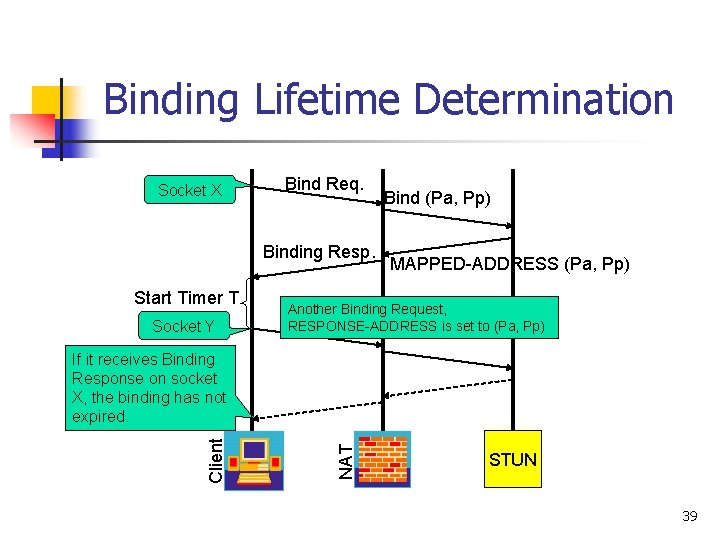
Binding Lifetime Determination Socket X Bind Req. Binding Resp. Start Timer T Socket Y Bind (Pa, Pp) MAPPED-ADDRESS (Pa, Pp) Another Binding Request, RESPONSE-ADDRESS is set to (Pa, Pp) NAT Client If it receives Binding Response on socket X, the binding has not expired. STUN 39
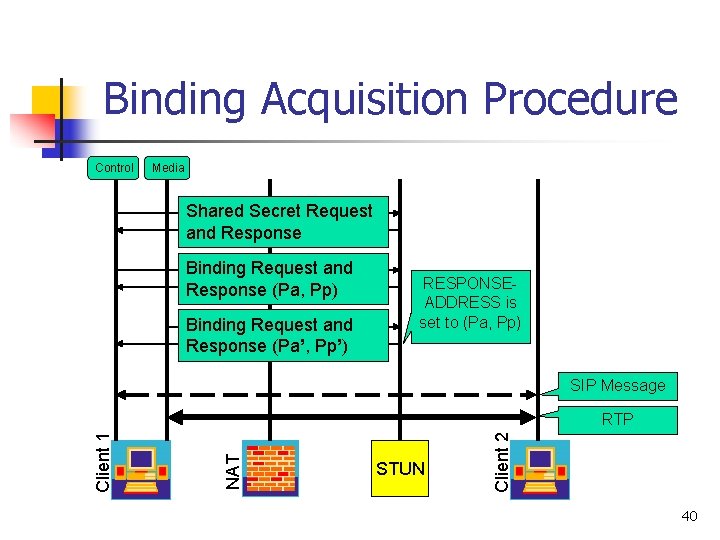
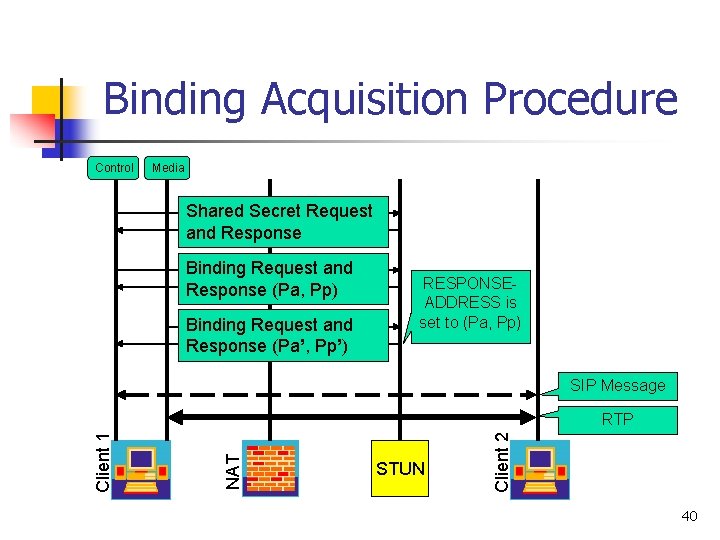
Binding Acquisition Procedure Control Media Shared Secret Request and Response Binding Request and Response (Pa, Pp) Binding Request and Response (Pa’, Pp’) RESPONSEADDRESS is set to (Pa, Pp) SIP Message STUN Client 2 NAT Client 1 RTP 40
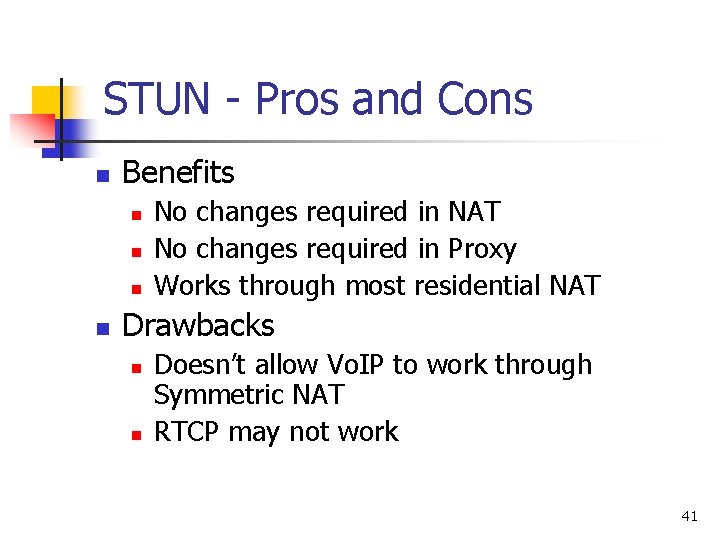
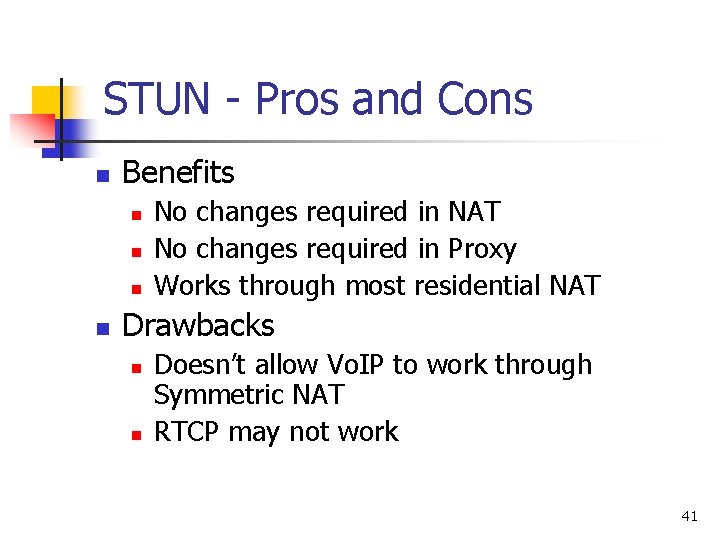
STUN - Pros and Cons n Benefits n n No changes required in NAT No changes required in Proxy Works through most residential NAT Drawbacks n n Doesn’t allow Vo. IP to work through Symmetric NAT RTCP may not work 41
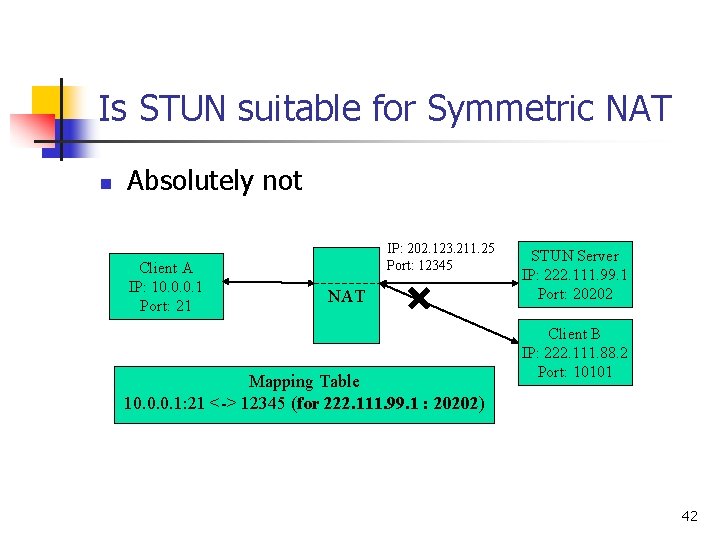
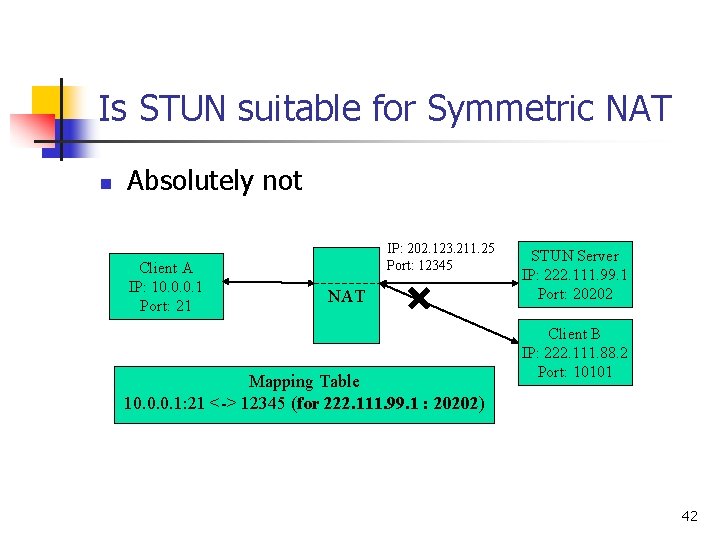
Is STUN suitable for Symmetric NAT n Absolutely not Client A IP: 10. 0. 0. 1 Port: 21 IP: 202. 123. 211. 25 Port: 12345 NAT Mapping Table 10. 0. 0. 1: 21 <-> 12345 (for 222. 111. 99. 1 : 20202) STUN Server IP: 222. 111. 99. 1 Port: 20202 Client B IP: 222. 111. 88. 2 Port: 10101 42
Solutions for Symmetric NATs n n Connection Oriented Media RTP-Relay 43
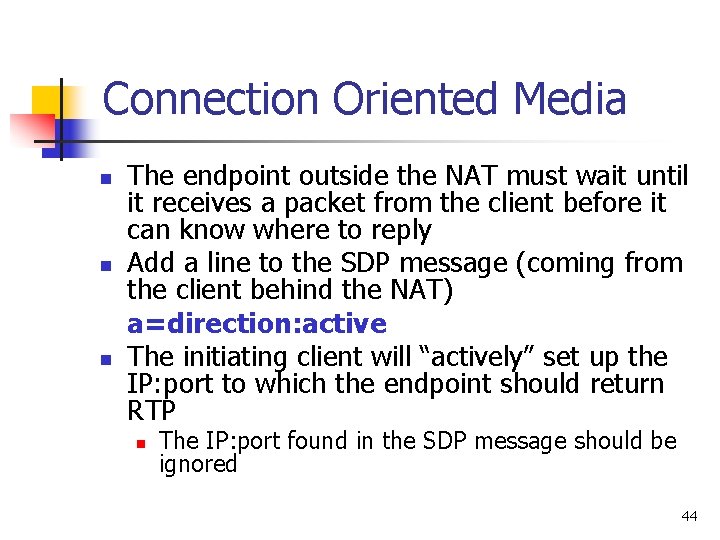
Connection Oriented Media n n n The endpoint outside the NAT must wait until it receives a packet from the client before it can know where to reply Add a line to the SDP message (coming from the client behind the NAT) a=direction: active The initiating client will “actively” set up the IP: port to which the endpoint should return RTP n The IP: port found in the SDP message should be ignored 44
Problem? 1) 2) If the endpoint does not support the a=direction: active tag If both endpoints are behind Symmetric NATs 45
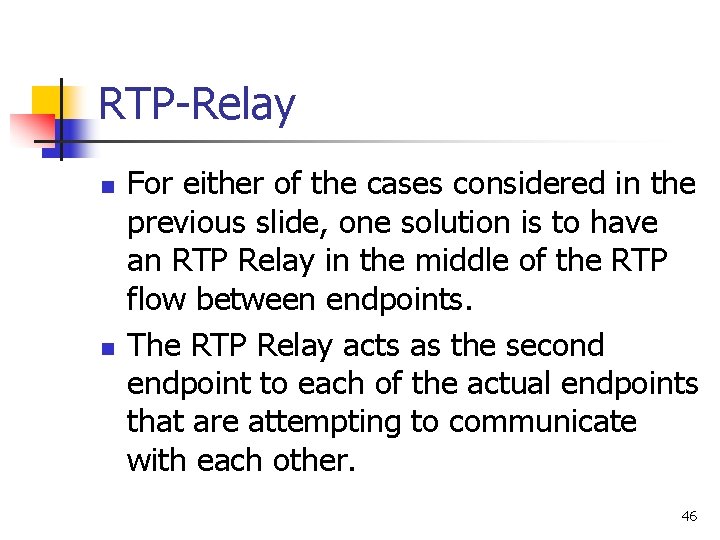
RTP-Relay n n For either of the cases considered in the previous slide, one solution is to have an RTP Relay in the middle of the RTP flow between endpoints. The RTP Relay acts as the second endpoint to each of the actual endpoints that are attempting to communicate with each other. 46
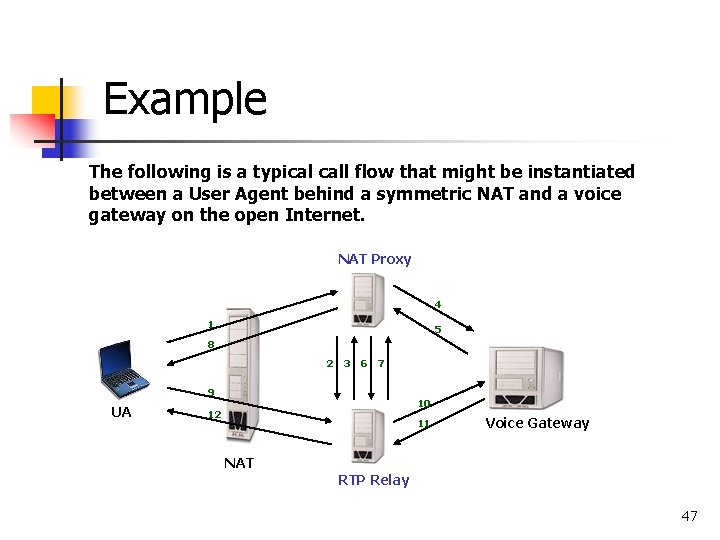
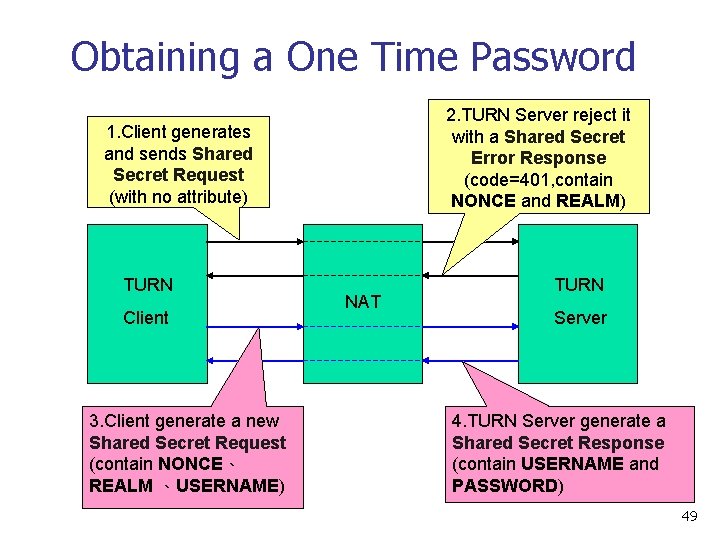
Example The following is a typical call flow that might be instantiated between a User Agent behind a symmetric NAT and a voice gateway on the open Internet. NAT Proxy 4 1 5 8 2 3 6 7 9 UA 10 12 11 Voice Gateway NAT RTP Relay 47
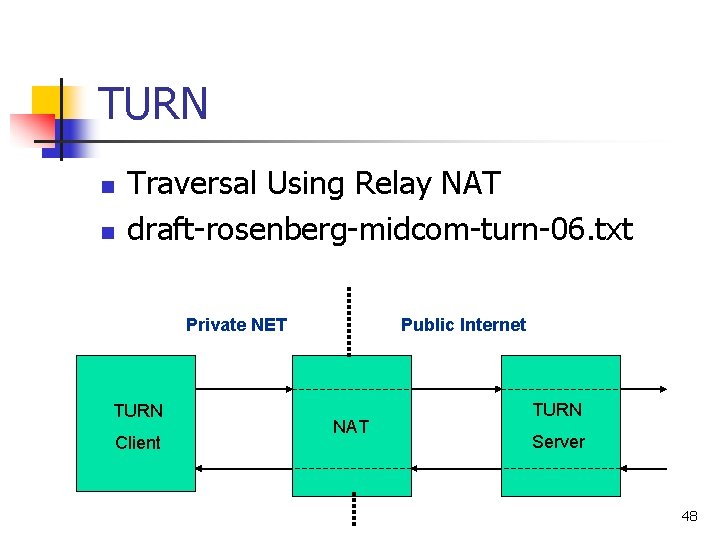
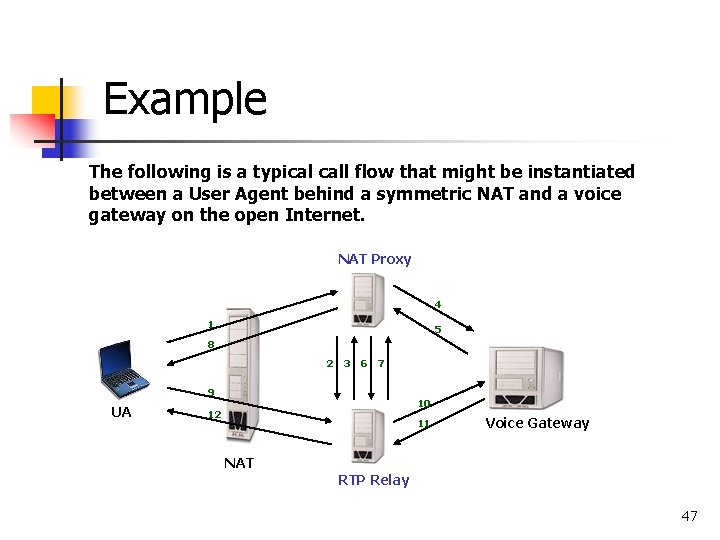
TURN n n Traversal Using Relay NAT draft-rosenberg-midcom-turn-06. txt Private NET TURN Client Public Internet NAT TURN Server 48
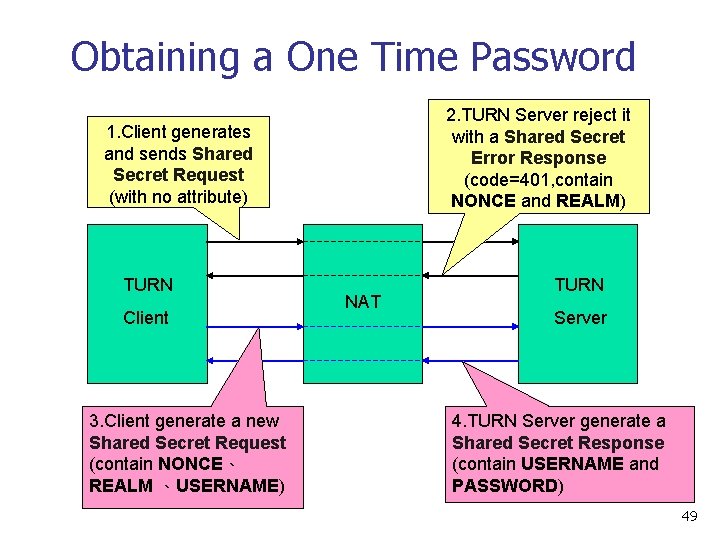
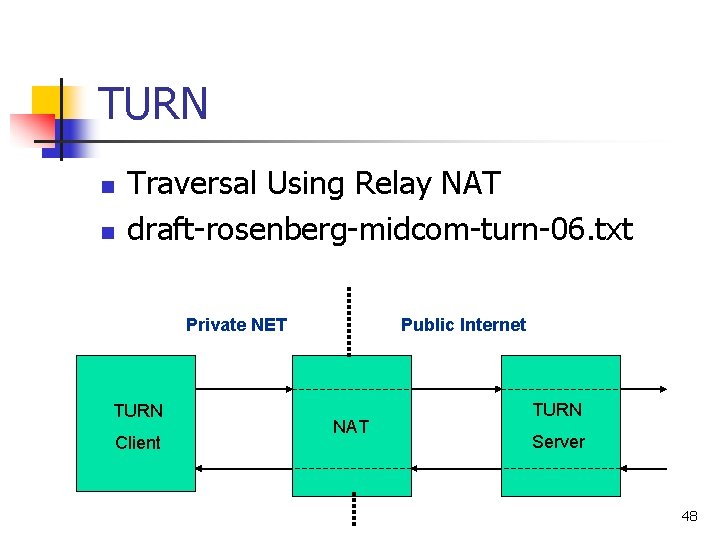
Obtaining a One Time Password 2. TURN Server reject it with a Shared Secret Error Response (code=401, contain NONCE and REALM) 1. Client generates and sends Shared Secret Request (with no attribute) TURN Client 3. Client generate a new Shared Secret Request (contain NONCE、 REALM 、USERNAME) NAT TURN Server 4. TURN Server generate a Shared Secret Response (contain USERNAME and PASSWORD) 49
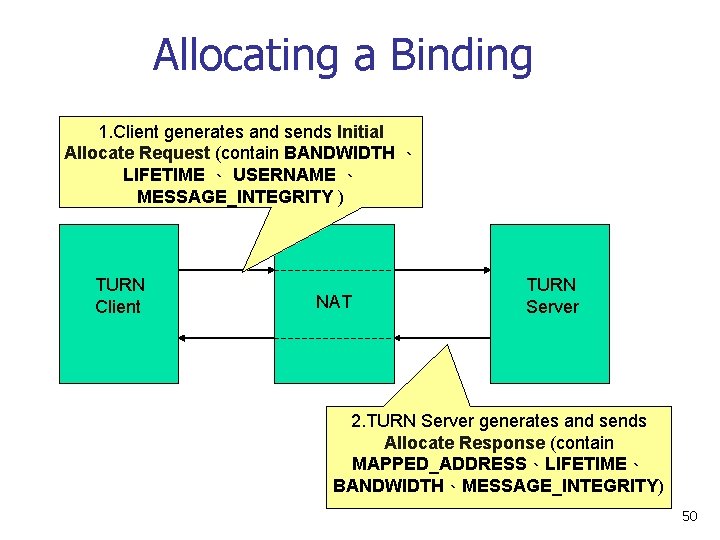
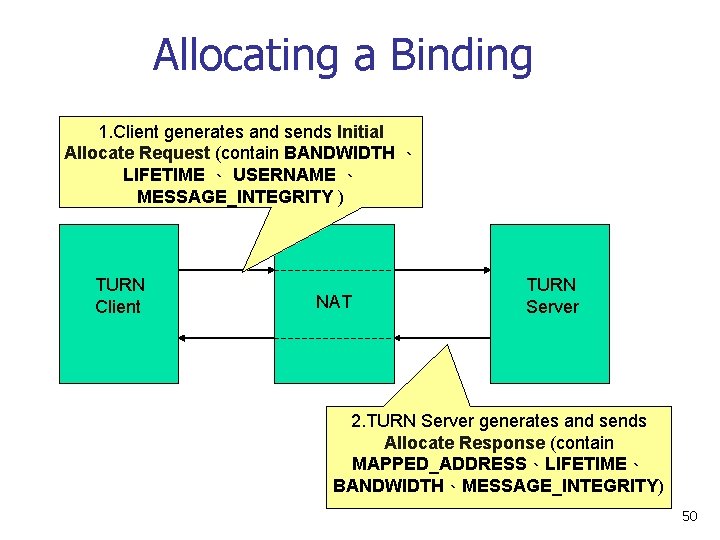
Allocating a Binding 1. Client generates and sends Initial Allocate Request (contain BANDWIDTH 、 LIFETIME 、 USERNAME 、 MESSAGE_INTEGRITY ) TURN Client NAT TURN Server 2. TURN Server generates and sends Allocate Response (contain MAPPED_ADDRESS、LIFETIME、 BANDWIDTH、MESSAGE_INTEGRITY) 50
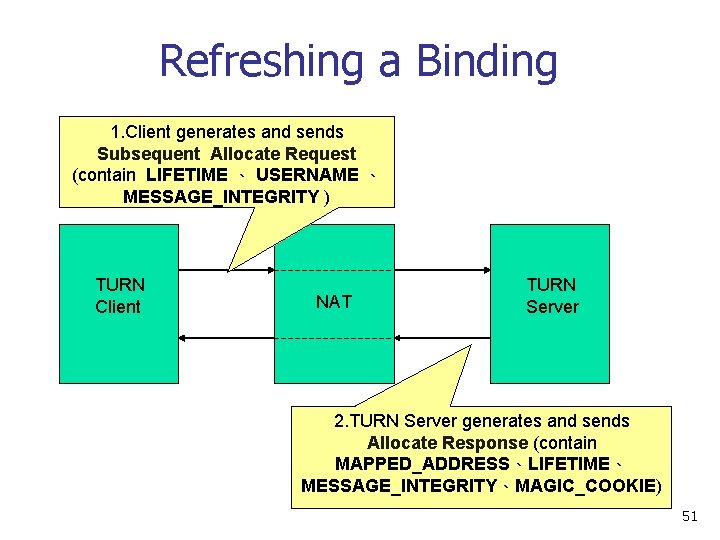
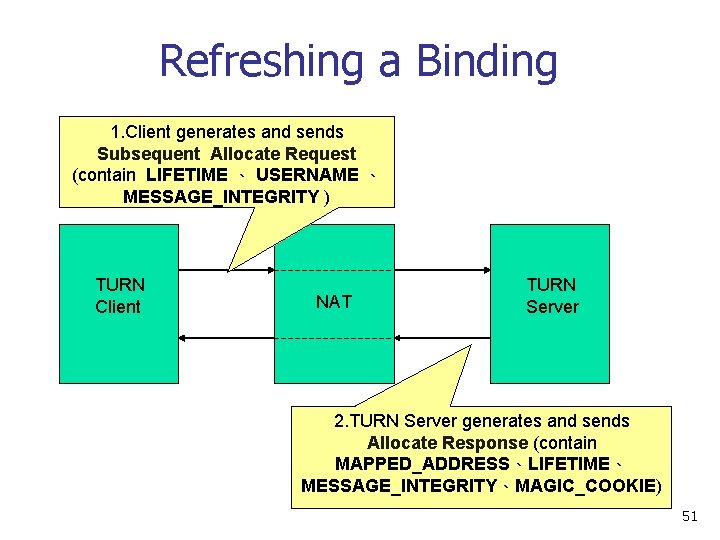
Refreshing a Binding 1. Client generates and sends Subsequent Allocate Request (contain LIFETIME 、 USERNAME 、 MESSAGE_INTEGRITY ) TURN Client NAT TURN Server 2. TURN Server generates and sends Allocate Response (contain MAPPED_ADDRESS、LIFETIME、 MESSAGE_INTEGRITY、MAGIC_COOKIE) 51
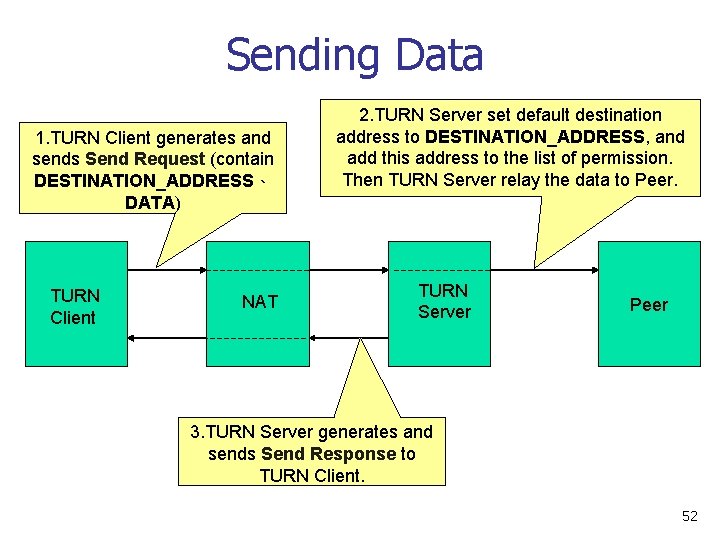
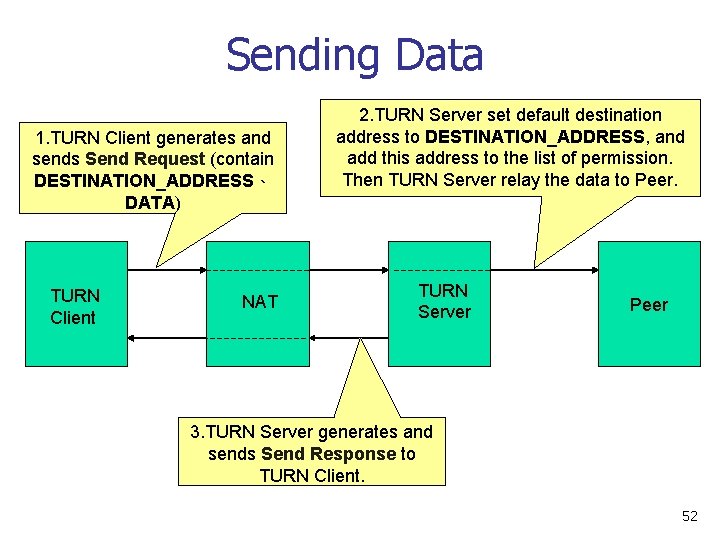
Sending Data 1. TURN Client generates and sends Send Request (contain DESTINATION_ADDRESS、 DATA) TURN Client NAT 2. TURN Server set default destination address to DESTINATION_ADDRESS, and add this address to the list of permission. Then TURN Server relay the data to Peer. TURN Server Peer 3. TURN Server generates and sends Send Response to TURN Client. 52
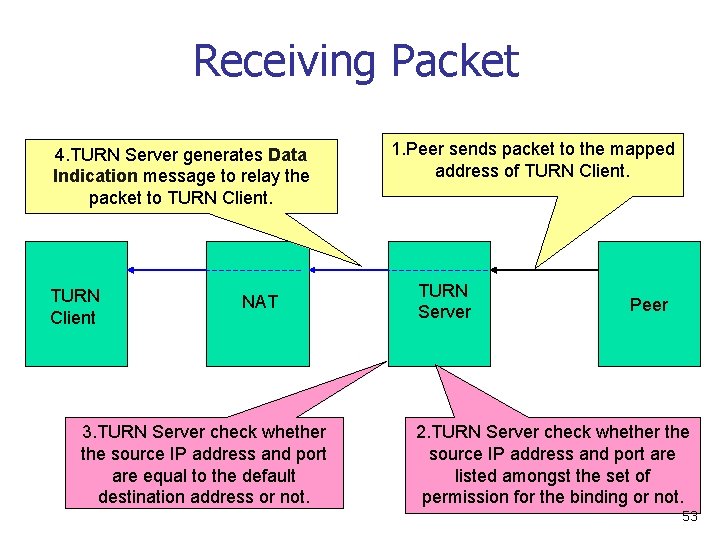
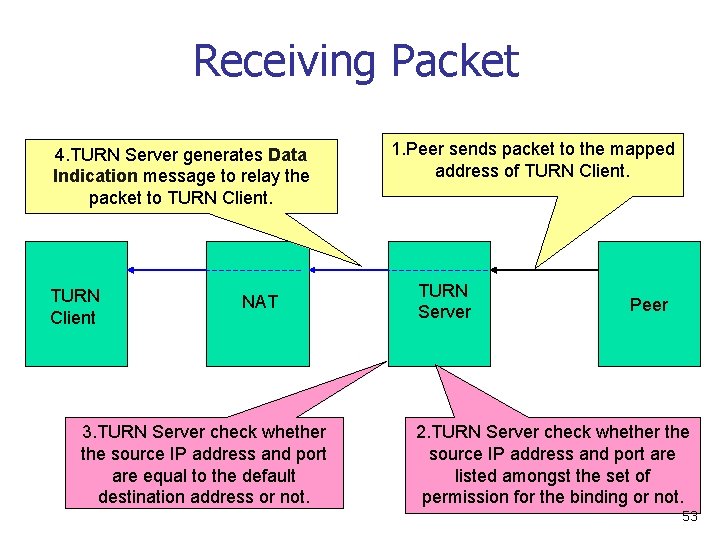
Receiving Packet 4. TURN Server generates Data Indication message to relay the packet to TURN Client NAT 3. TURN Server check whether the source IP address and port are equal to the default destination address or not. 1. Peer sends packet to the mapped address of TURN Client. TURN Server Peer 2. TURN Server check whether the source IP address and port are listed amongst the set of permission for the binding or not. 53
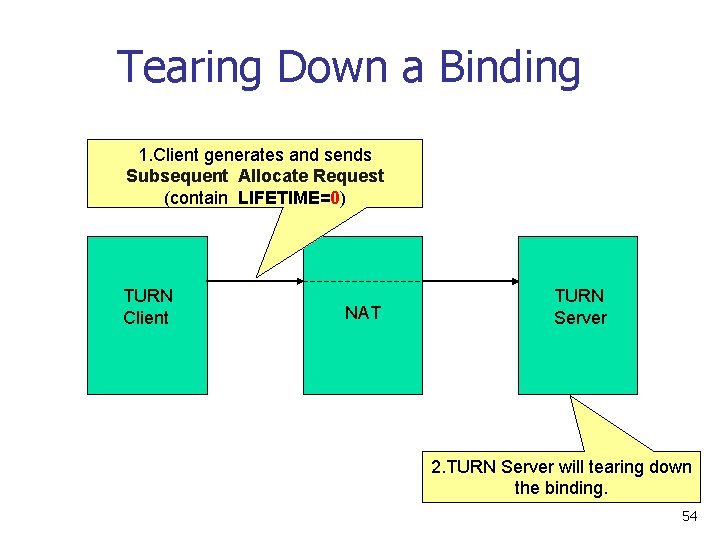
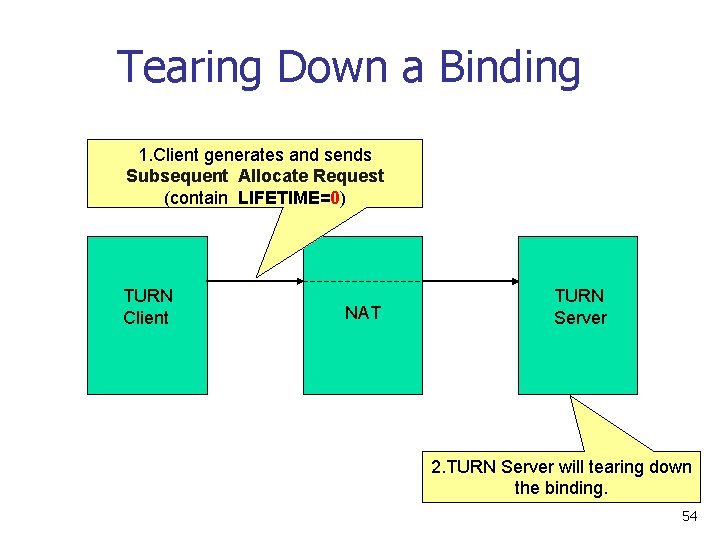
Tearing Down a Binding 1. Client generates and sends Subsequent Allocate Request (contain LIFETIME=0) TURN Client NAT TURN Server 2. TURN Server will tearing down the binding. 54
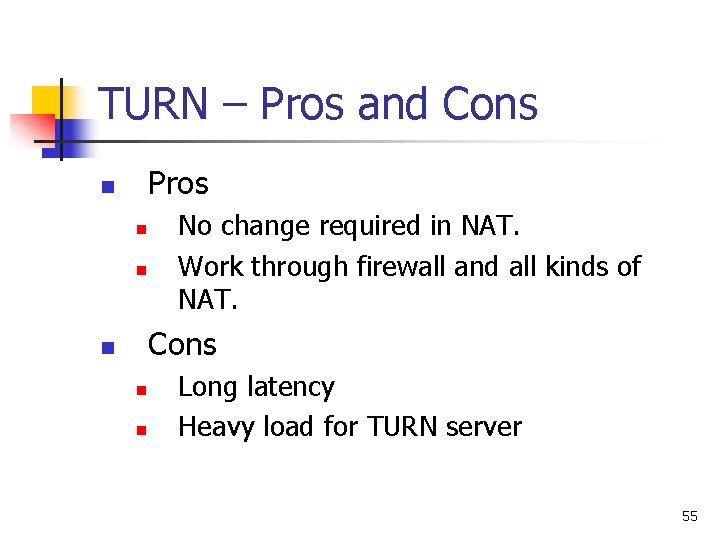
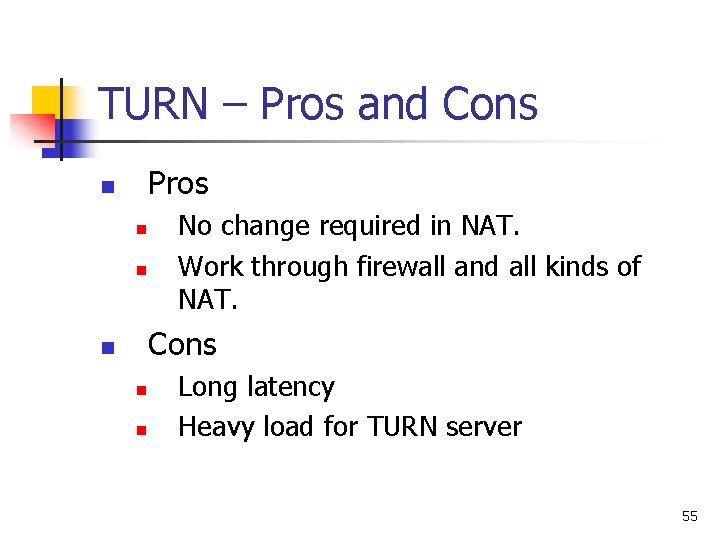
TURN – Pros and Cons Pros n n n No change required in NAT. Work through firewall and all kinds of NAT. Cons n n n Long latency Heavy load for TURN server 55