NAPAA Conference Payment Fraud Trends Don Binns Global
NAPAA Conference– Payment Fraud Trends Don Binns, Global Products Fraud Executive Glenna Thompson, Treasury Sales Officer May 15, 2014
Agenda Topics § § § 2 Headlines Data Breaches Payment Fraud How To Protect Your Entity On The Horizon
News Headlines Reuters January 10, 2014 Target breach worse than thought, states launch joint probe By Dhanya Skariachan and Jim Finkle (Reuters) - The data bre ach at Target Corp ove r the holiday shopping season was far bigger than initiall y thought, the U. S. compan y said on Friday, as sta te prosecutors announced a nationwide probe into the second-biggest retail cyb er attack on record. Target said an investiga tion has found that the hackers stole the person al information of at least 70 million customers, includ ing names, mailing addres ses, telephone numbers and email addresses. Previo usly, the No. 3 U. S. retailer sai d the hackers stole data from 40 million credit and deb it cards. The New York Times January 23, 2014 Neiman Marcus Data Breach Worse Than First Said By ELIZABETH A. HARRIS, NICOLE PERLROTH and NATHANIEL POPPER 3 The theft of cons umer data from Ne iman Marcus appears far deep er than had been disclosed origina with the luxury re lly, tailer now saying that hackers invaded its syste ms for several m onths in a breach that involved 1. 1 million credit and debit cards. Bank of America – Confidential. Do Not Distribute
3 align: right; flow: left DATA Breach
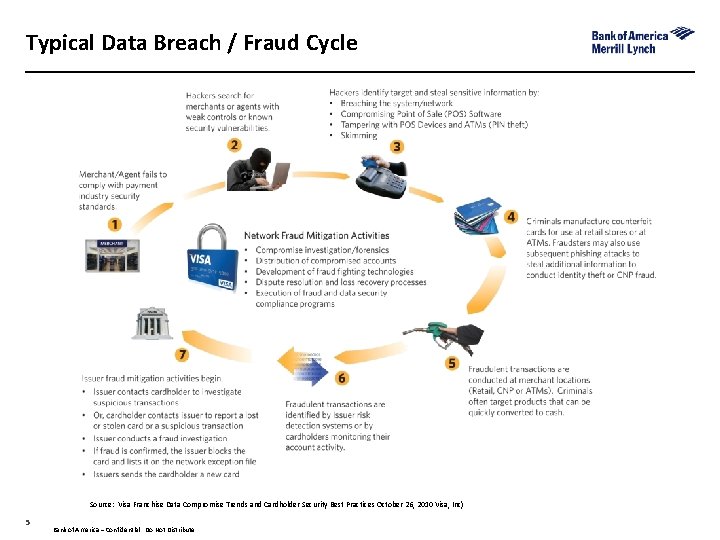
Typical Data Breach / Fraud Cycle Source: Visa Franchise Data Compromise Trends and Cardholder Security Best Practices October 26, 2010 Visa, Inc) 5 Bank of America – Confidential. Do Not Distribute 5
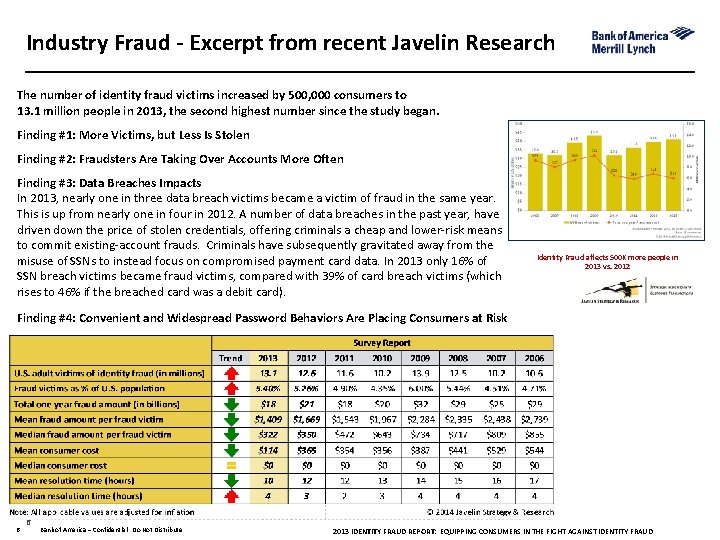
Industry Fraud - Excerpt from recent Javelin Research The number of identity fraud victims increased by 500, 000 consumers to 13. 1 million people in 2013, the second highest number since the study began. Finding #1: More Victims, but Less Is Stolen Finding #2: Fraudsters Are Taking Over Accounts More Often Finding #3: Data Breaches Impacts In 2013, nearly one in three data breach victims became a victim of fraud in the same year. This is up from nearly one in four in 2012. A number of data breaches in the past year, have driven down the price of stolen credentials, offering criminals a cheap and lower‐risk means to commit existing‐account frauds. Criminals have subsequently gravitated away from the misuse of SSNs to instead focus on compromised payment card data. In 2013 only 16% of SSN breach victims became fraud victims, compared with 39% of card breach victims (which rises to 46% if the breached card was a debit card). Identity Fraud affects 500 K more people in 2013 vs. 2012 Finding #4: Convenient and Widespread Password Behaviors Are Placing Consumers at Risk 6 6 Bank of America – Confidential. Do Not Distribute 2013 IDENTITY FRAUD REPORT: EQUIPPING CONSUMERS IN THE FIGHT AGAINST IDENTITY FRAUD
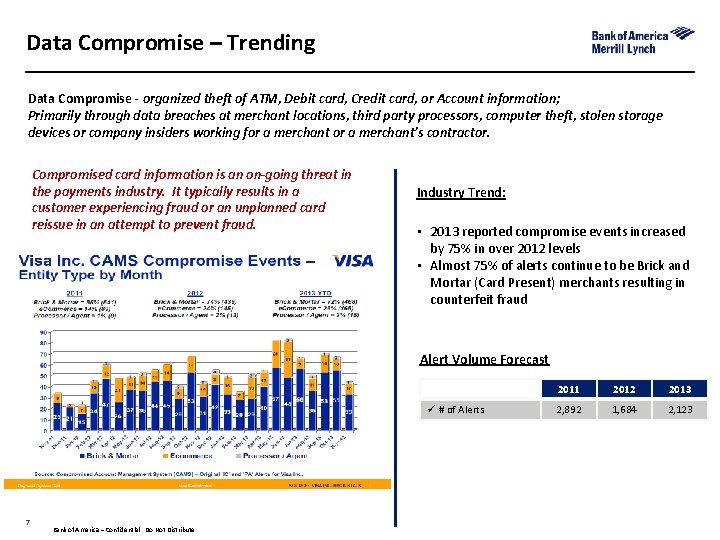
Data Compromise – Trending Data Compromise - organized theft of ATM, Debit card, Credit card, or Account information; Primarily through data breaches at merchant locations, third party processors, computer theft, stolen storage devices or company insiders working for a merchant’s contractor. Compromised card information is an on-going threat in the payments industry. It typically results in a customer experiencing fraud or an unplanned card reissue in an attempt to prevent fraud. Industry Trend: • 2013 reported compromise events increased by 75% in over 2012 levels • Almost 75% of alerts continue to be Brick and Mortar (Card Present) merchants resulting in counterfeit fraud Alert Volume Forecast ü # of Alerts 7 Bank of America – Confidential. Do Not Distribute 2011 2012 2013 2, 892 1, 684 2, 123
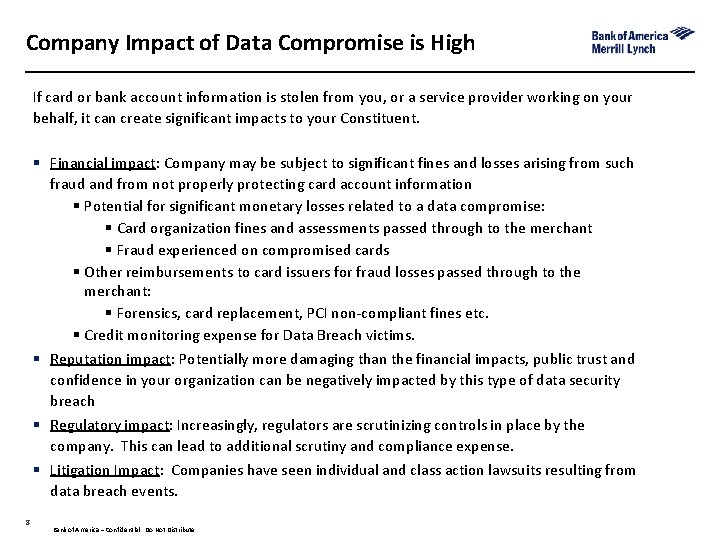
Company Impact of Data Compromise is High If card or bank account information is stolen from you, or a service provider working on your behalf, it can create significant impacts to your Constituent. § Financial impact: Company may be subject to significant fines and losses arising from such fraud and from not properly protecting card account information § Potential for significant monetary losses related to a data compromise: § Card organization fines and assessments passed through to the merchant § Fraud experienced on compromised cards § Other reimbursements to card issuers for fraud losses passed through to the merchant: § Forensics, card replacement, PCI non‐compliant fines etc. § Credit monitoring expense for Data Breach victims. § Reputation impact: Potentially more damaging than the financial impacts, public trust and confidence in your organization can be negatively impacted by this type of data security breach § Regulatory impact: Increasingly, regulators are scrutinizing controls in place by the company. This can lead to additional scrutiny and compliance expense. § Litigation Impact: Companies have seen individual and class action lawsuits resulting from data breach events. 8 Bank of America – Confidential. Do Not Distribute
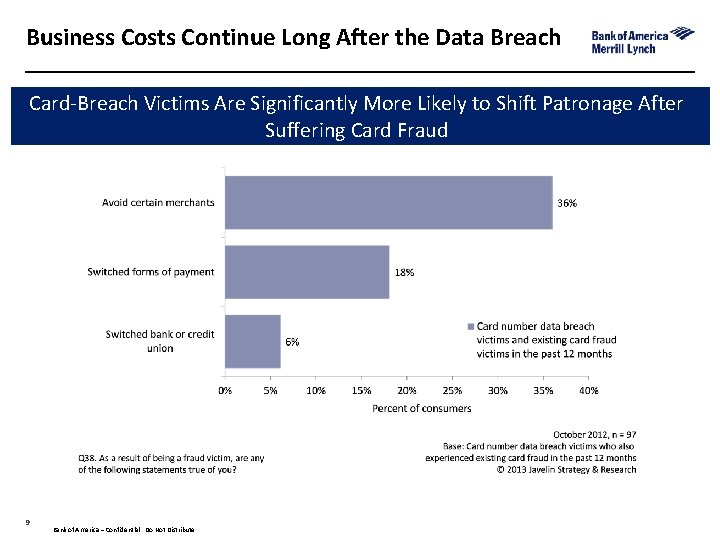
Business Costs Continue Long After the Data Breach Card‐Breach Victims Are Significantly More Likely to Shift Patronage After Suffering Card Fraud 9 Bank of America – Confidential. Do Not Distribute
3 align: right; flow: left Payment Fraud
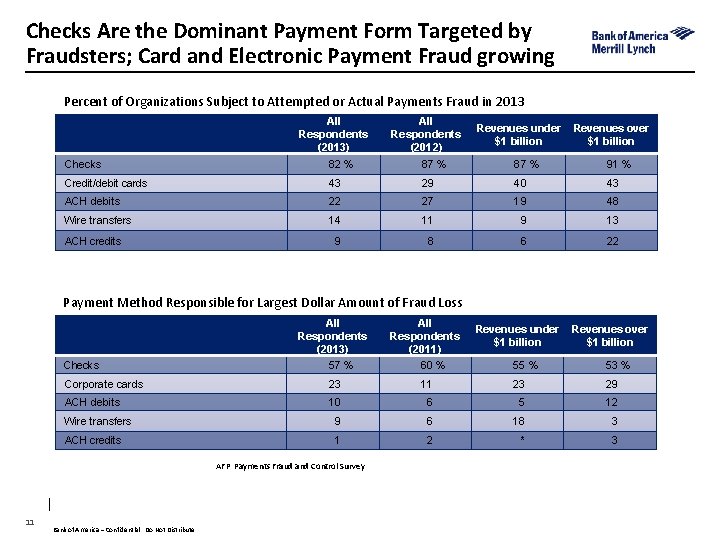
Checks Are the Dominant Payment Form Targeted by Fraudsters; Card and Electronic Payment Fraud growing Percent of Organizations Subject to Attempted or Actual Payments Fraud in 2013 All Respondents (2013) All Respondents (2012) Revenues under $1 billion Revenues over $1 billion Checks 82 % 87 % 91 % Credit/debit cards 43 29 40 43 ACH debits 22 27 19 48 Wire transfers 14 11 9 13 9 8 6 22 ACH credits Payment Method Responsible for Largest Dollar Amount of Fraud Loss All Respondents (2013) 57 % All Respondents (2011) 60 % Corporate cards 23 ACH debits Checks Revenues over $1 billion 55 % 53 % 11 23 29 10 6 5 12 Wire transfers 9 6 18 3 ACH credits 1 2 * 3 AFP Payments Fraud and Control Survey 11 Revenues under $1 billion Bank of America – Confidential. Do Not Distribute

Evolution of Malware On the Horizon: Internet connectivity & browsers incorporated into more diverse platforms: 12 • Electronic book readers ‐ Game Consoles • Smart TVs ‐ Smart Appliances • Blu‐Ray players ‐ Automobiles Bank of America – Confidential. Do Not Distribute

Malware Threats – How Fraud Occurs Fraudsters attack weakest point in transaction - user’s device • • • Phishing Drive By Downloads SMishing Anatomy of an attack User targeted & Malware installed: § Phishing & SMi. Shing: Infected files/malicious links sent through email or SMS message § Drive by Downloads: Clicking on a document, ad, or video, posted on legitimate website initiates malware download § Using infected flash drive Attack is launched and fraud committed: § Credential theft and/or HTML injection § Transaction manipulation 13 Bank of America – Confidential. Do Not Distribute
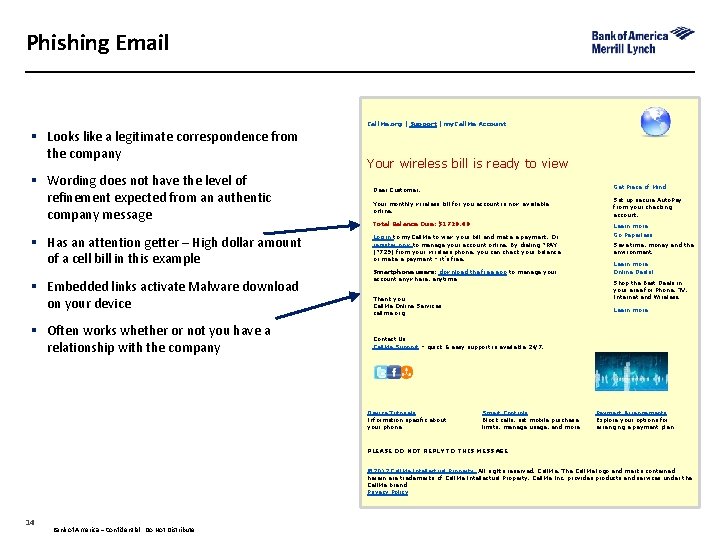
Phishing Email Call. Me. org | Support | my. Call. Me Account § Looks like a legitimate correspondence from the company § Wording does not have the level of refinement expected from an authentic company message § Has an attention getter – High dollar amount of a cell bill in this example § Embedded links activate Malware download on your device § Often works whether or not you have a relationship with the company Your wireless bill is ready to view Dear Customer, Get Piece of Mind Your monthly wireless bill for you account is now available online. Set up secure Auto. Pay from your checking account. Total Balance Due: $1720. 40 Log in to my. Call. Me to view your bill and make a payment. Or register now to manage your account online. By dialing *PAY (*729) from your wireless phone, you can check your balance or make a payment – it’s free. Smartphone users: download the free app to manage your account anywhere, anytime. Thank you Call. Me Online Services callme. org Learn more Go Paperless Save time, money and the environment. Learn more Online Deals! Shop the Best Deals in your area for Phone, TV, Internet and Wireless. Learn more Contact Us Call. Me Support – quick & easy support is available 24/7. Device Tutorials Information specific about your phone Smart Controls Block calls, set mobile purchase limits, manage usage, and more Payment Arrangements Explore your options for arranging a payment plan PLEASE DO NOT REPLY TO THIS MESSAGE © 2012 Call. Me Intellectual Property, All rights reserved. Call. Me, The Call. Me logo and marks contained herein are trademarks of Call. Me Intellectual Property. Call. Me Inc. provides products and services under the Call. Me brand. Privacy Policy 14 Bank of America – Confidential. Do Not Distribute
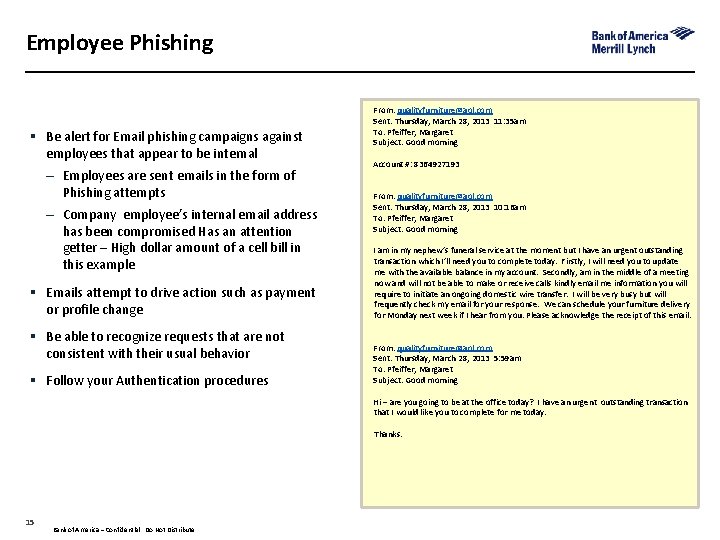
Employee Phishing § Be alert for Email phishing campaigns against employees that appear to be internal – Employees are sent emails in the form of Phishing attempts – Company employee’s internal email address has been compromised Has an attention getter – High dollar amount of a cell bill in this example § Emails attempt to drive action such as payment or profile change § Be able to recognize requests that are not consistent with their usual behavior § Follow your Authentication procedures From: qualityfurniture@aol. com Sent: Thursday, March 28, 2013 11: 35 am To: Pfeiffer, Margaret Subject: Good morning Account #: 8364927193 From: qualityfurniture@aol. com Sent: Thursday, March 28, 2013 10: 16 am To: Pfeiffer, Margaret Subject: Good morning I am in my nephew’s funeral service at the moment but I have an urgent outstanding transaction which I’ll need you to complete today. Firstly, I will need you to update me with the available balance in my account. Secondly, am in the middle of a meeting now and will not be able to make or receive calls kindly email me information you will require to initiate an ongoing domestic wire transfer. I will be very busy but will frequently check my email for your response. We can schedule your furniture delivery for Monday next week if I hear from you. Please acknowledge the receipt of this email. From: qualityfurniture@aol. com Sent: Thursday, March 28, 2013 5: 59 am To: Pfeiffer, Margaret Subject: Good morning Hi – are you going to be at the office today? I have an urgent outstanding transaction that I would like you to complete for me today. Thanks. 15 Bank of America – Confidential. Do Not Distribute
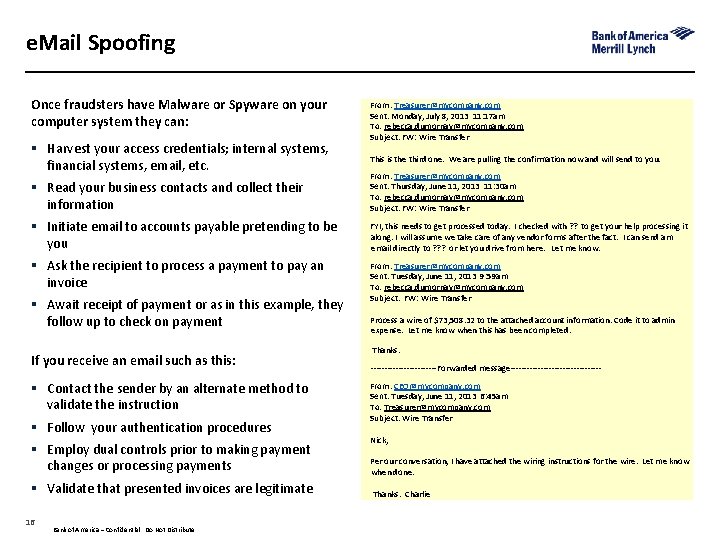
e. Mail Spoofing Once fraudsters have Malware or Spyware on your computer system they can: § Harvest your access credentials; internal systems, financial systems, email, etc. From: Treasurer@mycompany. com Sent: Monday, July 8, 2013 11: 17 am To: rebecca. dumornay@mycompany. com Subject: FW: Wire Transfer This is the third one. We are pulling the confirmation now and will send to you. § Read your business contacts and collect their information From: Treasurer@mycompany. com Sent: Thursday, June 11, 2013 11: 30 am To: rebecca. dumornay@mycompany. com Subject: FW: Wire Transfer § Initiate email to accounts payable pretending to be you FYI, this needs to get processed today. I checked with ? ? to get your help processing it along. I will assume we take care of any vendor forms after the fact. I can send am email directly to ? ? ? or let you drive from here. Let me know. § Ask the recipient to process a payment to pay an invoice From: Treasurer@mycompany. com Sent: Tuesday, June 11, 2013 9: 59 am To: rebecca. dumornay@mycompany. com Subject: FW: Wire Transfer § Await receipt of payment or as in this example, they follow up to check on payment If you receive an email such as this: § Contact the sender by an alternate method to validate the instruction § Follow your authentication procedures § Employ dual controls prior to making payment changes or processing payments § Validate that presented invoices are legitimate 16 Bank of America – Confidential. Do Not Distribute Process a wire of $73, 508. 32 to the attached account information. Code it to admin expense. Let me know when this has been completed. Thanks. ‐‐‐‐‐‐‐‐‐‐‐‐Forwarded message‐‐‐‐‐‐‐‐‐‐‐‐‐‐‐‐‐ From: CEO@mycompany. com Sent: Tuesday, June 11, 2013 6: 45 am To: Treasurer@mycompany. com Subject: Wire Transfer Nick, Per our conversation, I have attached the wiring instructions for the wire. Let me know when done. Thanks. Charlie
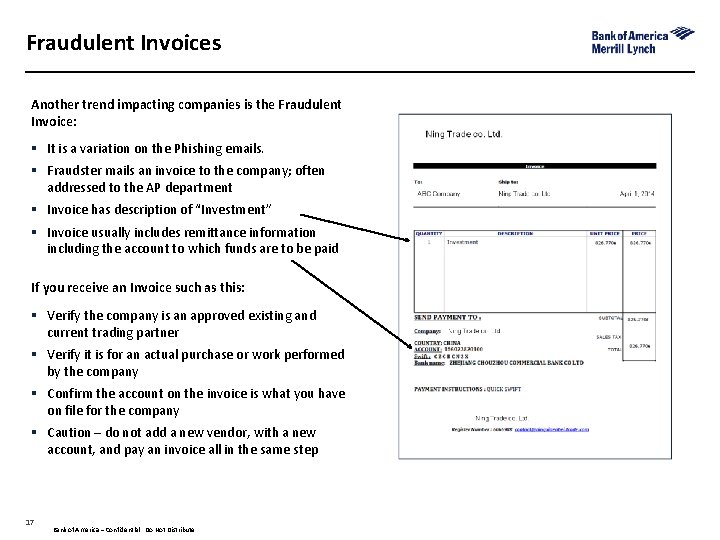
Fraudulent Invoices Another trend impacting companies is the Fraudulent Invoice: § It is a variation on the Phishing emails. § Fraudster mails an invoice to the company; often addressed to the AP department § Invoice has description of “Investment” § Invoice usually includes remittance information including the account to which funds are to be paid If you receive an Invoice such as this: § Verify the company is an approved existing and current trading partner § Verify it is for an actual purchase or work performed by the company § Confirm the account on the invoice is what you have on file for the company § Caution – do not add a new vendor, with a new account, and pay an invoice all in the same step 17 Bank of America – Confidential. Do Not Distribute
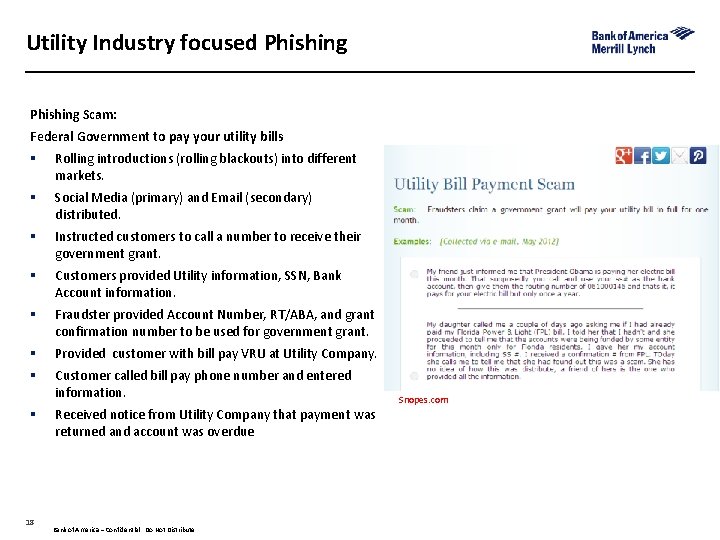
Utility Industry focused Phishing Scam: Federal Government to pay your utility bills § Rolling introductions (rolling blackouts) into different markets. § Social Media (primary) and Email (secondary) distributed. § Instructed customers to call a number to receive their government grant. § Customers provided Utility information, SSN, Bank Account information. § Fraudster provided Account Number, RT/ABA, and grant confirmation number to be used for government grant. § Provided customer with bill pay VRU at Utility Company. § Customer called bill pay phone number and entered information. § 18 Received notice from Utility Company that payment was returned and account was overdue Bank of America – Confidential. Do Not Distribute Snopes. com

Are you prepared to identify and manage events like these? Detection: Sample Social Media Dashboard § Social Media Monitoring § Bill Pay account changes – online and VRU § Bill Pay VRU increased activity § Contact Center inquiries § Return payment activity monitoring Impact to Consumers: § Victim of Identity Theft § Credit Monitoring and bank information changes § Financial loss, inability to pay current bills Impact to Company: § Potential Impact to cash flow § High ACH return rates – implications future direct debit programs § Media visibility and brand impact 19 • Were you proactive or reactive? • What support did you offer impacted customers? Bank of America – Confidential. Do Not Distribute (socialmediaexaminer. com)
3 align: right; flow: left How to protect your entity
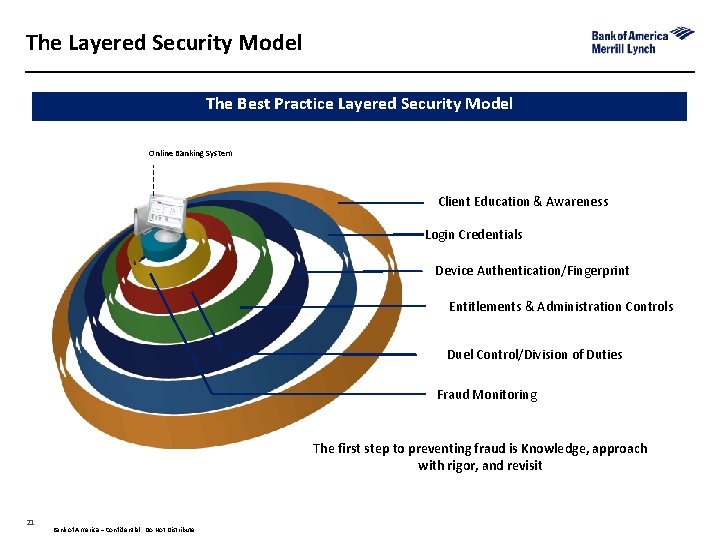
The Layered Security Model The Best Practice Layered Security Model Online Banking System Client Education & Awareness Login Credentials Device Authentication/Fingerprint Entitlements & Administration Controls Duel Control/Division of Duties Fraud Monitoring The first step to preventing fraud is Knowledge, approach with rigor, and revisit 21 Bank of America – Confidential. Do Not Distribute
Securing Online Transactions § Be attentive during online session: Are login prompts occurring where they should? Do your online screens look correct? § Ensure all users are educated to recognize Phishing scams and know to not open file attachments or click links in suspicious emails. Always be on lookout for: • Any requests for personal information • Urgent appeals claiming your account will be closed if you fail to respond • Messages about system/security updates § Use caution when visiting Internet sites, avoiding social networking & unknown sites that are not trusted and used for business purposes § Consider the use of dedicated, hardened computer § Ensure your Anti‐Virus software/system patches are kept up to date. Consider anti‐ malware software that specifically protects your Internet Browser § Implement Duty Segregation/Dual Administration § Prohibit shared user names/passwords and avoid using automatic login features that save usernames/passwords § Never access online banking via Internet cafes, public libraries or open Wi‐Fi hotspots § Report suspicious transaction activity to bank/authorities immediately 22 Bank of America – Confidential. Do Not Distribute
Mobile is Growing Target Mobile Fraud • A growing risk, albeit less than online • 1800 mobile strains vs 75 M online • Online techniques crossing over to mobile • All of threat vectors not yet known Physical device security • Secure mobile device with pin/strong password • Lock device after use • Install software to track mobile device in case of theft Manage system settings, downloads and device software • Don’t leave Wi‐Fi in ad hoc mode • Disable discoverable mode after enabling Bluetooth devices, if your Smartphone does not automatically default to off after adding a device • Setup a personal firewall • Don’t modify the device to: • Give yourself more control • Enable features that void warranties • Change root file systems • Allow modifications to install third party software/hardware components 23 Bank of America – Confidential. Do Not Distribute
Fraud Prevention Considerations for ACH & Wire Payment Fraud § Utilizes ID & Password obtained through Malware, Phishing, etc. to initiate outbound electronic payments from your account § Third party obtains your account information from an intercepted check. § Pays for bills, gets car loan, purchases goods on account. Provides biller with electronic debit authorization – not to his account but to your account Best Practices § Separate duties/auditing responsibilities across user credentials to provide additional security within cash management system § Set individual user limits appropriate for payment /user • Maximum dollar amount / transaction for initiating/approving wires/ACH • Maximum daily cumulative dollar amount of all wires initiated and/or approve § Review ACH / Wire Transfer Procedures on regular basis, confirm user credentials updated and maintained to represent appropriate needs § Use Repetitive Wire Templates to eliminate manual intervention/manipulation § Implement ACH Blocks to block incoming ACH transactions from posting to accounts § Use ACH Positive Pay to monitor / control ACH transactions before they post to your bank account, allow transaction acceptance or rejection in real time § Apply ACH Authorization Service to post only incoming “authorized” ACH items 24 Bank of America – Confidential. Do Not Distribute
Fraud Prevention Considerations for Check Best Practices § Reconcile accounts on a daily basis § Segregate internal duties for financial activities (Audit/Control) § Consider migration from Check Payments to Electronic Payment Products § Become fraud focused on inquiries from other banks/institutions regarding legitimacy of checks § Escalate suspicious activities to management team § Safeguard check stock/use check stock security features § Consider outsourcing check processing to secured vendor Prevention Products § Positive Pay ‐ Automate review of items before decision to Pay or Return § Teller Positive Pay ‐ Integrates check decision with banking center teller line § Payee Positive Pay ‐ Determines if payee names have been altered § Reverse Positive Pay ‐ Notify bank of exception items identified on file § Maximum Dollar Control ‐ Flag any check over a given dollar amount to decision 25 Bank of America – Confidential. Do Not Distribute
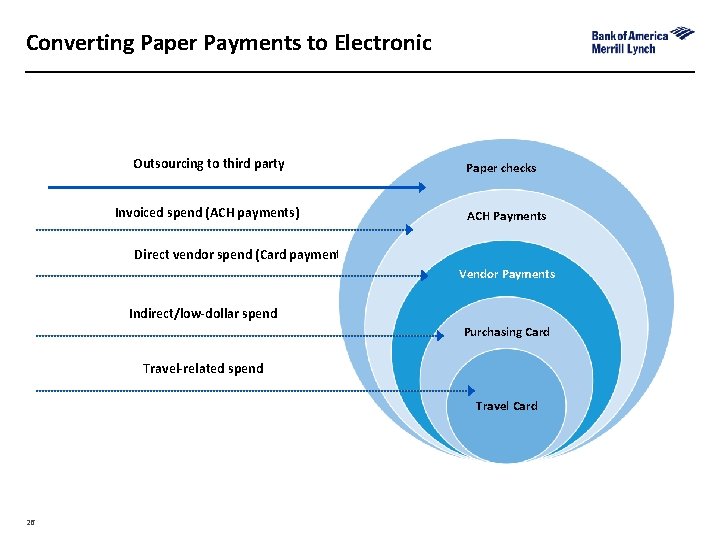
Converting Paper Payments to Electronic Outsourcing to third party Invoiced spend (ACH payments) Paper checks ACH Payments Direct vendor spend (Card payments) Vendor Payments Indirect/low-dollar spend Purchasing Card Travel-related spend Travel Card 26
Services Providers Fraud Risk and Role in Fraud Prevention Businesses that outsource transactional network servers and/or services (i. e. reporting services, payroll, accounts payable, etc. ) must ensure vendors maintain acceptable security levels § § § Reliance on third‐party/outsourcer security may present increased vulnerability to access by fraudsters Controls for identifying access to shared information/log‐ins managed beyond your four walls Potential losses/recovery need to include vendor impacting fraud recovery efforts Vendor Services Best Practices § Perform site review/engage all security/process experts to assist in decision making § Review internal needs/allow vendor access only to required data § Limit/segregate log‐ins to mitigate potential breaches § Address responsibility/liability if vendor compromise impacts your business § Understand vendor’s loss recovery processes and service level agreements currently in place § Do your homework – check references, awards, company standards regarding product /data security processes/procedures to ensure balanced risk/reward decision § Hold your vendor to the same “Best Practice” standards you adopt internally 27 Bank of America – Confidential. Do Not Distribute
Employee Education User Awareness Training: § Don’t assume employees understand email and internet risks § Don’t rely on your company’s email or intranet to inform employees of email and internet policies and procedures § Set rules for personal internet usage § Ensure that employees understand policies toward monitoring of their computer activity § Consider restricting the ability to load/download data on your company computers 28 Bank of America – Confidential. Do Not Distribute
Specificity Strengthens the Impact of Employee Training; Simple, Straight-forward Examples Can Be the Most Powerful Key Success Factors: § Show employees how to recognize threats and convey the consequences of those threats § Be explicit about what to look for to identify a malicious email § Explain that users will keep passwords in a secure place and not to share them with coworkers § Provide frequent reports of new threats and statistics of how many viruses have been caught within your company § Never turn off security protection on your computer and stay current with updates § Do not use your personal computer for company business § Do not connect to the internet through suspect wireless networks (e. g. , Wi‐Fi from a café) § Forward suspicious emails to the company’s designated email account (include the email address) § Open only identifiable attachments from known sources. Financial institutions never ask you to enter personal data, such as passwords, SSN, account numbers, etc. 29 Bank of America – Confidential. Do Not Distribute
3 align: right; flow: left On The Horizon
What is EMV Chip Technology? § Chip Technology allows data to be stored and processed in a microchip. § A chip has 3 key functions that help to create a more secure payment solution: • data storage • cardholder identification and authentication • cryptographic processing § EMV (Europay, Master. Card and Visa) is the global standard that defines how the chip card and terminal communicate. Chip technology provides additional layer of security: § Transaction is encrypted each time to protect against counterfeit fraud with both online and offline transactions. § Chip technology represents 3 primary enhancements: • Data is dynamic and every transaction made with the card is unique. The issuer can easily identify that the genuine card is being used. • The PIN validates the Card and the Cardholder; where with mag‐stripe it only validates the cardholder. • The card can be configured to make authorization decisions. 31 Bank of America – Confidential. Do Not Distribute
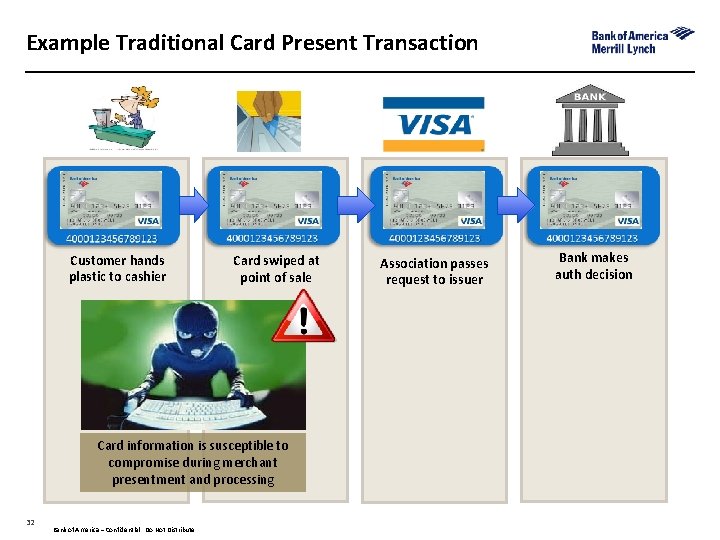
Example Traditional Card Present Transaction Customer hands plastic to cashier Card swiped at point of sale Association passes request to issuer Bank makes auth decision Card information is susceptible to compromise during merchant presentment and processing 32 Bank of America – Confidential. Do Not Distribute 32
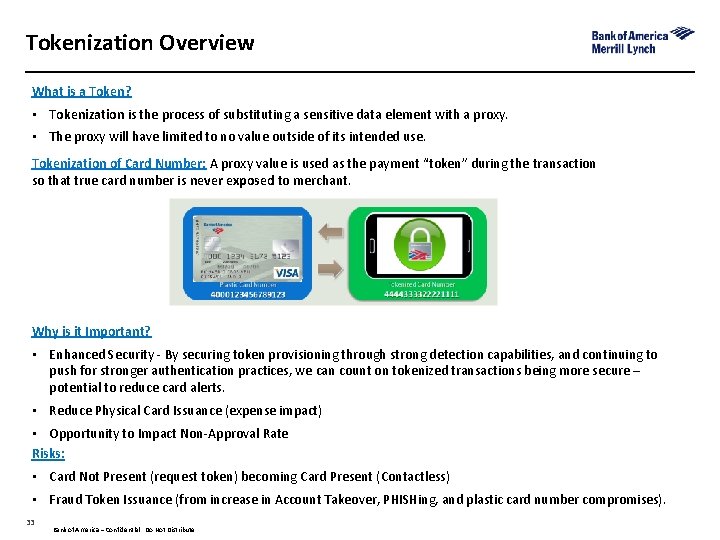
Tokenization Overview What is a Token? • Tokenization is the process of substituting a sensitive data element with a proxy. • The proxy will have limited to no value outside of its intended use. Tokenization of Card Number: A proxy value is used as the payment “token” during the transaction so that true card number is never exposed to merchant. Why is it Important? • Enhanced Security ‐ By securing token provisioning through strong detection capabilities, and continuing to push for stronger authentication practices, we can count on tokenized transactions being more secure – potential to reduce card alerts. • Reduce Physical Card Issuance (expense impact) • Opportunity to Impact Non‐Approval Rate Risks: • Card Not Present (request token) becoming Card Present (Contactless) • Fraud Token Issuance (from increase in Account Takeover, PHISHing, and plastic card number compromises). 33 Bank of America – Confidential. Do Not Distribute
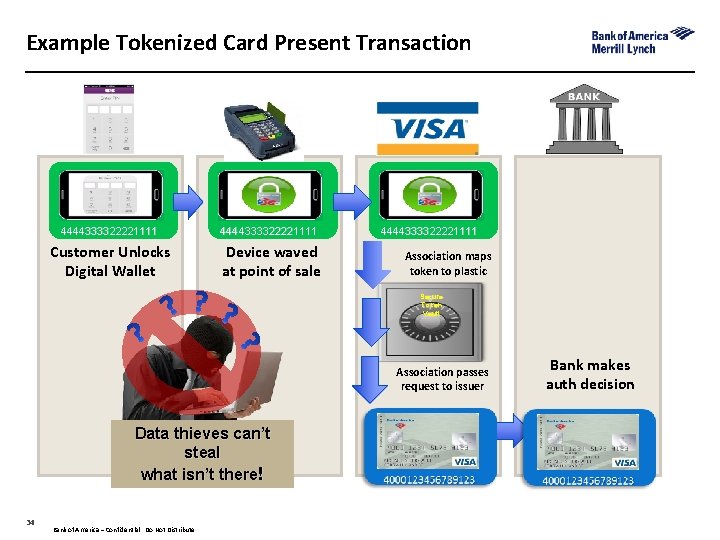
Example Tokenized Card Present Transaction 4444333322221111 Customer Unlocks Digital Wallet Device waved at point of sale 4444333322221111 Association maps token to plastic Secure Token Vault Association passes request to issuer Bank makes auth decision Data thieves can’t steal what isn’t there! 34 Bank of America – Confidential. Do Not Distribute 34 34
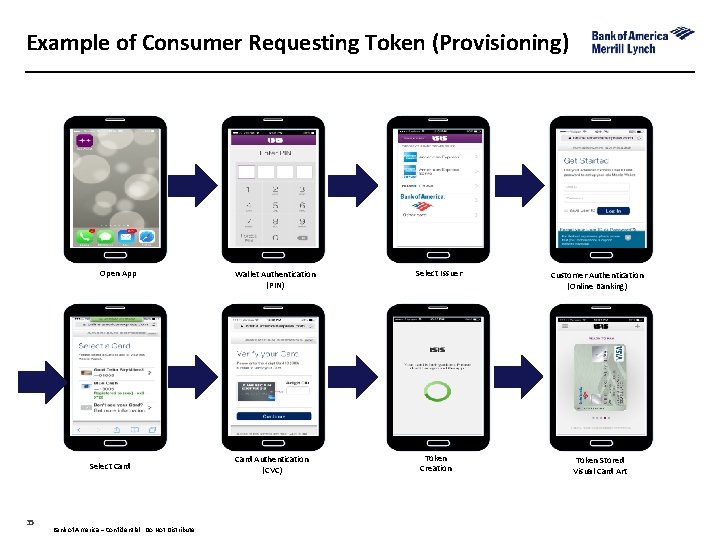
Example of Consumer Requesting Token (Provisioning) Open App Select Card 35 Bank of America – Confidential. Do Not Distribute Wallet Authentication (PIN) Card Authentication (CVC) Select Issuer Token Creation Customer Authentication (Online Banking) Token Stored Visual Card Art
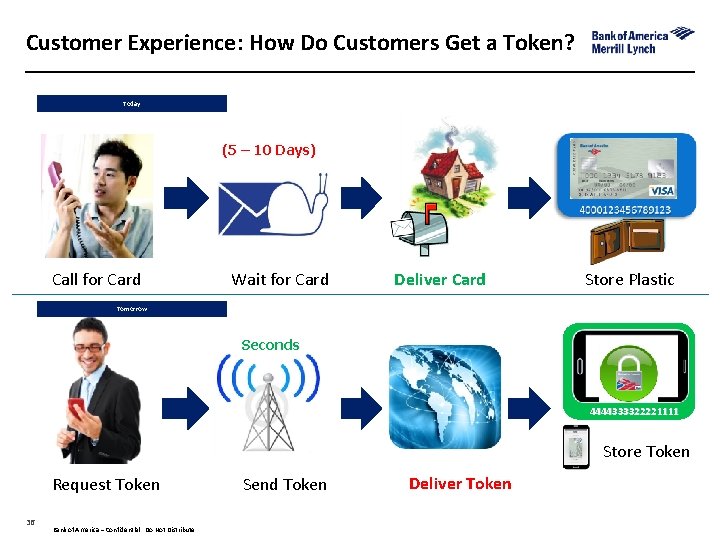
Customer Experience: How Do Customers Get a Token? Today (5 – 10 Days) Call for Card Wait for Card Deliver Card Store Plastic Tomorrow Seconds 4444333322221111 Store Token Request Token 36 Bank of America – Confidential. Do Not Distribute Send Token Deliver Token 36
Disclaimer “Bank of America Merrill Lynch” is the marketing name for the global banking and global markets businesses of Bank of America Corporation. Lending, derivatives, and other commercial banking activities are performed globally by banking affiliates of Bank of America Corporation, including Bank of America, N. A. , member FDIC. Securities, capital markets, strategic advisory, and other investment banking activities are performed globally by investment banking affiliates of Bank of America Corporation (“Investment Banking Affiliates”), including, in the United States, Merrill Lynch, Pierce, Fenner & Smith Incorporated and Merrill Lynch Professional Clearing Corp. , both of which are registered broker‐dealers and members of SIPC, and, in other jurisdictions, locally registered entities. Merrill Lynch, Pierce, Fenner & Smith Incorporated and Merrill Lynch Professional Clearing Corp. are registered as futures commission merchants with the CFTC and are members of the NFA. This document is intended for information purposes only and does not constitute a binding commitment to enter into any type of transaction or business relationship as a consequence of any information contained herein. These materials have been prepared by one or more subsidiaries of Bank of America Corporation solely for the client or potential client to whom such materials are directly addressed and delivered (the “Company”) in connection with an actual or potential business relationship and may not be used or relied upon for any purpose other than as specifically contemplated by a written agreement with us. We assume no obligation to update or otherwise revise these materials, which speak as of the date of this presentation (or another date, if so noted) and are subject to change without notice. Under no circumstances may a copy of this presentation be shown, copied, transmitted or otherwise given to any person other than your authorized representatives. Products and services that may be referenced in the accompanying materials may be provided through one or more affiliates of Bank of America, N. A. We are required to obtain, verify and record certain information that identifies our clients, which information includes the name and address of the client and other information that will allow us to identify the client in accordance with the USA Patriot Act (Title III of Pub. L. 107‐ 56, as amended (signed into law October 26, 2001)) and such other laws, rules and regulations. We do not provide legal, compliance, tax or accounting advice. Accordingly, any statements contained herein as to tax matters were neither written nor intended by us to be used and cannot be used by any taxpayer for the purpose of avoiding tax penalties that may be imposed on such taxpayer. For more information, including terms and conditions that apply to the service(s), please contact your Bank of America Merrill Lynch representative. Investment Banking Affiliates are not banks. The securities and financial instruments sold, offered or recommended by Investment Banking Affiliates, including without limitation money market mutual funds, are not bank deposits, are not guaranteed by, and are not otherwise obligations of, any bank, thrift or other subsidiary of Bank of America Corporation (unless explicitly stated otherwise), and are not insured by the Federal Deposit Insurance Corporation (“FDIC”) or any other governmental agency (unless explicitly stated otherwise). This document is intended for information purposes only and does not constitute investment advice or a recommendation or an offer or solicitation, and is not the basis for any contract to purchase or sell any security or other instrument, or for Investment Banking Affiliates or banking affiliates to enter into or arrange any type of transaction as a consequent of any information contained herein. With respect to investments in money market mutual funds, you should carefully consider a fund’s investment objectives, risks, charges, and expenses before investing. Although money market mutual funds seek to preserve the value of your investment at $1. 00 per share, it is possible to lose money by investing in money market mutual funds. The value of investments and the income derived from them may go down as well as up and you may not get back your original investment. The level of yield may be subject to fluctuation and is not guaranteed. Changes in rates of exchange between currencies may cause the value of investments to decrease or increase. We have adopted policies and guidelines designed to preserve the independence of our research analysts. These policies prohibit employees from offering research coverage, a favorable research rating or a specific price target or offering to change a research rating or price target as consideration for or an inducement to obtain business or other compensation. Copyright 2014 Bank of America Corporation. Bank of America N. A. , Member FDIC, Equal Housing Lender. 37
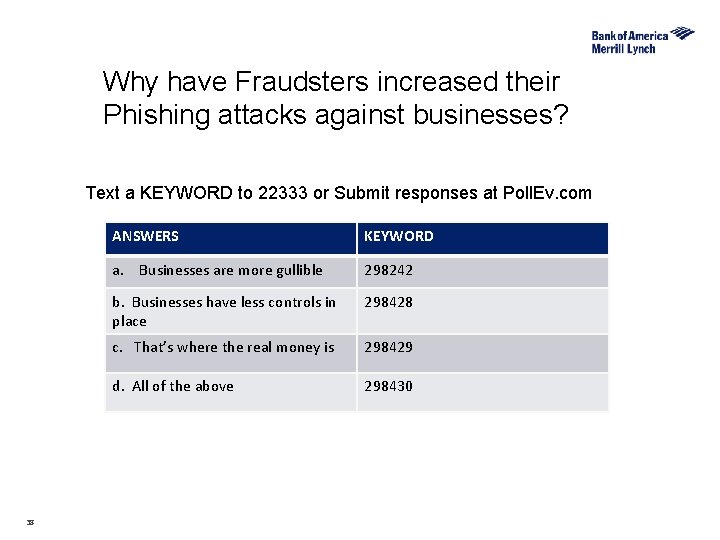
Why have Fraudsters increased their Phishing attacks against businesses? Text a KEYWORD to 22333 or Submit responses at Poll. Ev. com 38 ANSWERS KEYWORD a. Businesses are more gullible 298242 b. Businesses have less controls in place 298428 c. That’s where the real money is 298429 d. All of the above 298430
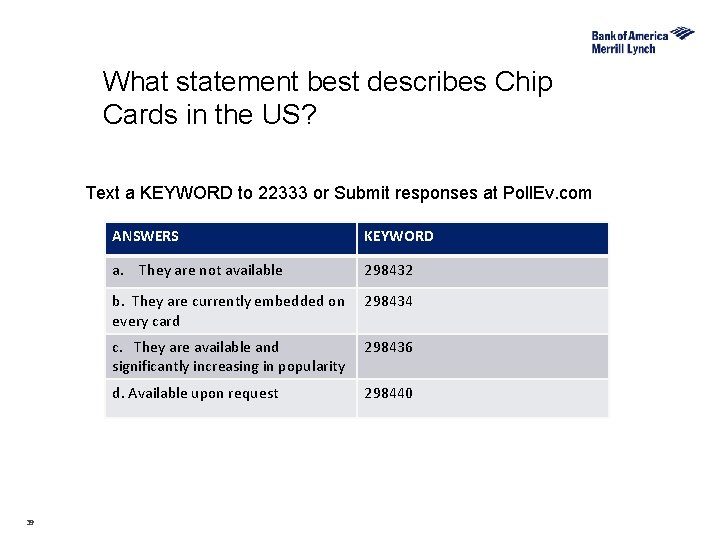
What statement best describes Chip Cards in the US? Text a KEYWORD to 22333 or Submit responses at Poll. Ev. com 39 ANSWERS KEYWORD a. They are not available 298432 b. They are currently embedded on every card 298434 c. They are available and significantly increasing in popularity 298436 d. Available upon request 298440
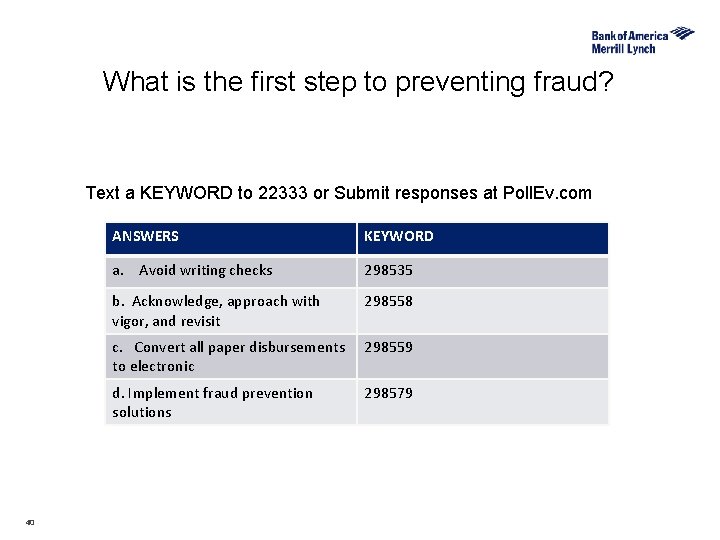
What is the first step to preventing fraud? Text a KEYWORD to 22333 or Submit responses at Poll. Ev. com 40 ANSWERS KEYWORD a. Avoid writing checks 298535 b. Acknowledge, approach with vigor, and revisit 298558 c. Convert all paper disbursements to electronic 298559 d. Implement fraud prevention solutions 298579
- Slides: 40