Multiplexing Multiple Access Multiplexing q SDM q FDMFDMA
- Slides: 38
Multiplexing & Multiple Access Multiplexing q SDM q FDM/FDMA q TDM/TDMA q CDMA q 1
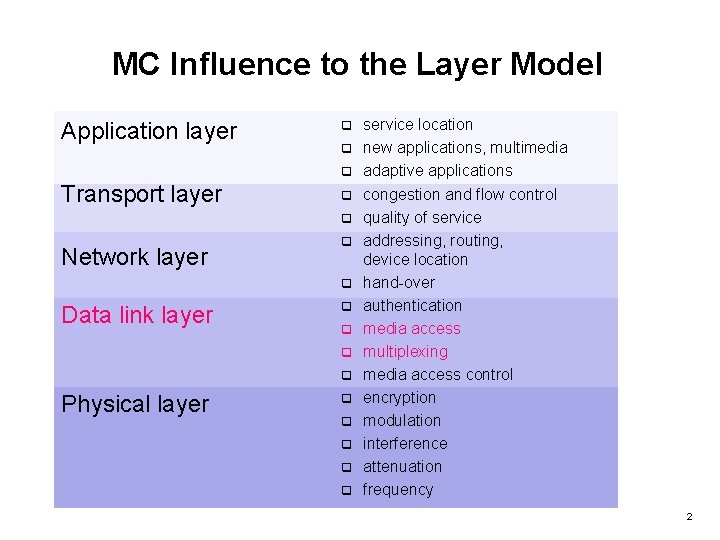
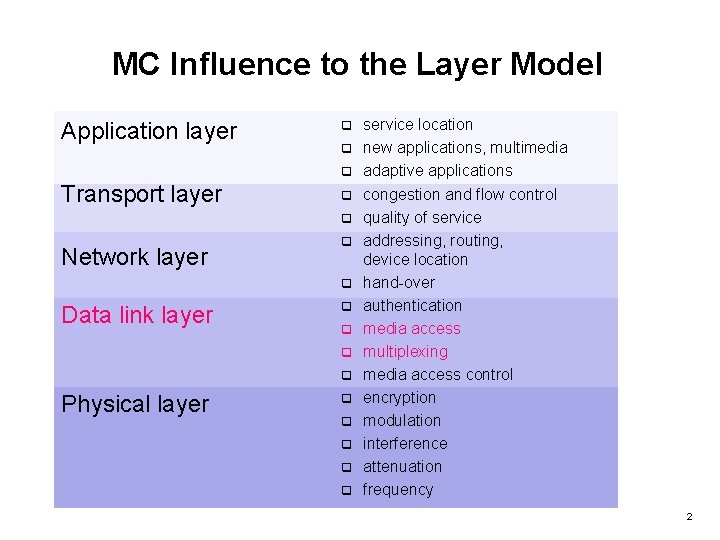
MC Influence to the Layer Model Application layer q q q Transport layer q q Network layer q q Data link layer q q Physical layer q q q service location new applications, multimedia adaptive applications congestion and flow control quality of service addressing, routing, device location hand-over authentication media access multiplexing media access control encryption modulation interference attenuation frequency 2
Multiple transmitters sending signals at the same time through the shared medium “air” How to share the medium (common channel) with other transmitters? Multiplexing Goal: Minimize the degree of interferences and maximize the bandwidth for data transmissions 3
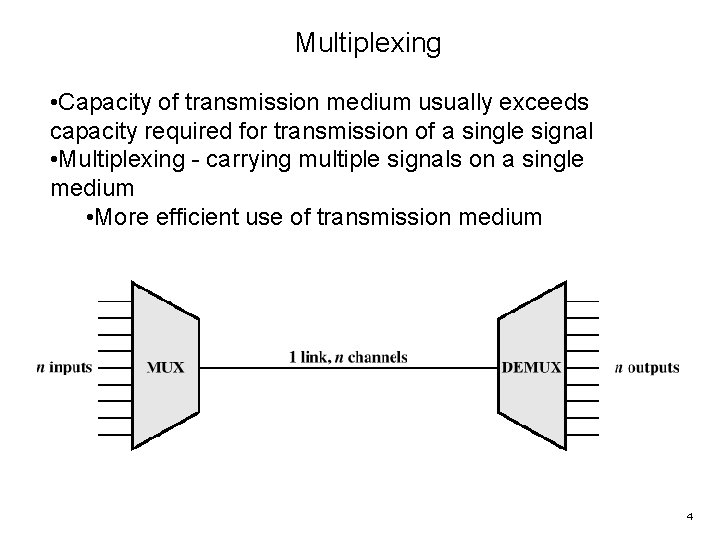
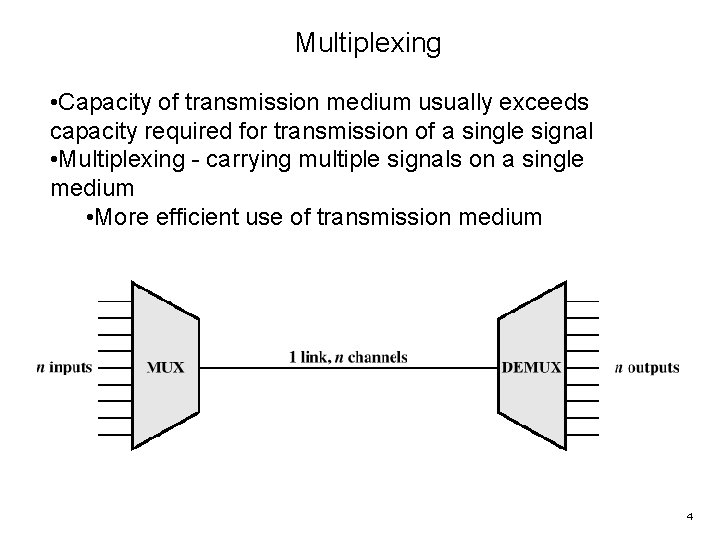
Multiplexing • Capacity of transmission medium usually exceeds capacity required for transmission of a single signal • Multiplexing - carrying multiple signals on a single medium • More efficient use of transmission medium 4
Reasons for Widespread Use of Multiplexing q Cost per kbps of transmission facility declines with an increase in the data rate q Cost of transmission and receiving equipment declines with increased data rate q Most individual data communicating devices require relatively modest data rate support 5
Multiplexing Techniques q Frequency-division multiplexing (FDM) q Takes advantage of the fact that the useful bandwidth of the medium exceeds the required bandwidth of a given signal q Time-division multiplexing (TDM) q Takes advantage of the fact that the achievable bit rate of the medium exceeds the required data rate of a digital signal 6
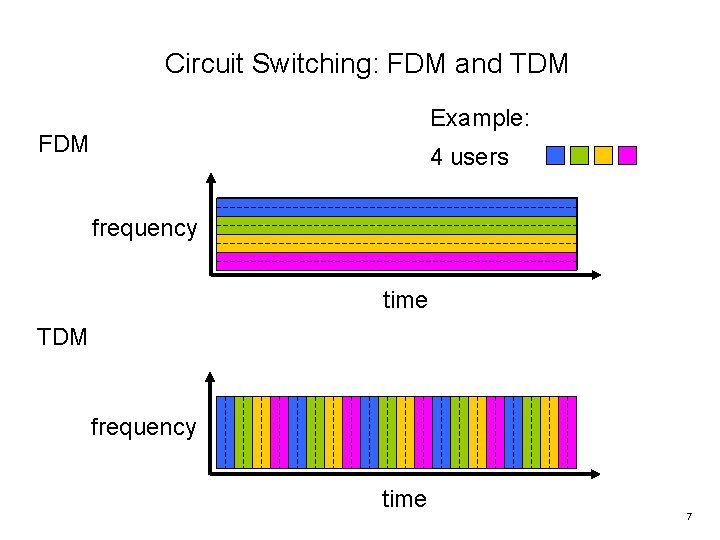
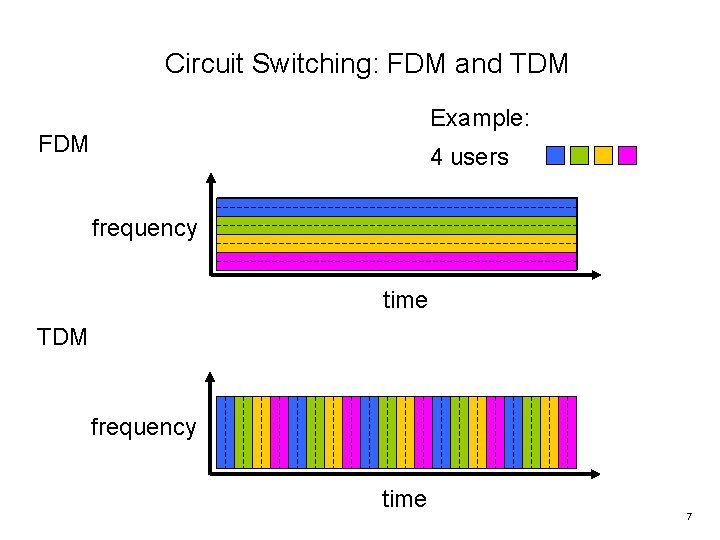
Circuit Switching: FDM and TDM Example: FDM 4 users frequency time TDM frequency time 7
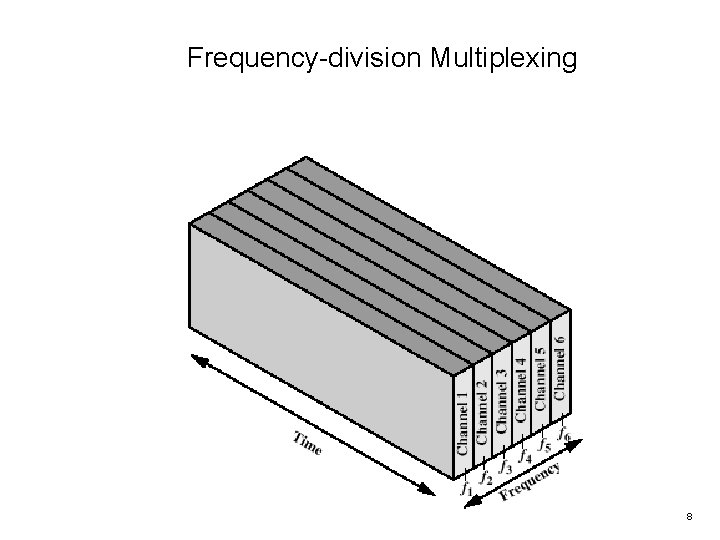
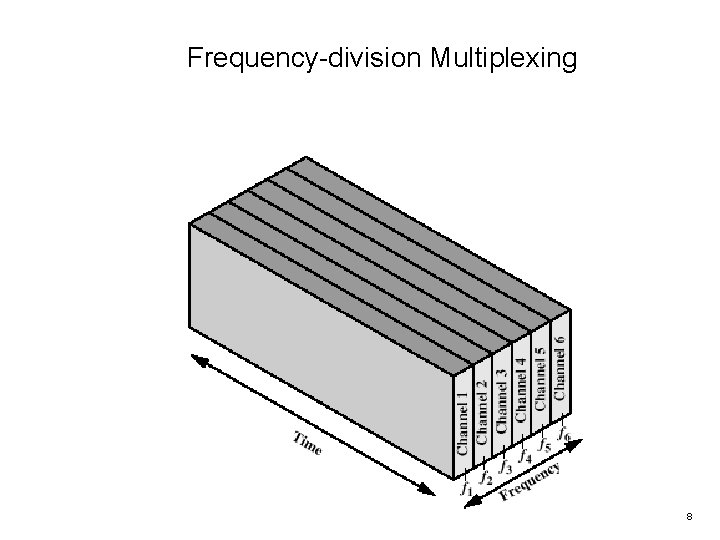
Frequency-division Multiplexing 8
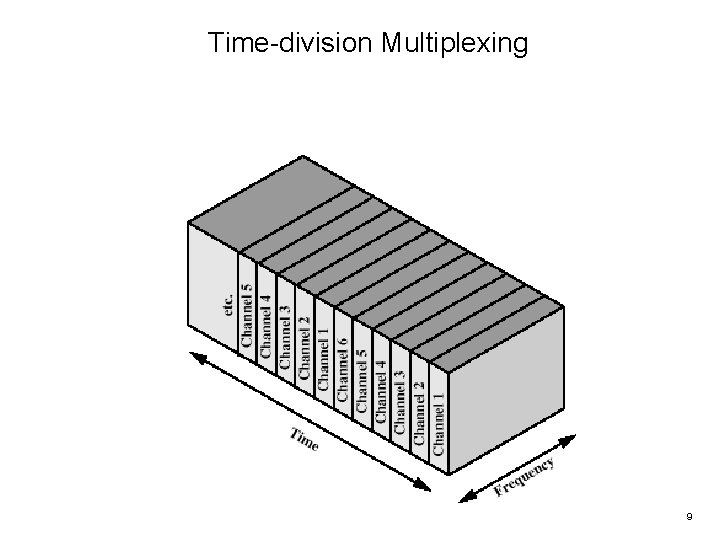
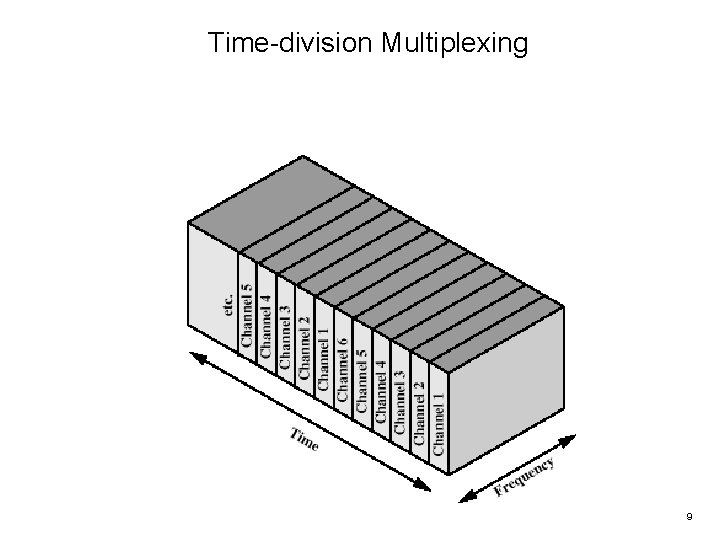
Time-division Multiplexing 9
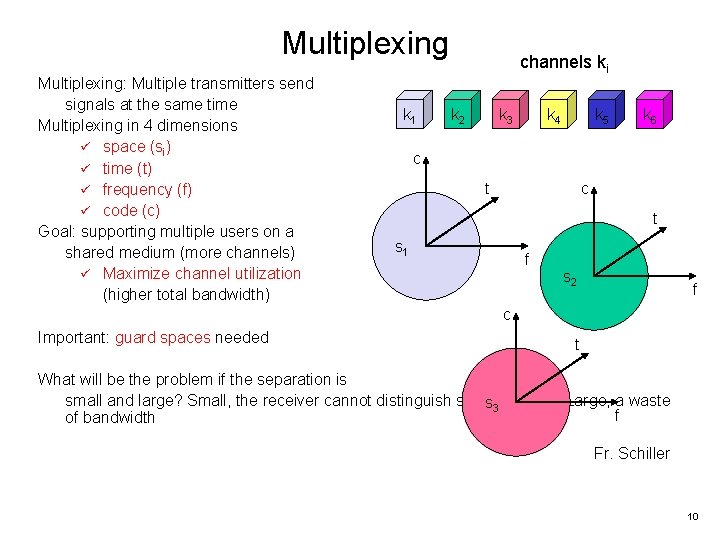
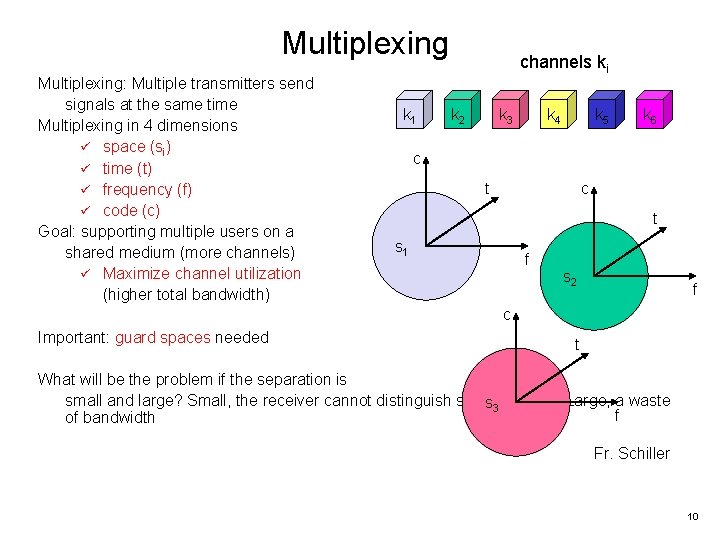
Multiplexing: Multiple transmitters send signals at the same time Multiplexing in 4 dimensions ü space (si) ü time (t) ü frequency (f) ü code (c) Goal: supporting multiple users on a shared medium (more channels) ü Maximize channel utilization (higher total bandwidth) k 1 channels ki k 2 k 3 k 4 k 5 k 6 c t s 1 f s 2 f c Important: guard spaces needed t What will be the problem if the separation is small and large? Small, the receiver cannot distinguish signals/noises. Large, a waste s 3 f of bandwidth Fr. Schiller 10
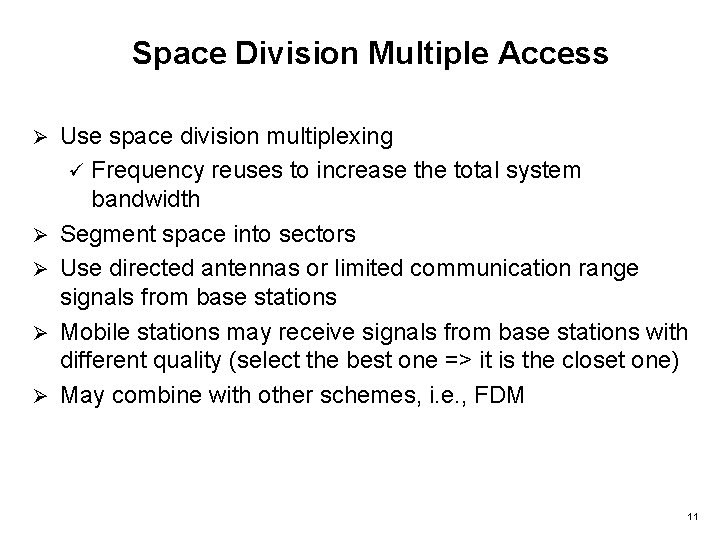
Space Division Multiple Access Ø Ø Ø Use space division multiplexing ü Frequency reuses to increase the total system bandwidth Segment space into sectors Use directed antennas or limited communication range signals from base stations Mobile stations may receive signals from base stations with different quality (select the best one => it is the closet one) May combine with other schemes, i. e. , FDM 11
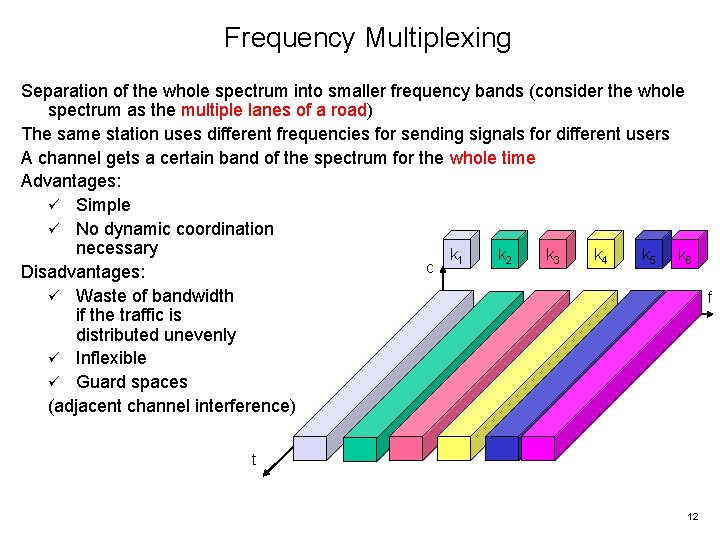
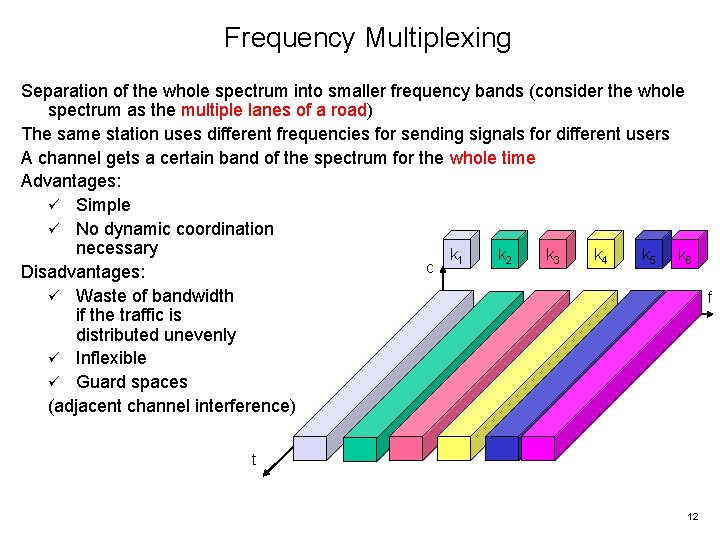
Frequency Multiplexing Separation of the whole spectrum into smaller frequency bands (consider the whole spectrum as the multiple lanes of a road) The same station uses different frequencies for sending signals for different users A channel gets a certain band of the spectrum for the whole time Advantages: ü Simple ü No dynamic coordination necessary k 1 k 2 k 3 k 4 k 5 k 6 c Disadvantages: ü Waste of bandwidth f if the traffic is distributed unevenly ü Inflexible ü Guard spaces (adjacent channel interference) t 12
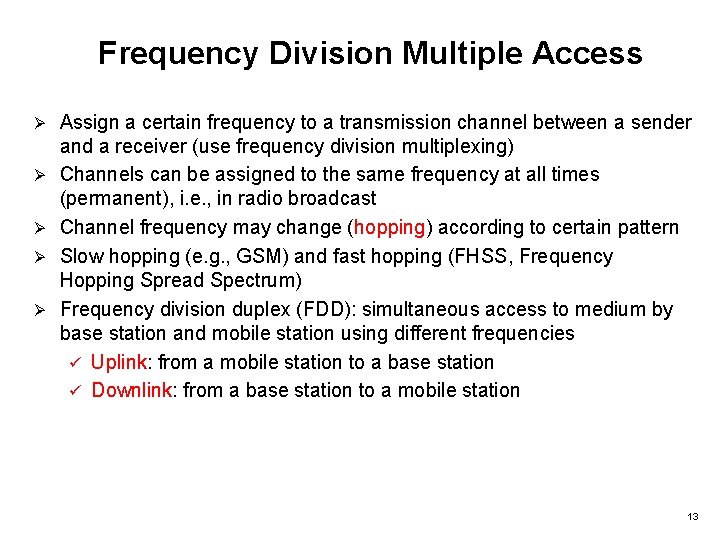
Frequency Division Multiple Access Ø Ø Ø Assign a certain frequency to a transmission channel between a sender and a receiver (use frequency division multiplexing) Channels can be assigned to the same frequency at all times (permanent), i. e. , in radio broadcast Channel frequency may change (hopping) according to certain pattern Slow hopping (e. g. , GSM) and fast hopping (FHSS, Frequency Hopping Spread Spectrum) Frequency division duplex (FDD): simultaneous access to medium by base station and mobile station using different frequencies ü Uplink: from a mobile station to a base station ü Downlink: from a base station to a mobile station 13
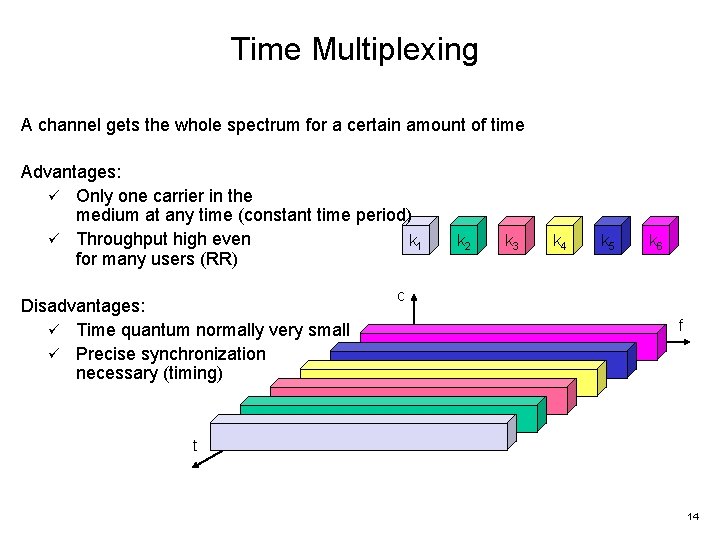
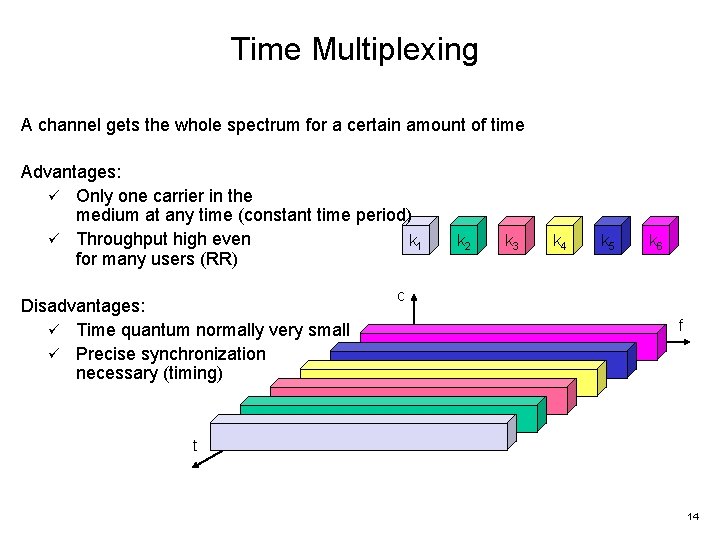
Time Multiplexing A channel gets the whole spectrum for a certain amount of time Advantages: ü Only one carrier in the medium at any time (constant time period) ü Throughput high even k 1 for many users (RR) Disadvantages: ü Time quantum normally very small ü Precise synchronization necessary (timing) k 2 k 3 k 4 k 5 k 6 c f t 14
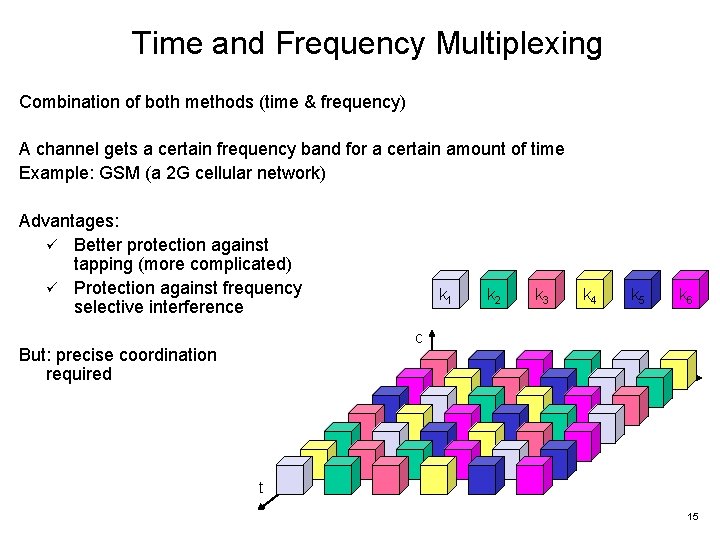
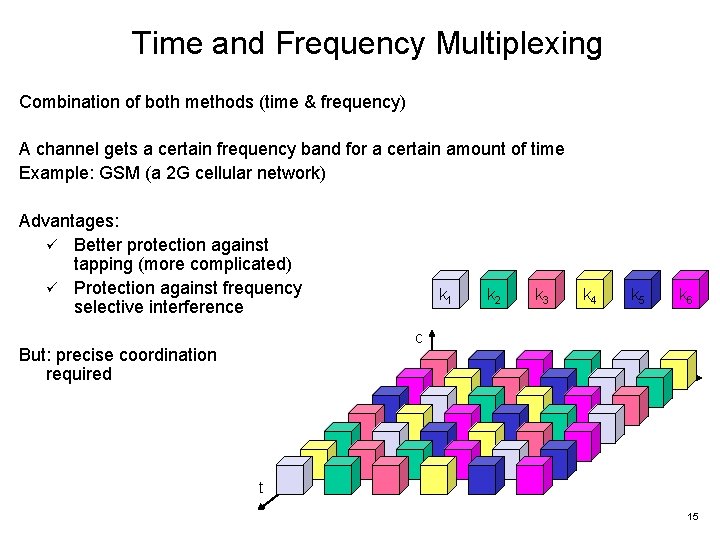
Time and Frequency Multiplexing Combination of both methods (time & frequency) A channel gets a certain frequency band for a certain amount of time Example: GSM (a 2 G cellular network) Advantages: ü Better protection against tapping (more complicated) ü Protection against frequency selective interference k 1 k 2 k 3 k 4 k 5 k 6 c But: precise coordination required f t 15
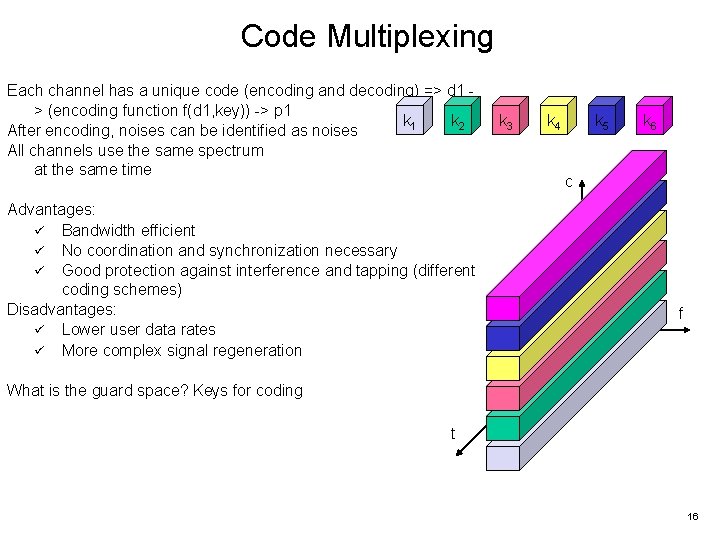
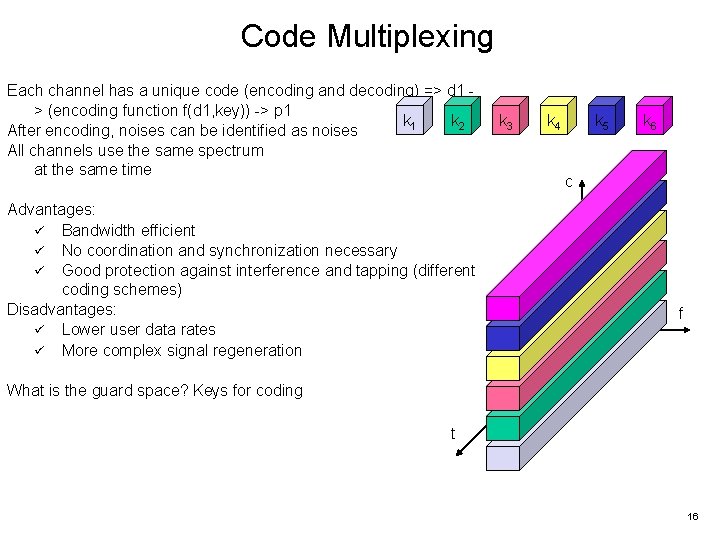
Code Multiplexing Each channel has a unique code (encoding and decoding) => d 1 > (encoding function f(d 1, key)) -> p 1 k 2 After encoding, noises can be identified as noises All channels use the same spectrum at the same time Advantages: ü Bandwidth efficient ü No coordination and synchronization necessary ü Good protection against interference and tapping (different coding schemes) Disadvantages: ü Lower user data rates ü More complex signal regeneration k 3 k 4 k 5 k 6 c f What is the guard space? Keys for coding t 16
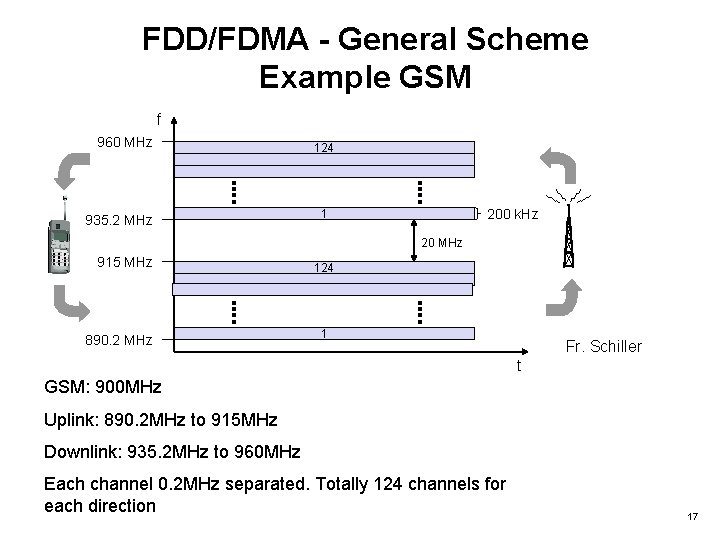
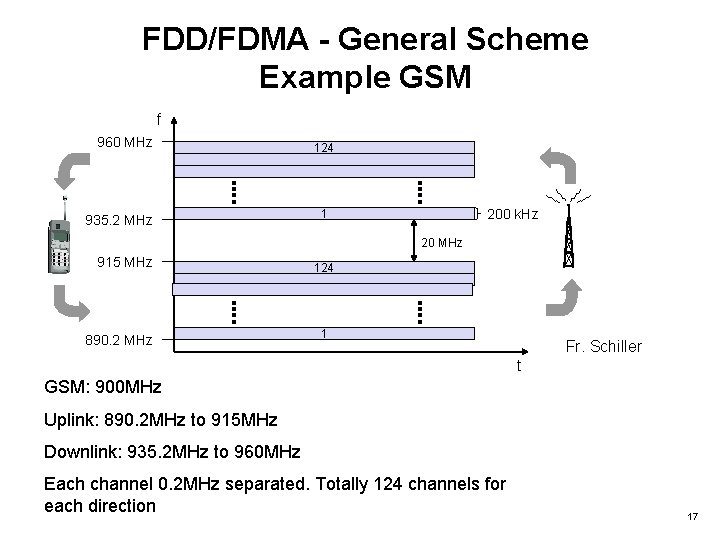
FDD/FDMA - General Scheme Example GSM f 960 MHz 935. 2 MHz 124 200 k. Hz 1 20 MHz 915 MHz 890. 2 MHz 124 1 Fr. Schiller t GSM: 900 MHz Uplink: 890. 2 MHz to 915 MHz Downlink: 935. 2 MHz to 960 MHz Each channel 0. 2 MHz separated. Totally 124 channels for each direction 17
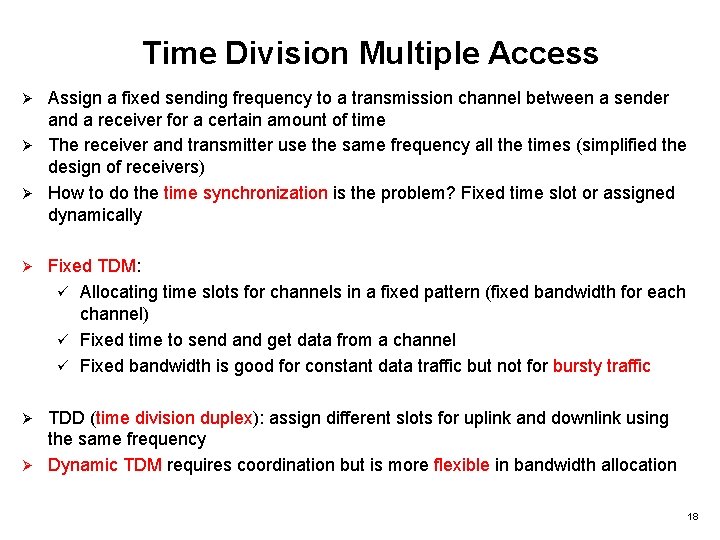
Time Division Multiple Access Assign a fixed sending frequency to a transmission channel between a sender and a receiver for a certain amount of time Ø The receiver and transmitter use the same frequency all the times (simplified the design of receivers) Ø How to do the time synchronization is the problem? Fixed time slot or assigned dynamically Ø Ø Fixed TDM: ü Allocating time slots for channels in a fixed pattern (fixed bandwidth for each channel) ü Fixed time to send and get data from a channel ü Fixed bandwidth is good for constant data traffic but not for bursty traffic TDD (time division duplex): assign different slots for uplink and downlink using the same frequency Ø Dynamic TDM requires coordination but is more flexible in bandwidth allocation Ø 18
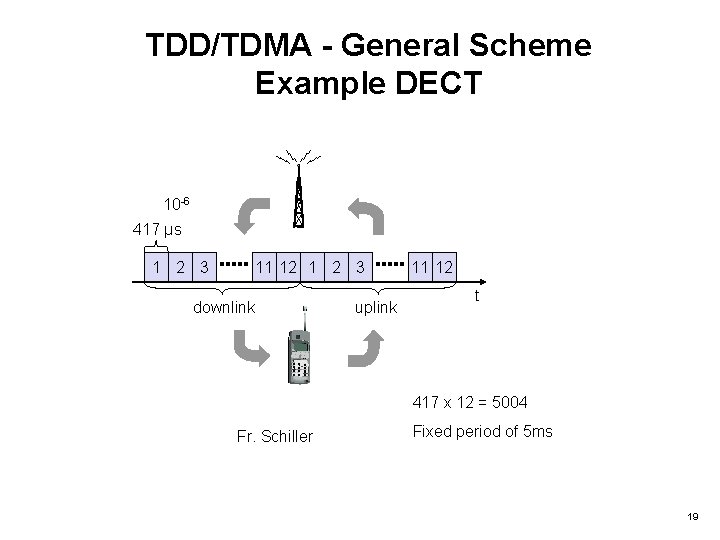
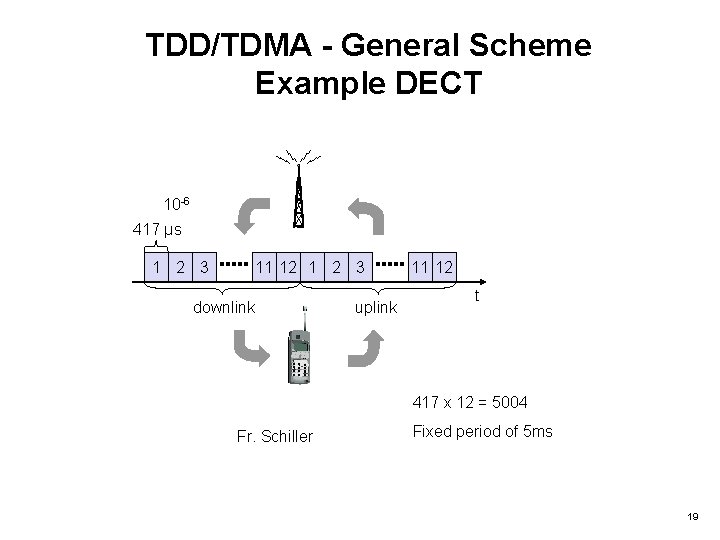
TDD/TDMA - General Scheme Example DECT 10 -6 417 µs 1 2 3 11 12 1 2 3 downlink uplink 11 12 t 417 x 12 = 5004 Fr. Schiller Fixed period of 5 ms 19
Polling Mechanisms If one terminal can be heard by all others, this “central” terminal can poll all other terminals according to a certain scheme, i. e. round-robin or random ü Now all schemes known from fixed networks can be used (typical mainframe - terminal scenario) Ø Example: Randomly Addressed Polling ü Base station signals readiness to all mobile terminals ü Terminals ready to send can now transmit a random number without collision with the help of CDMA or FDMA (the random number can be seen as dynamic address) ü The base station now chooses one address for polling from the list of all random numbers (collision if two terminals choose the same address) ü The base station acknowledges correct packets and continues polling the next terminal ü This cycle starts again after polling all terminals of the list Ø 20
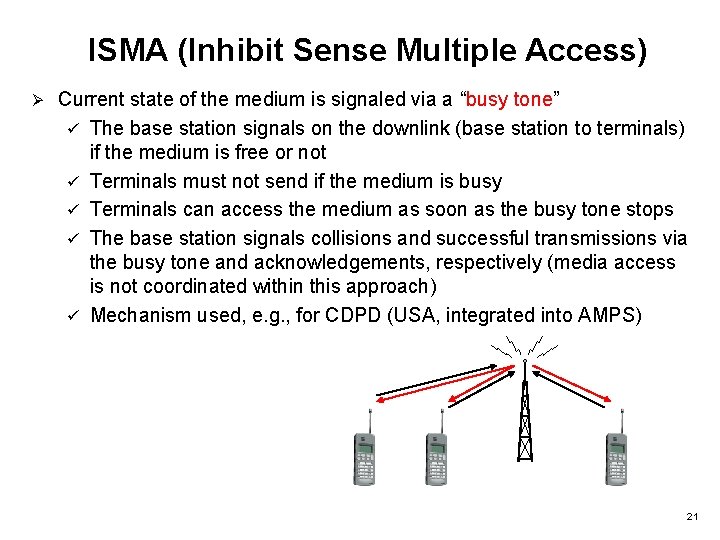
ISMA (Inhibit Sense Multiple Access) Ø Current state of the medium is signaled via a “busy tone” ü The base station signals on the downlink (base station to terminals) if the medium is free or not ü Terminals must not send if the medium is busy ü Terminals can access the medium as soon as the busy tone stops ü The base station signals collisions and successful transmissions via the busy tone and acknowledgements, respectively (media access is not coordinated within this approach) ü Mechanism used, e. g. , for CDPD (USA, integrated into AMPS) 21
Code Division Multiple Access Ø Ø Ø Ø All terminals send on the same frequency probably at the same time and can use the whole bandwidth of the transmission channel So, how the receivers identify the data/signals for them? Each sender has a unique random number (code), the sender XORs the signal with this random number ü Different senders use different codes ü The codes separate the signals from different senders The encoded signals are concatenated together for sending, i. e. , as a signal stream of signals The receiver “tunes” into this signal stream if it knows the pseudo random number. Tuning is done via a correlation function The received decodes the signal stream using the known code to identify the data for it Different receivers received different data as they use different codes 22
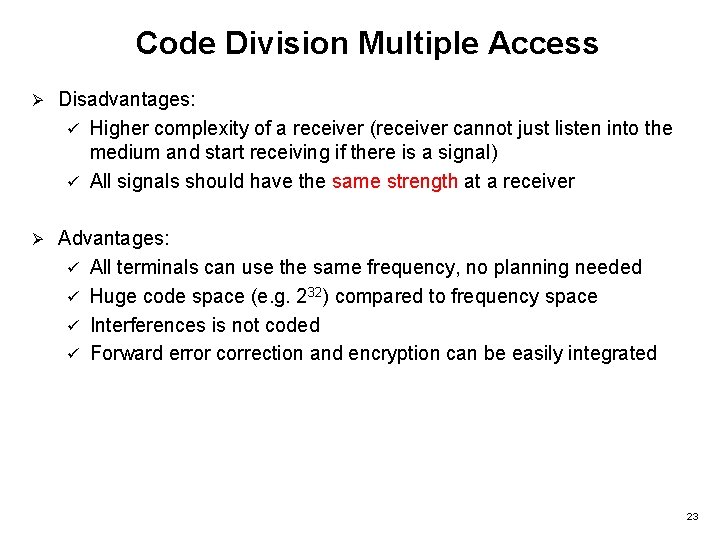
Code Division Multiple Access Ø Disadvantages: ü Higher complexity of a receiver (receiver cannot just listen into the medium and start receiving if there is a signal) ü All signals should have the same strength at a receiver Ø Advantages: ü All terminals can use the same frequency, no planning needed ü Huge code space (e. g. 232) compared to frequency space ü Interferences is not coded ü Forward error correction and encryption can be easily integrated 23
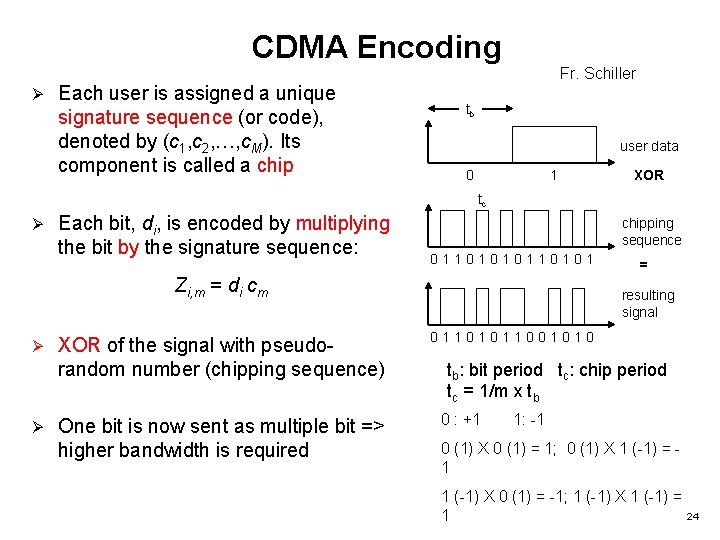
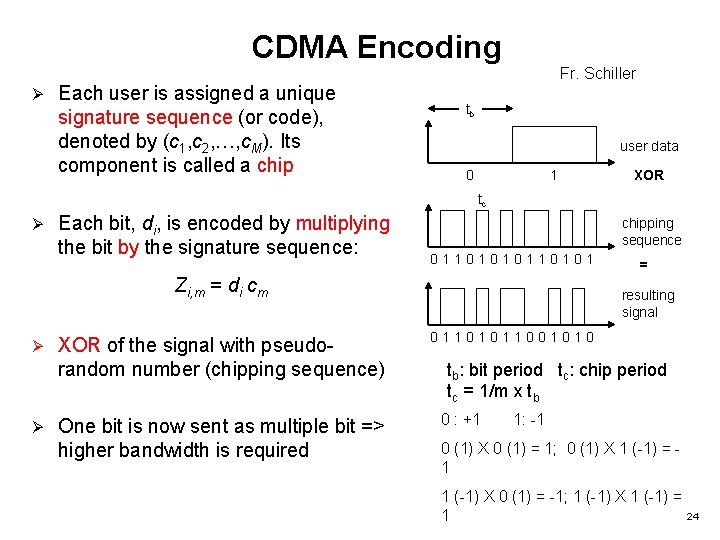
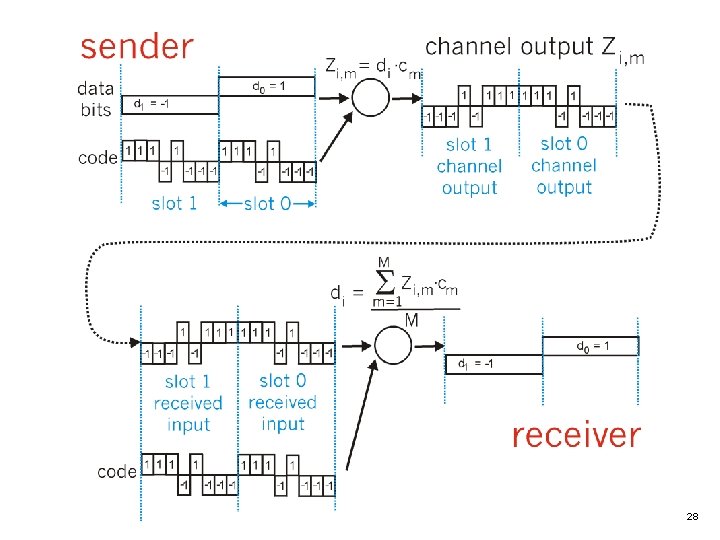
CDMA Encoding Ø Each user is assigned a unique signature sequence (or code), denoted by (c 1, c 2, …, c. M). Its component is called a chip Fr. Schiller tb user data 0 1 XOR tc Ø Each bit, di, is encoded by multiplying the bit by the signature sequence: chipping sequence 0110101 Zi, m = di cm Ø Ø XOR of the signal with pseudorandom number (chipping sequence) One bit is now sent as multiple bit => higher bandwidth is required = resulting signal 01101011001010 tb: bit period tc: chip period tc = 1/m x tb 0 : +1 1: -1 0 (1) X 0 (1) = 1; 0 (1) X 1 (-1) = 1 1 (-1) X 0 (1) = -1; 1 (-1) X 1 (-1) = 1 24
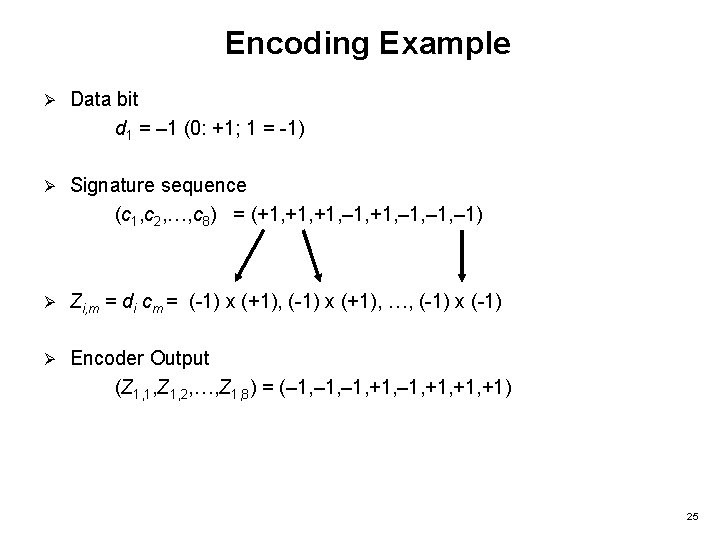
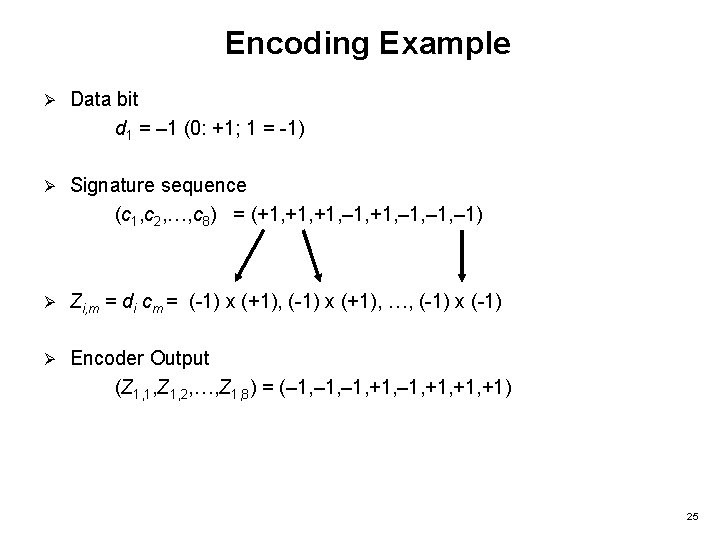
Encoding Example Ø Data bit d 1 = – 1 (0: +1; 1 = -1) Ø Signature sequence (c 1, c 2, …, c 8) = (+1, +1, – 1, – 1) Ø Zi, m = di cm = (-1) x (+1), …, (-1) x (-1) Ø Encoder Output (Z 1, 1, Z 1, 2, …, Z 1, 8) = (– 1, +1, +1, +1) 25
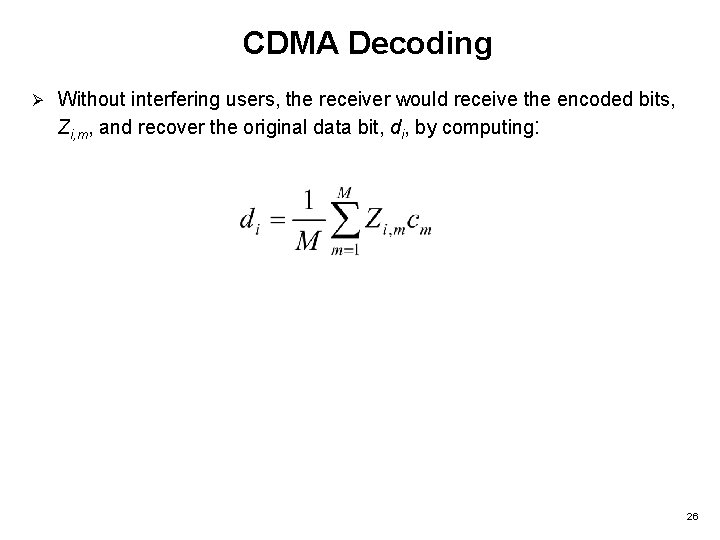
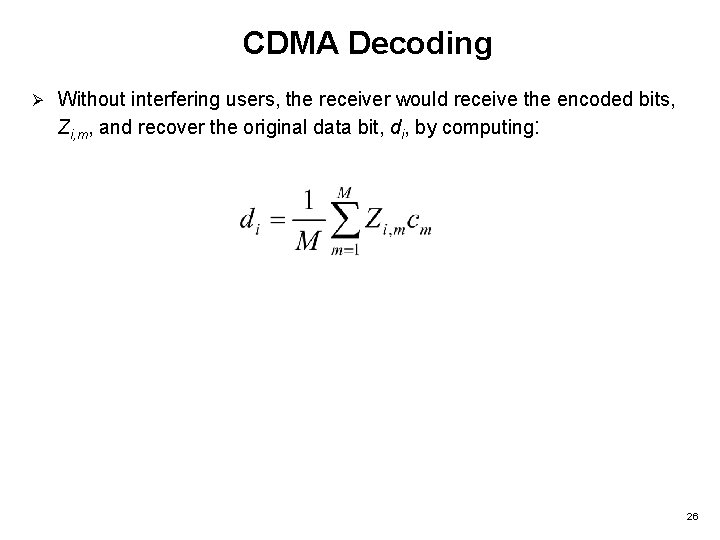
CDMA Decoding Ø Without interfering users, the receiver would receive the encoded bits, Zi, m, and recover the original data bit, di, by computing: 26
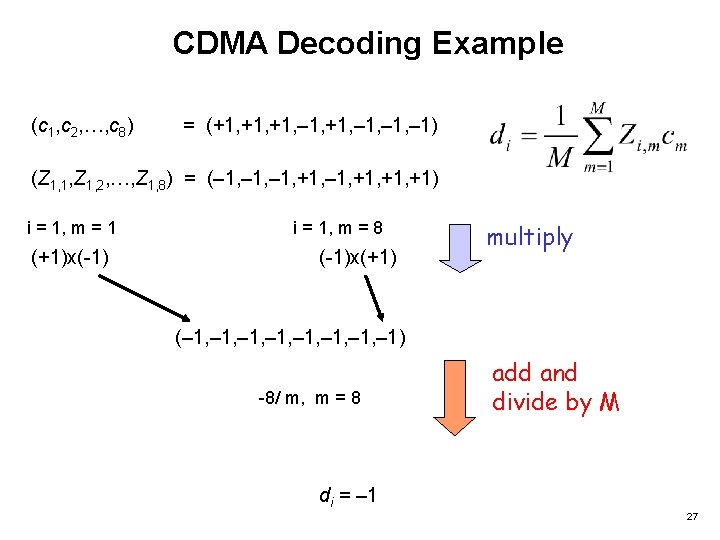
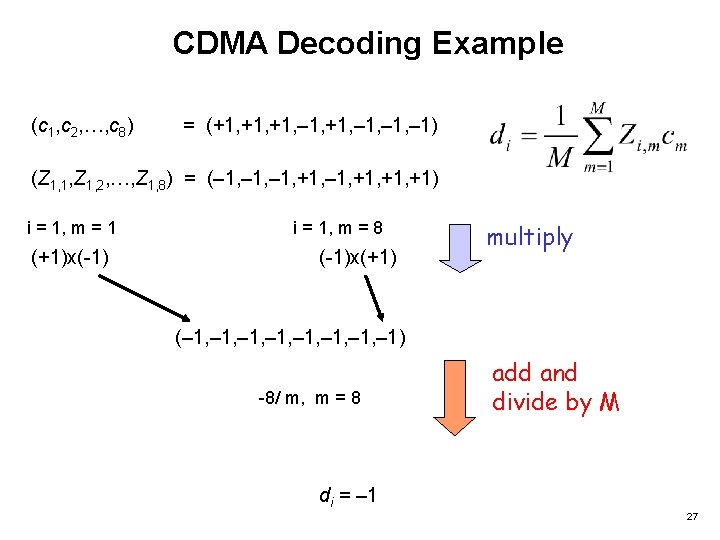
CDMA Decoding Example (c 1, c 2, …, c 8) = (+1, +1, – 1, – 1) (Z 1, 1, Z 1, 2, …, Z 1, 8) = (– 1, +1, +1, +1) i = 1, m = 1 (+1)x(-1) i = 1, m = 8 (-1)x(+1) multiply (– 1, – 1, – 1) -8/ m, m = 8 add and divide by M di = – 1 27
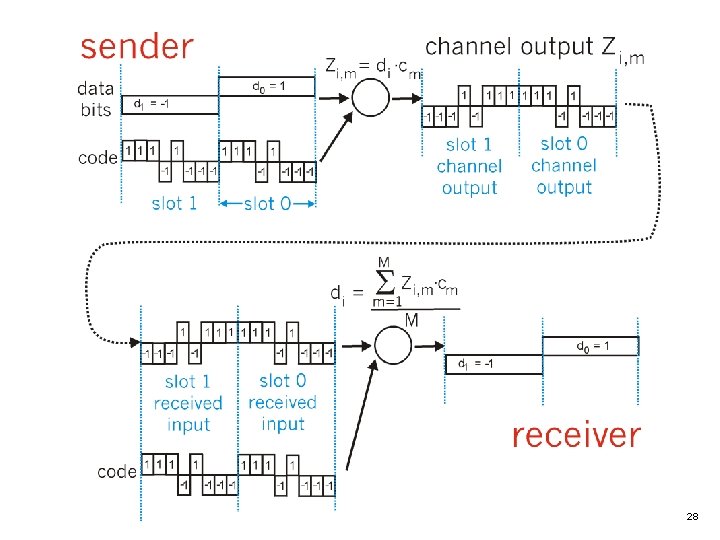
28
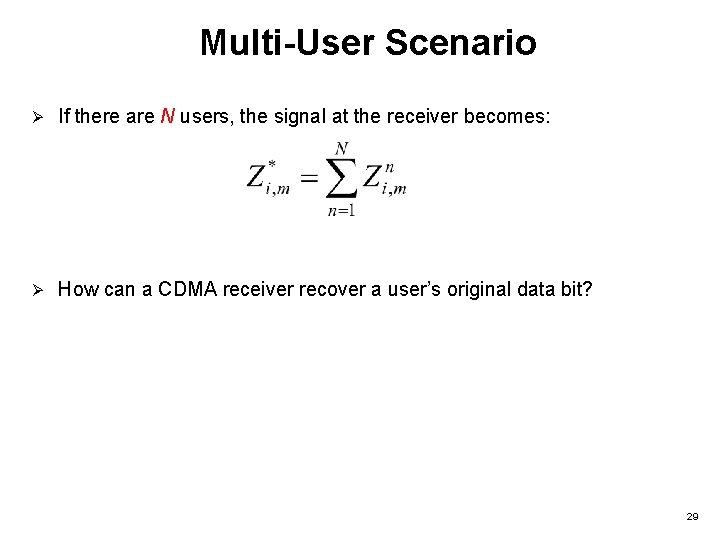
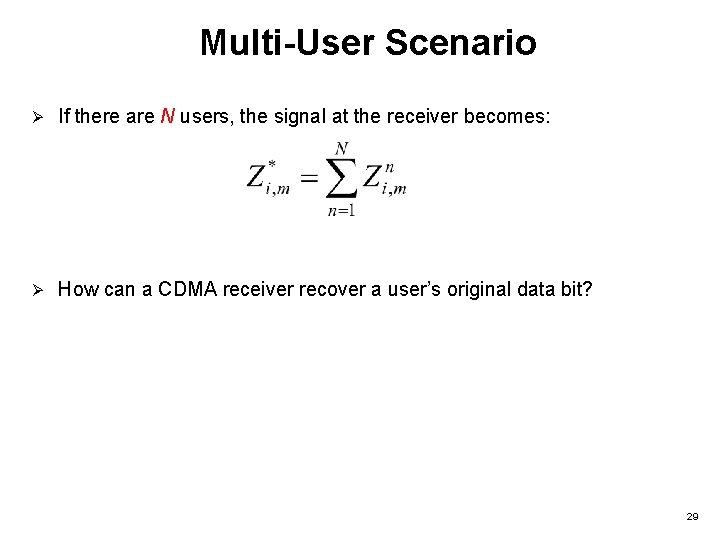
Multi-User Scenario Ø If there are N users, the signal at the receiver becomes: Ø How can a CDMA receiver recover a user’s original data bit? 29
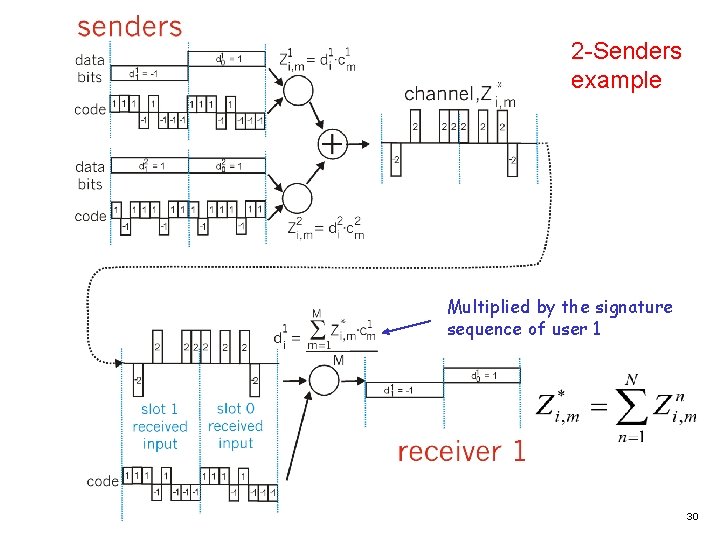
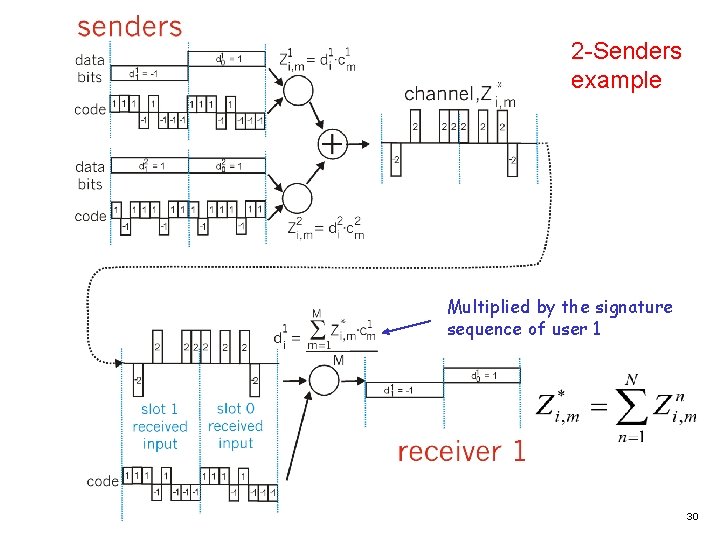
2 -Senders example Multiplied by the signature sequence of user 1 30
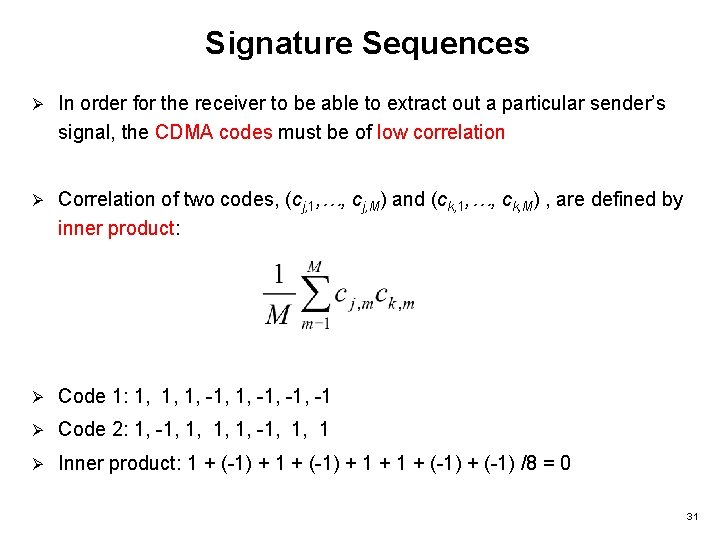
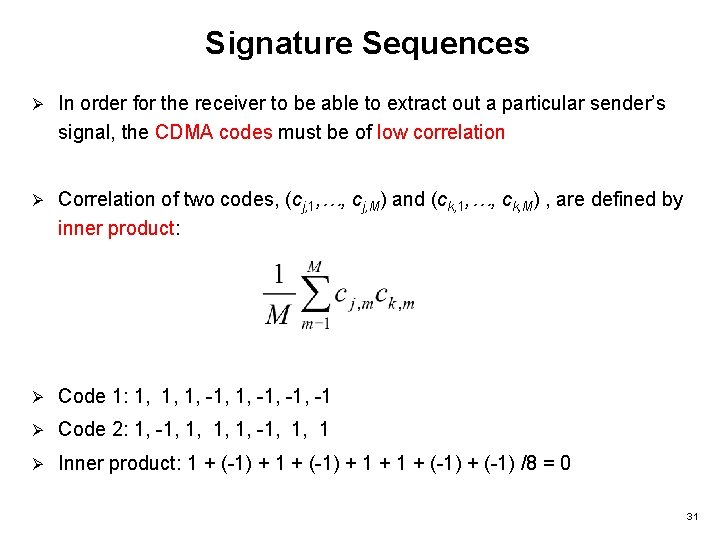
Signature Sequences Ø In order for the receiver to be able to extract out a particular sender’s signal, the CDMA codes must be of low correlation Ø Correlation of two codes, (cj, 1, …, cj, M) and (ck, 1, …, ck, M) , are defined by inner product: Ø Code 1: 1, 1, 1, -1, -1 Ø Code 2: 1, -1, 1, 1 Ø Inner product: 1 + (-1) + (-1) /8 = 0 31
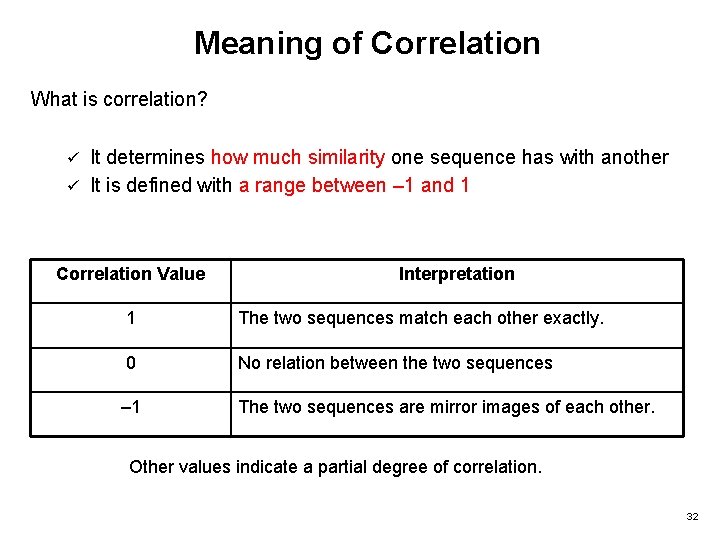
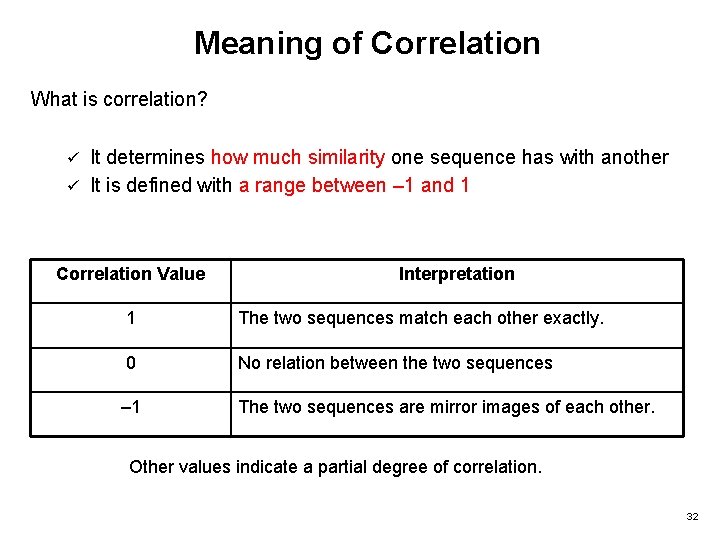
Meaning of Correlation What is correlation? It determines how much similarity one sequence has with another ü It is defined with a range between – 1 and 1 ü Correlation Value Interpretation 1 The two sequences match each other exactly. 0 No relation between the two sequences – 1 The two sequences are mirror images of each other. Other values indicate a partial degree of correlation. 32
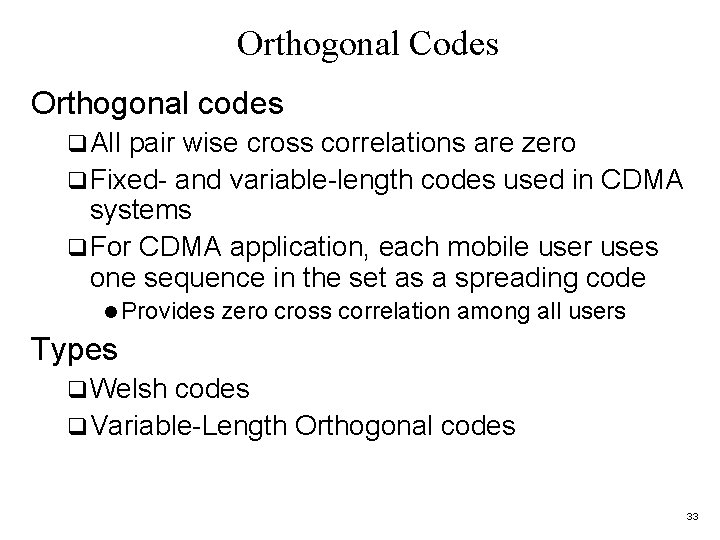
Orthogonal Codes Orthogonal codes q All pair wise cross correlations are zero q Fixed- and variable-length codes used in CDMA systems q For CDMA application, each mobile user uses one sequence in the set as a spreading code l Provides zero cross correlation among all users Types q Welsh codes q Variable-Length Orthogonal codes 33
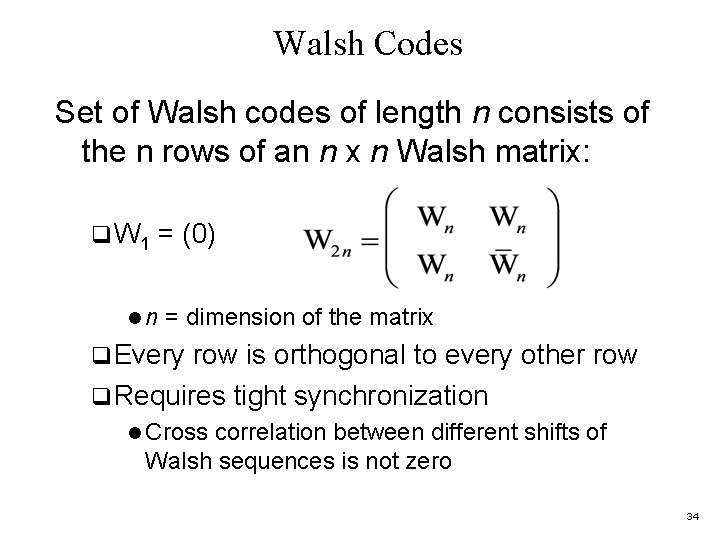
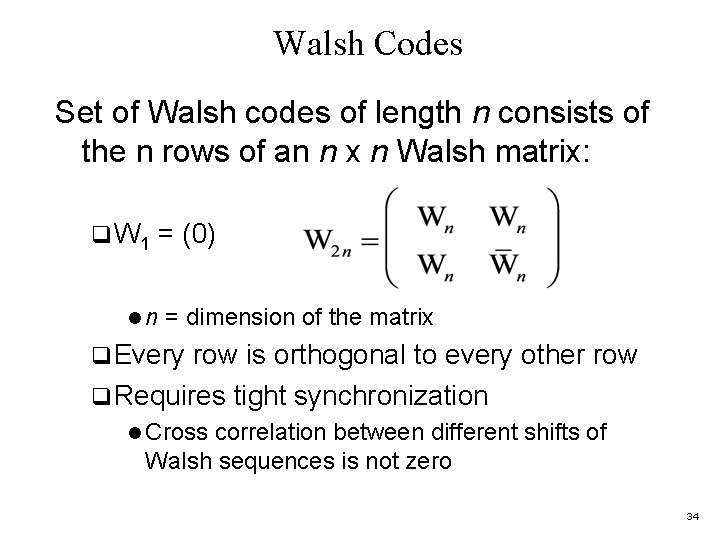
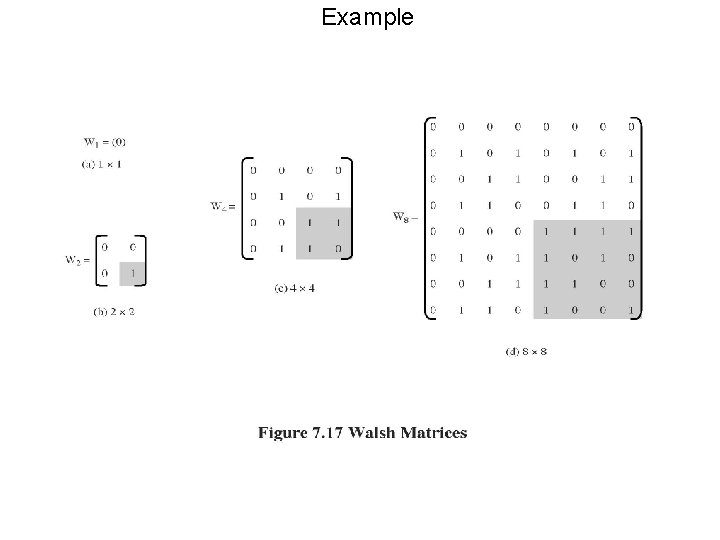
Walsh Codes Set of Walsh codes of length n consists of the n rows of an n x n Walsh matrix: q W 1 = (0) ln = dimension of the matrix q Every row is orthogonal to every other row q Requires tight synchronization l Cross correlation between different shifts of Walsh sequences is not zero 34
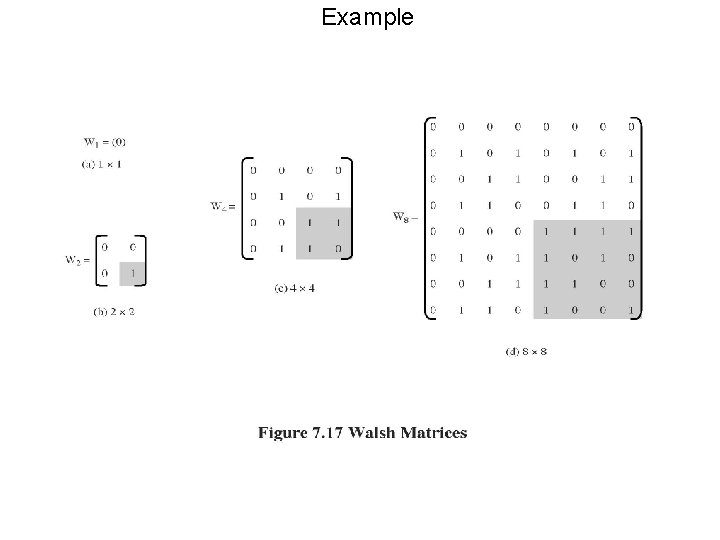
Example 35
Typical Multiple Spreading Approach q Spread data rate by an orthogonal code (channelization code) q Provides mutual orthogonality among all users in the same cell q Further spread result by a Pseudo-Noise (PN) sequence (scrambling code) q Provides mutual randomness (low cross correlation) between users in different cells 36
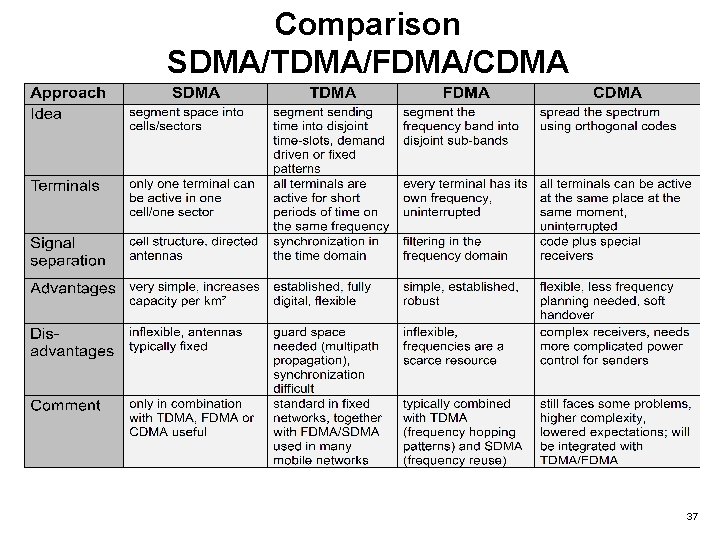
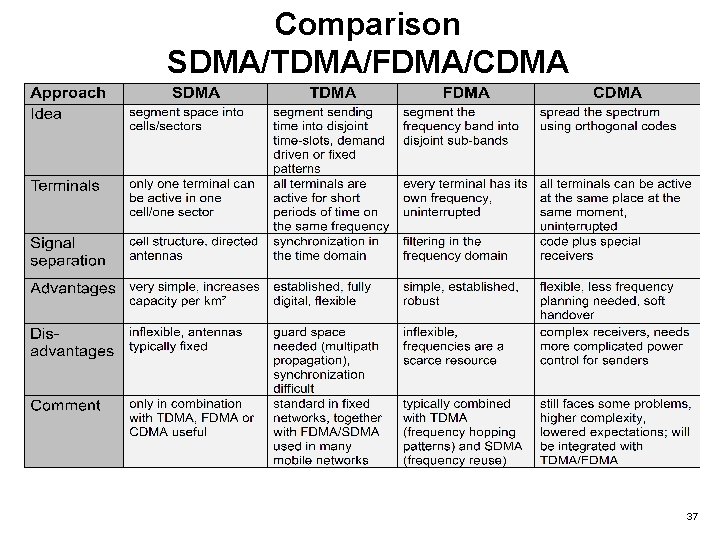
Comparison SDMA/TDMA/FDMA/CDMA 37
References Schiller: Ch. 2. 1, 2. 2, 2. 4, 2. 5, 2. 6. 1 -2. 6. 4 Ø Schiller: Ch 3. 1, 3. 2, 3. 3, 3. 4. 1, 3. 4. 8 , 3. 4. 9, 3. 4. 10, 3. 5, 3. 6 Ø Schiller, Mobile Communications, sections 4. 1 (except 4. 1. 7) and 4. 4. 2, 4. 4. 4 – 4. 4. 6 (except the protocol stack) Ø Wireless Communications & Networks, 2 Edition, Pearson, William Stallings (Ch 7) Ø 38