MSG 328 AntiSpam in Exchange 2003 Max Ciccotosto


- Slides: 30
MSG 328 Anti-Spam in Exchange 2003 Max Ciccotosto Program Manager - Exchange Microsoft Corporation
Agenda The Spam Problem Exchange 2003 Anti-Spam Features Client Server Integration Deployment
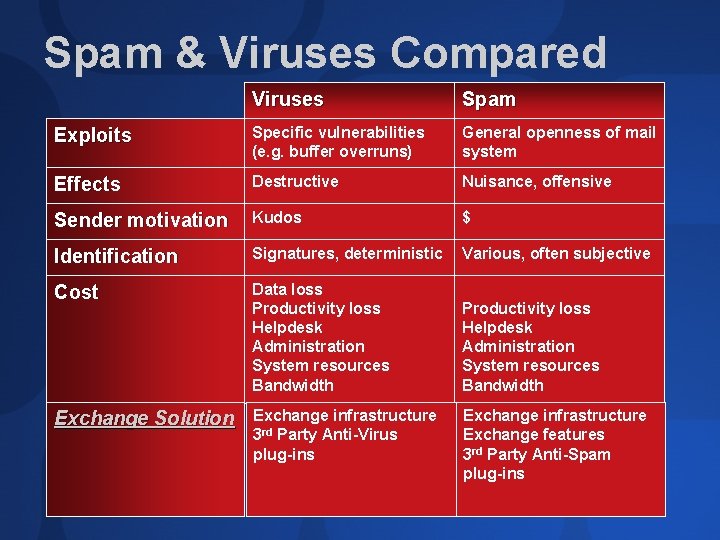
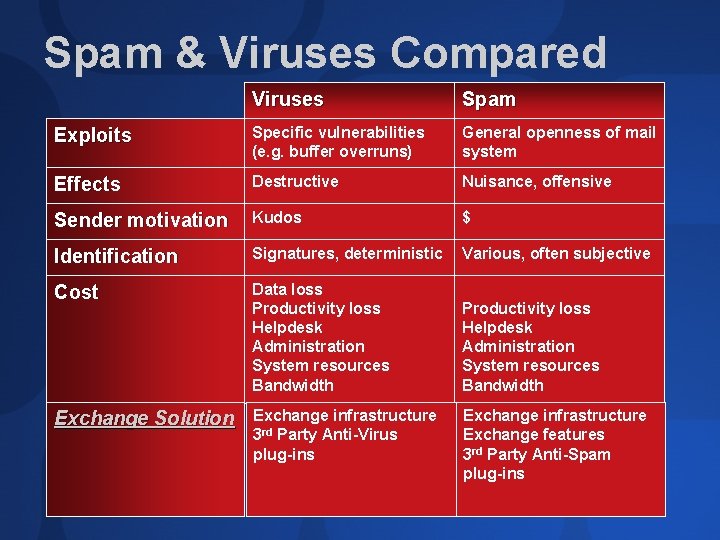
Spam & Viruses Compared Viruses Spam Exploits Specific vulnerabilities (e. g. buffer overruns) General openness of mail system Effects Destructive Nuisance, offensive Sender motivation Kudos $ Identification Signatures, deterministic Various, often subjective Cost Data loss Productivity loss Helpdesk Administration System resources Bandwidth Exchange Solution Exchange infrastructure 3 rd Party Anti-Virus plug-ins Exchange infrastructure Exchange features 3 rd Party Anti-Spam plug-ins
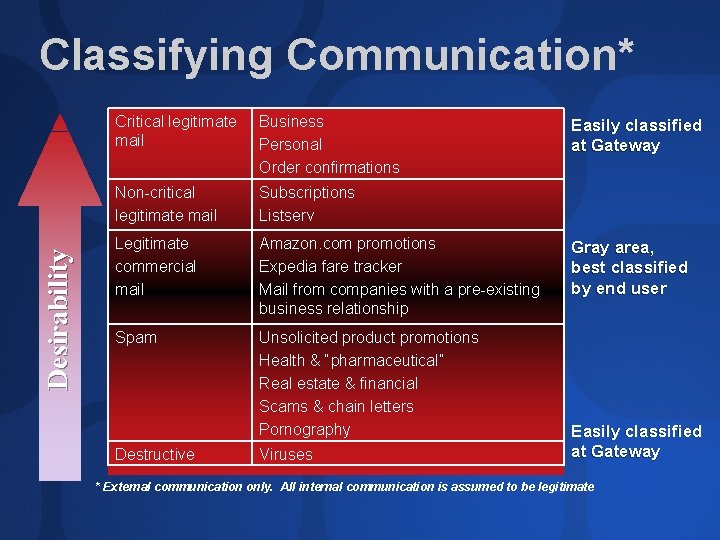
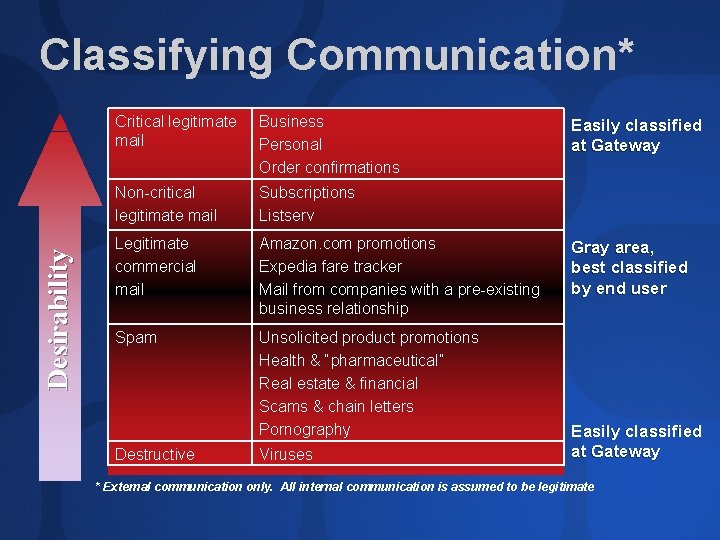
Desirability Classifying Communication* Critical legitimate mail Business Personal Order confirmations Non-critical legitimate mail Subscriptions Listserv Legitimate commercial mail Amazon. com promotions Expedia fare tracker Mail from companies with a pre-existing business relationship Spam Unsolicited product promotions Health & “pharmaceutical” Real estate & financial Scams & chain letters Pornography Destructive Viruses Easily classified at Gateway Gray area, best classified by end user Easily classified at Gateway * External communication only. All internal communication is assumed to be legitimate
Enterprise Requirements for Anti-Spam False positives are the #1 enterprise concern Valid mail in the junk folder is as good as lost Block at the gateway whenever possible User never sees it Reduced impact on bandwidth & other system resources Administration End to end solutions Easy to manage Balance corporate & end user control Legal considerations

Exchange 2003 Anti-Spam Features
Connection Filtering (IP based) Global Allow and Deny lists Configure individual IP or ranges by subnet mask Allow overrides Deny by design Support for subscribing to 3 rd party “realtime block list (RBL)” services Support for multiple RBL providers Customizable NDR response per configured provider Override exception email address
demo Connection Filtering
Sender Filtering Filter messages sent from particular email addresses or domains Filter messages with blank senders Optionally drop connection Blocking own domain will break list services Enhanced spoof detection – message submission method is persisted Don’t resolve anonymous sender by default
Recipient filtering Filter messages sent to nonexistent recipients No NDR – message rejected at protocol Address book mining Filter messages sent to particular email recipients (valid or invalid) Restricted Distribution Lists Allow only authenticated users to send to a DL Reduces impact of unsolicited email sent to internal only DLs
demo Recipient Filtering Restricted DL
ISV Infrastructure Support Partner integration Expose new message properties for authenticated and trusted (IP Accept List) connections Don’t filter mail from authenticated or trusted connection Virus scanning still performed Avoids potential false positives on internal or trusted mail Per Message Spam Rating (SCL) Leverage client integration
Client Features
Trusted and Blocked Senders Safe Recipients Blocked Senders Can optionally include Contacts User Lists shared by Outlook 2003 and Exchange 2003 OWA User Lists are stored on the server Move to junk folder determined by store based on user lists and per message SCL
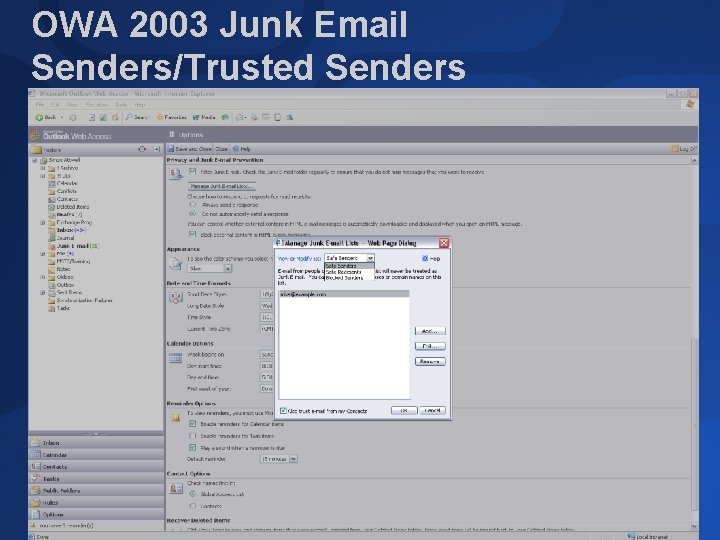
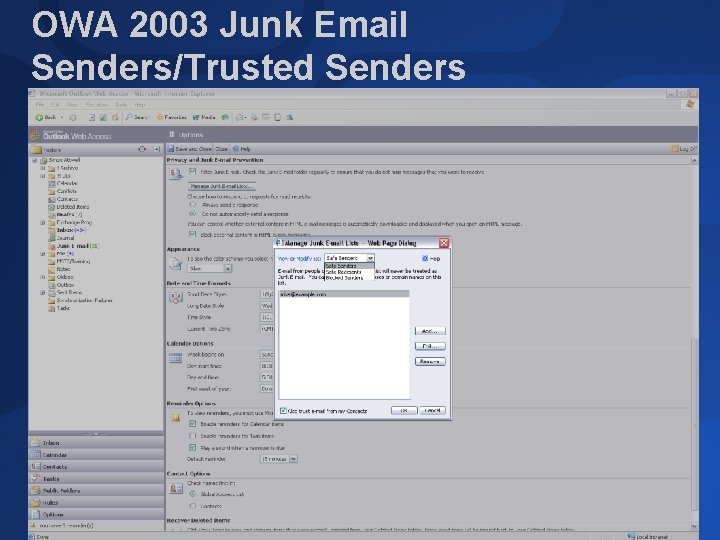
OWA 2003 Junk Email Senders/Trusted Senders
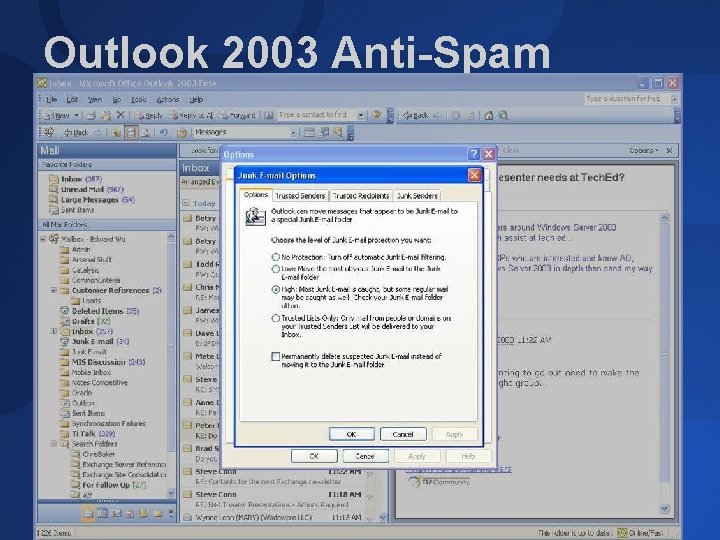
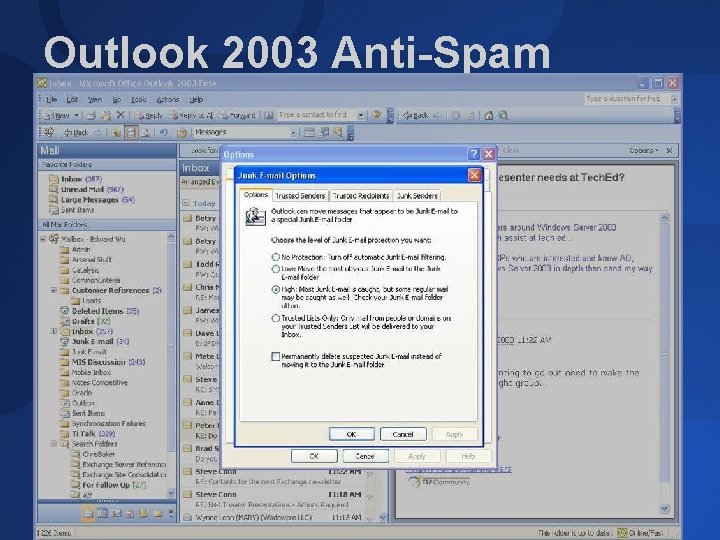
Outlook 2003 Anti-Spam
Client Server Integration
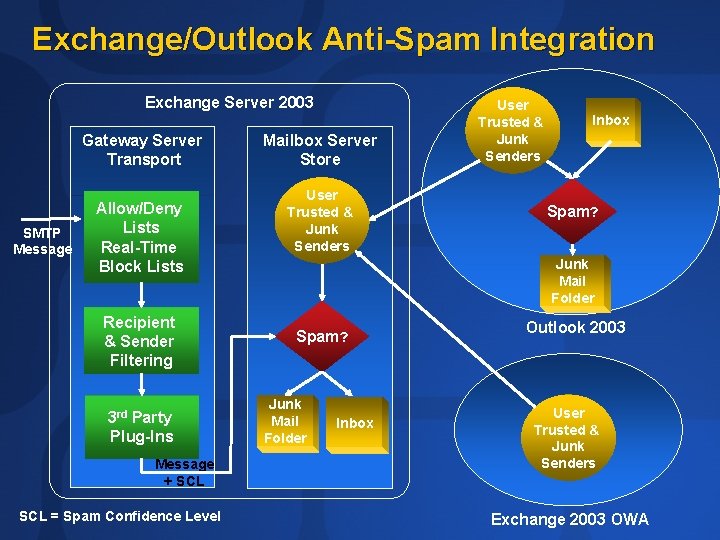
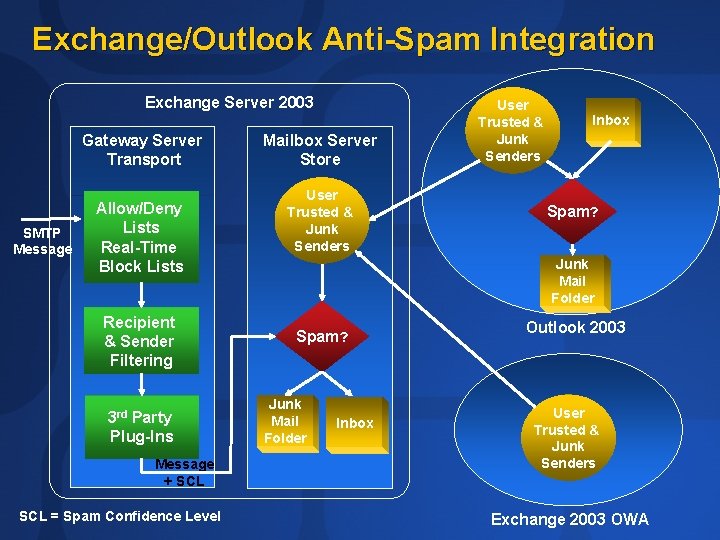
Exchange/Outlook Anti-Spam Integration Exchange Server 2003 Gateway Server Transport SMTP Message Allow/Deny Lists Real-Time Block Lists Recipient & Sender Filtering 3 rd Party Plug-Ins Message + SCL = Spam Confidence Level Mailbox Server Store User Trusted & Junk Senders Inbox Spam? Junk Mail Folder Spam? Junk Mail Folder Inbox Outlook 2003 User Trusted & Junk Senders Exchange 2003 OWA
demo OWA Trusted Senders

Deployment
What to Put Where Which features should be enabled Where features should be deployed Cross forest considerations Best practice recommendations
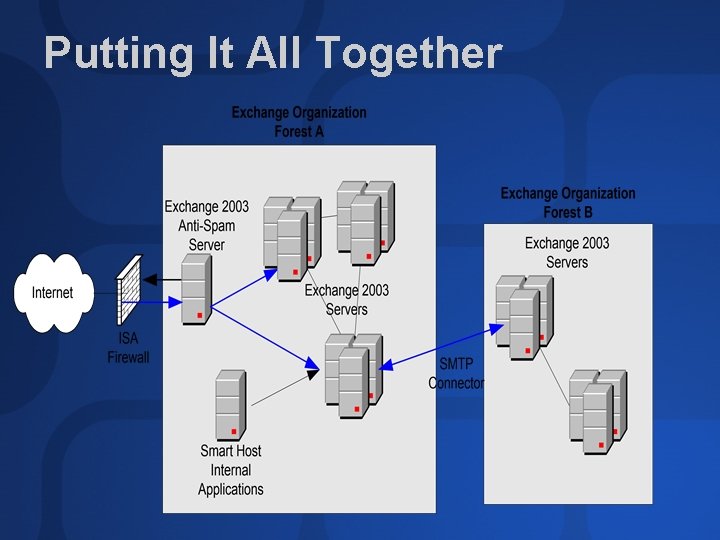
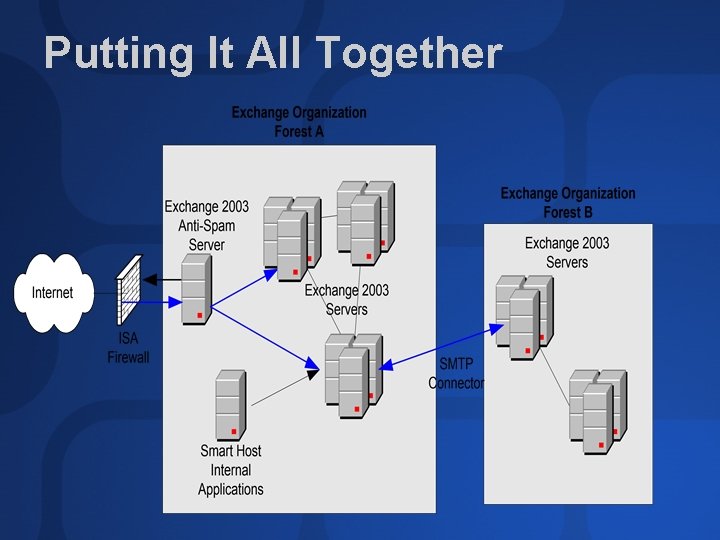
Putting It All Together
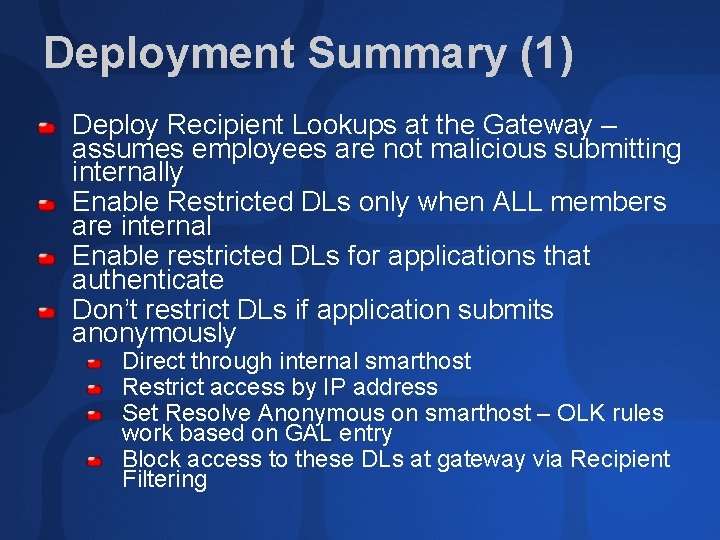
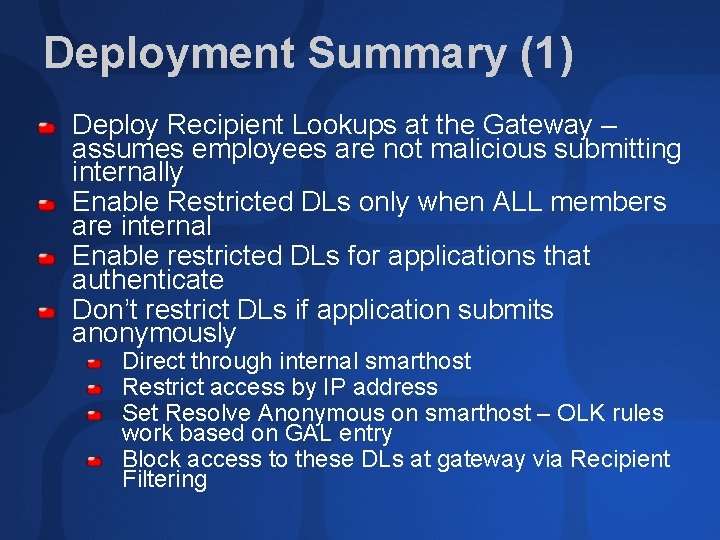
Deployment Summary (1) Deploy Recipient Lookups at the Gateway – assumes employees are not malicious submitting internally Enable Restricted DLs only when ALL members are internal Enable restricted DLs for applications that authenticate Don’t restrict DLs if application submits anonymously Direct through internal smarthost Restrict access by IP address Set Resolve Anonymous on smarthost – OLK rules work based on GAL entry Block access to these DLs at gateway via Recipient Filtering
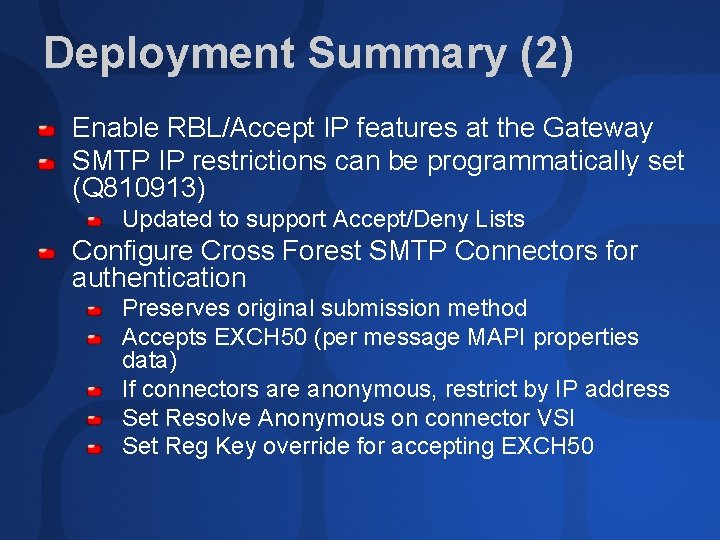
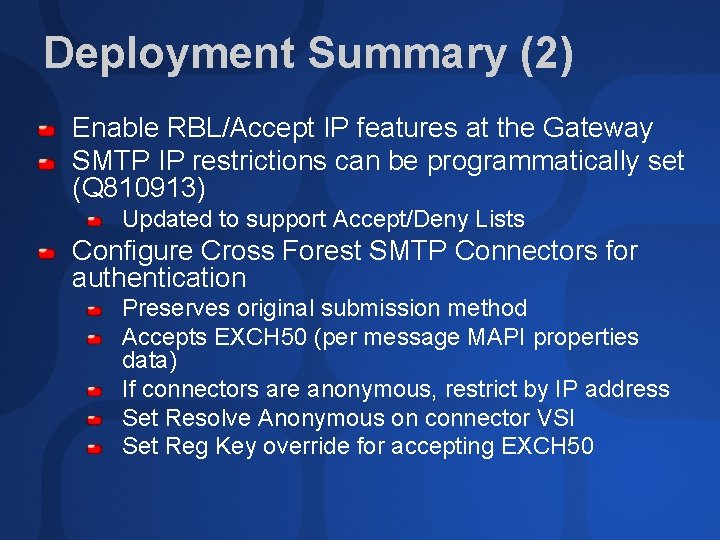
Deployment Summary (2) Enable RBL/Accept IP features at the Gateway SMTP IP restrictions can be programmatically set (Q 810913) Updated to support Accept/Deny Lists Configure Cross Forest SMTP Connectors for authentication Preserves original submission method Accepts EXCH 50 (per message MAPI properties data) If connectors are anonymous, restrict by IP address Set Resolve Anonymous on connector VSI Set Reg Key override for accepting EXCH 50
Summary There is no “silver bullet” in the war against spam. Microsoft is committed to fighting spam through on-going investments in anti-spam features & technologies. Through integration of our own products and ISV partner products, we aim to reduce spam by providing complete end to end solutions.
Ask The Experts Get Your Questions Answered I will be at the ATE after this session
Community Resources http: //www. microsoft. com/communities/default. mspx Most Valuable Professional (MVP) http: //www. mvp. support. microsoft. com/ Newsgroups Converse online with Microsoft Newsgroups, including Worldwide http: //www. microsoft. com/communities/newsgroups/default. mspx User Groups Meet and learn with your peers http: //www. microsoft. com/communities/usergroups/default. mspx
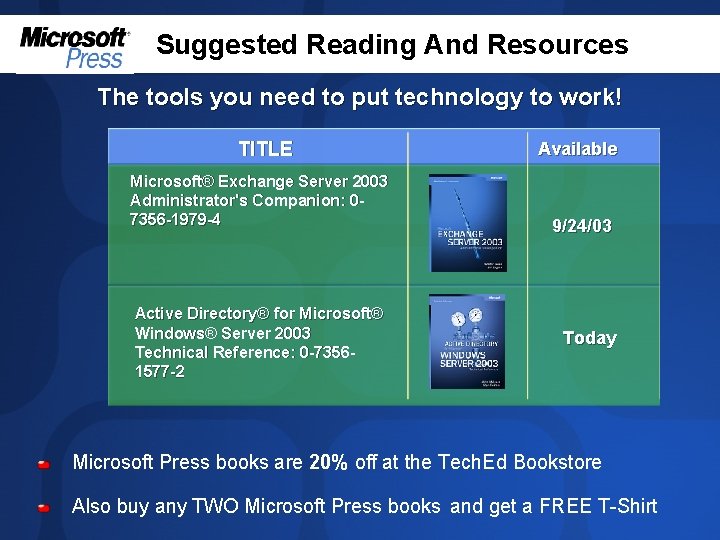
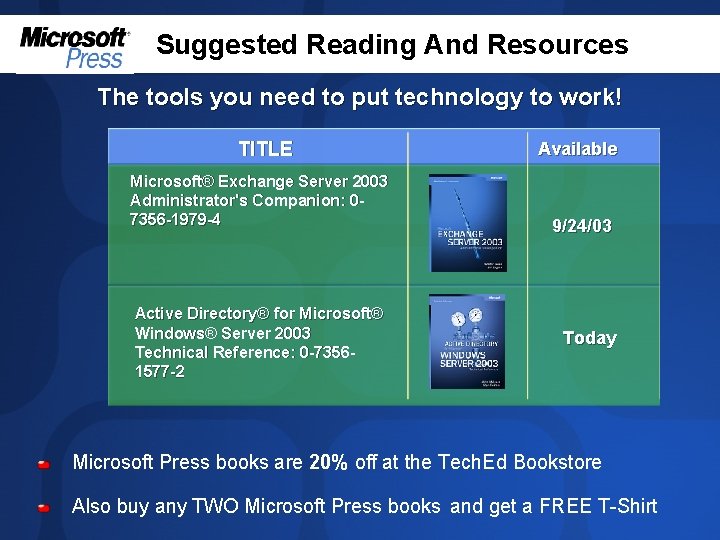
Suggested Reading And Resources The tools you need to put technology to work! TITLE Available Microsoft® Exchange Server 2003 Administrator's Companion: 07356 -1979 -4 9/24/03 Active Directory® for Microsoft® Windows® Server 2003 Technical Reference: 0 -73561577 -2 Today Microsoft Press books are 20% off at the Tech. Ed Bookstore Also buy any TWO Microsoft Press books and get a FREE T-Shirt
evaluations
© 2003 Microsoft Corporation. All rights reserved. This presentation is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, IN THIS SUMMARY.