MPLS and VPNs David Andersen Nick Feamster February
MPLS and VPNs (David Andersen) (Nick Feamster) February 18, 2008
Packet Switching l Source sends information as self-contained packets that have an address. » Source may have to break up single message into multiple l Each packet travels independently to the destination host. » Routers and switches use the address in the packet to determine how to forward the packets l l Destination recreates the message. Analogy: a letter in surface mail. 2
Circuit Switching l Source first establishes a connection (circuit) to the destination. » Each router or switch along the way may reserve some bandwidth for the data flow l Source sends the data over the circuit. » No need to include the destination address with the data since the routers know the path l l The connection is torn down. Example: telephone network. 3
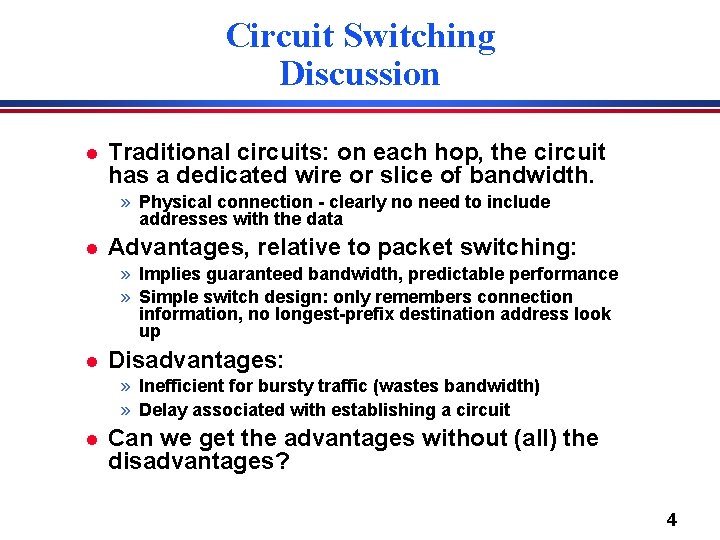
Circuit Switching Discussion l Traditional circuits: on each hop, the circuit has a dedicated wire or slice of bandwidth. » Physical connection - clearly no need to include addresses with the data l Advantages, relative to packet switching: » Implies guaranteed bandwidth, predictable performance » Simple switch design: only remembers connection information, no longest-prefix destination address look up l Disadvantages: » Inefficient for bursty traffic (wastes bandwidth) » Delay associated with establishing a circuit l Can we get the advantages without (all) the disadvantages? 4
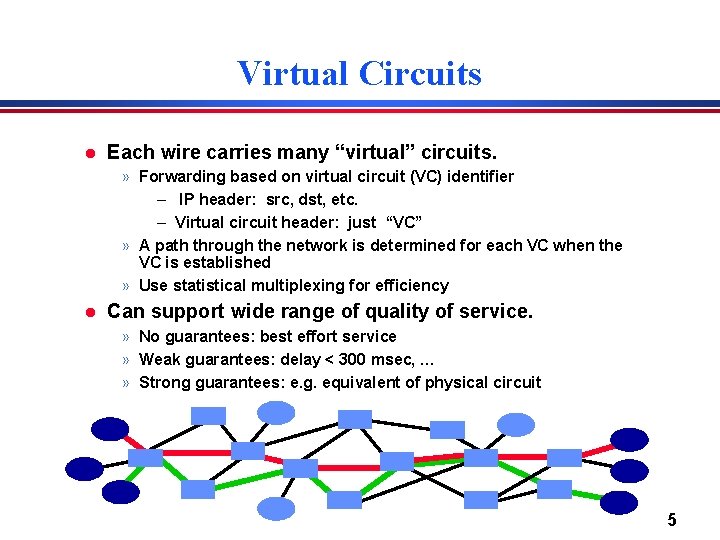
Virtual Circuits l Each wire carries many “virtual” circuits. » Forwarding based on virtual circuit (VC) identifier – IP header: src, dst, etc. – Virtual circuit header: just “VC” » A path through the network is determined for each VC when the VC is established » Use statistical multiplexing for efficiency l Can support wide range of quality of service. » No guarantees: best effort service » Weak guarantees: delay < 300 msec, … » Strong guarantees: e. g. equivalent of physical circuit 5
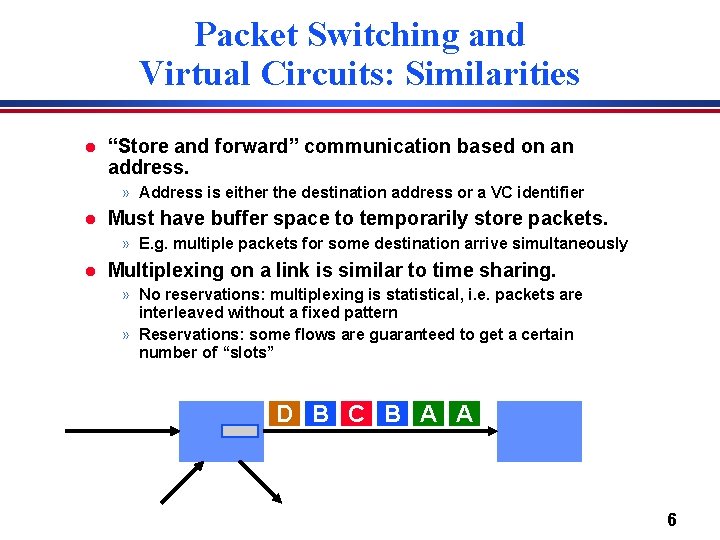
Packet Switching and Virtual Circuits: Similarities l “Store and forward” communication based on an address. » Address is either the destination address or a VC identifier l Must have buffer space to temporarily store packets. » E. g. multiple packets for some destination arrive simultaneously l Multiplexing on a link is similar to time sharing. » No reservations: multiplexing is statistical, i. e. packets are interleaved without a fixed pattern » Reservations: some flows are guaranteed to get a certain number of “slots” D B C B A A 6
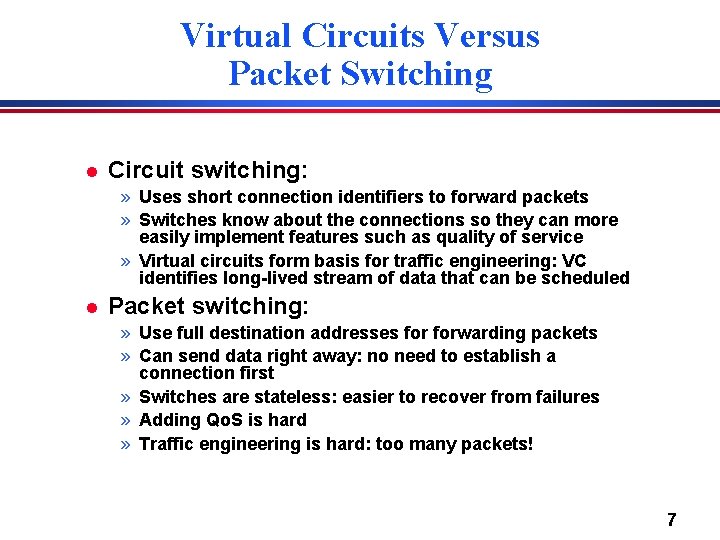
Virtual Circuits Versus Packet Switching l Circuit switching: » Uses short connection identifiers to forward packets » Switches know about the connections so they can more easily implement features such as quality of service » Virtual circuits form basis for traffic engineering: VC identifies long-lived stream of data that can be scheduled l Packet switching: » Use full destination addresses forwarding packets » Can send data right away: no need to establish a connection first » Switches are stateless: easier to recover from failures » Adding Qo. S is hard » Traffic engineering is hard: too many packets! 7
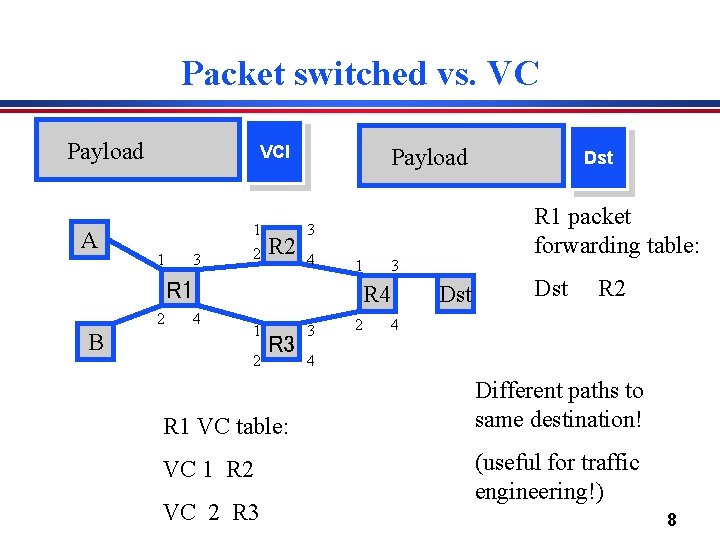
Packet switched vs. VC Payload A VCI 1 3 1 2 R 2 Payload 1 R 1 2 B 4 3 R 4 1 2 R 3 R 1 VC table: VC 1 R 2 VC 2 R 3 R 1 packet forwarding table: 3 4 3 2 Dst Dst R 2 4 4 Different paths to same destination! (useful for traffic engineering!) 8
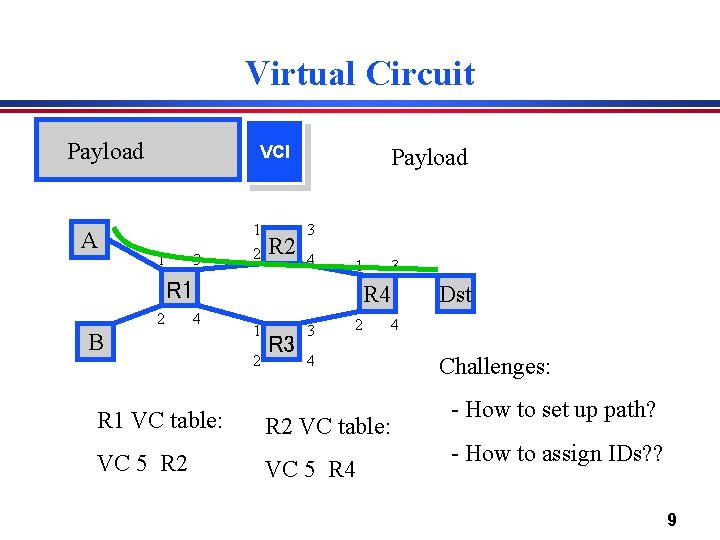
Virtual Circuit Payload A VCI 1 3 1 2 R 2 Payload 3 4 1 R 1 2 4 B R 1 VC table: VC 5 R 2 3 R 4 1 2 R 3 3 2 4 4 R 2 VC table: VC 5 R 4 Dst Challenges: - How to set up path? - How to assign IDs? ? 9
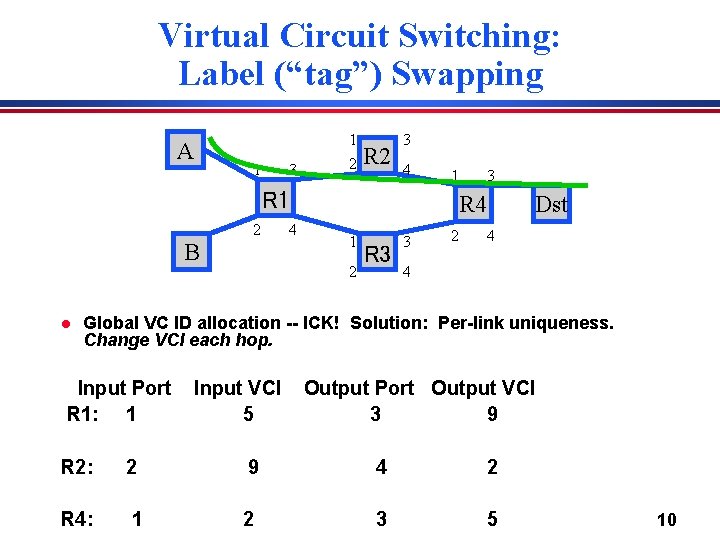
Virtual Circuit Switching: Label (“tag”) Swapping A 1 3 1 2 R 2 3 4 1 R 1 2 B l 4 3 R 4 1 2 R 3 3 2 Dst 4 4 Global VC ID allocation -- ICK! Solution: Per-link uniqueness. Change VCI each hop. Input Port R 1: 1 Input VCI 5 Output Port Output VCI 3 9 R 2: 2 9 4 2 R 4: 1 2 3 5 10
Label (“tag”) Swapping l Result: Signalling protocol must only find per -link unused VCIs. » “Link-local scope” » Connection setup can proceed hop-by-hop. – Good news for our setup protocols! 11
Virtual Circuits In Practice l Asynchronous Transfer Mode (ATM): Teleco approach » Kitchen sink. Based on voice, support file transfer, video, etc. » Intended as IP replacement. That didn’t happen. : ) » Today: Underlying network protocol in many teleco networks. E. g. , DSL speaks ATM. IP over ATM in some cases. l MPLS: The “IP Heads” answer to ATM » Stole good ideas from ATM » Integrates well with IP » Today: Used inside some networks to provide VPN support, traffic engineering, simplify core. l l Other nets just run IP. Older tech: Frame Relay » Only provided PVCs. Used for quasi-dedicated 56 k/T 1 links between offices, etc. Slower, less flexible than ATM. 12
![ATM Cell Switching l Small, fixed-size cells [Fixed-length data][header] l Why? » Efficiency: All ATM Cell Switching l Small, fixed-size cells [Fixed-length data][header] l Why? » Efficiency: All](http://slidetodoc.com/presentation_image_h/ae88aa1bdf14f1e6d7befccb357d9128/image-13.jpg)
ATM Cell Switching l Small, fixed-size cells [Fixed-length data][header] l Why? » Efficiency: All packets the same – Easier hardware parallelism, implementation » Switching efficiency: – Lookups are easy -- table index. » Result: Very high cell switching rates. » Initial ATM was 155 Mbit/s. Ethernet was 10 Mbit/s at the same time. (!) l How do you pick the cell size? 13
ATM Features l Fixed size cells (53 bytes). » Why 53? l l l Virtual circuit technology using hierarchical virtual circuits (VP, VC). PHY (physical layer) processing delineates cells by frame structure, cell header error check. Support for multiple traffic classes by adaptation layer. » E. g. voice channels, data traffic l Elaborate signaling stack. » Backwards compatible with respect to the telephone standards l Standards defined by ATM Forum. » Organization of manufacturers, providers, users 14
Why 53 Bytes? l Small cells favored by voice applications » delays of more than about 10 ms require echo cancellation » each payload byte consumes 125 s (8000 samples/sec) l Large cells favored by data applications » Five bytes of each cell are overhead l France favored 32 bytes » 32 bytes = 4 ms packetization delay. » France is 3 ms wide. » Wouldn’t need echo cancellers! l USA, Australia favored 64 bytes » 64 bytes = 8 ms » USA is 16 ms wide » Needed echo cancellers anyway, wanted less overhead l Compromise 15
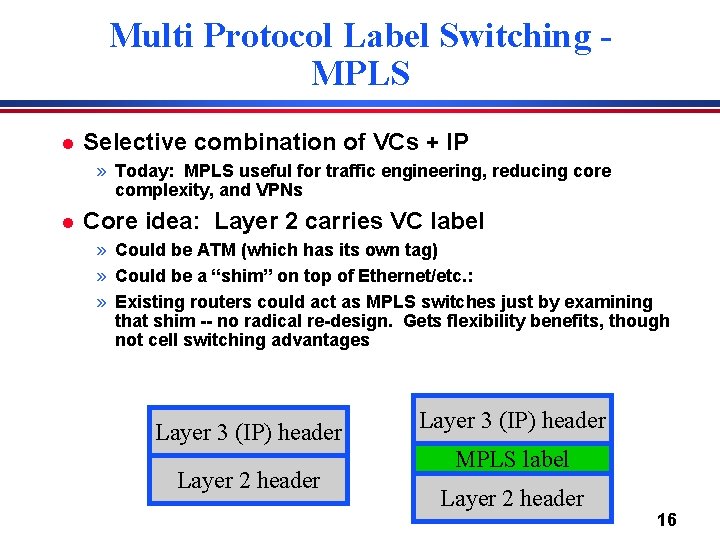
Multi Protocol Label Switching MPLS l Selective combination of VCs + IP » Today: MPLS useful for traffic engineering, reducing core complexity, and VPNs l Core idea: Layer 2 carries VC label » Could be ATM (which has its own tag) » Could be a “shim” on top of Ethernet/etc. : » Existing routers could act as MPLS switches just by examining that shim -- no radical re-design. Gets flexibility benefits, though not cell switching advantages Layer 3 (IP) header Layer 2 header Layer 3 (IP) header MPLS label Layer 2 header 16
MPLS + IP l Map packet onto Forward Equivalence Class (FEC) » Simple case: longest prefix match of destination address » More complex if Qo. S of policy routing is used l In MPLS, a label is associated with the packet when it enters the network and forwarding is based on the label in the network core. » Label is swapped (as ATM VCIs) l Potential advantages. » » Packet forwarding can be faster Routing can be based on ingress router and port Can use more complex routing decisions Can force packets to followed a pinned route 17
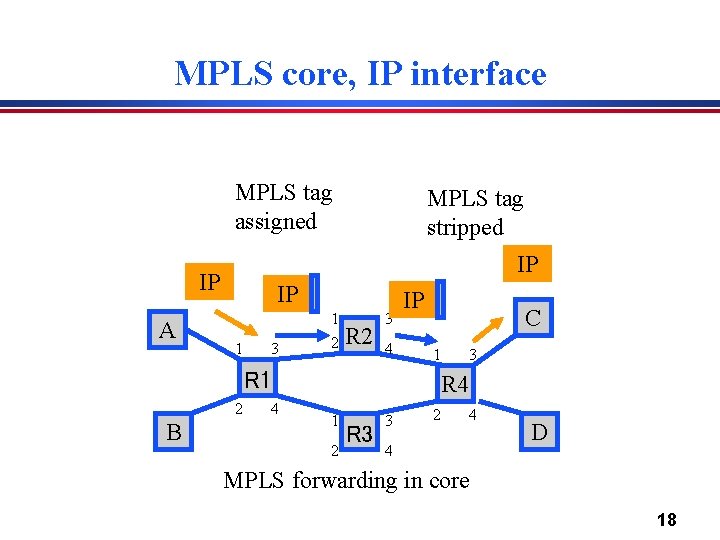
MPLS core, IP interface MPLS tag assigned IP IP A MPLS tag stripped IP 1 3 1 2 R 2 3 4 IP C 1 R 1 2 B 4 3 R 4 1 2 R 3 3 2 4 4 D MPLS forwarding in core 18
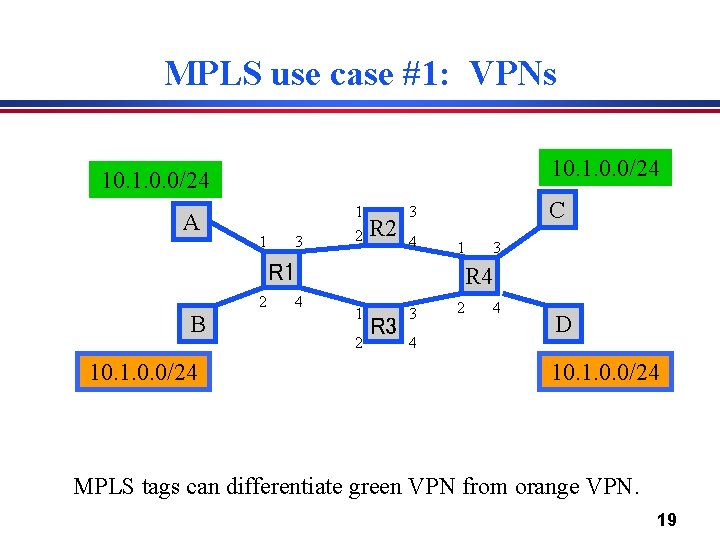
MPLS use case #1: VPNs 10. 1. 0. 0/24 A 1 3 1 2 R 2 C 3 4 1 R 1 2 B 10. 1. 0. 0/24 4 3 R 4 1 2 R 3 3 4 2 4 D 10. 1. 0. 0/24 MPLS tags can differentiate green VPN from orange VPN. 19
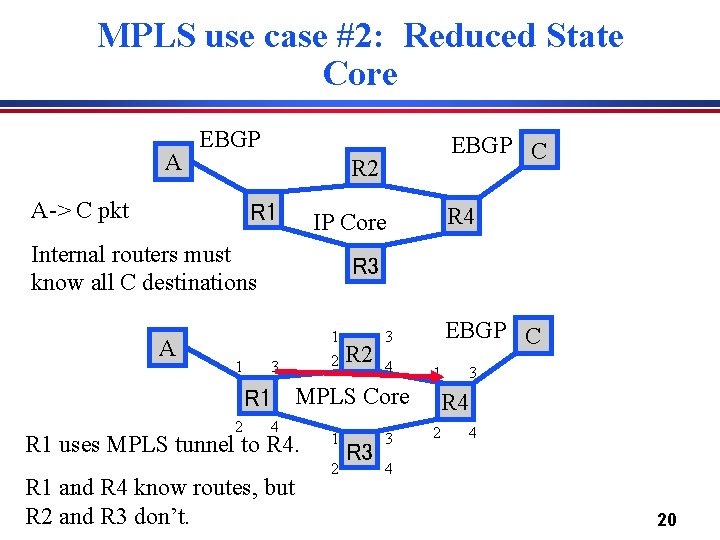
MPLS use case #2: Reduced State Core A EBGP R 2 A-> C pkt R 1 1 R 4 IP Core Internal routers must know all C destinations A EBGP C R 3 3 1 2 R 2 EBGP C 3 4 1 R 1 MPLS Core 2 4 R 1 uses MPLS tunnel to R 4. . R 4 know routes, but R 1 and R 2 and R 3 don’t. 1 2 R 3 3 3 R 4 2 4 4 20
MPLS use case #3: Traffic Engineering l l As discussed earlier -- can pick routes based upon more than just destination Used in practice by many ISPs, though certainly not all. 21
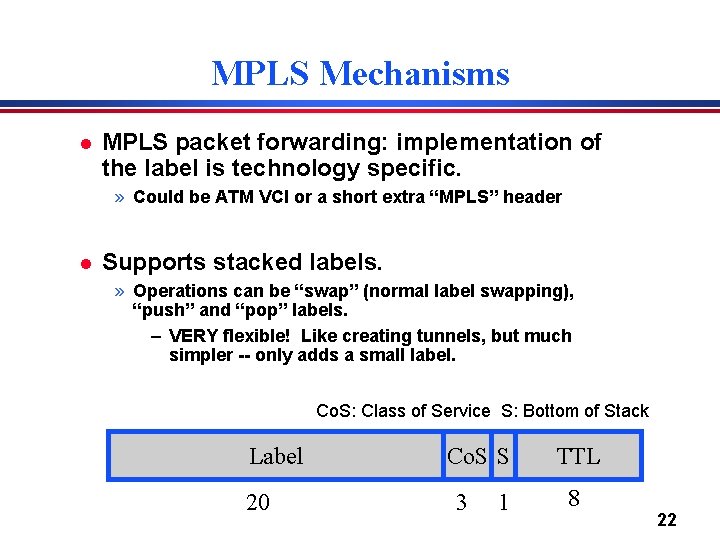
MPLS Mechanisms l MPLS packet forwarding: implementation of the label is technology specific. » Could be ATM VCI or a short extra “MPLS” header l Supports stacked labels. » Operations can be “swap” (normal label swapping), “push” and “pop” labels. – VERY flexible! Like creating tunnels, but much simpler -- only adds a small label. Co. S: Class of Service S: Bottom of Stack Label 20 Co. S S 3 1 TTL 8 22
MPLS Discussion l Original motivation. » Fast packet forwarding: – Use of ATM hardware – Avoid complex “longest prefix” route lookup – Limitations of routing table sizes » Quality of service l Currently mostly used for traffic engineering and network management. » LSPs can be thought of as “programmable links” that can be set up under software control » on top of a simple, static hardware infrastructure 23
Layer 3 Virtual Private Networks • Private communications over a public network • A set of sites that are allowed to communicate with each other • Defined by a set of administrative policies – determine both connectivity and Qo. S among sites – established by VPN customers – One way to implement: BGP/MPLS VPN mechanisms (RFC 2547) 24
Building Private Networks • Separate physical network – Good security properties – Expensive! • Secure VPNs – Encryption of entire network stack between endpoints • Layer 2 Tunneling Protocol (L 2 TP) – “PPP over IP” – No encryption • Layer 3 VPNs Privacy and interconnectivity (not confidentiality, integrity, etc. ) 25
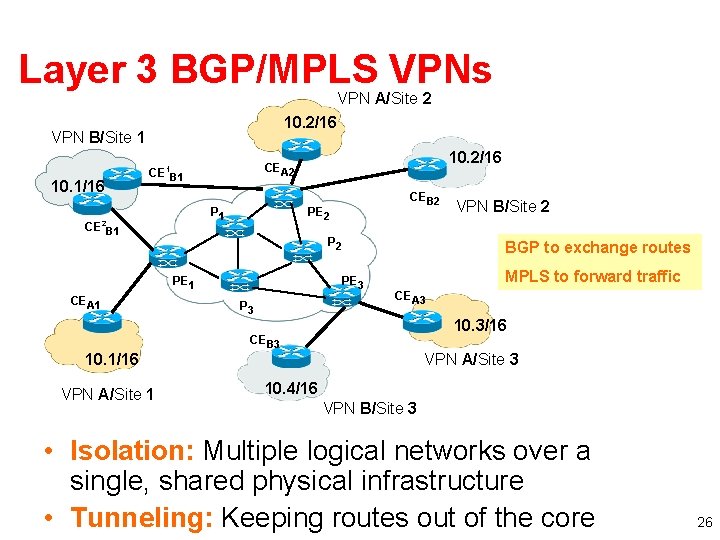
Layer 3 BGP/MPLS VPNs VPN A/Site 2 10. 2/16 VPN B/Site 1 10. 1/16 CE B 1 P 1 2 CE B 1 10. 2/16 CEA 2 1 P 2 PE 1 CEA 1 10. 1/16 VPN A/Site 1 CEB 2 PE 2 BGP to exchange routes PE 3 P 3 VPN B/Site 2 MPLS to forward traffic CEA 3 10. 3/16 CEB 3 VPN A/Site 3 10. 4/16 VPN B/Site 3 • Isolation: Multiple logical networks over a single, shared physical infrastructure • Tunneling: Keeping routes out of the core 26
High-Level Overview of Operation • IP packets arrive at PE (Provider Edger router) • Destination IP address is looked up in forwarding table for customer site • Datagram sent to customer’s network using tunneling (i. e. , an MPLS label-switched path) 27
BGP/MPLS VPN key components • Forwarding in the core: MPLS • Distributing routes between PEs: BGP • Isolation: Keeping different VPNs from routing traffic over one another – Constrained distribution of routing information – Multiple “virtual” forwarding tables • Unique addresses: VPN-IPV 4 Address extension (8 byte Route Distinguisher (RD) added to IPV 4 address) 28
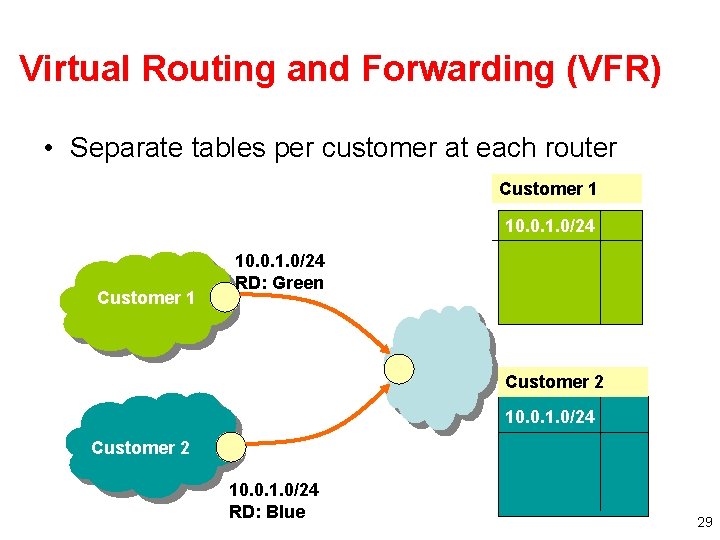
Virtual Routing and Forwarding (VFR) • Separate tables per customer at each router Customer 1 10. 0. 1. 0/24 RD: Green Customer 2 10. 0. 1. 0/24 RD: Blue 29
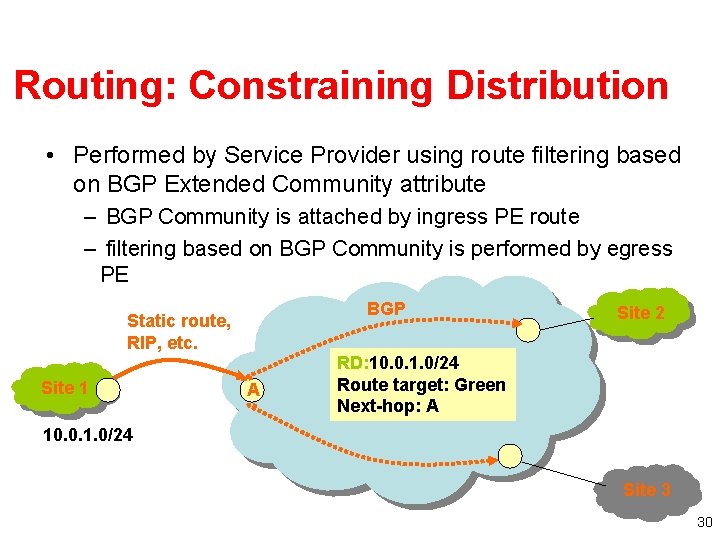
Routing: Constraining Distribution • Performed by Service Provider using route filtering based on BGP Extended Community attribute – BGP Community is attached by ingress PE route – filtering based on BGP Community is performed by egress PE BGP Static route, RIP, etc. Site 1 A Site 2 RD: 10. 0. 1. 0/24 Route target: Green Next-hop: A 10. 0. 1. 0/24 Site 3 30
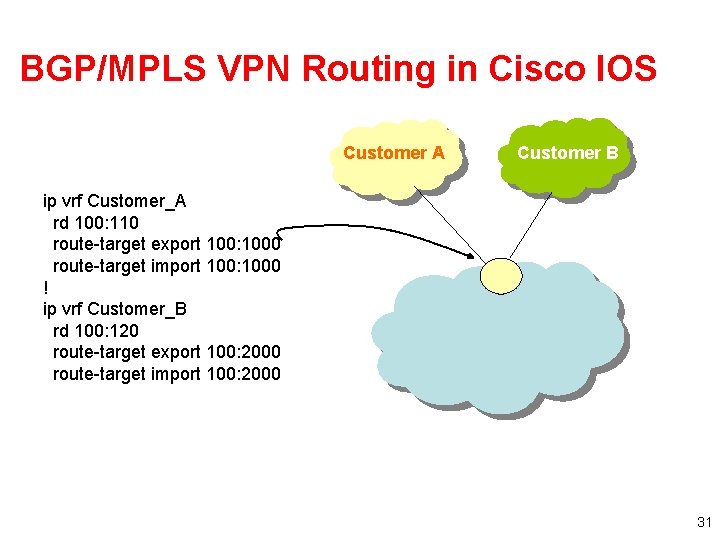
BGP/MPLS VPN Routing in Cisco IOS Customer A Customer B ip vrf Customer_A rd 100: 110 route-target export 100: 1000 route-target import 100: 1000 ! ip vrf Customer_B rd 100: 120 route-target export 100: 2000 route-target import 100: 2000 31
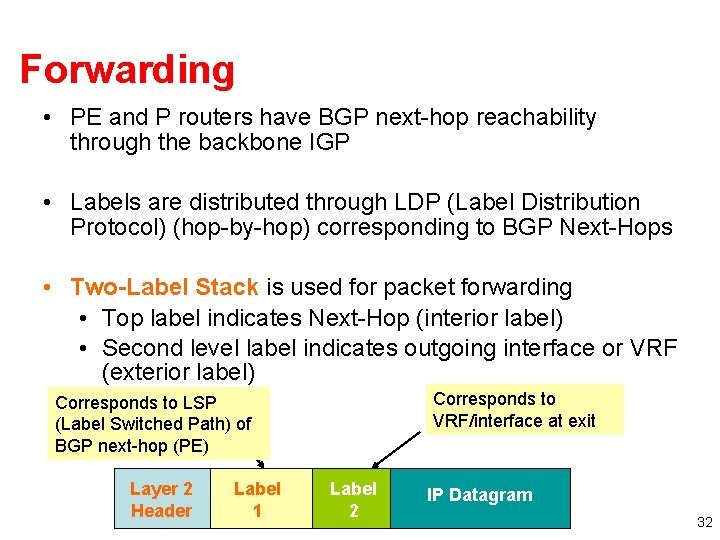
Forwarding • PE and P routers have BGP next-hop reachability through the backbone IGP • Labels are distributed through LDP (Label Distribution Protocol) (hop-by-hop) corresponding to BGP Next-Hops • Two-Label Stack is used for packet forwarding • Top label indicates Next-Hop (interior label) • Second level label indicates outgoing interface or VRF (exterior label) Corresponds to VRF/interface at exit Corresponds to LSP (Label Switched Path) of BGP next-hop (PE) Layer 2 Header Label 1 Label 2 IP Datagram 32
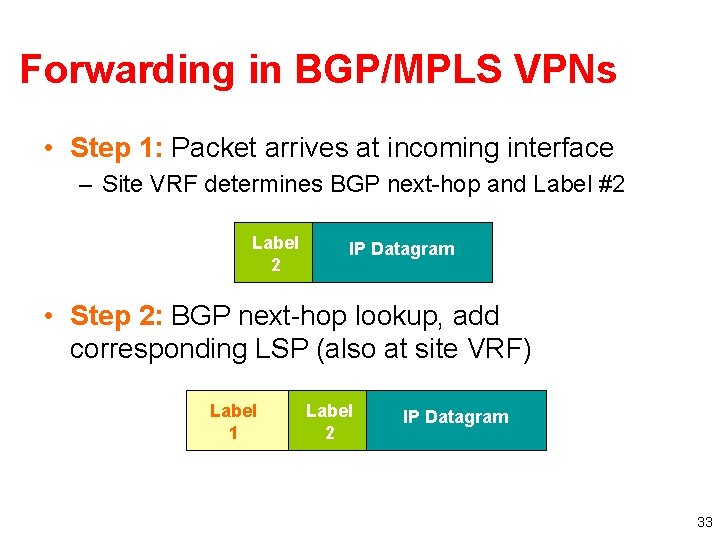
Forwarding in BGP/MPLS VPNs • Step 1: Packet arrives at incoming interface – Site VRF determines BGP next-hop and Label #2 Label 2 IP Datagram • Step 2: BGP next-hop lookup, add corresponding LSP (also at site VRF) Label 1 Label 2 IP Datagram 33
- Slides: 33