Mondriaan Memory Protection Emmett Witchel Krste Asanovic MIT


![Related Work • Capabilities [Dennis 65, IBM AS 400]. • Domain Pages [Koldinger ASPLOS Related Work • Capabilities [Dennis 65, IBM AS 400]. • Domain Pages [Koldinger ASPLOS](https://slidetodoc.com/presentation_image/1f4f7c62fcd32cfe5b7e907043bd9dc5/image-25.jpg)
- Slides: 27

Mondriaan Memory Protection Emmett Witchel Krste Asanovic MIT Lab for Computer Science
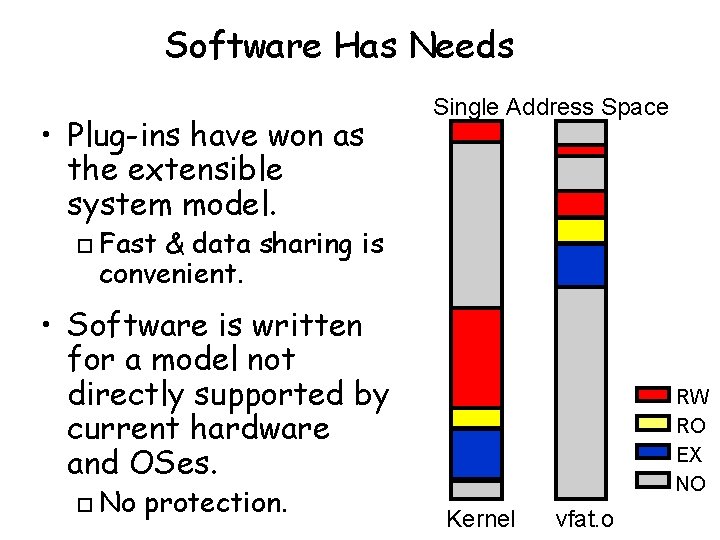
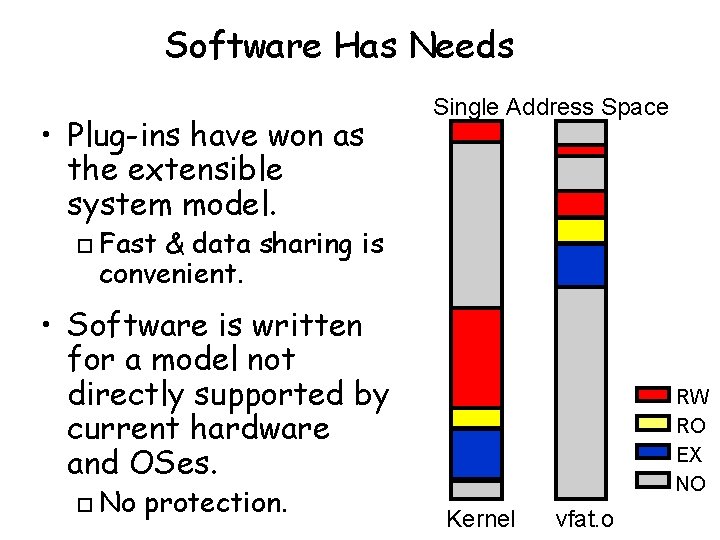
Software Has Needs • Plug-ins have won as the extensible system model. o Single Address Space Fast & data sharing is convenient. • Software is written for a model not directly supported by current hardware and OSes. o No protection. RW RO EX NO Kernel vfat. o
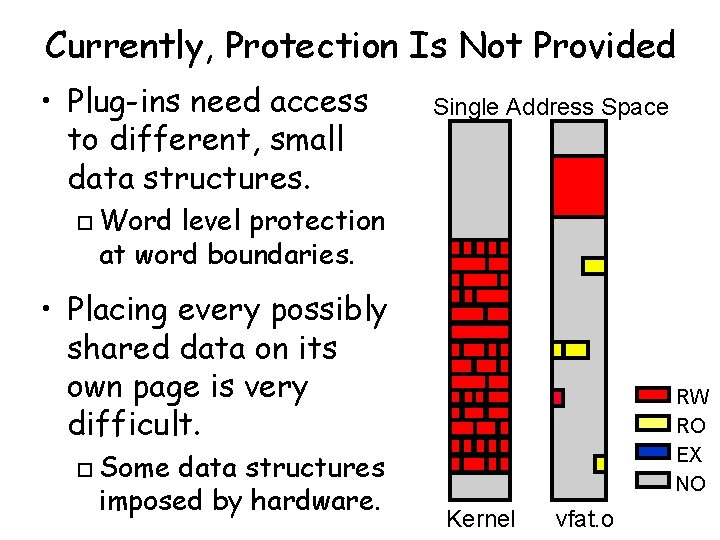
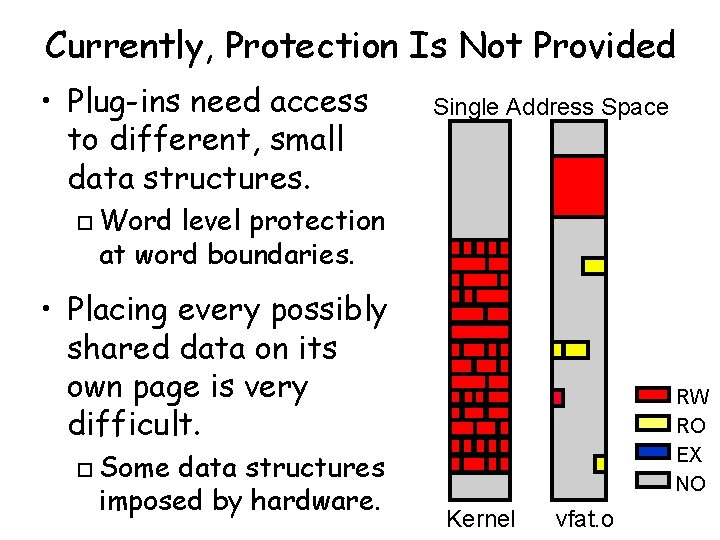
Currently, Protection Is Not Provided • Plug-ins need access to different, small data structures. o Single Address Space Word level protection at word boundaries. • Placing every possibly shared data on its own page is very difficult. o Some data structures imposed by hardware. RW RO EX NO Kernel vfat. o
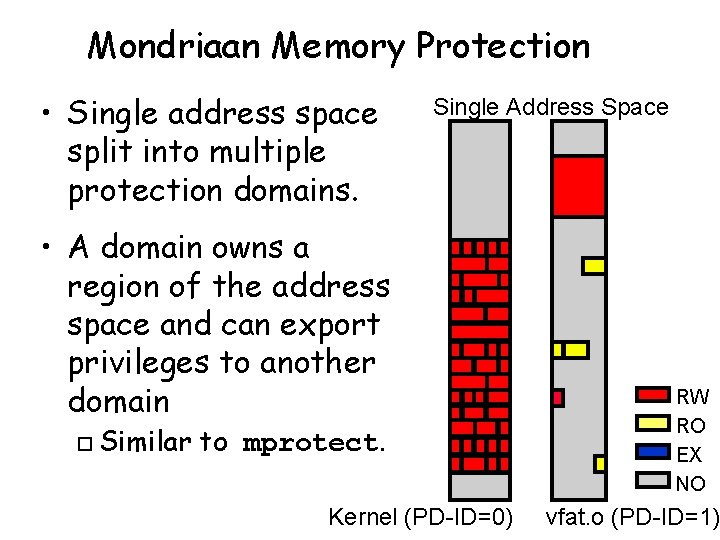
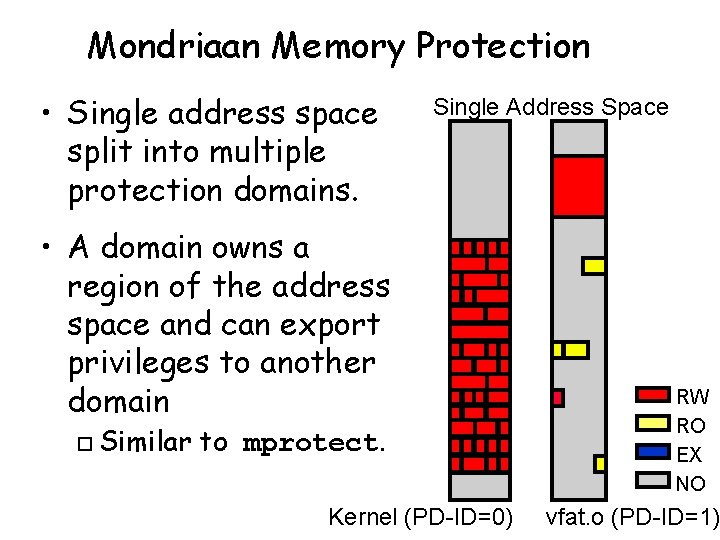
Mondriaan Memory Protection • Single address space split into multiple protection domains. Single Address Space • A domain owns a region of the address space and can export privileges to another domain o Similar to mprotect. Kernel (PD-ID=0) RW RO EX NO vfat. o (PD-ID=1)
Word Level Protection Is Not New • Segmentation is a traditional solution. + Provides word-level protection. o - Explicit segment registers [B 5000, x 86] o - Non-linear addressing o • Capability based machines. + Fine-grained sharing. o - Revocation difficult [System/38, Mmachine]. o - Different protection for different domains via shared capability is hard. o

MMP is a New Solution • Segmentation semantics without the problems. MMP provides fine-grained protection and data sharing. o MMP uses linear addressing. o MMP is compatible with existing ISAs o MMP has no segment registers. o MMP has easy perm. revocation. o MMP does not have tagged pointers. o • MMP is all the fun of segmentation without the headaches.
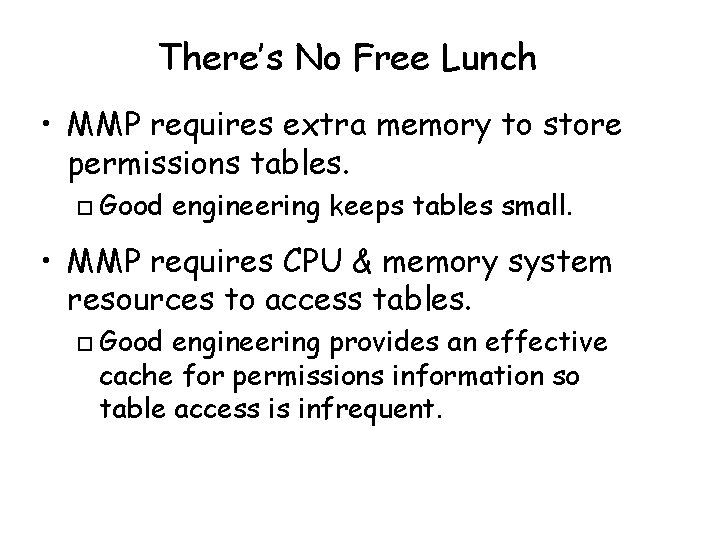
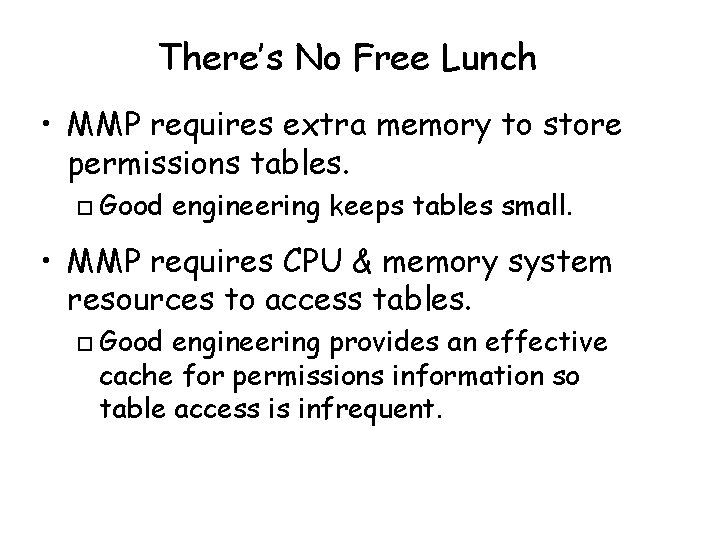
There’s No Free Lunch • MMP requires extra memory to store permissions tables. o Good engineering keeps tables small. • MMP requires CPU & memory system resources to access tables. o Good engineering provides an effective cache for permissions information so table access is infrequent.
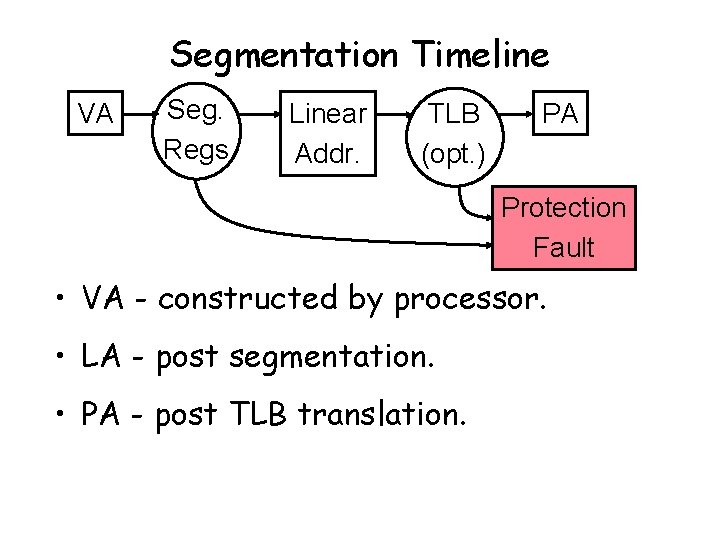
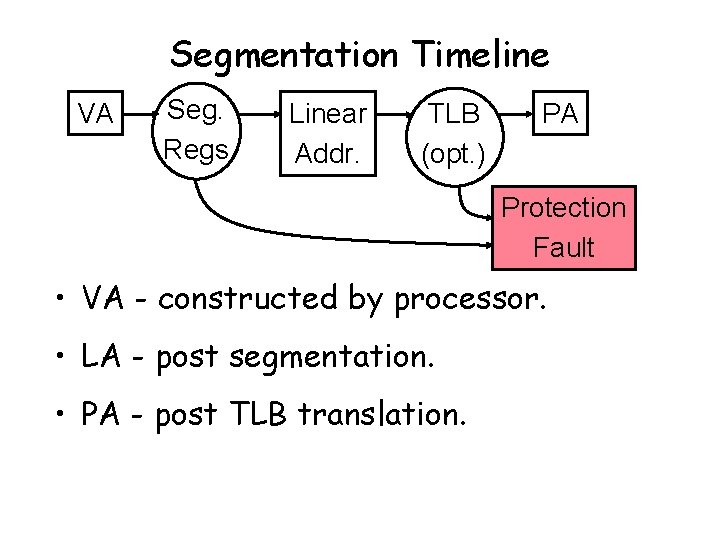
Segmentation Timeline VA Seg. Regs Linear Addr. TLB (opt. ) PA Protection Fault • VA - constructed by processor. • LA - post segmentation. • PA - post TLB translation.
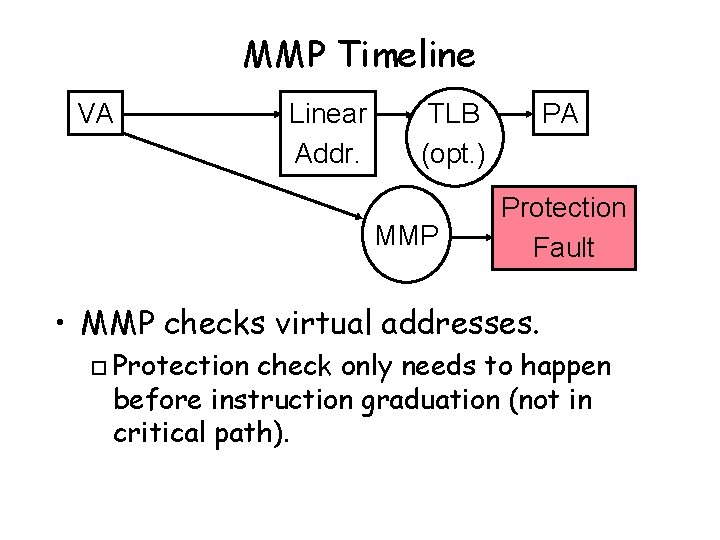
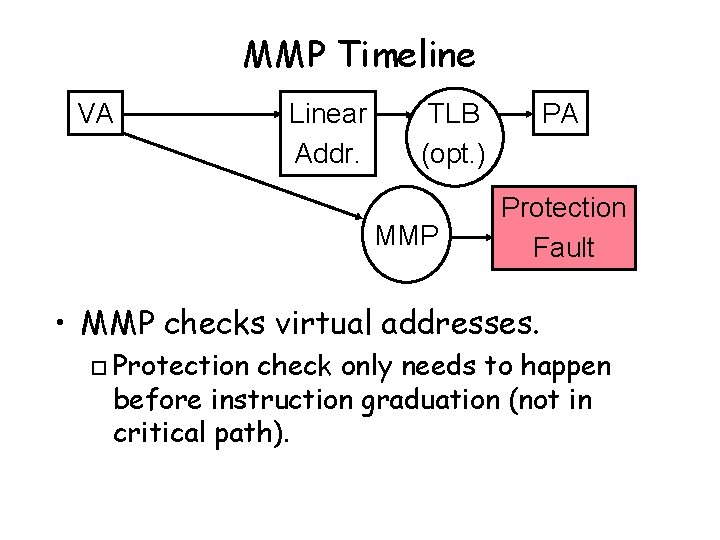
MMP Timeline VA Linear Addr. TLB (opt. ) MMP PA Protection Fault • MMP checks virtual addresses. o Protection check only needs to happen before instruction graduation (not in critical path).
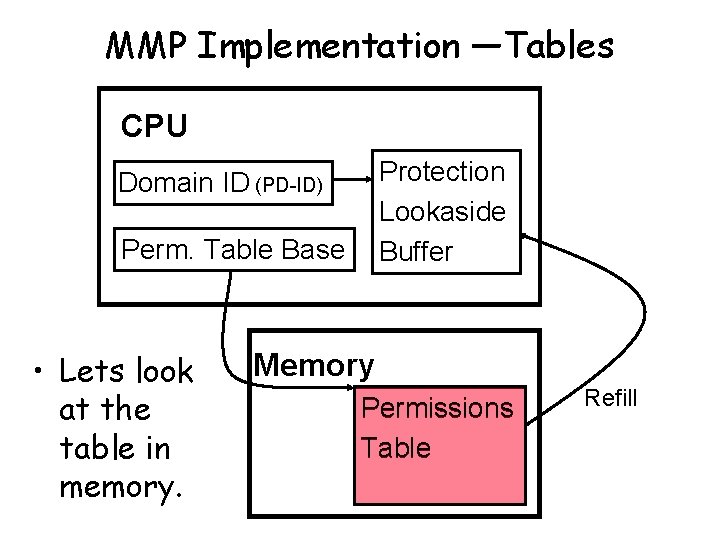
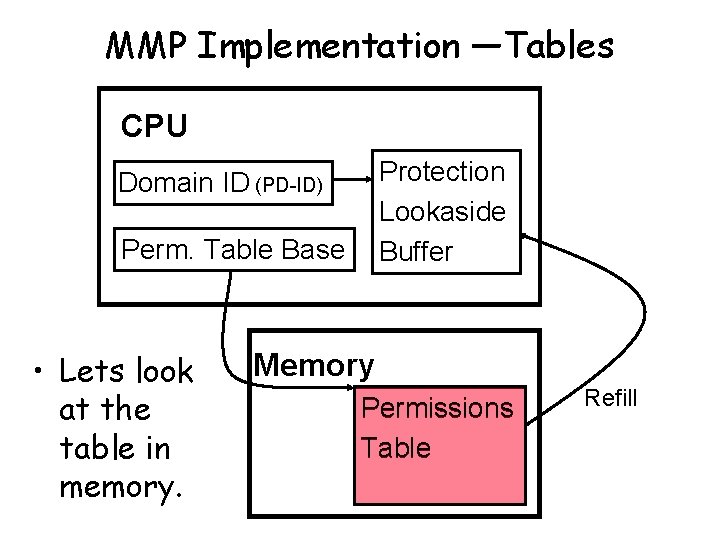
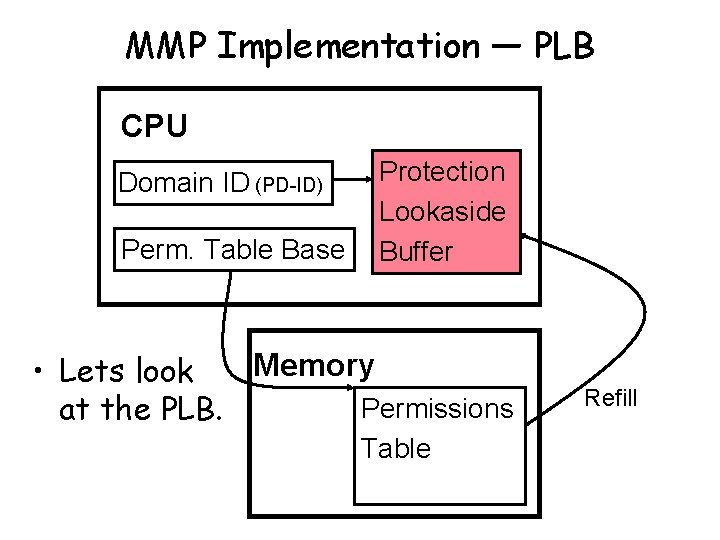
MMP Implementation —Tables CPU Protection Lookaside Buffer Domain ID (PD-ID) Perm. Table Base • Lets look at the table in memory. Memory Permissions Table Refill
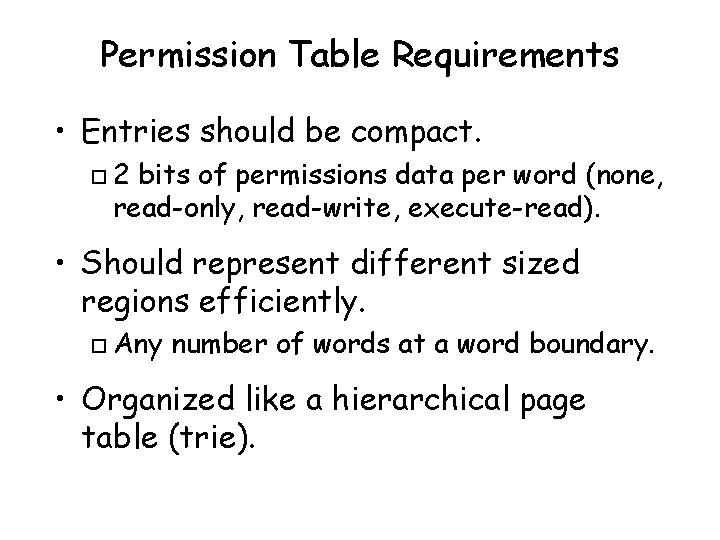
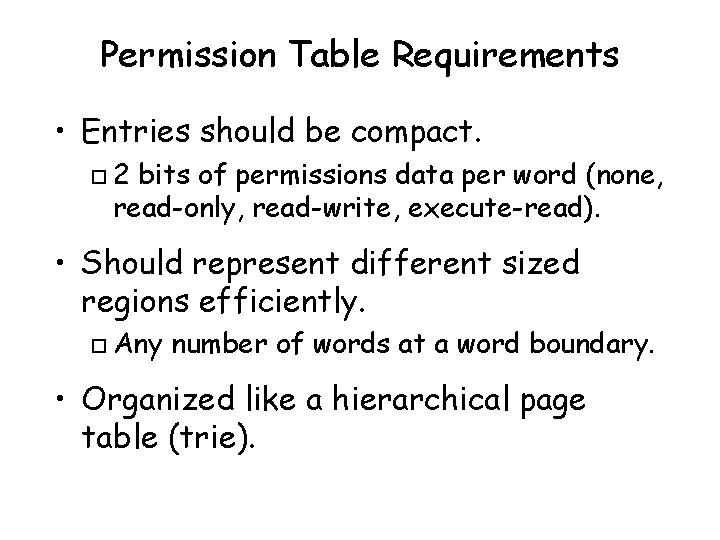
Permission Table Requirements • Entries should be compact. o 2 bits of permissions data per word (none, read-only, read-write, execute-read). • Should represent different sized regions efficiently. o Any number of words at a word boundary. • Organized like a hierarchical page table (trie).
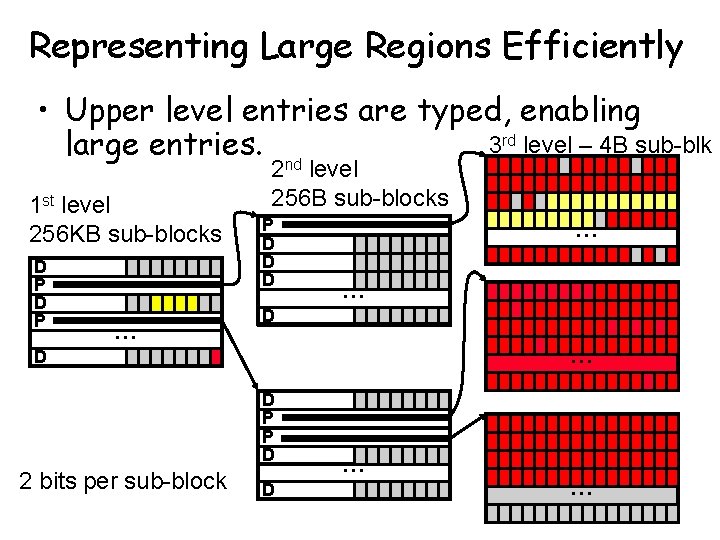
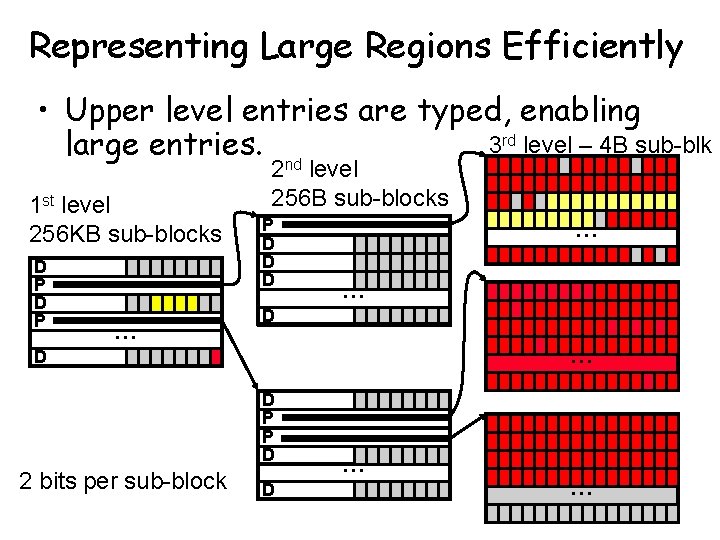
Representing Large Regions Efficiently • Upper level entries are typed, enabling 3 rd level – 4 B sub-blk large entries. nd 1 st level 256 KB sub-blocks D P … 2 level 256 B sub-blocks P D D D … … D D P P D 2 bits per sub-block D … …
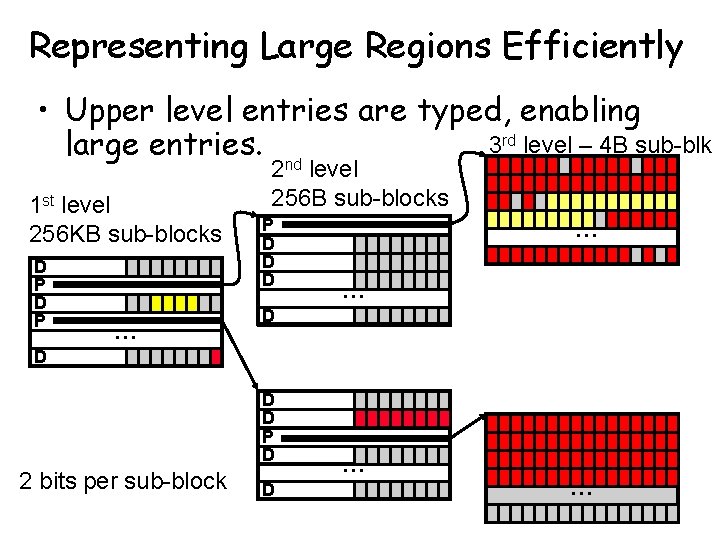
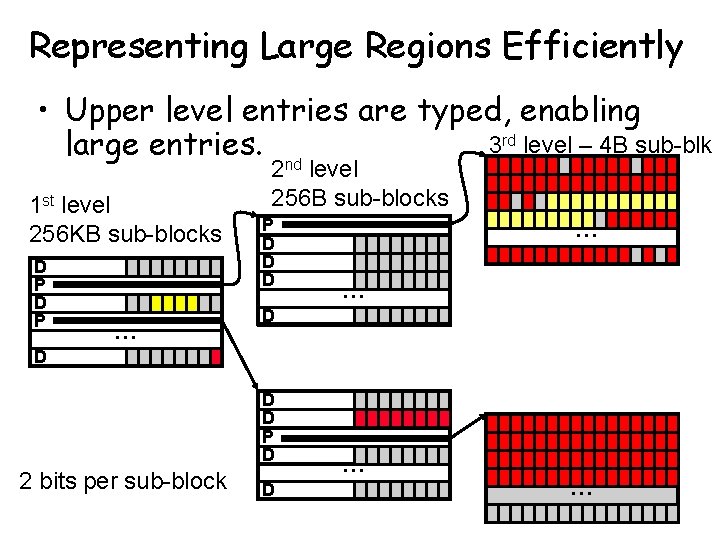
Representing Large Regions Efficiently • Upper level entries are typed, enabling 3 rd level – 4 B sub-blk large entries. nd 1 st level 256 KB sub-blocks D P … 2 level 256 B sub-blocks P D D D … … D D P D 2 bits per sub-block D … …
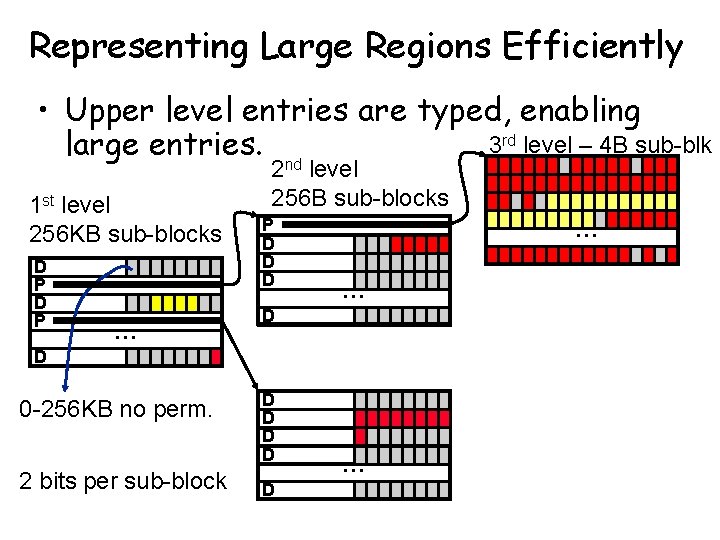
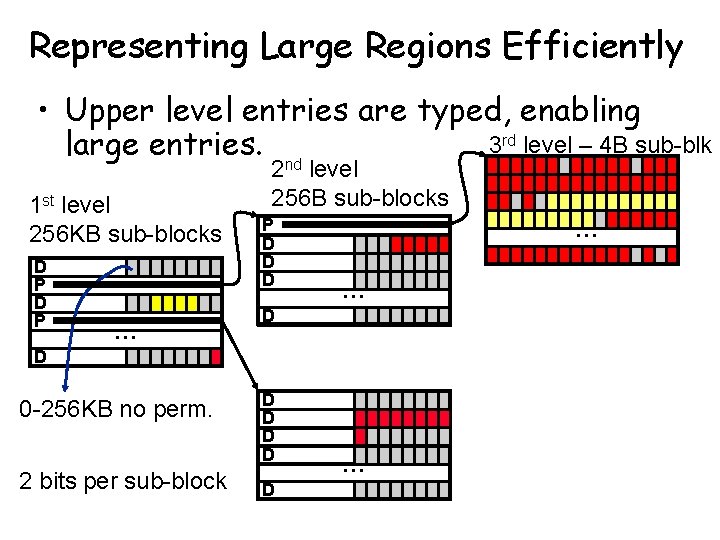
Representing Large Regions Efficiently • Upper level entries are typed, enabling 3 rd level – 4 B sub-blk large entries. nd 1 st level 256 KB sub-blocks D P … 2 level 256 B sub-blocks P D D D … … D D 0 -256 KB no perm. 2 bits per sub-block D D D …
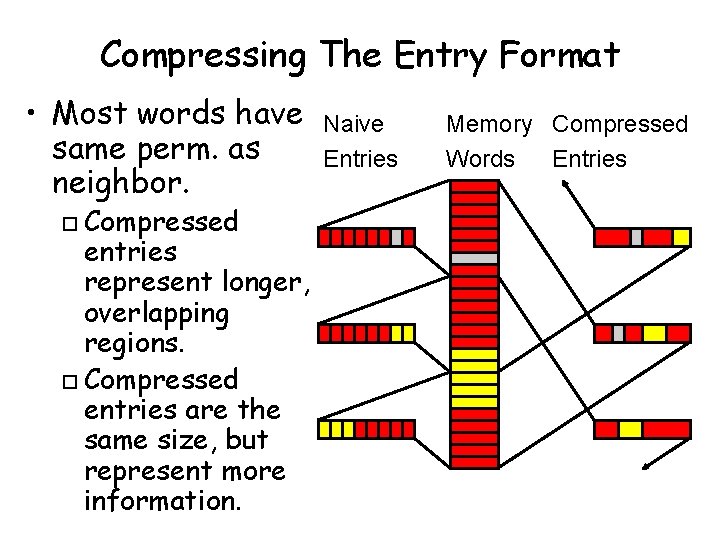
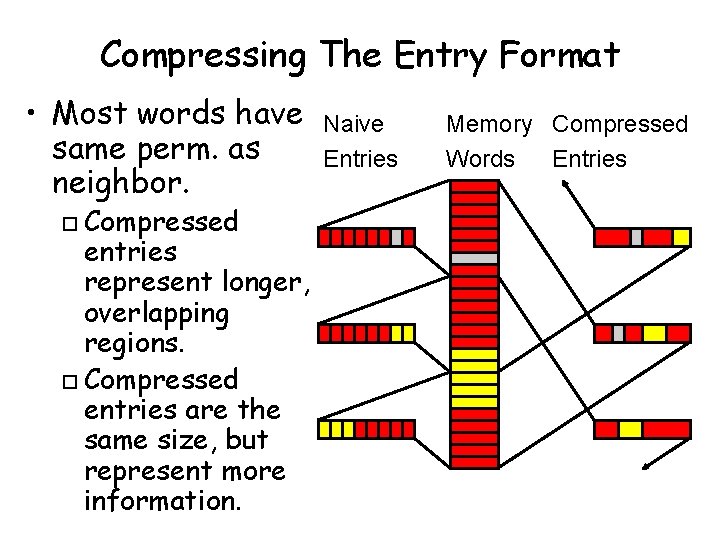
Compressing The Entry Format • Most words have same perm. as neighbor. Compressed entries represent longer, overlapping regions. o Compressed entries are the same size, but represent more information. o Naive Entries Memory Compressed Words Entries
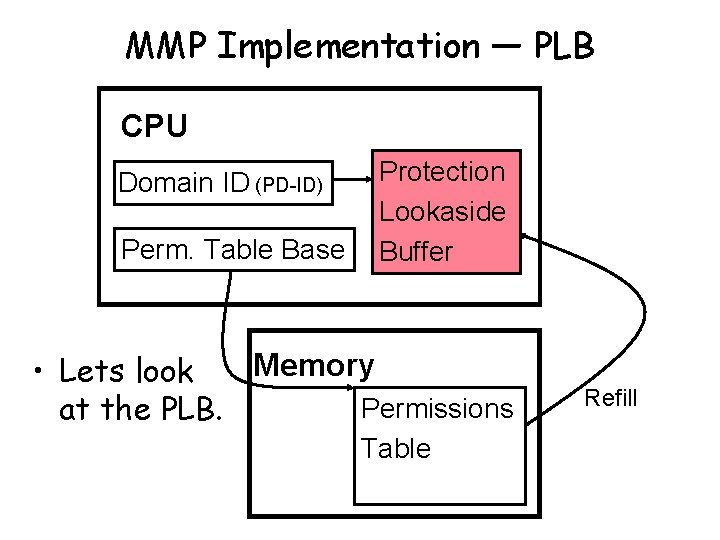
MMP Implementation — PLB CPU Domain ID (PD-ID) Perm. Table Base Protection Lookaside Buffer Memory • Lets look Permissions at the PLB. Table Refill
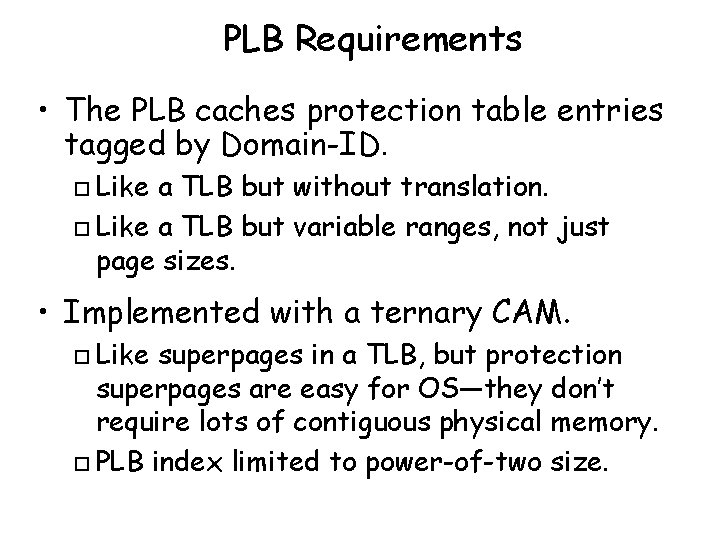
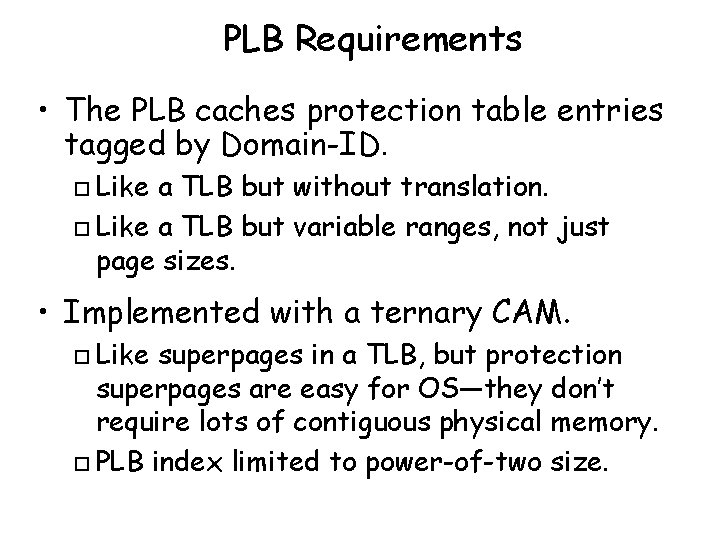
PLB Requirements • The PLB caches protection table entries tagged by Domain-ID. Like a TLB but without translation. o Like a TLB but variable ranges, not just page sizes. o • Implemented with a ternary CAM. Like superpages in a TLB, but protection superpages are easy for OS—they don’t require lots of contiguous physical memory. o PLB index limited to power-of-two size. o
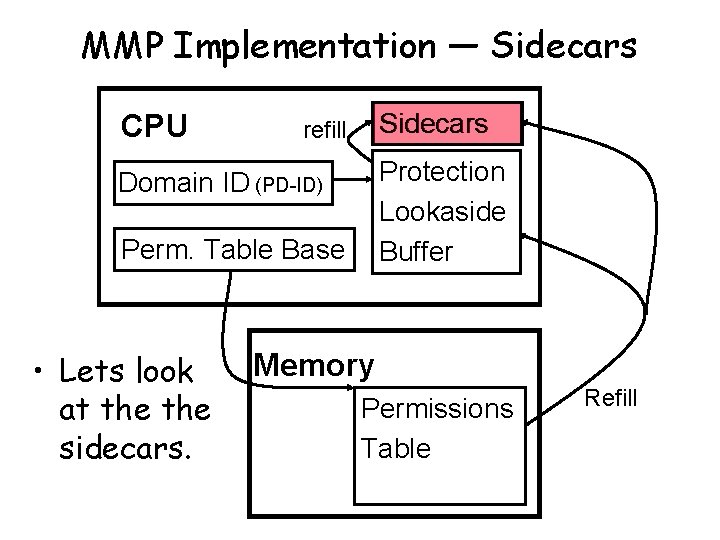
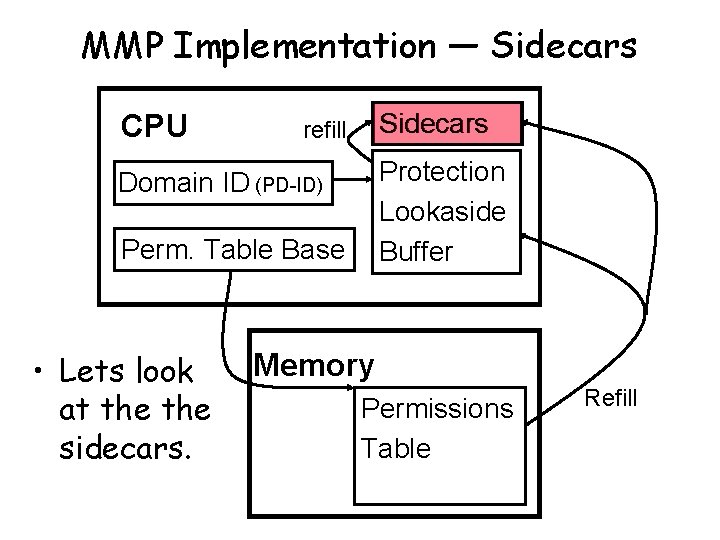
MMP Implementation — Sidecars CPU Sidecars refill Protection Lookaside Buffer Domain ID (PD-ID) Perm. Table Base • Lets look at the sidecars. Memory Permissions Table Refill
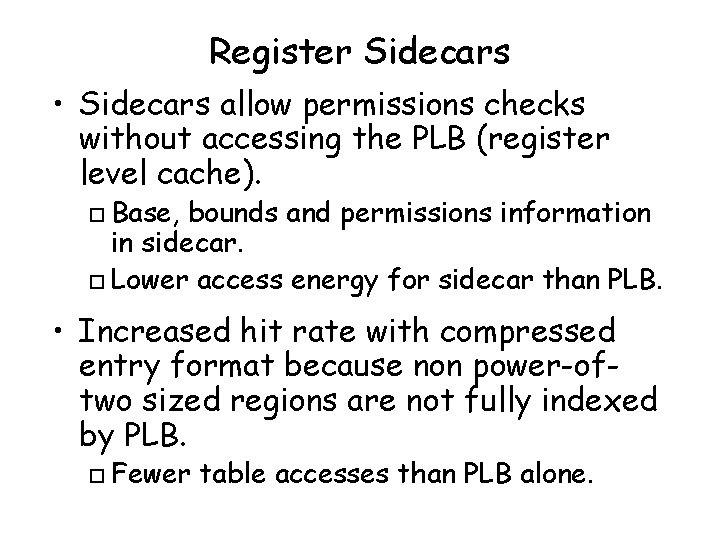
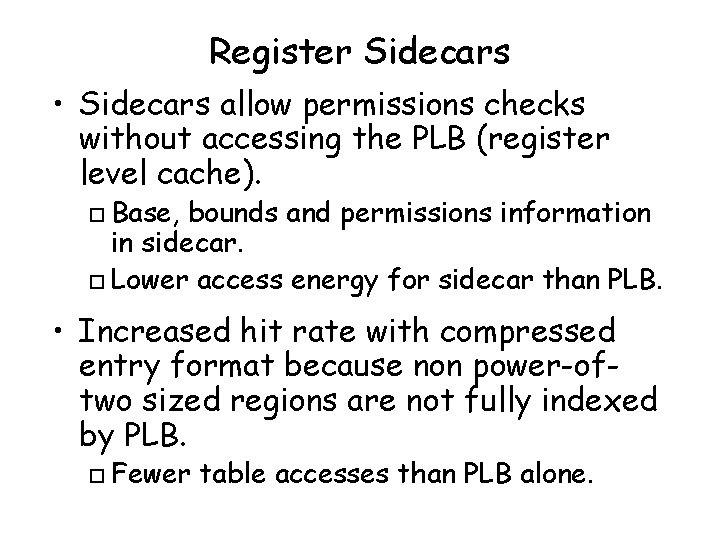
Register Sidecars • Sidecars allow permissions checks without accessing the PLB (register level cache). Base, bounds and permissions information in sidecar. o Lower access energy for sidecar than PLB. o • Increased hit rate with compressed entry format because non power-oftwo sized regions are not fully indexed by PLB. o Fewer table accesses than PLB alone.
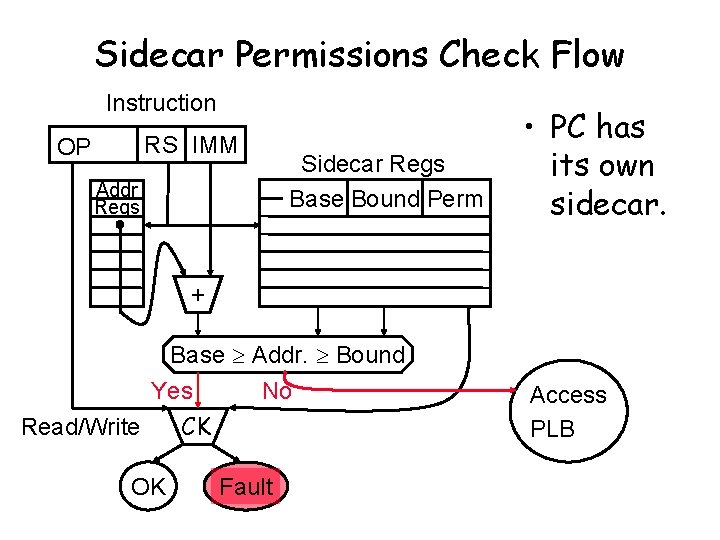
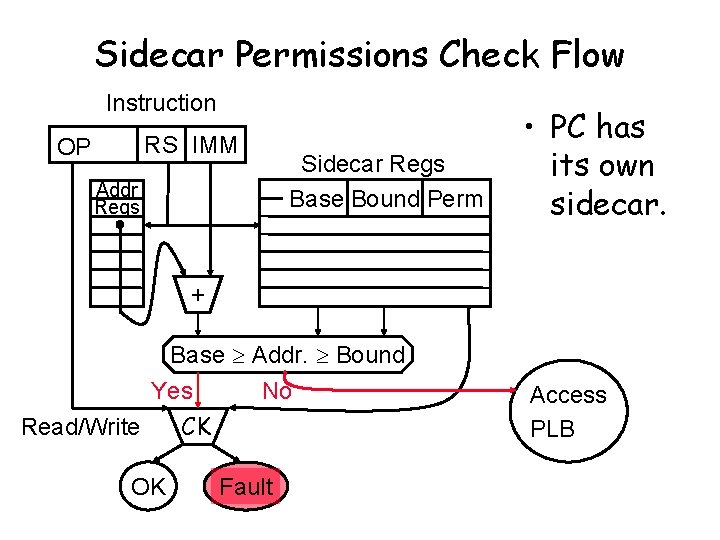
Sidecar Permissions Check Flow Instruction RS IMM OP Addr Regs Sidecar Regs Base Bound Perm • PC has its own sidecar. + Base Addr. Bound Yes No Read/Write OK CK Fault Access PLB
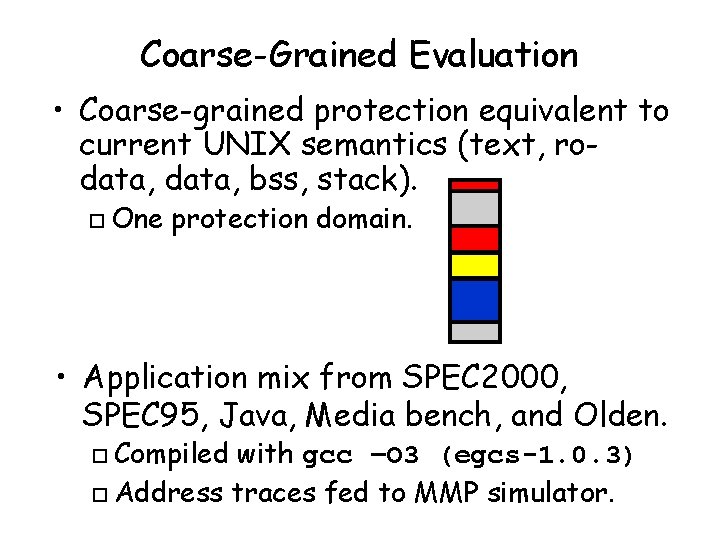
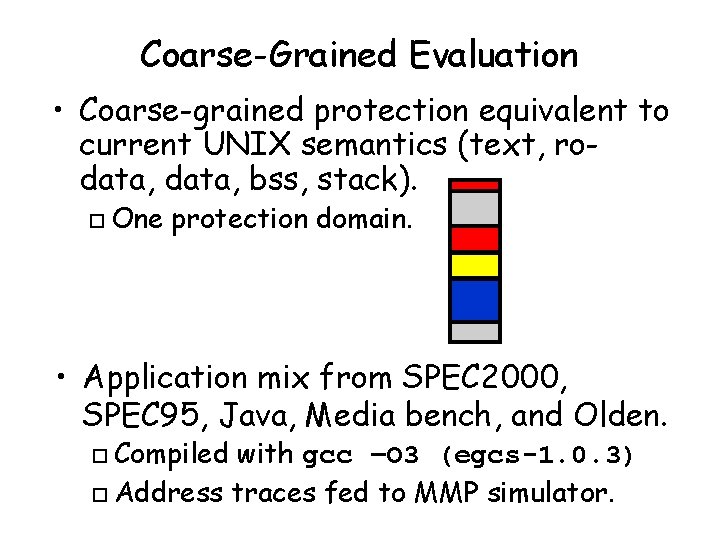
Coarse-Grained Evaluation • Coarse-grained protection equivalent to current UNIX semantics (text, rodata, bss, stack). o One protection domain. • Application mix from SPEC 2000, SPEC 95, Java, Media bench, and Olden. Compiled with gcc –O 3 (egcs-1. 0. 3) o Address traces fed to MMP simulator. o
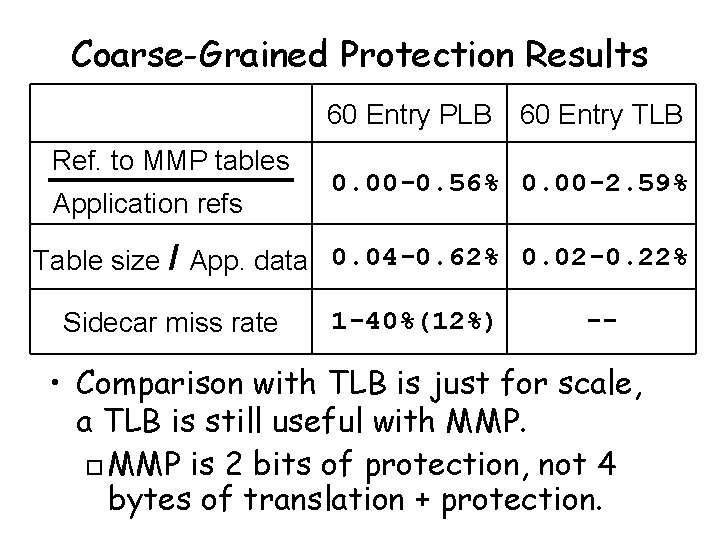
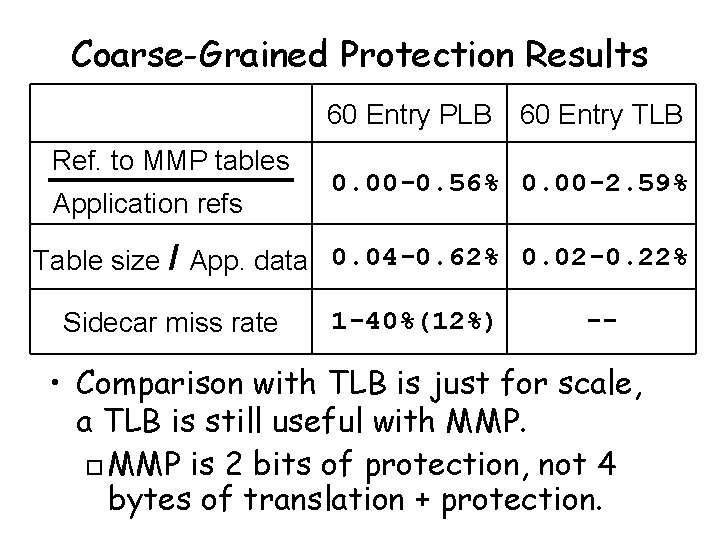
Coarse-Grained Protection Results 60 Entry PLB 60 Entry TLB Ref. to MMP tables Application refs 0. 00 -0. 56% 0. 00 -2. 59% Table size / App. data 0. 04 -0. 62% 0. 02 -0. 22% Sidecar miss rate 1 -40%(12%) -- • Comparison with TLB is just for scale, a TLB is still useful with MMP. o MMP is 2 bits of protection, not 4 bytes of translation + protection.
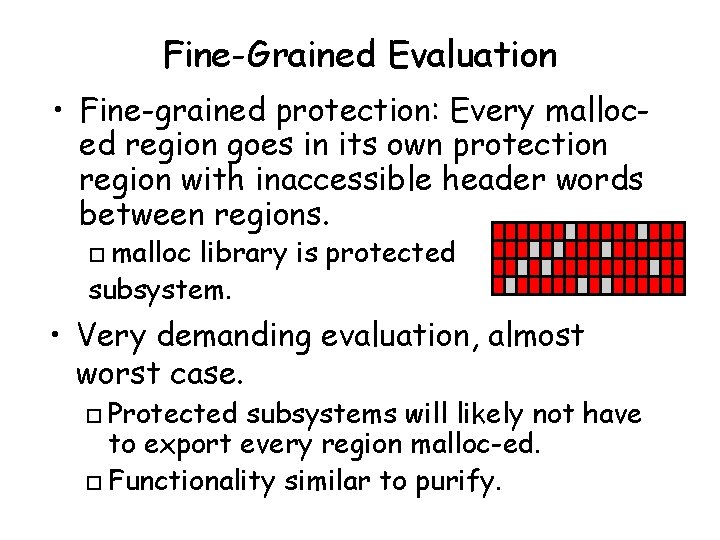
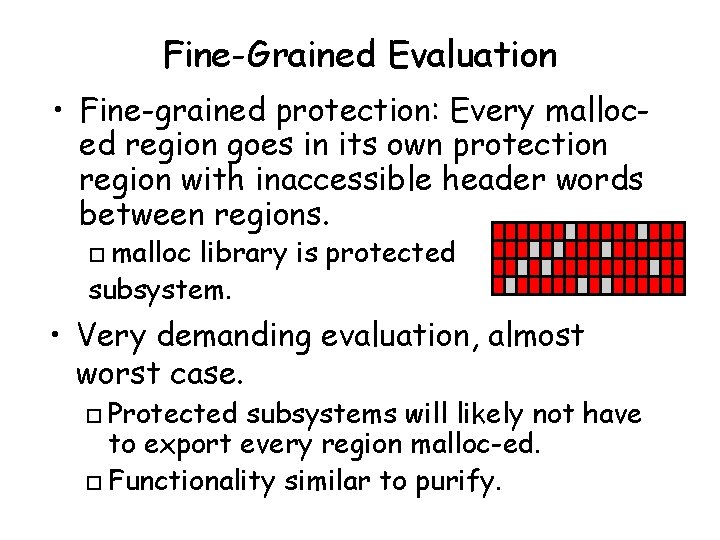
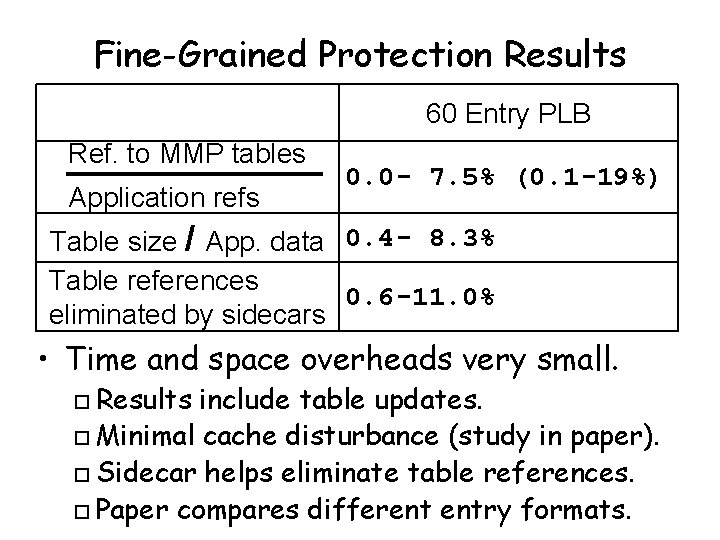
Fine-Grained Evaluation • Fine-grained protection: Every malloced region goes in its own protection region with inaccessible header words between regions. malloc library is protected subsystem. o • Very demanding evaluation, almost worst case. Protected subsystems will likely not have to export every region malloc-ed. o Functionality similar to purify. o
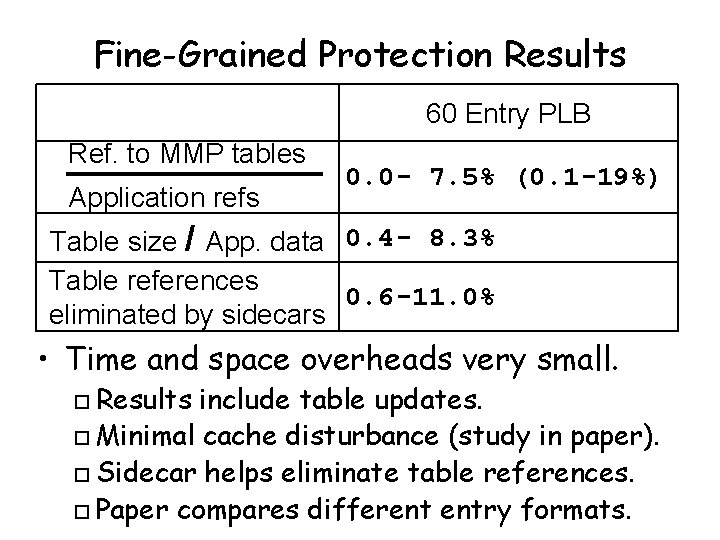
Fine-Grained Protection Results 60 Entry PLB Ref. to MMP tables Application refs 0. 0 - 7. 5% (0. 1 -19%) Table size / App. data 0. 4 - 8. 3% Table references 0. 6 -11. 0% eliminated by sidecars • Time and space overheads very small. Results include table updates. o Minimal cache disturbance (study in paper). o Sidecar helps eliminate table references. o Paper compares different entry formats. o
![Related Work Capabilities Dennis 65 IBM AS 400 Domain Pages Koldinger ASPLOS Related Work • Capabilities [Dennis 65, IBM AS 400]. • Domain Pages [Koldinger ASPLOS](https://slidetodoc.com/presentation_image/1f4f7c62fcd32cfe5b7e907043bd9dc5/image-25.jpg)
Related Work • Capabilities [Dennis 65, IBM AS 400]. • Domain Pages [Koldinger ASPLOS 92]. • Guarded pointers [Carter ASPLOS 94]. • Guarded page tables [Liedke 94]. • IP longest prefix match [Waldvogel TOCS 01].
Possible Applications • Safe kernel modules. o Safe plug-ins for apache and web browsers. • Eliminate memory copying from kernel calls. o Provide specialized kernel entry points. • Support millions of threads, each with a tiny stack. • Implement C++ const. • Use meta-data for cache coherence. • Disallow an activation frame to overrun its stack space or overwrite its return address.
Conclusion • Fine-grained protection is the solution for safe, extensible systems. • Fine-grained protection can be provided efficiently. • Mondriaan Memory Protection will enable more robust software. It matches the way we think about code. o It can be adopted incrementally (e. g. , 1 st just change malloc library). o