ModelBased Design and Verification of Embedded Systems Radu
Model-Based Design and Verification of Embedded Systems Radu Grosu SUNY at Stony Brook www. cs. sunysb. edu/~grosu
Talk Outline § Current trends in embedded software § Hierarchic mode diagrams § Modular reasoning § Efficient analysis [POPL 00, TOPLAS 03] [POPL 00, ASE 01, TOPLAS 03] [CAV 00, CAV 03, ICSE 01] § Extensions and tools [ASE 01, HSCC 00 -01, EW 02] § Current research projects [Career 02, Reuters 02]
A Quiet Computing Revolution Most computation no longer occurs on PCs and servers but rather in embedded devices like: • automobiles, cell phones, insulin pumps and aircraft. The extent of the embedded systems revolution can be seen in a In-Stat/MDR report : • 5. 7 billion embedded microprocessors shipped in 2001 • 98% of all shipped microprocessors • 11% forecasted annual growth through 2006.
Embedded Controllers Control functionality of embedded processors: • Traditionally it was application specific and with minimal amount of software. • Today it demands sophisticated services such as networking capabilities and preemptive scheduling, and is typically implemented in software (EOSs). The cost of software-enabled control: • Continental estimates it to 18% of the total cost of a vehicle in 2010. • For the automotive industry the cost was half of Microsoft revenue in 2001.
Embedded Software Properties Written in high level programming languages: • Typically in C but increasingly in Java or C++. Very stringent dependability requirements: • human safety, consumer expectations, liability and government regulation • BMW recalled 15, 000 7 -series sedans in 2002 at an estimated cost of $50 million. Very difficult to debug because of: • concurrency, interrupts, exceptions, process scheduling and hardware-in-the-loop.
Trends in Assuring Dependability Maturity and convergence of various methods: • Theorem provers, model checkers and compilers use each other techniques, • Run-time verification and testing tools use formal models to derive monitors and tests. Typical techniques to combat state explosion: • Efficient data structures, • Refinement and abstraction, • Modular reasoning.
Integrative Model Hierarchic state machines as common model: • As properties: omega/tree automata, • As designs: finite observation (Kripke) structures, • As code: structured control-flow graphs. Advantages of using this model: • • Support: CAV and compiler-based techniques, Abstraction: navigate between code and properties, Structure: modular reasoning and state exploration, Appeal: software engineers happy (UML, SDL).
Hierarchic Reactive Modules Hierarchic state machine model featuring: • • hierarchic states, state sharing, group transitions, history. Observational trace semantics: • • state refinement, compositional and assume/guarantee reasoning. Efficient model checking • • Symbolic as well as enumerative, Heuristics to exploit the hierarchical structure.
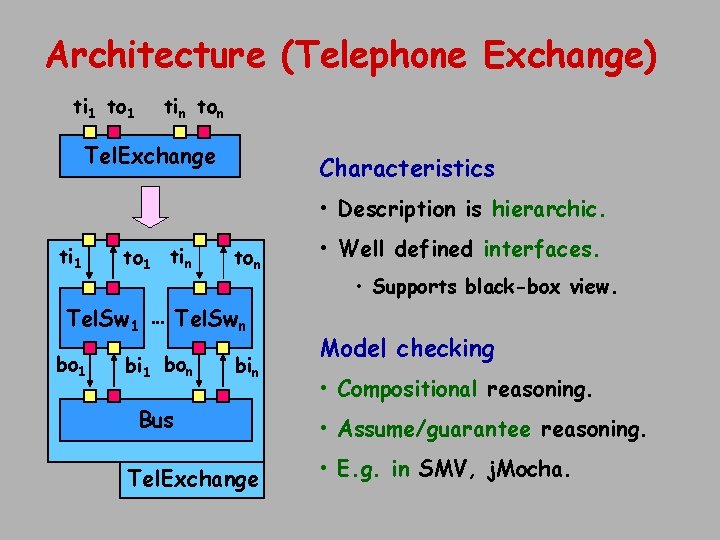
Architecture (Telephone Exchange) ti 1 to 1 tin ton Tel. Exchange Characteristics • Description is hierarchic. ti 1 to 1 tin ton Tel. Sw 1 … Tel. Swn bo 1 bi 1 bon bin Bus Tel. Exchange • Well defined interfaces. • Supports black-box view. Model checking • Compositional reasoning. • Assume/guarantee reasoning. • E. g. in SMV, j. Mocha.
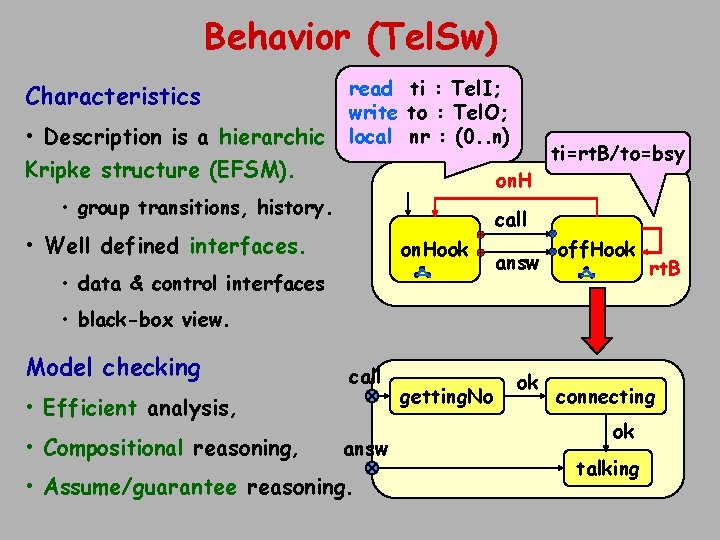
Behavior (Tel. Sw) Characteristics • Description is a hierarchic Kripke structure (EFSM). read ti : Tel. I; write to : Tel. O; local nr : (0. . n) on. H • group transitions, history. ti=rt. B/to=bsy call • Well defined interfaces. on. Hook • data & control interfaces answ off. Hook rt. B • black-box view. Model checking call • Efficient analysis, • Compositional reasoning, answ • Assume/guarantee reasoning. getting. No ok connecting ok talking

Hierarchic Behavior Diagrams Software engineering • Statecharts: introduced in 1987 by David Harel, • Key component in OO Methods: UML, ROOM, OMT, etc, • Event based. Formal methods • Informal diagrams: for LTSs (CCS or CSP processes), • Proof diagrams: for FTS (Pnueli, Manna) • Event based and state-based respectively. Compilers (program analysis) • Structured control-flow graphs, • State-based (variables), entry/exit points, • Sequential programs: no trace semantics or refinement rules.

Modes and Contexts A mode (context) is a tuple (C, V, SM, T) consisting of: read ti : Tel. I; write to : Tel. O; local nr : (0. . n) ini off. H idle rt. E rt. B on. Hook call Read variables Vr: finite set Write variables Vw: finite set Local variables Vl: finite set Submodes m SM visible or not: rt. B ringing Entry points E: finite set. Exit points X: finite set Variables V = Vr Vw Vl: on. H Control points C = E X: m. Vr Vl, off. H answ m. Vw Vl Transitions (e, , x): e E SM. X, x X SM. E Vr Vl Vw Vl

Semantics of Modes Executions (game semantics) • Environment round: from exit points to entry points. • Mode round: from entry points to exit points. • Example: (ini, s 0) (call, s 1) (on. H, s 2) (answ, s 3) • Micro steps: ini on. H off. H idle h=idle de call ~(off. H|rt. B) rt. E dx rt. B h=ringing ~(off. H|rt. B|rt. E) rt. B ringing on. Hook off. H answ (ini, s 0) (idle, t 1) (call, s 1) (ini, s 5) (idle, t 6) (dx, s 6)
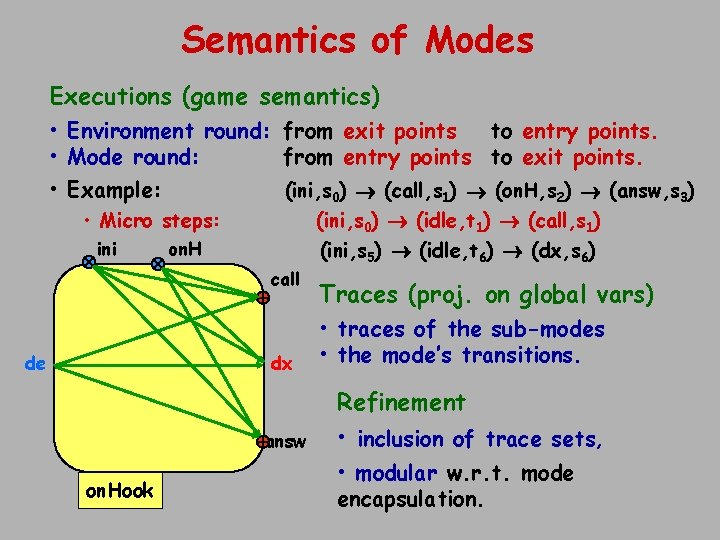
Semantics of Modes Executions (game semantics) • Environment round: from exit points to entry points. • Mode round: from entry points to exit points. • Example: (ini, s 0) (call, s 1) (on. H, s 2) (answ, s 3) • Micro steps: ini on. H call de dx (ini, s 0) (idle, t 1) (call, s 1) (ini, s 5) (idle, t 6) (dx, s 6) Traces (proj. on global vars) • traces of the sub-modes • the mode’s transitions. Refinement answ on. Hook • inclusion of trace sets, • modular w. r. t. mode encapsulation.

Modular Reasoning Terminology • Compositional and assume/guarantee reasoning based on observable behaviors. Application area • Only recently is being automated by model checkers, • Until now restricted to architecture hierarchies. Compositional Reasoning • Central to many formalisms: CCS, I/O Automata, TLA, etc. Circular Assume/Guarantee Reasoning • Valid only when the interaction of a module with its environment is non-blocking.
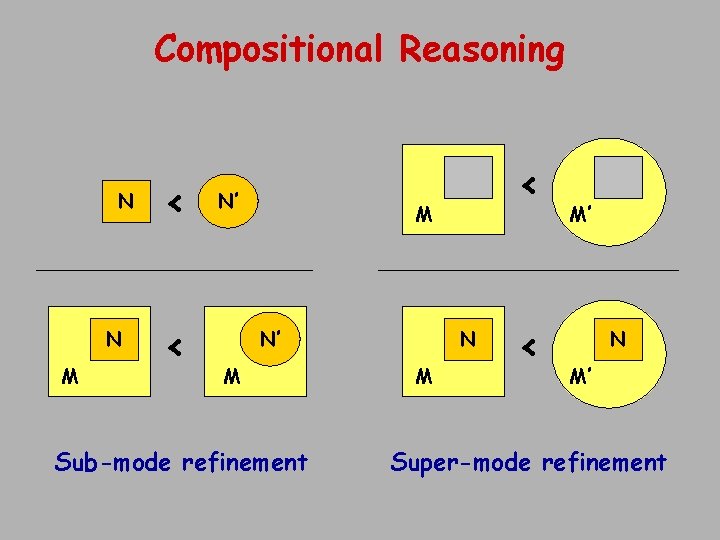
Compositional Reasoning N N M < < N’ < M N N’ M Sub-mode refinement M < M’ N M’ Super-mode refinement

Assume/Guarantee Reasoning N’ M < N N’ M’ M’ N M < N’ M’
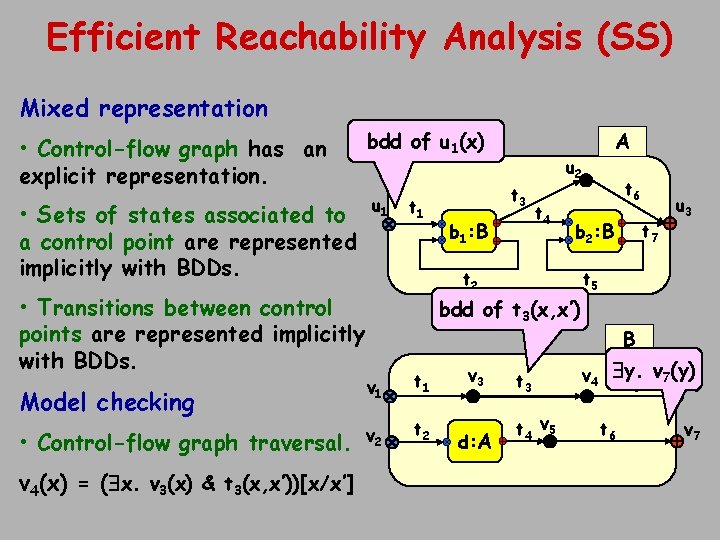
Efficient Reachability Analysis (SS) Mixed representation • Control-flow graph has an explicit representation. bdd of u 1(x) • Sets of states associated to a control point are represented implicitly with BDDs. u 1 • Transitions between control points are represented implicitly with BDDs. Model checking • Control-flow graph traversal. v 4(x) = ( x. v 3(x) & t 3(x, x’))[x/x’] t 1 t 3 b 1: B A u 2 t 4 t 6 b 2: B t 2 t 5 bdd of t 3(x, x’) v 1 t 1 v 2 t 2 v 3 d: A t 7 u 3 t 4 v 5 B v 4 y. v 7(y) t v 5 t 6 6 v 7
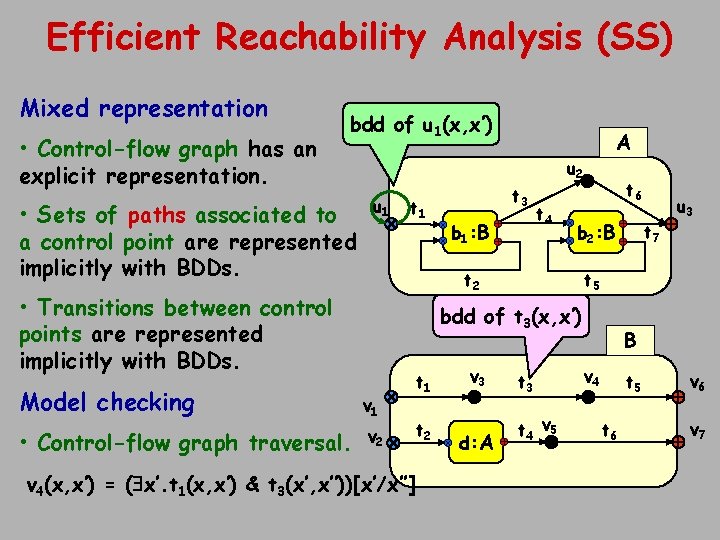
Efficient Reachability Analysis (SS) Mixed representation • Control-flow graph has an explicit representation. bdd of u 1(x, x’) • Sets of paths associated to a control point are represented implicitly with BDDs. u 1 t 3 b 1: B u 2 t 4 t 6 b 2: B t 2 • Transitions between control points are represented implicitly with BDDs. A t 5 bdd of t 3(x, x’) Model checking v 1 • Control-flow graph traversal. v 2 v 4(x, x’) = ( x’. t 1(x, x’) & t 3(x’, x’’))[x’/x’’] t 1 t 2 v 3 d: A t 7 u 3 t 4 v 5 B v 4 t 5 t 6 v 7
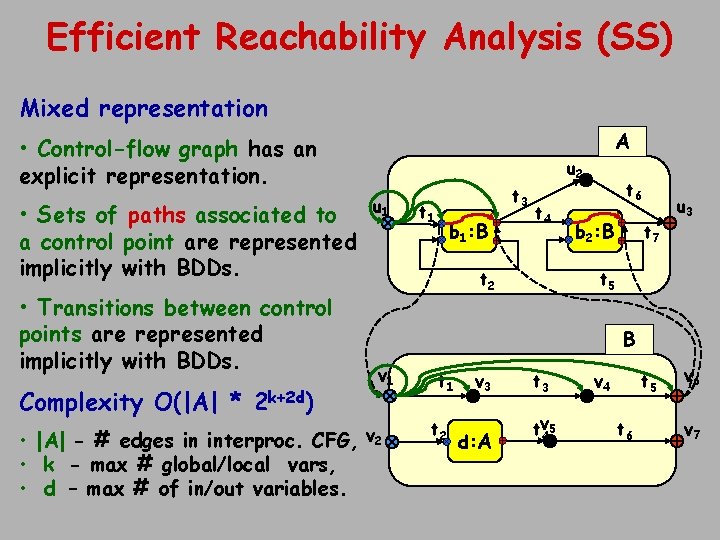
Efficient Reachability Analysis (SS) Mixed representation A • Control-flow graph has an explicit representation. • Sets of paths associated to a control point are represented implicitly with BDDs. • Transitions between control points are represented implicitly with BDDs. Complexity O(|A| * 2 k+2 d) u 1 t 1 b 1: B t 4 t 2 t 6 b 2: B t 7 u 3 t 5 B v 1 • |A| - # edges in interproc. CFG, v 2 • k - max # global/local vars, • d – max # of in/out variables. t 3 u 2 t 1 t 2 v 3 d: A t 3 tv 45 v 4 t 5 t 6 v 7
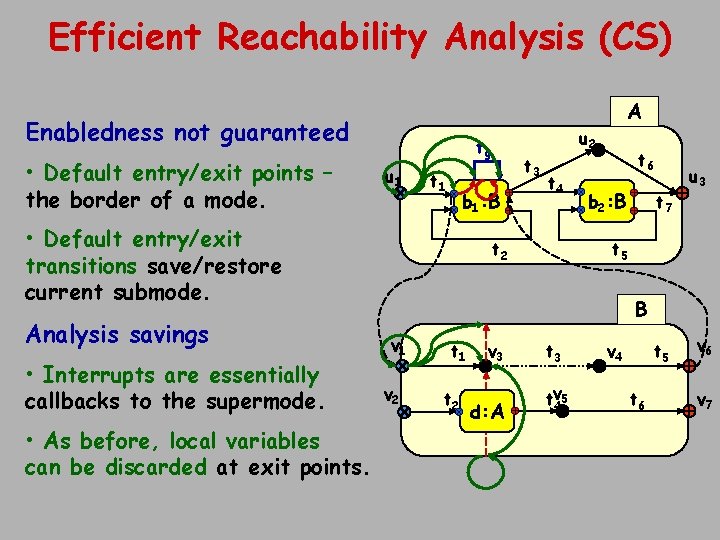
Efficient Reachability Analysis (CS) A Enabledness not guaranteed • Default entry/exit points – the border of a mode. tg u 1 t 1 b 1: B • Default entry/exit transitions save/restore current submode. Analysis savings • Interrupts are essentially callbacks to the supermode. • As before, local variables can be discarded at exit points. t 3 u 2 t 4 t 2 t 6 b 2: B t 7 u 3 t 5 B v 1 v 2 t 1 t 2 v 3 d: A t 3 tv 45 v 4 t 5 t 6 v 7
Other Techniques Structured control-flow representation opens the way to applying various other CAV and compiler analysis techniques: • control-flow & counterexample guided abstraction-refinement, • shape analysis, live variable analysis, modification / reference sets, • pattern-based model extraction.
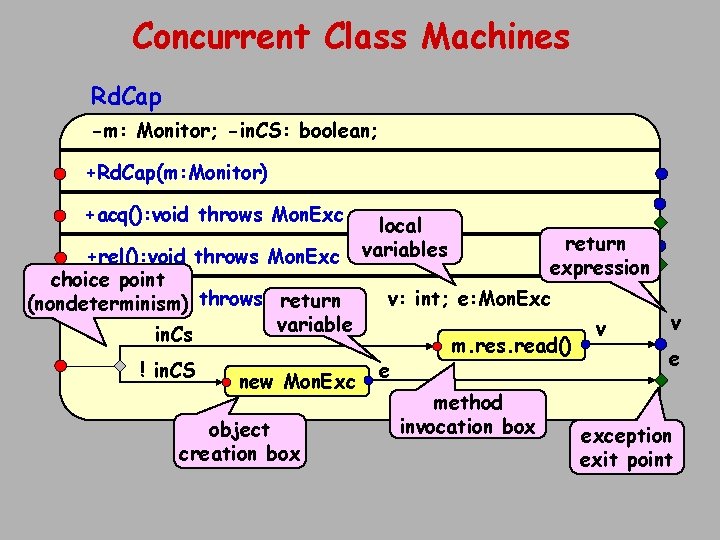
Concurrent Class Machines Rd. Cap -m: Monitor; -in. CS: boolean; +Rd. Cap(m: Monitor) +acq(): void throws Mon. Exc +rel(): void throws Mon. Exc choice point +read(): int throws Mon. Exc return (nondeterminism) variable in. Cs ! in. CS new Mon. Exc object creation box local variables return expression v: int; e: Mon. Exc e m. res. read() method invocation box v v e exception exit point
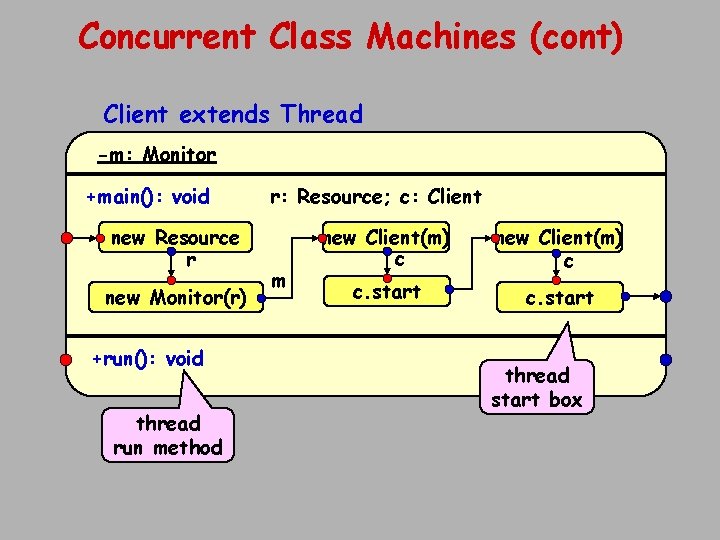
Concurrent Class Machines (cont) Client extends Thread -m: Monitor +main(): void new Resource r new Monitor(r) +run(): void thread run method r: Resource; c: Client m new Client(m) c c. start thread start box
![Hierarchic Hybrid Machines (Charon) differential constraint • {t = 1} { level [2, 10] Hierarchic Hybrid Machines (Charon) differential constraint • {t = 1} { level [2, 10]](http://slidetodoc.com/presentation_image_h2/5e1d4c5391d1170d89a8ad1a5d1e104b/image-25.jpg)
Hierarchic Hybrid Machines (Charon) differential constraint • {t = 1} { level [2, 10] } Compute t=10 e local t, rate global level, infusion • {level = f(infusion)} level [4, 8] x dx de t: =0 level global infusion level [2, 10] Emergency infusion Maintain {t<10} Normal Agent Controller invariant • Agents describe concurrency • Modes describe sequential behavior – Control flow between control points – Group transitions describe exceptions Agent Tank

Hermes: Top Level

Hermes: Looking Inside Modes
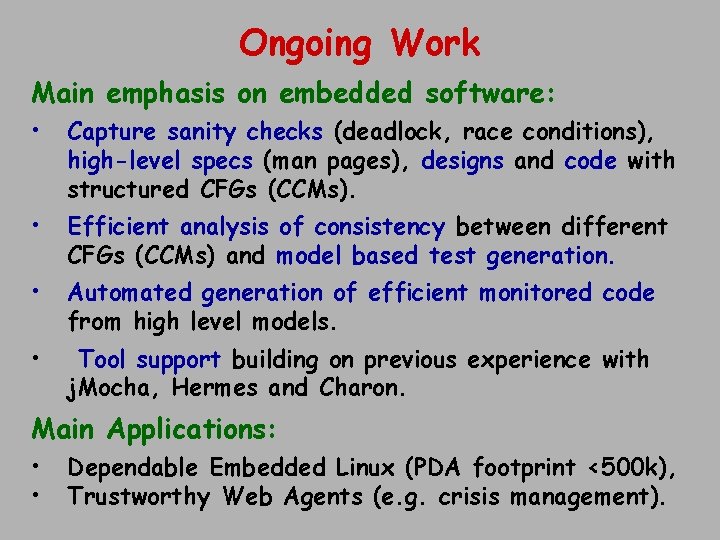
Ongoing Work Main emphasis on embedded software: • Capture sanity checks (deadlock, race conditions), high-level specs (man pages), designs and code with structured CFGs (CCMs). • Efficient analysis of consistency between different CFGs (CCMs) and model based test generation. • Automated generation of efficient monitored code from high level models. • Tool support building on previous experience with j. Mocha, Hermes and Charon. Main Applications: • • Dependable Embedded Linux (PDA footprint <500 k), Trustworthy Web Agents (e. g. crisis management).

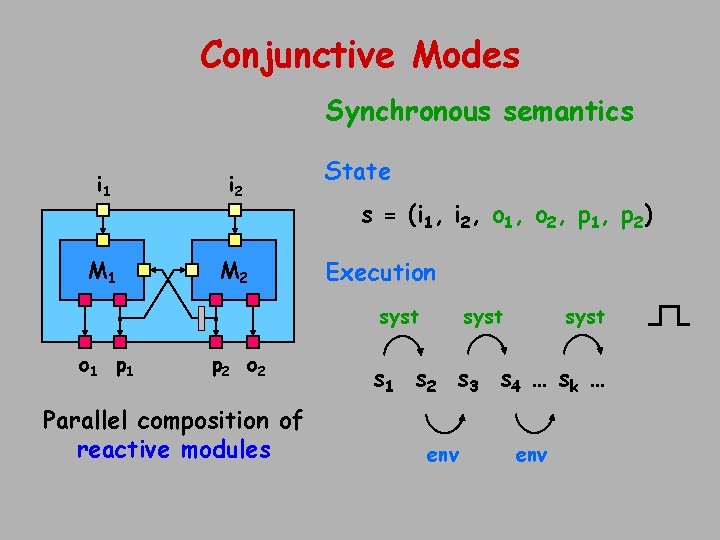
Conjunctive Modes Synchronous semantics i 1 i 2 M 1 M 2 State s = (i 1, i 2, o 1, o 2, p 1, p 2) Execution syst o 1 p 2 o 2 Parallel composition of reactive modules syst s 1 s 2 s 3 s 4 … s k … env
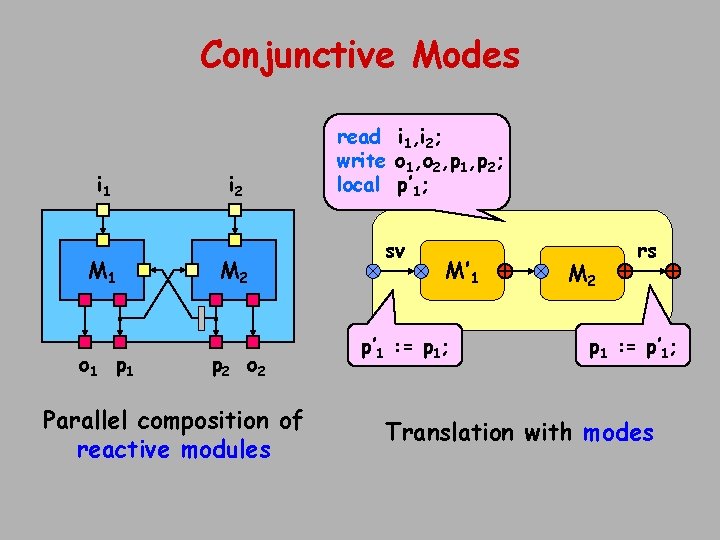
Conjunctive Modes i 1 M 1 o 1 p 1 i 2 M 2 p 2 o 2 Parallel composition of reactive modules read i 1, i 2; write o 1, o 2, p 1, p 2; local p’ 1; sv M’ 1 p’ 1 : = p 1; M 2 rs p 1 : = p’ 1; Translation with modes
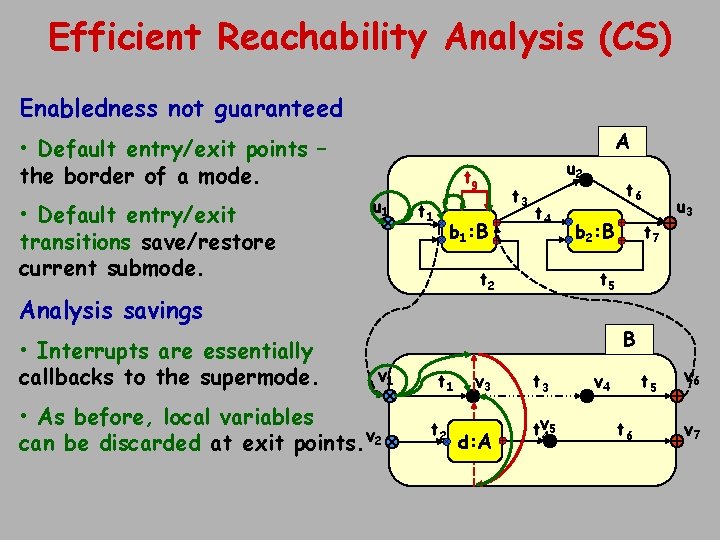
Efficient Reachability Analysis (CS) Enabledness not guaranteed A • Default entry/exit points – the border of a mode. • Default entry/exit transitions save/restore current submode. tg u 1 t 1 b 1: B t 4 t 2 Analysis savings • Interrupts are essentially callbacks to the supermode. t 3 u 2 t 6 b 2: B t 7 u 3 t 5 B v 1 • As before, local variables can be discarded at exit points. v 2 t 1 t 2 v 3 d: A t 3 tv 45 v 4 t 5 t 6 v 7
- Slides: 32