MOCA Mobile Certificate Authority for Wireless Ad Hoc
MOCA : Mobile Certificate Authority for Wireless Ad Hoc Networks The 2 nd Annual PKI Research Workshop (PKI 2003) Seung Yi, Robin Kravets September. 25, 2003 Presented by Sookhyun, Yang
Contents n Introduction n Background n Requirements n MOCA (MObile Certificate Authority) Framework n Evaluation n Conclusion 2
Introduction n Wireless ad hoc networks n Infrastructure-less nature n n n Inhibit guaranteeing any kind of connectivity Increased physical vulnerability of the nodes Key management framework for ad hoc networks n MOCA framework n PKI (Public Key Infrastructure) without infrastrucutre n n Threshold cryptography n MOCA nodes Communication protocol between a client and CAs n MP (MOCA certification protocol) 3

Background n PKI n Collection of components and procedure that support the management of cryptographic keys through the use of digital certificates n Public key certificate CA MOCAs KUa CA KUb CB CA’s private key : KRauth CA’s public key : KUauth X’s public key : Kux (1) CA A B CA = EKRauth[TIme 1, IDA, KUa] (2) CB n Threshold cryptography n n threshold Divide up a secret to n pieces Reconstruct the full secret with any k pieces out of those n 4
Requirements n Requirements for MOCA framework n Fault tolerance n n n Security n n n Maintain correct operation in the presence of faulty nodes Tolerant to a fraction of faulty nodes Act as the trust anchor for the whole network Operate securely against malicious nodes or adversaries Availability n n Highly dependent on the connectivity of the network Certification service should be always available to clients 5
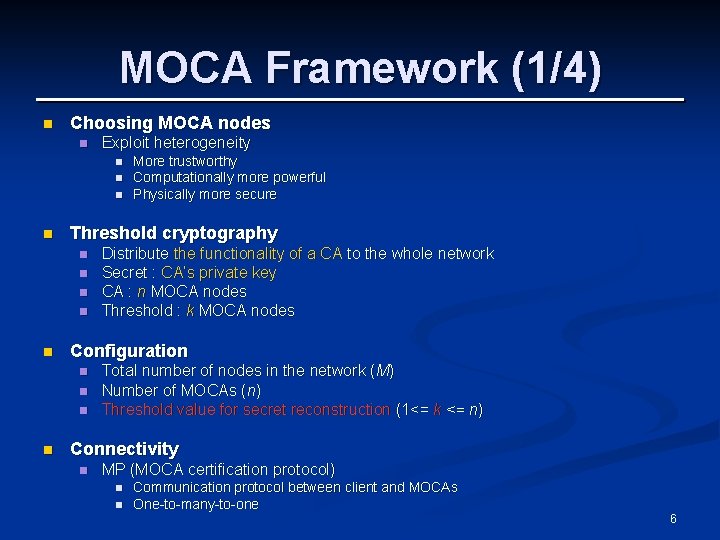
MOCA Framework (1/4) n Choosing MOCA nodes n Exploit heterogeneity n n Threshold cryptography n n n Distribute the functionality of a CA to the whole network Secret : CA’s private key CA : n MOCA nodes Threshold : k MOCA nodes Configuration n n More trustworthy Computationally more powerful Physically more secure Total number of nodes in the network (M) Number of MOCAs (n) Threshold value for secret reconstruction (1<= k <= n) Connectivity n MP (MOCA certification protocol) n n Communication protocol between client and MOCAs One-to-many-to-one 6
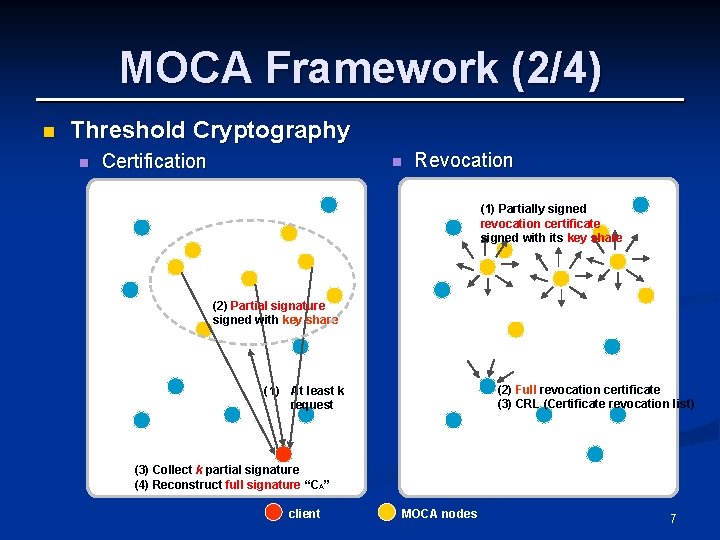
MOCA Framework (2/4) n Threshold Cryptography n Certification n Revocation (1) Partially signed revocation certificate signed with its key share (2) Partial signature signed with key share (2) Full revocation certificate (3) CRL (Certificate revocation list) (1) At least k request (3) Collect k partial signature (4) Reconstruct full signature “CA” client MOCA nodes 7
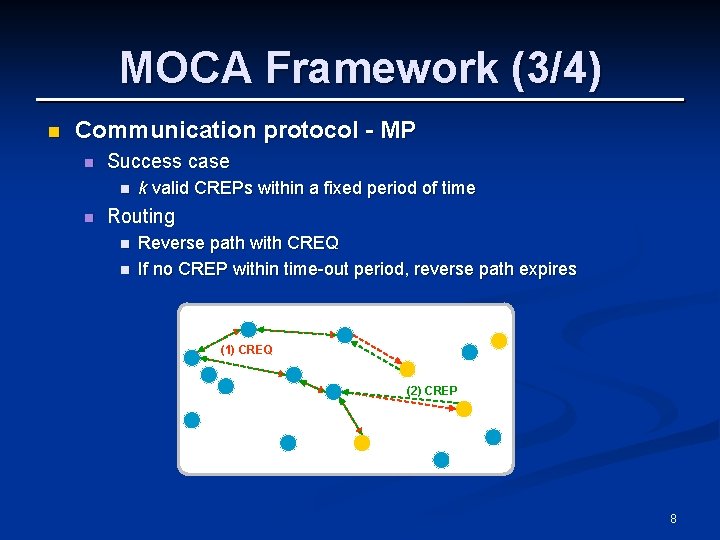
MOCA Framework (3/4) n Communication protocol - MP n Success case n n k valid CREPs within a fixed period of time Routing n n Reverse path with CREQ If no CREP within time-out period, reverse path expires (1) CREQ (2) CREP 8
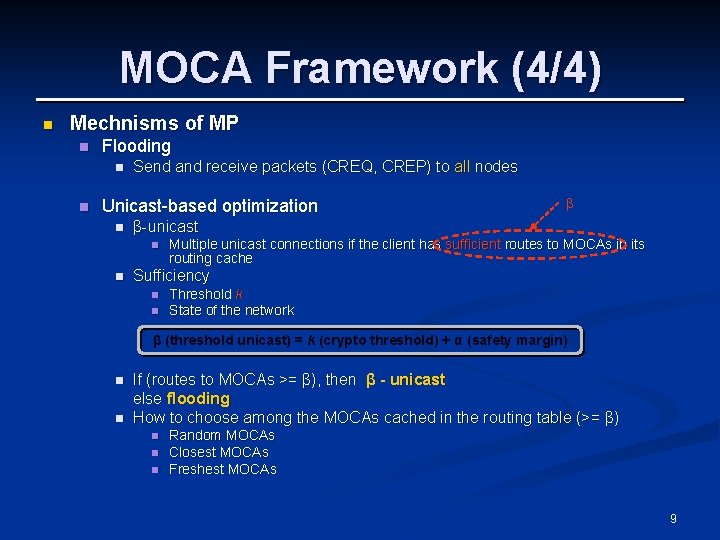
MOCA Framework (4/4) n Mechnisms of MP n Flooding n n Send and receive packets (CREQ, CREP) to all nodes Unicast-based optimization n β-unicast n n β Multiple unicast connections if the client has sufficient routes to MOCAs in its routing cache Sufficiency n n Threshold k State of the network β (threshold unicast) = k (crypto threshold) + α (safety margin) n n If (routes to MOCAs >= β), then β - unicast else flooding How to choose among the MOCAs cached in the routing table (>= β) n n n Random MOCAs Closest MOCAs Freshest MOCAs 9
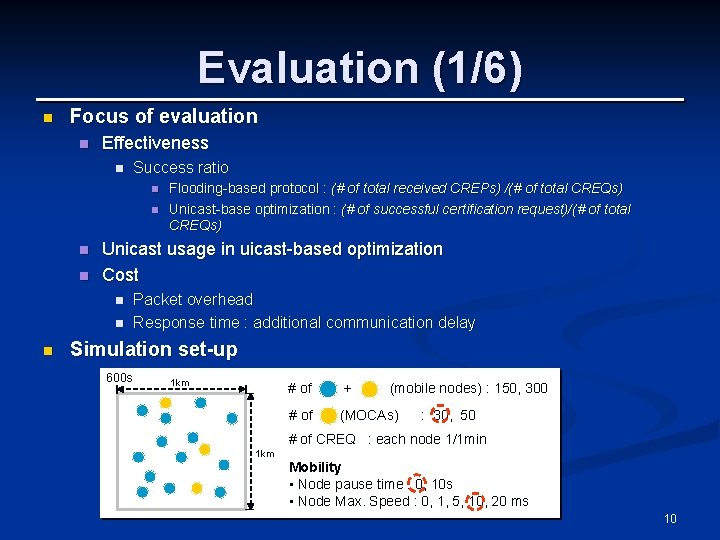
Evaluation (1/6) n Focus of evaluation n Effectiveness n Success ratio n n Unicast usage in uicast-based optimization Cost n n n Flooding-based protocol : (# of total received CREPs) /(# of total CREQs) Unicast-base optimization : (# of successful certification request)/(# of total CREQs) Packet overhead Response time : additional communication delay Simulation set-up 600 s 1 km # of + (mobile nodes) : 150, 300 # of (MOCAs) : 30, 50 # of CREQ : each node 1/1 min 1 km Mobility • Node pause time : 0, 10 s • Node Max. Speed : 0, 1, 5, 10, 20 ms 10
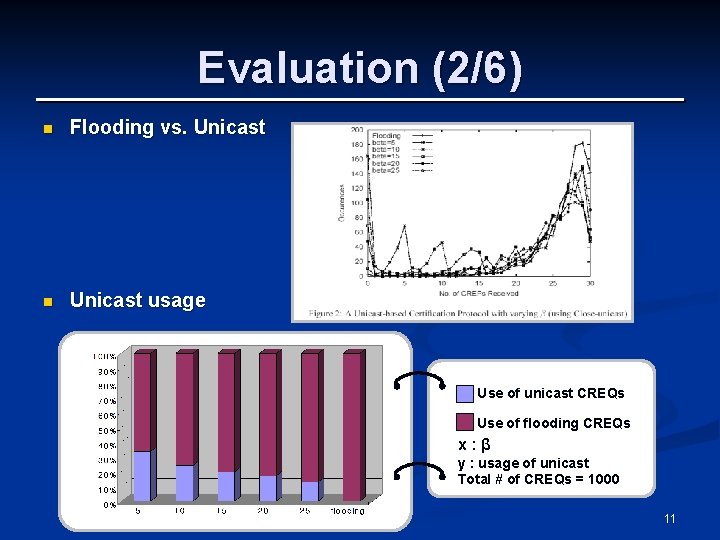
Evaluation (2/6) n Flooding vs. Unicast n Unicast usage Use of unicast CREQs Use of flooding CREQs x: β y : usage of unicast Total # of CREQs = 1000 11
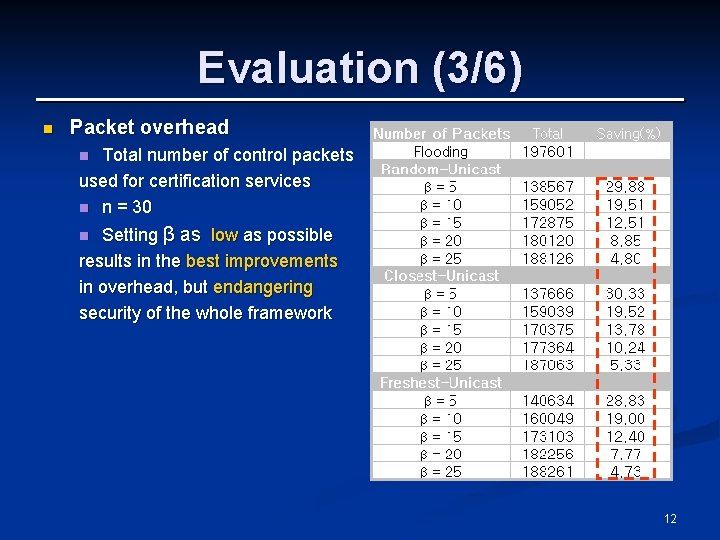
Evaluation (3/6) n Packet overhead Total number of control packets used for certification services n n = 30 n Setting β as low as possible results in the best improvements in overhead, but endangering security of the whole framework n 12
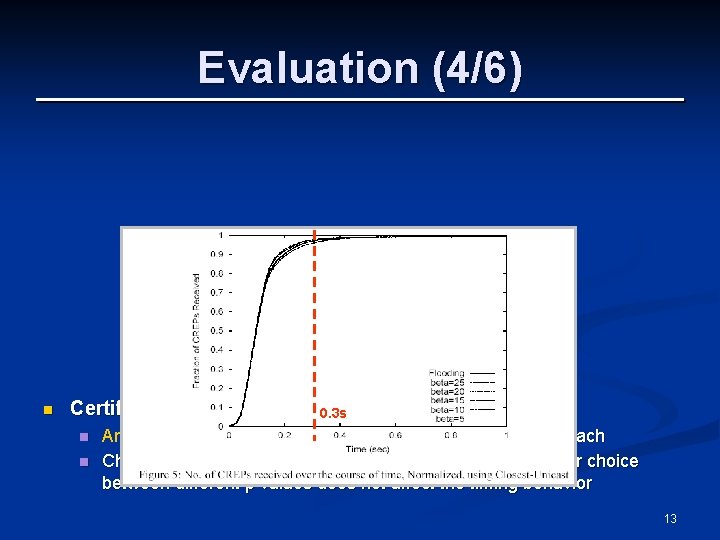
Evaluation (4/6) n Certification delay n n 0. 3 s Arrival time of CREP packets with the closest-unicast approach Choice between flooding and unicast-based optimizations or choice between different β values does not affect the timing behavior 13
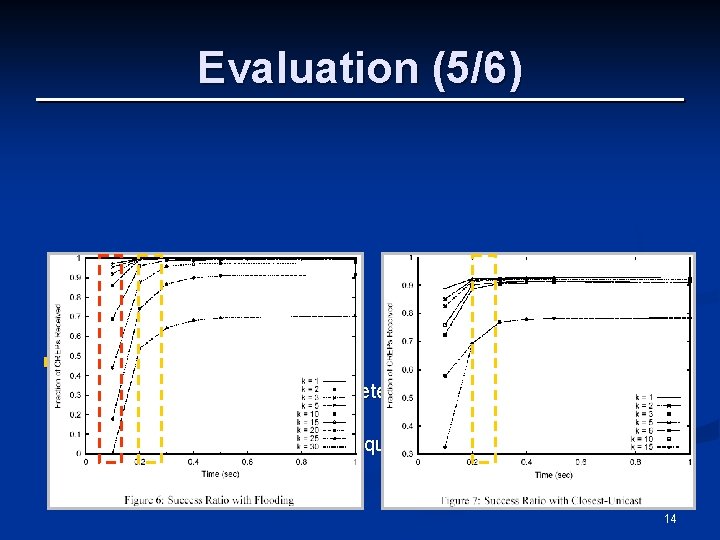
Evaluation (5/6) n Success ratios n n α plays an important role in determining the success ratio within a given τ Helpful when deciding an adequate τ for a given k 14
Evaluation (6/6) n Summary n High success ratio n n n Reduced overhead n n Flooding-based protocol : almost 99% Unicast-based optimization : 75%~97% Unicast optimization saves up to about 30% of control packets Certification delay is acceptable 15
Conclusion n Present a practical key management framework for ad hoc wireless networks using PKI n Clarify the necessity and the problem of providing a PKI framework for ad hoc network n Identify requirements for such a framework n Show effectiveness of paper’s approach through simulation results n Provide some insights into the configuration of such security services in ad hoc networks 16
- Slides: 16