Mobile Sensor Networks PeiLing Chiu Outline l l
Mobile Sensor Networks Pei-Ling Chiu
Outline l l Research Framework Paper: ”Movement-Assisted Sensor Deployment” Related Work Discussion Pei-Ling Chiu 2
Movement-Assisted Sensor Deployment Guiling Wang, Guohong Cao, and Tom La Porta Department of Computer Science & Engineering The Pennsylvania State University IEEE INFOCOM 2004 Pei-Ling Chiu
Introduction In this paper, the authors design and evaluate three distributed self -deployment protocols for sensor networks. The problem statement is: given the target area, how to maximize the sensor coverage with less time, movement distance and message complexity. The proposed distributed self-deployment protocols l l l l 1. To discover the existence of coverage holes 2. The proposed protocols calculate the target positions of these sensors. They use Voronoi diagrams to discover the coverage holes and design three movement-assisted sensor deployment protocols. Performance metrics: coverage, deployment time, moving distance, scalability to initial deployment and communication range, etc. Pei-Ling Chiu 4
Voronoi Diagram l l l l The Voronoi diagram of a collection of nodes partitions the space into polygons. Every point in a given polygon is closer to the node in this polygon than to any other node. Fig. 1 Voronoi polygon of point O: Gp(O)=( p(O), Ep(O)) p(O) is the set of Voronoi vertices of O. Ep(O) is the set of Voronoi edges of O. N(O) denotes the set of Voronoi neighbors of O. The Voronoi edges of O are the vertical bisectors of the line passing O and its Voronoi neighbors, e. g. , V 5 V 1 is OA’s bisector. Pei-Ling Chiu 5
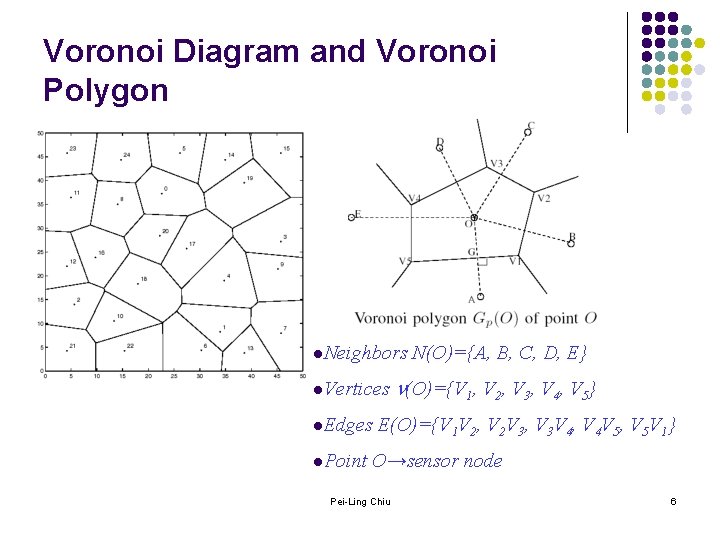
Voronoi Diagram and Voronoi Polygon l. Neighbors l. Vertices l. Edges l. Point N(O)={A, B, C, D, E} (O)={V 1, V 2, V 3, V 4, V 5} E(O)={V 1 V 2, V 2 V 3, V 3 V 4, V 4 V 5, V 5 V 1} O→sensor node Pei-Ling Chiu 6
Voronoi Diagram l l l These Voronoi polygons together cover the target field. The points inside one polygon are closer to the sensor inside this polygon than the sensors positioned elsewhere. Each sensor is responsible for the sensing task in its Voronoi polygon. In this way, each sensor can examine the coverage hole locally. To construct the Voronoi polygon, each sensor only needs to know the existence of its Voronoi neighbors, which reduces the communication complexity. Pei-Ling Chiu 7
Movement-Assisted Sensor Deployment Protocols l l The sensor deployment protocol runs iteratively until it terminates or reaches the specified maximum round. In each round, sensors 1. 2. 3. 4. To broadcast their locations To construct their local Voronoi polygons based on the received neighbor information The Voronoi polygons are examined to determine the existence of coverage holes. If any coverage hole exists, sensors decide where to move to eliminate or reduce the size of the coverage hole; otherwise, they stay. Pei-Ling Chiu 8
Three Movement-Assisted Sensor Deployment Protocols l The VECtor-based Algorithm (VEC) l l l The virtual forces will push sensors from the densely covered area to the sparsely covered area. The VORonoi-based Algorithm (VOR) The Minimax Algorithm (Minimax) Pei-Ling Chiu 9
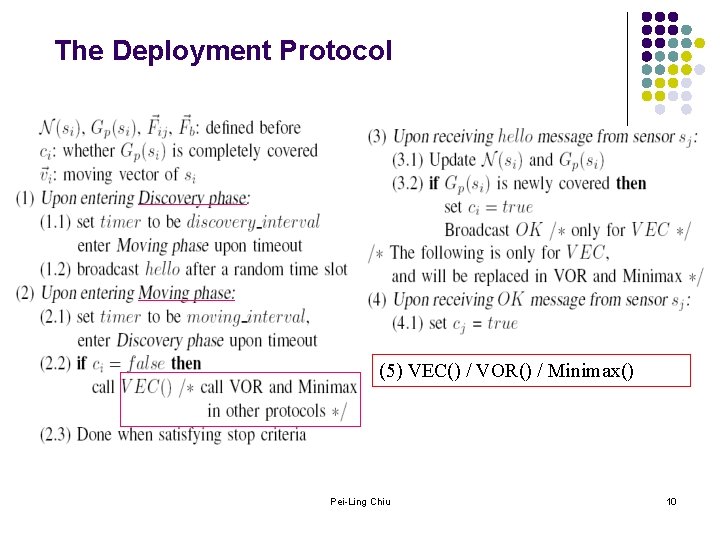
The Deployment Protocol (5) VEC() / VOR() / Minimax() Pei-Ling Chiu 10
The VECtor-based Algorithm l l l VEC is motivated by the attributes of electro-magnetic particles: when two electro-magnetic particles are too close to each other, an expelling force pushes them apart. Assume d(si, sj) is the distance between sensor si and sensor sj. dave is the average distance between two sensors when the sensors are evenly distributed in the target area. dave can be calculated beforehand since the target area and the number of sensors to be deployed are known. The virtual force exerted by sj on si is denoted as Fij , with the direction from sj to si. Pei-Ling Chiu 11
Virtual Force l l The virtual force between two sensors si and sj will push them to move (dave - d(si, sj))/2 away from each other. In case one sensor covers its Voronoi polygon completely and should not move, the other sensor will be pushed dave - d(si, sj) away. The field boundary also exert forces, denoted as Fb, to push sensors too close to the boundary inside. Fb exerted on si will push it to move dave/ 2 - db(si) l l l db(si) is the distance of si to the boundary. dave/2 is the distance from the boundary to the sensors closest to it when sensors are evenly distributed. The final overall force on sensors is the vector summation of virtual forces from the boundary and all Voronoi neighbors. Pei-Ling Chiu 12
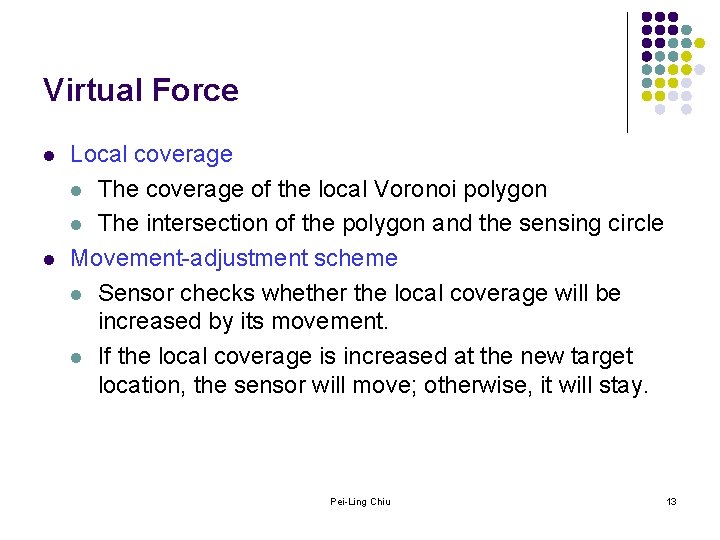
Virtual Force l l Local coverage l The coverage of the local Voronoi polygon l The intersection of the polygon and the sensing circle Movement-adjustment scheme l Sensor checks whether the local coverage will be increased by its movement. l If the local coverage is increased at the new target location, the sensor will move; otherwise, it will stay. Pei-Ling Chiu 13
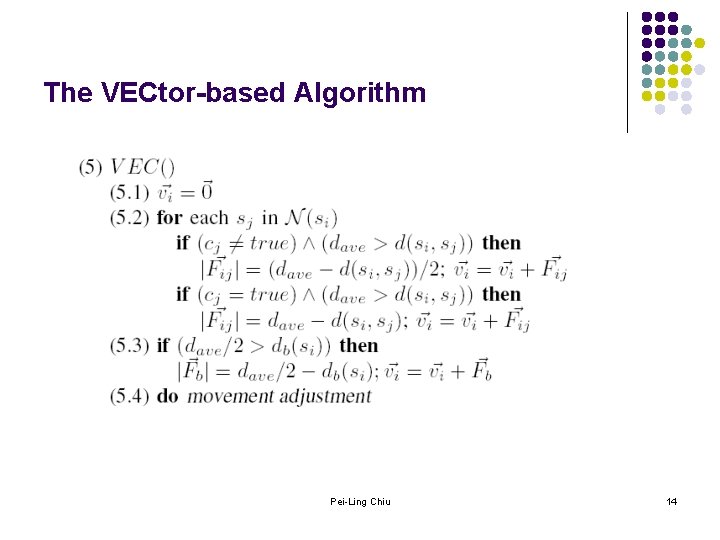
The VECtor-based Algorithm Pei-Ling Chiu 14
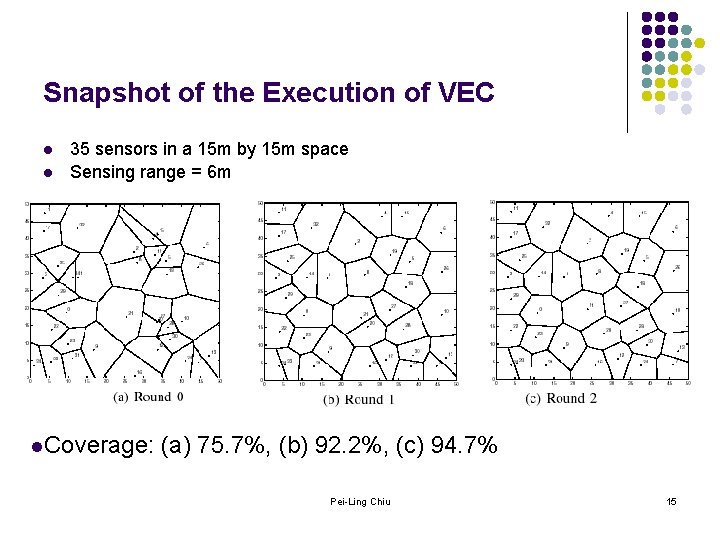
Snapshot of the Execution of VEC l l 35 sensors in a 15 m by 15 m space Sensing range = 6 m l. Coverage: (a) 75. 7%, (b) 92. 2%, (c) 94. 7% Pei-Ling Chiu 15
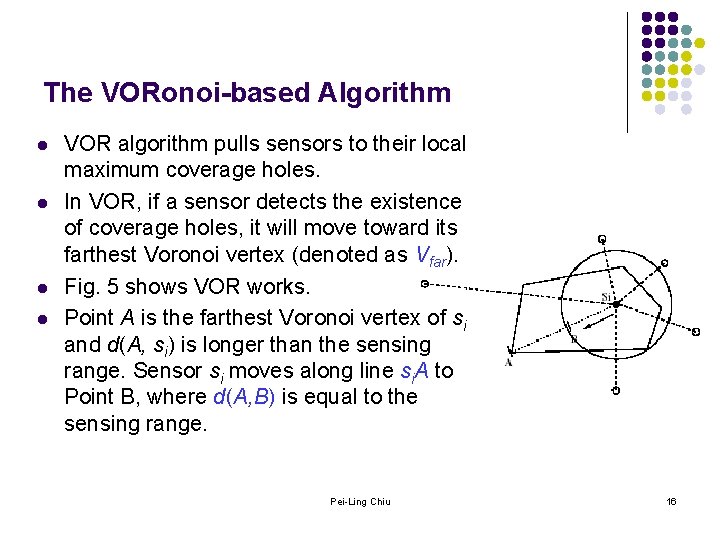
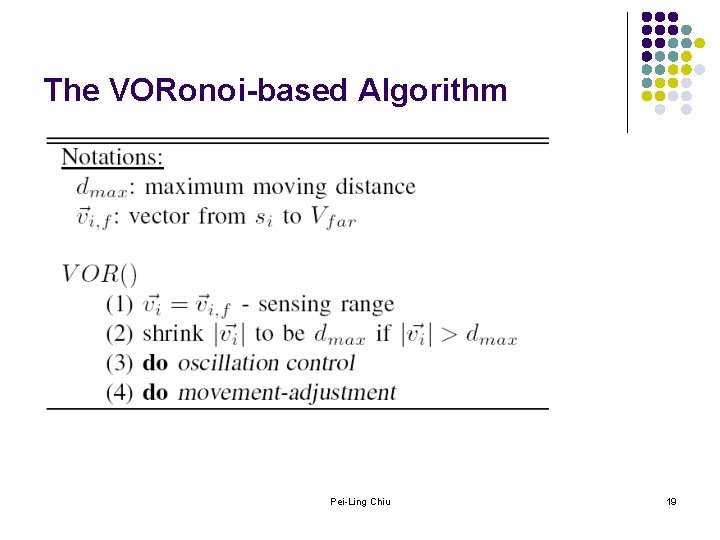
The VORonoi-based Algorithm l l VOR algorithm pulls sensors to their local maximum coverage holes. In VOR, if a sensor detects the existence of coverage holes, it will move toward its farthest Voronoi vertex (denoted as Vfar). Fig. 5 shows VOR works. Point A is the farthest Voronoi vertex of si and d(A, si) is longer than the sensing range. Sensor si moves along line si. A to Point B, where d(A, B) is equal to the sensing range. Pei-Ling Chiu 16
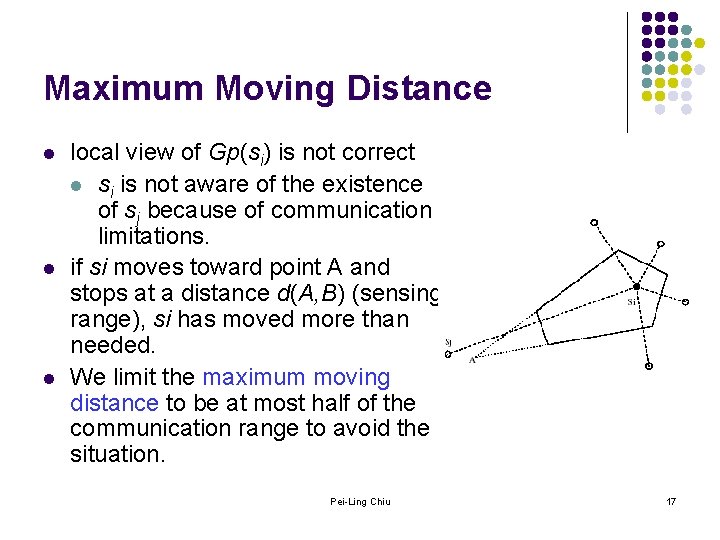
Maximum Moving Distance l local view of Gp(si) is not correct l si is not aware of the existence of sj because of communication limitations. if si moves toward point A and stops at a distance d(A, B) (sensing range), si has moved more than needed. We limit the maximum moving distance to be at most half of the communication range to avoid the situation. Pei-Ling Chiu 17
Oscillation Control l l Moving oscillations may occur if new holes are generated due to sensor’s leaving. To deal with this problem, we add oscillation control which does not allow sensors to move backward immediately. l l Each time a sensor wants to move, it first checks whether its moving direction is opposite to that in the previous round. If yes, it stops for one round. Pei-Ling Chiu 18
The VORonoi-based Algorithm Pei-Ling Chiu 19
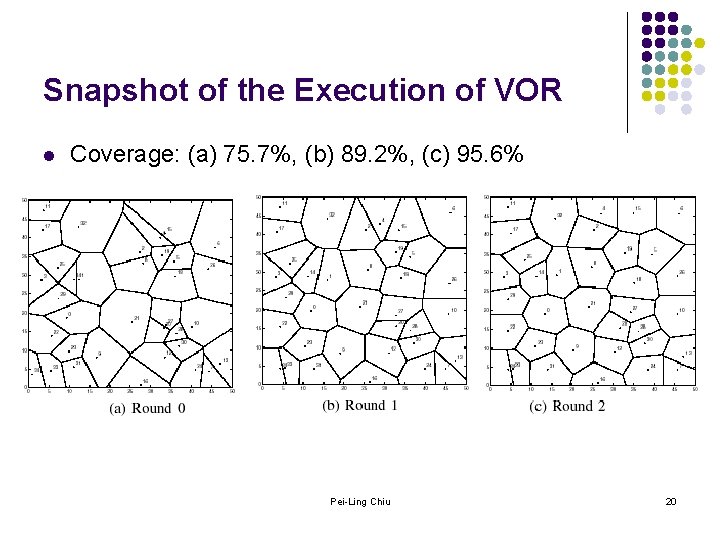
Snapshot of the Execution of VOR l Coverage: (a) 75. 7%, (b) 89. 2%, (c) 95. 6% Pei-Ling Chiu 20
The Minimax Algorithm l l Minimax does not move as far as VOR to avoid the situation that the vertex which was originally close becomes a new farthest vertex. Minimax chooses the target location as the point inside the Voronoi polygon whose distance to the farthest Voronoi vertex (Vfar) is minimized. We call this point the Minimax point, denoted as Om. Minimax can reduce the variance of the distances to the Voronoi Vertices, resulting in a more regular shaped Voronoi polygon, which better utilizes sensor’s sensing circle. Pei-Ling Chiu 21
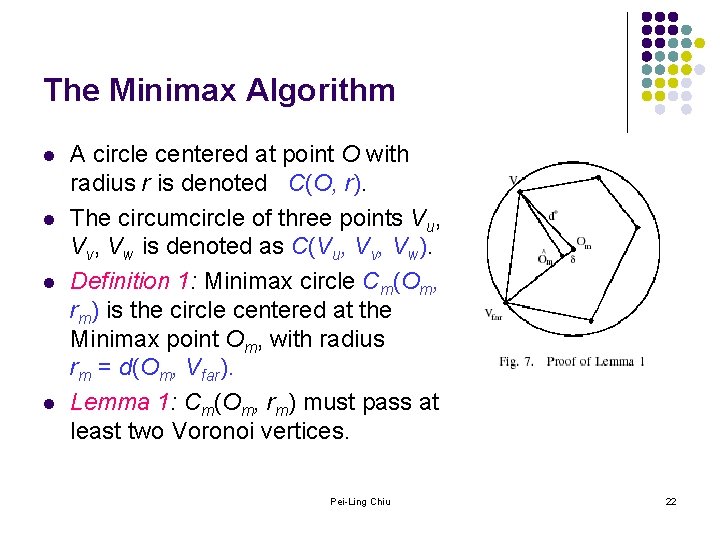
The Minimax Algorithm l l A circle centered at point O with radius r is denoted C(O, r). The circumcircle of three points Vu, Vv, Vw is denoted as C(Vu, Vv, Vw). Definition 1: Minimax circle Cm(Om, rm) is the circle centered at the Minimax point Om, with radius rm = d(Om, Vfar). Lemma 1: Cm(Om, rm) must pass at least two Voronoi vertices. Pei-Ling Chiu 22
The Minimax Algorithm l l Definition 2: The circumcircle of two point Vu and Vw (C(Vu, Vw)) is defined as the circle whose center is the midpoint of Vu and Vw and whose radius is d(Vu, Vw)/2. Lemma 2: If Cm(Om, rm) passes exactly two Voronoi vertices: Vu and Vw, then Cm(Om, rm) = C(Vu, Vw). In other words, if the Minimax circle passes only two Voronoi vertices, it must be centered at the midpoint of these two vertices. Pei-Ling Chiu 23
The Minimax Algorithm l l If the Minimax circle passes more than two Voronoi vertices, it is the circumcircle of these vertices. To find the Minimax point, l l to find all the circumcircles of any two and any three Voronoi vertices Among those circles, the one with the minimum radius covering all the vertices is the Minimax circle. The center of this circle is the Minimax point. Theorem 1: Let Γ = {C(Vu, Vv) | C(Vu, Vv) covers all vertices in Vp, and Vu, Vv Vp} { C(Vu, Vv, Vw) | C(Vu, Vv, Vw) covers all vertices in Vp, and Vu, Vv, Vw Vp}, then Cm(Om, rm) Γ and C(O, r) Γ, r rm. Pei-Ling Chiu 24
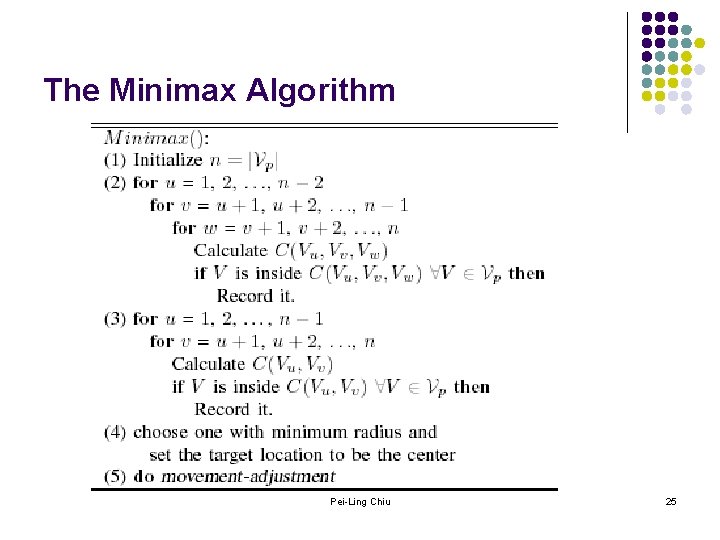
The Minimax Algorithm Pei-Ling Chiu 25
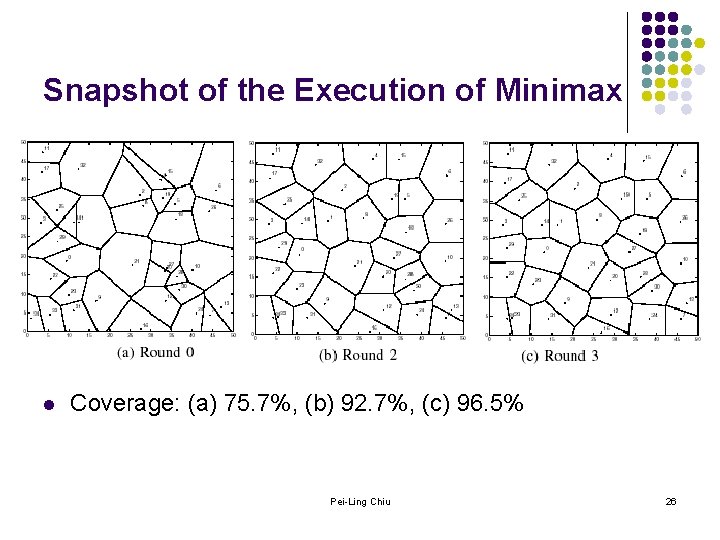
Snapshot of the Execution of Minimax l Coverage: (a) 75. 7%, (b) 92. 7%, (c) 96. 5% Pei-Ling Chiu 26
Termination l l The local coverage increase of one sensor does not affect the local coverage of another sensor. Thus, sensors will stop naturally when the best coverage is obtained. In some applications, the coverage requirement is not that high. To terminate the deployment procedure earlier, we use a threshold , defined as the minimum increase in coverage below which a sensor will not move. With a larger , the deployment will finish earlier. Pei-Ling Chiu 27
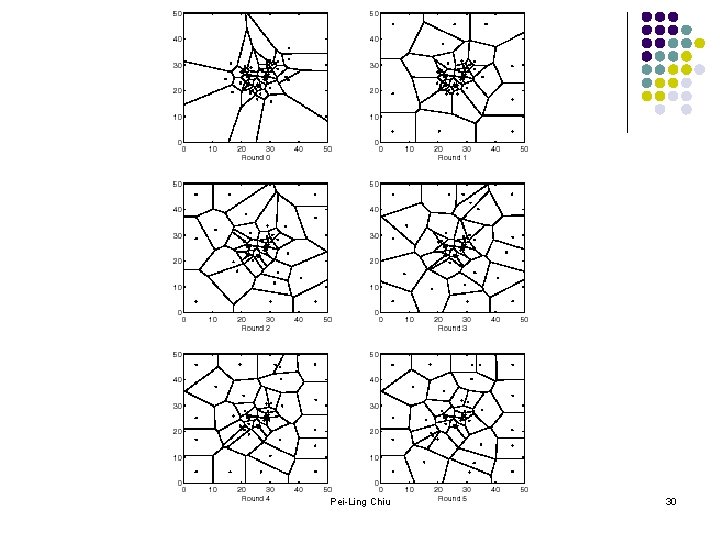
Optimizations l l l In some cases, the initial deployment of sensors may form clusters, as shown in Fig. 10. In this case, sensors located inside the clusters can not move for several rounds, since their Voronoi polygons are well covered initially. This problem prolongs the deployment time. To reduce the deployment time in this situation, we propose an optimization which detects whether too many sensors are clustered in a small area. The algorithm “explodes” the cluster to scatter the sensors apart, if necessary. Pei-Ling Chiu 28
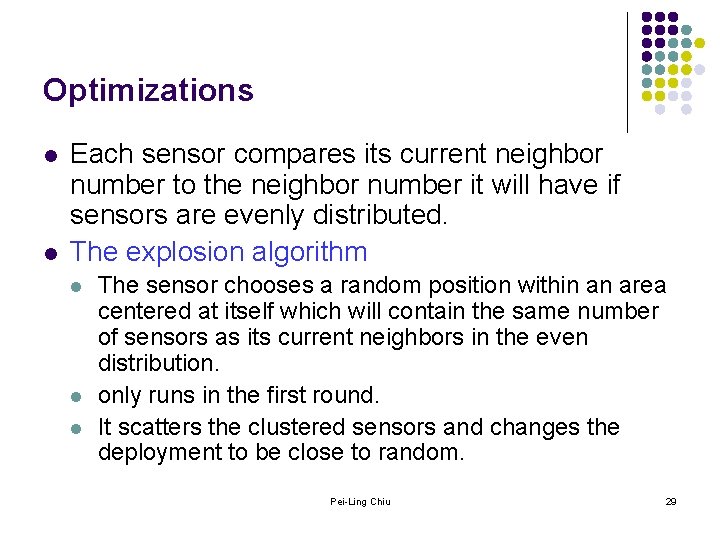
Optimizations l l Each sensor compares its current neighbor number to the neighbor number it will have if sensors are evenly distributed. The explosion algorithm l l l The sensor chooses a random position within an area centered at itself which will contain the same number of sensors as its current neighbors in the even distribution. only runs in the first round. It scatters the clustered sensors and changes the deployment to be close to random. Pei-Ling Chiu 29
Pei-Ling Chiu 30
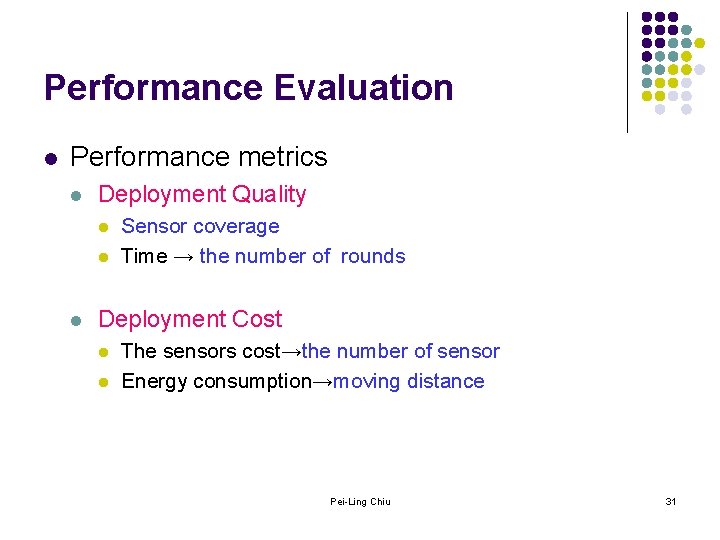
Performance Evaluation l Performance metrics l Deployment Quality l l l Sensor coverage Time → the number of rounds Deployment Cost l l The sensors cost→the number of sensor Energy consumption→moving distance Pei-Ling Chiu 31
Parameters l l l Fields size: 50 m, 150 m Sensor density: 30, 35, 40, 45 sensors/50 mx 50 m Initial deployments: l l random distribution, normal distribution Sensor communication range: 10 m~28 m, (20 m) Sensor sensing range: 10 m =0 Pei-Ling Chiu 32
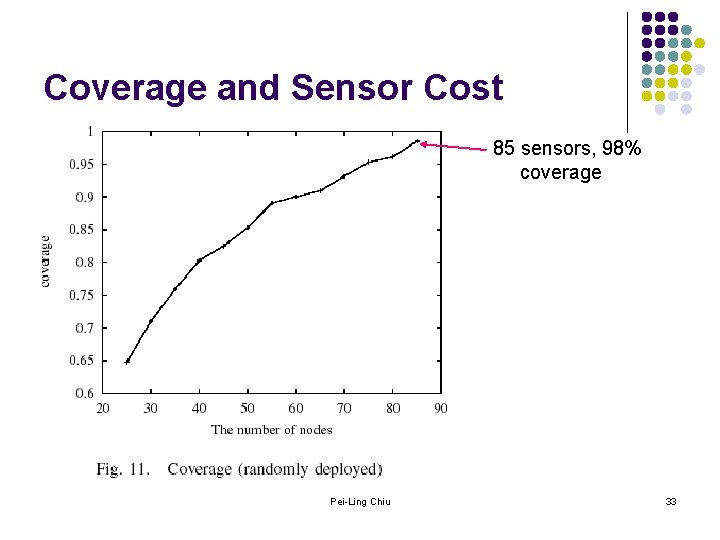
Coverage and Sensor Cost 85 sensors, 98% coverage Pei-Ling Chiu 33
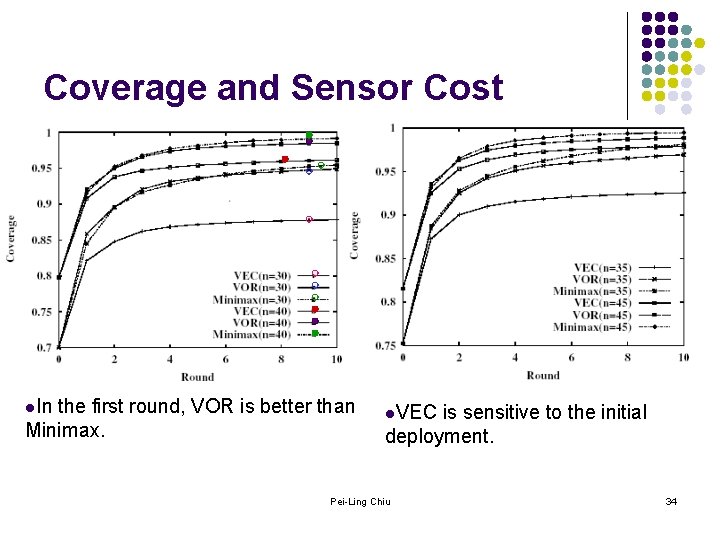
Coverage and Sensor Cost l. In the first round, VOR is better than Minimax. l. VEC is sensitive to the initial deployment. Pei-Ling Chiu 34
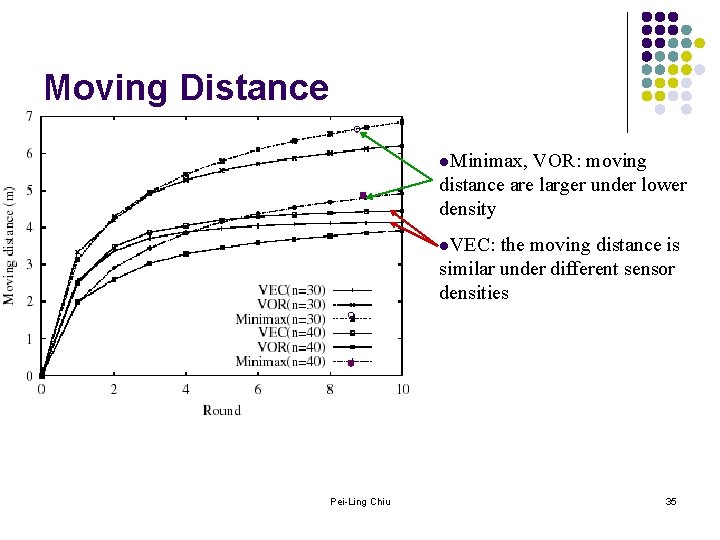
Moving Distance l. Minimax, VOR: moving distance are larger under lower density l. VEC: the moving distance is similar under different sensor densities Pei-Ling Chiu 35
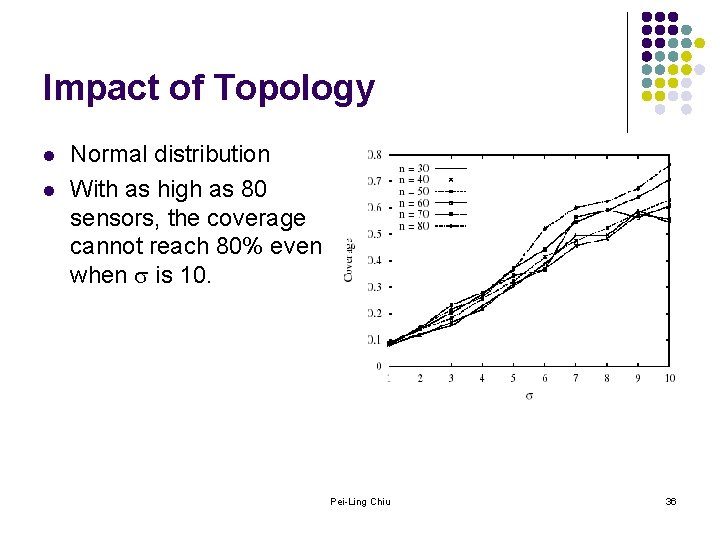
Impact of Topology l l Normal distribution With as high as 80 sensors, the coverage cannot reach 80% even when is 10. Pei-Ling Chiu 36
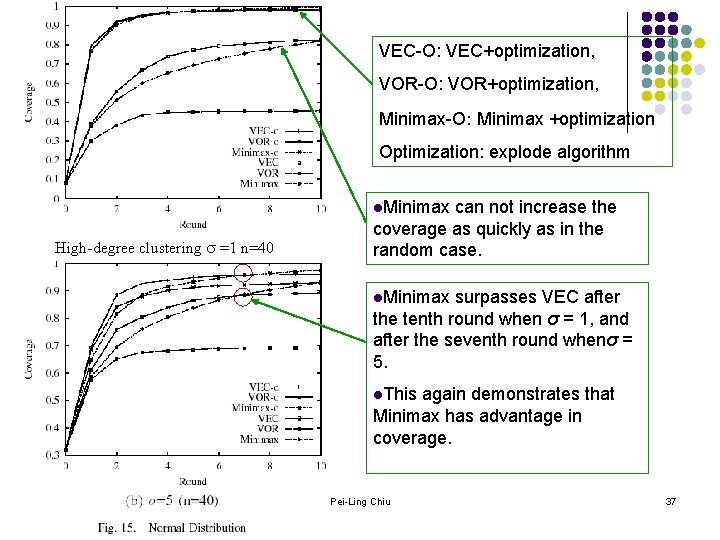
VEC-O: VEC+optimization, VOR-O: VOR+optimization, Minimax-O: Minimax +optimization Optimization: explode algorithm l. Minimax High-degree clustering =1 n=40 can not increase the coverage as quickly as in the random case. l. Minimax surpasses VEC after the tenth round when σ = 1, and after the seventh round whenσ = 5. l. This again demonstrates that Minimax has advantage in coverage. Pei-Ling Chiu 37
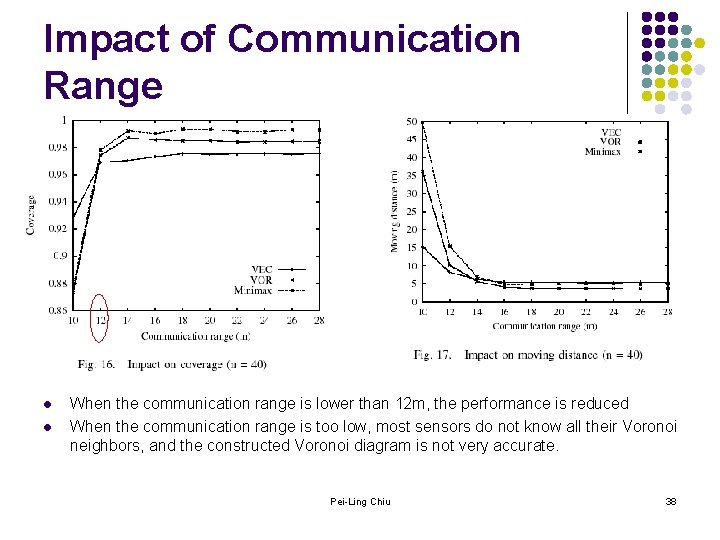
Impact of Communication Range l l When the communication range is lower than 12 m, the performance is reduced When the communication range is too low, most sensors do not know all their Voronoi neighbors, and the constructed Voronoi diagram is not very accurate. Pei-Ling Chiu 38
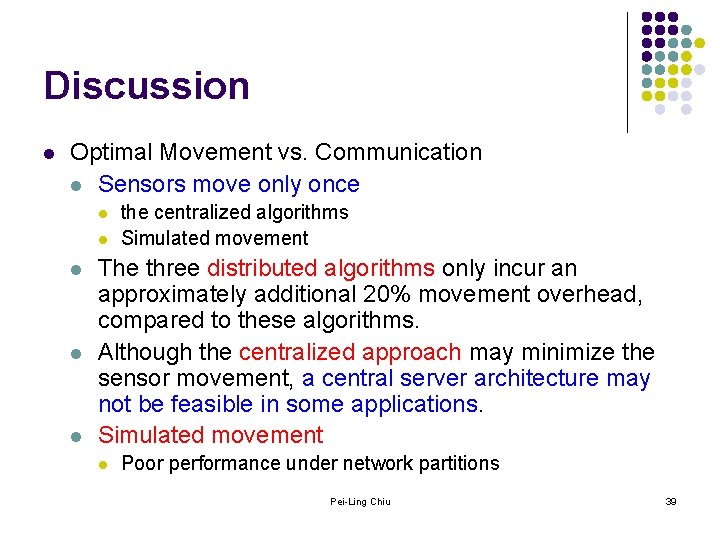
Discussion l Optimal Movement vs. Communication l Sensors move only once l l l the centralized algorithms Simulated movement The three distributed algorithms only incur an approximately additional 20% movement overhead, compared to these algorithms. Although the centralized approach may minimize the sensor movement, a central server architecture may not be feasible in some applications. Simulated movement l Poor performance under network partitions Pei-Ling Chiu 39
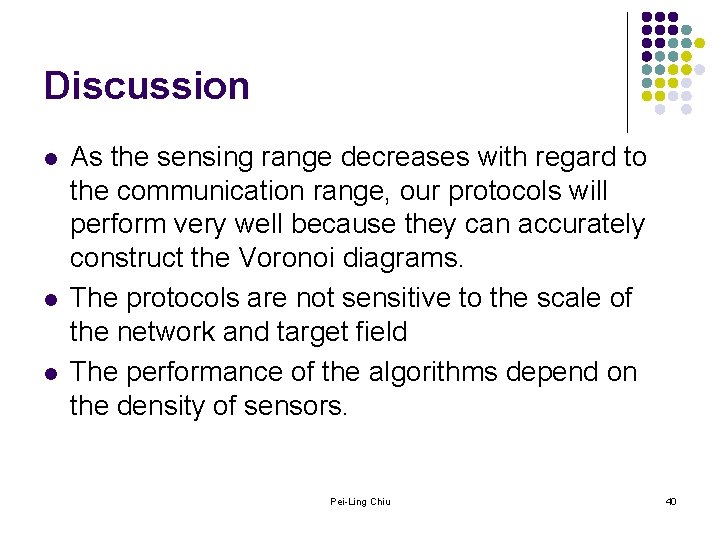
Discussion l l l As the sensing range decreases with regard to the communication range, our protocols will perform very well because they can accurately construct the Voronoi diagrams. The protocols are not sensitive to the scale of the network and target field The performance of the algorithms depend on the density of sensors. Pei-Ling Chiu 40
Outline l l Research Framework Paper: ”Movement-Assisted Sensor Deployment” Related Work Discussion Pei-Ling Chiu 41
Constrained Coverage for Mobile Sensor Networks Sameera Poduri and Gaurav S. Sukhatme In IEEE International Conference on Robotics and Automation, May 2004 Department of Computer Science University of Southern California, Los Angeles, California, USA Pei-Ling Chiu
Introduction l l In this paper the authors consider constrained coverage for a mobile sensor network. The constraint is node degree - the number of neighbors of each node in the network. More precisely, the authors require each node to have a minimum degree K, where K is parameter of the deployment algorithm. Motivation: l l Reliability: Sometimes a high degree is required for the sake of redundancy. Connectivity: Global network connectivity is strongly dependent on node degree. Pei-Ling Chiu 43
Introduction l l l A global map of the environment is either unavailable or of little use because the environment is not static. They also assume that no global positioning system (GPS) is available. Approach: l l Based on virtual potential fields Force laws: l l Repulsive force: to maximum coverage Attractive force: to impose the constraint of K-degree Pei-Ling Chiu 44
Problem Formulation l l l Problem: Given N mobile nodes with isotropic radial sensors of range Rs and isotropic radio communication of range Rc, how should they deploy themselves so that the resulting configuration maximizes the net sensor coverage of the network with the constraint that each node has at least K neighbors? Neighbors: if the Euclidean distance between two nodes is less than or equal to the communication range Rc. Assumptions: l l l 1) The nodes are capable of omni-directional motion, 2) Each node can sense the exact relative range and bearing of its neighbors, 3) It follows a binary detection model. Pei-Ling Chiu 45
Problem Formulation l The deployment algorithm: l l l Distributed and scalable Not require a prior map or localization of nodes Performance metrics: l 1) the normalized per-node coverage. Coverage =(Net Area Covered by the Network) / N Rs 2 l l 2) the percentage of nodes in the network that have at least K neighbors. 3) the average degree of the network. Pei-Ling Chiu 46
The Deployment Algorithm Pei-Ling Chiu 47
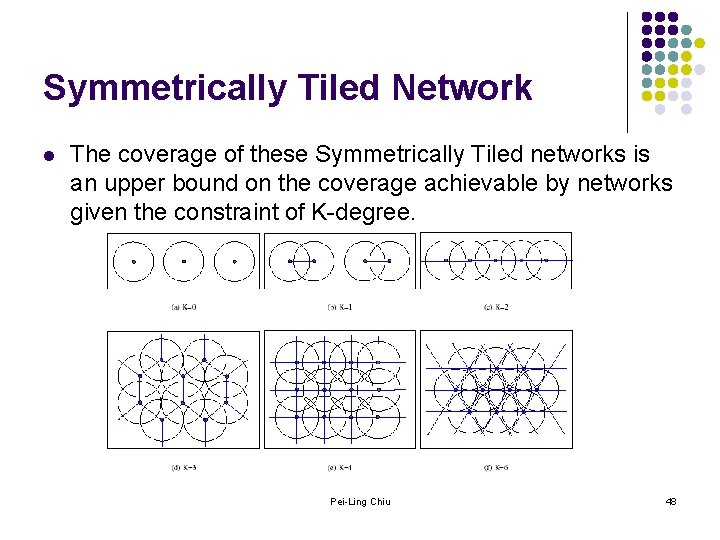
Symmetrically Tiled Network l The coverage of these Symmetrically Tiled networks is an upper bound on the coverage achievable by networks given the constraint of K-degree. Pei-Ling Chiu 48
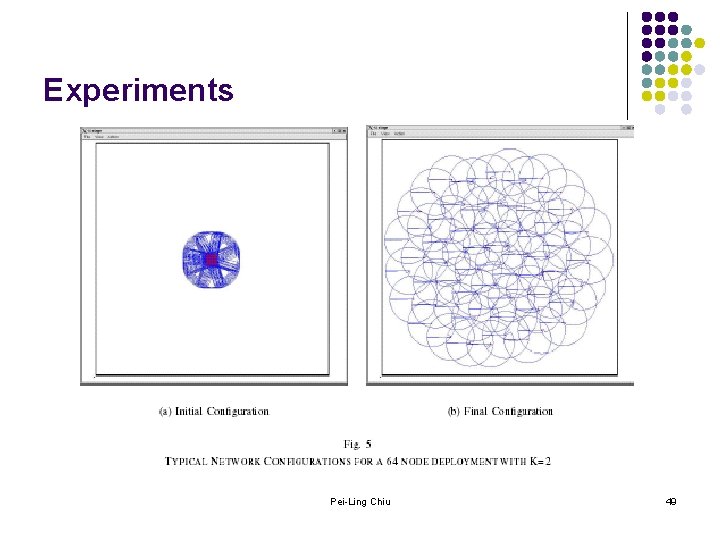
Experiments Pei-Ling Chiu 49
Event-Based Motion Control 1. Zack Butler and Daniela Rus, “Controlling Mobile Sensors for Monitoring Events with Coverage Constraints”, ICRA '04. 2004 IEEE International Conference on , Volume: 2 , April 26 -May 1, 2004. 2. Zack Butler and Daniela Rus, “Event-Based Motion Control for Mobile-Sensor Networks, ” IEEE Pervasive Computing, October-December 2003. Pei-Ling Chiu
Introduction l Scenario: l l l If the specific area of interest (within a larger area) is unknown during deployment. For example, if a network is deployed to monitor the migration of a herd of animals, the herd’s exact path through an area will be unknown beforehand. Event-based l l l The sensors could converge on the event to get the maximum amount of data. The sensors could move such that they also maintain complete coverage of their environment while reacting to the events in that environment. In this way, at least one sensor still detects any events that occur in isolation, while several sensors more carefully observe dense clusters of events. Pei-Ling Chiu 51
Introduction l l The authors have developed distributed algorithms for mobile-sensor networks to physically react to changes or events in their environment or in the network itself. Assumptions: l l The sensor begin in a uniform distribution over the environment. The events can be represented discretely in space and time. At least one sensor can sense each event and broadcast the event location to the other sensors. Every sensor learns about each event location. Pei-Ling Chiu 52
History-Free Approach l l The approach uses only the current position of the sensor and the position of an event to determine the motion of the sensor. A sensor will move toward each event by the amount given by f , f(d)= d e- d l l d: the distance between a sensor and an event. f( )=0, 0 f(d) d, d, f(d 1)-f (d 2) <(d 1 -d 2), d 1>d 2 Pei-Ling Chiu 53
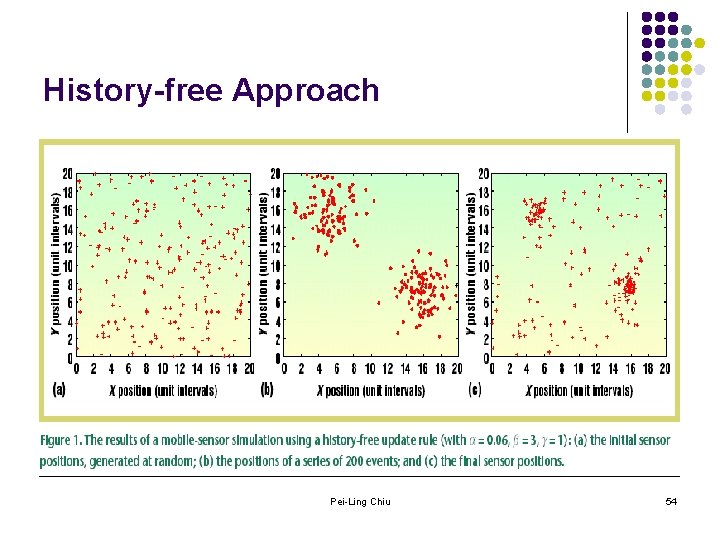
History-free Approach Pei-Ling Chiu 54
History-based Approach l l The approach uses a small of history and more carefully analyzes the distribution of events. It uses a coarse histogram of the events as a basis for determining its correct position. Each sensor computes the cumulative distribution (CDF) of the scaled event distribution. The sensor then finds the point in the scaled CDF corresponding to its initial position, and moves to that location. Pei-Ling Chiu 55
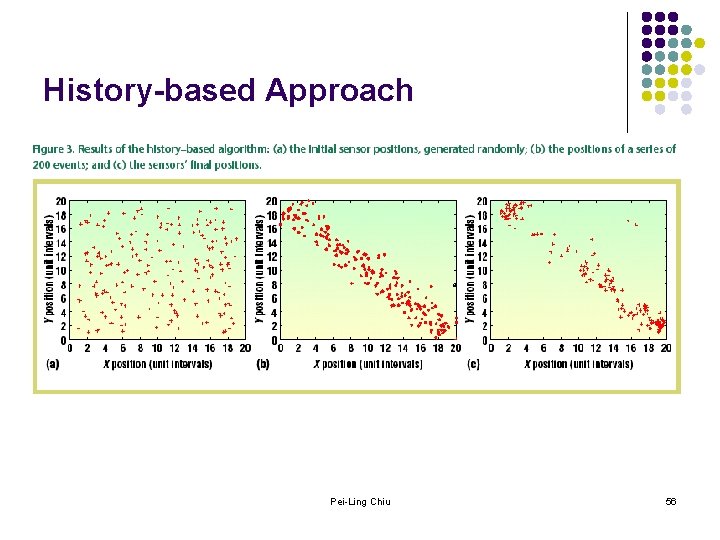
History-based Approach Pei-Ling Chiu 56
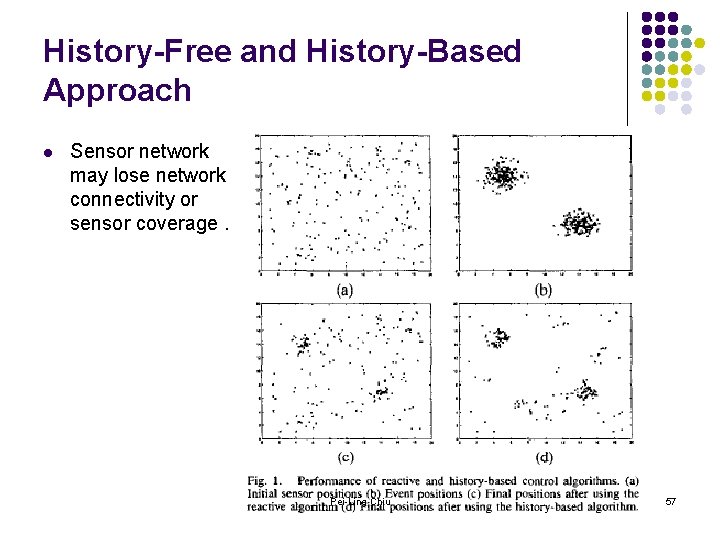
History-Free and History-Based Approach l Sensor network may lose network connectivity or sensor coverage. Pei-Ling Chiu 57
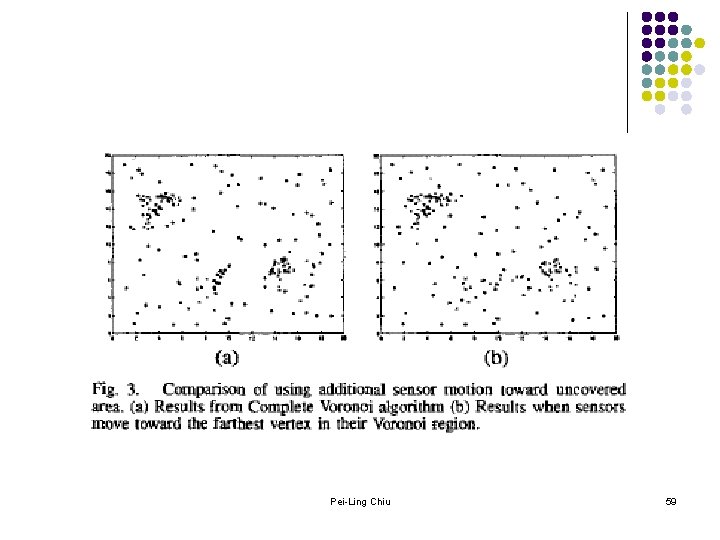
Maintaining Coverage l l The Authors instead have the sensors follow the event distribution exactly until required for coverage, so that they can achieve a good approximation to the event distribution in high density area and good coverage in low density area. Approaches: l l Complete Voronoi Algorithm Local Voronoi Algorithm Pei-Ling Chiu 58
Pei-Ling Chiu 59
Outline l l Research Framework Paper: ”Movement-Assisted Sensor Deployment” Related Work Discussion Pei-Ling Chiu 60
- Slides: 60