Mobile Security Guide Matt Scofield Eric Samson Cong
Mobile Security Guide Matt Scofield, Eric Samson, Cong Le
Overview I. Introduction II. Background III. Related Works I IV. Related Works II V. Survey VI. Results VII. Conclusion
Introduction Goal: Create a simple Best Practice Guidelines for Mobile Device Security Methodology: Two Pronged Approach a. Research topics related to mobile security and existing and conduct a survey to obtain user behavior patterns. b. Use gathered information to create a simpler and easier to follow guideline.
Background There are currently 1. 2 billion mobile web users according to mobithinking. com http: //mobithinking. com/mobile-marketing-tools/latest-mobile-stats The threat of malicious attacks to mobile devices is likely to increase according to a paper on malicious software in mobile devices. http: //lyle. smu. edu/~tchen/papers/mobile-malware. pd Existing guidelines are often overly specific, highly specialized, or obscure.
Research I Guidelines examples https: //wiki. internet 2. edu/confluence/display/itsg 2/Mobile+Device+Security http: //www. cmu. edu/iso/governance/guidelines/mobile-device. html http: //www. stanford. edu/group/security/securecomputing/mobile_devices. html Common suggestions • Enable Password • Keep Software Updated • Back up data • Install anti-virus

Research II MMS and bluetooth • • • MMS vulnerabilities bypassed through use of CAPTCHAs Blue. Tooth vulnerabilities bypassed through a number of means Possibly eliminated entirely at the Telecom level Cloud based antivirus • Advantages: Power consumption, Computing power, Larger database Disadvantages: Requires internet connection, Reactive protection Manufacturer Enabled Security • • Radio control parameters are stored during the manufacturing process Secure booting
Survey Target Audience: General Mobile Device users Total Number of Participants: 38 Objective: Obtain data on mobile device usage patterns Distribution Model: Online Survey (Google Docs - Forms)
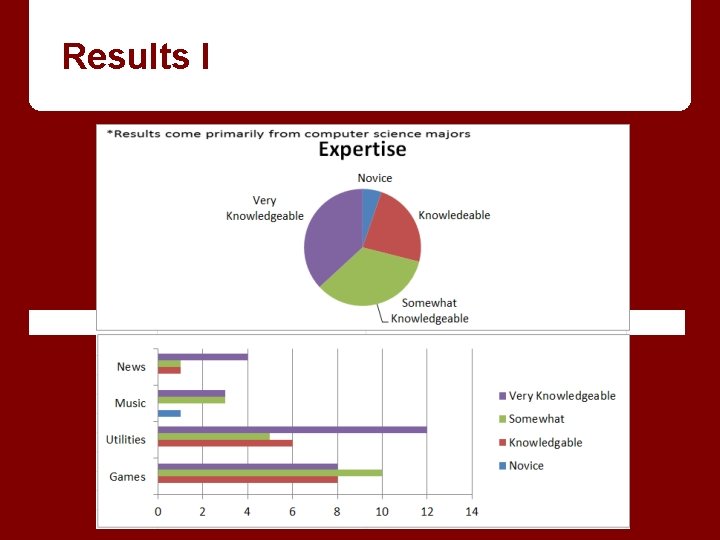
Results I
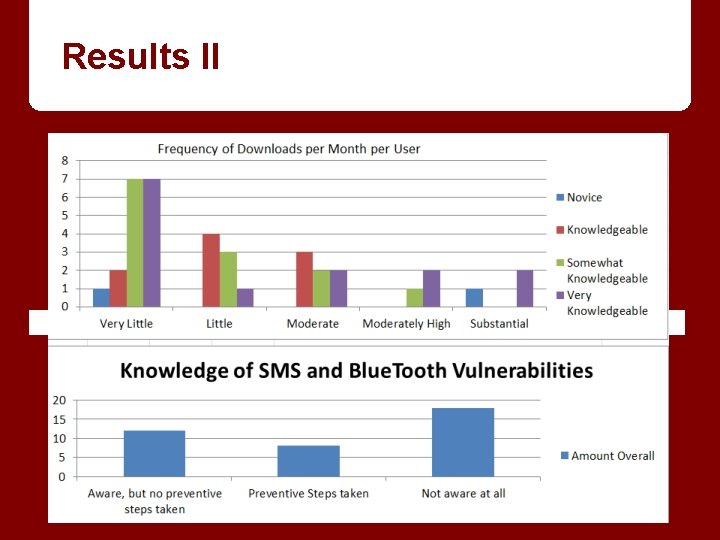
Results II
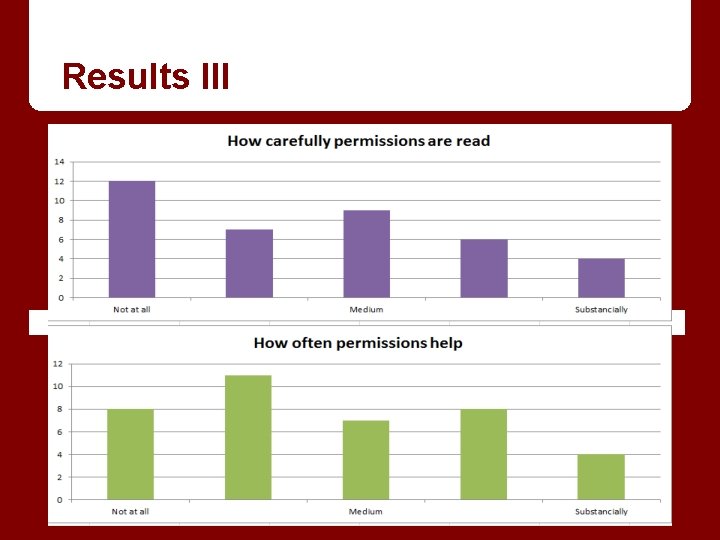
Results III
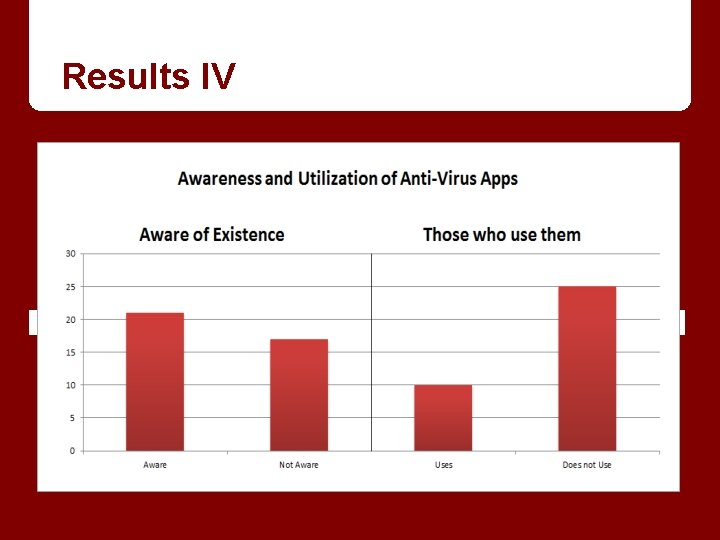
Results IV
Conclusion / Proposed Guideline § Enable password lock § Keep software up-to-date § Read reviews and comments of applications § Install anti-virus software § Back up data regularly
Extended Guideline § Read permission requests before accepting § Enable remote lock and wipe § Keep up to date on information about security § Do not join unknown access points § Only download from trusted sources § Do not leave device unattended
Comments and Questions ? All your questions are belong to us!
- Slides: 14