Mobile Protection for Trustmark Insurance Protecting the Confidentiality
Mobile Protection for Trustmark Insurance Protecting the Confidentiality and Integrity of Corporate and Client Data When in the Hands of a Mobile Workforce
Topics 1 - Gerard • Categorization of Mobile Security 2 - Andy • Justifying Costs to Management and Problem at Hand 3 - Gwen • Phase 1 Product Selection
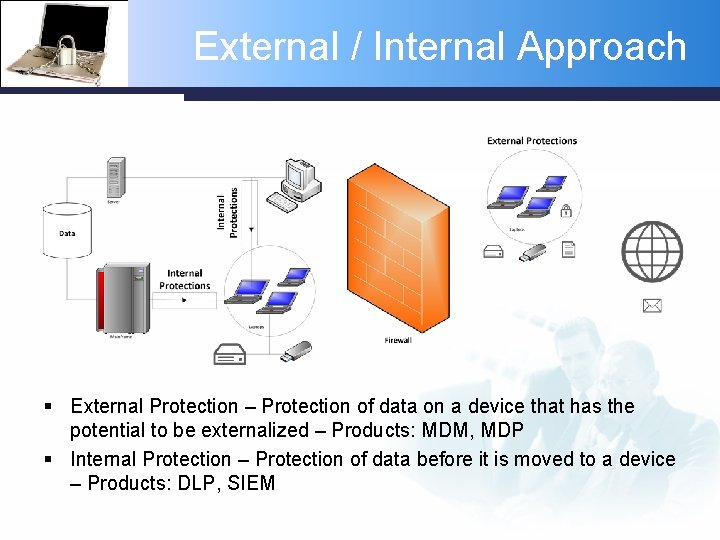
External / Internal Approach § External Protection – Protection of data on a device that has the potential to be externalized – Products: MDM, MDP § Internal Protection – Protection of data before it is moved to a device – Products: DLP, SIEM
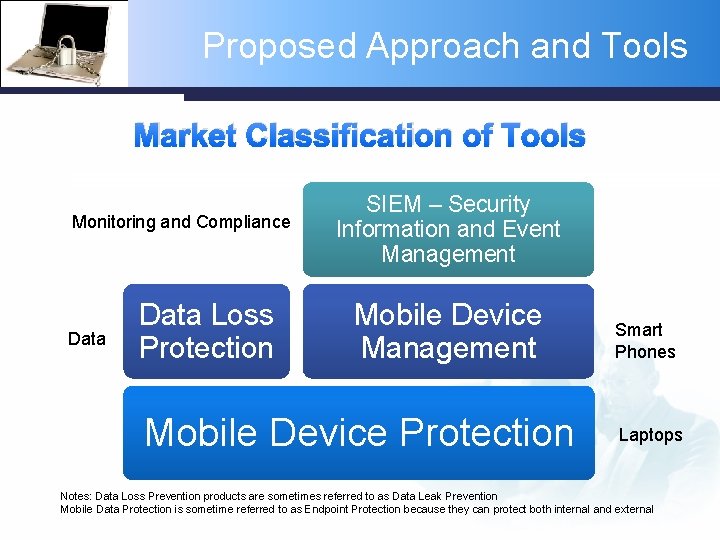
Proposed Approach and Tools Market Classification of Tools Monitoring and Compliance Data Loss Protection SIEM – Security Information and Event Management Mobile Device Protection Smart Phones Laptops Notes: Data Loss Prevention products are sometimes referred to as Data Leak Prevention Mobile Data Protection is sometime referred to as Endpoint Protection because they can protect both internal and external
Mobile Data Protection § Mobile data protection (MDP) is a category of products for securing data on movable storage systems - laptops, smartphones, and removable media. Provides common protection policies across multiple platforms Provides auditable proof that data is protected. Should entail minimal support costs Should provide FIPS-140 certified encryption* *Federal Information Processing Standards, issued by NSIT
Mobile Device Management § Mobile Device Management (MDM) is a category of applications for managing smartphones. Includes the following functionality: Software Distribution — The ability to manage and support mobile application including deploy, install, update, delete or block. Policy Management — Development, control and operations of enterprise mobile policy. Inventory Management — Beyond basic inventory management, this includes provisioning and support. Security Management — The enforcement of standard device security, authentication and encryption. Service Management — Rating of telecom services.
Data Loss Protection § Data loss protection (DLP) is a category of tools that protects data as it leaves the network (sometimes referred to as “Content-Aware” DLP). Includes the following functionality: Enables the dynamic application of policy based on the classification of content Can be applied to data in rest (storage), data in use (during an operation), and data in transit (across a network) Can dynamically apply policies , such as log, report, classify, relocate, tag , or encrypt protections. Helps organizations develop, educate and enforce better business practices concerning the handling and transmission of sensitive data. Designed to: § Protect customer information, HIPPA privacy, and intellectual property § Stop data leaks to media § Provide device and port control when protected data is passed to laptops, USB drives, CDs, etc. § Provide endpoint auditing and discovery – where’s my data?
SIEM – Security Information and Event Management § Security Information and Event Management (SIEM) is a category of tools that aid in regulatory compliance and threat management. Includes the following functionality: Supports the real-time collection and analysis of events from host systems, security devices and network devices combined with contextual information for users, assets and data Provides long-term event and context data storage and analytics Not limited to mobile data
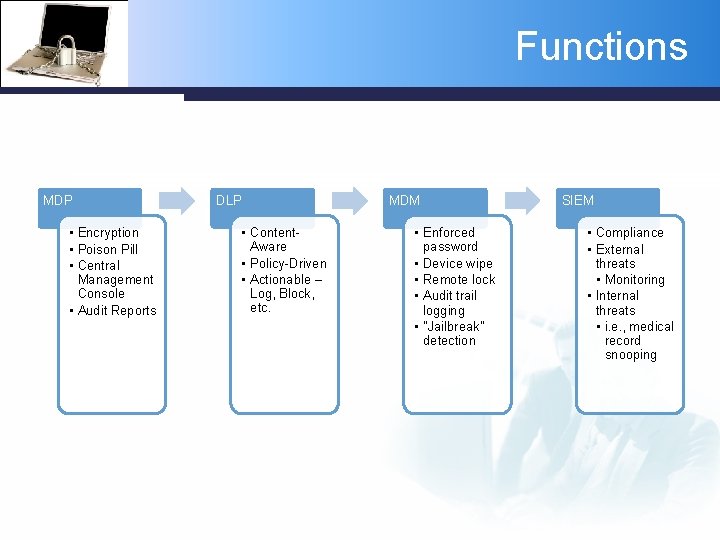
Functions MDP • Encryption • Poison Pill • Central Management Console • Audit Reports DLP • Content. Aware • Policy-Driven • Actionable – Log, Block, etc. MDM • Enforced password • Device wipe • Remote lock • Audit trail logging • "Jailbreak" detection SIEM • Compliance • External threats • Monitoring • Internal threats • i. e. , medical record snooping
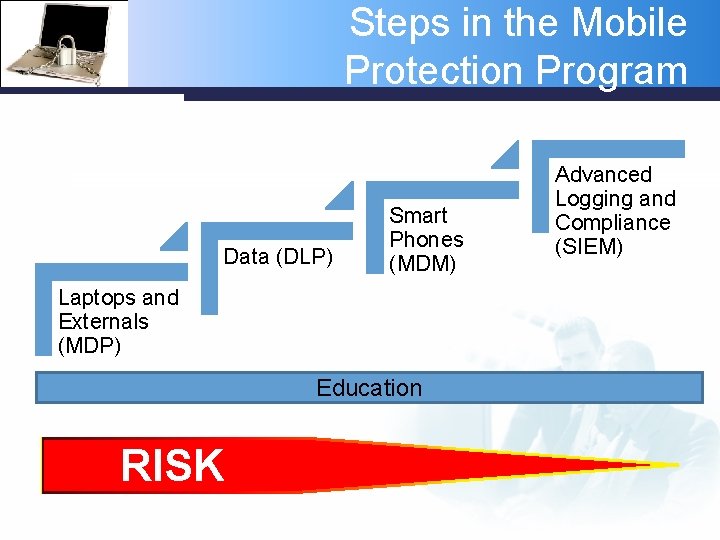
Steps in the Mobile Protection Program Data (DLP) Smart Phones (MDM) Laptops and Externals (MDP) Education RISK Advanced Logging and Compliance (SIEM)
Justifying Costs to Management Explaining to senior management the costs of doing nothing and making a case for mobile protection
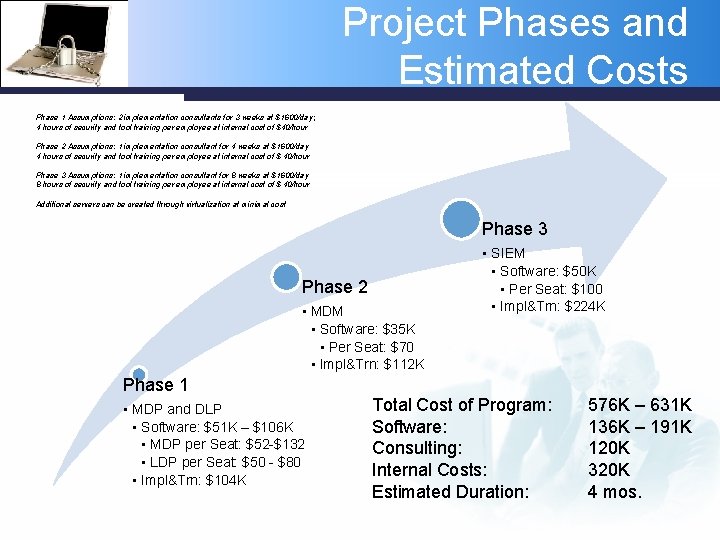
Project Phases and Estimated Costs Phase 1 Assumptions: 2 implementation consultants for 3 weeks at $1600/day; 4 hours of security and tool training per employee at internal cost of $40/hour Phase 2 Assumptions: 1 implementation consultant for 4 weeks at $1600/day 4 hours of security and tool training per employee at internal cost of $ 40/hour Phase 3 Assumptions: 1 implementation consultant for 8 weeks at $1600/day 8 hours of security and tool training per employee at internal cost of $ 40/hour Additional servers can be created through virtualization at minimal cost Phase 3 Phase 2 • MDM • Software: $35 K • Per Seat: $70 • Impl&Trn: $112 K • SIEM • Software: $50 K • Per Seat: $100 • Impl&Trn: $224 K Phase 1 • MDP and DLP • Software: $51 K – $106 K • MDP per Seat: $52 -$132 • LDP per Seat: $50 - $80 • Impl&Trn: $104 K Total Cost of Program: Software: Consulting: Internal Costs: Estimated Duration: 576 K – 631 K 136 K – 191 K 120 K 320 K 4 mos.
Justifying Costs to Management § Leakage of personally identifiable information (PII) and personal health information (PHI), direct costs: The average cost per record associated with a leak to make affected parties whole Fees for legal representation Engaging a PR firm to minimize damage and restore reputation to the extent possible Consumer credit monitoring for all customers (not necessarily only those affected by the leak) Up to five years of system and process audits conducted by an independent third party Forrester estimates $218 per leaked record, so a leak of 100, 000 records would cost $21. 8 M Source: Trends: Calculating the Cost of a Security Breach. Forrester Research, Inc. April 10, 2007.
Justifying Costs to Management § Intellectual property, direct costs: Fees for legal recourse to address who leaked the data and discover if it is being used inappropriately Short-term impact to R&D cost recuperation Long-term impact to profitability/revenue projections System and process audits to identify and correct the source of the leak Forrester estimates the average leak results in $1. 5 M loss Most IP data losses go unreported because there are no public disclosure laws that apply to intellectual property and the impact on valuation from a publicized loss would likely be tremendous.
Justifying Costs to Management § § § § Total economic impact in one lost laptop: $49, 256 (incl. replacement cost, detection, forensics, data breach, lost intellectual property costs, lost productivity and legal, consulting and regulatory expenses) Occurrence of data breach represents 80 % of cost; intellectual property loss is 59% of cost If the company discovers the loss in one day, it is $8, 950. After one week, it is $115, 849 Average cost for senior management is $28, 449. For a manager or director it is about $61, 000 Productivity loss is only about 1% of the cost Loss if laptop is encrypted: $29, 256 (> $20, 000 less) Loss varies by industry – financial services: $112, 853, healthcare: $67, 873, manufacturing: $2, 184 Loss of intellectual property for healthcare is quite high - $17, 999 Source: The Cost of a Lost Laptop, Ponemon Institute (sponsored by Intel), February 9, 2009
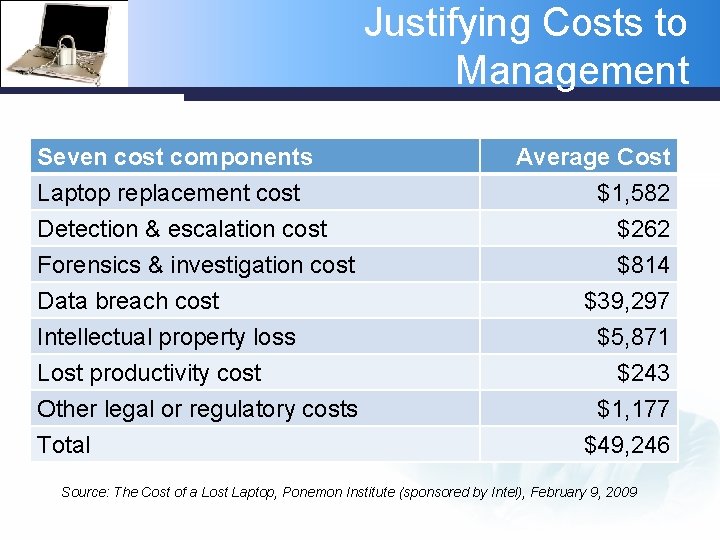
Justifying Costs to Management Seven cost components Laptop replacement cost Detection & escalation cost Forensics & investigation cost Average Cost $1, 582 $262 $814 Data breach cost Intellectual property loss Lost productivity cost Other legal or regulatory costs Total $39, 297 $5, 871 $243 $1, 177 $49, 246 Source: The Cost of a Lost Laptop, Ponemon Institute (sponsored by Intel), February 9, 2009
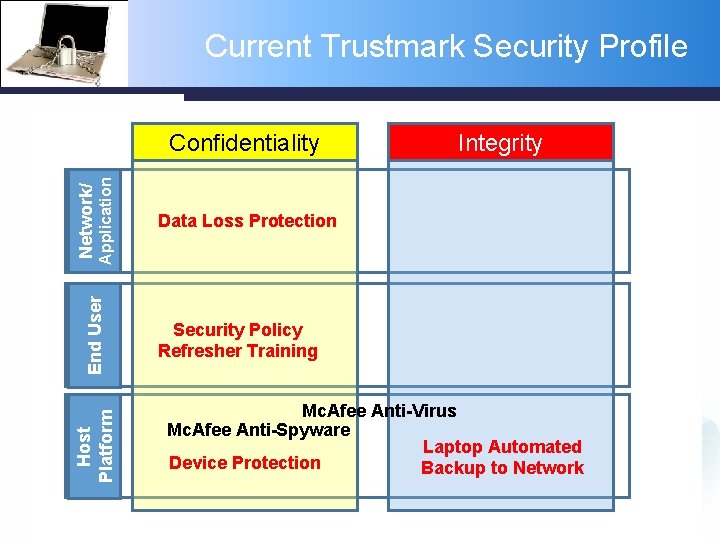
Current Trustmark Security Profile Confidentiality Integrity End User Application Network/ Network Confidentiality Border Router Firewall Proxy Server NAT S-FTP HTTPS Verizon MPLS VLANs Departmental VLANs Authentication Integrity RADIUS PEAP LDAP Server NAC Host Platform Cisco u. RPF Microsoft Certificate Server VPN Data Loss Protection Database Security IPsec PPTP Internet Content Filter WS-Security Global. SCAPE FTP server Open. PGP Edifecs EDI Translator Security Policy Refresher Training Business Application Level Security Role-Based Access Control Single-Factor Authentication Two-Factor Authentication PKIs P-Synch Laptop Biometrics MS WSUS GFI LANGuard Patch Mgmt PPTP Physical Availability Mc. Afee Anti-Virus Mc. Afee Anti-Spyware Laptop Automated Device Protection Backup to Network VMware RAID-5/RAID-6 Encrypted Tape Backups EMC Key Mgmt Appliance Device Protection Door Locks Security Guards Secure Paper Documents Laptop Automated Backup to Network CCTV Hardware Security Token Mantrap Sun. Gard Disaster Recovery Subscription levels? Iron Mountain CO 2 Fire Suppression System ID Badges Enterprise SANs
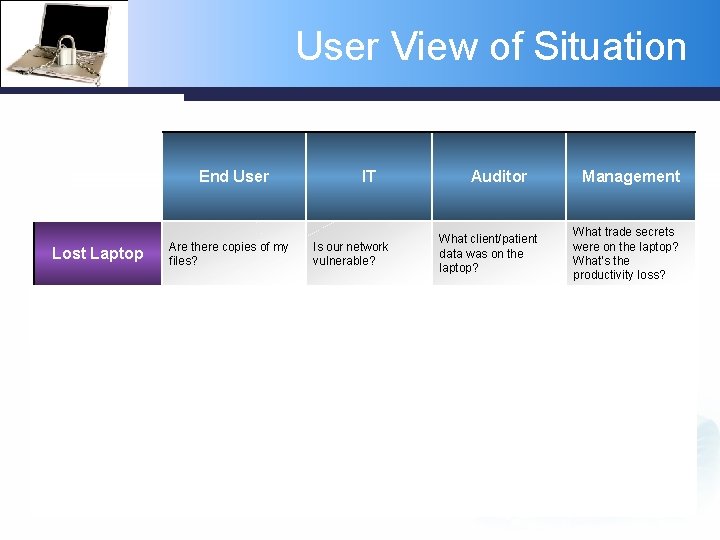
User View of Situation End User IT Management What client/patient data was on the laptop? What trade secrets were on the laptop? What’s the productivity loss? Lost Laptop Are there copies of my files? Sensitive Information I’m told which users I need the data if I’m should have access expected to work off-site. to the application. Personally identifiable data is governed by regulation, such as PCI and HIPPA. Employees can’t be productive if they don’t have what they need to work. Corporate Smartphone The smartphone my company gives shouldn’t be a pain to use. Need to be prepared with users access lists and activity logs for an audit. Need to control costs. If we have audits on laptops for personally identifiable information, shouldn’t other sources of leaks be examined too? If it ain't broke, don’t fix it. Proliferation of Tools Is our network vulnerable? Auditor How should the phones be provisioned? I don’t have time for this. 3 rd I want any tool that makes my job easier. I know that party tools like flash drives can make our network vulnerable.
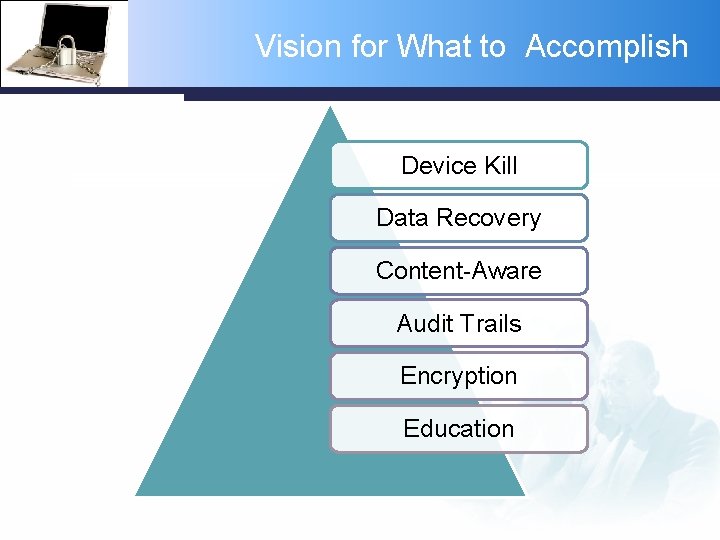
Vision for What to Accomplish Device Kill Data Recovery Content-Aware Audit Trails Encryption Education
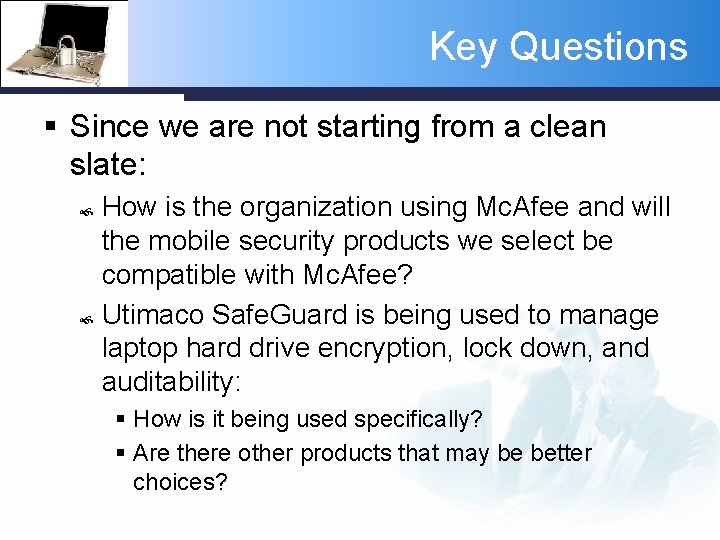
Key Questions § Since we are not starting from a clean slate: How is the organization using Mc. Afee and will the mobile security products we select be compatible with Mc. Afee? Utimaco Safe. Guard is being used to manage laptop hard drive encryption, lock down, and auditability: § How is it being used specifically? § Are there other products that may be better choices?
Phase 1 Product Selection Identifying vendor products, comparing features, developing final selection pros and cons
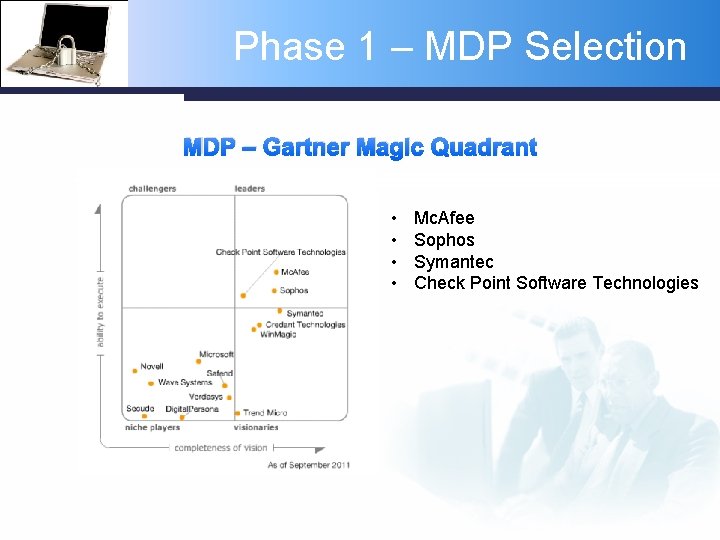
Phase 1 – MDP Selection MDP – Gartner Magic Quadrant • • Mc. Afee Sophos Symantec Check Point Software Technologies
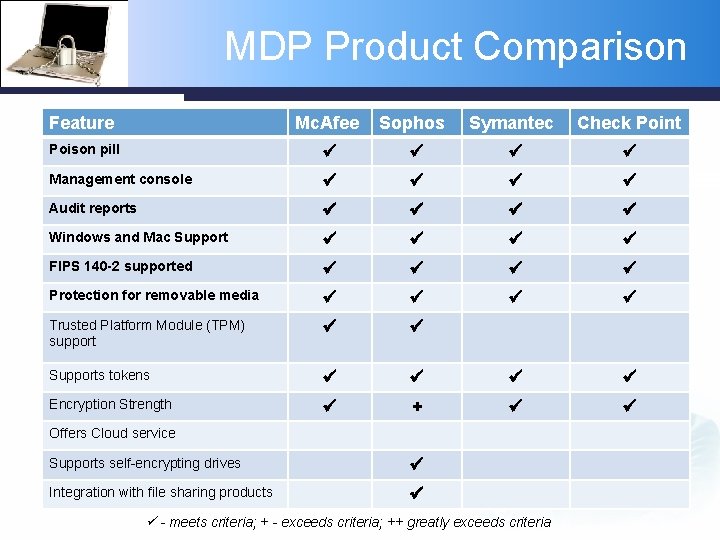
MDP Product Comparison Feature Mc. Afee Sophos Symantec Check Point Poison pill Management console Audit reports Windows and Mac Support FIPS 140 -2 supported Protection for removable media Trusted Platform Module (TPM) support Supports tokens Encryption Strength + Offers Cloud service Supports self-encrypting drives Integration with file sharing products - meets criteria; + - exceeds criteria; ++ greatly exceeds criteria
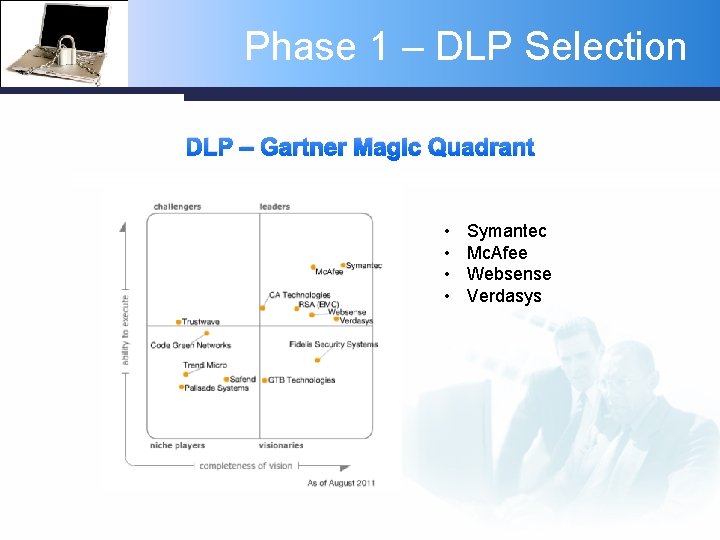
Phase 1 – DLP Selection DLP – Gartner Magic Quadrant • • Symantec Mc. Afee Websense Verdasys
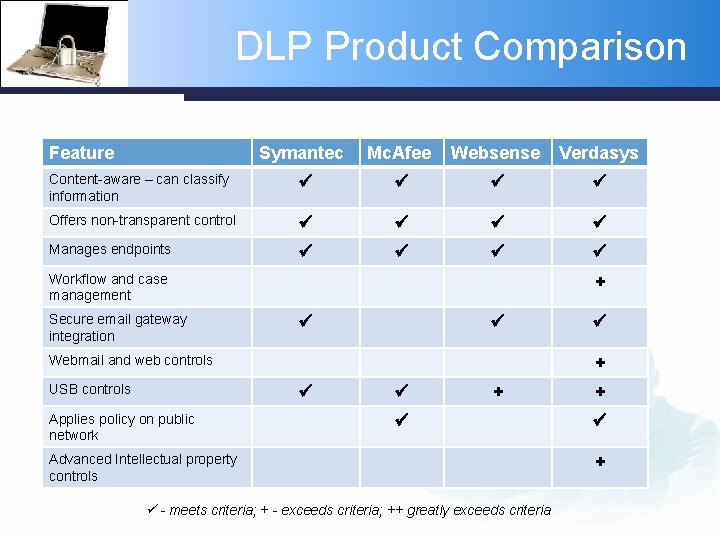
DLP Product Comparison Feature Symantec Mc. Afee Websense Verdasys Content-aware – can classify information Offers non-transparent control Manages endpoints Workflow and case management Secure email gateway integration + Webmail and web controls USB controls + Applies policy on public network + Advanced Intellectual property controls - meets criteria; + - exceeds criteria; ++ greatly exceeds criteria + +
Most Suitable Product - MDP § Winner of MDP Category – Sophos Pros § Content-aware, integrated DLP to help decide when to enforce encryption on information being written to external devices. § Platform support is provided for Windows 2000 through 64 -bit Windows 7, Mac OS X, and Linux. § Embedded system support includes TPM, TCG encrypting drives, Intel v. Pro and UEFI. § Smaller mobile devices to be separately supported under an MDM product include i. Phone, i. Pad, and Android. Cons § North American penetration and brand recognition needs to improve
Most Feature-Rich Product - DLP § Winner of feature-Rich DLP Category – Verdasys Pros § Offers strongest controls for the protection of sensitive information. § Has strong workflow and case management § Simple and easy-to-use process for creating custom dashboards and reports. § Can audit every access to (and control the movement of) files that contain sensitive data (sought after by IP firms and organizations fearing Wiki. Leaks-type data disclosures) § Sensitive files are encrypted when copied to mobile media and devices. Cons § § High-end controls and complexity Priced at premium market Limited RBAC (role-based access control) capabilities Offers just endpoint DLP
Best DLP for Trustmark § Best DLP for Trustmark – Websense Pros § Less costly § Easier to implement § “Fast, effective security leak prevention without a lot of hassle” (Forrester) § Offers both network and endpoint DLP Cons § Less robust solution for complex business processes
Question and Answer
Extra Slides NOT IN PRESENTATION
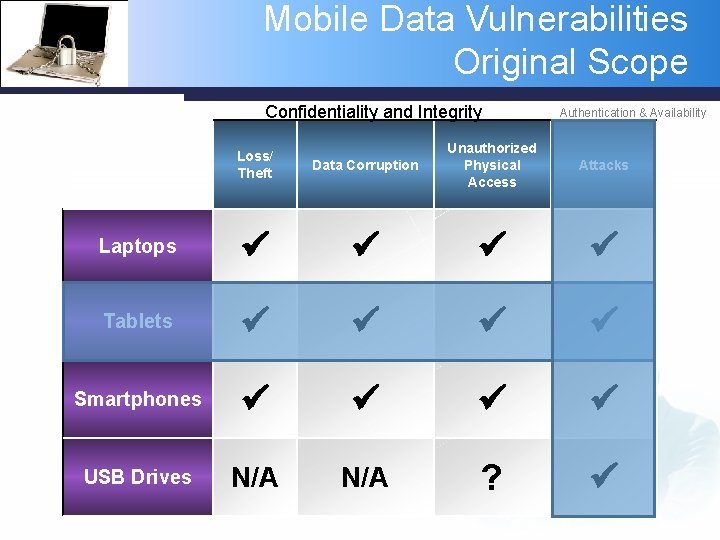
Mobile Data Vulnerabilities Original Scope Confidentiality and Integrity Authentication & Availability Data Corruption Unauthorized Physical Access Attacks Tablets Smartphones USB Drives N/A ? Loss/ Theft Laptops
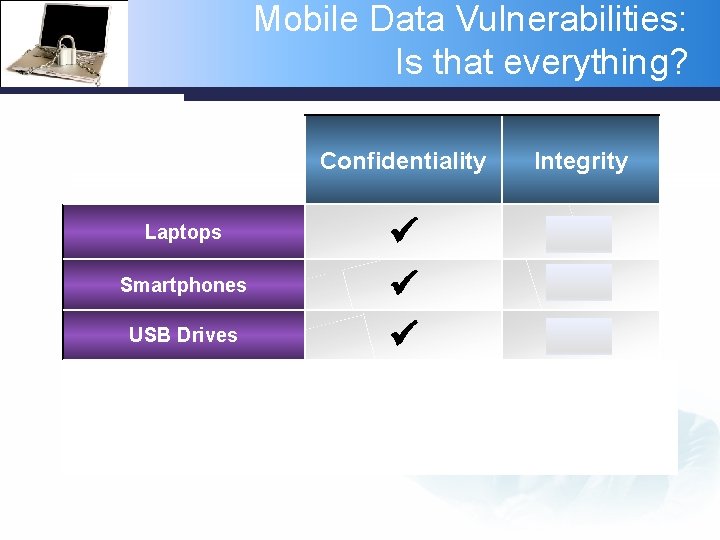
Mobile Data Vulnerabilities: Is that everything? Laptops Smartphones USB Drives External Media (CDs) Paper Confidentiality Integrity N/A N/A
User View of Situation Presenting ‘as is’ and ‘to be’ situations and a vision for the future D
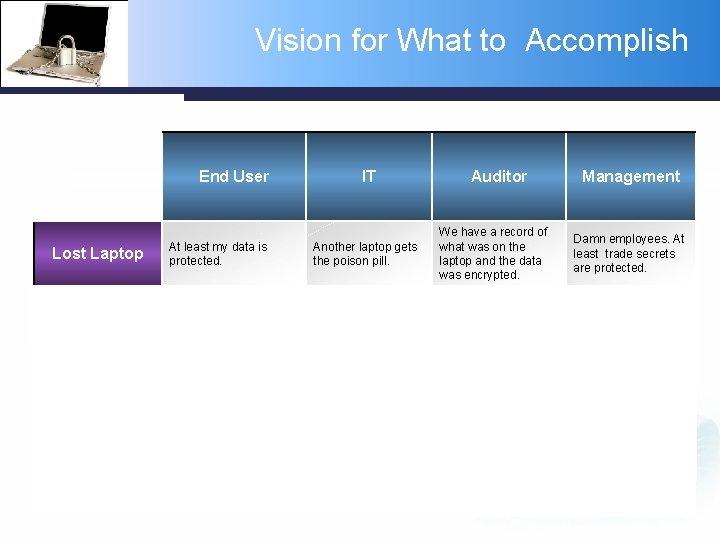
Vision for What to Accomplish End User IT Auditor Management Lost Laptop At least my data is protected. Another laptop gets the poison pill. We have a record of what was on the laptop and the data was encrypted. Damn employees. At least trade secrets are protected. Sensitive Information Reminder of what data is sensitive and limits on quantity. I’m told what the policies are and given tools to enforce it. I can establish enforceable policies in compliance with regulation. Employees can get access to the data they need to work, but not in excess. Corporate Smartphone My smartphone allows access to the applications and data I need Easy provisioning and support. User activity is auditable for smartphones. I know where the money is going and my costs are predictable. I am reminded of the risks of using certain tools. Flash drives and portable hard drives no longer frighten us. We have logs of where sensitive and personally identifiable information goes. If it ain't broke, don’t fix it. Proliferation of Tools
Mobile Security Program Management Defining solution categories and putting the initiative within a project framework
Tool Descriptions Mobile Device Protection (Endpoint Protection) Data Loss Protection (Endpoint Protection)
Preparing the Users and Infrastructure § Putting it all together: How do we select compatible products and vendors? What will it cost to buy and implement? How should we roll it out to the organization? How do we justify the costs to management?
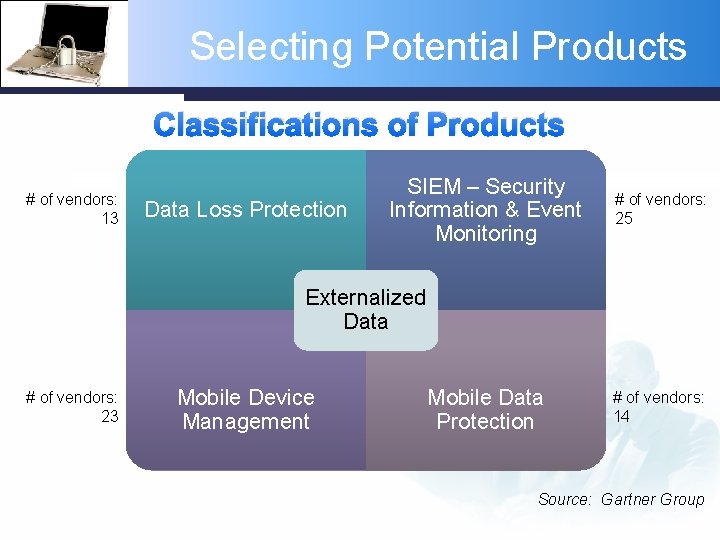
Selecting Potential Products Classifications of Products # of vendors: 13 Data Loss Protection SIEM – Security Information & Event Monitoring # of vendors: 25 Externalized Data # of vendors: 23 Mobile Device Management Mobile Data Protection # of vendors: 14 Source: Gartner Group

Selecting the Best Products Market Leaders or Visionaries Data Loss Protection – DLP Security Information Event Mgmt - SIEM • • • • Symantec Mc. Afee Verdasys Websense RSA (EMC) CA Technologies HP/Arc. Sight Q 1 Labs RSA (RMC) Symantec Nitro. Security (Mc. Afee) Logic Novell Mobile Device Management - MDM Mobile Data Protection - MDP • • • ü • • Good Technology Sybase Air. Watch Mobile. Iron Mc. Afee Sophos* Check. Point Software Technologies Symantec *Trustmark uses Utimaco Safe. Guard Enterprise, which was purchased by Sophos
Selecting the Best Products § For everything except MDM, trend is for vendor consolidation in the marketplace, so that vendor can be “one-stop shop”. Example: Mc. Afee bought Nitro. Security Sophos bought Utimaco Symantec already has products in MDP, DLP, and SIEM categories § Selection should follow a disciplined process for evaluation examining comparative features, ease of configuration, price, and vendor support
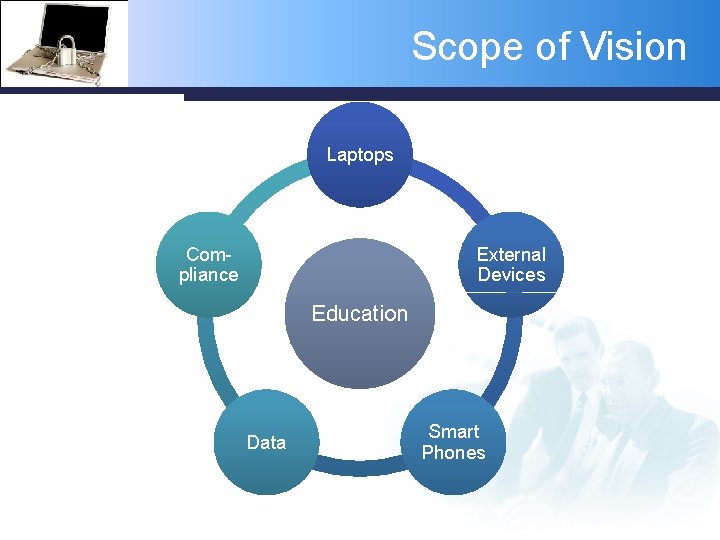
Scope of Vision Laptops Compliance External Devices Education Data Smart Phones
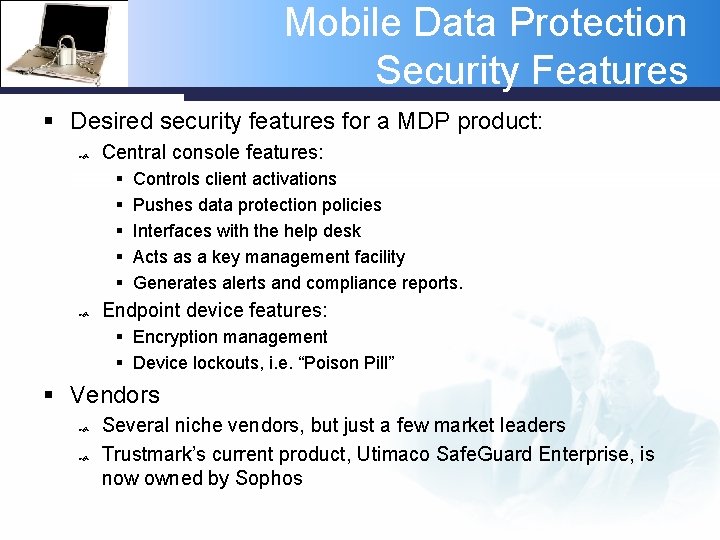
Mobile Data Protection Security Features § Desired security features for a MDP product: Central console features: § § § Controls client activations Pushes data protection policies Interfaces with the help desk Acts as a key management facility Generates alerts and compliance reports. Endpoint device features: § Encryption management § Device lockouts, i. e. “Poison Pill” § Vendors Several niche vendors, but just a few market leaders Trustmark’s current product, Utimaco Safe. Guard Enterprise, is now owned by Sophos
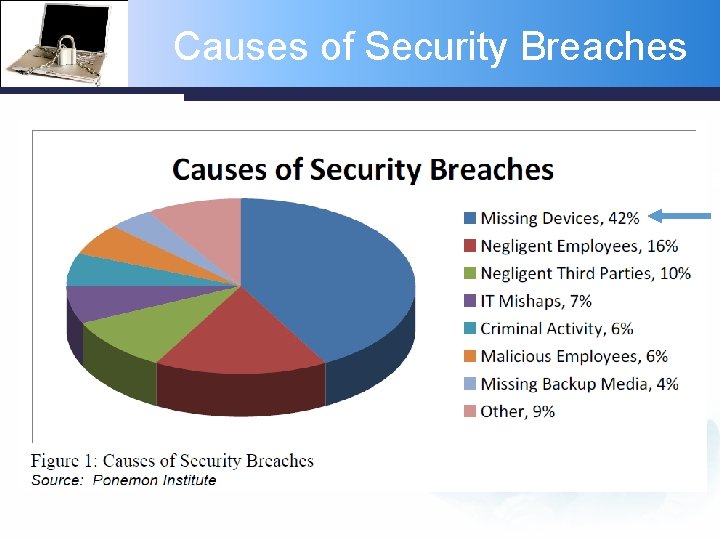
Causes of Security Breaches
The Mobile Workforce § 75% of US workers are mobile; One billion mobile workers worldwide* § 12, 000 laptop were lost in US airports**; 10, 000 cell phones are left in London taxis per month*** § 62% of mobile devices that were lost or stolen contained sensitive or confidential information** § 35% of organizations report that a lost or stolen mobile device caused the data breach they experienced** Sources: * IDC ** Ponemon Institute *** The Register
Data Loss Protection Security Features § Desired security features for a LDP product: Content-aware § Advanced content inspection and analysis techniques Ability to define data policies § What data is governed? § How it can be moved outside the network to external media? Ability take action when a policy violate is detected § Log, block, encrypt, etc. § Can also be triggered based on data quantity § Vendors Several well-known vendors are considered market leaders
Mobile Device Management Security Features § Desired security features for a MDM product: Enforced password Device wipe Remote lock Audit trail/logging "Jailbreak" detection § Vendors: Very crowded marketplace, but most vendors are considered niche players
SEIM Compliance/Security Features § Desired compliance/security features for a SEIM product: Security information management (SIM) — log management and compliance reporting Security event management (SEM) — real-time monitoring and incident management for security-related events from networks, security devices, systems, and applications Primary uses: § Compliance — log management and regulatory compliance reporting § External Threat management — real-time monitoring of user activity, data access, and application activity and incident management § Internal Threat Management - authorized user misuses of electronic health records (employee, partners, contractors). Medical record snooping, internal identity theft, internal medical identity theft § Vendors Many vendors to choose from; healthcare specialized features may limit the field
- Slides: 47