Mobile Protection Driving Productivity Without Compromising Protection Jon
Mobile Protection Driving Productivity Without Compromising Protection Jon Baker, Jason Kataila Endpoint Management & Mobility Specialist
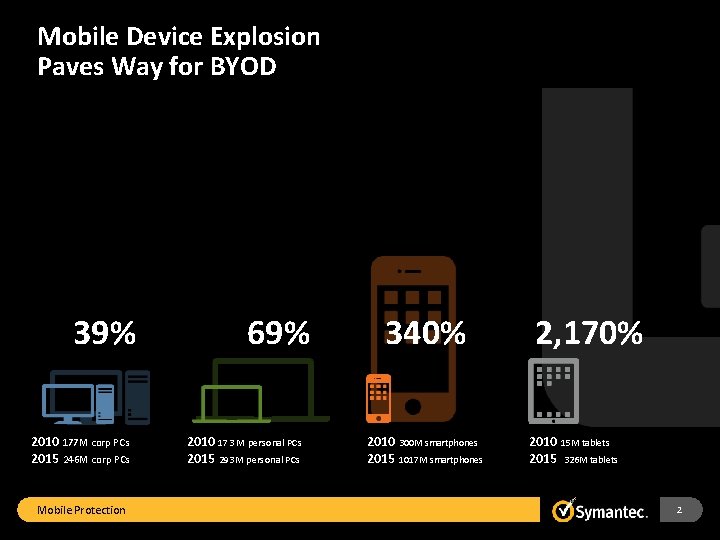
Mobile Device Explosion Paves Way for BYOD 39% 2010 177 M corp PCs 2015 246 M corp PCs Mobile Protection 69% 2010 173 M personal PCs 2015 293 M personal PCs 340% 2010 300 M smartphones 2015 1017 M smartphones 2, 170% 2010 15 M tablets 2015 326 M tablets 2
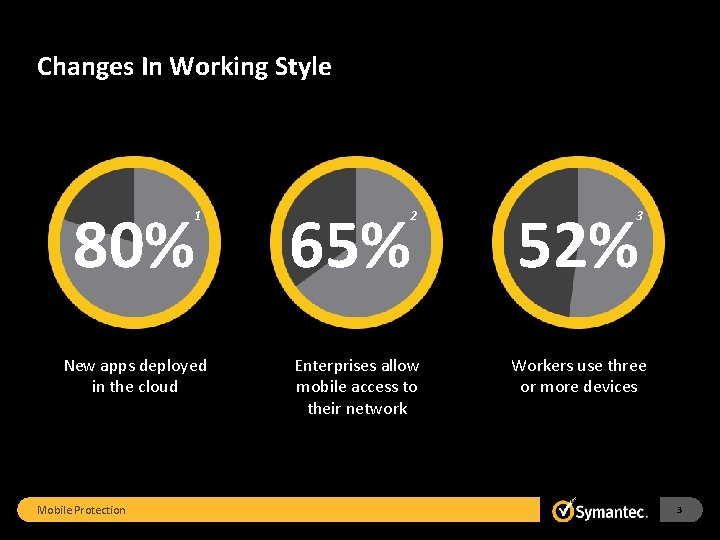
Changes In Working Style 80% 1 New apps deployed in the cloud Mobile Protection 65% 2 Enterprises allow mobile access to their network 52% 3 Workers use three or more devices 3
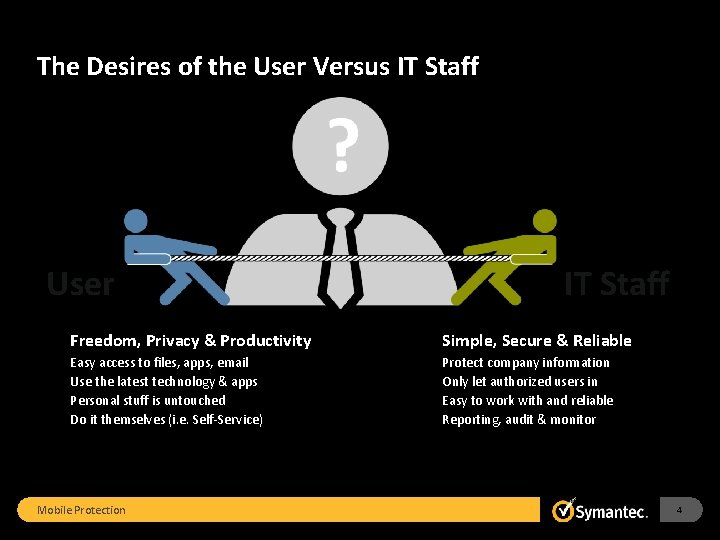
The Desires of the User Versus IT Staff User IT Staff Freedom, Privacy & Productivity Simple, Secure & Reliable Easy access to files, apps, email Use the latest technology & apps Personal stuff is untouched Do it themselves (i. e. Self-Service) Protect company information Only let authorized users in Easy to work with and reliable Reporting, audit & monitor Mobile Protection 4

Success = Mastering Control Points Devices Apps Data …without disrupting user experience Mobile Protection 5
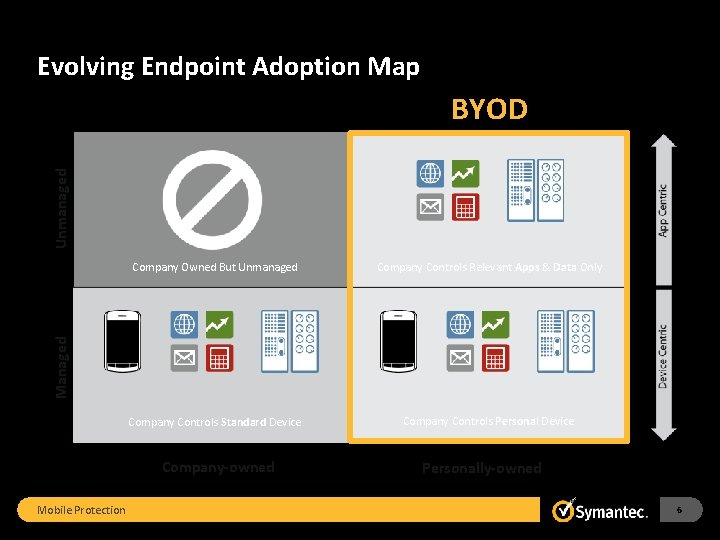
Evolving Endpoint Adoption Map Unmanaged BYOD Company Controls Relevant Apps & Data Only Company Controls Standard Device Company Controls Personal Device Managed Company Owned But Unmanaged Company-owned Mobile Protection Personally-owned 6
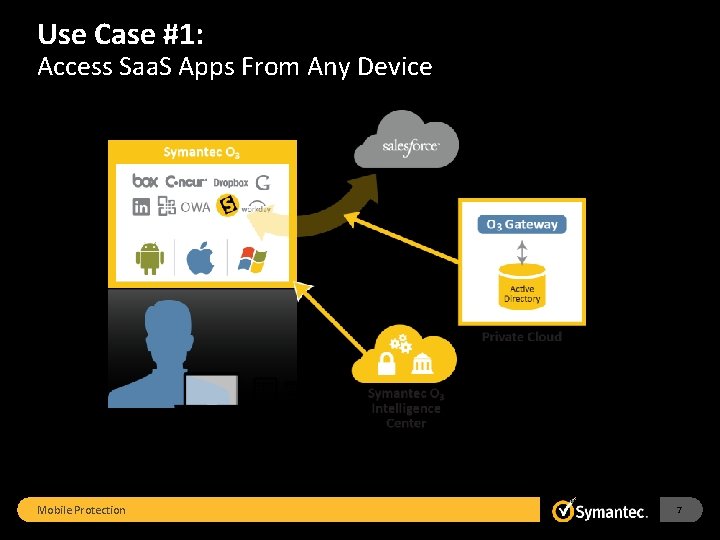
Use Case #1: Access Saa. S Apps From Any Device Mobile Protection 7
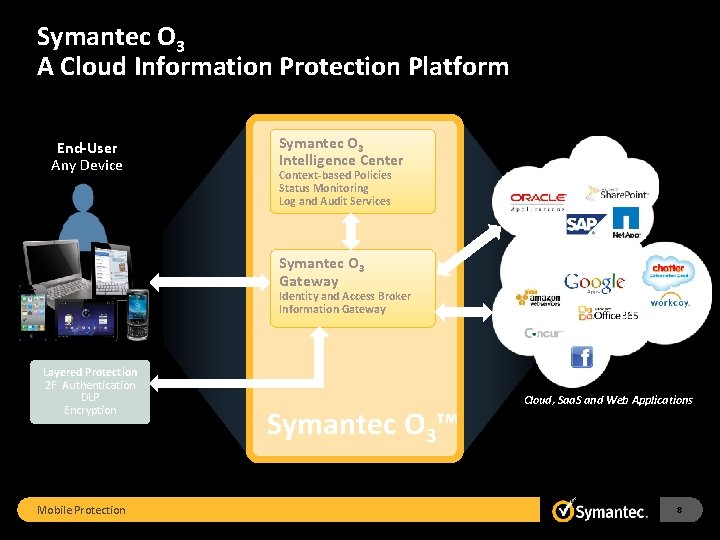
Symantec O 3 A Cloud Information Protection Platform End-User Any Device Symantec O 3 Intelligence Center Context-based Policies Status Monitoring Log and Audit Services Symantec O 3 Gateway Private Cloud / Data Center Public Cloud Identity and Access Broker Information Gateway Layered Protection 2 F Authentication DLP Encryption Mobile Protection Symantec O 3™ Cloud, Saa. S and Web Applications 8

Cloud & mobile: Opportunity And Challenge Private Cloud Mobile Challenge Mobile Protection “We should embrace BYOD, BYOA and the new mobile platform to augment productivity and innovate new business models” “How do we layer common protection across cloud and mobile without undermining the convenience of the mobile experience? ” 9
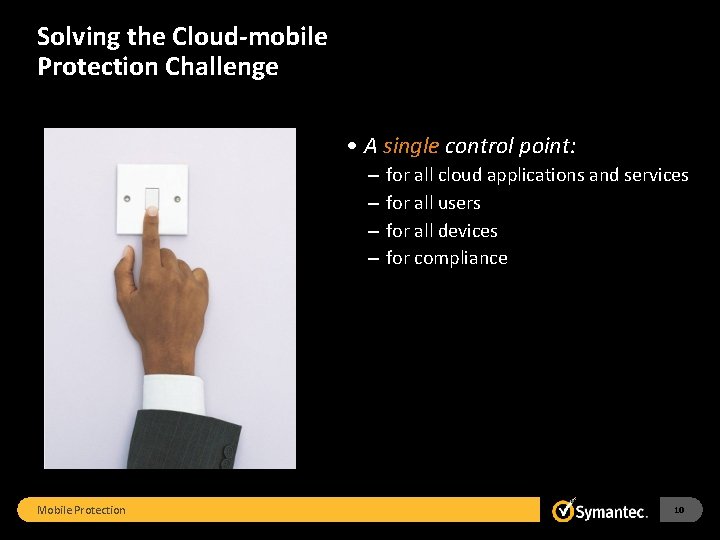
Solving the Cloud-mobile Protection Challenge • A single control point: – – Mobile Protection for all cloud applications and services for all users for all devices for compliance 10
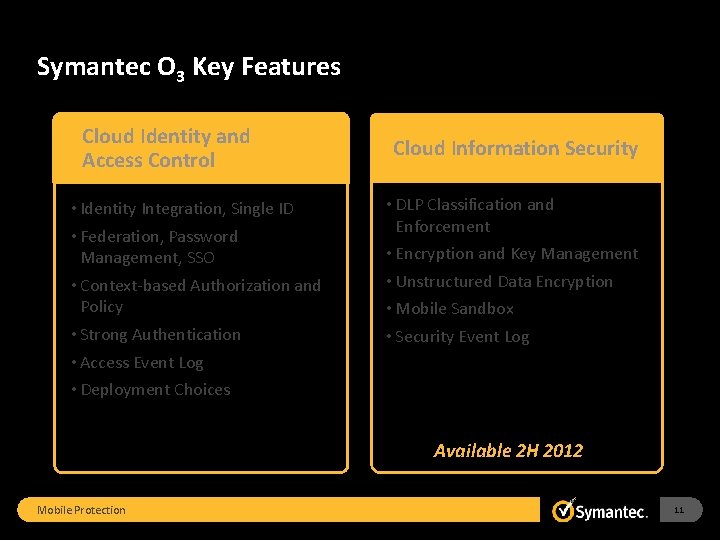
Symantec O 3 Key Features Cloud Identity and Access Control • Identity Integration, Single ID • Federation, Password Management, SSO • Context-based Authorization and Policy • Strong Authentication • Access Event Log • Deployment Choices Cloud Information Security • DLP Classification and Enforcement • Encryption and Key Management • Unstructured Data Encryption • Mobile Sandbox • Security Event Log Available 2 H 2012 Mobile Protection 11
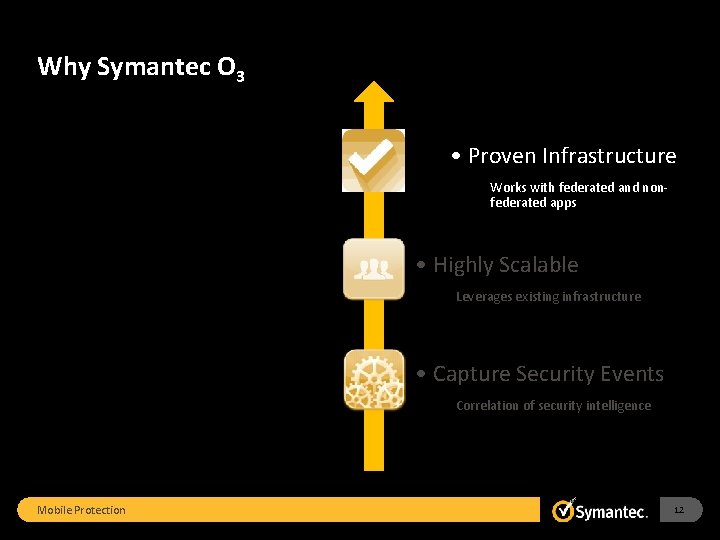
Why Symantec O 3. 1. . 2 Mobile Protection . 3 • Proven Infrastructure Works with federated and nonfederated apps 2 • Highly Scalable 3 • Capture Security Events Leverages existing infrastructure Correlation of security intelligence 12
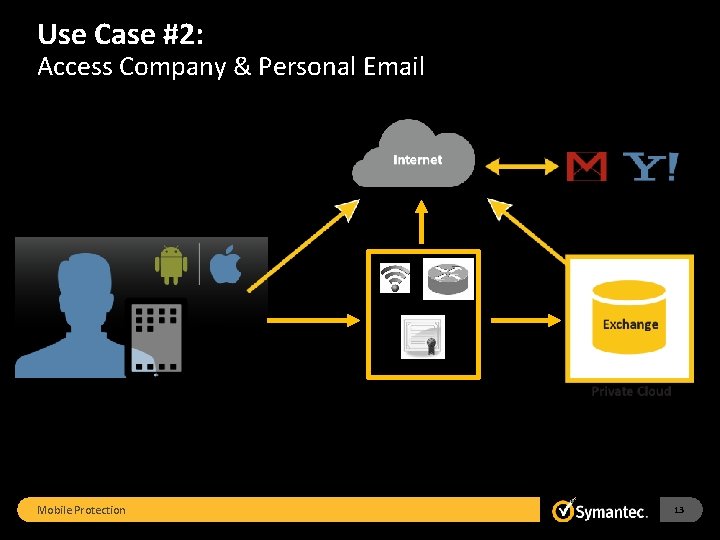
Use Case #2: Access Company & Personal Email Wi-Fi VPN CA Network Access Mobile Protection 13
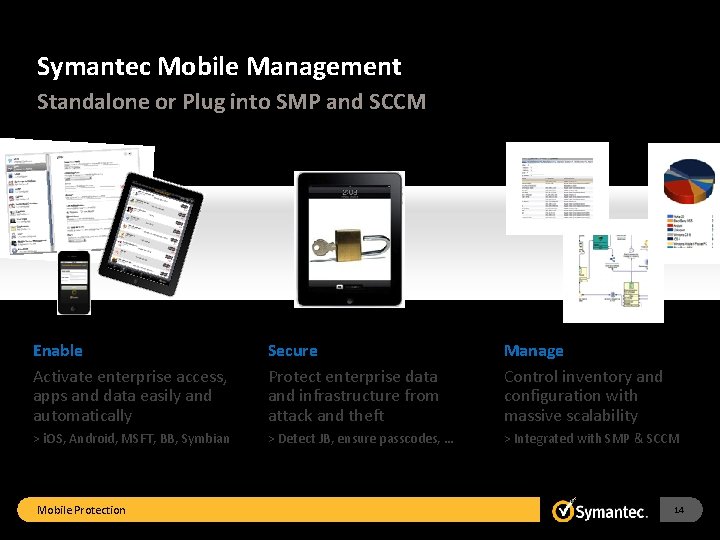
Symantec Mobile Management Standalone or Plug into SMP and SCCM Enable Activate enterprise access, apps and data easily and automatically Secure Protect enterprise data and infrastructure from attack and theft Manage Control inventory and configuration with massive scalability > i. OS, Android, MSFT, BB, Symbian > Detect JB, ensure passcodes, … > Integrated with SMP & SCCM Mobile Protection 14
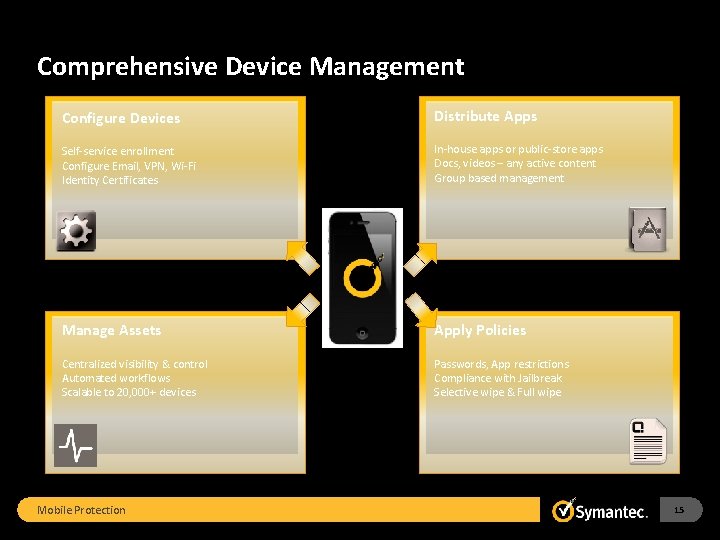
Comprehensive Device Management Configure Devices Distribute Apps Self-service enrollment Configure Email, VPN, Wi-Fi Identity Certificates In-house apps or public-store apps Docs, videos – any active content Group based management Manage Assets Apply Policies Centralized visibility & control Automated workflows Scalable to 20, 000+ devices Passwords, App restrictions Compliance with Jailbreak Selective wipe & Full wipe Mobile Protection 15
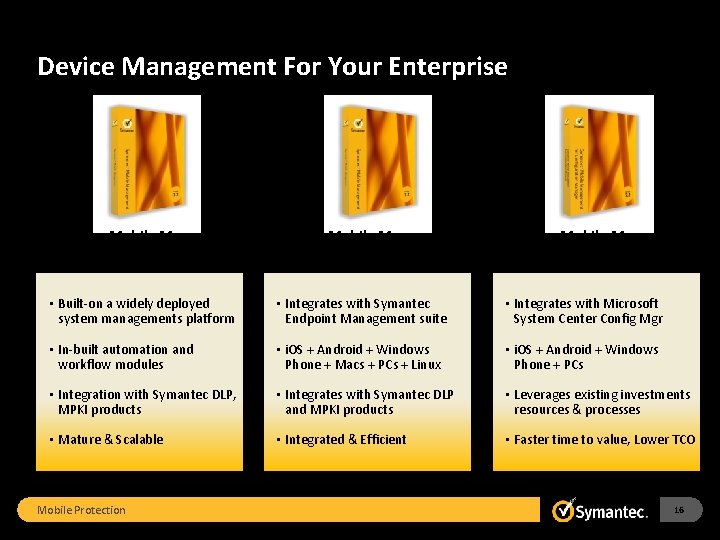
Device Management For Your Enterprise Symantec Mobile Management (stand-alone) for Symantec ITMS Symantec Mobile Management for Microsoft SCCM • Built-on a widely deployed system managements platform • Integrates with Symantec Endpoint Management suite • Integrates with Microsoft System Center Config Mgr • In-built automation and workflow modules • i. OS + Android + Windows Phone + Macs + PCs + Linux • i. OS + Android + Windows Phone + PCs • Integration with Symantec DLP, MPKI products • Integrates with Symantec DLP and MPKI products • Leverages existing investments resources & processes • Mature & Scalable • Integrated & Efficient • Faster time to value, Lower TCO Mobile Protection 16
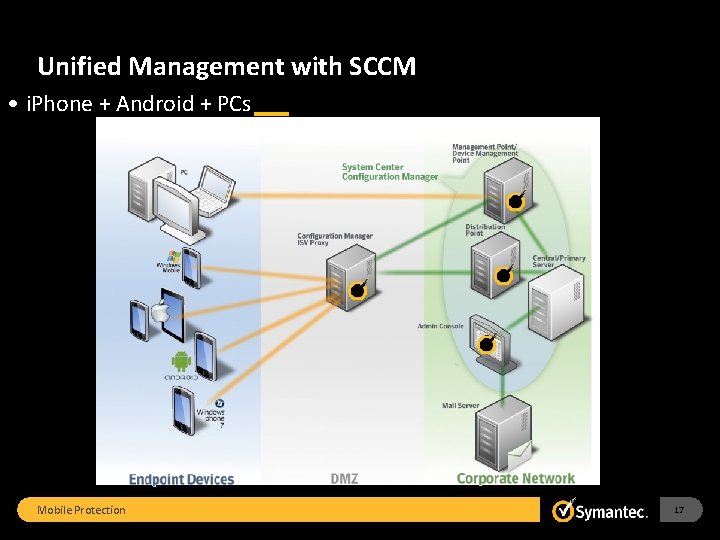
Unified Management with SCCM • i. Phone + Android + PCs Mobile Protection 17
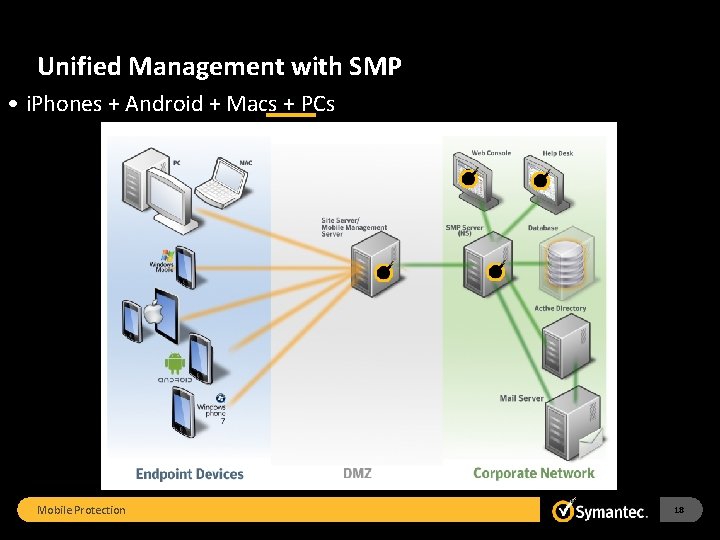
Unified Management with SMP • i. Phones + Android + Macs + PCs Mobile Protection 18
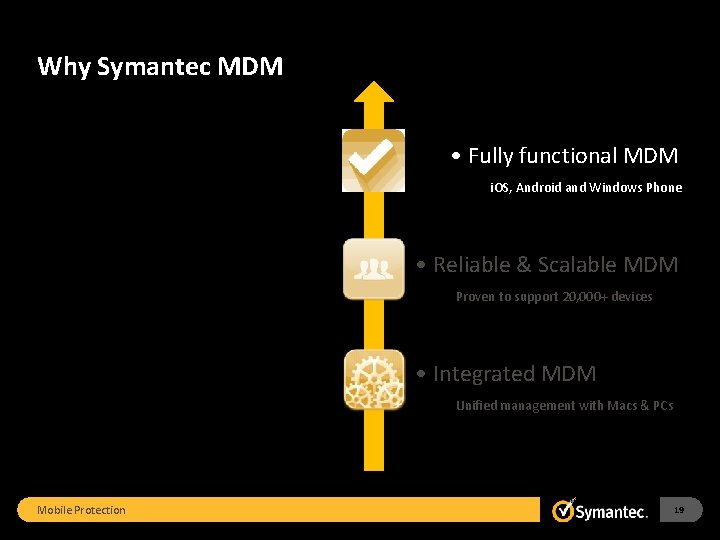
Why Symantec MDM. 1. . 2 Mobile Protection . 3 • Fully functional MDM i. OS, Android and Windows Phone 2 • Reliable & Scalable MDM 3 • Integrated MDM Proven to support 20, 000+ devices Unified management with Macs & PCs 19
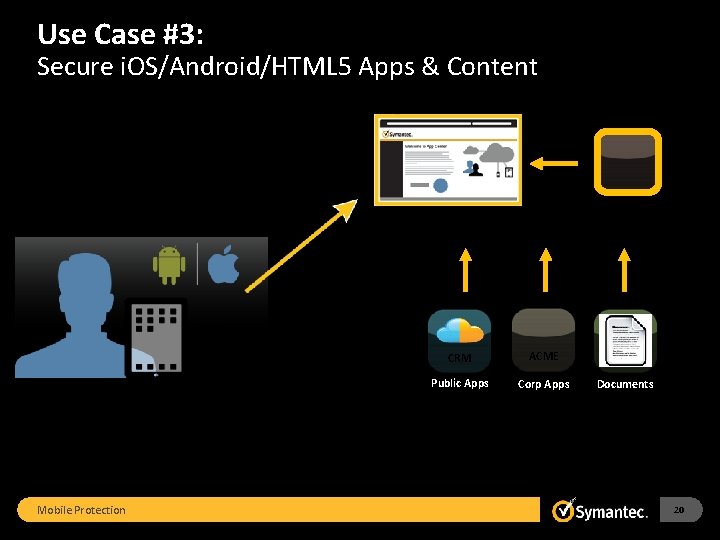
Use Case #3: Secure i. OS/Android/HTML 5 Apps & Content Enterprise App Store Containerized Application Personal Mobile Protection CRM ACME Corp App Public Apps Corp Apps Documents 20

Mobile Application Management Comprehensive App Wrapping Tech App Store Repository for internal and external mobile applications Mobile App Management App Policy Protect app against data loss through encryption, removal control and separation of corporate data Content Center DLP policy to control confidential data access 21
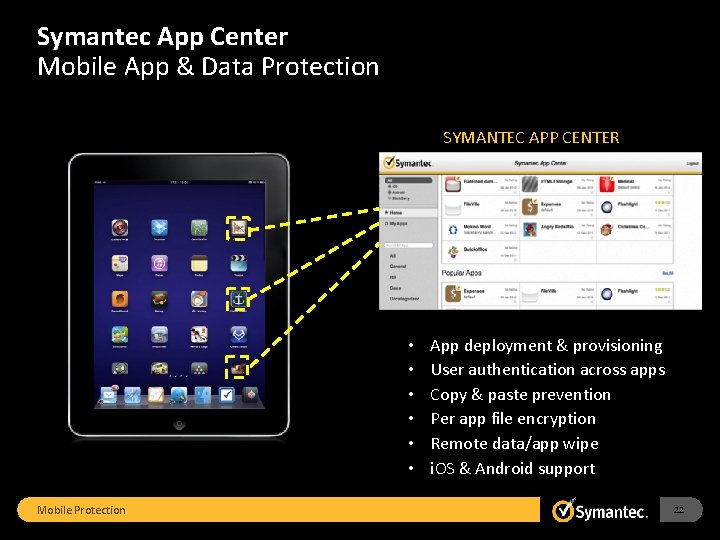
Symantec App Center Mobile App & Data Protection SYMANTEC APP CENTER • • • Mobile Protection App deployment & provisioning User authentication across apps Copy & paste prevention Per app file encryption Remote data/app wipe i. OS & Android support 22
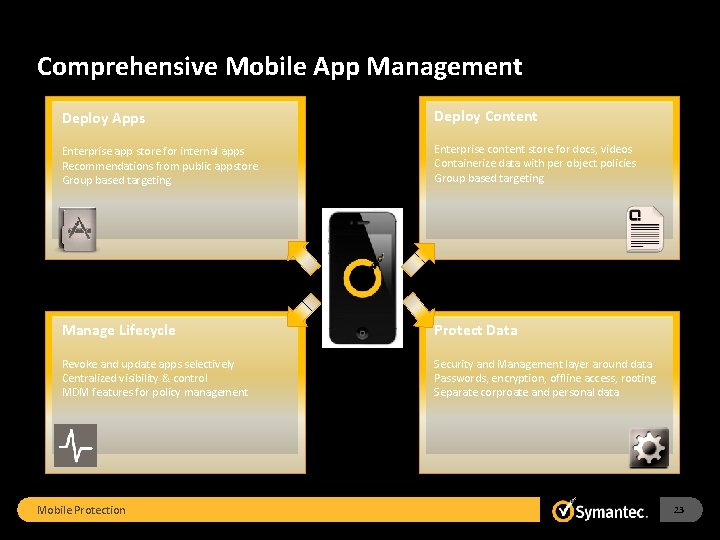
Comprehensive Mobile App Management Deploy Apps Deploy Content Enterprise app store for internal apps Recommendations from public appstore Group based targeting Enterprise content store for docs, videos Containerize data with per object policies Group based targeting Manage Lifecycle Protect Data Revoke and update apps selectively Centralized visibility & control MDM features for policy management Security and Management layer around data Passwords, encryption, offline access, rooting Separate corproate and personal data Mobile Protection 23
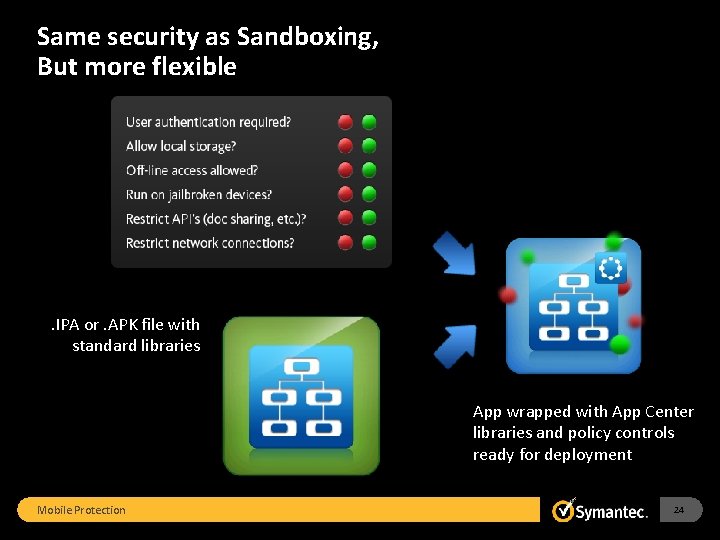
Same security as Sandboxing, But more flexible . IPA or. APK file with standard libraries App wrapped with App Center libraries and policy controls ready for deployment Mobile Protection 24
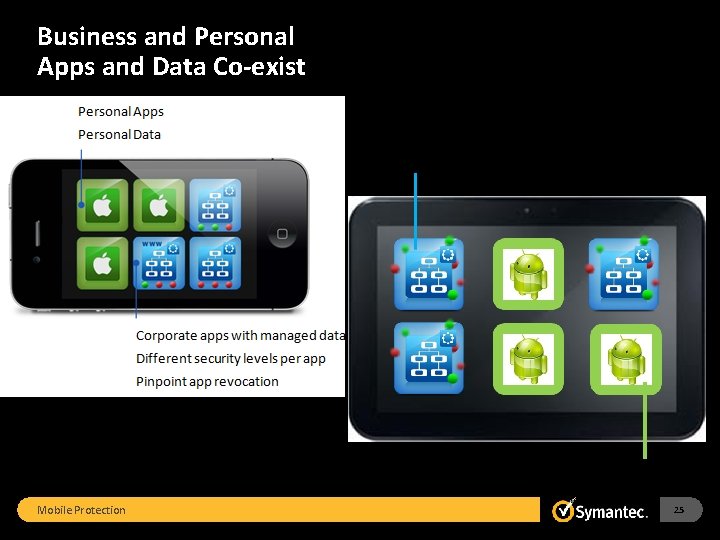
Business and Personal Apps and Data Co-exist Mobile Protection 25
i. OS & MDM Enhancements • Ability to upload config profiles • Additional i. OS MDM restrictions • “Badge” wrapped apps FIPS 140 -2 Level 1 Encryption for apps & data on i. OS devices • … • Customers in regulated verticals can confidently use App Center data protection • Customers can comply with regulatory requirements with App Center • Customers can use App Center for additional MDM capabilities Mobile Protection 26
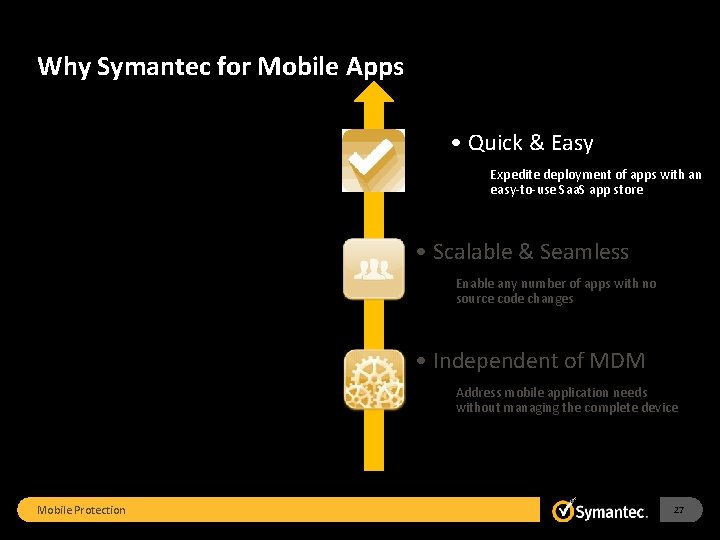
Why Symantec for Mobile Apps. 3. . 2. 1 • Quick & Easy Expedite deployment of apps with an easy-to-use Saa. S app store • Scalable & Seamless Enable any number of apps with no source code changes • Independent of MDM Address mobile application needs without managing the complete device Mobile Protection 27
Use Case #4: Secure Email and Prevent Malware Personal Mobile Protection CRM ACME Corp App Email Corp Apps Documents 28
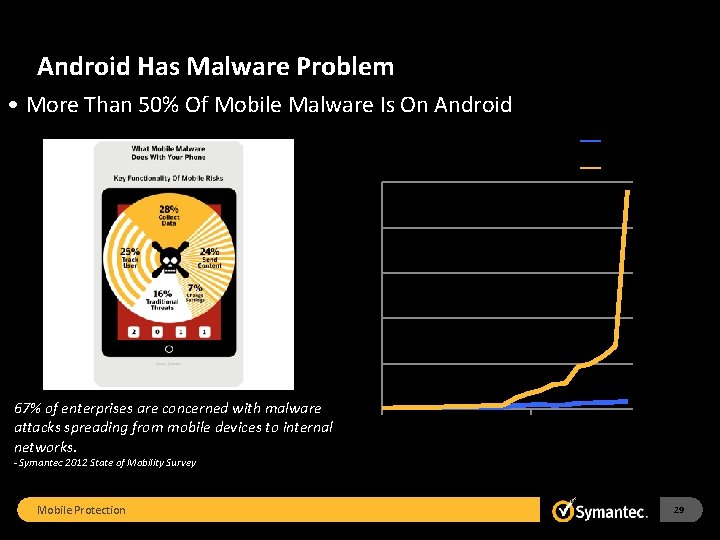
Android Has Malware Problem • More Than 50% Of Mobile Malware Is On Android Malware 2500 Family Variants 2000 1500 1000 500 67% of enterprises are concerned with malware attacks spreading from mobile devices to internal networks. 0 Jul-11 - Symantec 2012 State of Mobility Survey Mobile Protection 29
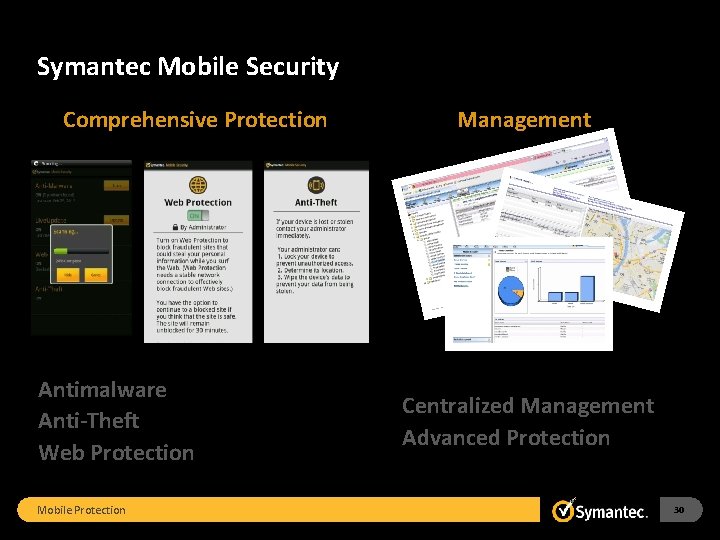
Symantec Mobile Security Comprehensive Protection Antimalware Anti-Theft Web Protection Mobile Protection Management Centralized Management Advanced Protection 30
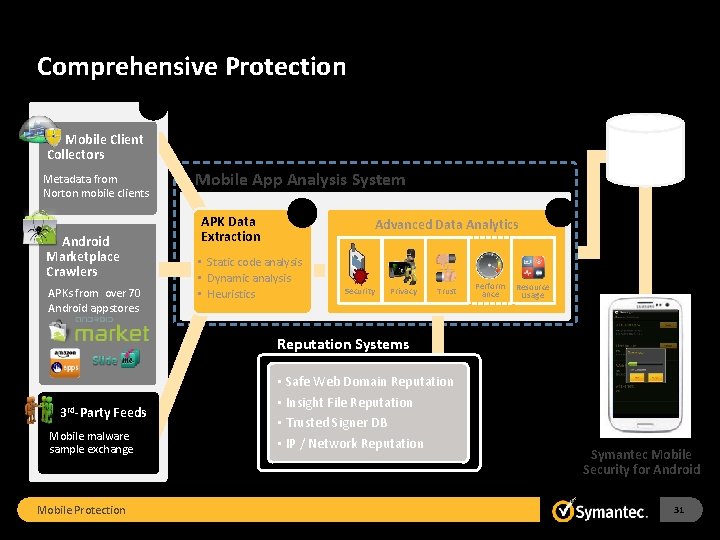
Comprehensive Protection 1 Mobile Client Collectors Metadata from Norton mobile clients Android Marketplace Crawlers APKs from over 70 Android appstores App Profiles Mobile App Analysis System APK Data Extraction 2 • Static code analysis • Dynamic analysis • Heuristics Advanced Data Analytics Security Privacy Trust Perform ance 3 Resource Usage Reputation Systems 3 rd-Party Feeds Mobile malware sample exchange Mobile Protection • Safe Web Domain Reputation • Insight File Reputation • Trusted Signer DB • IP / Network Reputation Symantec Mobile Security for Android 31

Symantec Mobile Security for Android • 1. On-device Anti-Malware Scanning Google Play Amazon External Sources Browser 2 to 10 seconds Background, Scheduled OR Manual 3 rd Party Markets Mobile Protection 32
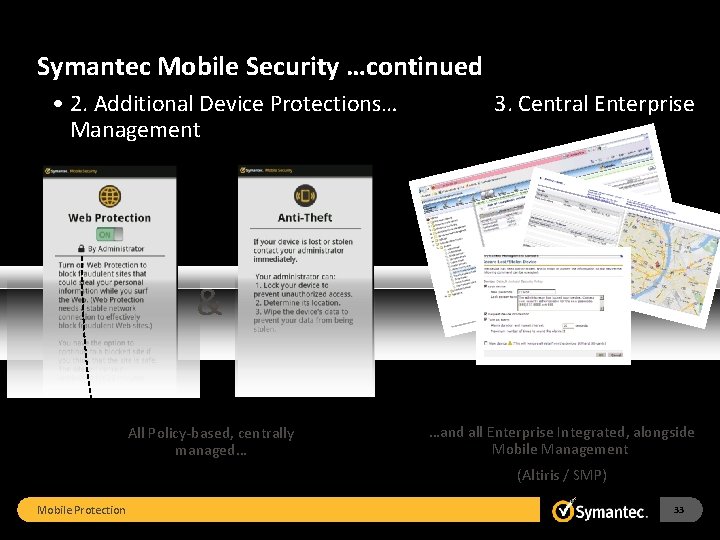
Symantec Mobile Security …continued • 2. Additional Device Protections… Management 3. Central Enterprise & All Policy-based, centrally managed… …and all Enterprise Integrated, alongside Mobile Management (Altiris / SMP) Mobile Protection 33
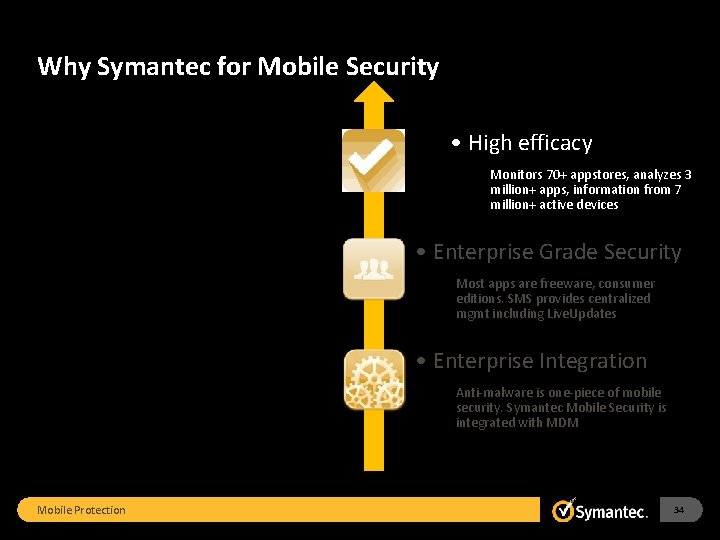
Why Symantec for Mobile Security. 3. . 2. 1 • High efficacy Monitors 70+ appstores, analyzes 3 million+ apps, information from 7 million+ active devices • Enterprise Grade Security Most apps are freeware, consumer editions. SMS provides centralized mgmt including Live. Updates • Enterprise Integration Anti-malware is one-piece of mobile security. Symantec Mobile Security is integrated with MDM Mobile Protection 34
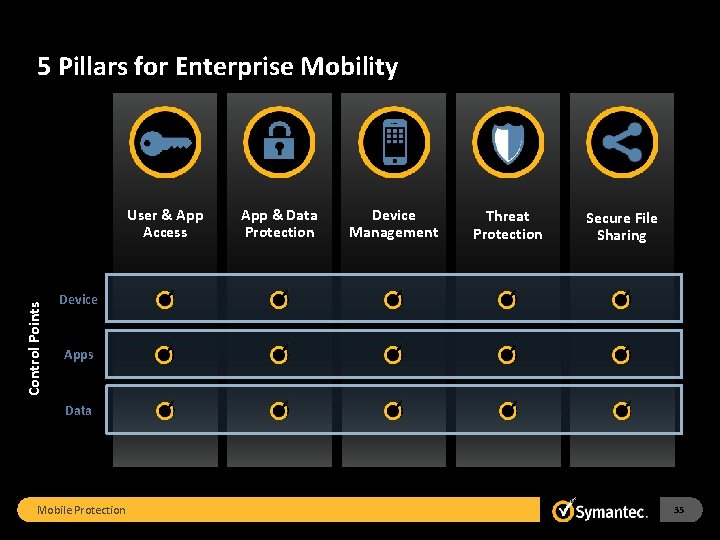
5 Pillars for Enterprise Mobility Control Points User & App Access App & Data Protection Device Management Threat Protection Secure File Sharing Device Apps Data Mobile Protection 35
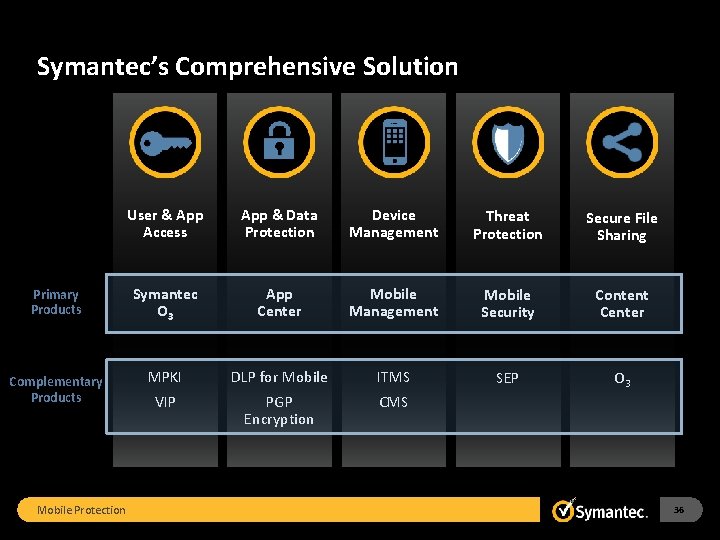
Symantec’s Comprehensive Solution Primary Products Complementary Products Mobile Protection User & App Access App & Data Protection Device Management Threat Protection Secure File Sharing Symantec O 3 App Center Mobile Management Mobile Security Content Center SEP O 3 MPKI DLP for Mobile ITMS VIP PGP Encryption CMS 36
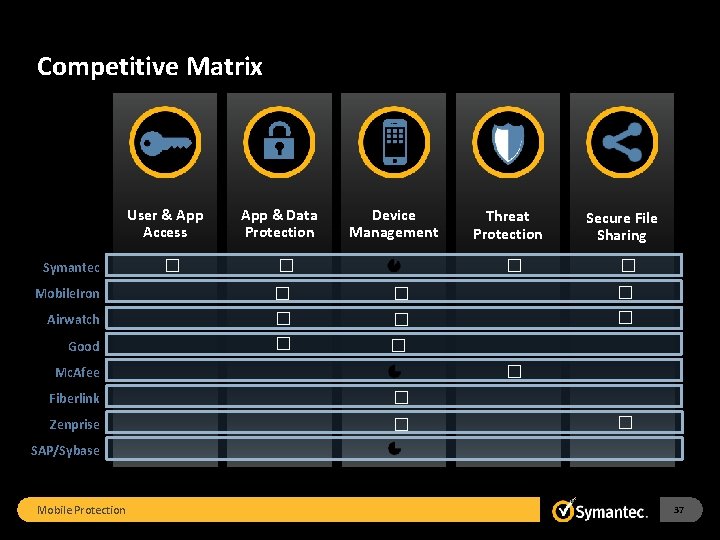
Competitive Matrix User & App Access Symantec Mobile. Iron Airwatch Good � App & Data Protection Device Management � � � Zenprise Secure File Sharing � � � � Mc. Afee Fiberlink Threat Protection � � � SAP/Sybase Mobile Protection 37
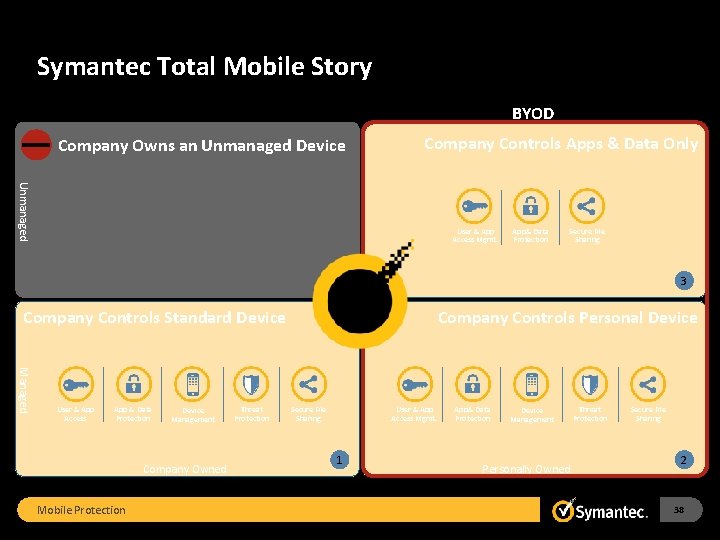
Symantec Total Mobile Story BYOD Company Owns an Unmanaged Device Company Controls Apps & Data Only Unmanaged User & App Access Mgmt. App& Data Protection Secure File Sharing 3 Company Controls Standard Device Managed User & App Access App & Data Protection Device Management Company Owned Mobile Protection Threat Protection Company Controls Personal Device Secure File Sharing User & App Access Mgmt. 1 App& Data Protection Device Management Personally Owned Threat Protection Secure File Sharing 2 38
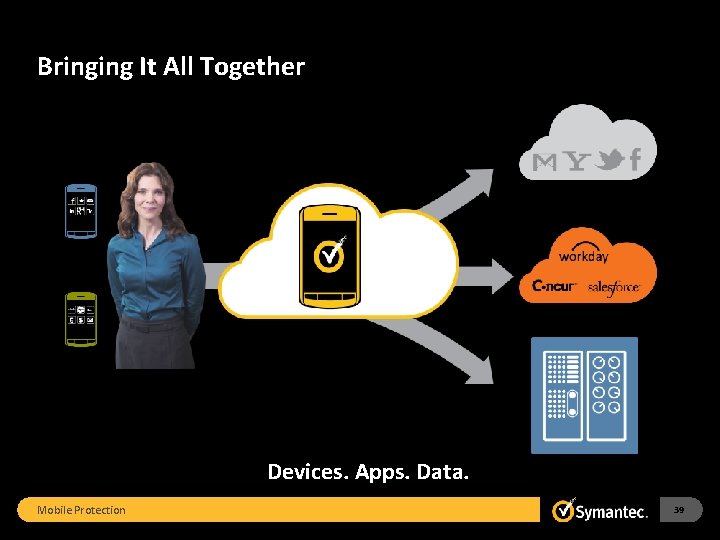
Bringing It All Together Devices. Apps. Data. Mobile Protection 39
Thank you! Jon Baker, Jason Kataila www. Symantec. com Mobility Specialist Group Copyright © 2011 Symantec Corporation. All rights reserved. Symantec and the Symantec Logo are trademarks or registered trademarks of Symantec Corporation or its affiliates in the U. S. and other countries. Other names may be trademarks of their respective owners. This document is provided for informational purposes only and is not intended as advertising. All warranties relating to the information in this document, either express or implied, are disclaimed to the maximum extent allowed by law. The information in this document is subject to change without notice. Mobile Protection 40
- Slides: 40