Mobile Health A Cautionary Tale NJDV HIMSS Fall
“Mobile Health - A Cautionary Tale” NJ/DV HIMSS Fall Conference October 29, 2015 Sharon R. Klein , Partner (Pepper Hamilton LLP) Yale H. Bohn, Special Counsel (Pepper Hamilton LLP) Edward Henry, Director of Technology, Information Security Officer (Princeton Health. Care System) #35750149 v. 3
Mobility in Health. Care • Technology has evolved and medical practices are getting more patients actively engaged by providing mobile solutions • Patient Portals – These portals can be accessed via a mobile device or mobile application • Mobile Apps - Traditional desktop applications do not provide the needed flexibility and convenience provided by mobile solutions • Activity Trackers – Mobile applications that are design to track vital information for patient, staff workflows • Text Messages – Many physicians are resorting to texting fellow colleagues for consults • Mobile Devices – Tablets, smart phones provide caregivers real-time access to critical data when needed 2
Basic Principles Key Definitions • Telemedicine is the practice of medicine using electronic communications, information technology or other means between a licensee in one location, and a patient in another location with or without an intervening health care provider. (Federation of State Medical Boards) • Telehealth is a broader term than telemedicine because telehealth refers to more than just clinical services. Telehealth includes remote monitoring, telepharmacy, regional health information sharing, and non-clinical services, such as education programs, administration, and public health. 3
Basic Principles Telemedicine vs. Telehealth • Types of Telemedicine: - Non-simultaneous: involves after-the-fact interpretation or assessment, such as teleradiology services - Simultaneous: involves “real-time” interpretation or assessment, such as telestroke and tele. ICU services • (Generally) NOT Telemedicine: - Informal consultations between practitioners - Telephone conversations, e-mail/instant messaging conversations, or fax transmissions • Telemedicine and telehealth are tools in medical practice, not distinct services 4
Basic Principles Telemedicine Participants • Patient • On Site Provider – health care provider that is with the patient at the time of service - Treating Provider - Allied Health Professionals • Remote Provider - Treating Provider – provider that has a treatment relationship with the patient at the originating site - Consulting Provider – provider at a distant site that is being consulted by the treating provider; often specialty telemedicine consultations 5
Basic Principles Telemedicine Participants • Technology Vendor - Device – the hardware that is being used to conduct the telemedicine session (e. g. , i. Pad, cell phone, computer) - Software/Application – the program or application that is being used to conduct the telemedicine session • Telecom Carrier • Payor – Medicare, Medicaid, private payors 6
Information Security Risks • • • Data Loss from lost, stolen or decommissioned devices Mobile Device operating system vulnerabilities Public and unsecured Wi-Fi, rogue access points Mobile Malware – Information Stealing Data leakage from Mobile Device Applications 7
Mobile Security Safeguards Patient Portals • Establish Business Associate Agreements • Breach notification and associated policies • Documentation of security standards (Do they Comply? ) - Password Management - Access Control - Change Management • Audit Logs to monitor EHR activities • Secure Data Interfaces 8
Mobile Security Safeguards Mobile Devices • Establish Bring Your Own Device (BYOD) Policy • Formalize asset management templates for all mobile device users • Consider Mobile Device Management Solutions - Application Containment - Secure Corporate Data - Availability Restrictions • Standardize End Point Encryption • Isolate Guest Network Traffic 9
HIPAA Privacy and Security Considerations HIPAA/HITECH Privacy and Security Laws & Regulations • Health Insurance Portability and Accountability Act of 1996 (HIPAA) • Health Information Technology for Economic and Clinical Health Act (HITECH) (American Recovery and Reinvestment Act of 2009) • HIPAA Rules: 45 C. F. R. Parts 160, 162, 164 (Final Omnibus Rule: 01/25/13, Compliance date: 09/23/13) • Enforcement - Civil and criminal penalties - HHS/OCR, DOJ, SAG 10
HIPAA Privacy and Security Considerations What is PHI? • Protected Health Information (PHI), includes demographic information collected from an individual, that: - is created or received by a health care provider, health plan, employer or health care clearinghouse; and - relates to: (a) the past, present, or future physical or mental health or condition of an individual; (b) the provision of health care to an individual; or (c) the past, present or future payment for the provision of health care to an individual; and - identifies the individual OR there is a reasonable basis to believe the information can be used to identify the individual; and - is transmitted or maintained by electronic media or in any other form or medium. 11
HIPAA Privacy and Security Considerations Who is Responsible? • Covered Entity (CE) - Health care provider who conducts electronic transactions • Institutional providers • Non-institutional providers • “any other person or organization who furnishes, bills, or is paid for health care in the normal course of business” - Health plan - Health care clearinghouse 12
HIPAA Privacy and Security Considerations Who is Responsible? • Business Associate (BA) - Creates, receives, maintains or transmits PHI on behalf of a Covered Entity • OR - Provides certain services (identified in the Rule) involving PHI, to or for, a Covered Entity • Examples: actuarial, legal, accounting, consulting, management, administrative, financial • Data transmission providers - Routine access to PHI versus mere conduit 13
HIPAA Privacy and Security Considerations Subcontractor Business Associates • Business associate includes: any subcontractor that creates, receives, maintains, or transmits protected health information on behalf of the business associate • Subcontractor – any person to whom a business associate delegates a function, activity, or service, other than in the capacity of a member of the workforce of such business associate 14
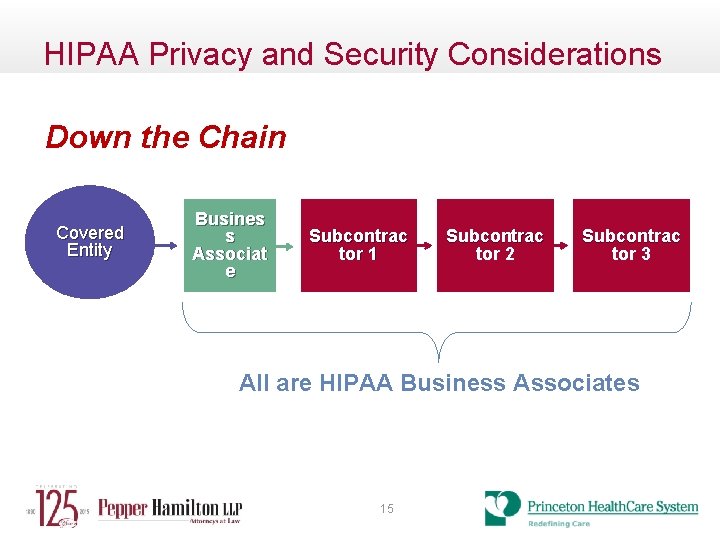
HIPAA Privacy and Security Considerations Down the Chain Covered Entity Busines s Associat e Subcontrac tor 1 Subcontrac tor 2 Subcontrac tor 3 All are HIPAA Business Associates 15
HIPAA Privacy and Security Considerations Key Concept: HIPAA Security • Privacy Rule – includes mini security rule - administrative, technical and physical safeguards to protect privacy of PHI • Security Rule regulations for secure storage, maintenance and transmission of e. PHI • Security Rule requirements: - administrative, technical and physical safeguards for e. PHI - document requirements of policies, procedures, etc. - required and addressable implementation specifications • Key administrative safeguards: - implement a Security Management process • Risk assessment is a critical component 16
Other Privacy and Security Considerations • Telemedicine vs. Mobile Health - Chat messaging software between patients and health care providers - Health applications with patient-entered data - Remote patient monitoring devices and privacy collection • Is it a HIPAA issue? - Federal Trade Commission • Internet of Things - Food and Drug Administration - Federal Communications Commission 17
Regulatory Framework Non-HIPAA Regulated Medical Data • • Information sharing not from CE Wellness Tracking Data to person directly from medical device Mobile medical applications 18
Regulatory Framework Federal Trade Commission • Congress has been unable to pass a Federal Privacy Bill • Protecting Consumer Privacy in Era of Rapid Change (Report, Mar 2012) • Mobile Privacy Disclosures, Building Trust Through Transparency (Report, Feb 2013) • Internet of Things – Privacy & Security in a Connected World (Report, January 2015) • Start with Security (Report June, 2015) 19
Regulatory Framework Federal Trade Commission • Protecting Consumer Privacy in Era of Rapid Change (Report, Mar 2012) - Privacy by Design: • Promote privacy throughout the organization and at every stage of development of products and services • Delete consumer data no longer needed and allow consumers to do the same • Provide reasonable security for data • Limit collection of data (consistent with context of particular transaction) • Implement reasonable data retention and disposal policies • Maintain reasonable accuracy of data 20
Regulatory Framework Federal Trade Commission • Protecting Consumer Privacy in Era of Rapid Change - Simplify Consumer Choice: • Provide Consumer choice for any communications not related to original transaction • “Do Not Track” mechanisms allow consumers to control collection and use of their online data • Certain choices require consumers to “opt in” - Improve Transparency to Consumers: • Clearer and shorter privacy notices • Provide access to consumer data • Educate consumers about company’s data privacy practices 21
Regulatory Framework Internet of Things – Benefits of Mobile Devices Connected health devices can “improve quality of life and safety by providing a richer source of data to the patient’s doctor for diagnosis and treatment. . . improve disease prevention, making the healthcare system more efficient and driving costs down. . . [and] provide an incredible wealth of data, revolutionizing medical research and allowing the medical community to better treat, and ultimately eradicate, diseases. ” Comment of Consumer Elec. Ass’n, #484 cmt. #00027 at 16. 22
Regulatory Framework Federal Communications Commission • • • Regulates the airwaves Wireless technology issues Wireless co-existence with electromagnetic compatibility Root cause analysis of problems with connectivity 802. 11 wireless data security not robust 23
Regulatory Framework Food & Drug Administration • Mobile Medical Applications (Final Guidance, February 9, 2015) - Software as Medical Device - FDA intends to regulate mobile medical software that poses a threat to public safety - The key regulatory factor is the intended use of the mobile health application - Is software application what it claims? 24
Regulatory Framework Food & Drug Administration • Mobile Medical Applications Visual Acuity Test - Regulated Applications: • Extending medical device to control the device for use in active patient monitoring • Acting as an accessory to a medical device • Using attachments, screens, sensors to transform mobile platform into a medical device • Performing patient-specific analyses • Assisting with diagnosis or treatment recommendations 25
Regulatory Framework Food & Drug Administration • Mobile Medical Applications - Non-Regulated Applications • Supplementing clinical care by helping patients manage EHR / PHR their health • Providing patients with tools to organize/track health information • Providing easy access to patient’s health conditions • Helping patients document or communicate medical information to providers • Performing simple calculations used in clinical practice • Enabling individuals to interact with Personal Health Records (“PHRs”) and Electronic Health Records (“EHRs”) 26
Challenging Scenarios Case Study: Telemedicine (Tele- Radiology) 27
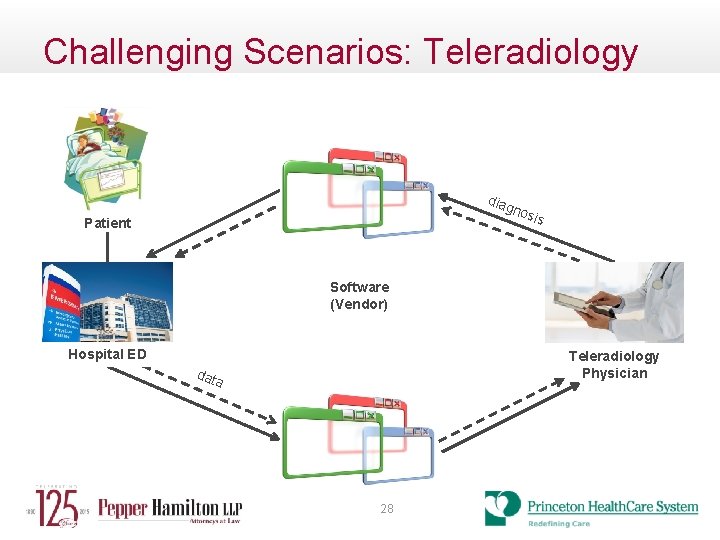
Challenging Scenarios: Teleradiology diag nos Patient is Software (Vendor) Hospital ED Teleradiology Physician dat a 28
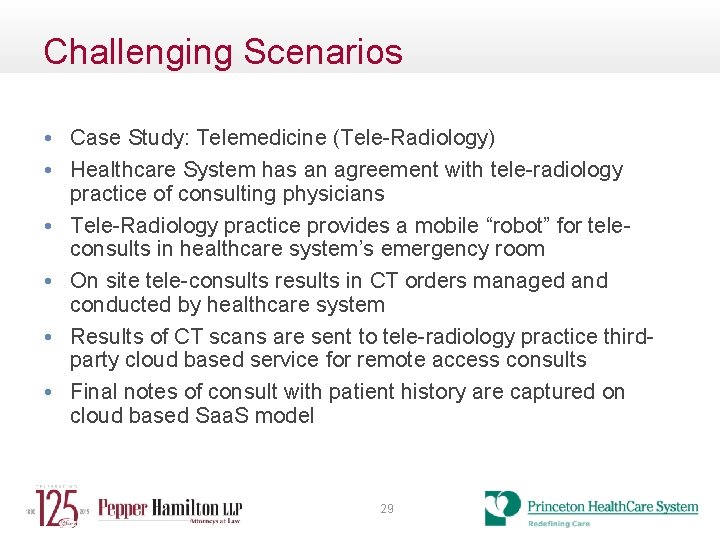
Challenging Scenarios • Case Study: Telemedicine (Tele-Radiology) • Healthcare System has an agreement with tele-radiology practice of consulting physicians • Tele-Radiology practice provides a mobile “robot” for teleconsults in healthcare system’s emergency room • On site tele-consults results in CT orders managed and conducted by healthcare system • Results of CT scans are sent to tele-radiology practice thirdparty cloud based service for remote access consults • Final notes of consult with patient history are captured on cloud based Saa. S model 29
Challenging Scenarios –Proper Safeguards • Case Study: Telemedicine (Tele-Radiology) • Healthcare System has an agreement with tele-radiology practice of consulting physicians (Establish Contract with BAA) • Tele-Radiology practice provides a mobile “robot” for tele-consults in healthcare system’s emergency room (Proper identification of patient and secure transmission between healthcare system and tele-radiology practice) • Results of CT scans are sent to tele-radiology practice third-party cloud based service for remote access consults (Secure Encrypted Tunnel connection for transmission of results with third party) • In this case since sensitive patient data was being sent to a third party, who was not contracted with the healthcare system, thirdparty vendor had to sign a new BAA with healthcare system • Always : FOLLOW THE DATA 30
Challenging Scenarios Case Study: Mobile Application 31
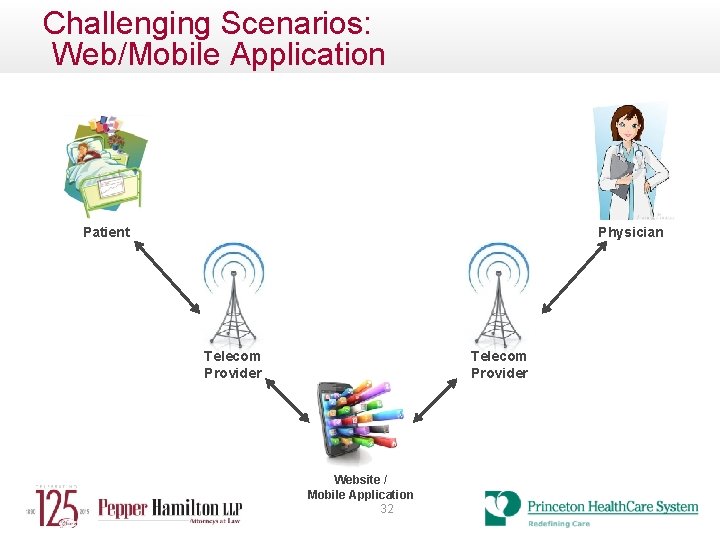
Challenging Scenarios: Web/Mobile Application Physician Patient Telecom Provider Website / Mobile Application 32
Challenging Scenarios Case Study: Mobile Application • Physician has a new cloud based application that will improve patient satisfaction • The application is designed to improve communication with patients and family members • Assigned staff will enter patient information to cloud, such as appointment schedules and pre-operative instructions • Application will E-mail or text appointment time, location and provide selected family members updates on procedure progress • Information may be viewed by patients and selected family members from any mobile device • E-mail or text Post Op instructions and paperwork 33
Challenging Scenarios – Proper Safeguards Case Study: Mobile Application • Physician has a new cloud based application that will improve patient satisfaction (What data will be sent to the cloud? Will the contracted company host the data or will a third party? ) • The application is designed to improve communication with patients and family members (Risk vs Reward) • Assigned staff will enter patient information to cloud such as appointment schedules and pre-operative instructions (Establish access control measures. Who will administer the application? How can security be controlled? ) • Application will E-mail or text appointment time, location and provide selected family members updates on procedure progress (What exactly will be sent? Defined templates or free text? Will data be de-classified? Patient consent? ) • E-mail or text Post Op instructions and paperwork (Is there a complete audit trail for data access? ) 34
Challenging Scenarios: Questions to Consider • Does HIPAA apply? - Is there PHI? - Are there Covered Entities? • • Are there Business Associates? Business Associate Agreement v. Service Agreement Physical security issues Data collection, transmission, access/use, disclosure, storage, ownership • FTC, FDA, FCC, State Law 35
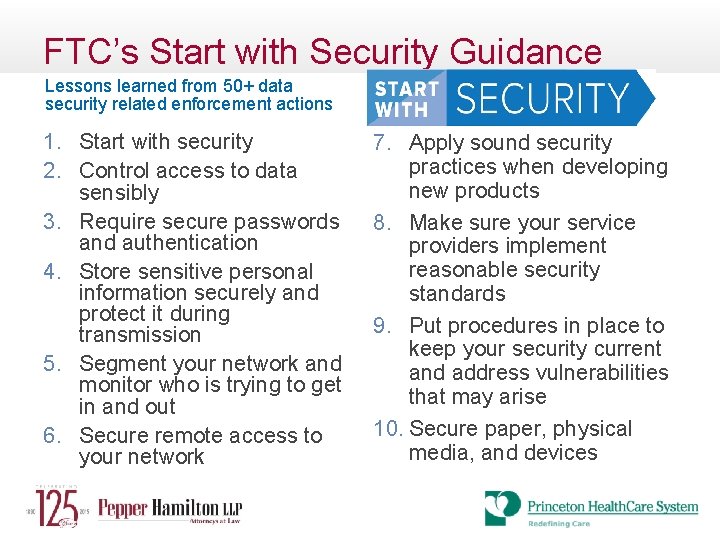
FTC’s Start with Security Guidance Lessons learned from 50+ data security related enforcement actions 1. Start with security 2. Control access to data sensibly 3. Require secure passwords and authentication 4. Store sensitive personal information securely and protect it during transmission 5. Segment your network and monitor who is trying to get in and out 6. Secure remote access to your network 7. Apply sound security practices when developing new products 8. Make sure your service providers implement reasonable security standards 9. Put procedures in place to keep your security current and address vulnerabilities that may arise 10. Secure paper, physical media, and devices
Consequences of Non-Compliance • • • Direct financial impact Diversion of resources Derivative lawsuits Class action lawsuits Reputational damage Regulatory exposure 37
Questions Sharon R. Klein kleins@pepperlaw. com Yale H. Bohn bohny@pepperlaw. com Edward Henry ehenry@princetonhcs. org 38
- Slides: 38