MITIGATING YOUR NONPROFITS DIGITAL RISK Ryan Prindiville MBA

MITIGATING YOUR NONPROFIT’S DIGITAL RISK Ryan Prindiville, MBA

PRESENTER Ryan Prindiville, MBA Director, Armanino Practice Lead, Strategy and Transformation Consulting • Multi-functional experience includes strategy, technology, product commercialization, innovation, operations, solution delivery, process improvement and management consulting • Extensive business, technology and operations leadership experience in Fortune 50, mid-market and entrepreneurial environments • Led global teams in the Americas, Asia and Europe • MBA from University of Southern California • BA from University of California at Santa Barbara
OVERVIEW • Discuss trends and developments in cybersecurity for the nonprofit sector • Evaluate practical steps your nonprofit can take to establish and enhance your cybersecurity program • Consider how to effectively communicate the importance of cybersecurity across the enterprise

WERE ARE NONPROFITS FALLING SHORT?
IN THE NEWS…
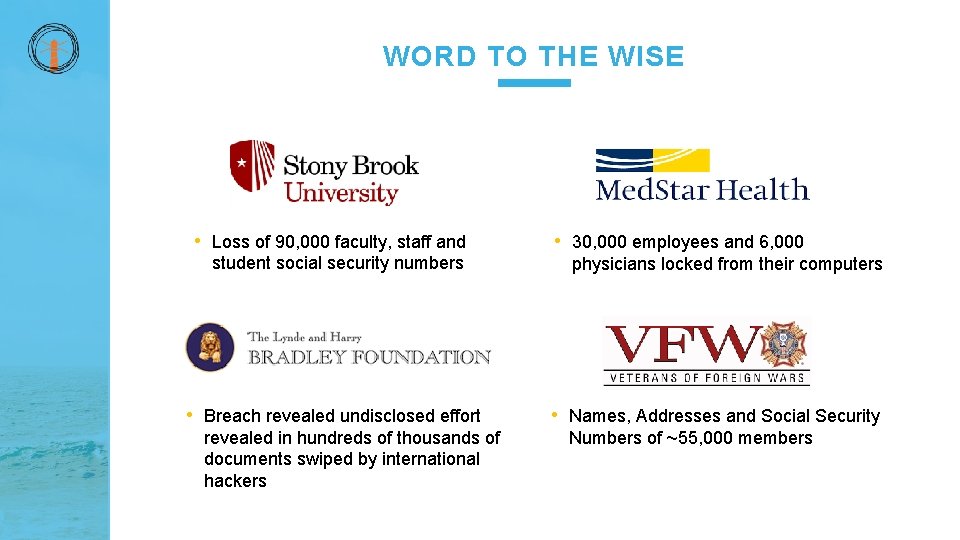
WORD TO THE WISE • Loss of 90, 000 faculty, staff and student social security numbers • Breach revealed undisclosed effort revealed in hundreds of thousands of documents swiped by international hackers • 30, 000 employees and 6, 000 physicians locked from their computers • Names, Addresses and Social Security Numbers of ~55, 000 members
IN THE NEWS…
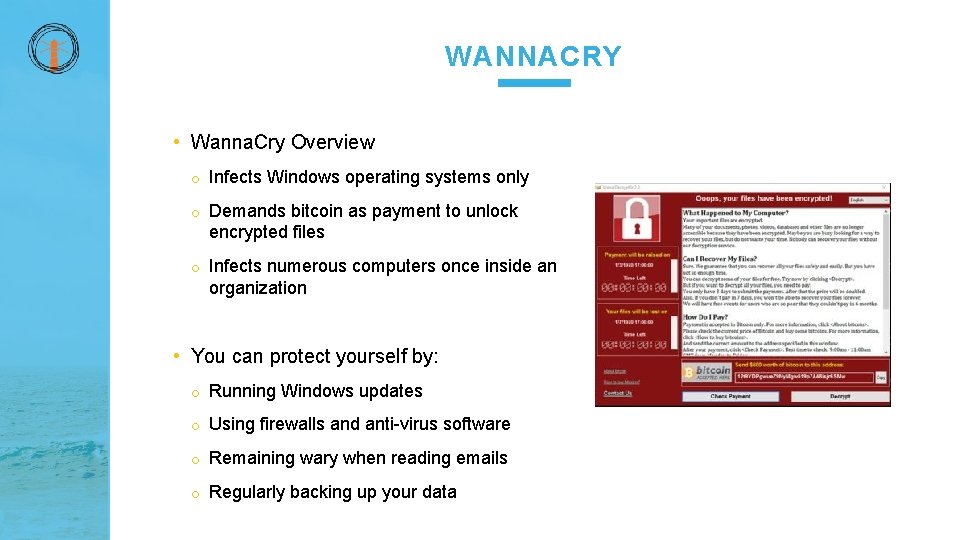
WANNACRY • Wanna. Cry Overview o Infects Windows operating systems only o Demands bitcoin as payment to unlock encrypted files o Infects numerous computers once inside an organization • You can protect yourself by: o Running Windows updates o Using firewalls and anti-virus software o Remaining wary when reading emails o Regularly backing up your data
DO YOU WORK IN STARBUCKS OR OTHER PUBLIC AREAS OFTEN? RAISE YOUR HAND

LACK OF SAFEGUARDS 80% …of nonprofits do not have adequate data backup and protection to safeguard sensitive donor data.

HOW MANY PEOPLE THINK CYBERSECURITY IS A TECHNOLOGY PROBLEM? RAISE YOUR HAND
AICPA CYBERSECURITY FRAMEWORK Sue Coffey, CPA, CGMA AICPA Executive VP Cybersecurity threats are escalating, thereby unnerving boards of directors, managers, investors, and customers of businesses of all sizes—whether public or private. While there are many methods, controls, and frameworks for developing cybersecurity risk management programs, until now there hasn’t been a common language for companies to communicate about, and report on, these efforts.
AICPA TOP ISSUE FACING NONPROFITS Issue #1: Cybersecurity • Common hacking risks • Credit card fraud from online contributions o Forego requiring personal identification information o Easier testing ground • Highest risk o Real-time credit card authorization and settlement highest risk • Repay fraudulent donations + pay fees related to the refunds o Hospitals and nonprofit healthcare • Patient data (e. g. , medical records and insurance)
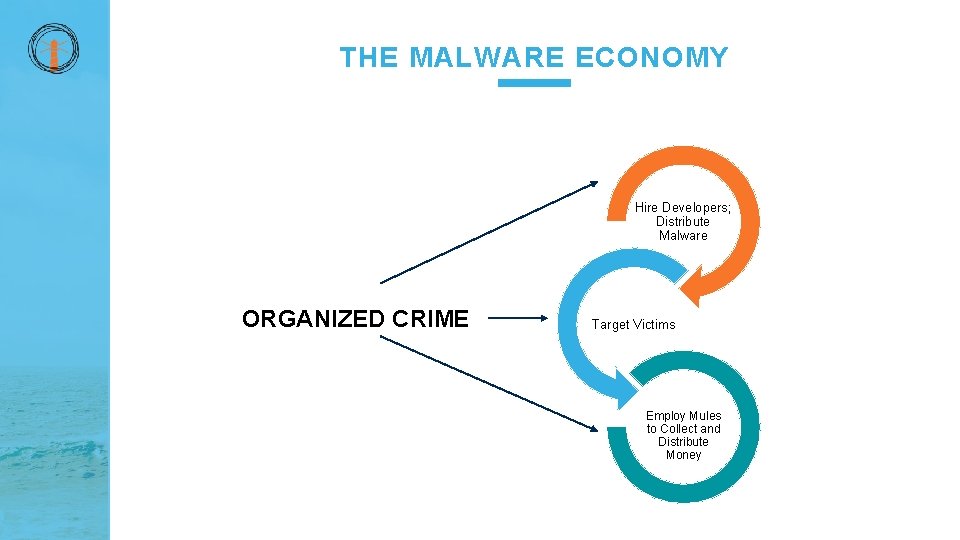
THE MALWARE ECONOMY Hire Developers; Distribute Malware ORGANIZED CRIME Target Victims Employ Mules to Collect and Distribute Money
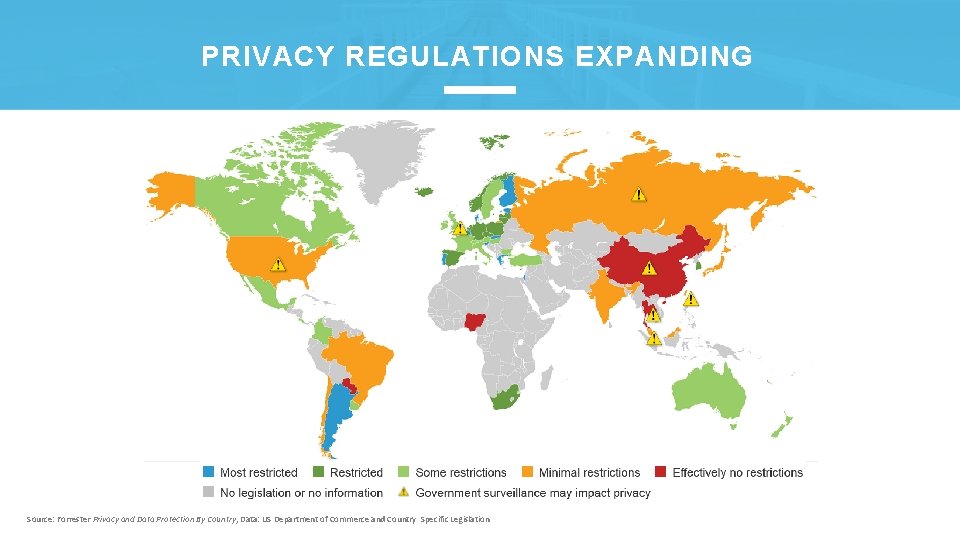
PRIVACY REGULATIONS EXPANDING Source: Forrester Privacy and Data Protection By Country, Data: US Department of Commerce and Country Specific Legislation

DO YOU USE THE SAME PASSWORD FOR HOME AND WORK ACCOUNTS? RAISE YOUR HAND
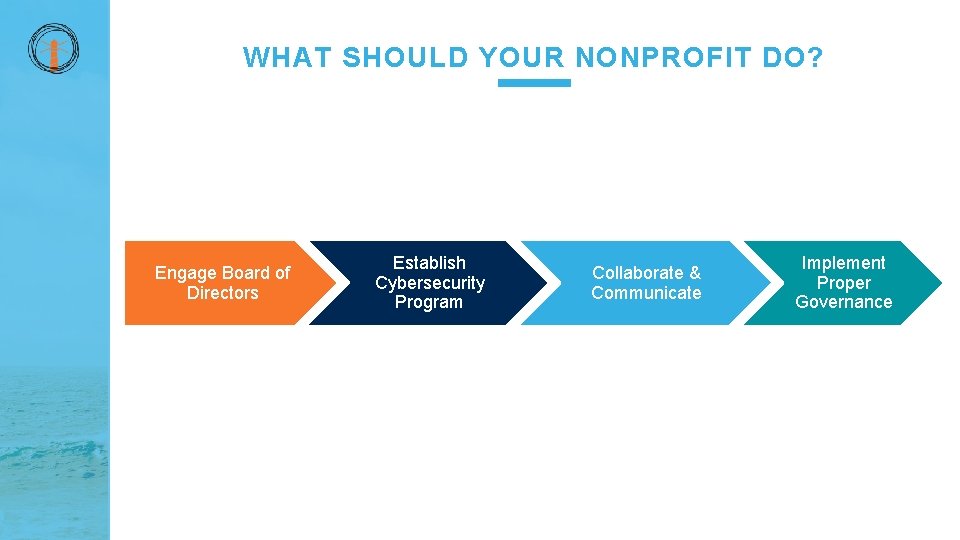
WHAT SHOULD YOUR NONPROFIT DO? Engage Board of Directors Establish Cybersecurity Program Collaborate & Communicate Implement Proper Governance
BOARD INVOLVEMENT & OVERSIGHT • Evaluate and update board composition and re-define board committees • Understand the board’s fiduciary responsibility o Put systems and controls in place to effectively manage the risk of cyberattacks • Establish proper governance and board oversight o Periodically review your cyber-risk assessment o Understand the cybersecurity strategy, governance structure and how it fits into the Enterprise Risk Management (ERM) program o Insist on a cybersecurity scorecard o Understand the nonprofit's cyber incident response process o Retain outside experts as necessary and as resources permit o Review professional and general liability insurance policies
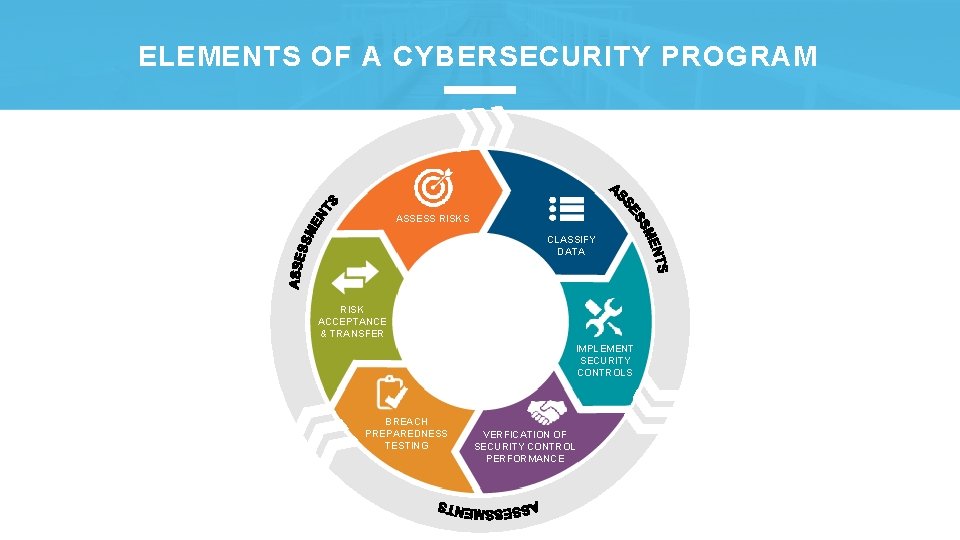
ELEMENTS OF A CYBERSECURITY PROGRAM ASSESS RISKS CLASSIFY DATA RISK ACCEPTANCE & TRANSFER IMPLEMENT SECURITY CONTROLS BREACH PREPAREDNESS TESTING VERFICATION OF SECURITY CONTROL PERFORMANCE
VENDORS EXTEND YOUR RISK • Understand where your security perimeter ends • Supplier security is paramount, especially for small to midmarket companies and nonprofits • Leverage your risk assessment process o What data can they access? • Extend process to include their controls and safeguards o How is it protected? • Exercise right to audit
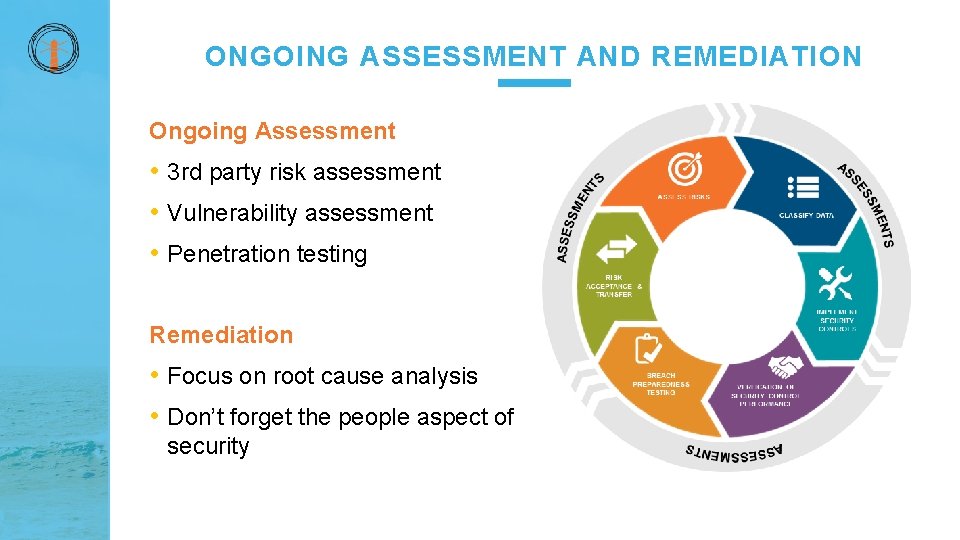
ONGOING ASSESSMENT AND REMEDIATION Ongoing Assessment • 3 rd party risk assessment • Vulnerability assessment • Penetration testing Remediation • Focus on root cause analysis • Don’t forget the people aspect of security
IMPLEMENTATION APPROACH QUESTION How can you move rapidly to build and enhance a cybersecurity program? ANSWER It depends…
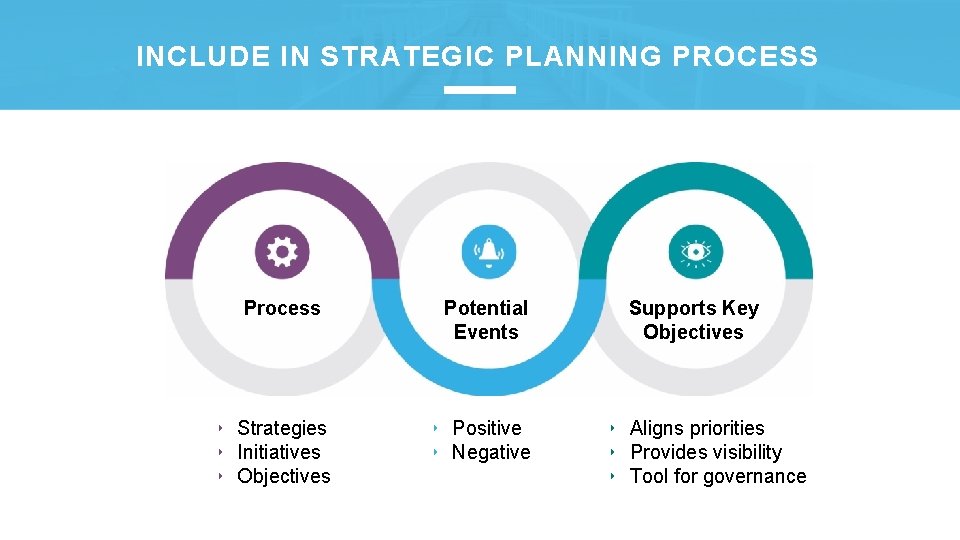
INCLUDE IN STRATEGIC PLANNING PROCESS Process ‣ Strategies ‣ Initiatives ‣ Objectives Potential Events ‣ Positive ‣ Negative Supports Key Objectives ‣ Aligns priorities ‣ Provides visibility ‣ Tool for governance
IMPLEMENTATION APPROACH Collaboration Transparency Integration Governance

DO YOU PROCESS DONATIONS ONLINE? RAISE YOUR HAND
KEYS TO SUCCESS Threats continue to increase in frequency and complexity, so: • Nonprofits must be proactive to maintain security • Support from the top is a necessity • Align cybersecurity with other mission-driven initiatives (including strategic planning process) • Increase collaboration, communication and transparency • Apply governance principles throughout
COMPLEXITY IS STILL THE ENEMY OF SECURITY Goals to aim for: • Integration • Consolidation o Fewer devices o More capabilities • Automation

QUESTIONS ? RAISE YOUR HAND! WE’LL BRING A MIC OVER!
- Slides: 28